| File name: | KRSWL0cker.exe |
| Full analysis: | https://app.any.run/tasks/90afd431-455e-4260-9b3a-494d501e8163 |
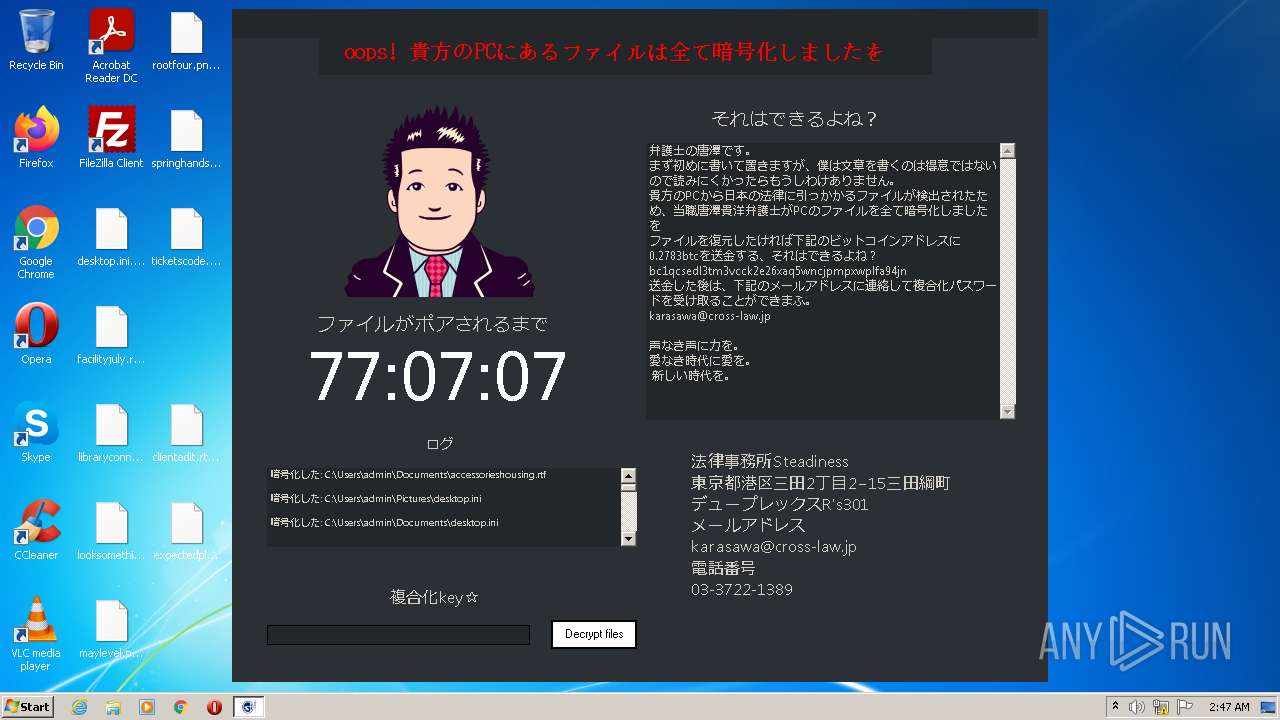
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 01:46:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | FB2E388FDFFEBD783B4164FD091ECF18 |
| SHA1: | 466AE3A186A90EEA8702E1D17C90EF42E69D260F |
| SHA256: | 16FE9B940B4483675EF1F6C72A73E195707FE7AB4C260D9DEF931BC17F98BE23 |
| SSDEEP: | 1536:pNKK+663BZWxKovAsYaN2mR4KY2vbYAm5PV45L6:nKh6CB0Uoos1N2g5YAmyL6 |
MALICIOUS
Changes the autorun value in the registry
- KRSWL0cker.exe (PID: 3064)
SUSPICIOUS
Checks supported languages
- KRSWL0cker.exe (PID: 3064)
Reads the computer name
- KRSWL0cker.exe (PID: 3064)
Creates files in the user directory
- KRSWL0cker.exe (PID: 3064)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-May-08 00:21:25 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | KRSWL0cker |
| FileVersion: | 1.0.0.0 |
| InternalName: | KRSWL0cker.exe |
| LegalCopyright: | Copyright © 2783 |
| LegalTrademarks: | - |
| OriginalFilename: | KRSWL0cker.exe |
| ProductName: | KRSWL0cker |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2022-May-08 00:21:25 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 80356 | 80384 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.59342 |
.reloc | 90112 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
.rsrc | 98304 | 1464 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.1267 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30248 | 812 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#2) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3064 | "C:\Users\admin\AppData\Local\Temp\KRSWL0cker.exe" | C:\Users\admin\AppData\Local\Temp\KRSWL0cker.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: KRSWL0cker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
189
Read events
180
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3064) KRSWL0cker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NR |
Value: "C:\Users\admin\AppData\Local\Temp\KRSWL0cker.exe" | |||
| (PID) Process: | (3064) KRSWL0cker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3064) KRSWL0cker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3064) KRSWL0cker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3064) KRSWL0cker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
31
Text files
68
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | KRSWL0cker.exe | C:\Users\admin\Pictures\desktop.ini.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\AppData\Local\Temp\krswtkhrkrs.txt | text | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Desktop\facilityjuly.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Pictures\mortgagetom.jpg.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Desktop\clientedit.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Documents\northernsimple.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Desktop\looksomething.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Pictures\careervalid.jpg.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Documents\volpeace.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
| 3064 | KRSWL0cker.exe | C:\Users\admin\Documents\woodexecutive.rtf.krsw | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report