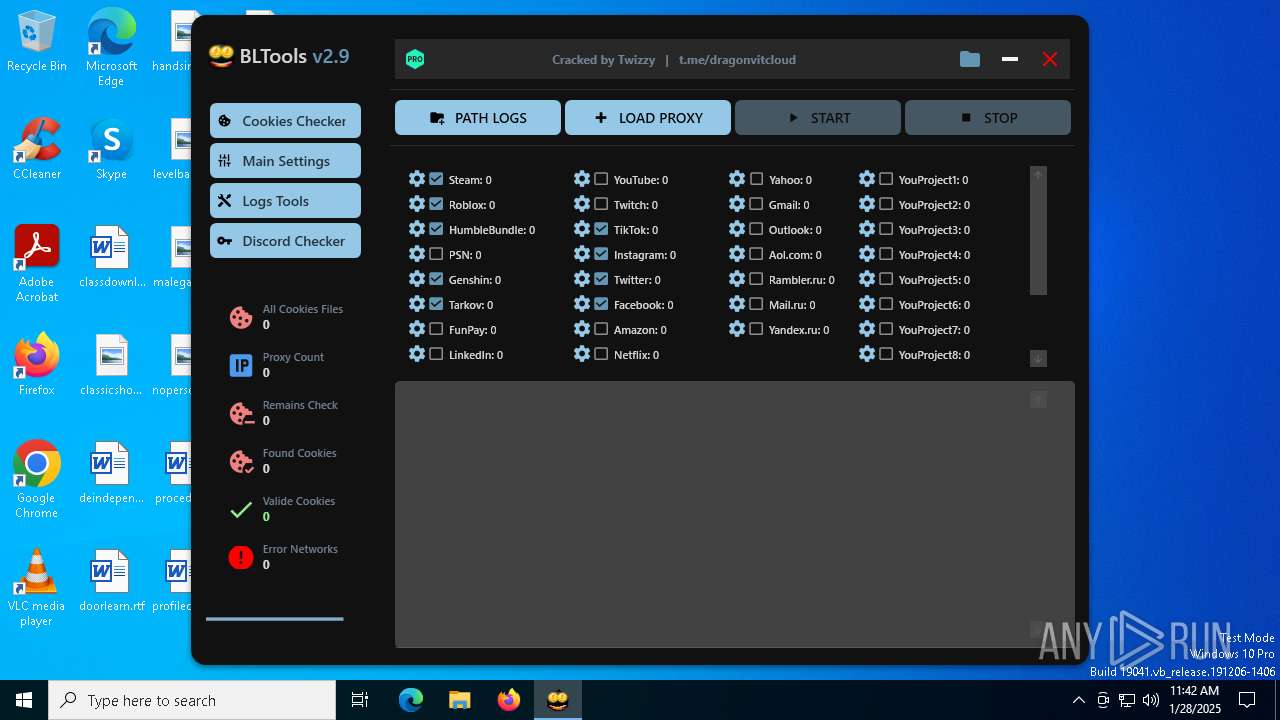
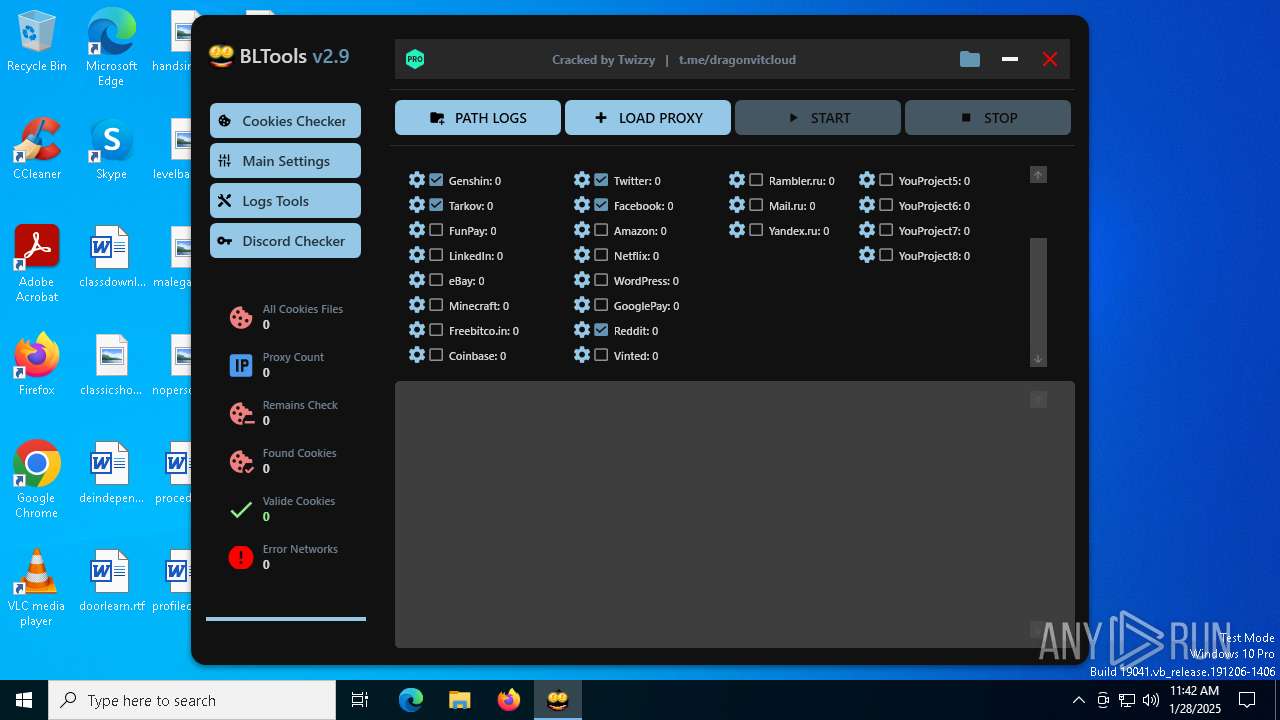
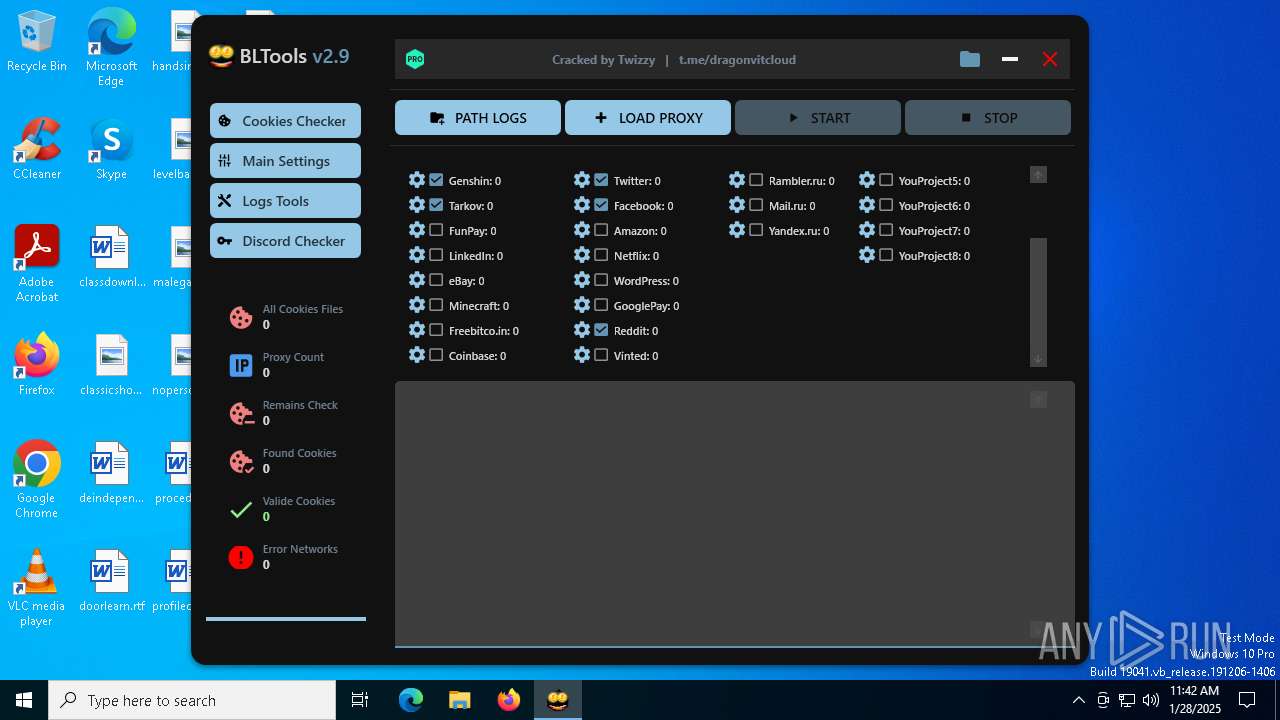
| File name: | BLTools v2.9 PRO.exe |
| Full analysis: | https://app.any.run/tasks/942a6428-4552-41b3-a845-e21a90a2573a |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2025, 11:41:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 9C4FA57A0D02A2E71EF4DCAC942C08D8 |
| SHA1: | 9E6BC8DA3463B3DCA5B3BB0BCB87E946674767C5 |
| SHA256: | 16EC1D273039535A660AC22CE026B37E989E2D011FC0EAD57F9C60DC7E96355F |
| SSDEEP: | 98304:Ub8wDJFqFvCpetDLTfemxb3ksfhkHHmWwjZuN7JZ6iI0RZA+GSayy4Q7r3BxiMTo:3f8s+hvIp652ub |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- BLTools v2.9 PRO.exe (PID: 6360)
- s.exe (PID: 6948)
Executing commands from a ".bat" file
- wscript.exe (PID: 6836)
The process executes VB scripts
- BLTools v2.9 PRO.exe (PID: 6360)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6836)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6836)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6836)
Likely accesses (executes) a file from the Public directory
- wscript.exe (PID: 6836)
- cmd.exe (PID: 6888)
- BLToolsv2.9.exe (PID: 7016)
- csrs.exe (PID: 7060)
Process drops legitimate windows executable
- BLTools v2.9 PRO.exe (PID: 6360)
Reads security settings of Internet Explorer
- BLTools v2.9 PRO.exe (PID: 6360)
- BLToolsv2.9.exe (PID: 7016)
INFO
Reads the computer name
- BLTools v2.9 PRO.exe (PID: 6360)
- s.exe (PID: 6948)
- BLToolsv2.9.exe (PID: 7016)
- csrs.exe (PID: 7060)
Checks supported languages
- BLTools v2.9 PRO.exe (PID: 6360)
- s.exe (PID: 6948)
- BLToolsv2.9.exe (PID: 7016)
- csrs.exe (PID: 7060)
Process checks computer location settings
- BLTools v2.9 PRO.exe (PID: 6360)
- s.exe (PID: 6948)
The sample compiled with english language support
- s.exe (PID: 6948)
Creates files or folders in the user directory
- csrs.exe (PID: 7060)
Reads the machine GUID from the registry
- BLToolsv2.9.exe (PID: 7016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2090:05:09 08:18:44+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 6472192 |
| InitializedDataSize: | 70144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x62e1de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | app |
| FileVersion: | 1.0.0.0 |
| InternalName: | app.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | app.exe |
| ProductName: | app |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
134
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6360 | "C:\Users\admin\AppData\Local\Temp\BLTools v2.9 PRO.exe" | C:\Users\admin\AppData\Local\Temp\BLTools v2.9 PRO.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: app Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6836 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\Public\MicrosoftEdgeUpdates\ps.vbs" | C:\Windows\SysWOW64\wscript.exe | — | BLTools v2.9 PRO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6888 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\MicrosoftEdgeUpdates\pss.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6948 | s.exe -pC#X#niM5N$nXf$FbKnDEm | C:\Users\Public\MicrosoftEdgeUpdates\s.exe | cmd.exe | ||||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Version: 1.6.0.2712 Modules
| |||||||||||||||
| 7016 | "C:\Users\Public\BLToolsv2.9\BLToolsv2.9.exe" | C:\Users\Public\BLToolsv2.9\BLToolsv2.9.exe | — | BLTools v2.9 PRO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BLTools Cookies Checker Exit code: 0 Version: 2.9.0.0 Modules
| |||||||||||||||
| 7060 | "C:\Users\Public\MicrosoftEdgeUpdates\csrs.exe" | C:\Users\Public\MicrosoftEdgeUpdates\csrs.exe | — | s.exe | |||||||||||
User: admin Company: Maël Hörz Integrity Level: MEDIUM Description: HxD Hex Editor Version: 2.5.0.0 Modules
| |||||||||||||||
Total events
3 782
Read events
3 779
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6360) BLTools v2.9 PRO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7016) BLToolsv2.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Left |
Value: 0 | |||
| (PID) Process: | (7016) BLToolsv2.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Top |
Value: 0 | |||
Executable files
10
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\MicrosoftEdgeUpdates\s.exe | executable | |
MD5:EA0C431D39020ADF9188B15731A4C6A1 | SHA256:44719C936FBA5283A48388094691CA4472CF9E5980D583FECA8D5BBC0D1D4ACD | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9.zip | compressed | |
MD5:A1150833D239AFFBE607681119BA613F | SHA256:C9A92D871ECDB4B285D3522640B4D400955A2E4D2EAE2A13C5039AF135035993 | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\MicrosoftEdgeUpdates\ps.vbs | text | |
MD5:A7A7DFD9BF4B1BC6CB369B02D8766F9F | SHA256:4A405629649CA66445CD39DD9F5D83D622913EEE1B6DE6EBF2E7B7AE5C8F9B2A | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\CookiesCreator.exe | executable | |
MD5:E42B6AA3255C2A75AD2E05CD40FE7063 | SHA256:A0B162A146BCF19634559A88877C21FABB512FBED11834F82D2FA60E56F0FAA6 | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\AlphaFS.dll | executable | |
MD5:F2F6F6798D306D6D7DF4267434B5C5F9 | SHA256:837F2CEAB6BBD9BC4BF076F1CB90B3158191888C3055DD2B78A1E23F1C3AAFDD | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\Extreme.Net.dll | executable | |
MD5:F79F0E3A0361CAC000E2D3553753CD68 | SHA256:8A6518AB7419FBEC3AC9875BAA3AFB410AD1398C7AA622A09CD9084EC6CADFCD | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\Ookii.Dialogs.Wpf.dll | executable | |
MD5:932EBB3F9E7113071C6A17818342B7CC | SHA256:285AA8225732DDBCF211B1158BD6CFF8BF3ACBEEAB69617F4BE85862B7105AB5 | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\License.dll | text | |
MD5:B08A5C34CF0A06615DA2CA89010D8B4F | SHA256:04CC5B3B49A7E9E9B6C66C7BE59A20992BF2653746B5D43829C383FB233F88FA | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\MaterialDesignColors.dll | executable | |
MD5:5C108C4DA6D03F0FA2C3B4DC7890CB52 | SHA256:B5EC30C93B1D2B4631EE2B178750EC92E302E2E331090EC9783981B9572354F8 | |||
| 6360 | BLTools v2.9 PRO.exe | C:\Users\Public\BLToolsv2.9\Microsoft.Xaml.Behaviors.dll | executable | |
MD5:95F46F34C099421D917D5FEADBB33EDB | SHA256:8E77A1DD5E2DF4D4AF801376CC3428B082EB49FCB6E647B933967FAE12AD9D5D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3928 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4044 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4044 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 92.123.22.101:80 | www.microsoft.com | AKAMAI-AS | AT | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |