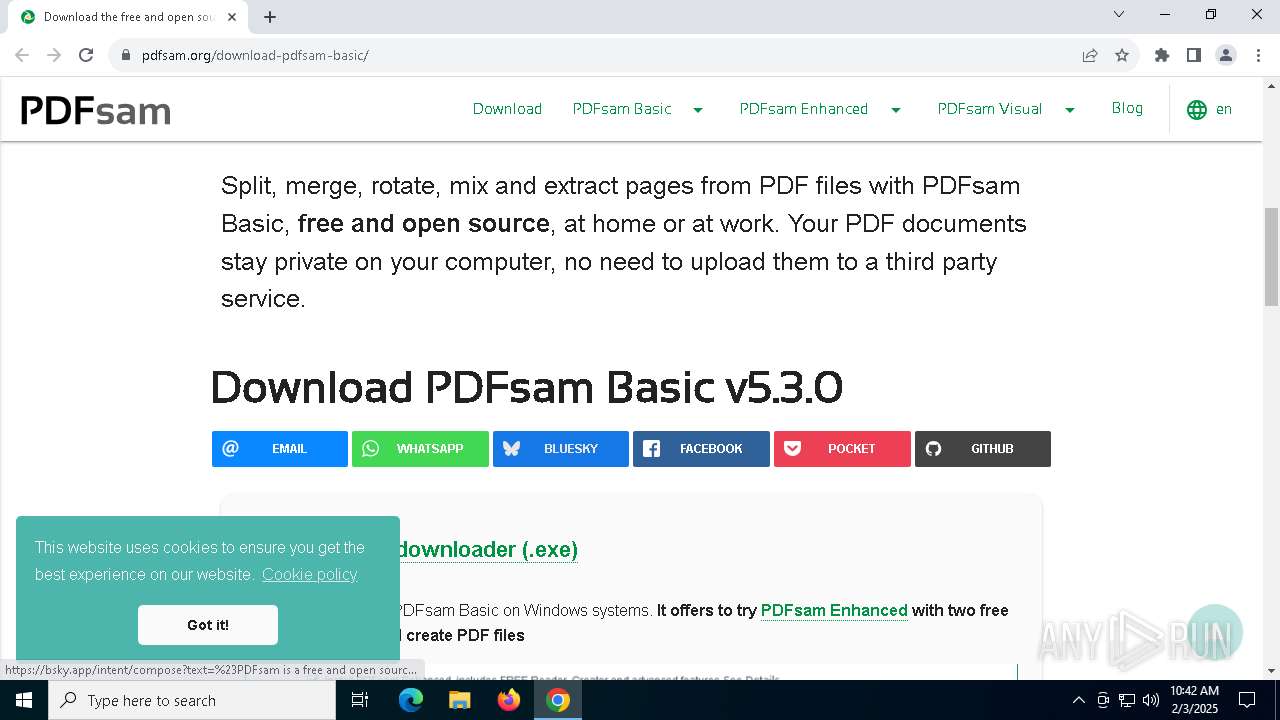
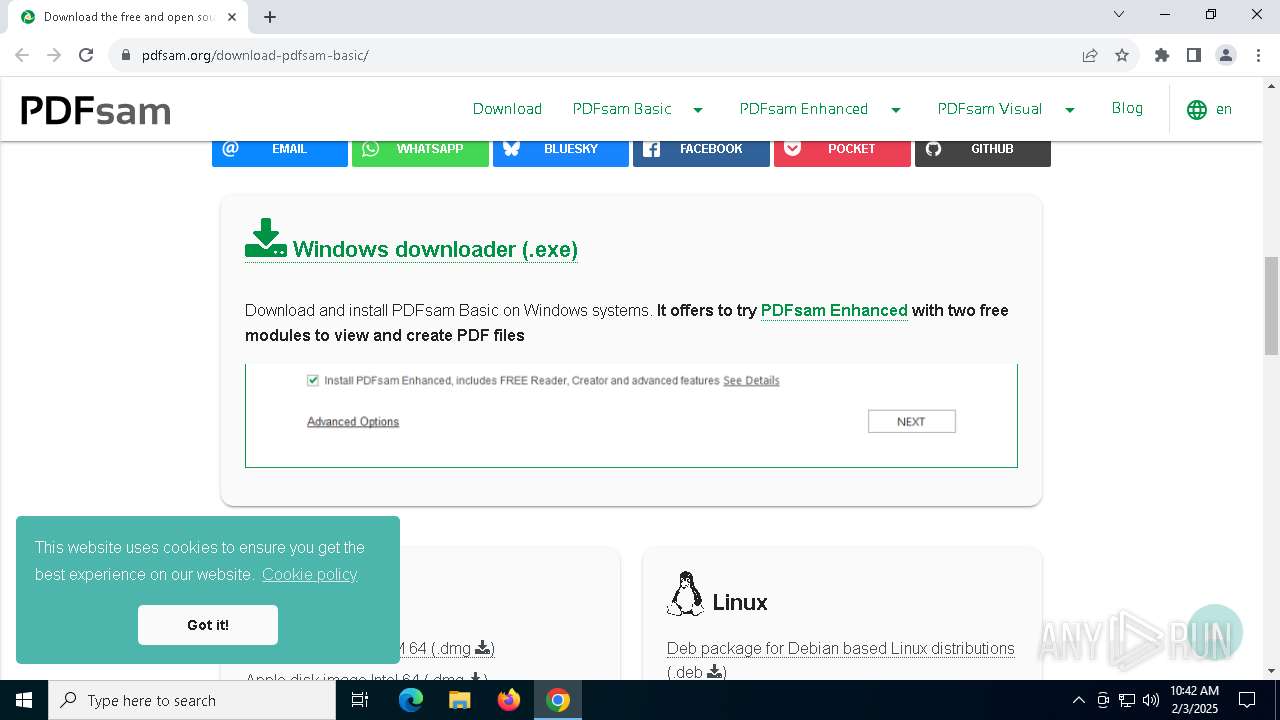
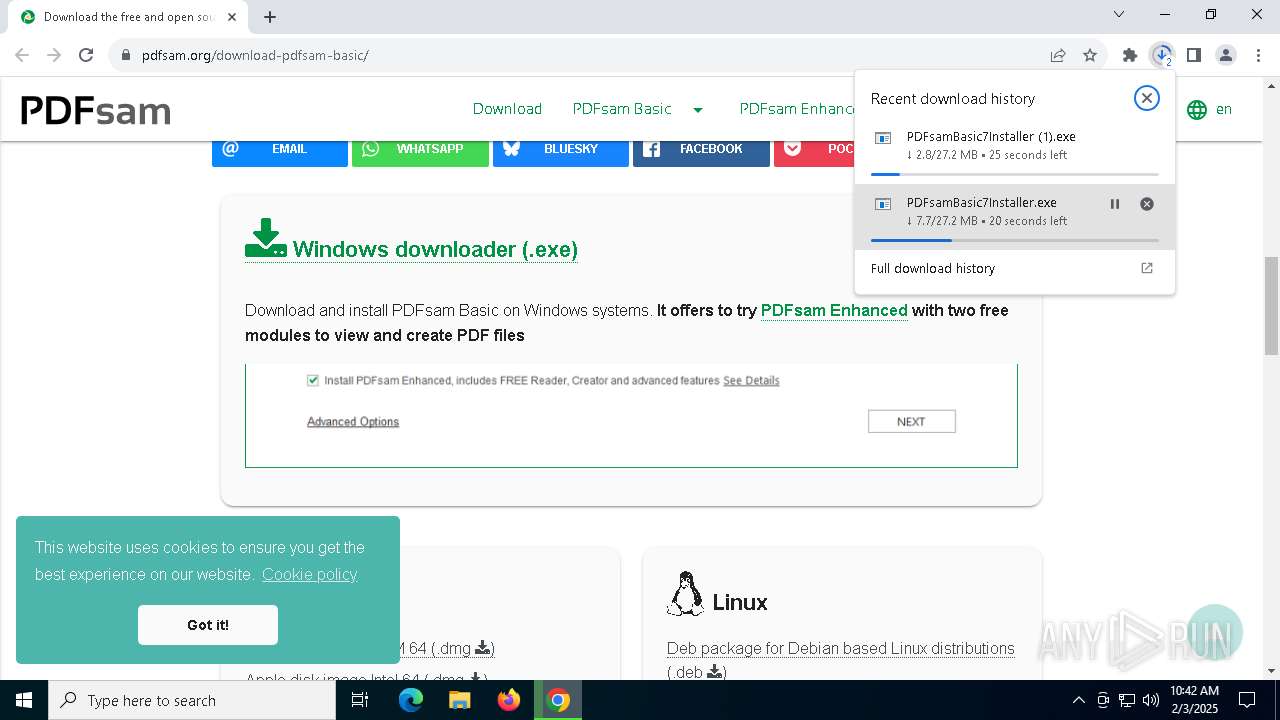
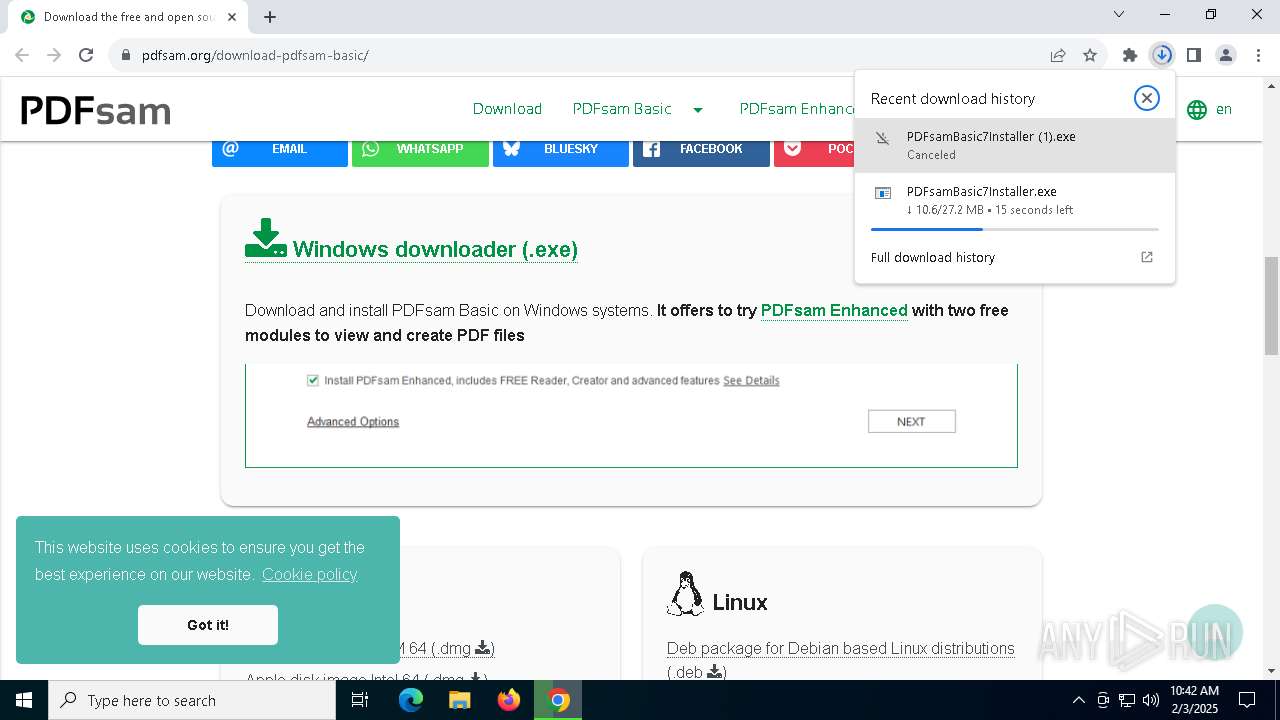
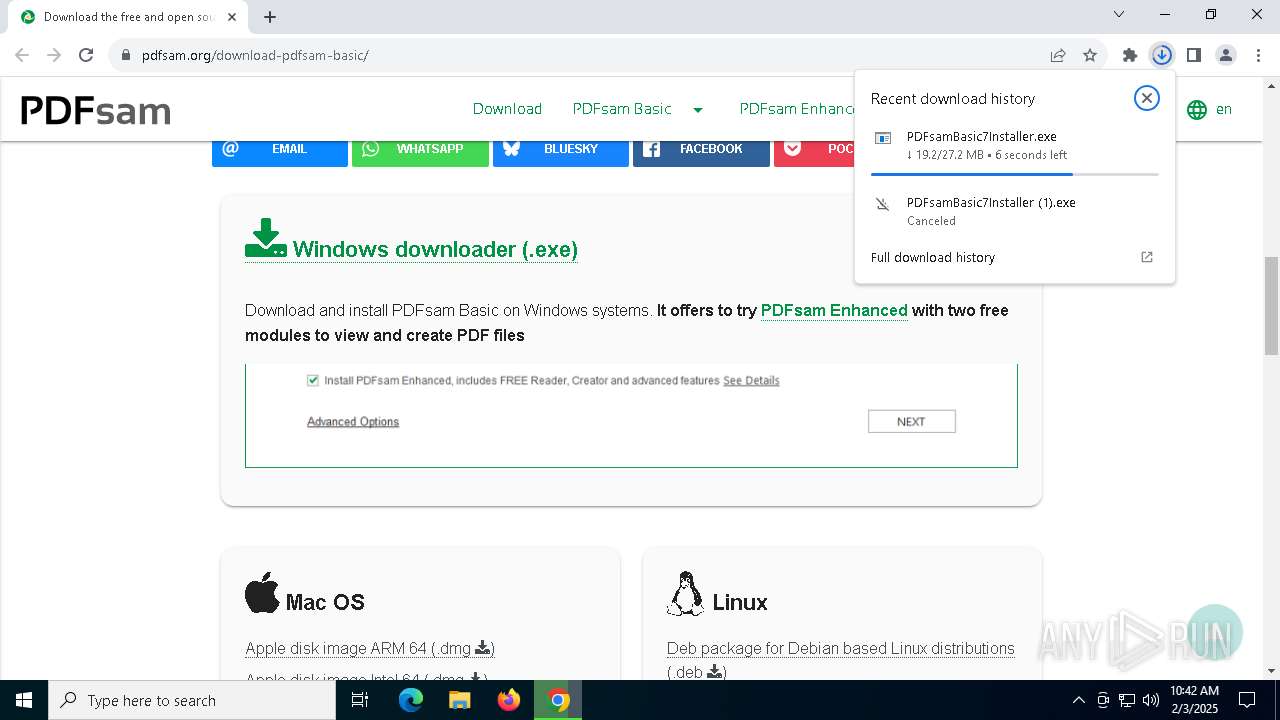
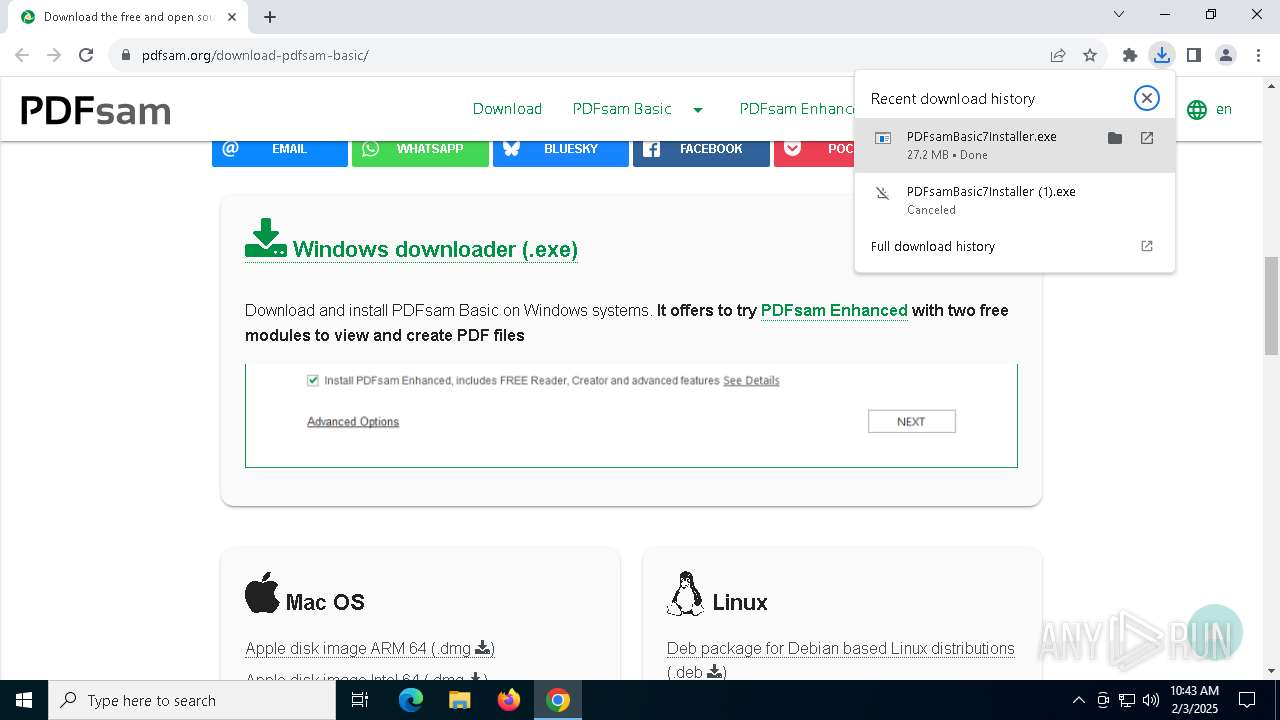
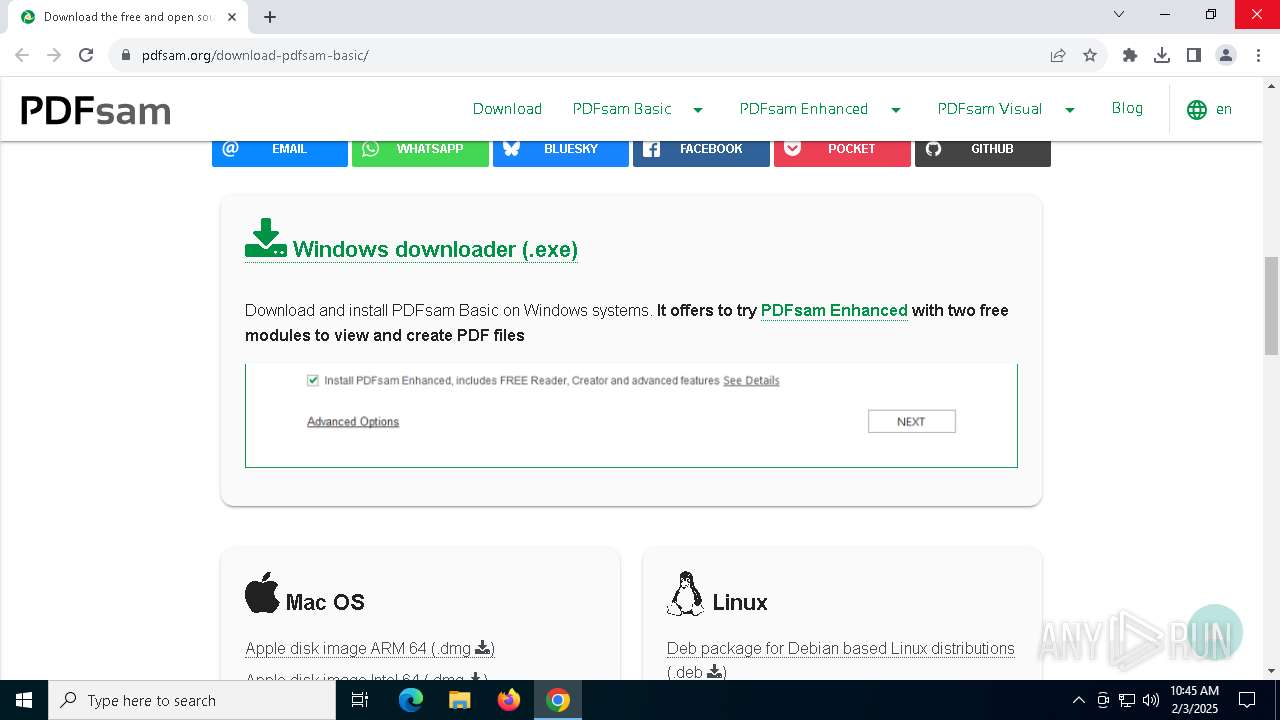
| URL: | https://pdfsam.org/download-pdfsam-basic/ |
| Full analysis: | https://app.any.run/tasks/e43f3895-c5a5-4a9c-8b01-ccecf1449a49 |
| Verdict: | Malicious activity |
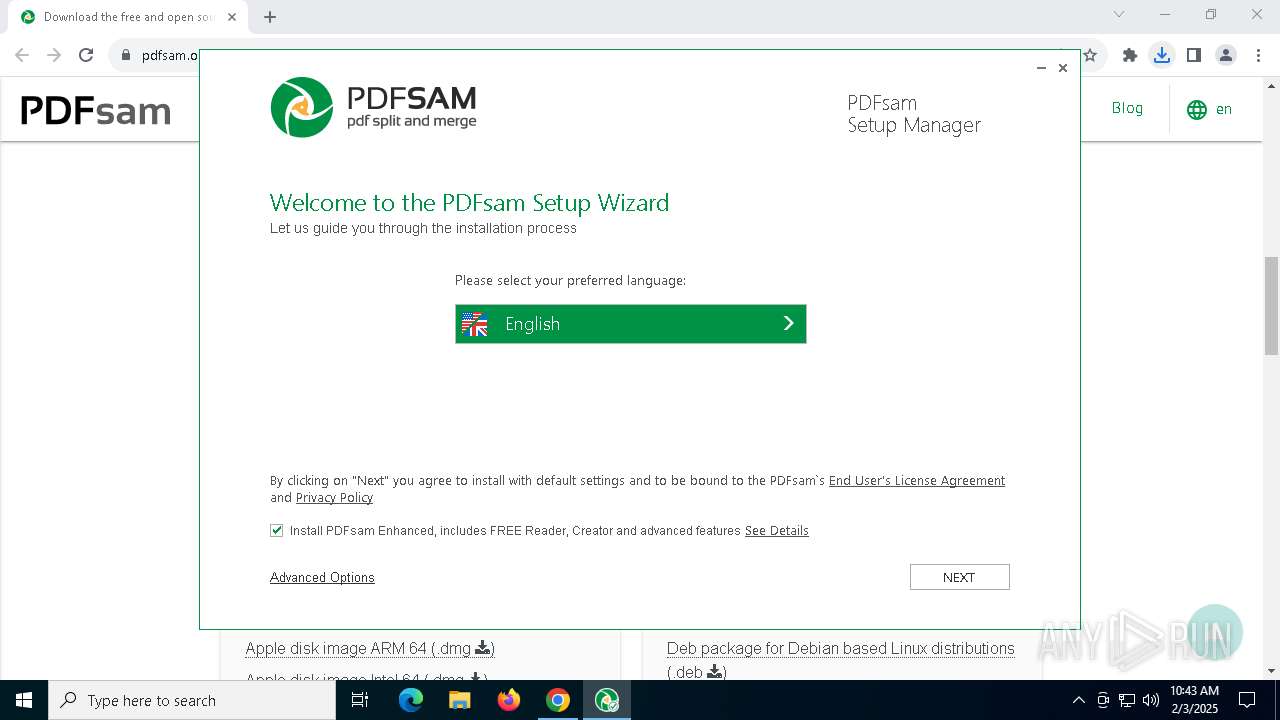
| Analysis date: | February 03, 2025, 10:42:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 528AC2C69D326EBED192731814425634 |
| SHA1: | A661A9EA449B32AD454135BF026B9A8A627AF51B |
| SHA256: | 16F526B64743C6565EA8A22F986A4EA8510DB405B5CF8FF28160A92C4FE63365 |
| SSDEEP: | 3:N8FKE2KCVBNkWMdn:25gNkLdn |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- PDFsamBasic7Installer.exe (PID: 2804)
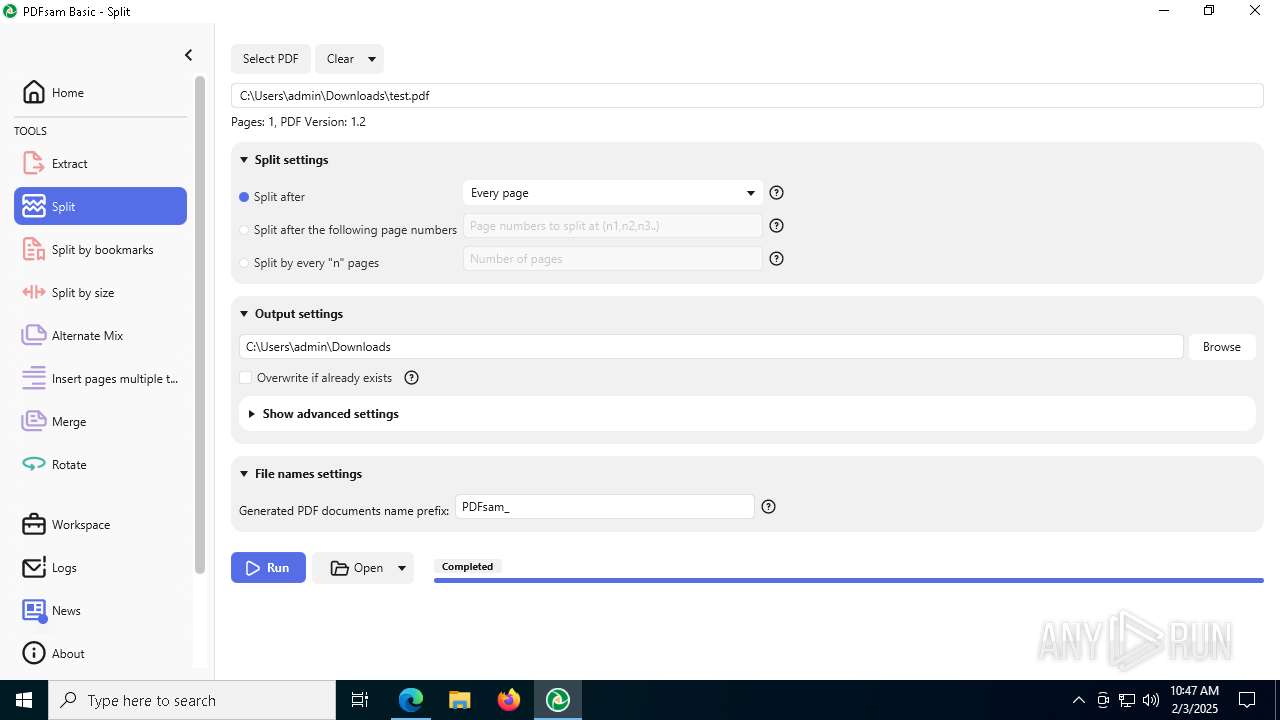
Executing a file with an untrusted certificate
- pdfsam.exe (PID: 1512)
- pdfsam.exe (PID: 4704)
SUSPICIOUS
Executable content was dropped or overwritten
- PDFsamBasic7Installer.exe (PID: 2804)
- rundll32.exe (PID: 8188)
- pdfsam.exe (PID: 4704)
Reads security settings of Internet Explorer
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 5836)
- pdfsam.exe (PID: 4704)
Checks Windows Trust Settings
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2548)
Adds/modifies Windows certificates
- PDFsamBasic7Installer.exe (PID: 2804)
Executes as Windows Service
- VSSVC.exe (PID: 6336)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1572)
Process drops legitimate windows executable
- msiexec.exe (PID: 1572)
- pdfsam.exe (PID: 4704)
The process drops C-runtime libraries
- msiexec.exe (PID: 1572)
- pdfsam.exe (PID: 4704)
Application launched itself
- pdfsam.exe (PID: 1512)
Checks for Java to be installed
- pdfsam.exe (PID: 4704)
INFO
Application launched itself
- chrome.exe (PID: 6412)
- msedge.exe (PID: 4980)
- msedge.exe (PID: 3828)
- msedge.exe (PID: 7624)
Creates files in the program directory
- PDFsamBasic7Installer.exe (PID: 2804)
- dllhost.exe (PID: 5588)
Reads Microsoft Office registry keys
- PDFsamBasic7Installer.exe (PID: 2804)
The sample compiled with english language support
- chrome.exe (PID: 6412)
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
- pdfsam.exe (PID: 4704)
- msedge.exe (PID: 1488)
Reads the computer name
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
- msiexec.exe (PID: 5836)
- identity_helper.exe (PID: 7272)
- msiexec.exe (PID: 8108)
- ShellExperienceHost.exe (PID: 396)
Checks supported languages
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
- msiexec.exe (PID: 5836)
- identity_helper.exe (PID: 5488)
- pdfsam.exe (PID: 1512)
- msiexec.exe (PID: 8108)
- identity_helper.exe (PID: 7272)
- pdfsam.exe (PID: 4704)
- ShellExperienceHost.exe (PID: 396)
Executable content was dropped or overwritten
- chrome.exe (PID: 6412)
- msiexec.exe (PID: 1572)
- msedge.exe (PID: 1488)
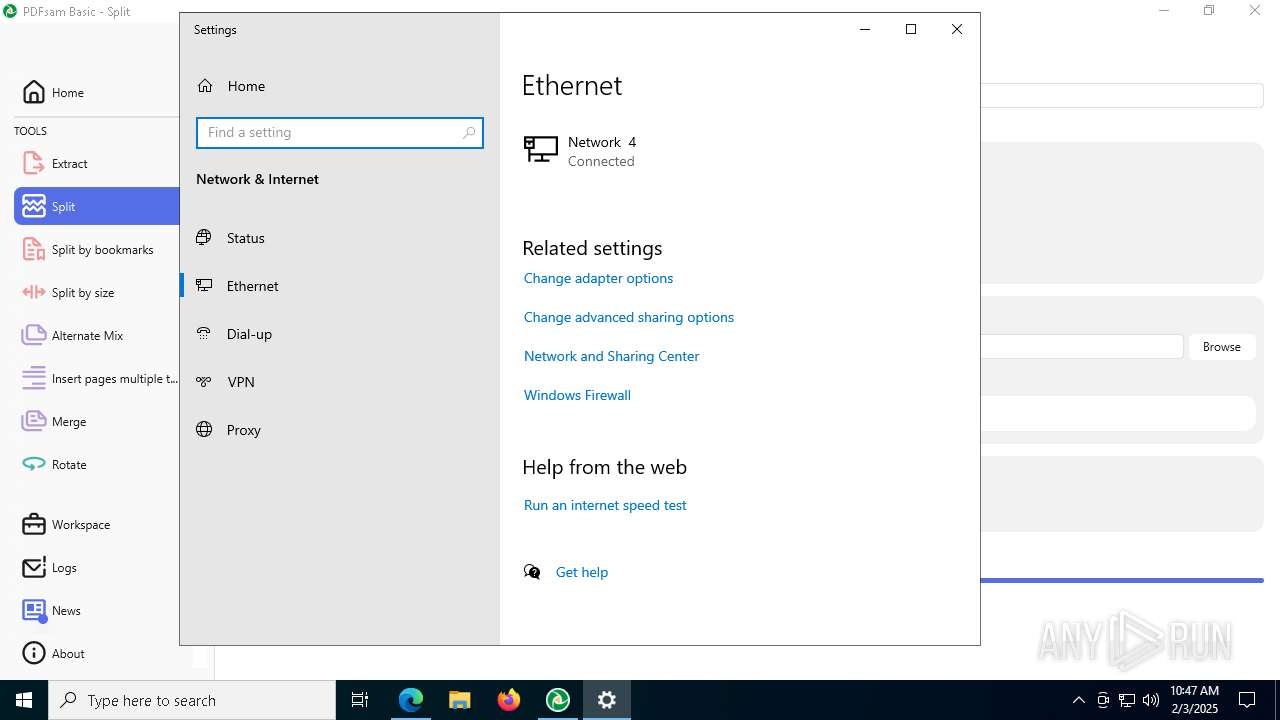
Checks proxy server information
- PDFsamBasic7Installer.exe (PID: 2804)
- dllhost.exe (PID: 5588)
Creates files or folders in the user directory
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
Reads the machine GUID from the registry
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
- pdfsam.exe (PID: 4704)
Reads the software policy settings
- PDFsamBasic7Installer.exe (PID: 2804)
- msiexec.exe (PID: 1572)
- dllhost.exe (PID: 5588)
Manages system restore points
- SrTasks.exe (PID: 1488)
Manual execution by a user
- msedge.exe (PID: 3828)
- pdfsam.exe (PID: 1512)
- msedge.exe (PID: 524)
Creates a software uninstall entry
- msiexec.exe (PID: 1572)
Reads Environment values
- identity_helper.exe (PID: 7272)
- pdfsam.exe (PID: 4704)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 5588)
Local mutex for internet shortcut management
- msiexec.exe (PID: 8108)
Reads CPU info
- pdfsam.exe (PID: 4704)
Create files in a temporary directory
- pdfsam.exe (PID: 4704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
259
Monitored processes
114
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1696 --field-trial-handle=2256,i,12540996630321417703,13369495737956936022,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 396 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2344 --field-trial-handle=2348,i,3355182780602963134,10876550021139684286,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3372 --field-trial-handle=2256,i,12540996630321417703,13369495737956936022,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ff820a55fd8,0x7ff820a55fe4,0x7ff820a55ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=4860 --field-trial-handle=1924,i,4770219596308118476,7158301673302326332,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4908 --field-trial-handle=2256,i,12540996630321417703,13369495737956936022,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 1304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=6496 --field-trial-handle=2256,i,12540996630321417703,13369495737956936022,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=7928 --field-trial-handle=2256,i,12540996630321417703,13369495737956936022,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
Total events
52 507
Read events
51 223
Write events
1 177
Delete events
107
Modification events
| (PID) Process: | (6412) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6412) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6412) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6412) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6412) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000004DD9CD672876DB01 | |||
| (PID) Process: | (2804) PDFsamBasic7Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\PDFsam Enhanced 7\Installation |
| Operation: | write | Name: | INSTALL_FOLDER |
Value: C:\Program Files\PDFsam Enhanced 7 | |||
| (PID) Process: | (2548) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A869D8E5-32F1-4706-96DB-C05D95FD4A5B}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (2548) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A869D8E5-32F1-4706-96DB-C05D95FD4A5B} |
| Operation: | write | Name: | AppID |
Value: {77EC23C5-BB68-4A7B-AE5C-F4AD0B6C678D} | |||
| (PID) Process: | (2548) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{5887D2B7-4C1D-41FA-889A-0179A2B37687}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
239
Suspicious files
808
Text files
271
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 6412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF137fe1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
246
DNS requests
270
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5988 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5988 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3820 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3820 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6584 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2804 | PDFsamBasic7Installer.exe | GET | 200 | 23.38.74.33:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCEE5A5DdU7eaMAAAAAFHTlH8%3D | unknown | — | — | whitelisted |
2804 | PDFsamBasic7Installer.exe | GET | 200 | 23.38.74.33:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRr2bwARTxMtEy9aspRAZg5QFhagQQUgrrWPZfOn89x6JI3r%2F2ztWk1V88CEDWvt3udNB9q%2FI%2BERqsxNSs%3D | unknown | — | — | whitelisted |
2804 | PDFsamBasic7Installer.exe | GET | 200 | 151.101.194.133:80 | http://ocsp.globalsign.com/gsgccr6alphasslca2023/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTYuQbxgZqJCf3D06HBxH57o5XEXgQUvQW384qTPHPLefoPhRKhd5YYkXQCDA3ZJFfaA0%2BWNA8nSA%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1684 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5988 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5988 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5988 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.19.80.121:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
pdfsam.org |
| unknown |
accounts.google.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2632 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2632 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |