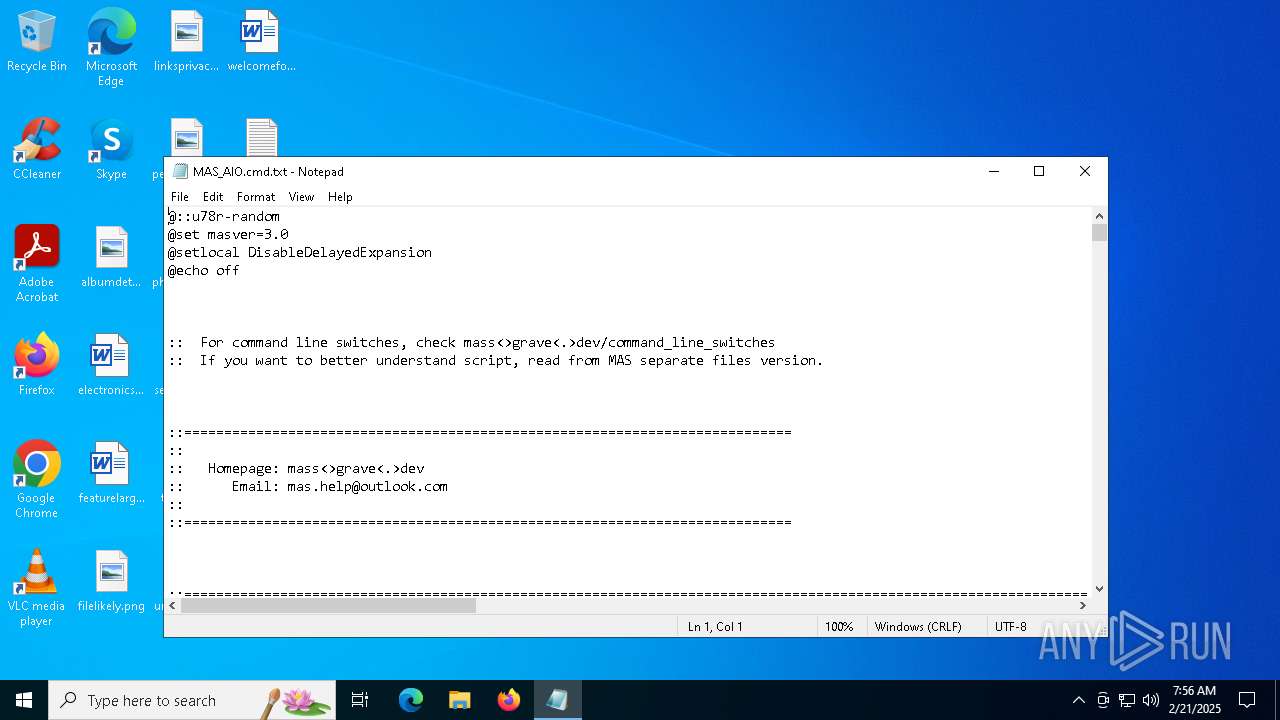
| File name: | MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/3ae30c84-813d-4b1b-ad7c-a3a3c8a93ea1 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2025, 07:56:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (348), with CRLF line terminators |
| MD5: | 5B9A3CF1F44FACE6C7BA60B2F729A2D3 |
| SHA1: | 253041DFB0D8F58E0A2D9480C69830CB0484B86E |
| SHA256: | 16F0FFCDD242A0D514B9D96AE1535F48A2E2811D45A8094E98BB0A26EA2FEBBA |
| SSDEEP: | 6144:5oIjH+imAc5g+9YCMD0a9g7nc/4IsK0ykpBwuI:5oIjHOAWYCMDF0c/psK0ykpBm |
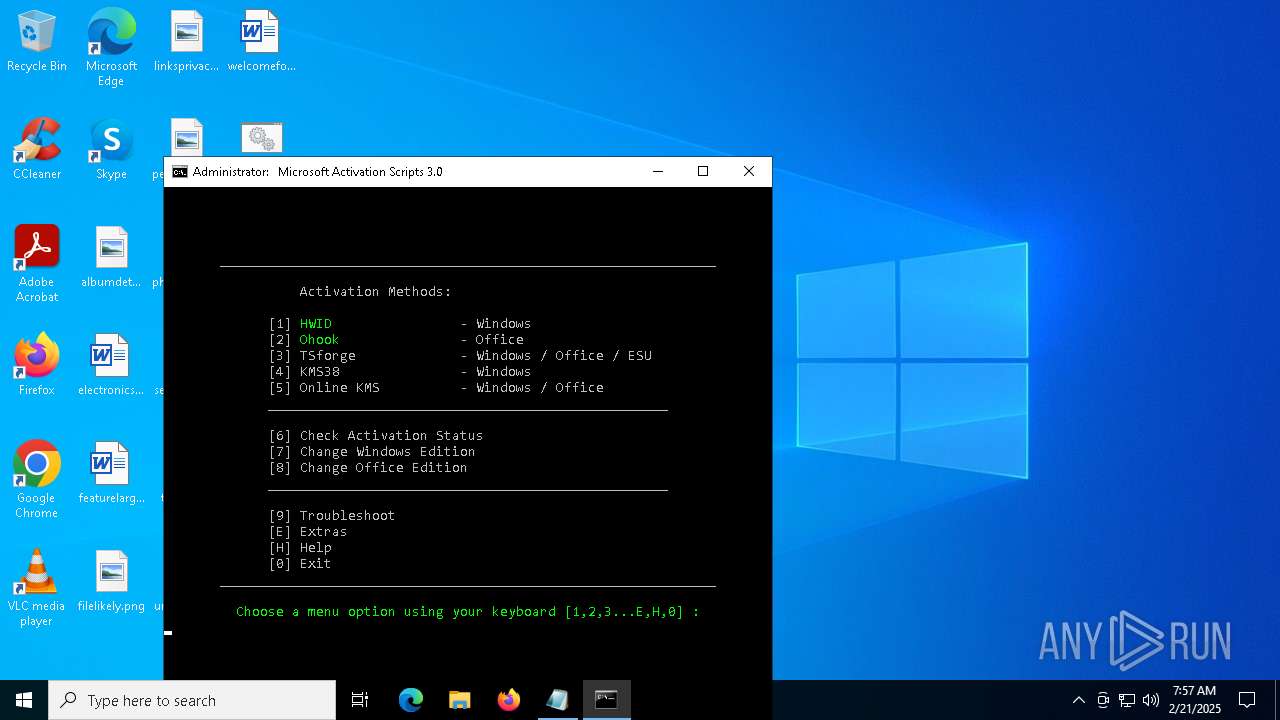
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 7120)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 4996)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7120)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 4996)
Windows service management via SC.EXE
- sc.exe (PID: 5316)
- sc.exe (PID: 6500)
- sc.exe (PID: 5256)
- sc.exe (PID: 5008)
- sc.exe (PID: 2792)
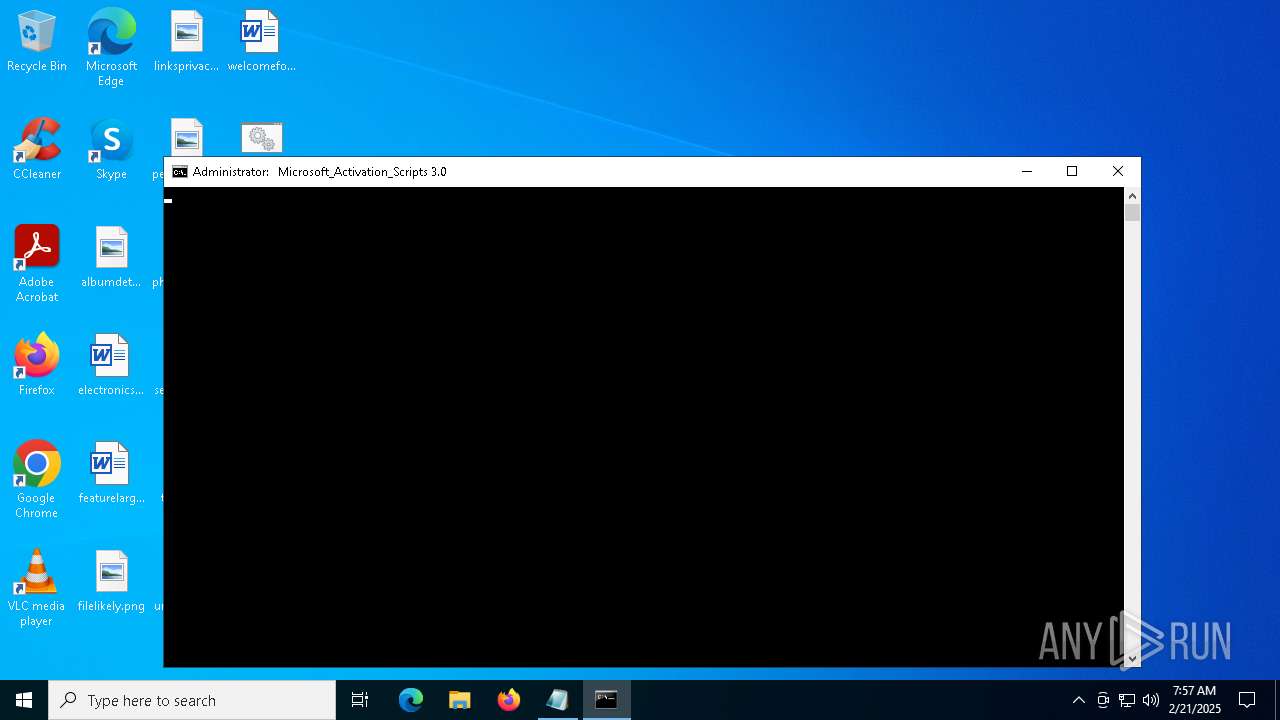
Application launched itself
- cmd.exe (PID: 7120)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 6504)
- powershell.exe (PID: 3052)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7120)
- cmd.exe (PID: 5740)
- powershell.exe (PID: 6452)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 6960)
- powershell.exe (PID: 3420)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 6504)
Executing commands from ".cmd" file
- cmd.exe (PID: 7120)
- cmd.exe (PID: 1864)
- powershell.exe (PID: 6452)
- powershell.exe (PID: 3420)
- cmd.exe (PID: 4996)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4388)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 4996)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4388)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 4996)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4388)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 904)
- cmd.exe (PID: 6496)
- powershell.exe (PID: 3052)
- cmd.exe (PID: 7108)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 68)
Hides command output
- cmd.exe (PID: 68)
- cmd.exe (PID: 6504)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4996)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4264)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3052)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4996)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 3052)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6420)
- notepad.exe (PID: 6220)
- WMIC.exe (PID: 6364)
- WMIC.exe (PID: 4468)
- WMIC.exe (PID: 5604)
Manual execution by a user
- notepad.exe (PID: 6420)
- cmd.exe (PID: 7120)
Checks operating system version
- cmd.exe (PID: 7120)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 4996)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 5392)
Starts MODE.COM to configure console settings
- mode.com (PID: 4968)
- mode.com (PID: 4864)
Checks supported languages
- mode.com (PID: 4968)
- mode.com (PID: 4864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
241
Monitored processes
112
Malicious processes
5
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 68 | C:\WINDOWS\System32\cmd.exe /c "wmic Path Win32_OperatingSystem Get OperatingSystemSKU /format:LIST" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\Desktop\MAS_AIO.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | C:\WINDOWS\System32\cmd.exe /c ping -4 -n 1 activated.win | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "AMD64 " " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\System32\cmd.exe /c "powershell.exe $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); [void]$TypeBuilder.DefinePInvokeMethod('SLGetWindowsInformationDWORD', 'slc.dll', 'Public, Static', 1, [int], @([String], [int].MakeByRefType()), 1, 3); $Sku = 0; [void]$TypeBuilder.CreateType()::SLGetWindowsInformationDWORD('Kernel-BrandingInfo', [ref]$Sku); $Sku" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | find /i "FullLanguage" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 435
Read events
57 435
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qunrcu0b.ei2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6916 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lprsunbd.fpp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6916 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yqnmwaph.gwj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3420 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qmro2wog.pff.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eko5kvy2.cia.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5556 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_o5q4azcf.rwa.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_e5g2h1oj.rup.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3420 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zfsuw1e5.bml.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5556 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_s5ec5oyl.1jo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4824 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:457B7EE4815078F9C3916A7A5F4DF901 | SHA256:E012D2EF3DFDF200504614D28AF7A79FE56FBF38745F88AFA6B3DD63DC263BB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6572 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.23.227.208:443 | — | Ooredoo Q.S.C. | QA | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | — | Ooredoo Q.S.C. | QA | unknown |
1520 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |