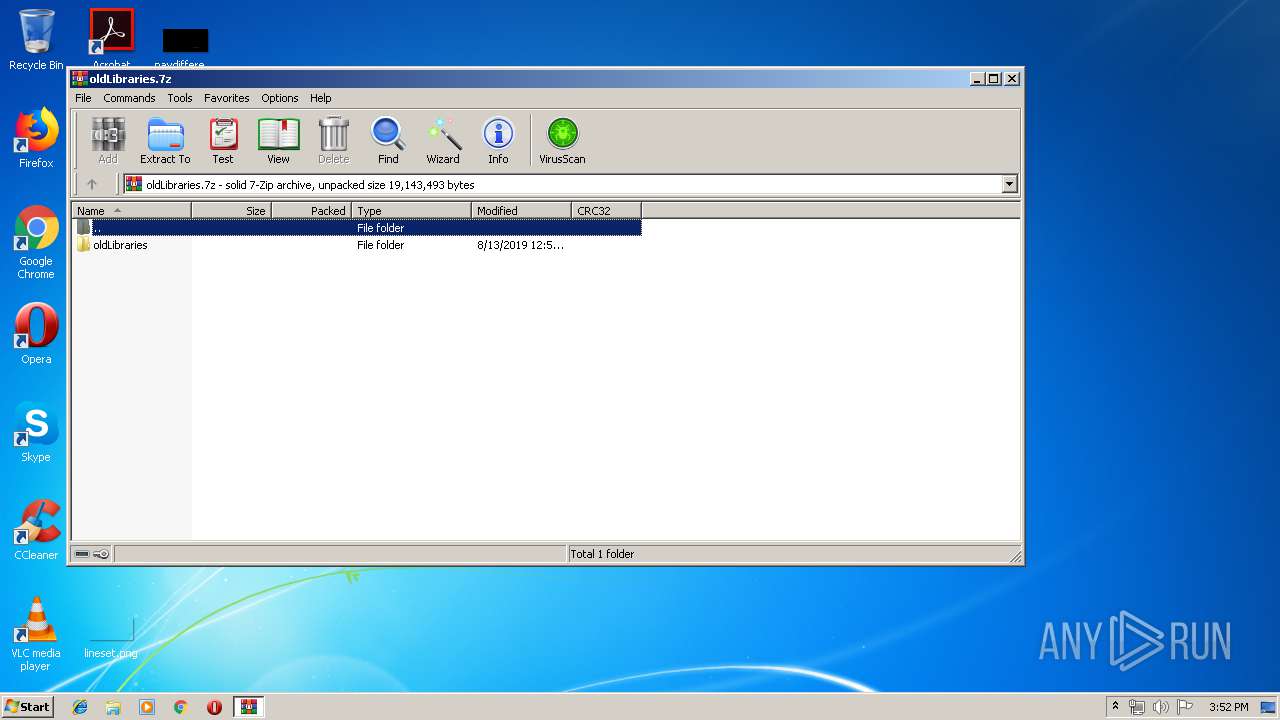
| File name: | oldLibraries.7z |
| Full analysis: | https://app.any.run/tasks/6c760f80-2827-4db4-9445-44ee473dd905 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 14:52:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
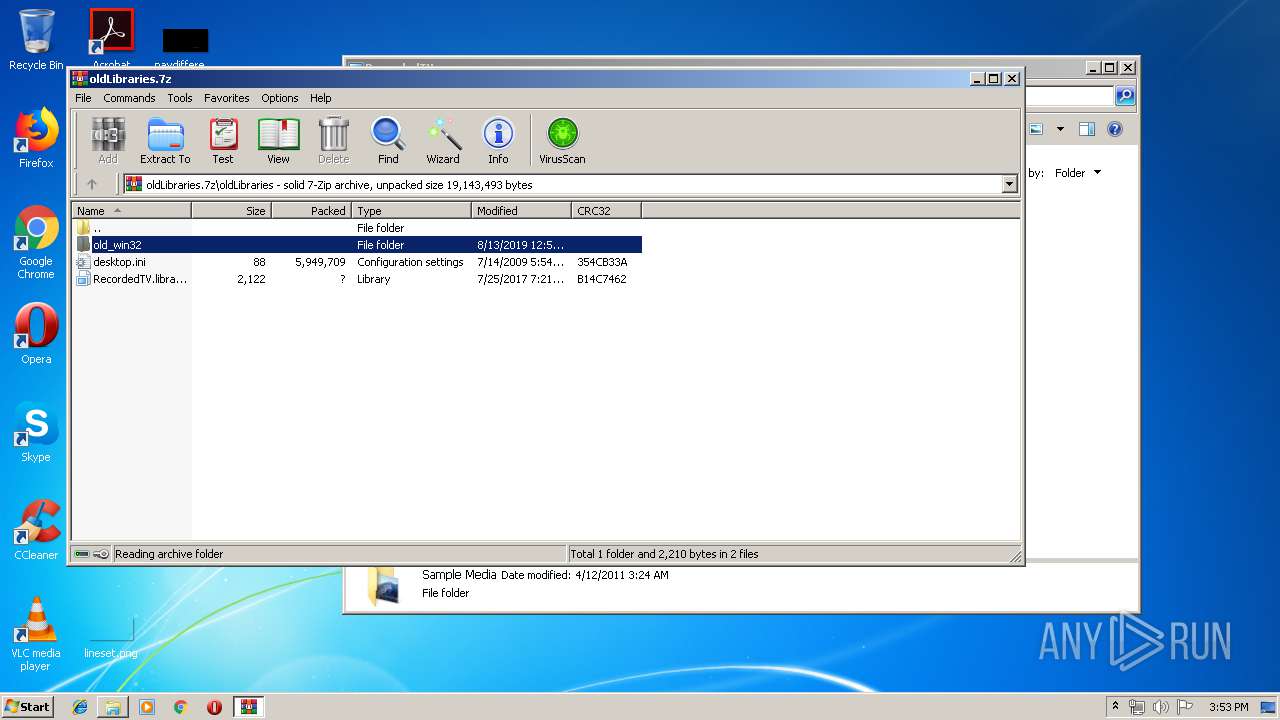
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | C4A2AF8C3DB1521F64803BBF14136067 |
| SHA1: | 6F071F8CB674DFA05C871052A4AADD2DB7D94670 |
| SHA256: | 16F477F460A97C9AE5277675E1753C0024B1F3FA192B1571CA17C41F0FBDCF9B |
| SSDEEP: | 98304:cjS9/xtr9WQfojnv9MnmigoFeXaL1QZHsURVshwwaS+ia5RLddN8Vc4Rpovqxb:cWbtVonvN9axQZnrsy0+7f98Vcb0 |
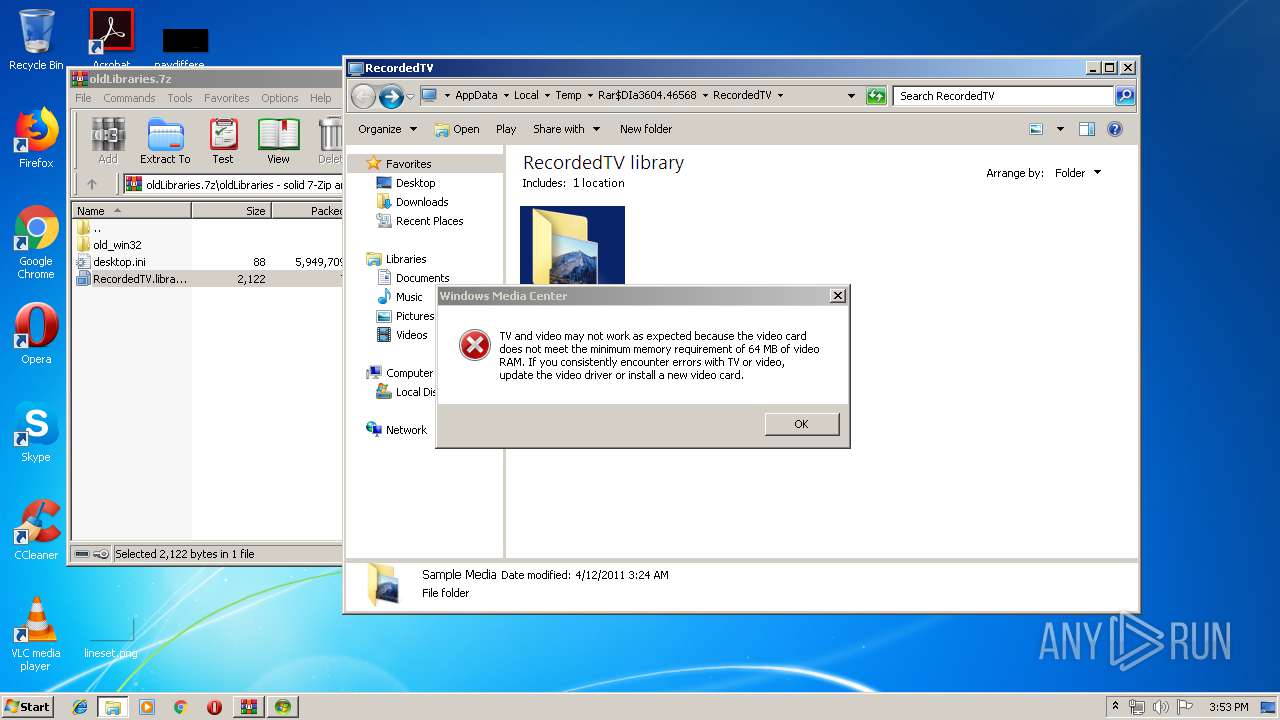
MALICIOUS
Loads the Task Scheduler COM API
- ehshell.exe (PID: 3812)
- ehRec.exe (PID: 456)
SUSPICIOUS
Creates files in the program directory
- ehshell.exe (PID: 3812)
Creates files in the user directory
- ehshell.exe (PID: 3812)
- EhTray.exe (PID: 2140)
Executed via COM
- ehRec.exe (PID: 456)
Creates files in the Windows directory
- ehRec.exe (PID: 456)
Executed as Windows Service
- ehsched.exe (PID: 2708)
Application launched itself
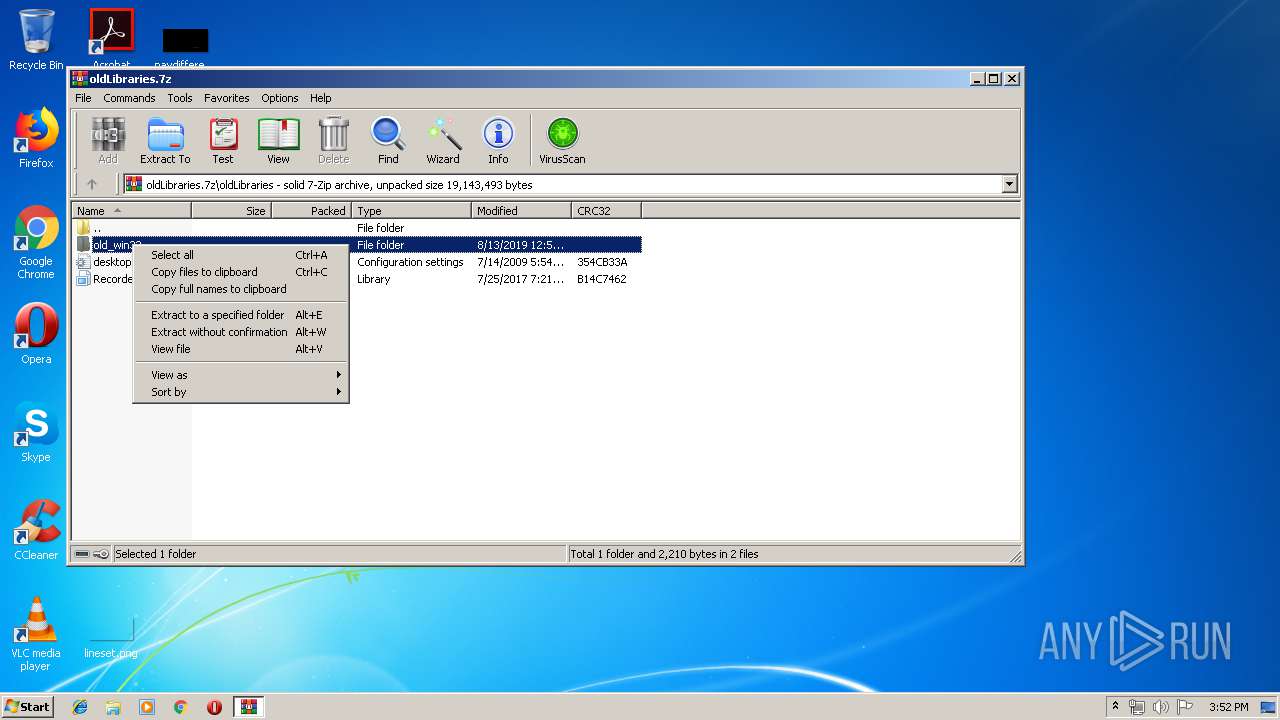
- WinRAR.exe (PID: 3604)
INFO
Manual execution by user
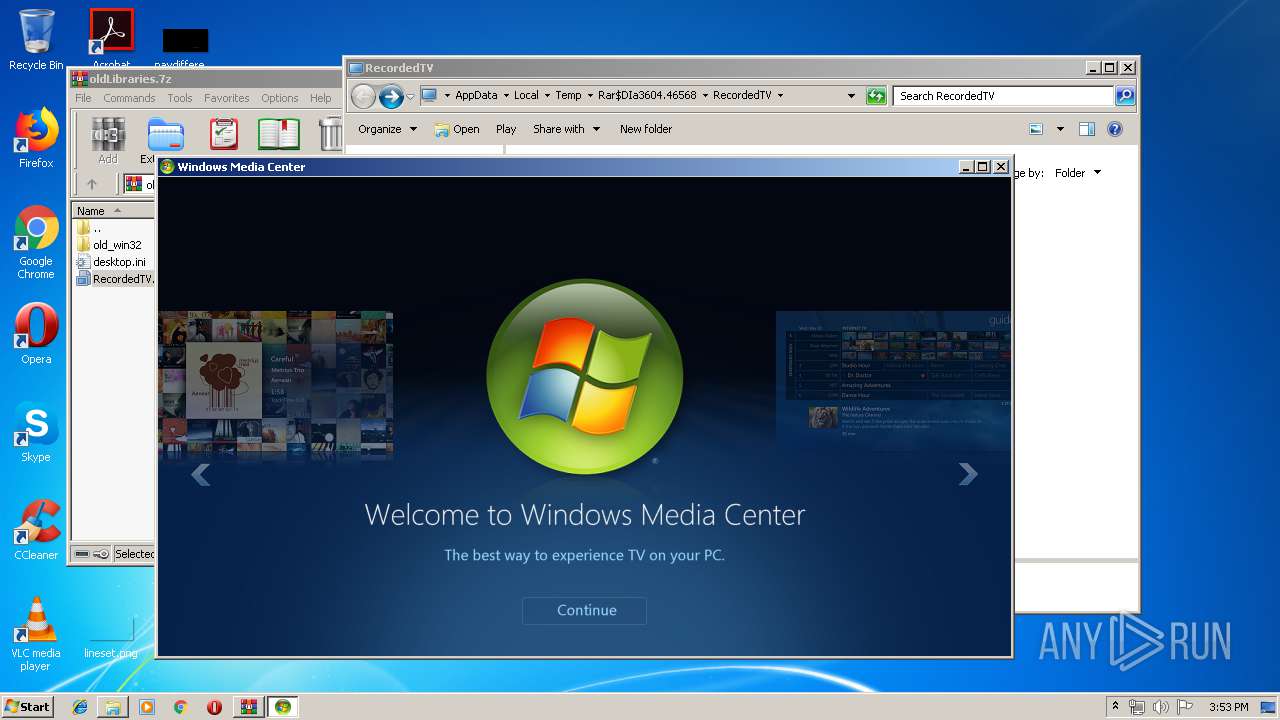
- EhTray.exe (PID: 2140)
- ehshell.exe (PID: 3812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
41
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\Windows\ehome\ehRec.exe -Embedding | C:\Windows\ehome\ehRec.exe | — | svchost.exe | |||||||||||
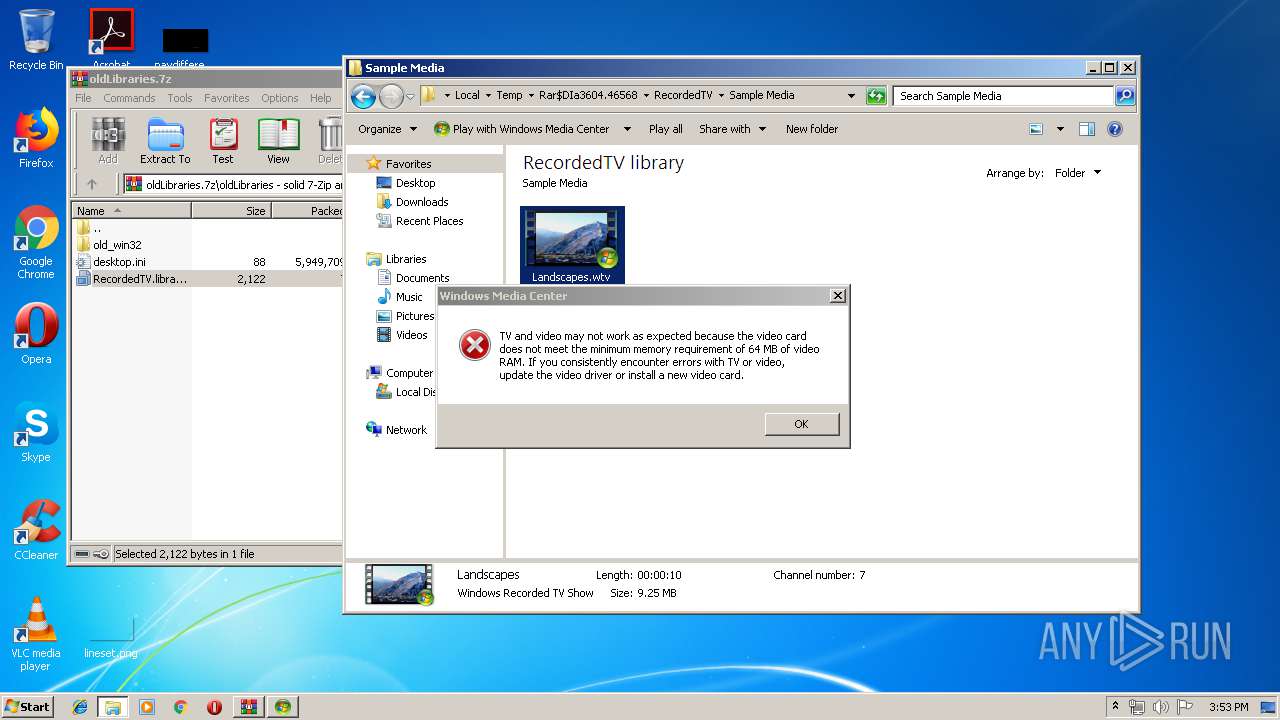
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Media Center Host Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Windows\eHome\EhTray.exe" /nav:-2 | C:\Windows\eHome\EhTray.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Center Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
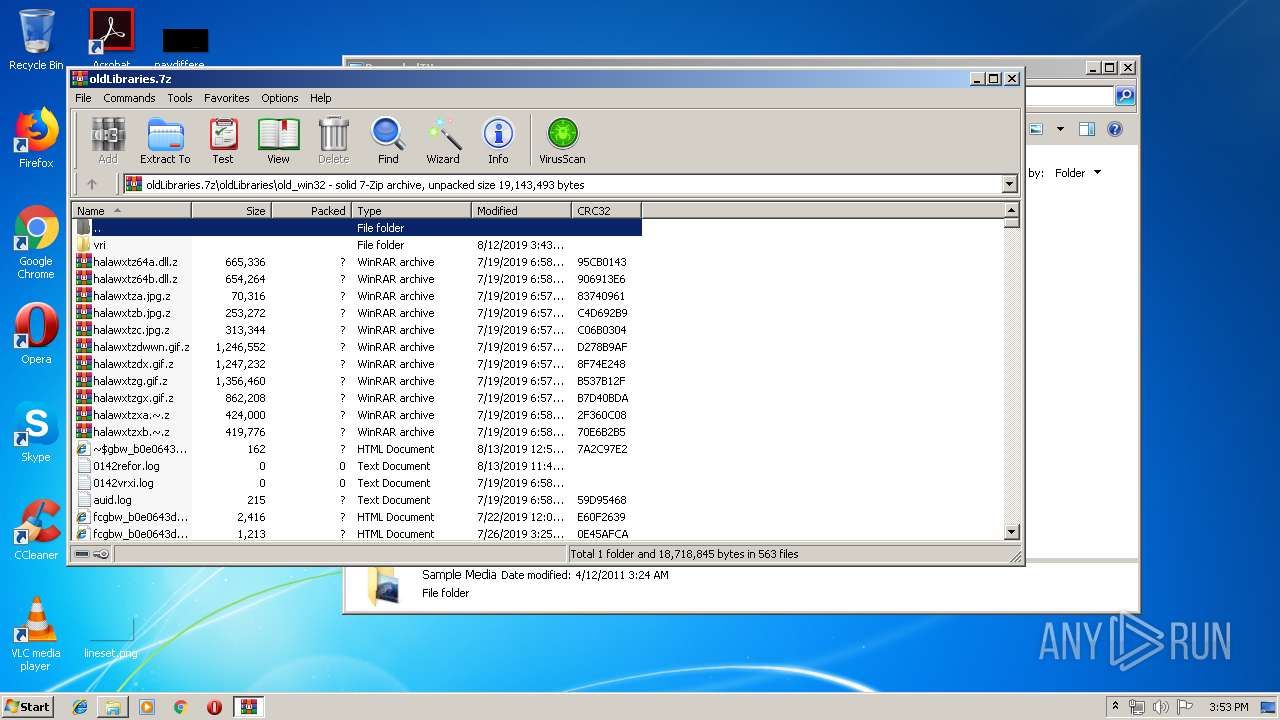
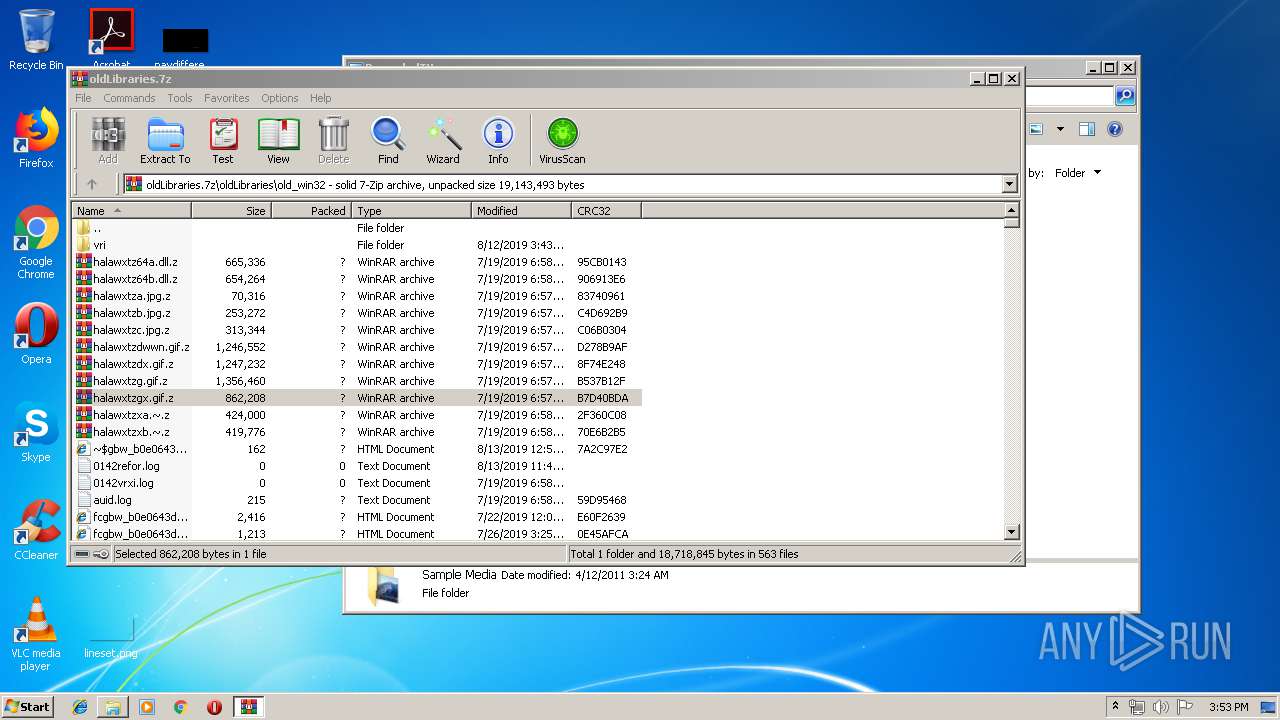
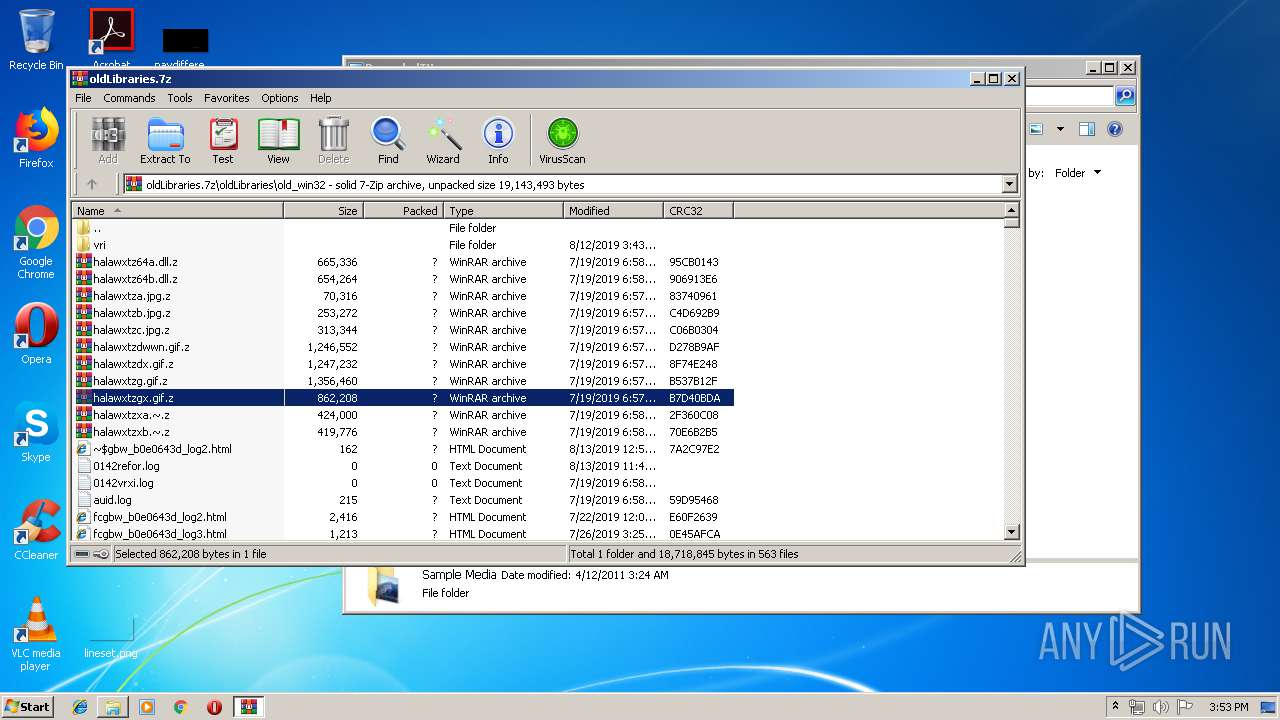
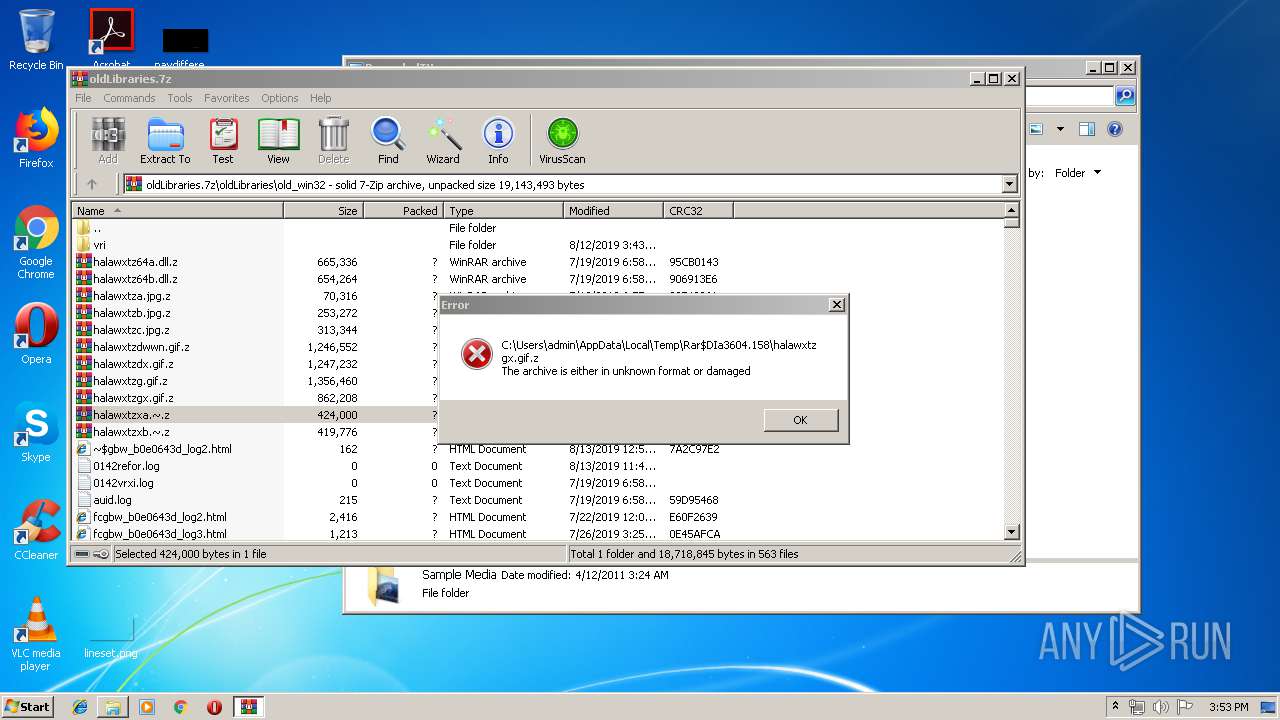
| 2308 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3604.158\halawxtzgx.gif.z" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2708 | C:\Windows\ehome\ehsched.exe | C:\Windows\ehome\ehsched.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Media Center Scheduler Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
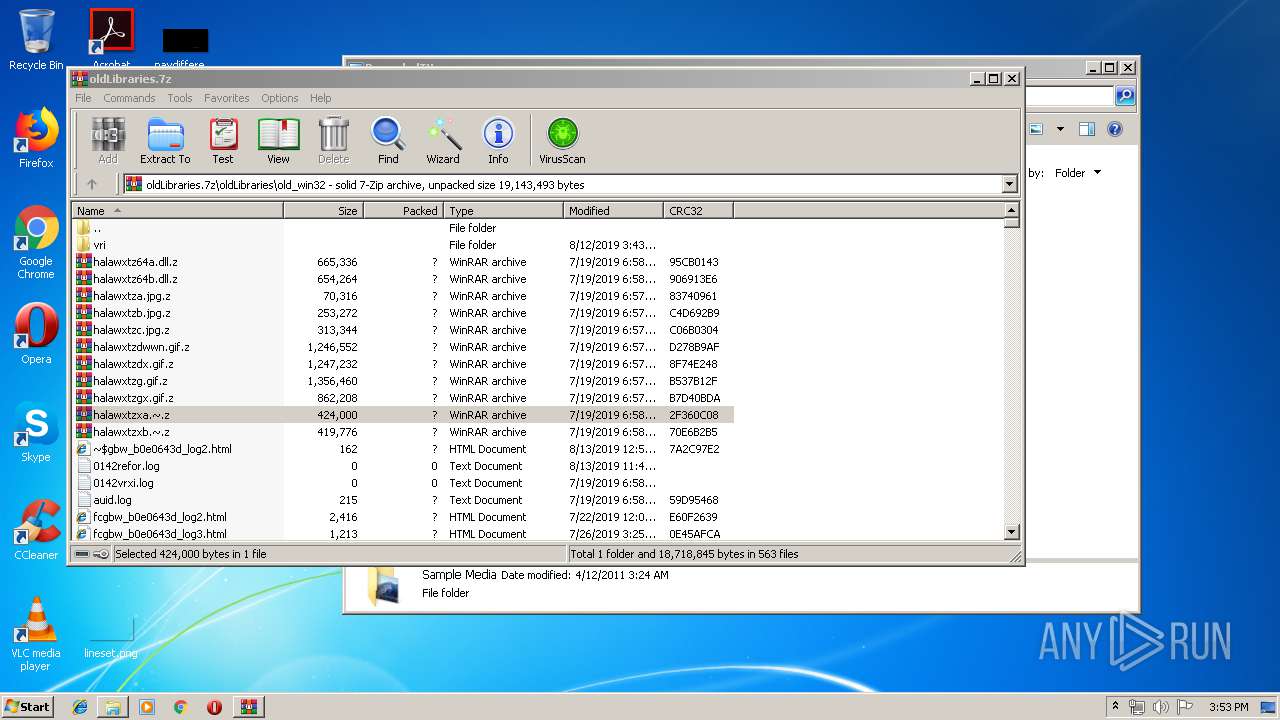
| 3028 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3604.741\halawxtzxa.~.z" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | |||||||||||||||
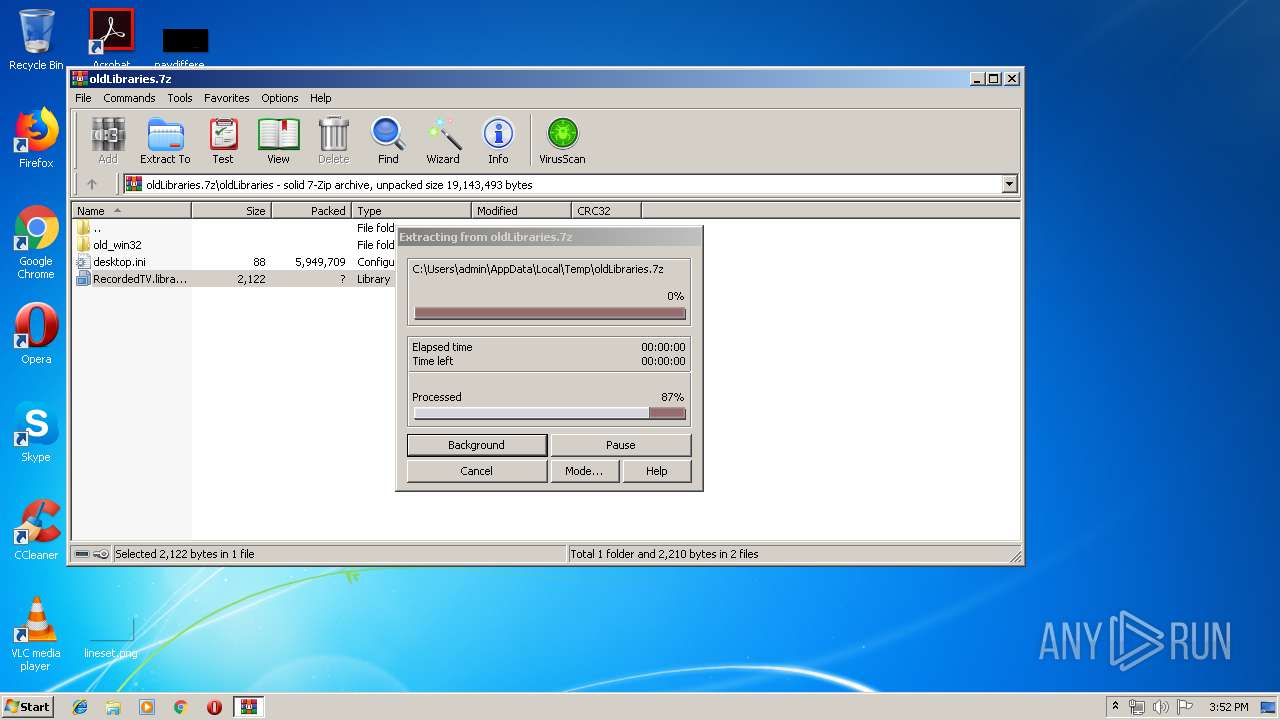
| 3604 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\oldLibraries.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
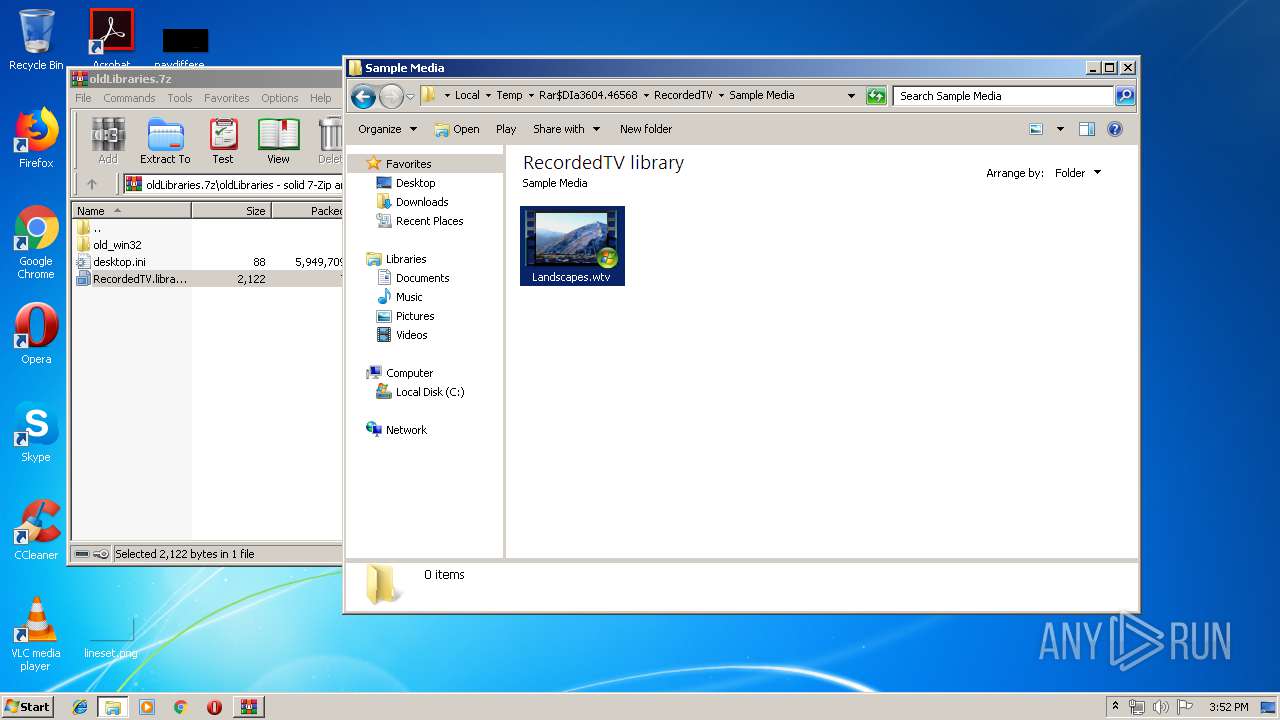
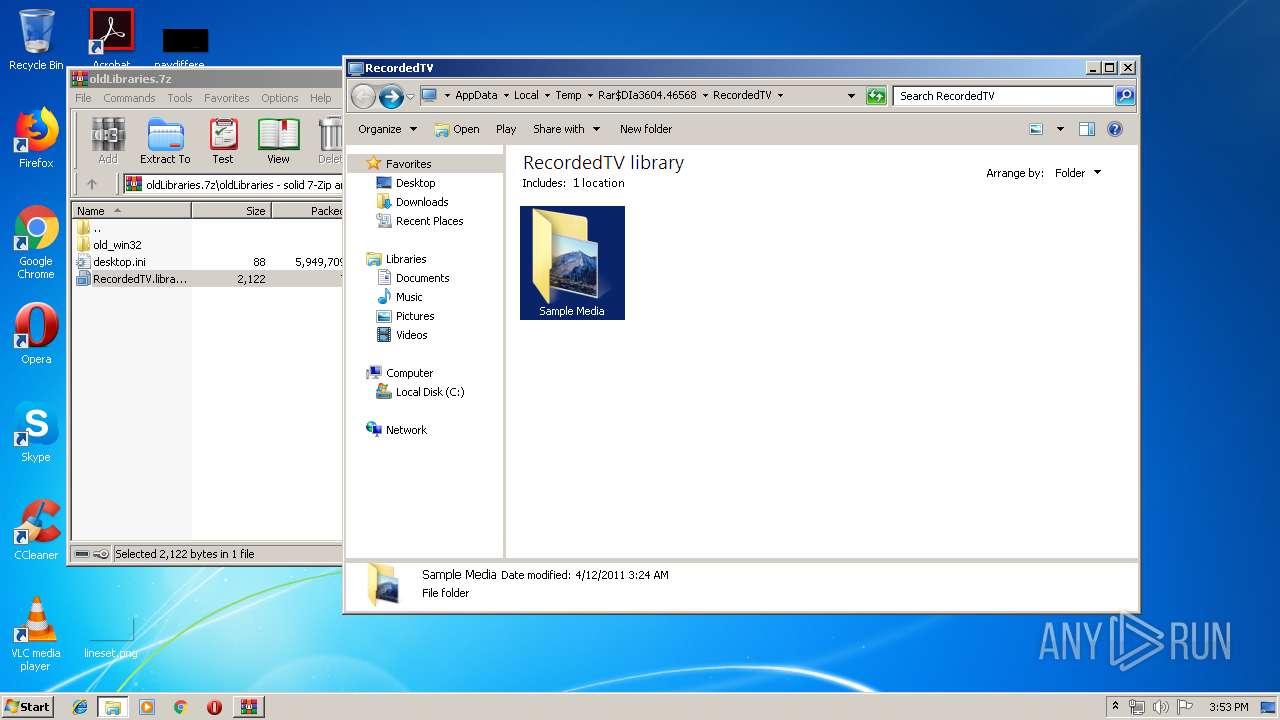
| 3812 | "C:\Windows\eHome\ehshell.exe" /prefetch:1003 "C:\Users\Public\Recorded TV\Sample Media\win7_scenic-demoshort_raw.wtv" | C:\Windows\eHome\ehshell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Center Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 767
Read events
1 484
Write events
283
Delete events
0
Modification events
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\oldLibraries.7z | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3812) ehshell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: ehshell.exe | |||
| (PID) Process: | (3812) ehshell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Media Center\Service\EPG |
| Operation: | write | Name: | clientid |
Value: b4869c9fb4fe4f4fa3fcca8114748039 | |||
Executable files
0
Suspicious files
5
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | EhTray.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JJ46JZKH67CZJ7HYV8N8.temp | — | |
MD5:— | SHA256:— | |||
| 2140 | EhTray.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WZ1Z8MVI3YU5KZKLR5ZN.temp | — | |
MD5:— | SHA256:— | |||
| 3812 | ehshell.exe | C:\ProgramData\Microsoft\eHome\logs\FirstRun.log | xml | |
MD5:— | SHA256:— | |||
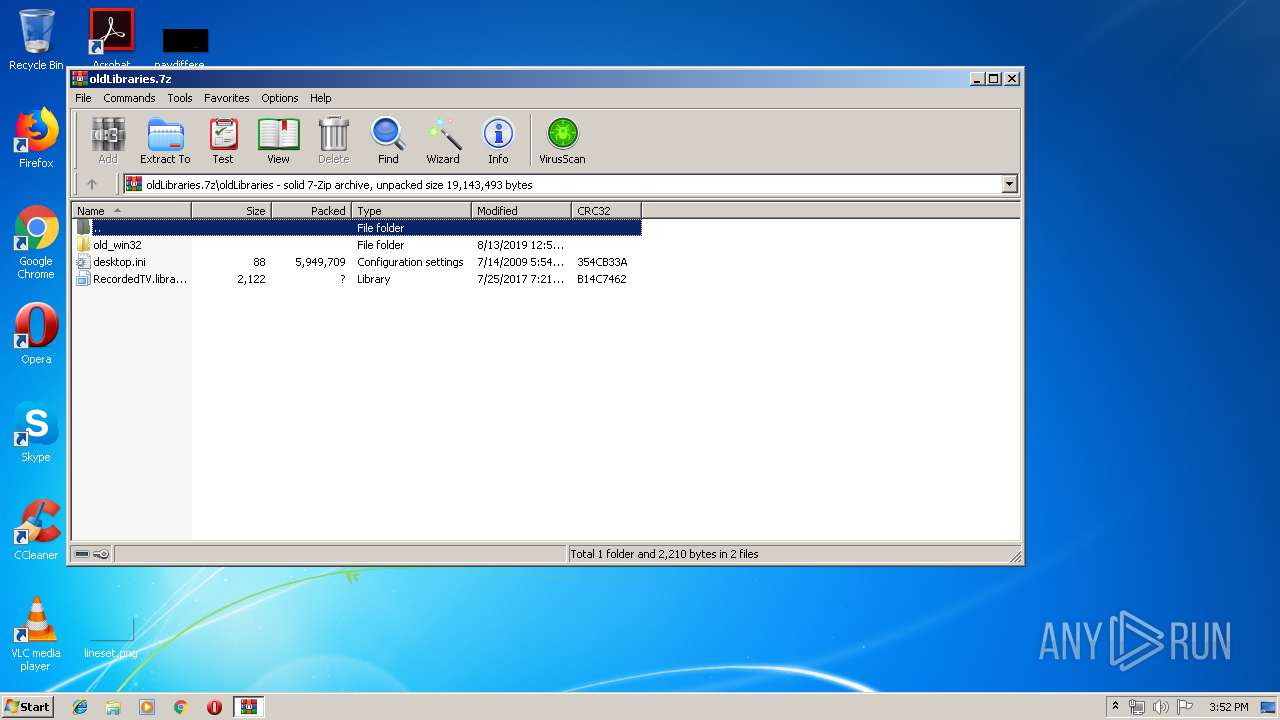
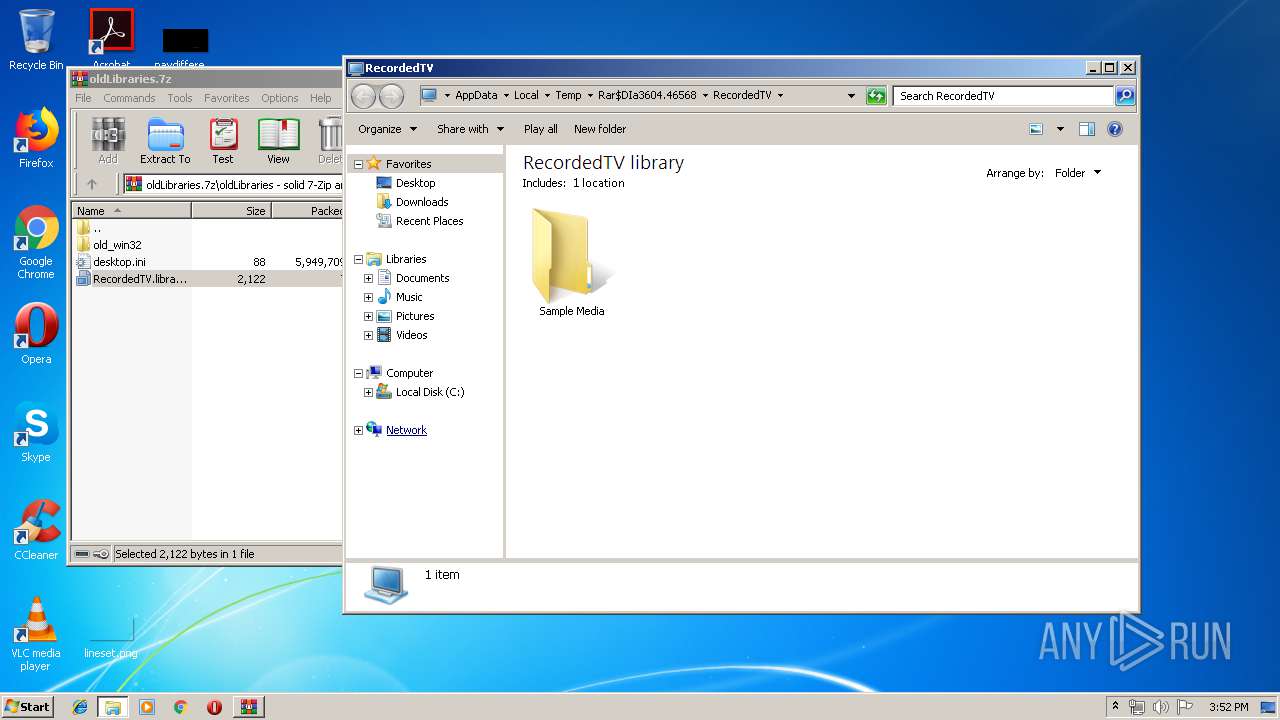
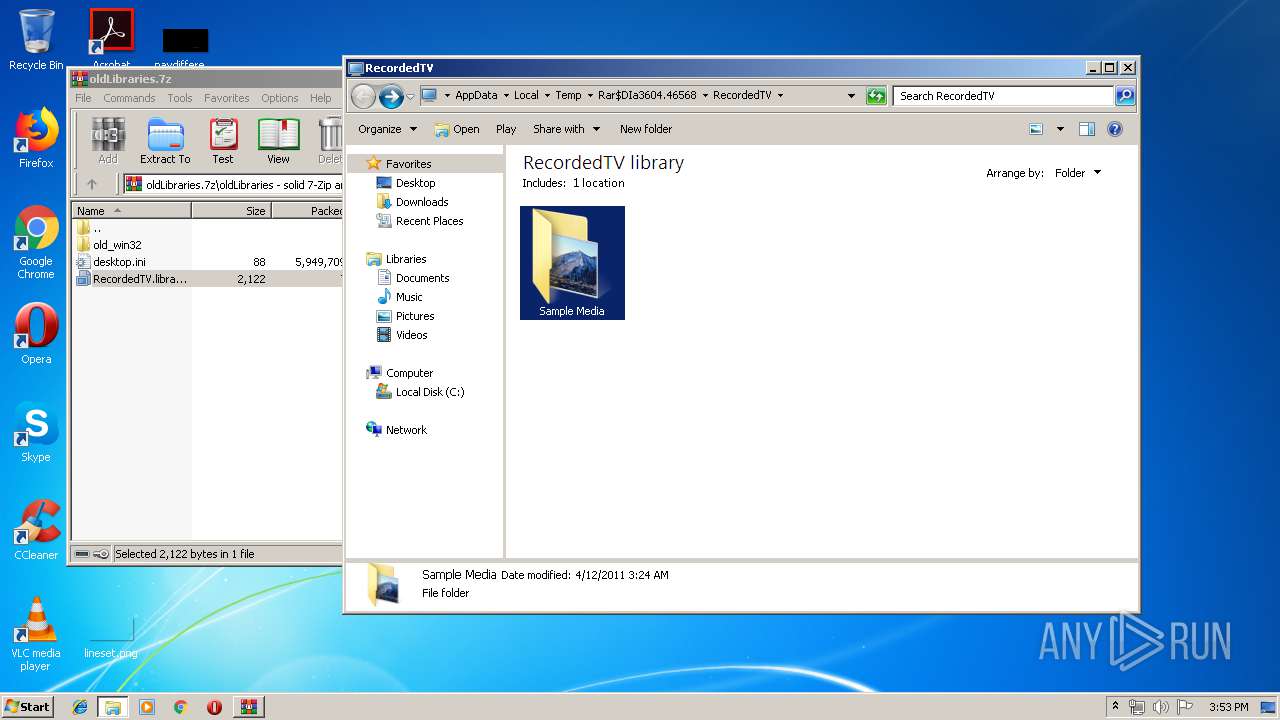
| 3604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3604.46568\RecordedTV.library-ms | xml | |
MD5:— | SHA256:— | |||
| 456 | ehRec.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-20\8f96978fc46d9f00d8780351026924d7_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:DB733E033C397FEC5917611957620271 | SHA256:1F3FFADD3B80C7F95BE06E245410768E8302A24E573868DA3C6FD91230025BDC | |||
| 2140 | EhTray.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b91050d8b077a4e8.customDestinations-ms~RF3773dc.TMP | binary | |
MD5:B9BD716DE6739E51C620F2086F9C31E4 | SHA256:7116FF028244A01F3D17F1D3BC2E1506BC9999C2E40E388458F0CCCC4E117312 | |||
| 3604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3604.158\halawxtzgx.gif.z | text | |
MD5:— | SHA256:— | |||
| 3812 | ehshell.exe | C:\programdata\microsoft\ehome\mcepg2-0.db | binary | |
MD5:— | SHA256:— | |||
| 456 | ehRec.exe | C:\ProgramData\Microsoft\eHome\mcepg2-0.db | binary | |
MD5:— | SHA256:— | |||
| 3604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3604.741\halawxtzxa.~.z | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
ehshell.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ehshell.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ehshell.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ehshell.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ehshell.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|