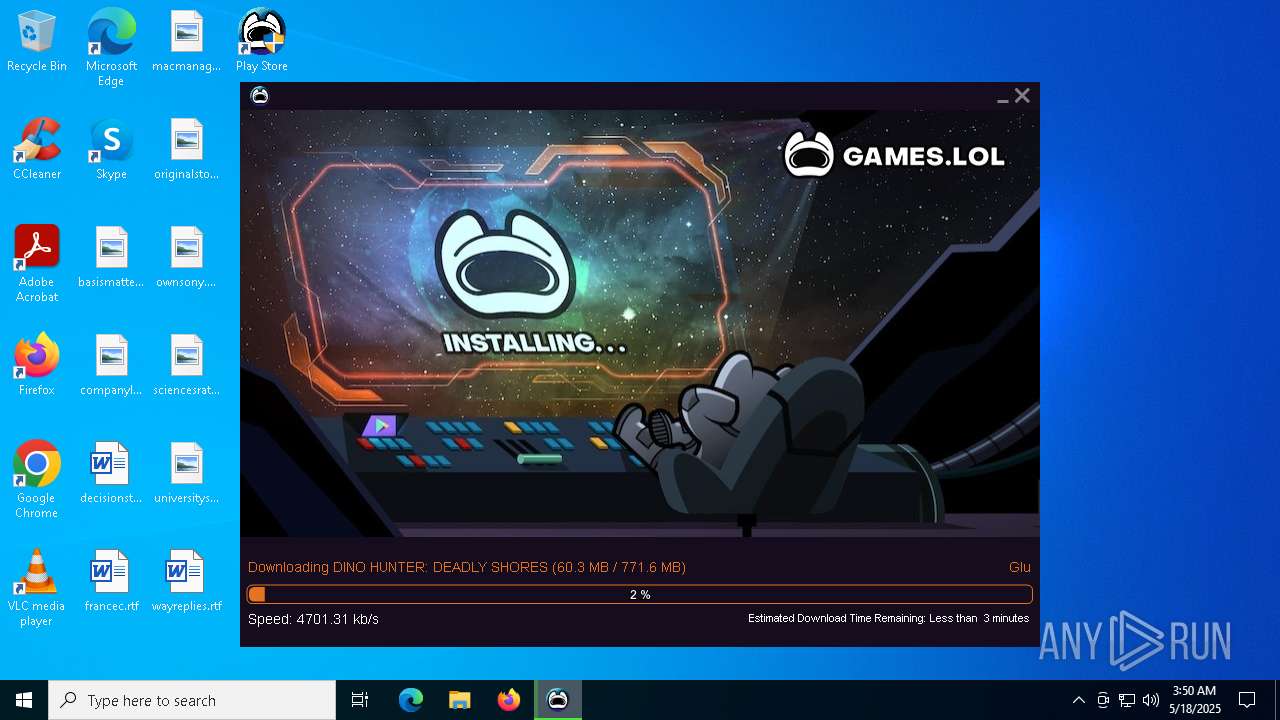
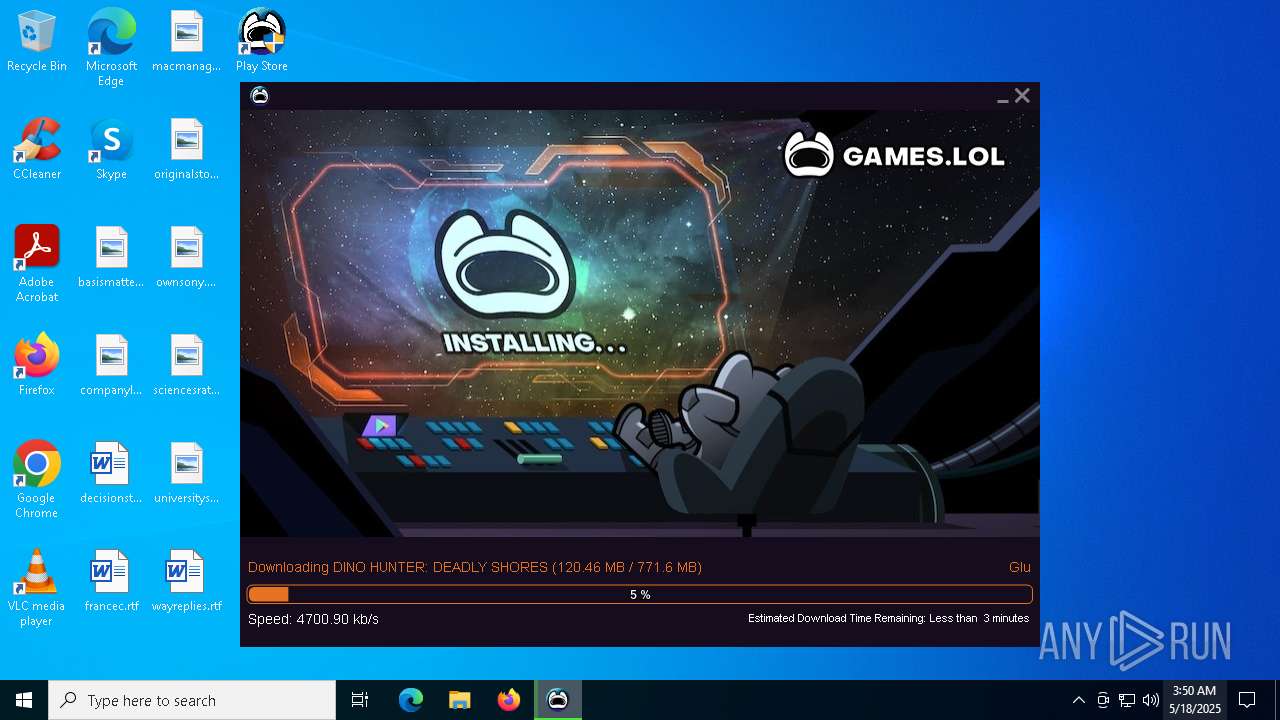
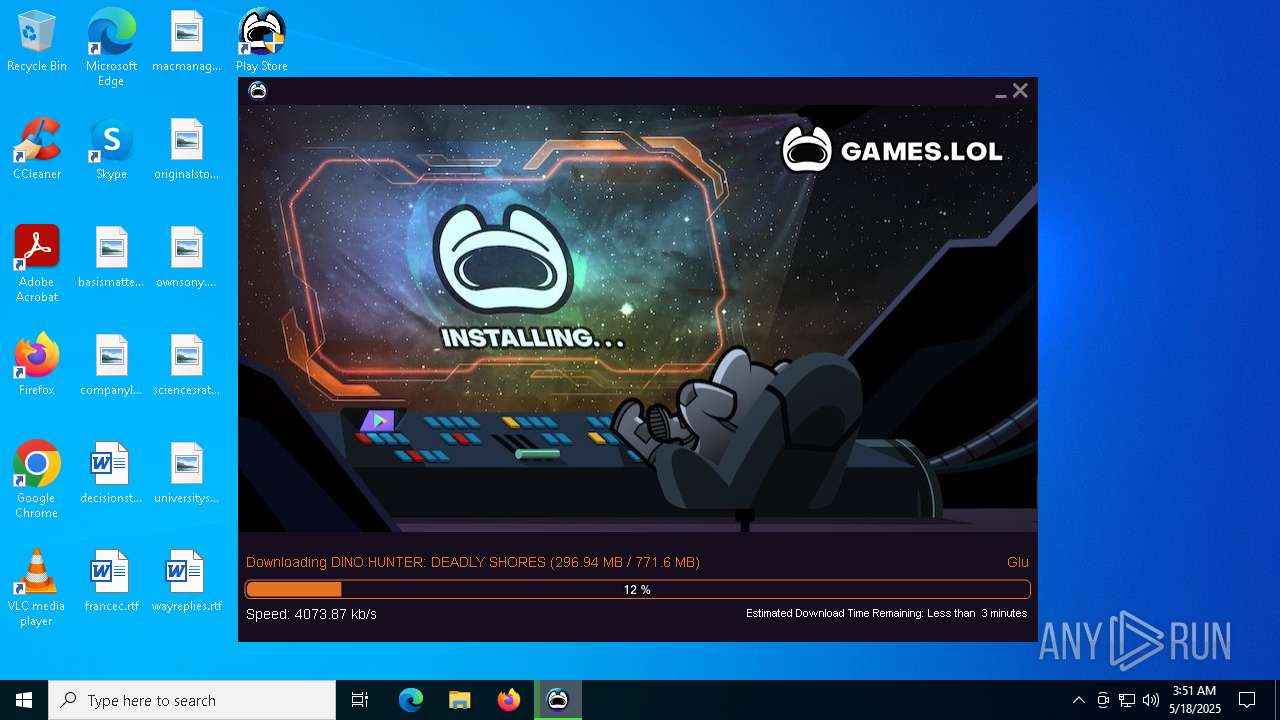
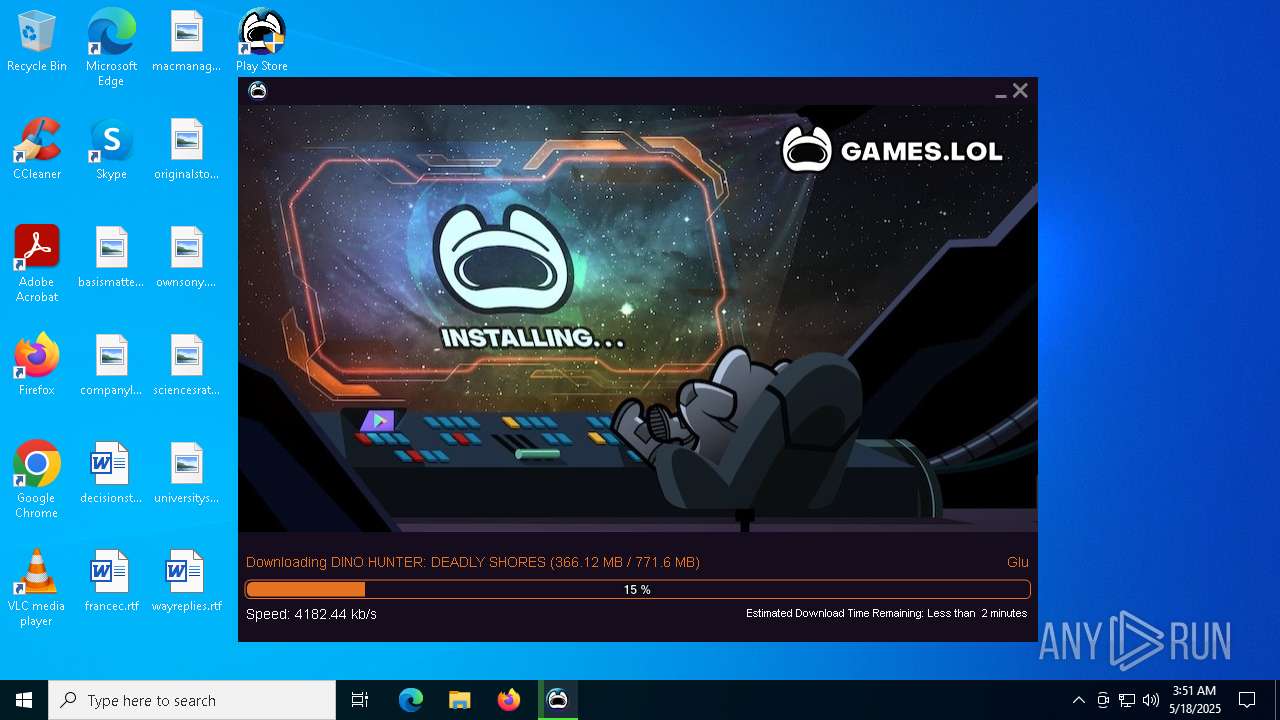
| File name: | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe |
| Full analysis: | https://app.any.run/tasks/29022655-d231-4eb7-abd1-6e1818dfaf38 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 03:49:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | E23D97827EA3C90CD85F2D11402E8940 |
| SHA1: | 67C01979B3516F9C3082CC05367142A74E413BE8 |
| SHA256: | 16F7D9D609C24C5AF75C0141059D49008EB9B1F016D198E224BDB486668CC7B5 |
| SSDEEP: | 98304:M6Q6sYmCFsQvc6zlINdRCDOkNZjzP70E+liOrofVo64kAavqD0I6g6f/+qk6LMS7:koqhe |
MALICIOUS
Changes the autorun value in the registry
- ie4uinit.exe (PID: 7992)
- ie4uinit.exe (PID: 1388)
SUSPICIOUS
Process drops legitimate windows executable
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- msiexec.exe (PID: 3024)
Executable content was dropped or overwritten
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- rundll32.exe (PID: 7888)
- rundll32.exe (PID: 3760)
- rundll32.exe (PID: 976)
- rundll32.exe (PID: 6072)
- rundll32.exe (PID: 8144)
Reads the date of Windows installation
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Starts POWERSHELL.EXE for commands execution
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
Starts CMD.EXE for commands execution
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- rundll32.exe (PID: 8144)
The executable file from the user directory is run by the CMD process
- sysinfo-app.exe (PID: 6800)
Executes as Windows Service
- WmiApSrv.exe (PID: 7220)
Reads security settings of Internet Explorer
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Reads the Windows owner or organization settings
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
Application launched itself
- msiexec.exe (PID: 3024)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 7616)
- msiexec.exe (PID: 5232)
The process drops C-runtime libraries
- msiexec.exe (PID: 3024)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 3024)
INFO
Checks supported languages
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- sysinfo-app.exe (PID: 6800)
- MobiHelper.exe (PID: 7688)
Creates files or folders in the user directory
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- ie4uinit.exe (PID: 7992)
Process checks computer location settings
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Reads the machine GUID from the registry
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Reads Environment values
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
Reads the computer name
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- sysinfo-app.exe (PID: 6800)
- MobiHelper.exe (PID: 7688)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Disables trace logs
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
Checks proxy server information
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Reads the software policy settings
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- slui.exe (PID: 7444)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Creates files in the program directory
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
Create files in a temporary directory
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
- MobiHelper.exe (PID: 7688)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 4180)
Reads CPU info
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
Reads security settings of Internet Explorer
- ie4uinit.exe (PID: 7992)
- ie4uinit.exe (PID: 1388)
- Taskmgr.exe (PID: 7852)
Reads product name
- MobiHelper.exe (PID: 7688)
- DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe (PID: 7248)
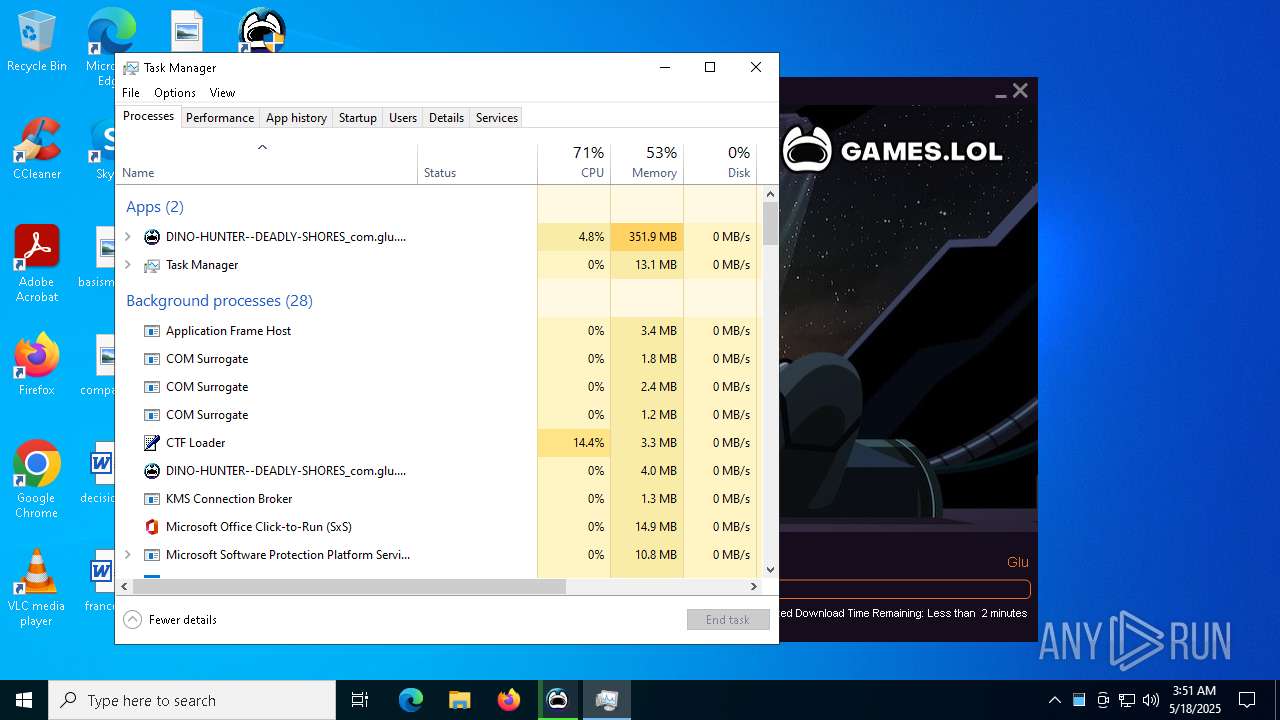
Manual execution by a user
- Taskmgr.exe (PID: 7572)
- Taskmgr.exe (PID: 7852)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3024)
The sample compiled with english language support
- msiexec.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:10:18 09:16:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.29 |
| CodeSize: | 783872 |
| InitializedDataSize: | 2619904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8b3a8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.87.1.0 |
| ProductVersionNumber: | 3.87.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 3.87.1.0 |
| InternalName: | Downloader.exe |
| LegalCopyright: | GamesLOL |
| LegalTrademarks: | - |
| OriginalFileName: | Downloader.exe |
| ProductName: | - |
| ProductVersion: | 3.87.1.0 |
| AssemblyVersion: | 3.87.1.0 |
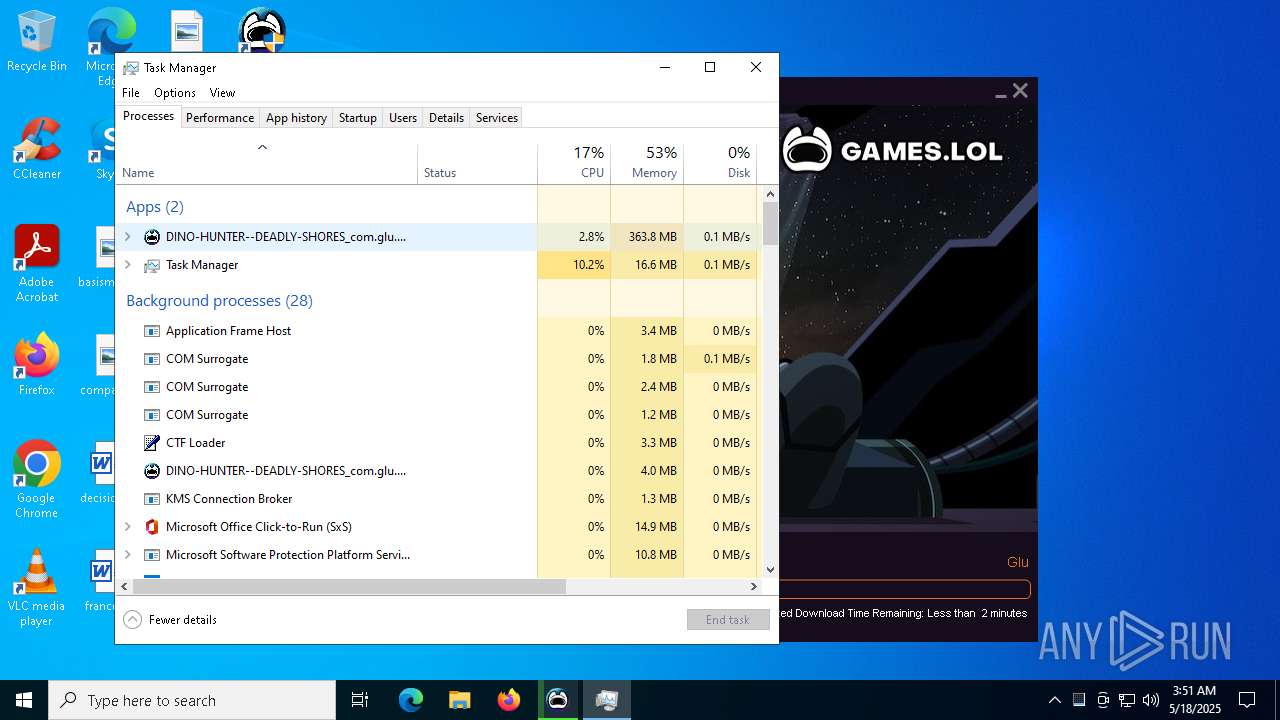
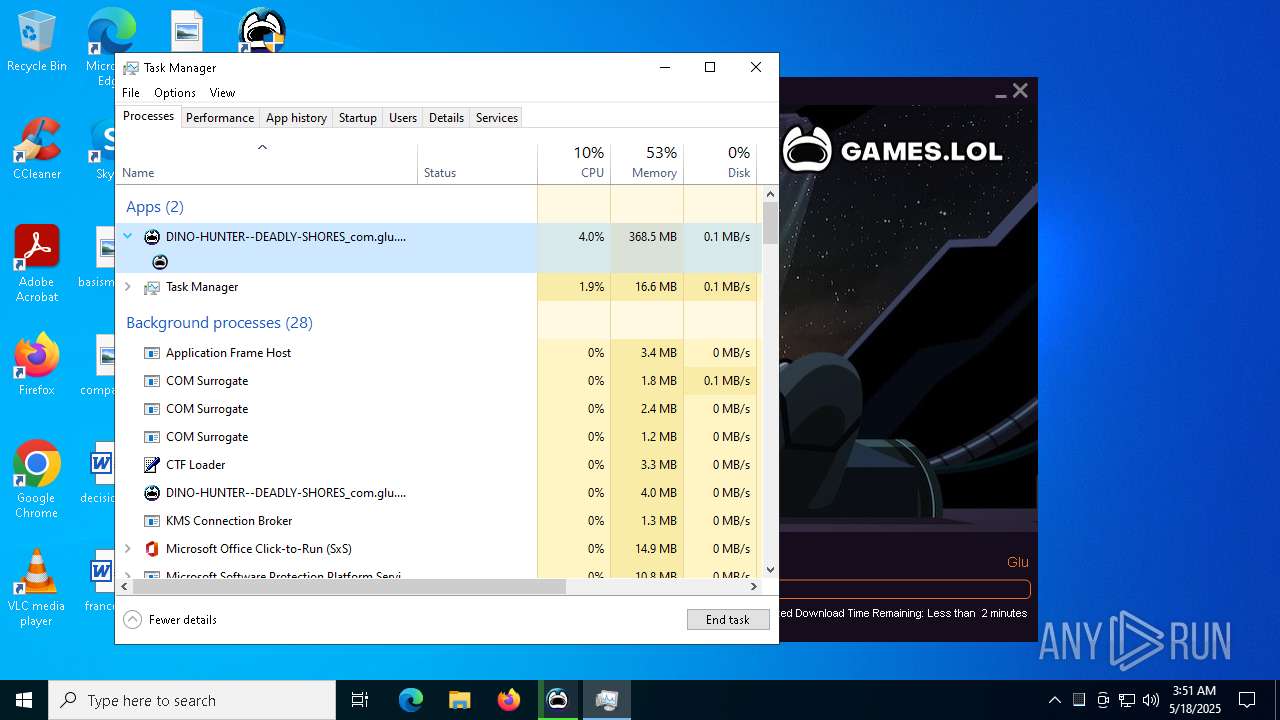
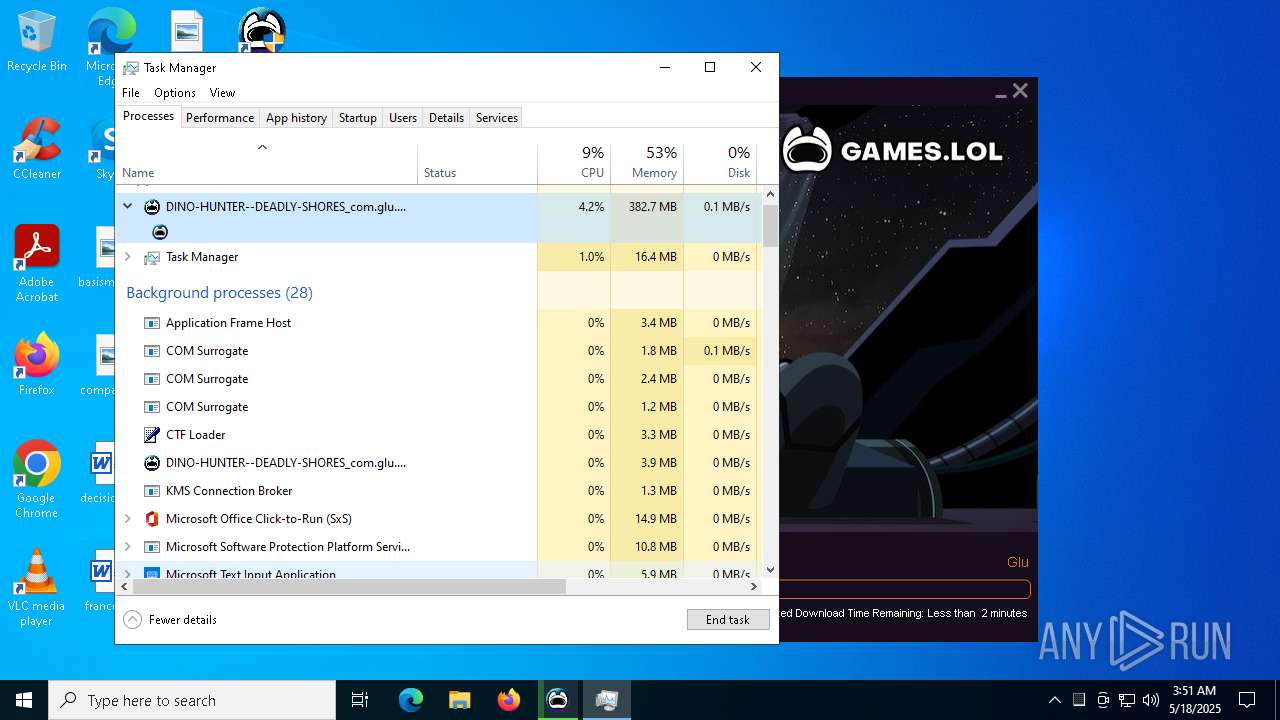
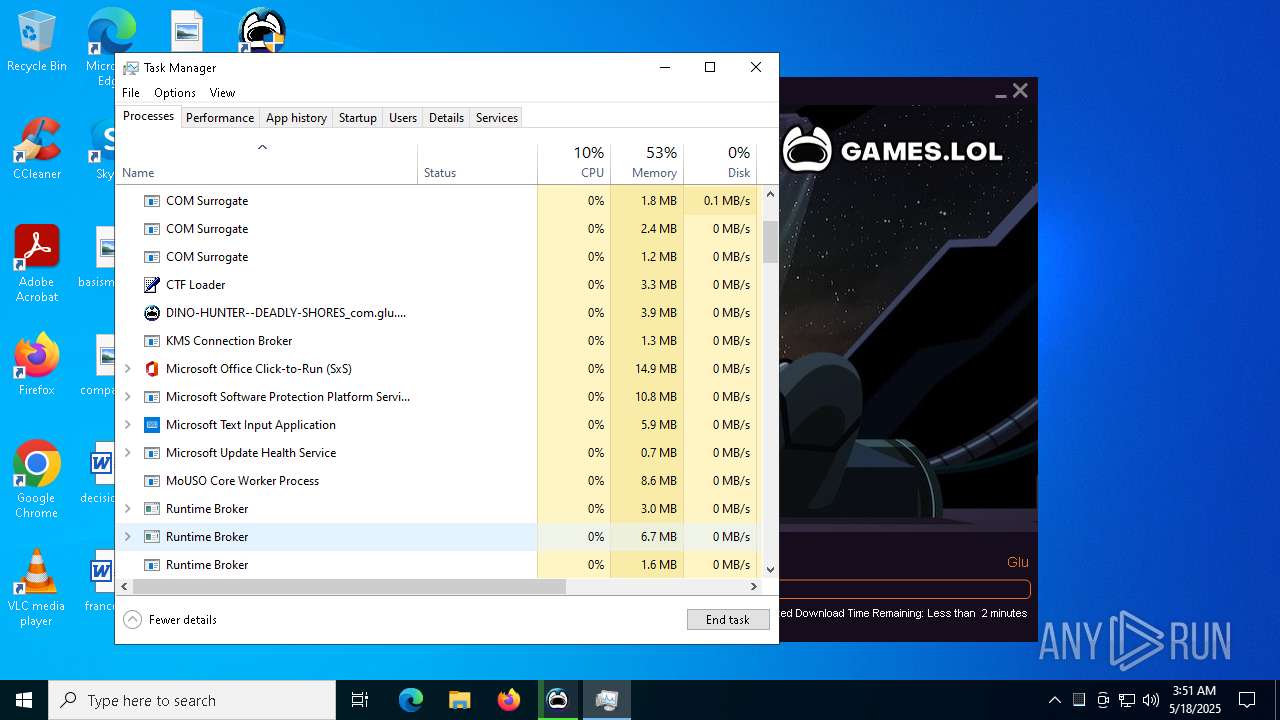
Total processes
182
Monitored processes
43
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | rundll32.exe "C:\WINDOWS\Installer\MSIA8F8.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1354046 83 VirtualBoxSetup!VirtualBoxSetup.CustomActions.CloseProcessesAndUsedFiles | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\WINDOWS\system32\ie4uinit.exe" -show | C:\Windows\System32\ie4uinit.exe | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "powershell.exe" (Get-CimInstance Win32_ComputerSystem).HypervisorPresent | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\utils\sysinfo-app.exe" | C:\Windows\System32\cmd.exe | — | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3024 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3760 | rundll32.exe "C:\WINDOWS\Installer\MSI8BF4.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1346625 32 VirtualBoxSetup!VirtualBoxSetup.CustomActions.SetSessionPropertiesFromConfig | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Users\admin\AppData\Local\Temp\DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe" | C:\Users\admin\AppData\Local\Temp\DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3.87.1.0 Modules
| |||||||||||||||
Total events
63 833
Read events
63 126
Write events
698
Delete events
9
Modification events
| (PID) Process: | (4180) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4180) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4180) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7248) DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DINO-HUNTER--DEADLY-SHORES_com_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
508
Suspicious files
152
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\MobiGame\hwid.dat | text | |
MD5:18D47A67FA67E6C2A92E62DC5989579D | SHA256:9C78F2A6B86923A5E1E9CFABF955DFD9F8315BBF88E85723421629C5D8E3389B | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\Downloader.exe.config | xml | |
MD5:6517457E21BED85A6E41E8B84942C8DC | SHA256:3148B743BB5599EE95FF171D8ED7F66C48979D5993A328F9E9291C1443E0FD28 | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\Downloader.exe | executable | |
MD5:8AFDF50F0097E7FC7254C83B2B2BF097 | SHA256:1C96BAB3B22B9E52736982B58FF5D75EB22293AA184024AD29C4F722BF1420F3 | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\log4net.dll | executable | |
MD5:7C11F28D40F846515C132C5E358913BB | SHA256:8CDAE744CB81A397C61F9311E1BD089206783B8B173D6E8216005B84662FDA1E | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\utils\sysinfo-app.exe | executable | |
MD5:2B30334153D41D8C762207309BE73D92 | SHA256:9B4EEE17B496A35E88B5F1631BA21C2BEE262B3C6DA0024C18E3D1B7996B3484 | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:82EB1CCF28F3AF897C2DB27282B41156 | SHA256:CED6CAB3C04C08CE5705AF0B6986965DBDBFDA17CBD66C973BB371ED3B95F37A | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\MobiGame\installid.dat | text | |
MD5:9CBCD6AF8818CC7DCD3805CDA4BB803B | SHA256:E00438DD545A683E94C2E116C9317F6A884F9020AADCF39E280526F7682BD5B6 | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\ResumeService.exe | executable | |
MD5:D293DB543D714D4B6A959911F04982CC | SHA256:DD31C28D11F79D4DD84C531B68FE52AA8F1076EF585BCF438D8976F8D3BAF14D | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:794C559A28F595F2DCB5489950437455 | SHA256:19DA3AE6FC8E99DE67CCD89623037886AABC68AF877B0FFDA64E21D6989C9344 | |||
| 4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | C:\Users\admin\AppData\Local\Temp\pcgame_E9F9850C\MobiHelper.exe | executable | |
MD5:751672B3DC8E48B7632544B57E01A069 | SHA256:ACFF977962EE68C47B786C28186B43B093EF41EC6ED617EE019F1227E17D8799 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
53
DNS requests
93
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | GET | 200 | 18.66.145.213:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7248 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | 108.138.2.58:443 | d3ce8h3h5q39ah.cloudfront.net | AMAZON-02 | US | whitelisted |
4180 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | 18.66.145.213:80 | ocsp.rootca1.amazontrust.com | AMAZON-02 | US | whitelisted |
7248 | DINO-HUNTER--DEADLY-SHORES_com.glu.dino_gameslolc_29011275.exe | 18.245.60.104:443 | api.mbdl219.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
d3ce8h3h5q39ah.cloudfront.net |
| whitelisted |
d3dwbsfzh4yjt6.cloudfront.net |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| whitelisted |
api.mbdl219.com |
| shared |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |