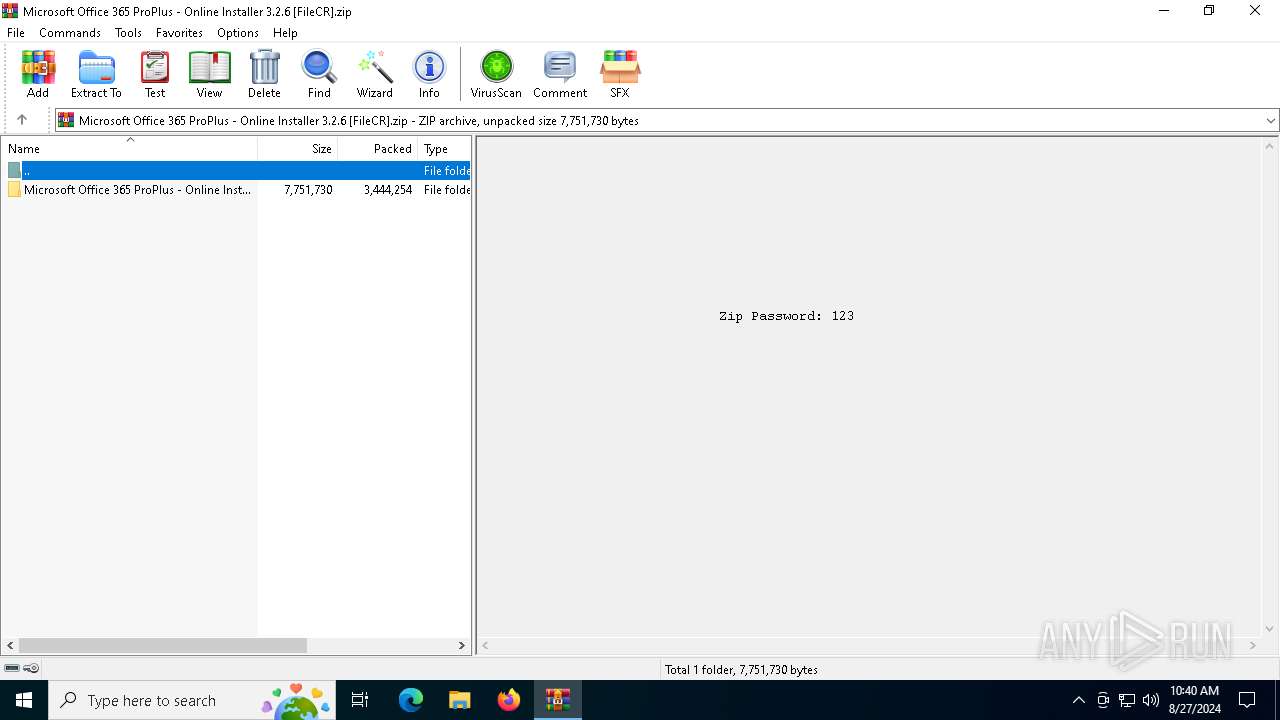
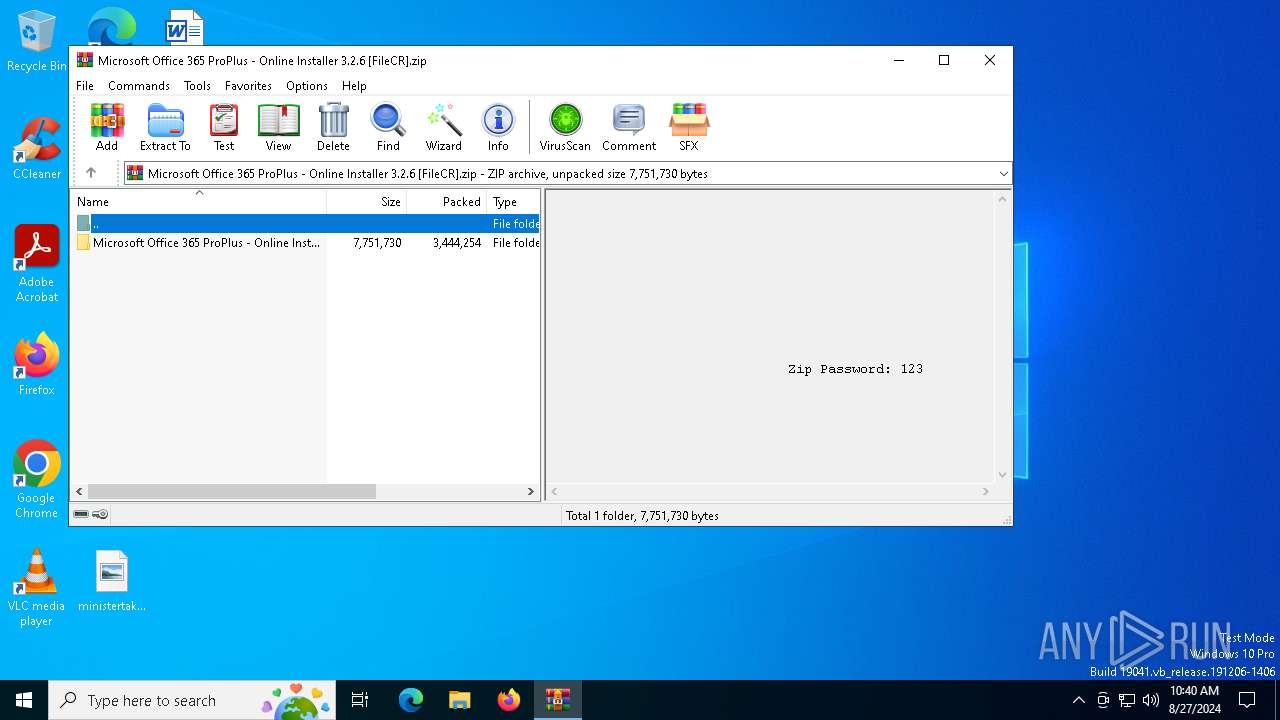
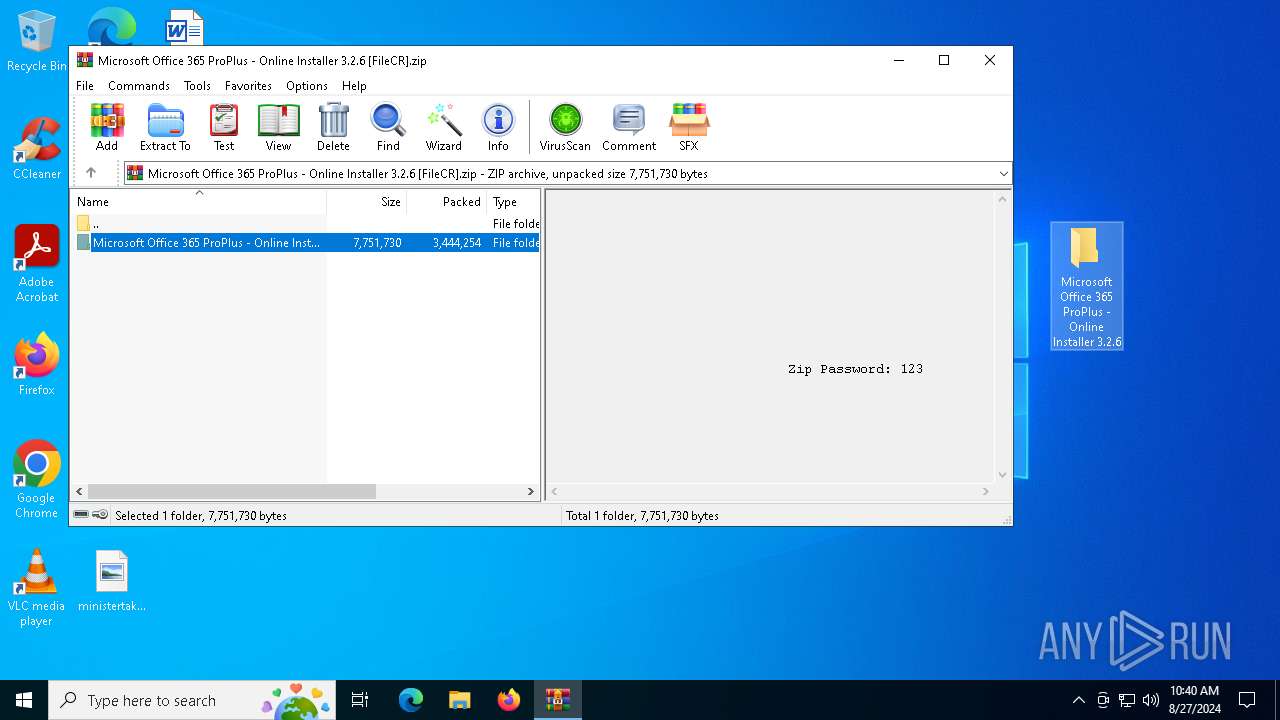
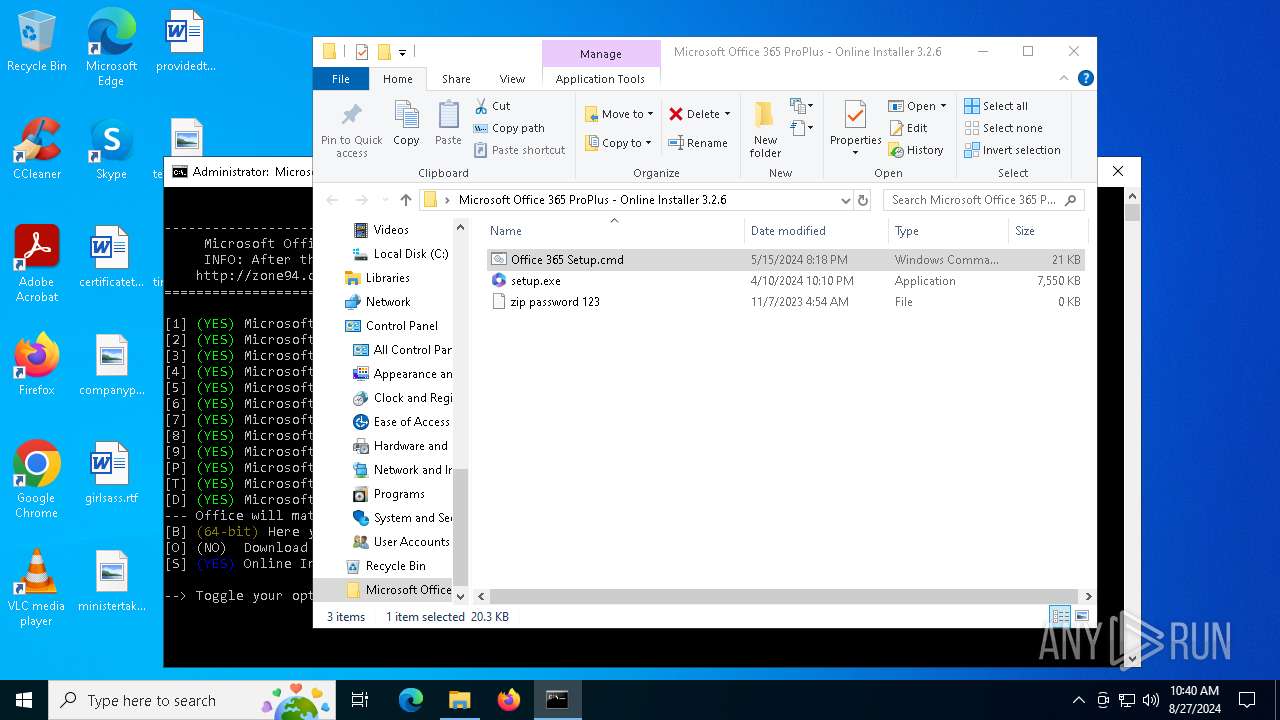
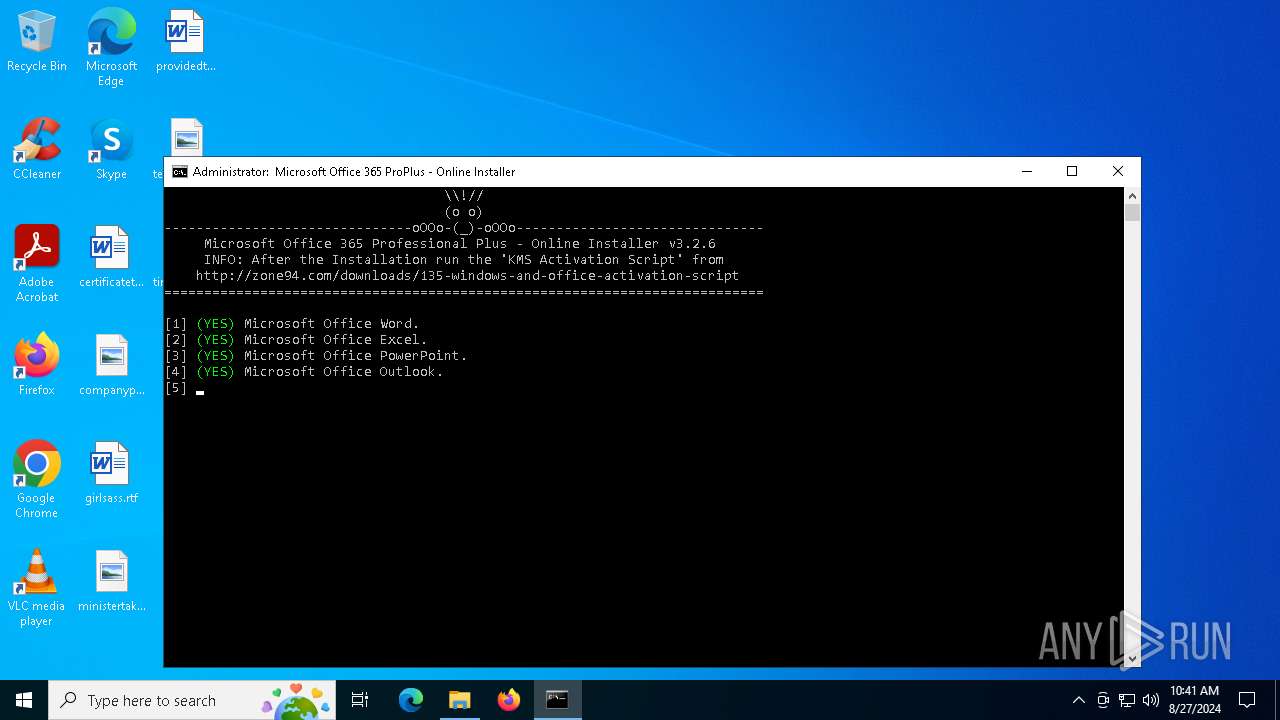
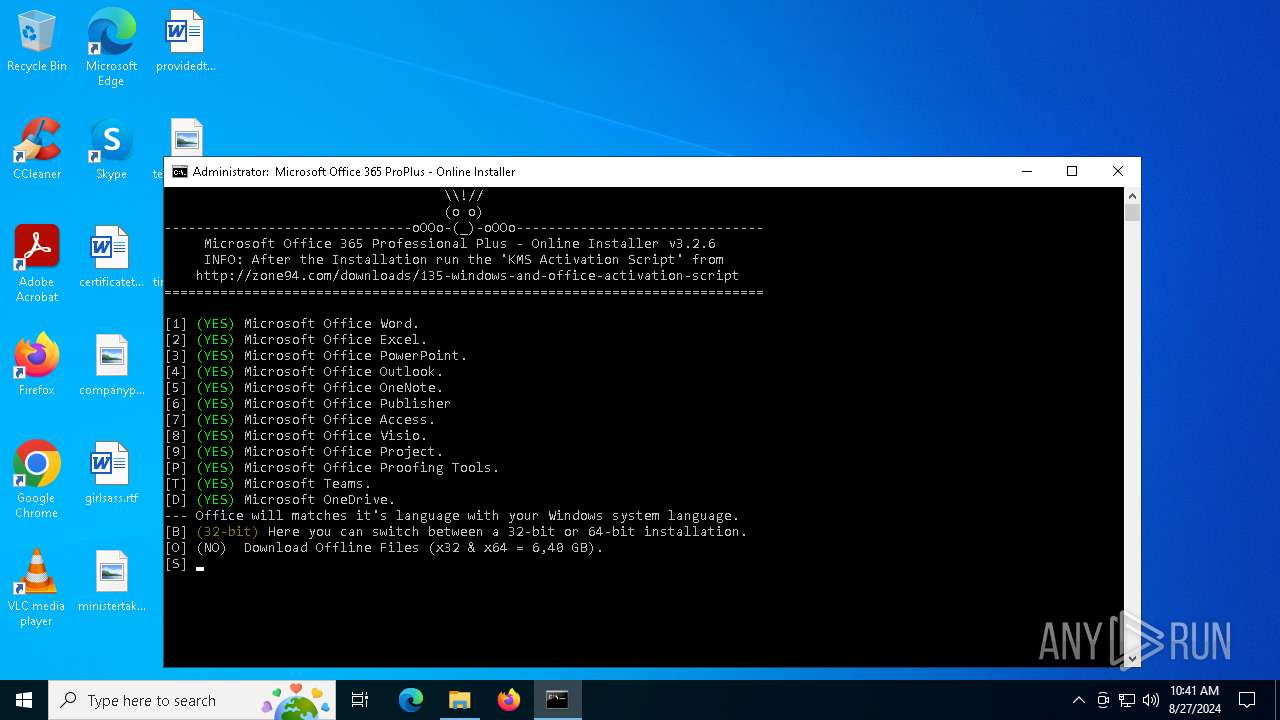
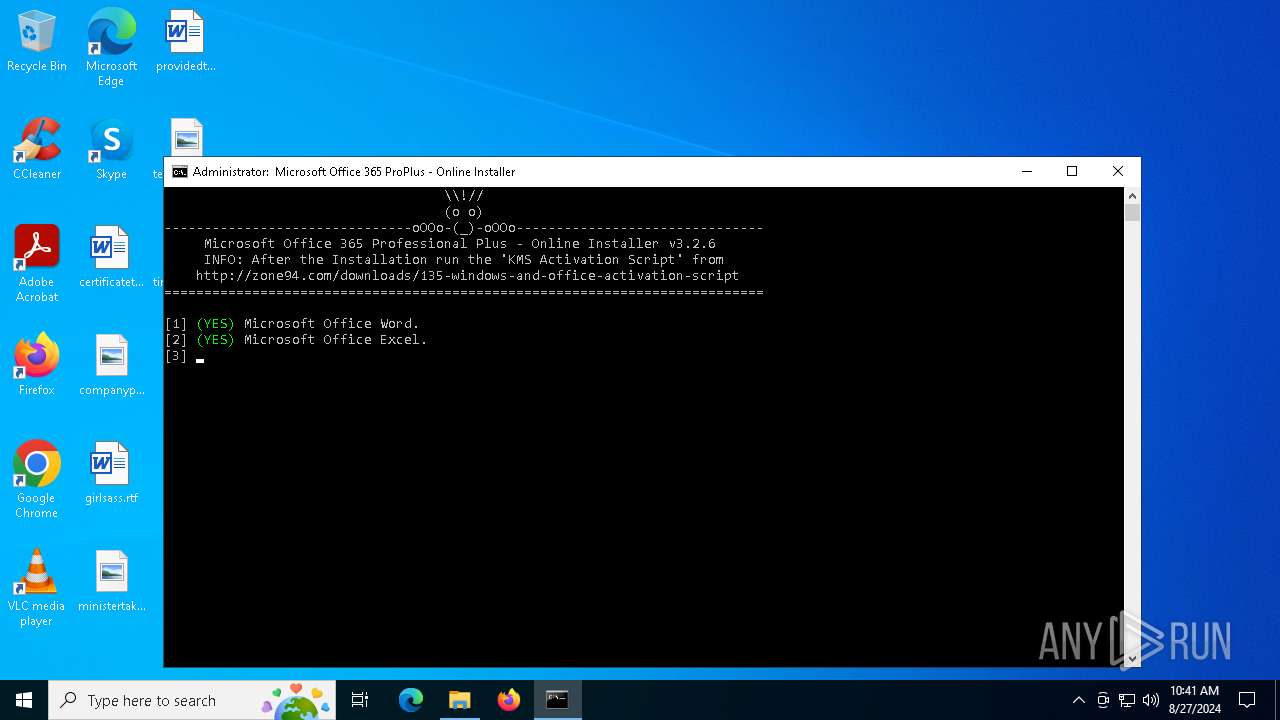
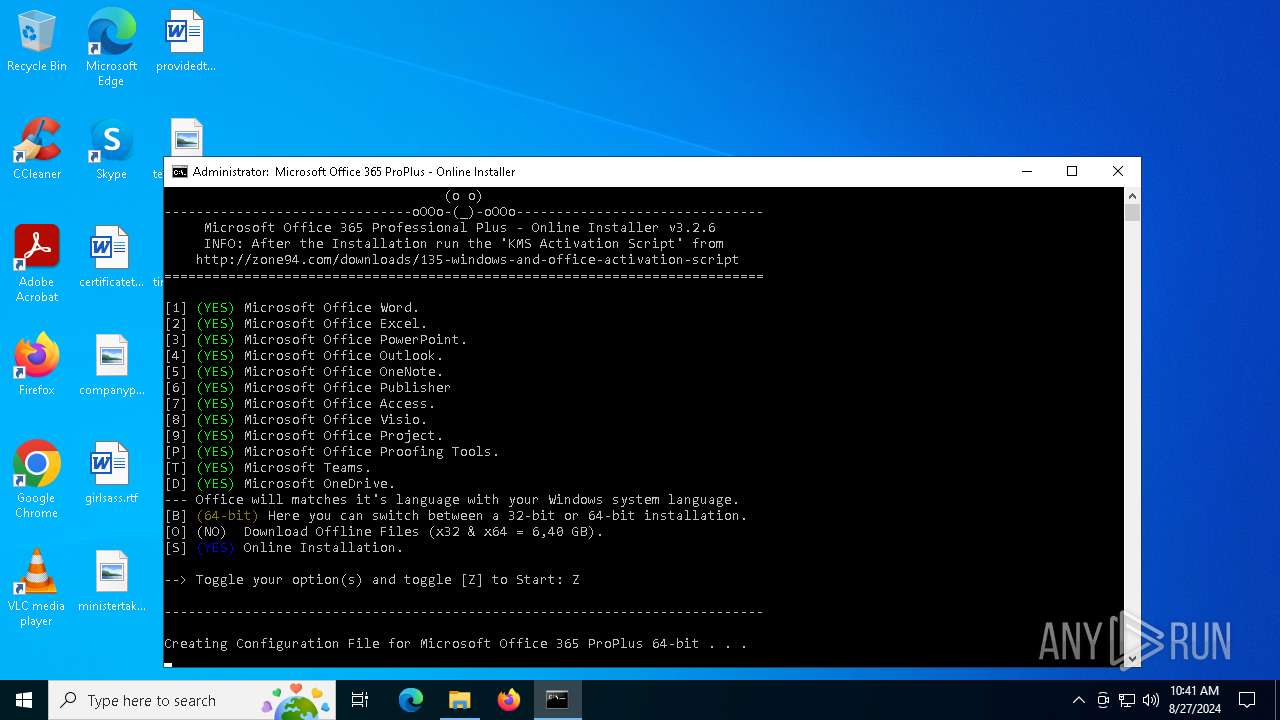
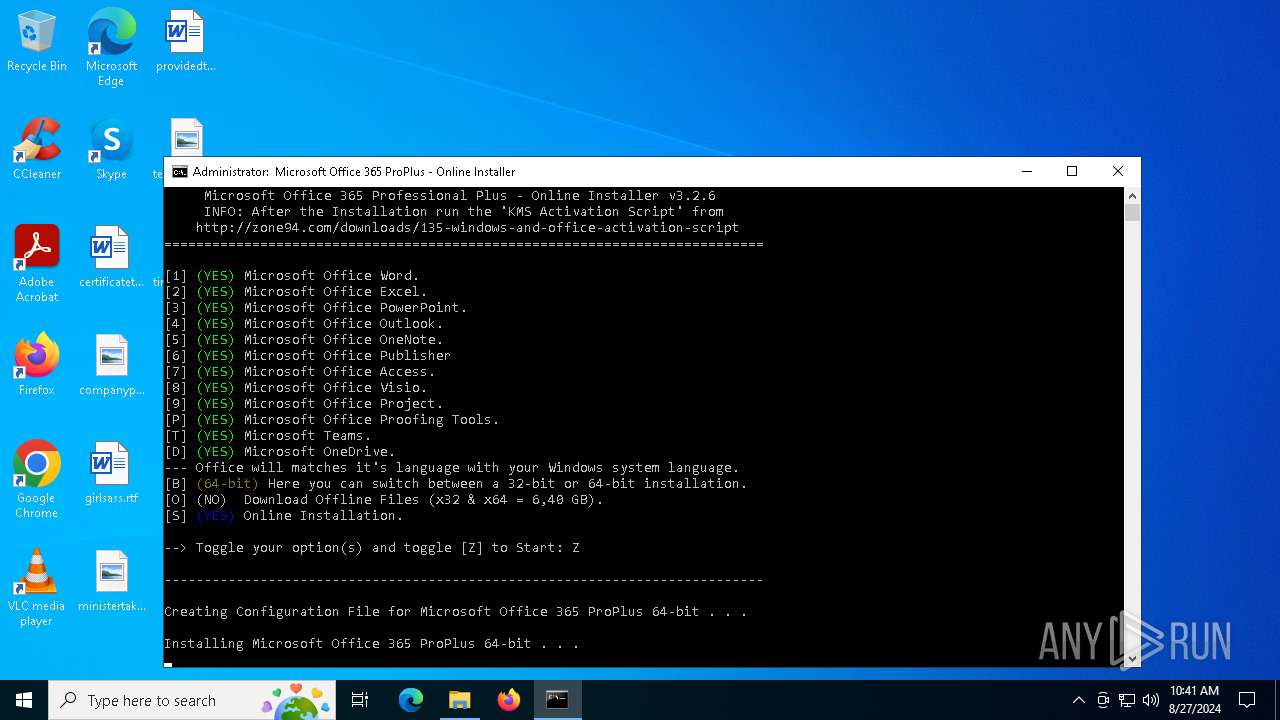
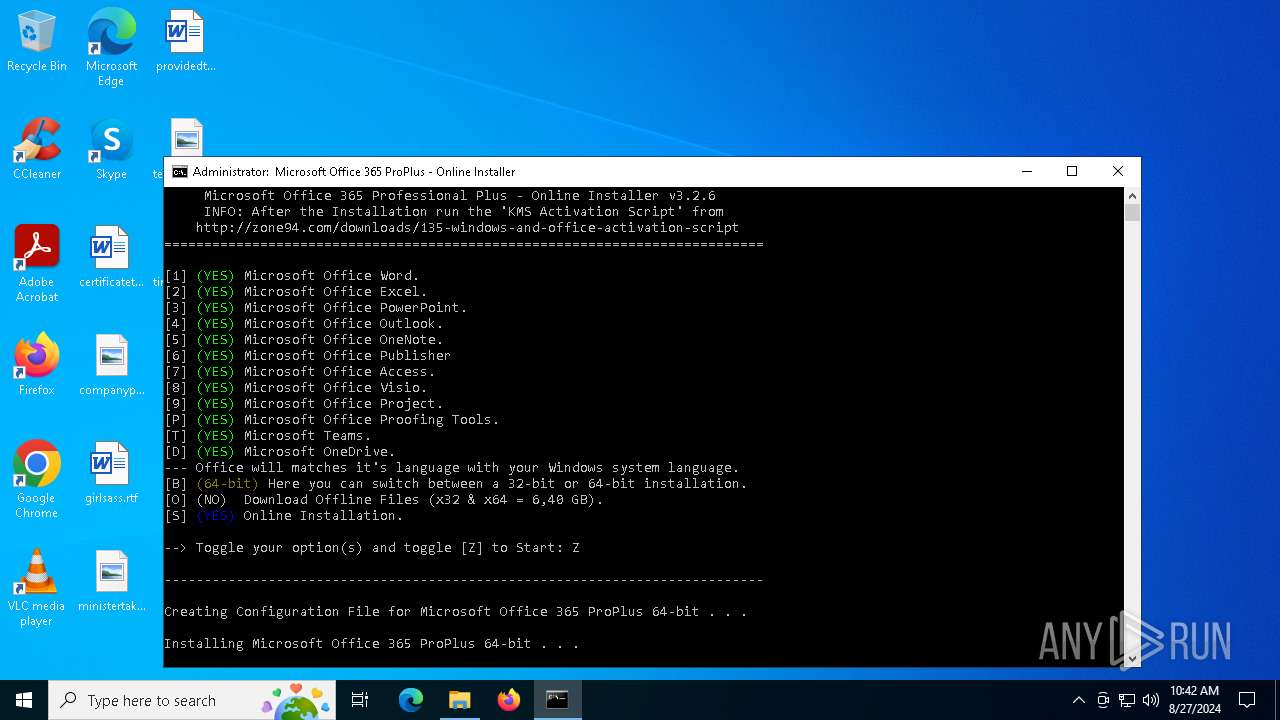
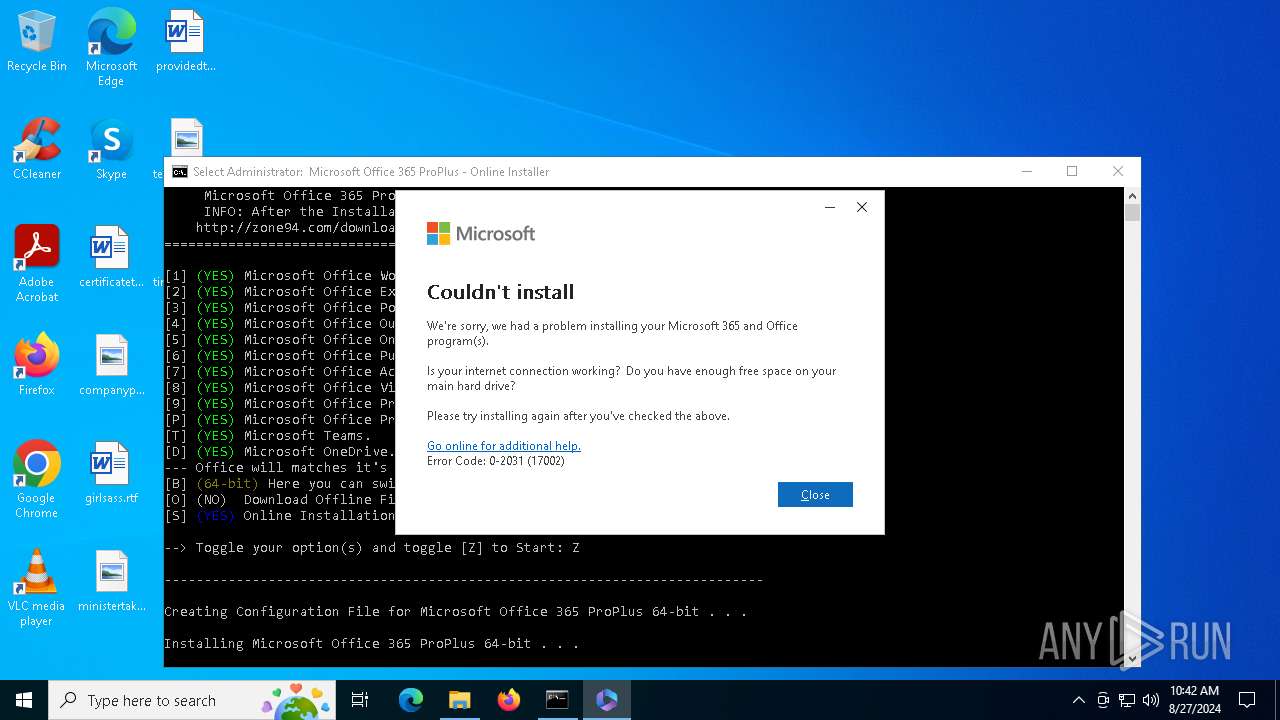
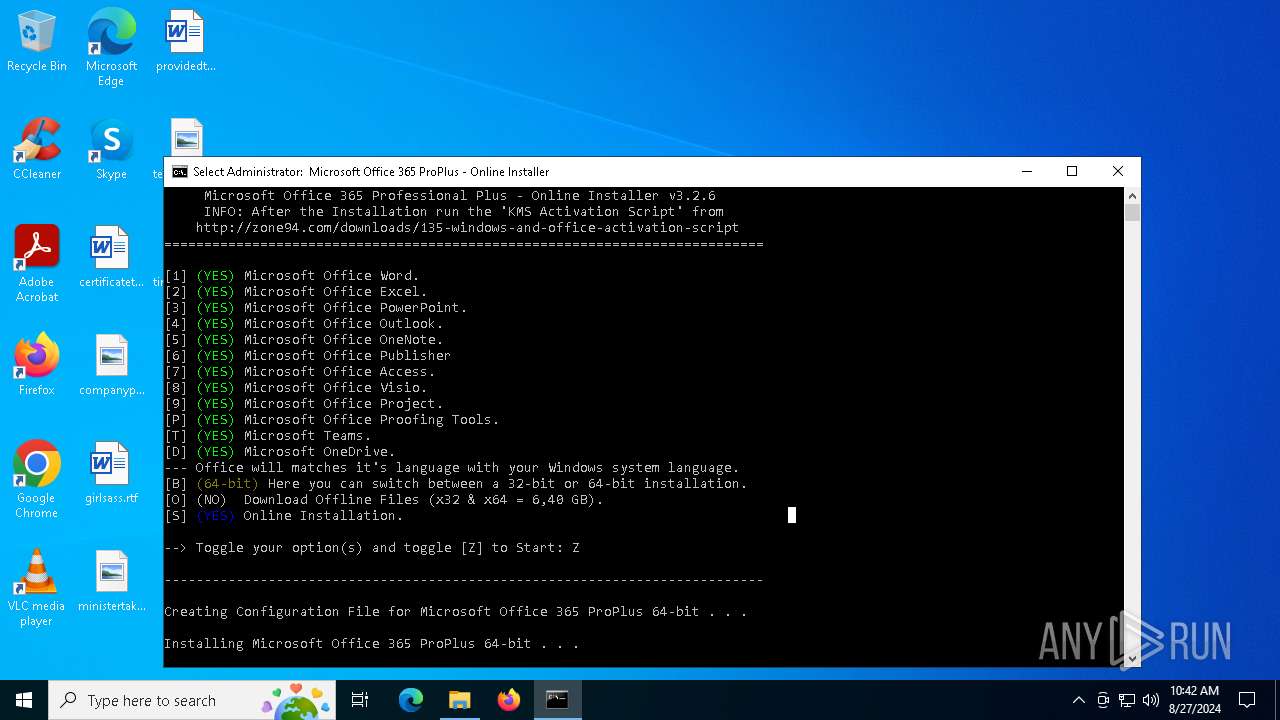
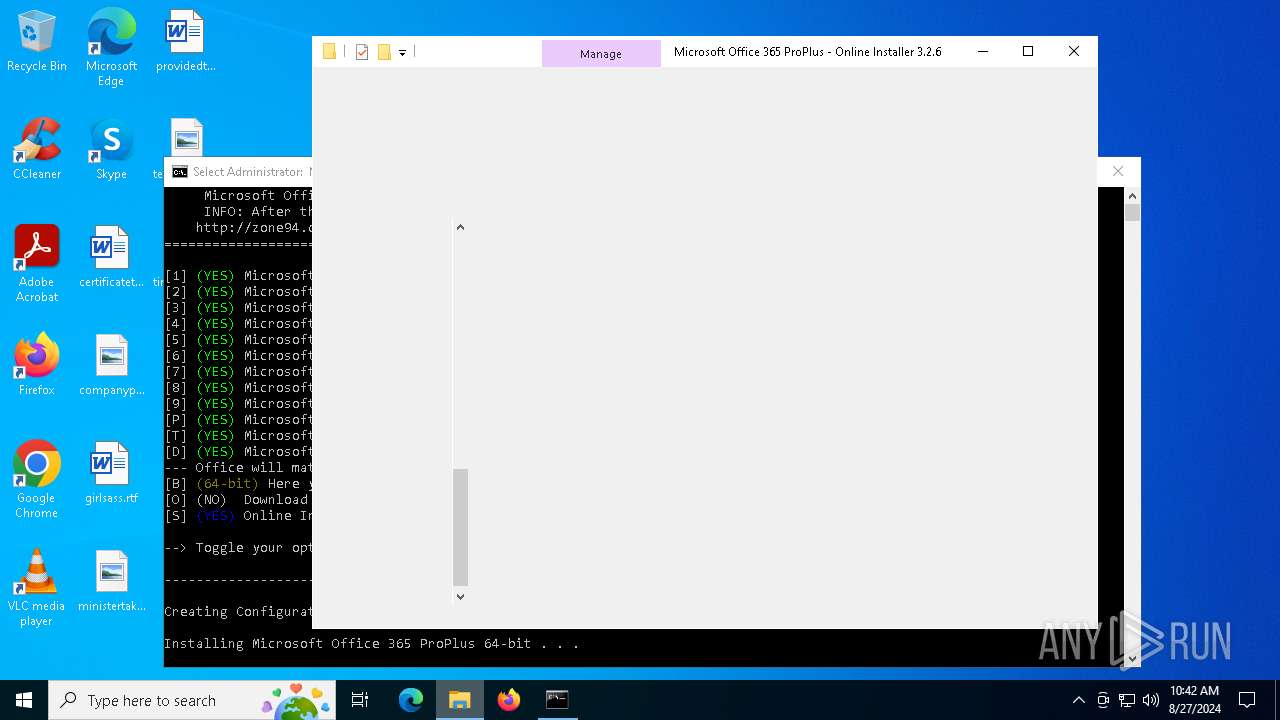
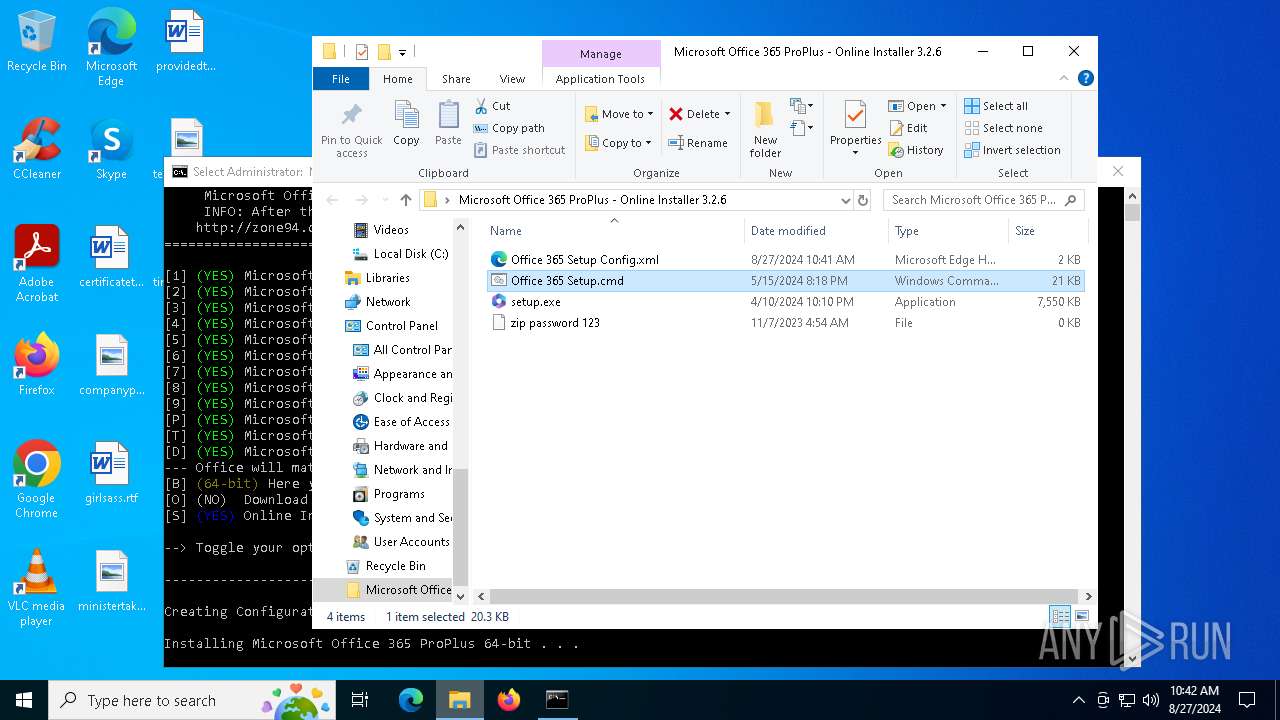
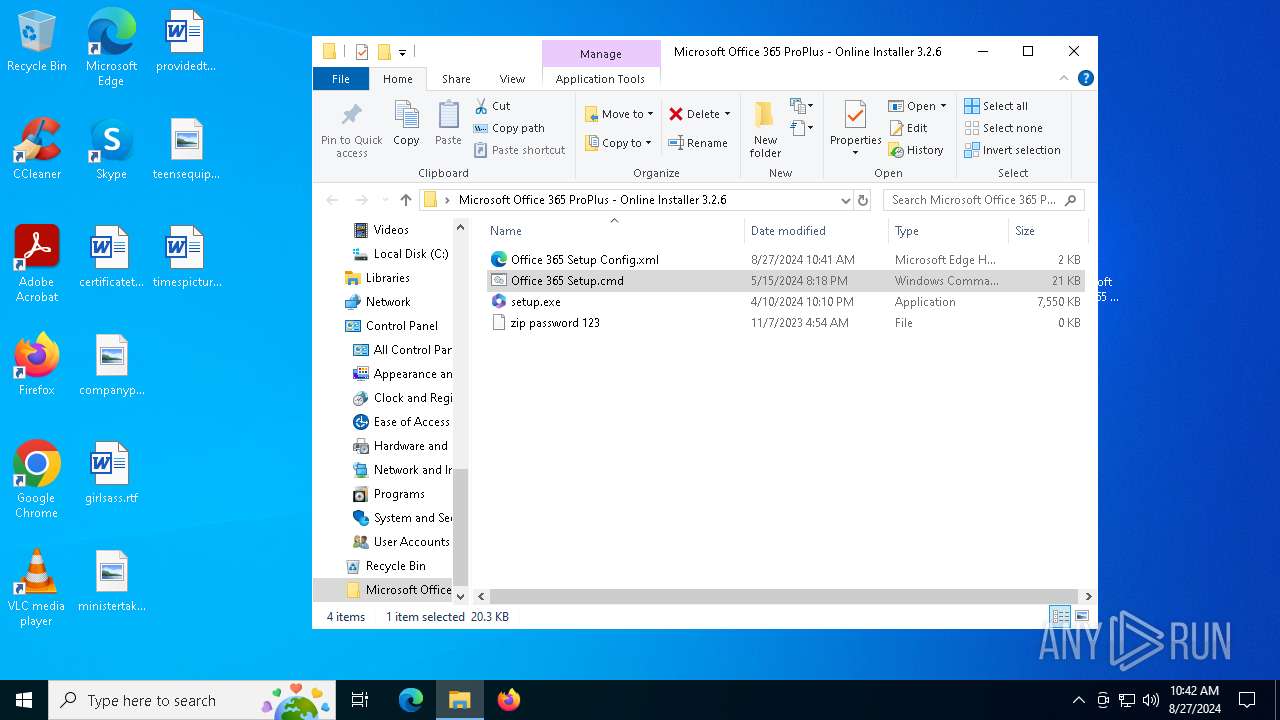
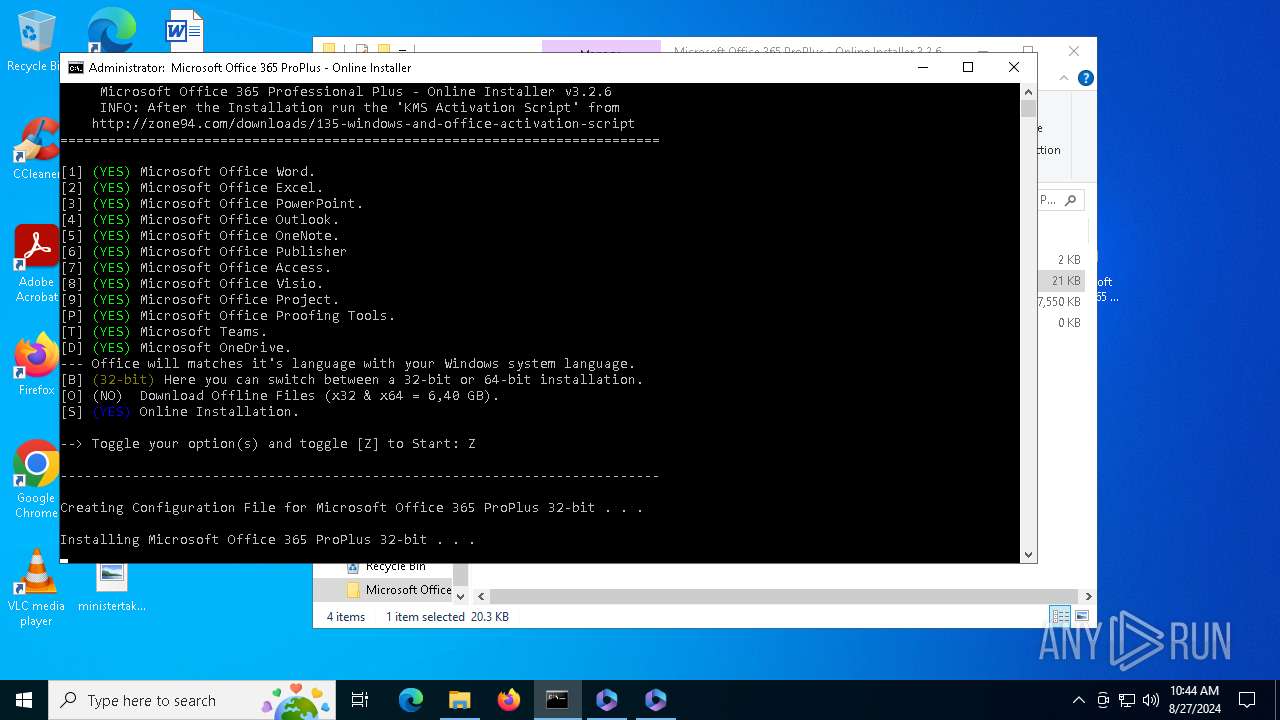
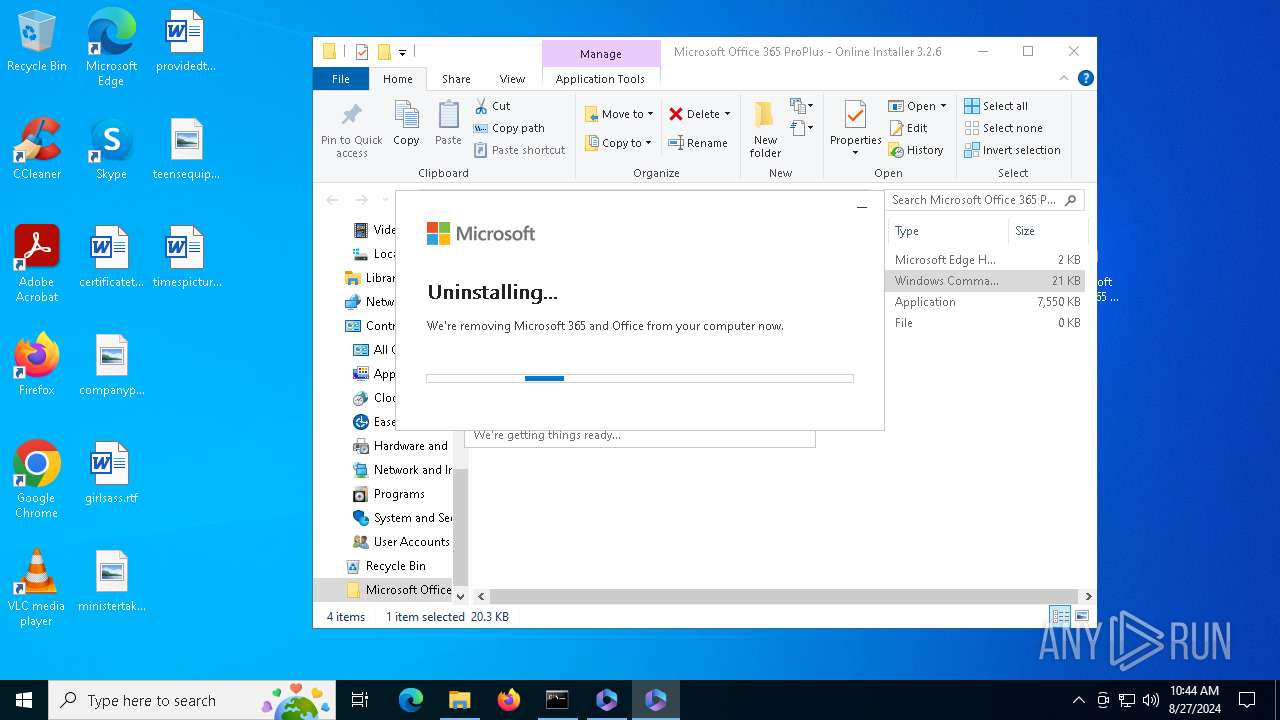
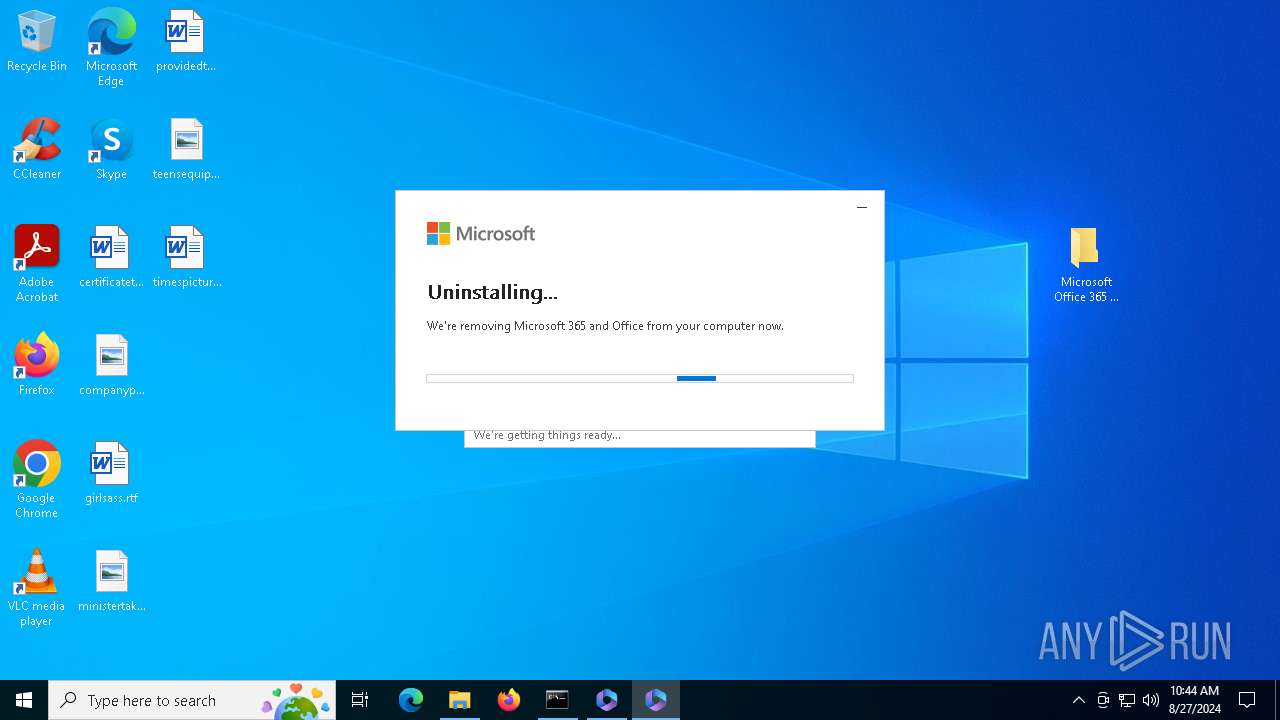
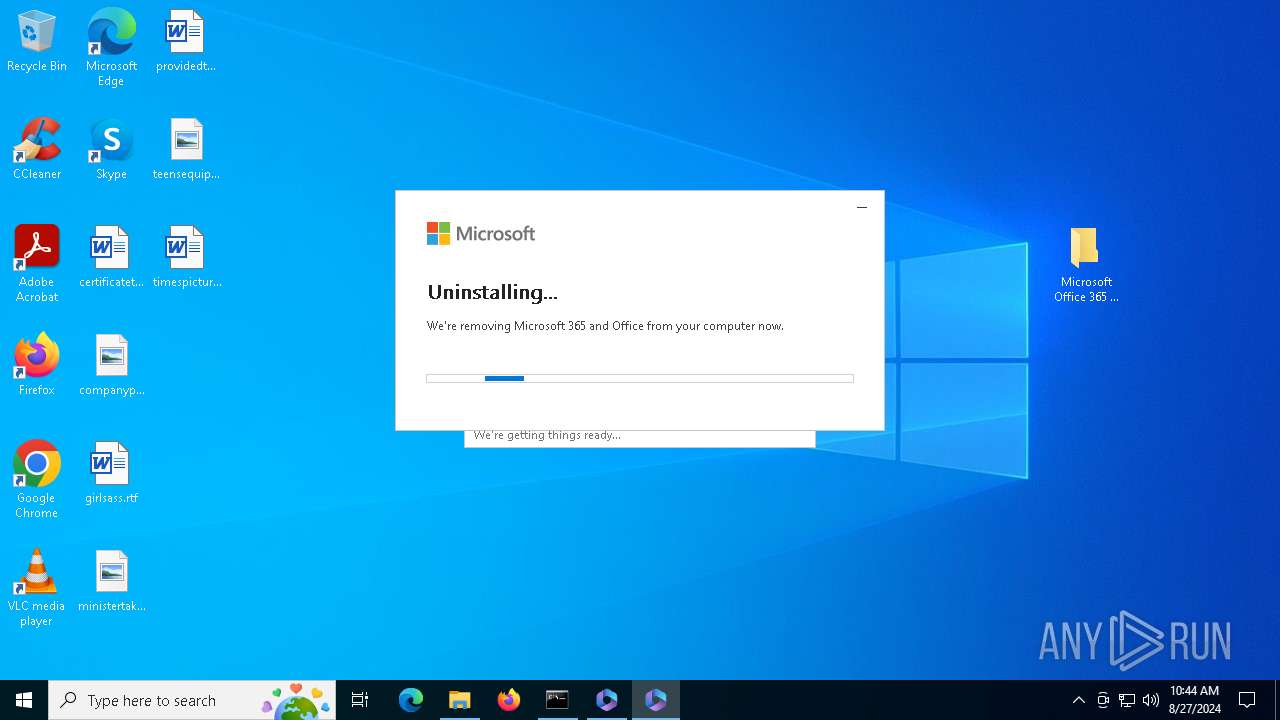
| File name: | Microsoft Office 365 ProPlus - Online Installer 3.2.6 [FileCR].zip |
| Full analysis: | https://app.any.run/tasks/673efafe-adba-4f19-9b2d-b528933cc8d3 |
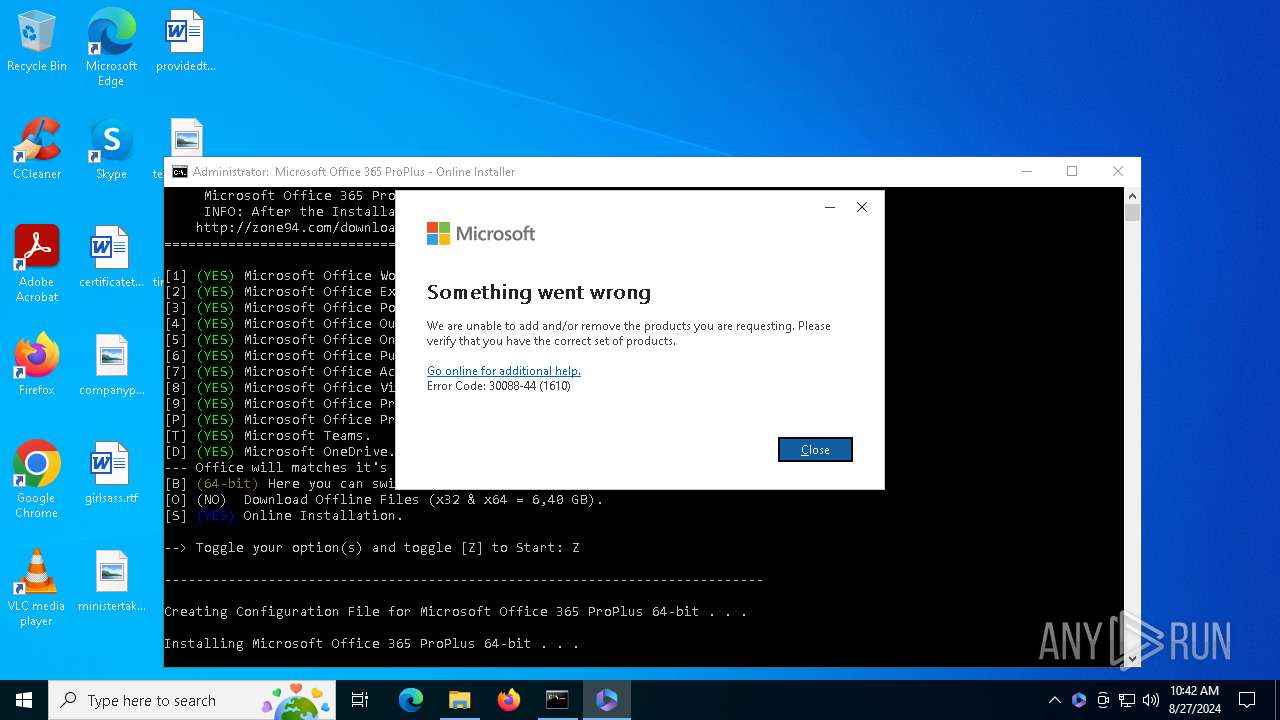
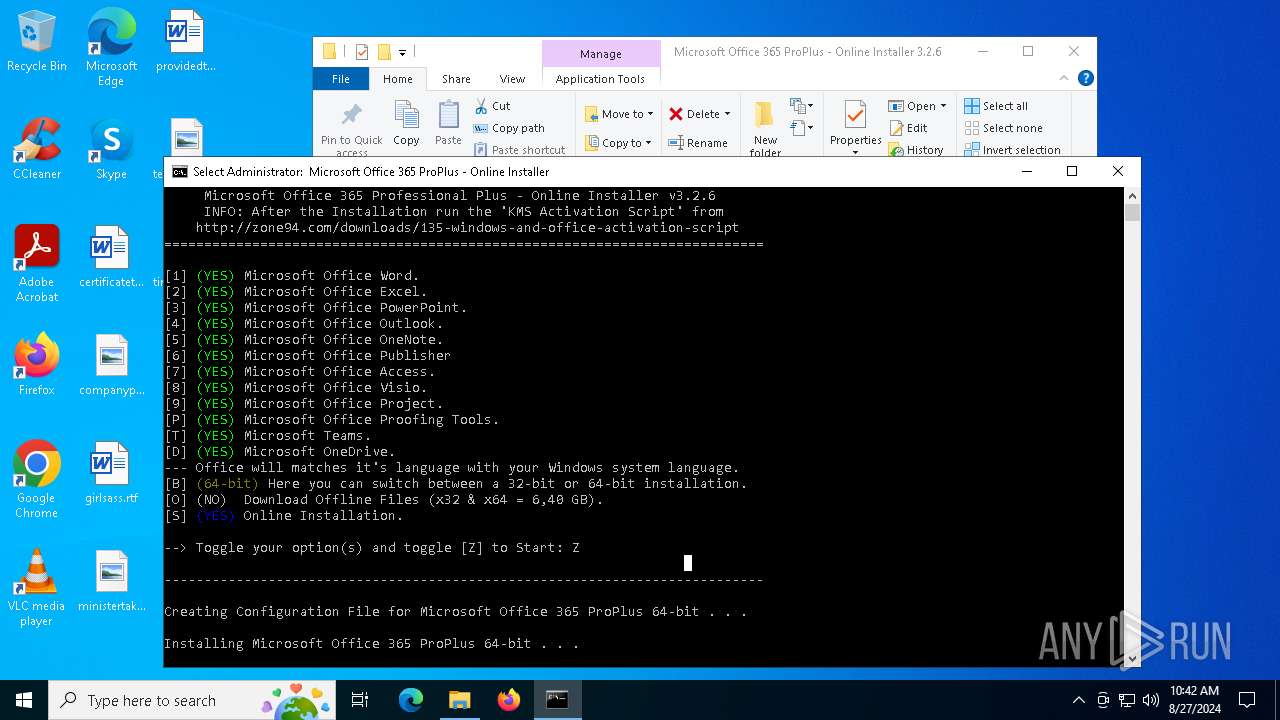
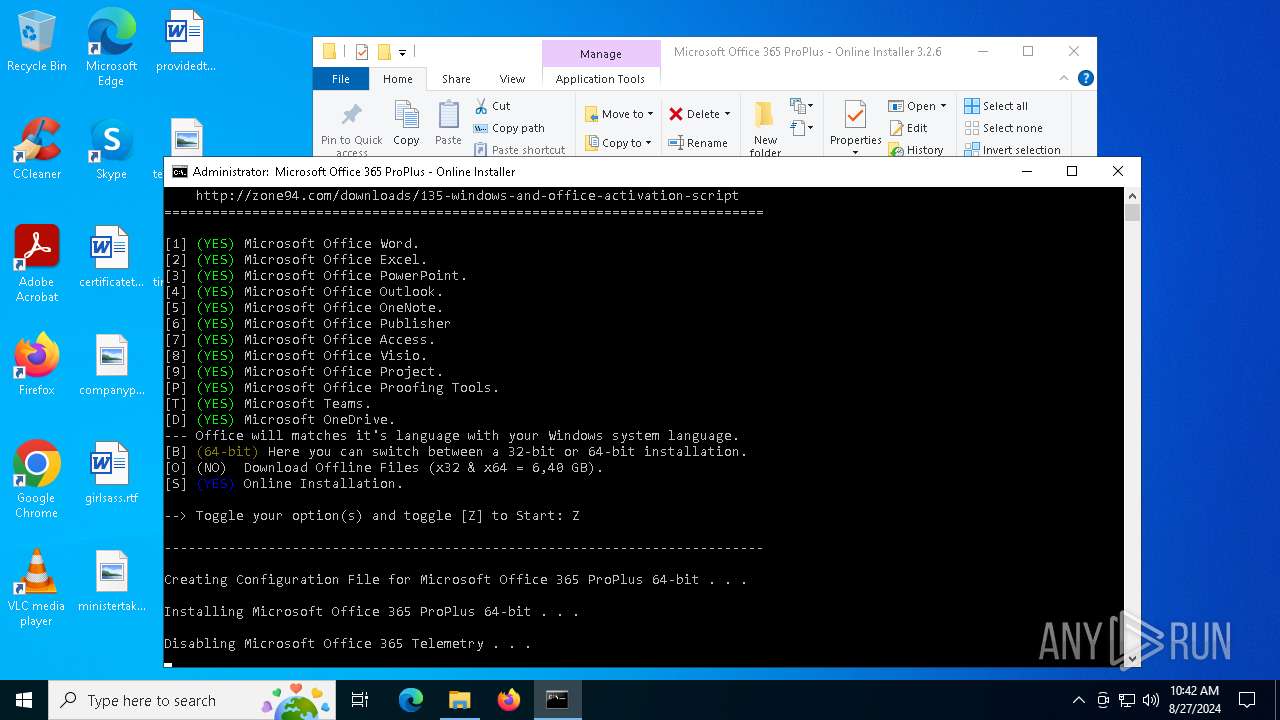
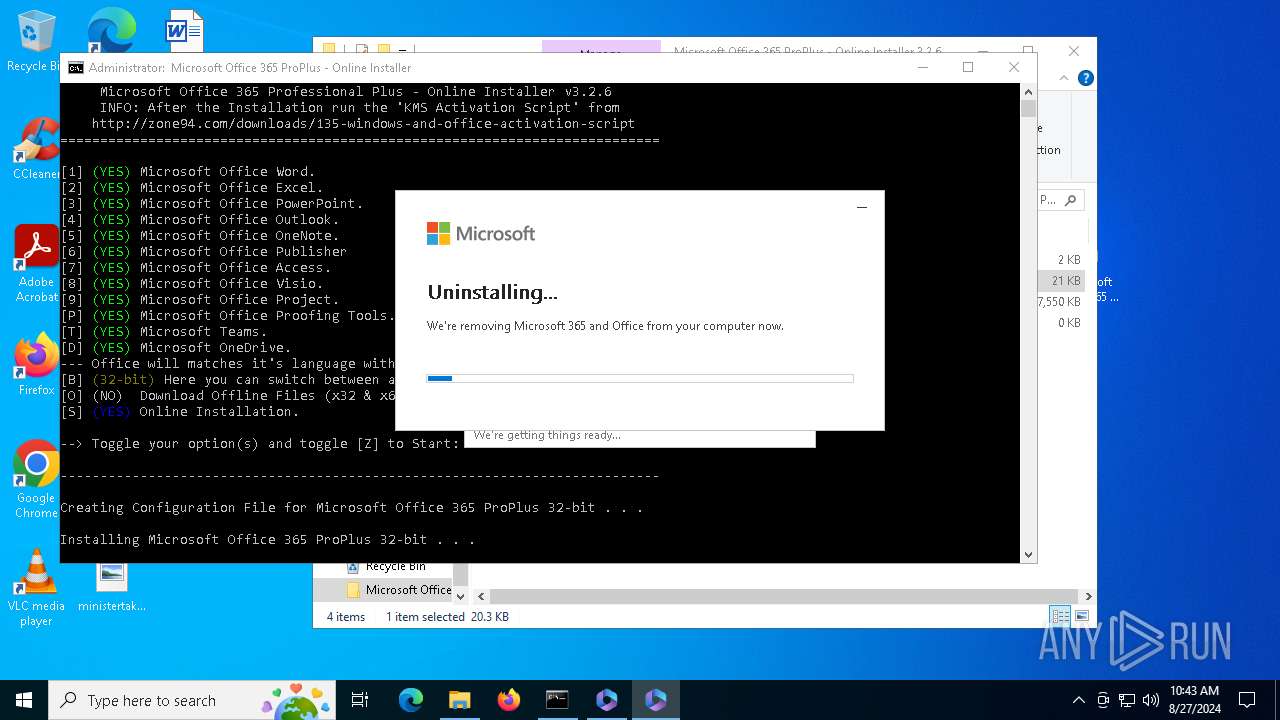
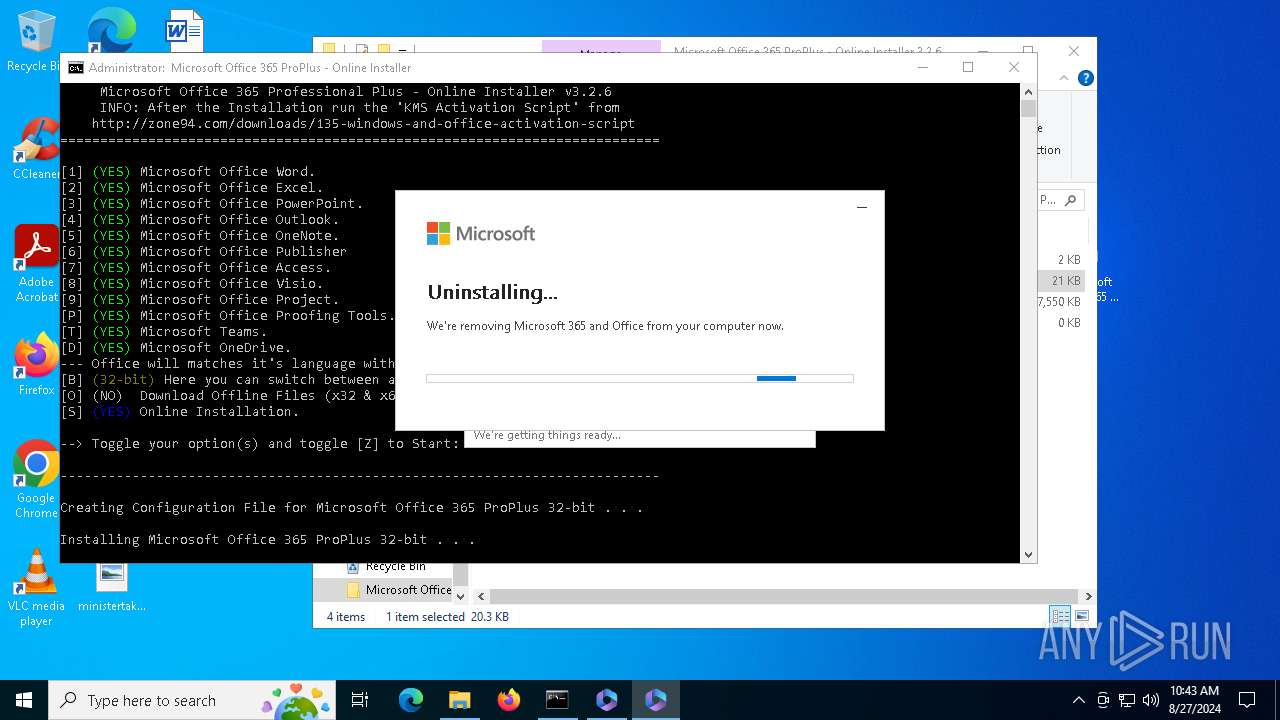
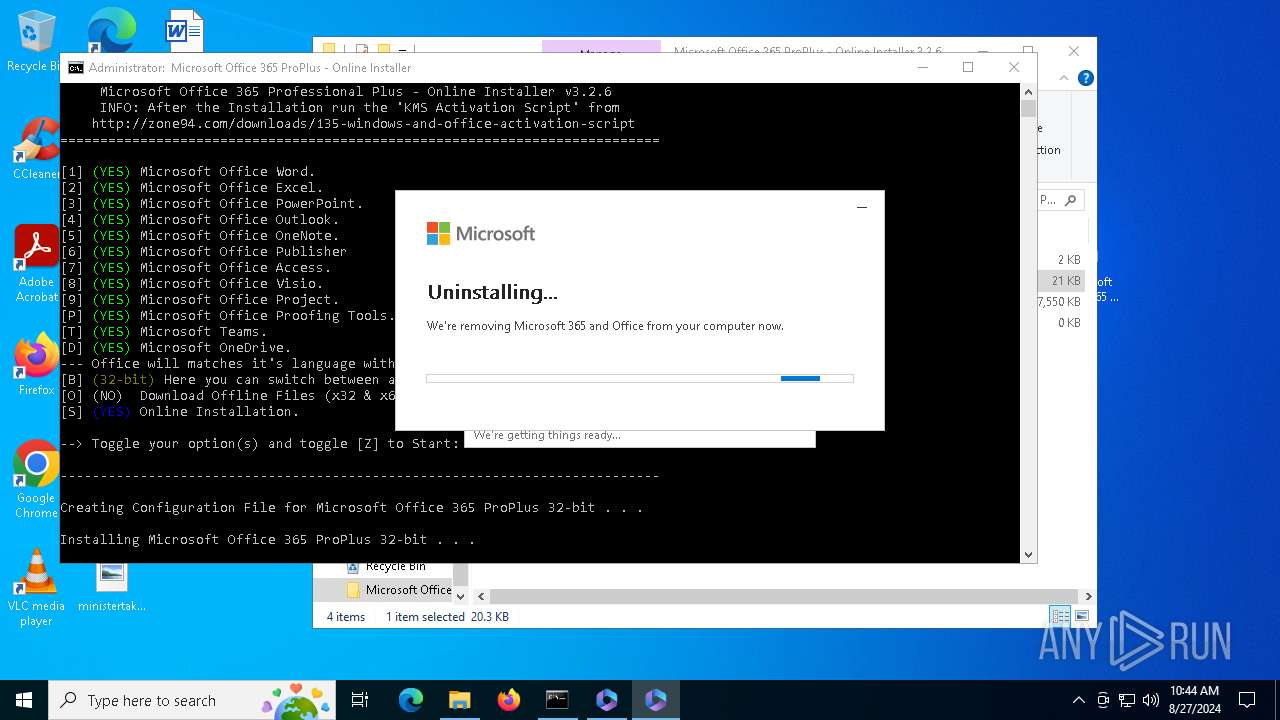
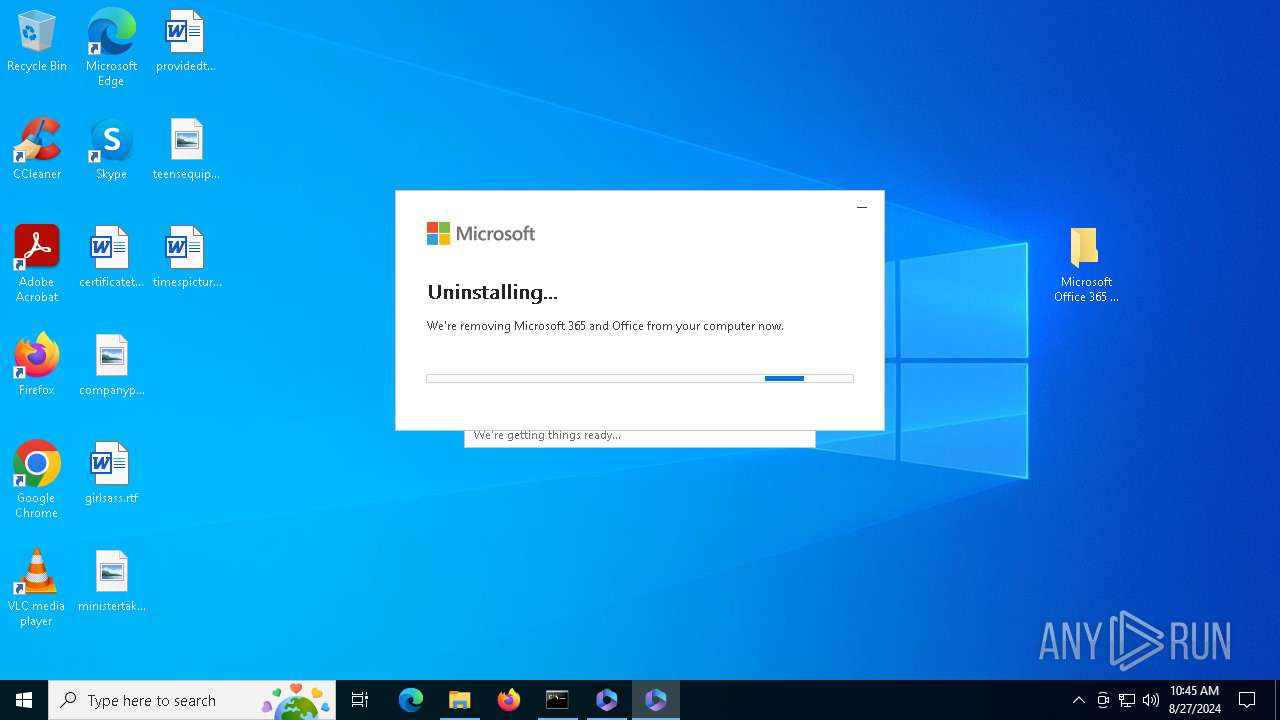
| Verdict: | Malicious activity |
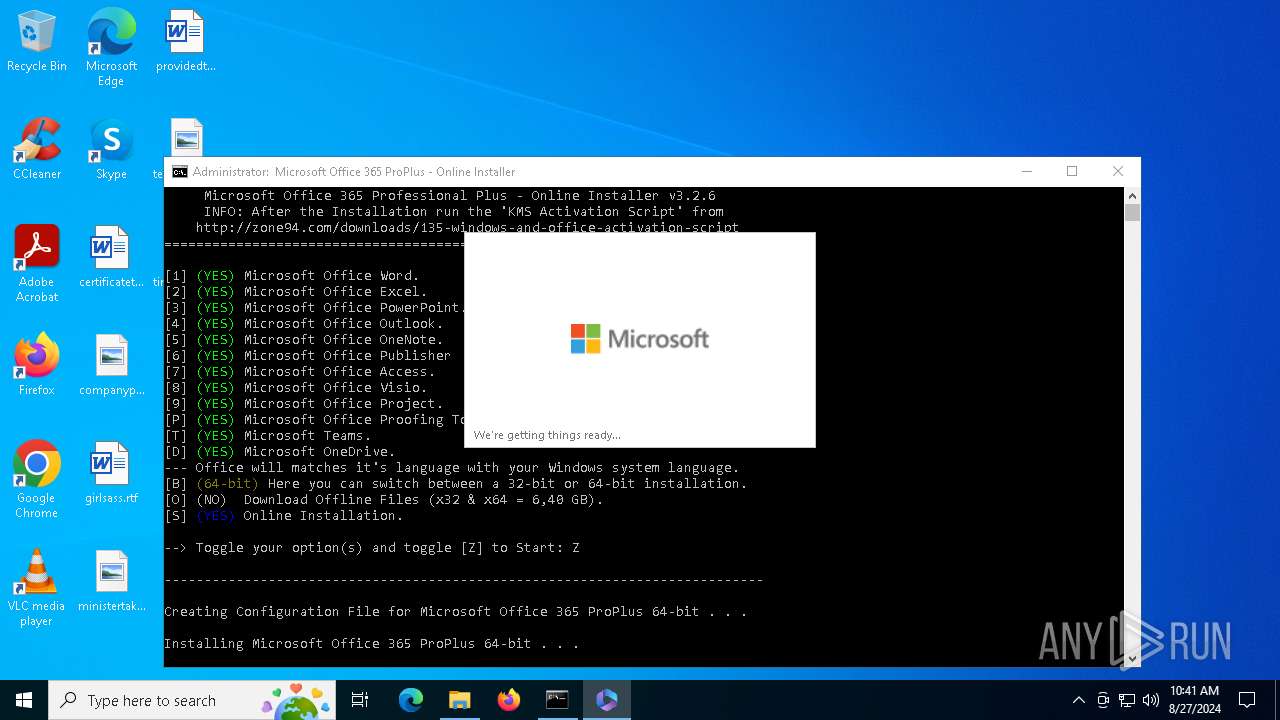
| Analysis date: | August 27, 2024, 10:40:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | A7A3607691E597A7940DE9580BB2EBE2 |
| SHA1: | 48EB3F31FB5055C3FCBA6819CBC40B537051A98E |
| SHA256: | 16E9F7231C4ED888FC2C374E1D40FBC3C97544EB5665750B8FC2581C4844804C |
| SSDEEP: | 98304:kTnXTeGs148KCDwE4Qwv9lXuu6/AHjEuCYQbKb4xGIrHg0ieY2n8nLDsiWONbEdK:1p7sVr |
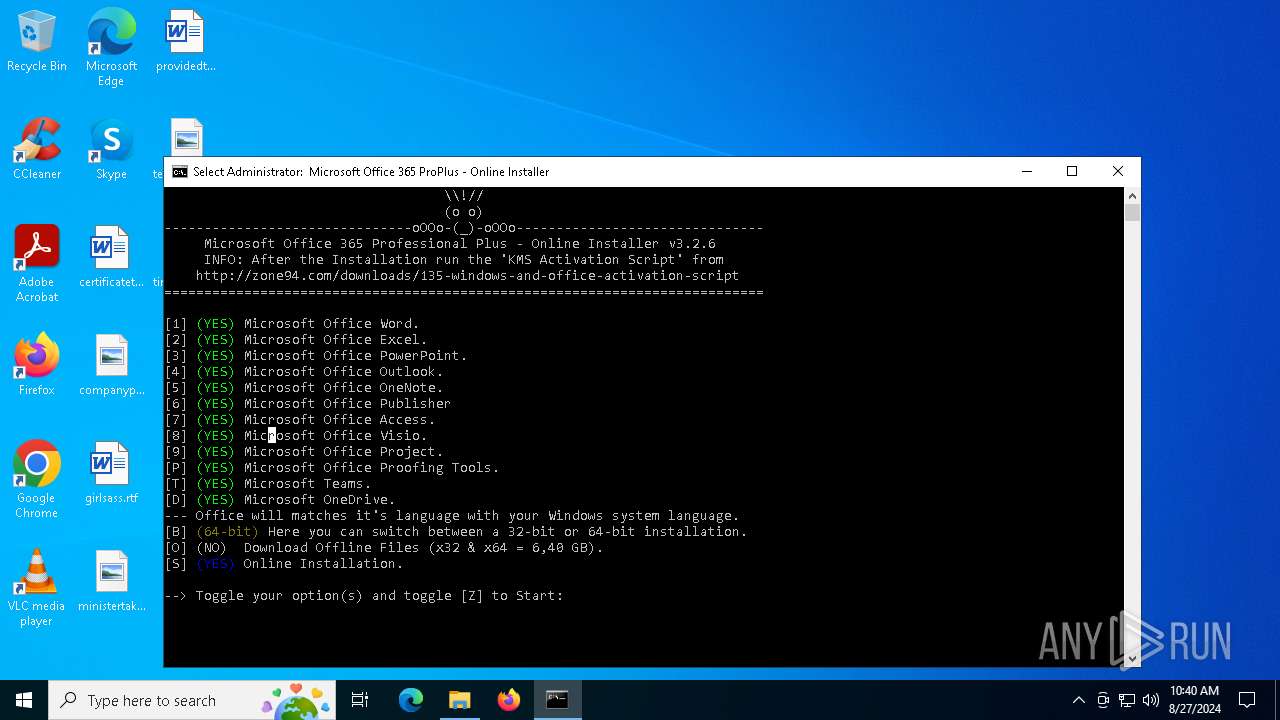
MALICIOUS
Scans artifacts that could help determine the target
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6152)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
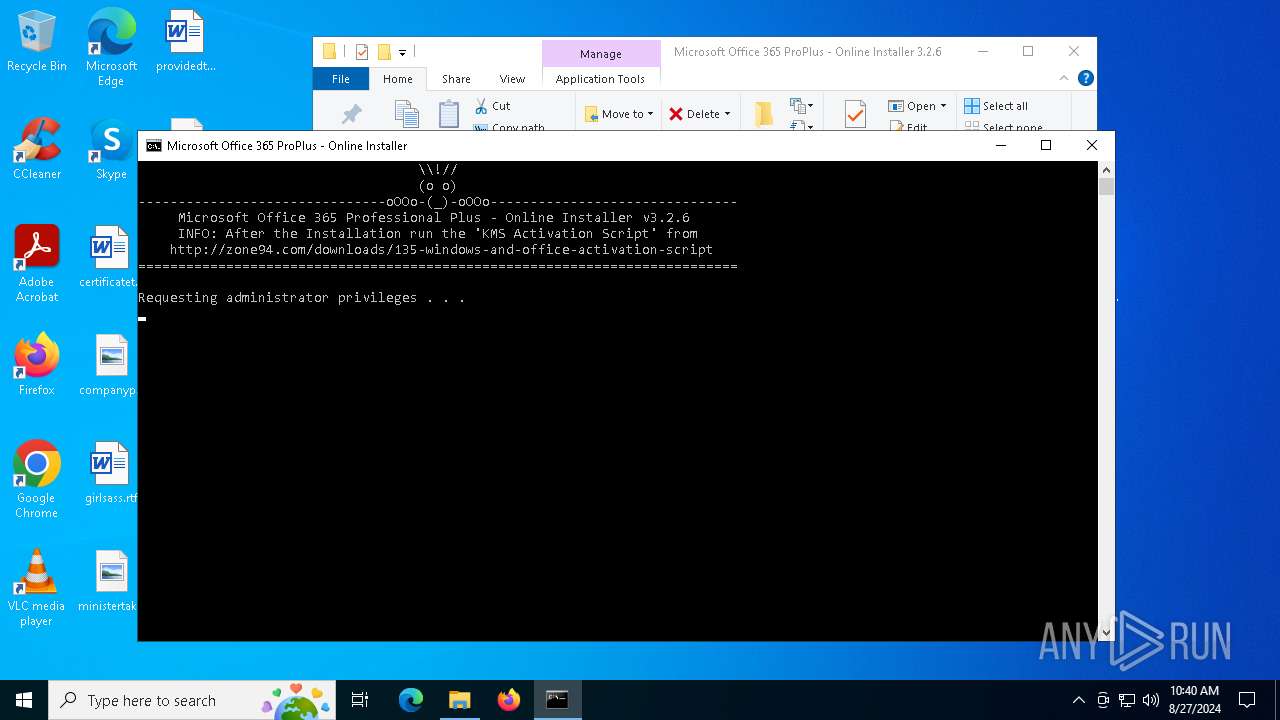
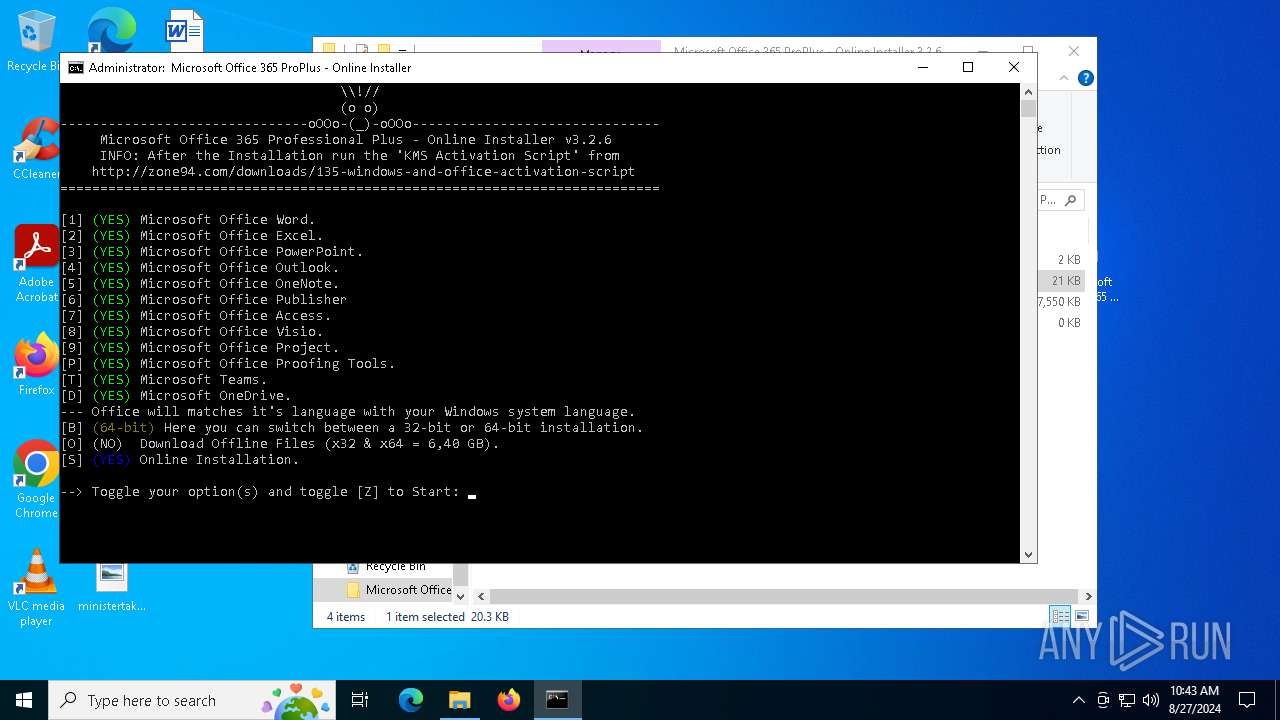
Starts application with an unusual extension
- cmd.exe (PID: 2040)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 6780)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2040)
- cmd.exe (PID: 2768)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2040)
- cmd.exe (PID: 2768)
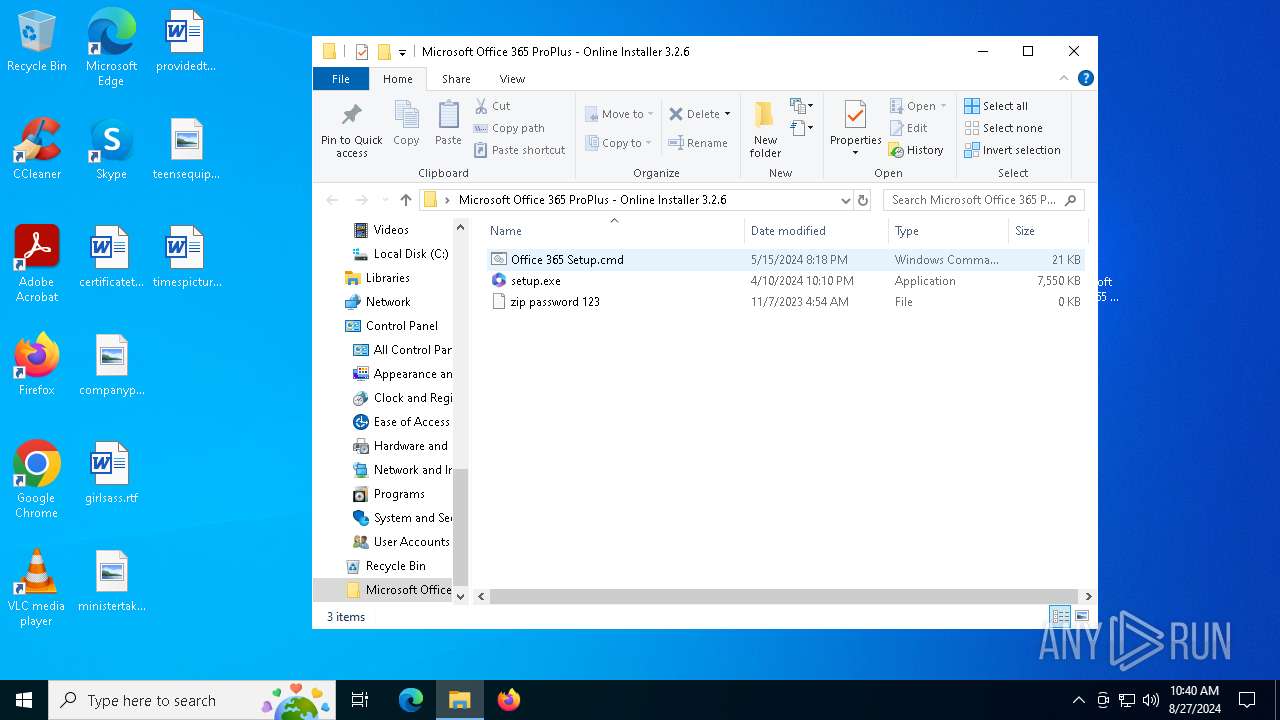
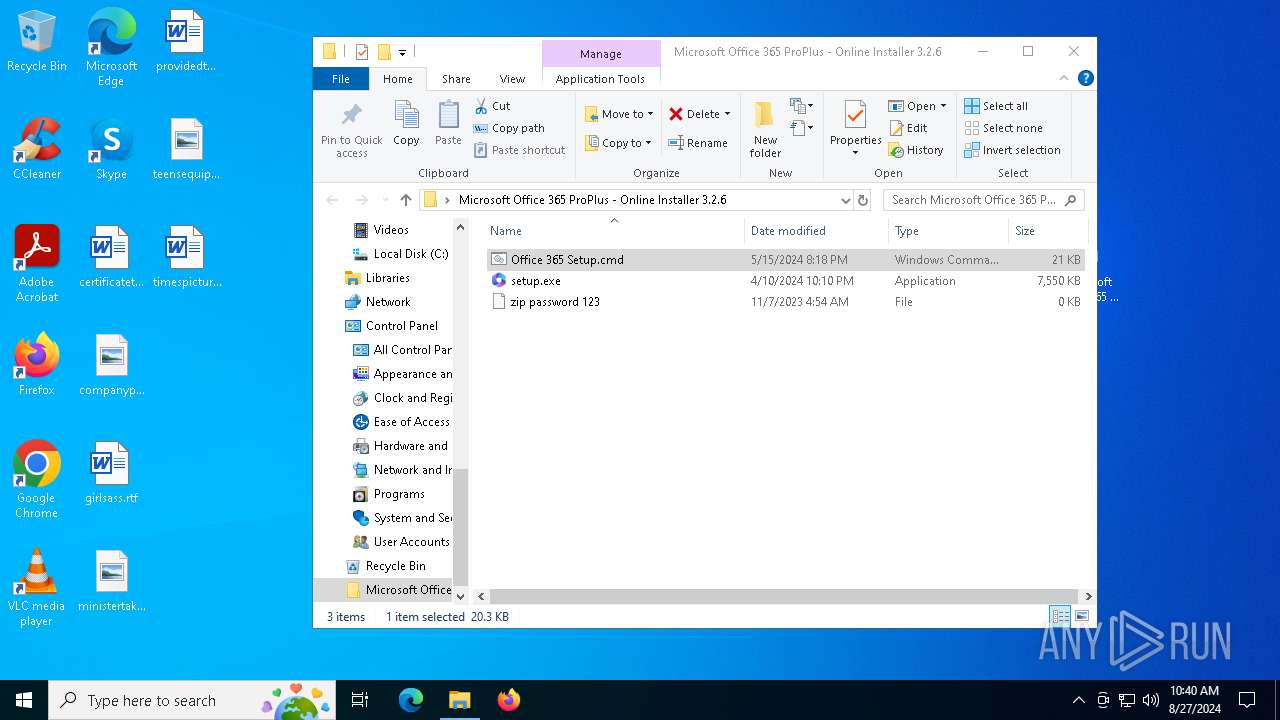
Executing commands from ".cmd" file
- powershell.exe (PID: 3332)
- powershell.exe (PID: 6260)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3332)
- cmd.exe (PID: 6568)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 6016)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 320)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 376)
- cmd.exe (PID: 888)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 188)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 4392)
- powershell.exe (PID: 6260)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 376)
- cmd.exe (PID: 5816)
- cmd.exe (PID: 6052)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 1776)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 6580)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 5548)
Application launched itself
- cmd.exe (PID: 6568)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 320)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 6016)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 376)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 888)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 188)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 4392)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 376)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5816)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 1776)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 6052)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 6580)
- cmd.exe (PID: 2640)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4576)
- cmd.exe (PID: 6780)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4576)
- cmd.exe (PID: 6780)
Starts a Microsoft application from unusual location
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Reads security settings of Internet Explorer
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Checks Windows Trust Settings
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Searches for installed software
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Executable content was dropped or overwritten
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
Drops the executable file immediately after the start
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
The process drops C-runtime libraries
- OfficeClickToRun.exe (PID: 3112)
INFO
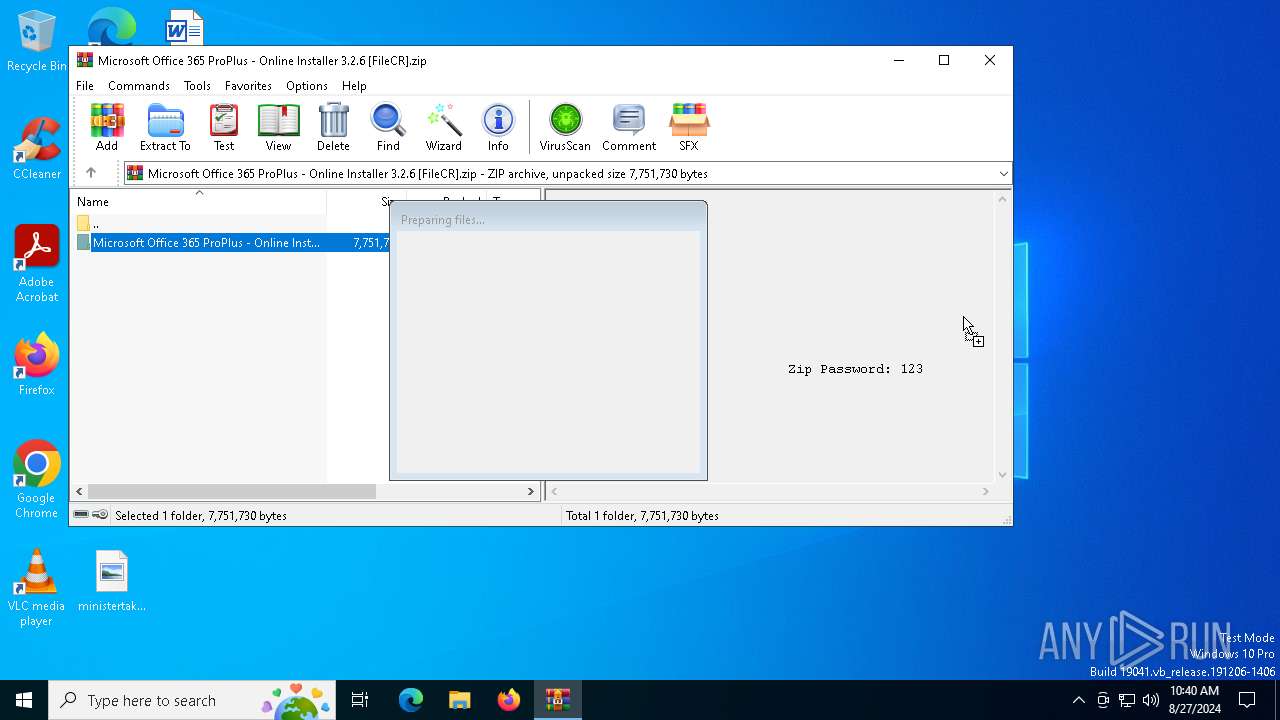
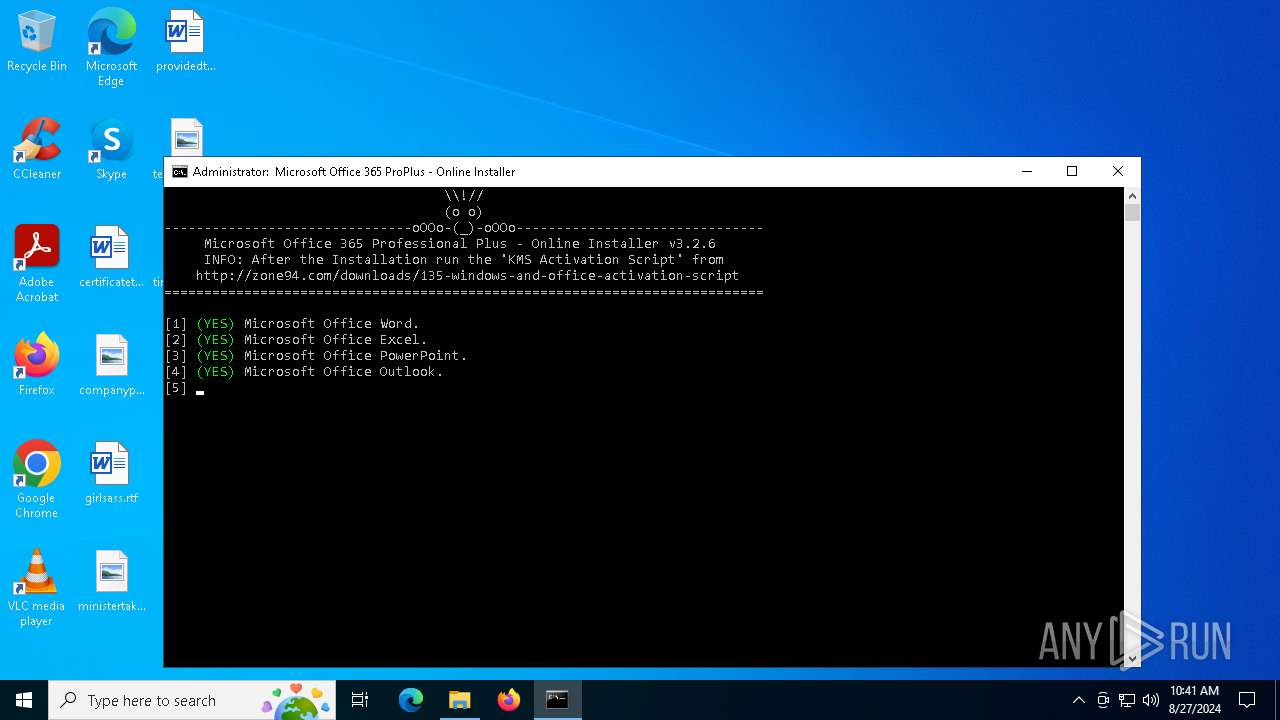
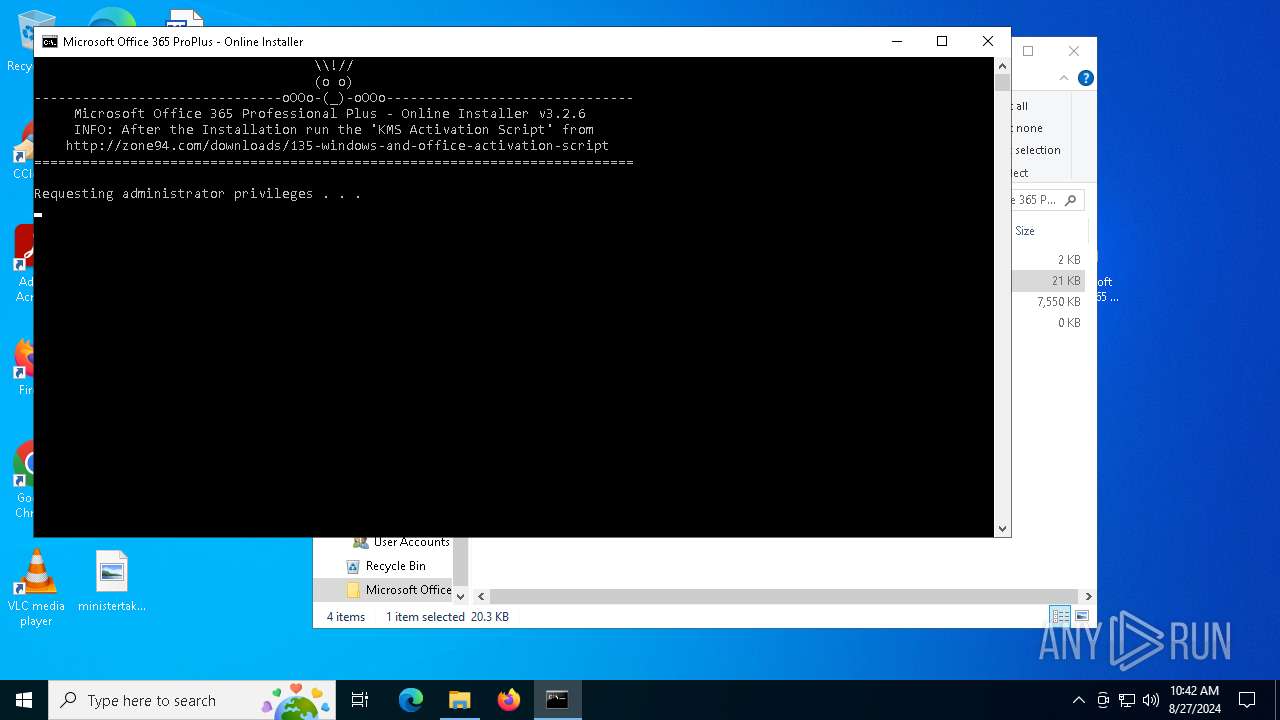
Manual execution by a user
- cmd.exe (PID: 2040)
- cmd.exe (PID: 2768)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6152)
Changes the display of characters in the console
- chcp.com (PID: 2576)
- chcp.com (PID: 1020)
- chcp.com (PID: 2904)
- chcp.com (PID: 6240)
Checks supported languages
- chcp.com (PID: 2576)
- chcp.com (PID: 1020)
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
- OfficeClickToRun.exe (PID: 3304)
- chcp.com (PID: 6240)
- chcp.com (PID: 2904)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Reads Microsoft Office registry keys
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
- OfficeClickToRun.exe (PID: 3304)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Reads the software policy settings
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 3304)
- OfficeClickToRun.exe (PID: 6132)
- setup.exe (PID: 5988)
Process checks computer location settings
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Checks proxy server information
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
- OfficeClickToRun.exe (PID: 3304)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Create files in a temporary directory
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 3304)
- OfficeClickToRun.exe (PID: 6132)
- setup.exe (PID: 5988)
Creates files or folders in the user directory
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 3304)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Reads Environment values
- setup.exe (PID: 1568)
- setup.exe (PID: 5988)
Reads the machine GUID from the registry
- OfficeClickToRun.exe (PID: 3112)
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 5524)
- OfficeClickToRun.exe (PID: 3304)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Reads the computer name
- setup.exe (PID: 1568)
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
- OfficeClickToRun.exe (PID: 3304)
- setup.exe (PID: 5988)
- OfficeClickToRun.exe (PID: 6132)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 5524)
Creates files in the program directory
- OfficeClickToRun.exe (PID: 3112)
- OfficeClickToRun.exe (PID: 5524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:05:16 11:27:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft Office 365 ProPlus - Online Installer 3.2.6/ |
Total processes
574
Monitored processes
447
Malicious processes
10
Suspicious processes
92
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\system32\cmd.exe /S /D /c" Echo PROMPT $H " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 32 | C:\WINDOWS\system32\cmd.exe /S /D /c" Echo PROMPT $H " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\system32\cmd.exe /c Echo PROMPT $H | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | FindStr /l /i /b /p /a:0a /s /c:"_" ""(YES)"" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | C:\WINDOWS\system32\cmd.exe /c Echo PROMPT $H | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | C:\WINDOWS\system32\cmd.exe /S /D /c" Echo PROMPT $H " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | C:\WINDOWS\system32\cmd.exe /S /D /c" Echo PROMPT $H " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | C:\WINDOWS\system32\cmd.exe /c Echo PROMPT $H | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
62 384
Read events
61 577
Write events
458
Delete events
349
Modification events
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft Office 365 ProPlus - Online Installer 3.2.6 [FileCR].zip | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
392
Suspicious files
138
Text files
76
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4576 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_(32-bit)\(32-bit) | binary | |
MD5:B14A7B8059D9C055954C92674CE60032 | SHA256:— | |||
| 4576 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_(YES)\(YES) | binary | |
MD5:B14A7B8059D9C055954C92674CE60032 | SHA256:— | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rawk2ylm.dj2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pcoumqea.bm1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
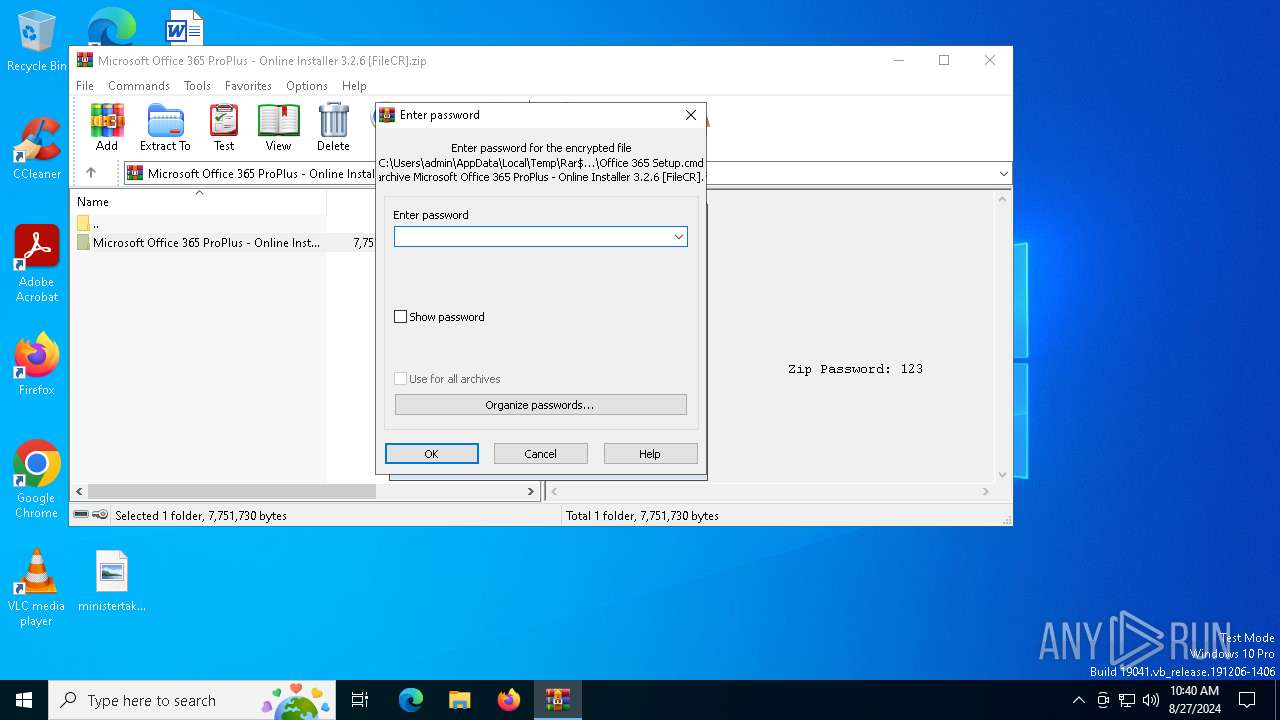
| 6152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6152.5487\Microsoft Office 365 ProPlus - Online Installer 3.2.6\setup.exe | executable | |
MD5:7488D696F9A3D74E093B4C31EF7282C6 | SHA256:B03C4CC3C1377EE81B1F94DA126E58A30F484D4D935889538FAE1C650DD6828B | |||
| 4576 | cmd.exe | C:\Users\admin\Desktop\Microsoft Office 365 ProPlus - Online Installer 3.2.6\Office 365 Setup Config.xml | text | |
MD5:78F4E24C56550AB2621EE652849786E6 | SHA256:A77144AA552B42F5C843FEC95EDB9629E90DB2797897DA1DC27B67918D3D8AA6 | |||
| 1568 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RD7B392F9-8D56-4307-8893-459BF275833EOfficeC2R25E7EF84-CB16-4122-AE1C-7F4948198AC6\v64.hash | text | |
MD5:C3A09920865CD6D77D272EB642C29316 | SHA256:49232E0AAEC5F37F784258E24FB7C1B188633E6013DE0118233A4BFD4DB23BD7 | |||
| 1568 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\17278173-FD18-4BEE-8D7E-ABE32809C51F | xml | |
MD5:CB6BF6E021C786939C1E0E619E3DEDE1 | SHA256:4859ED3A01641AFCF685CAD9E30DC2C9FFDD578545751E9DCEFE6A08B5C8426B | |||
| 1568 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-journal | binary | |
MD5:4F9CB033EDC9D8CD689E7018F1D59E15 | SHA256:5AAE78AF578C0C16E8E68EF479055CBE0A8EF282FFFBE53422EF5CD5F591862B | |||
| 6152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6152.5487\Microsoft Office 365 ProPlus - Online Installer 3.2.6\Office 365 Setup.cmd | text | |
MD5:C3BFBAAB698A4F4C6A77F54BBE30ACA7 | SHA256:88843969A25D7E8F1E54EC565DA655CD1ABF328677F52F0B3357E09E91C9EE37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
119
TCP/UDP connections
44
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6112 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3784 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1568 | setup.exe | HEAD | 200 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.17928.20114.cab | unknown | — | — | whitelisted |
1568 | setup.exe | HEAD | 200 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.16026.20146.cab | unknown | — | — | whitelisted |
240 | svchost.exe | HEAD | 200 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.17928.20114.cab | unknown | — | — | whitelisted |
240 | svchost.exe | GET | 206 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.17928.20114.cab | unknown | — | — | whitelisted |
1568 | setup.exe | HEAD | 200 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.17928.20114.cab | unknown | — | — | whitelisted |
3784 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
240 | svchost.exe | HEAD | 200 | 163.177.116.4:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.17928.20114.cab | unknown | — | — | whitelisted |
1568 | setup.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6612 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6776 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6112 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6112 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |