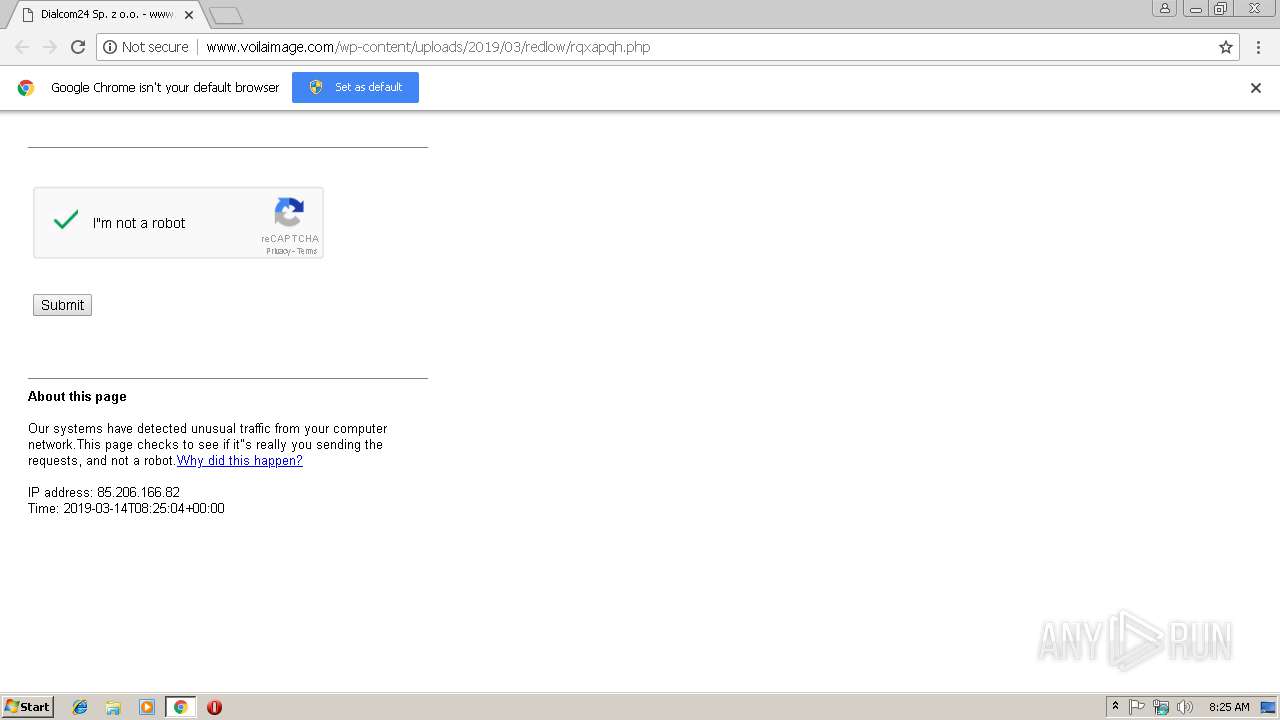
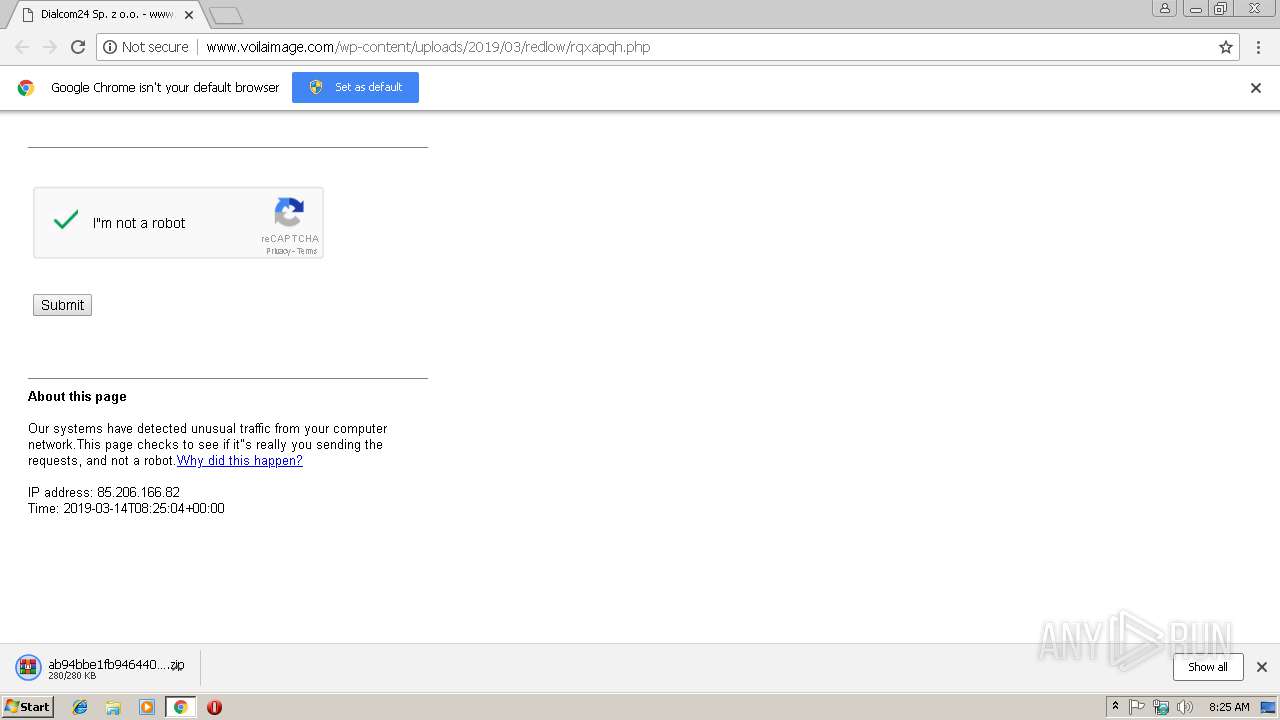
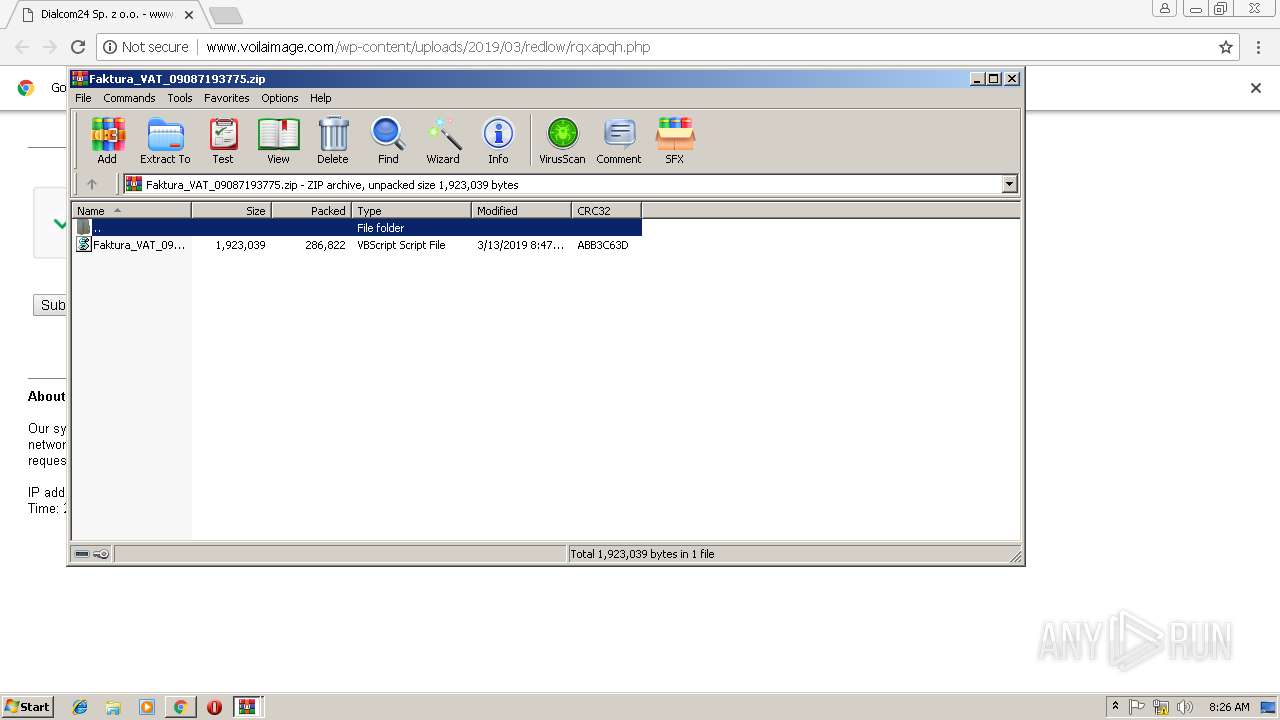
| URL: | http://voilaimage.com/wp-content/uploads/2019/03/redlow/rqxapqh.php |
| Full analysis: | https://app.any.run/tasks/a055f311-81ec-41aa-852e-2d427649a46e |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 08:24:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E8956CDCA63C6CCBE4066E4483CDF08C |
| SHA1: | 00EFAC9E28FF94F5F739F8B00B2404F42702022C |
| SHA256: | 1703BA9F6761E9BC7E18A234FB4BA69E7BE109B06A72994D41131ABC54A1FB51 |
| SSDEEP: | 3:N1KIXKMIECJK3SVOlAQyX28K6KXEEV+:CIXKMIrJFVOlAZG908+ |
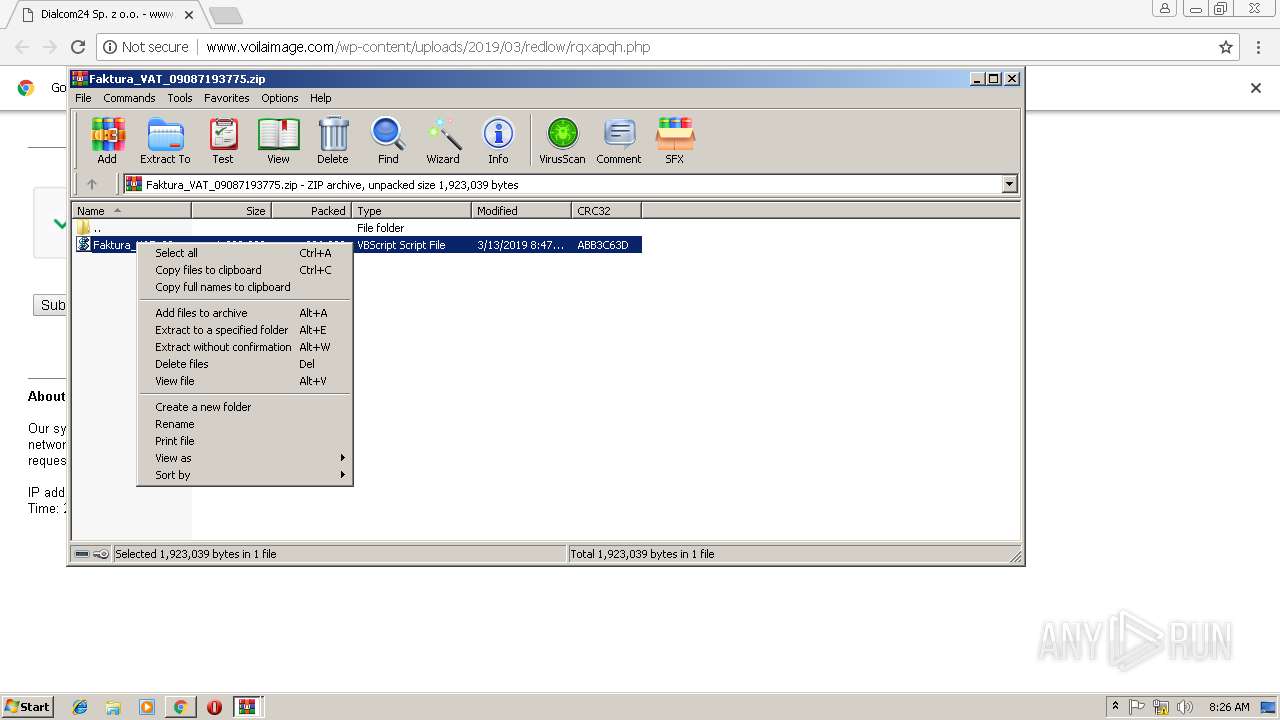
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3240)
- rundll32.exe (PID: 2676)
Registers / Runs the DLL via REGSVR32.EXE
- WScript.exe (PID: 3632)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 3632)
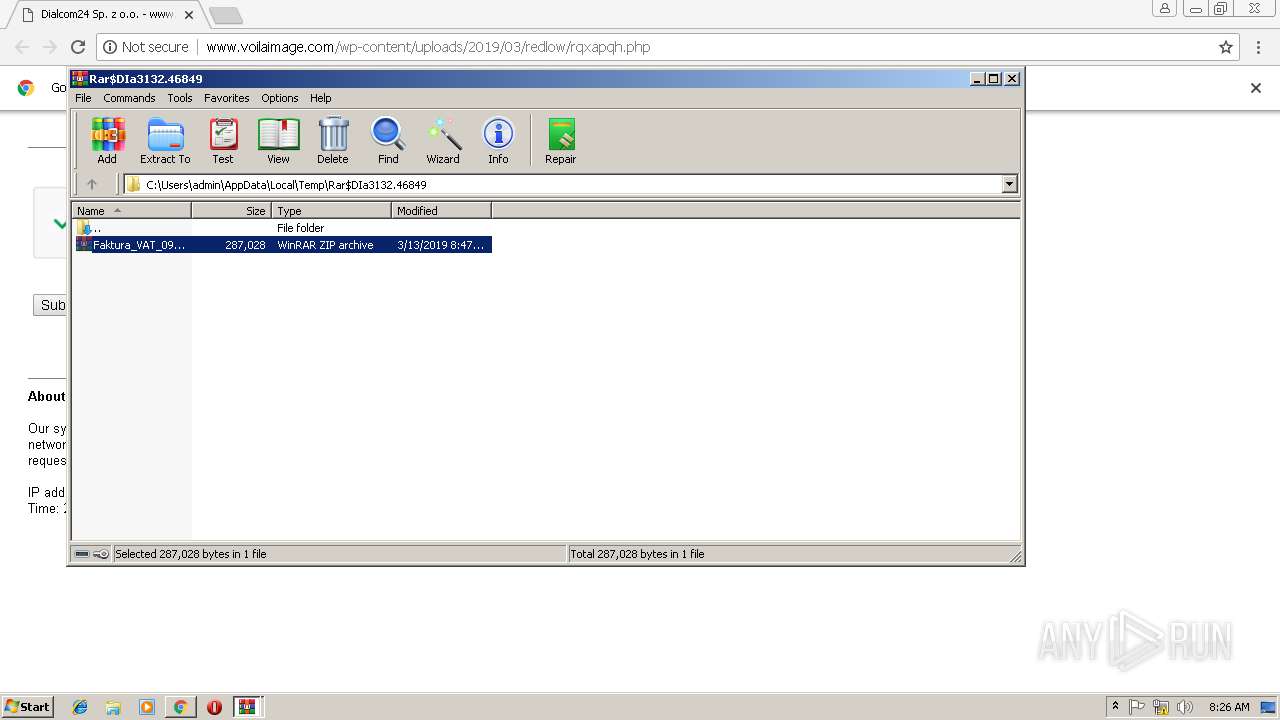
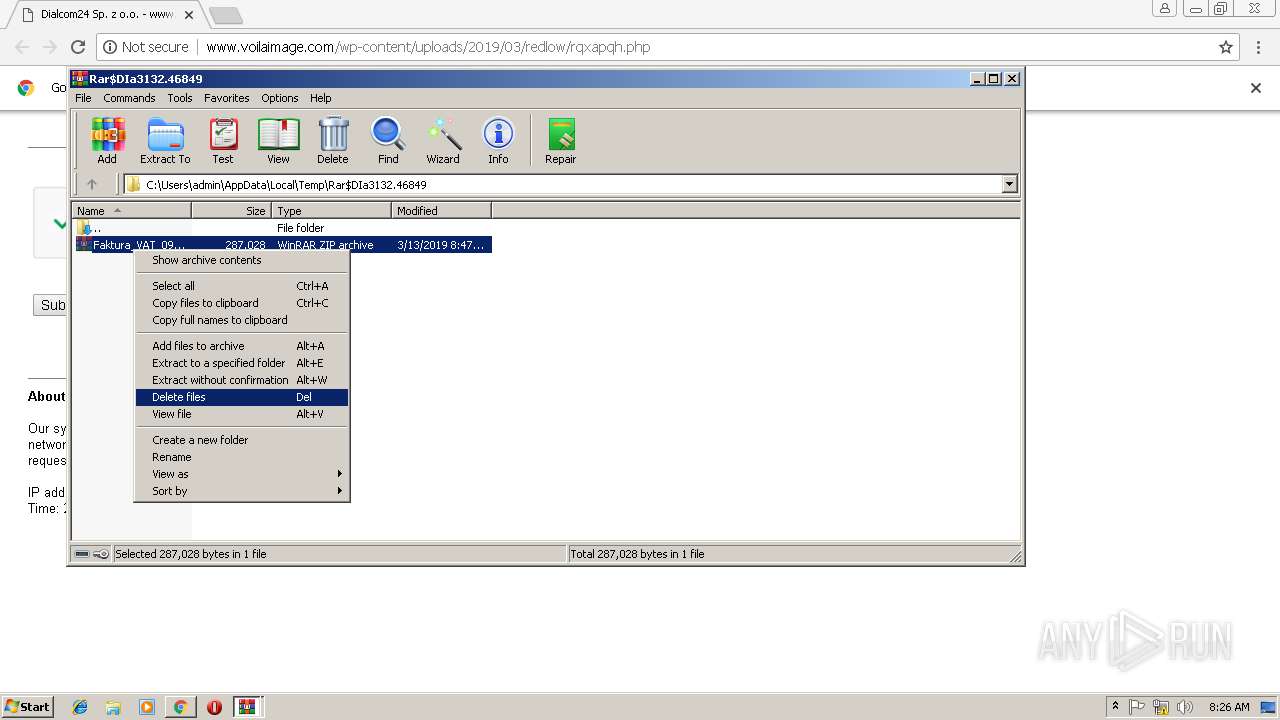
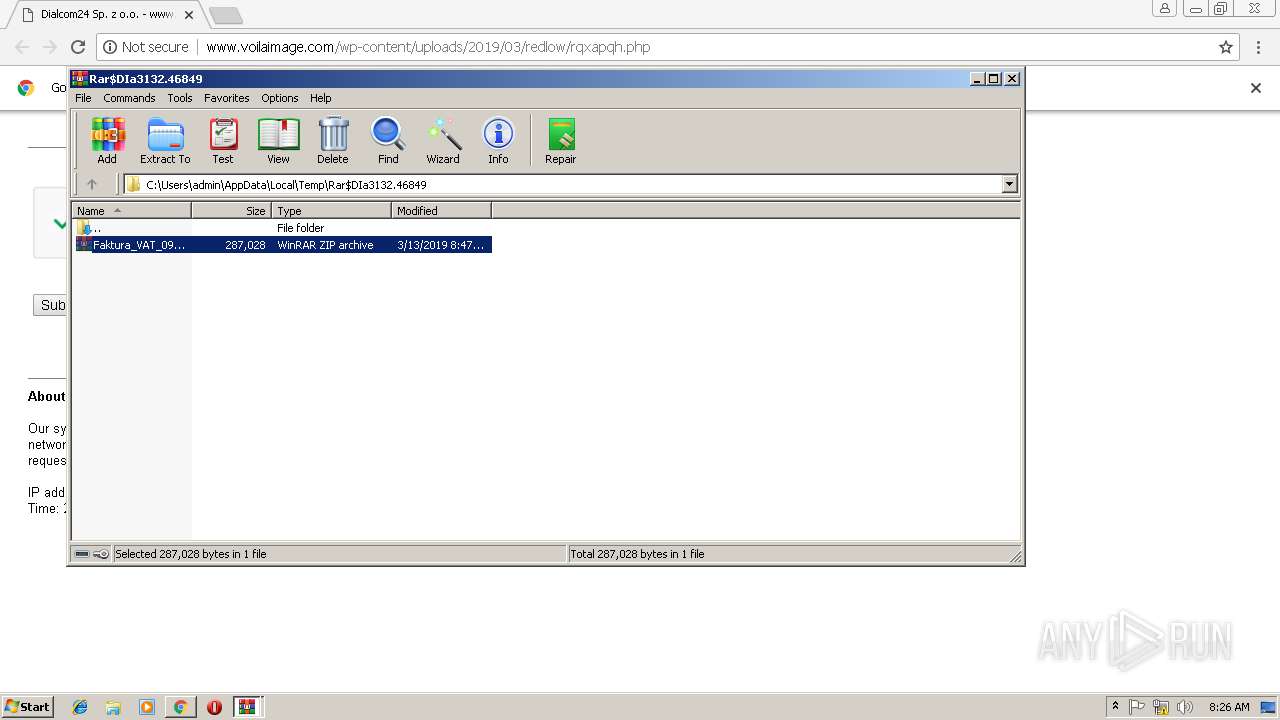
Application launched itself
- WinRAR.exe (PID: 3132)
Uses RUNDLL32.EXE to load library
- regsvr32.exe (PID: 3240)
Executes scripts
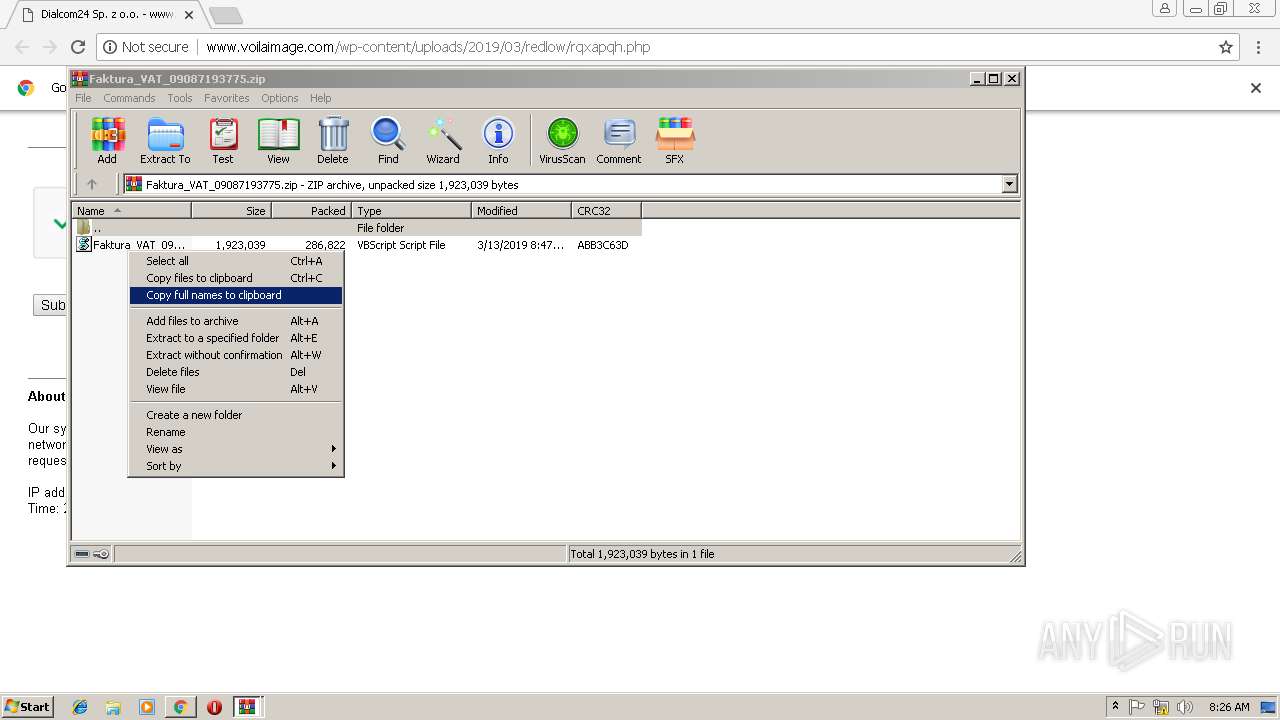
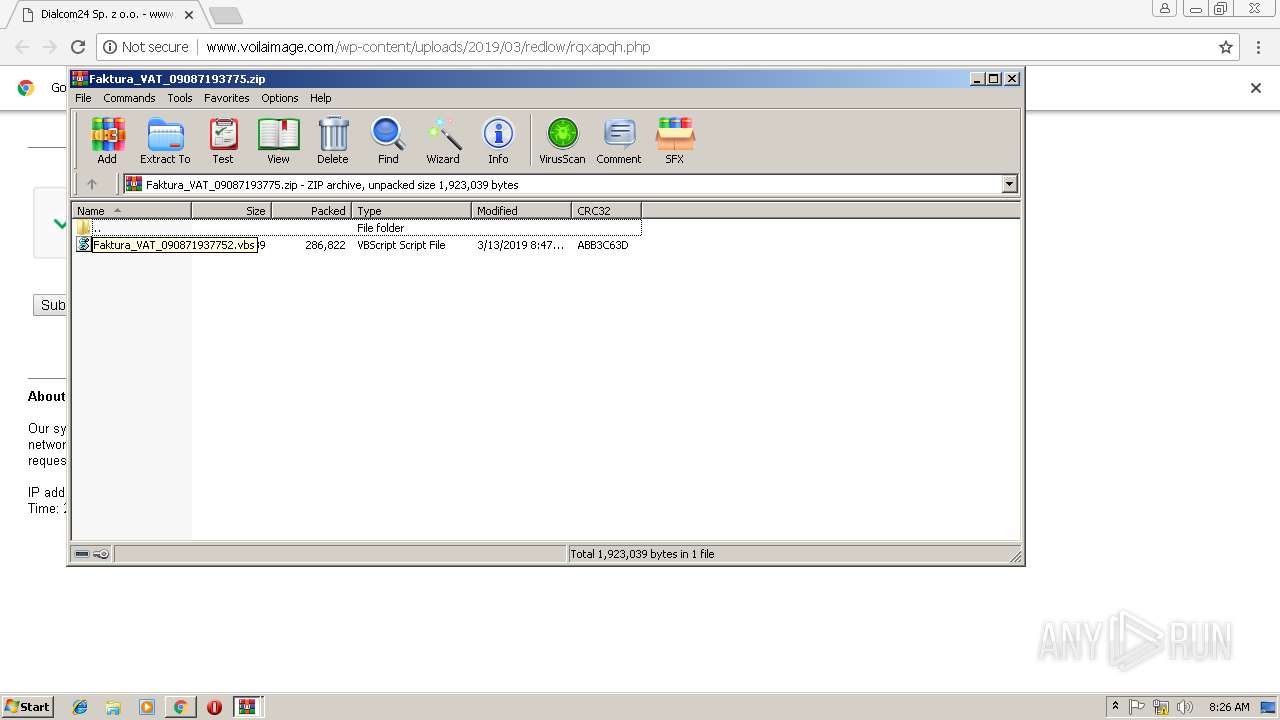
- WinRAR.exe (PID: 3684)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2748)
Application launched itself
- chrome.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
16
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
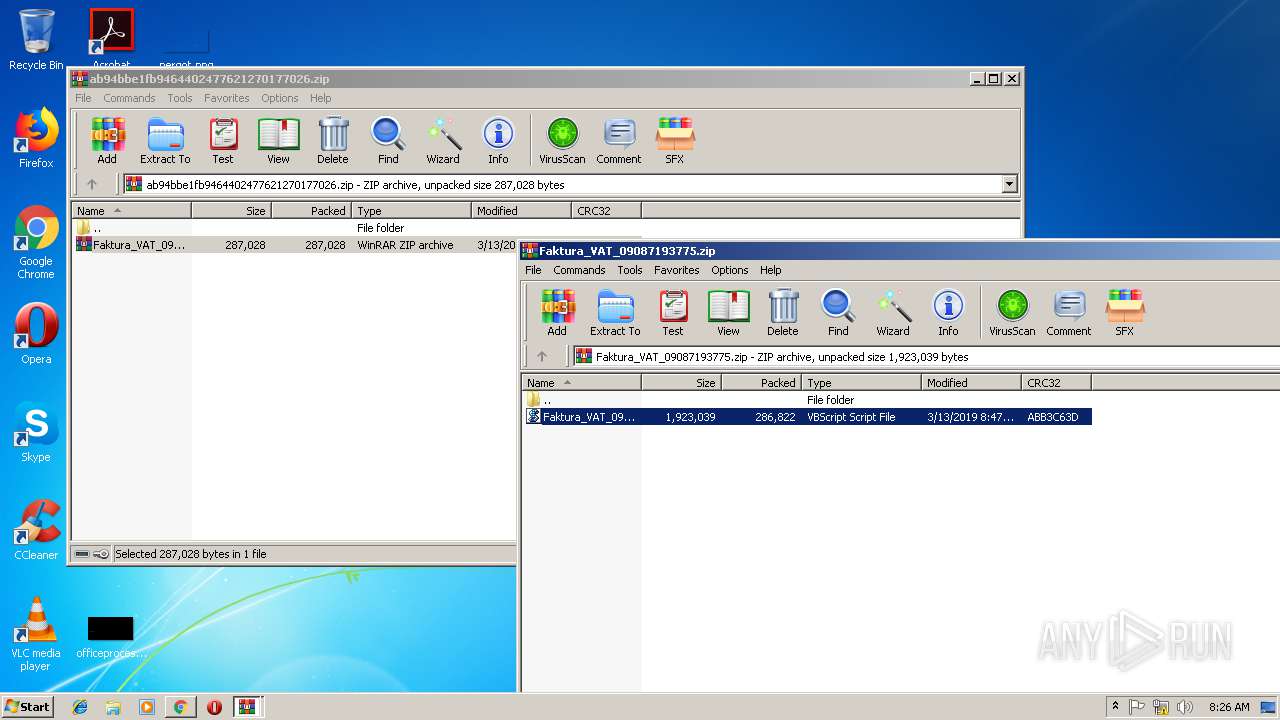
| 340 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3684.2499\Faktura_VAT_090871937752.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2752 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D24AAD625AB16B6FA0E38663173B429A --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=27AD89FC8BB72F08471F18F7D30E85AB --mojo-platform-channel-handle=2464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=799686DB822B9B8837BF1AEACD406BDA --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2676 | C:\Windows\system32\\rundll32.exe C:\Users\admin\AppData\Local\Temp\ofoM.dll,f0 | C:\Windows\system32\rundll32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://voilaimage.com/wp-content/uploads/2019/03/redlow/rqxapqh.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=7D54F1FD2EBDA03F550594F9872F4BC4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7D54F1FD2EBDA03F550594F9872F4BC4 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
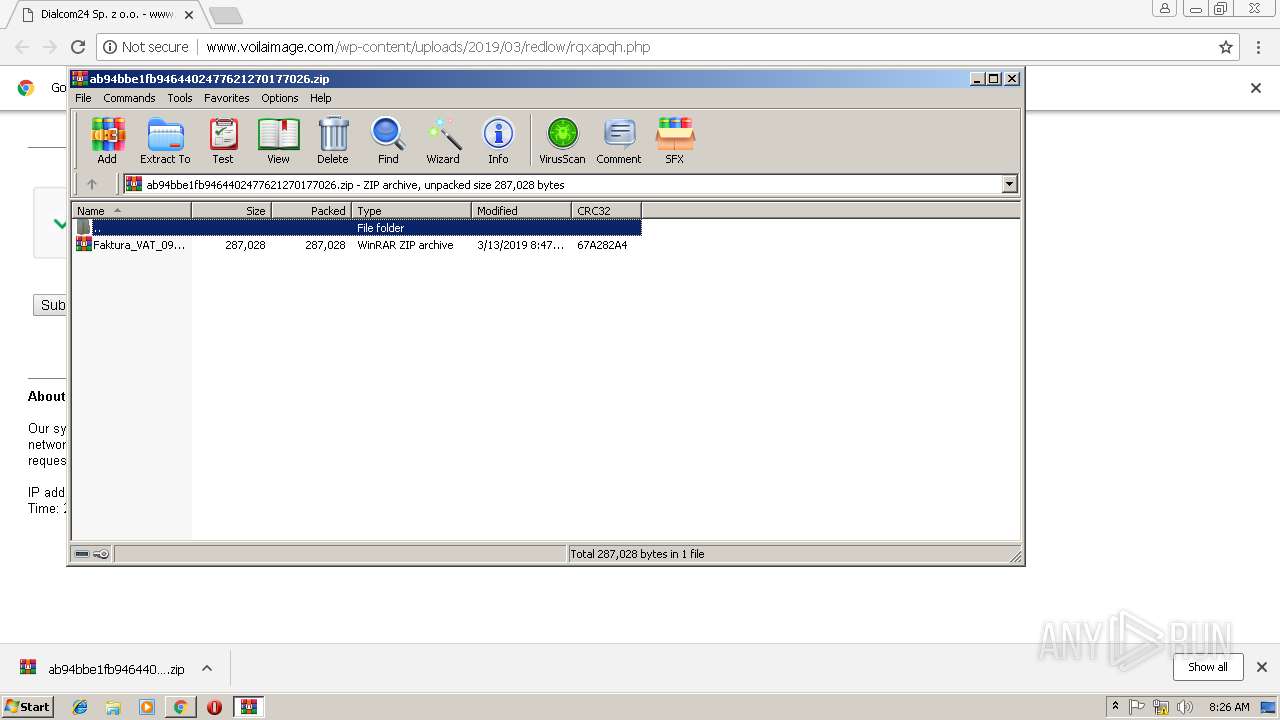
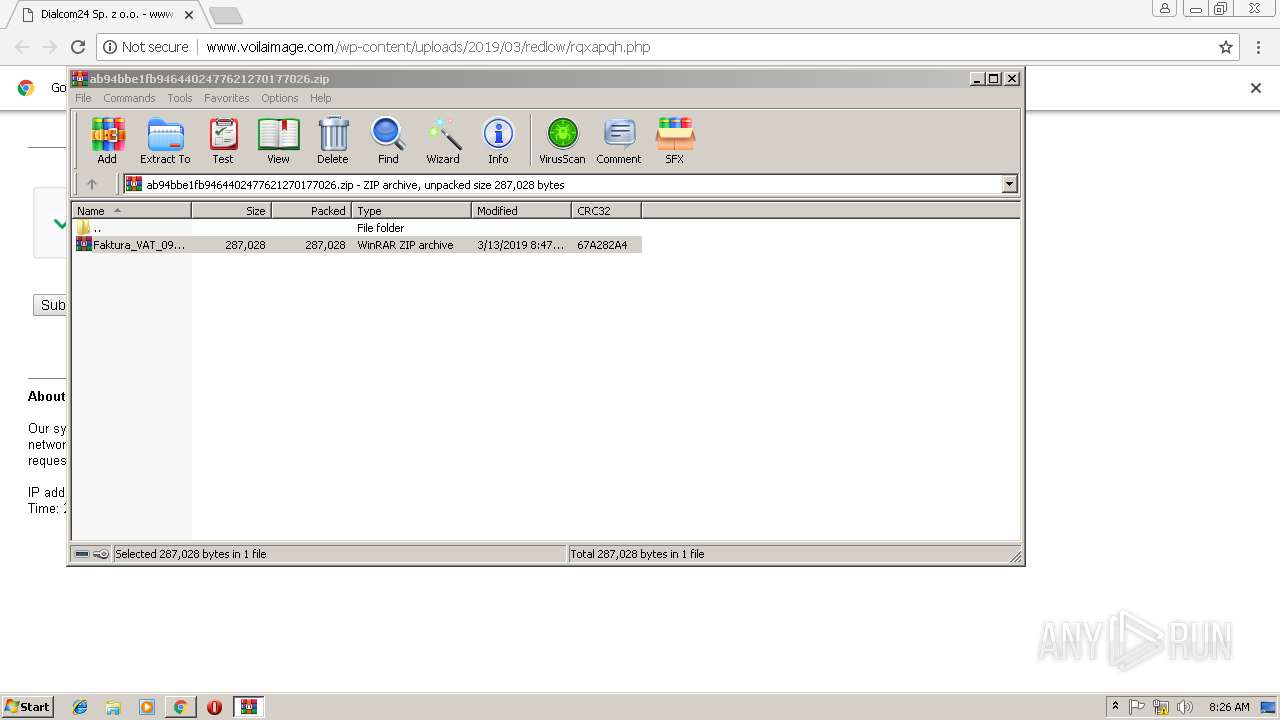
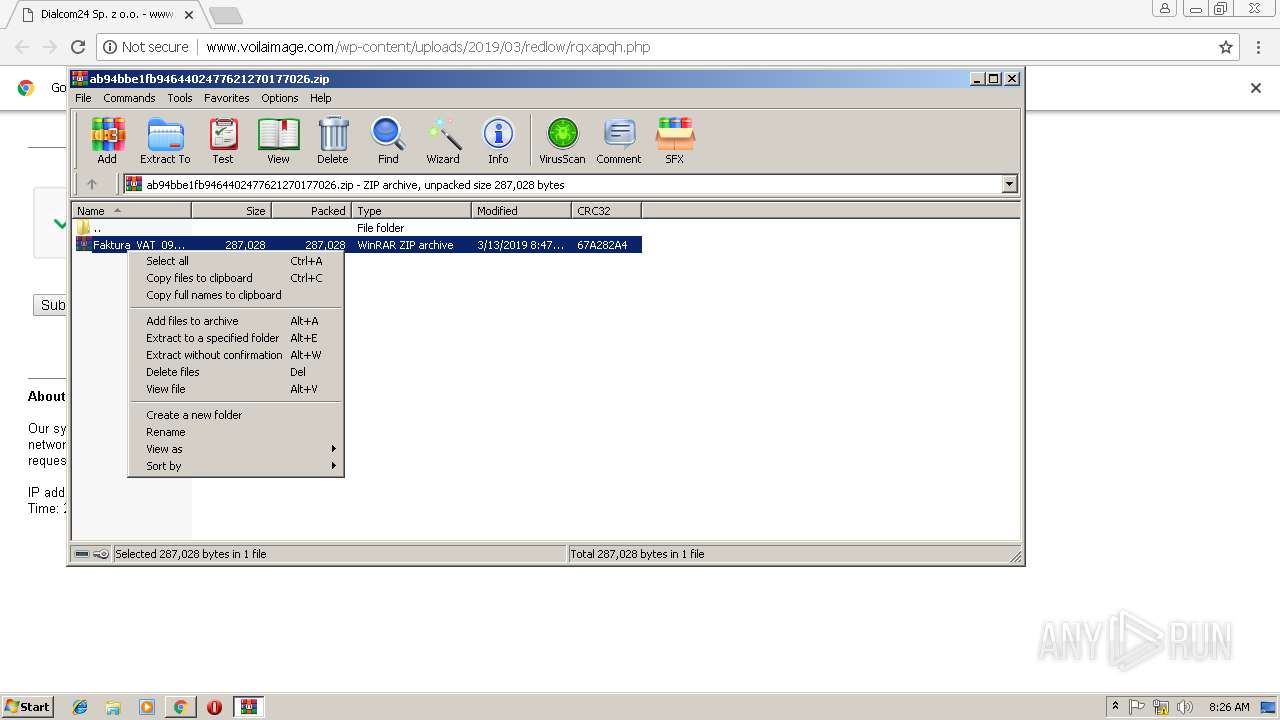
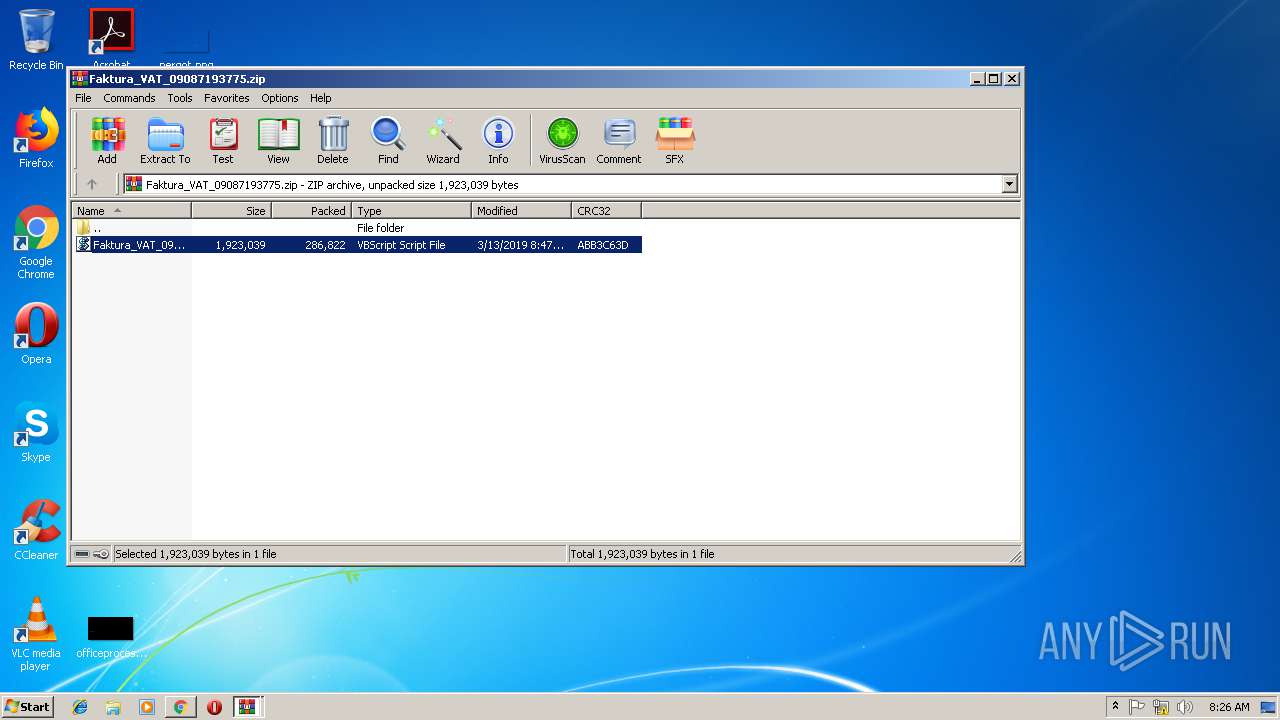
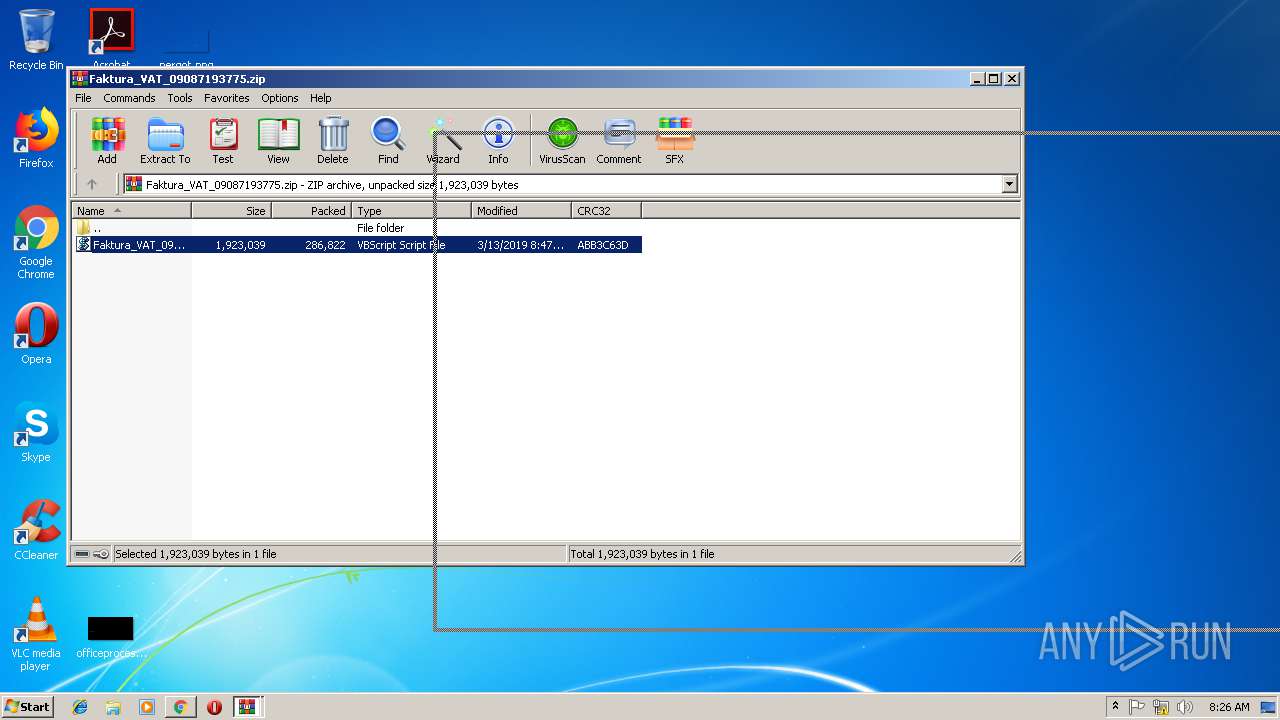
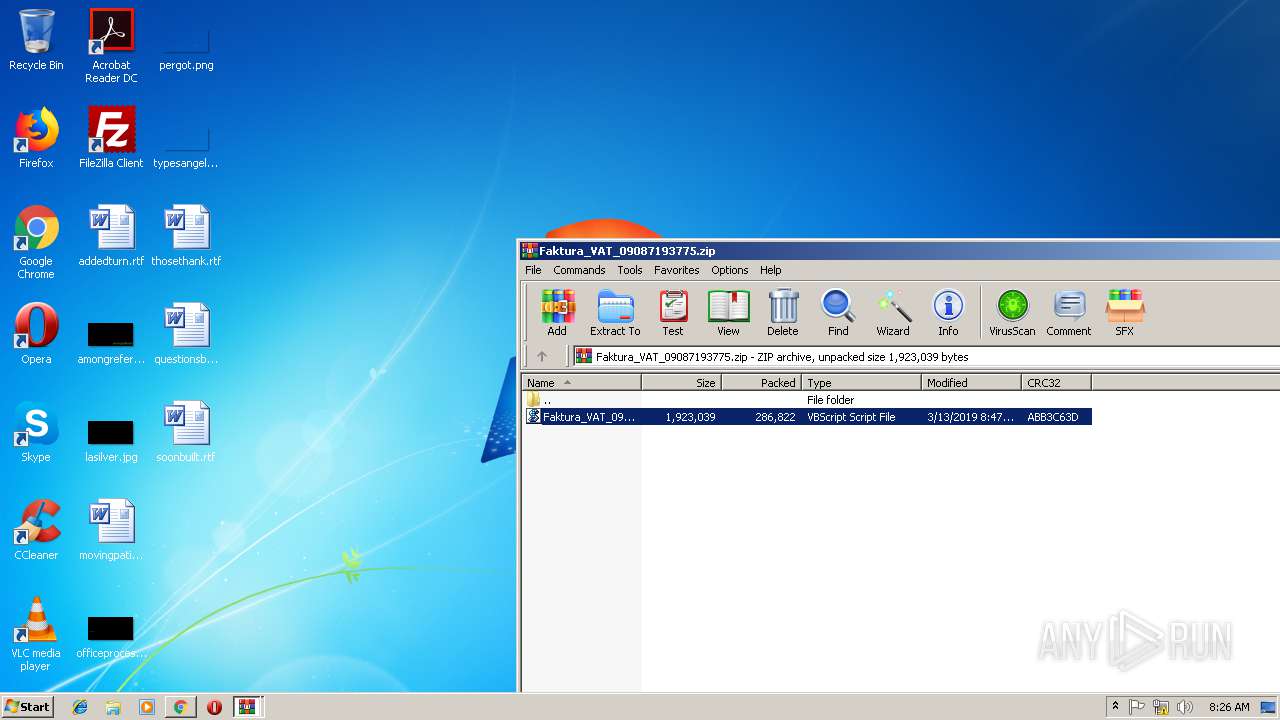
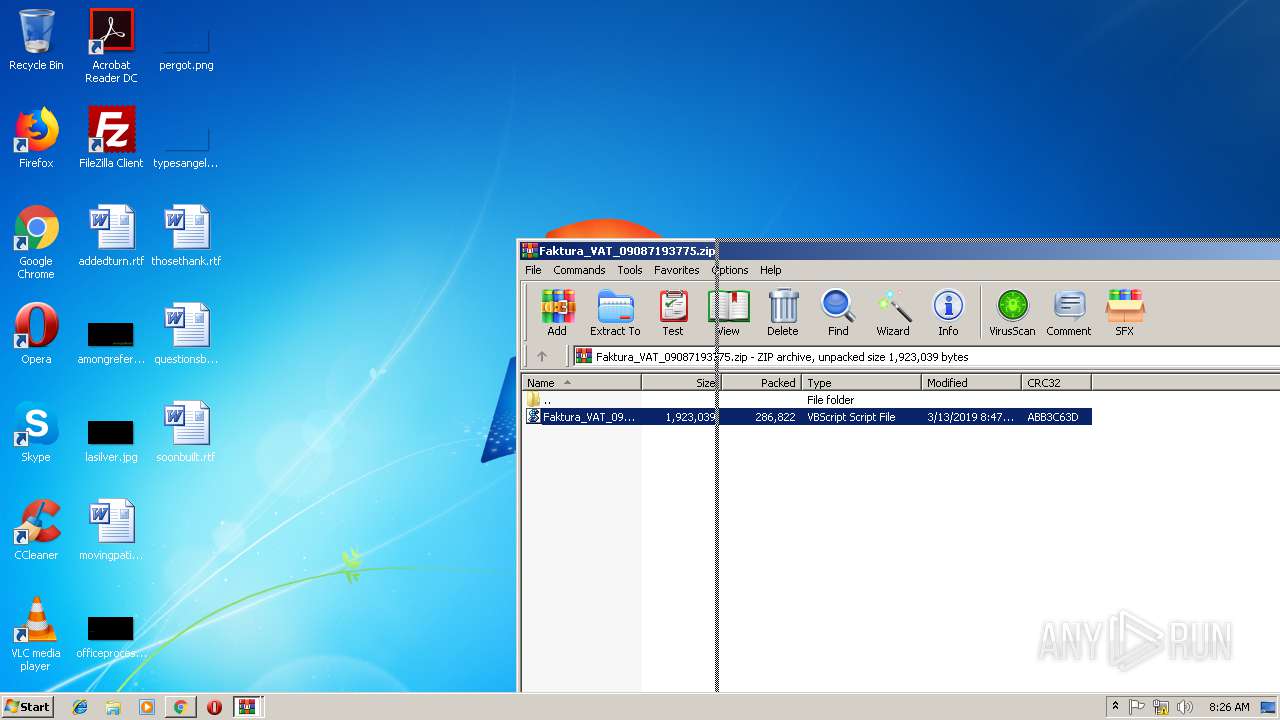
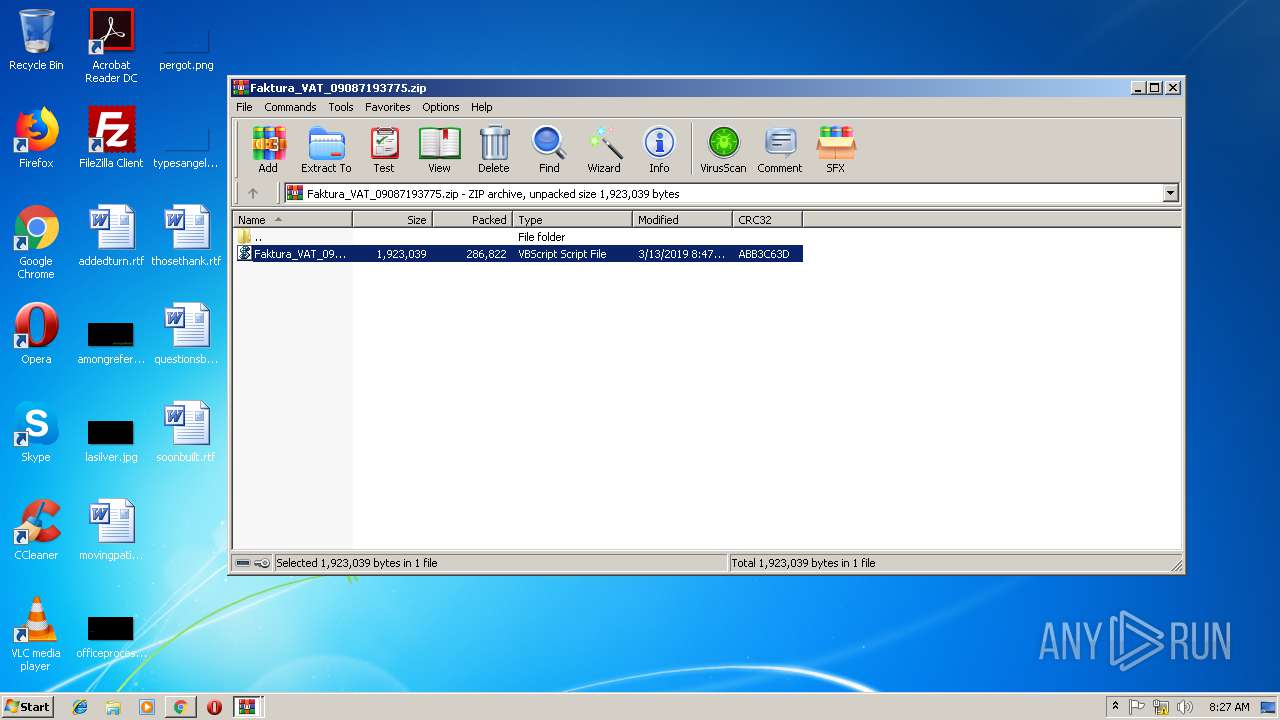
| 3132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ab94bbe1fb9464402477621270177026.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=255A988EE7649BB5EE6978F7373AF367 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 841
Read events
1 744
Write events
94
Delete events
3
Modification events
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2748-13197025500764750 |
Value: 259 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2748-13197025500764750 |
Value: 259 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
6
Suspicious files
31
Text files
68
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4cfba733-4308-44a7-8e63-db4e11cb7ad1.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f4176161-f60e-4b4c-a26c-2d78d233f7fe.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198e9a.TMP | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF198ef8.TMP | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF19938b.TMP | binary | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
10
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | chrome.exe | GET | 200 | 195.8.66.1:80 | http://www.voilaimage.com/favicon.ico | GB | — | — | malicious |
2748 | chrome.exe | GET | — | 195.8.66.1:80 | http://www.voilaimage.com/wp-content/uploads/2019/03/redlow/rqxapqh.php?downb5cfd4137054dc89ea2ce70b5db9c5b2 | GB | — | — | malicious |
2748 | chrome.exe | GET | 301 | 195.8.66.1:80 | http://voilaimage.com/wp-content/uploads/2019/03/redlow/rqxapqh.php | GB | html | 343 b | malicious |
2748 | chrome.exe | GET | 200 | 195.8.66.1:80 | http://www.voilaimage.com/wp-content/uploads/2019/03/redlow/rqxapqh.php | GB | html | 175 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 195.8.66.1:80 | voilaimage.com | Claranet Ltd | GB | suspicious |
2676 | rundll32.exe | 62.187.103.29:443 | — | — | GB | malicious |
2748 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2676 | rundll32.exe | 61.231.104.167:443 | — | Data Communication Business Group | TW | malicious |
2676 | rundll32.exe | 214.161.108.156:443 | — | DoD Network Information Center | US | malicious |
2748 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 216.58.206.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2676 | rundll32.exe | 85.192.219.39:443 | — | Teloise | FR | malicious |
2676 | rundll32.exe | 153.182.78.20:443 | — | NTT Communications Corporation | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
voilaimage.com |
| malicious |
accounts.google.com |
| shared |
www.voilaimage.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2676 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
2676 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
2676 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
2676 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
2676 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |