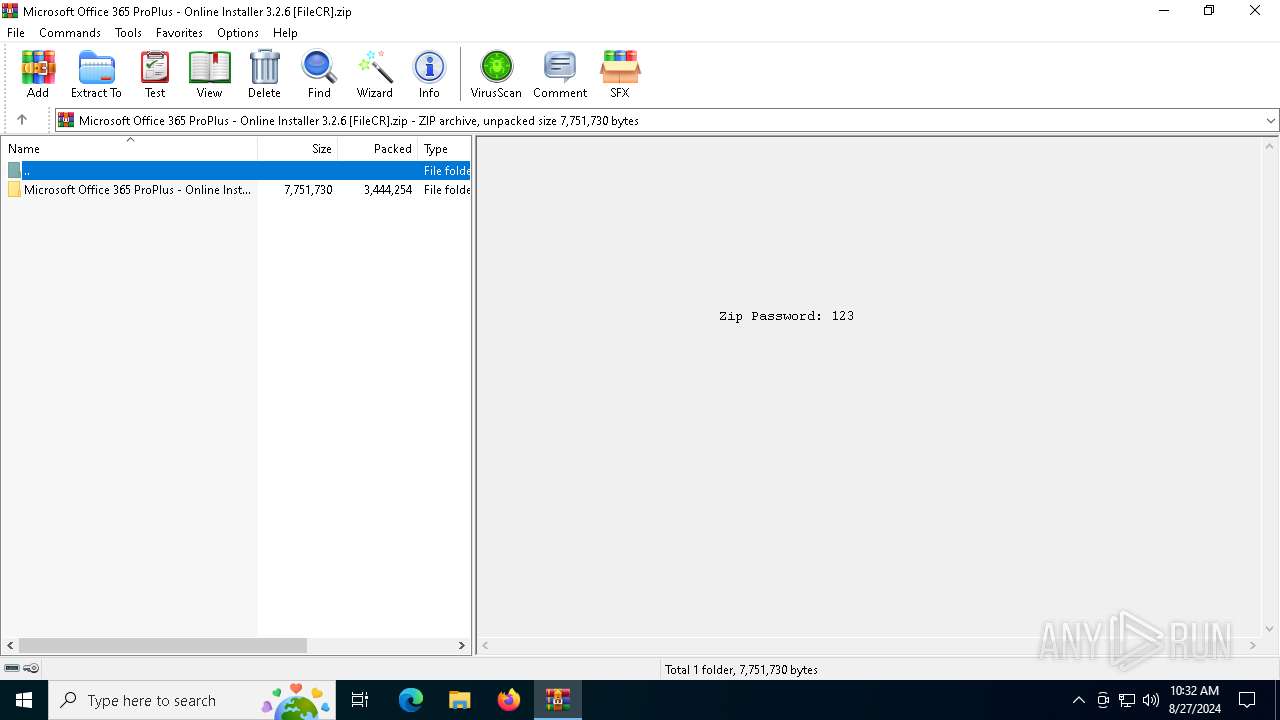
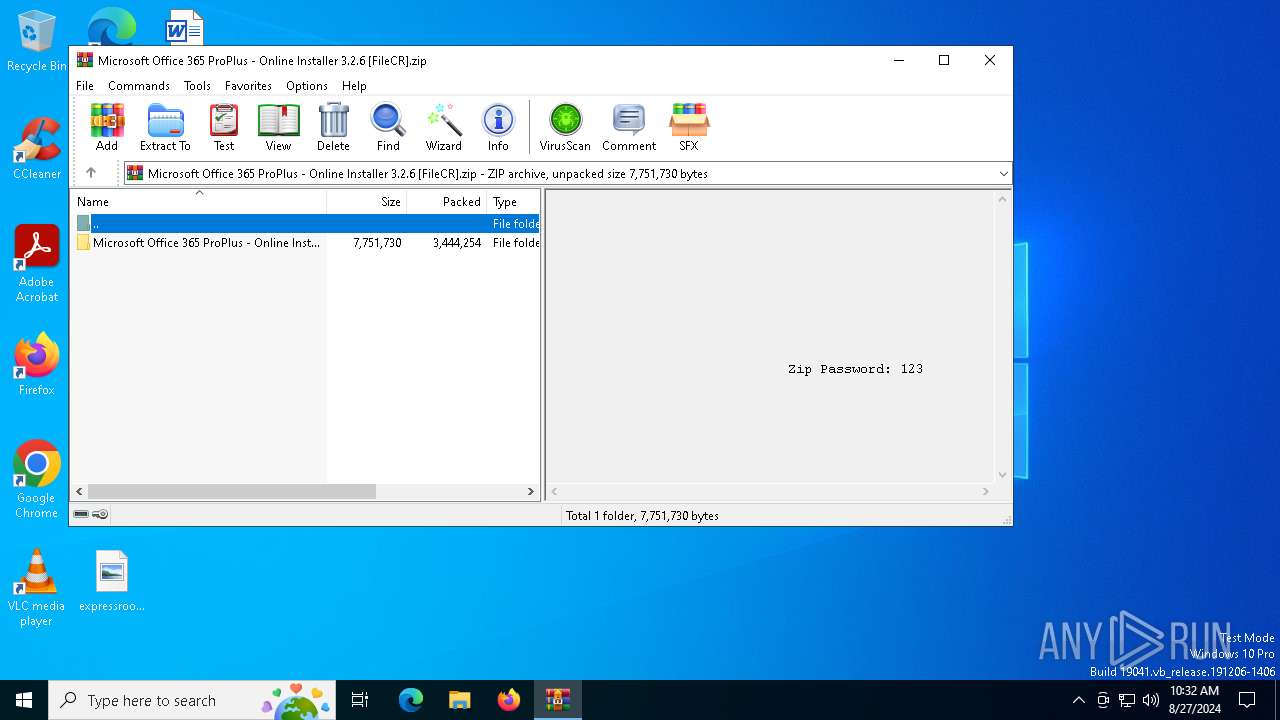
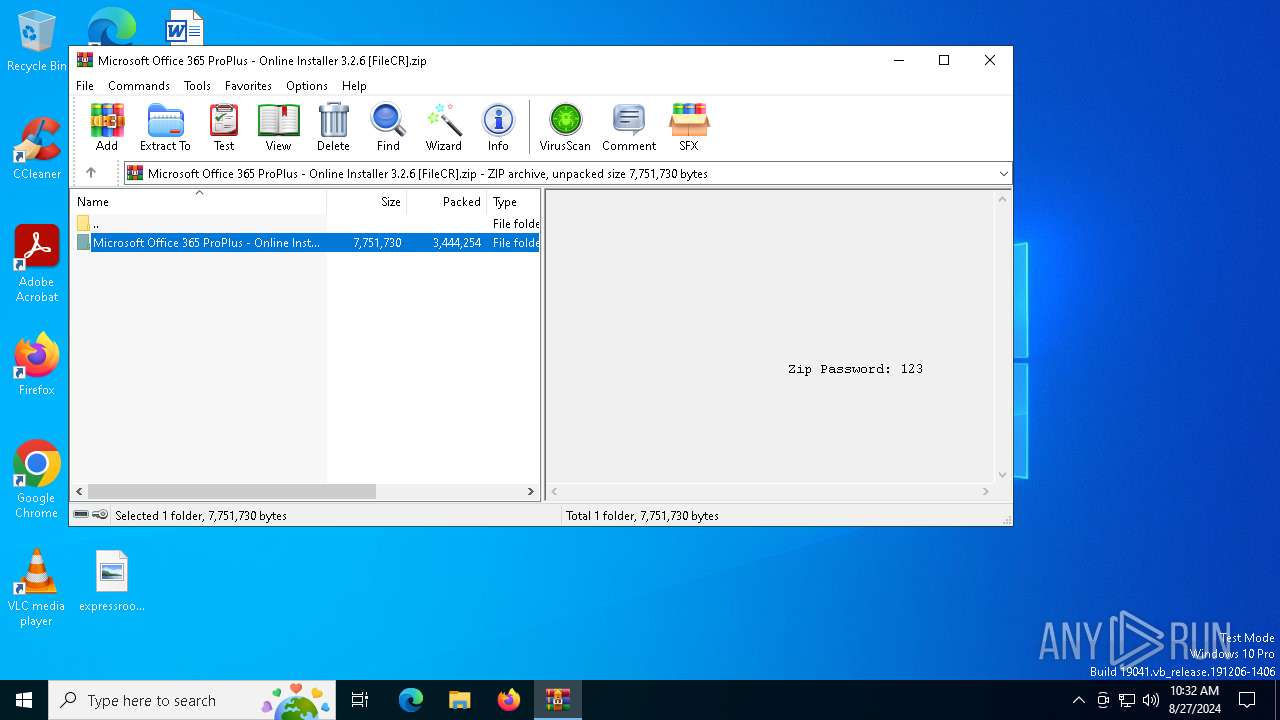
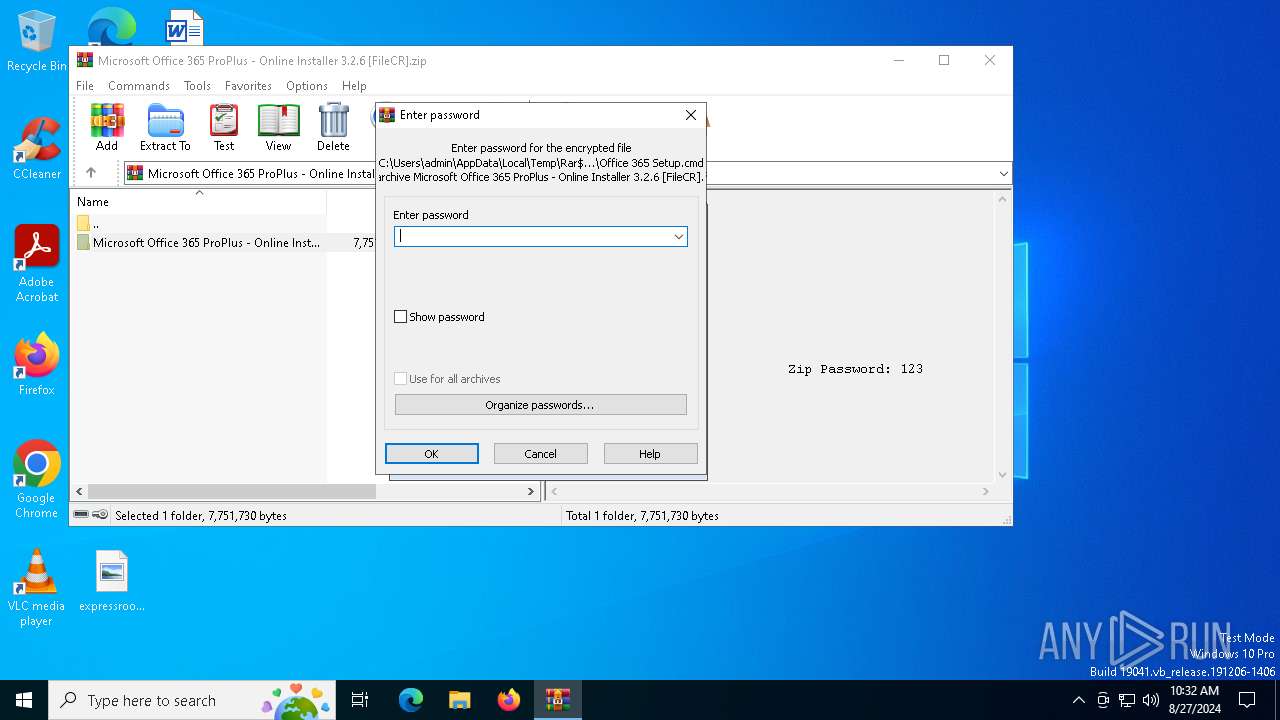
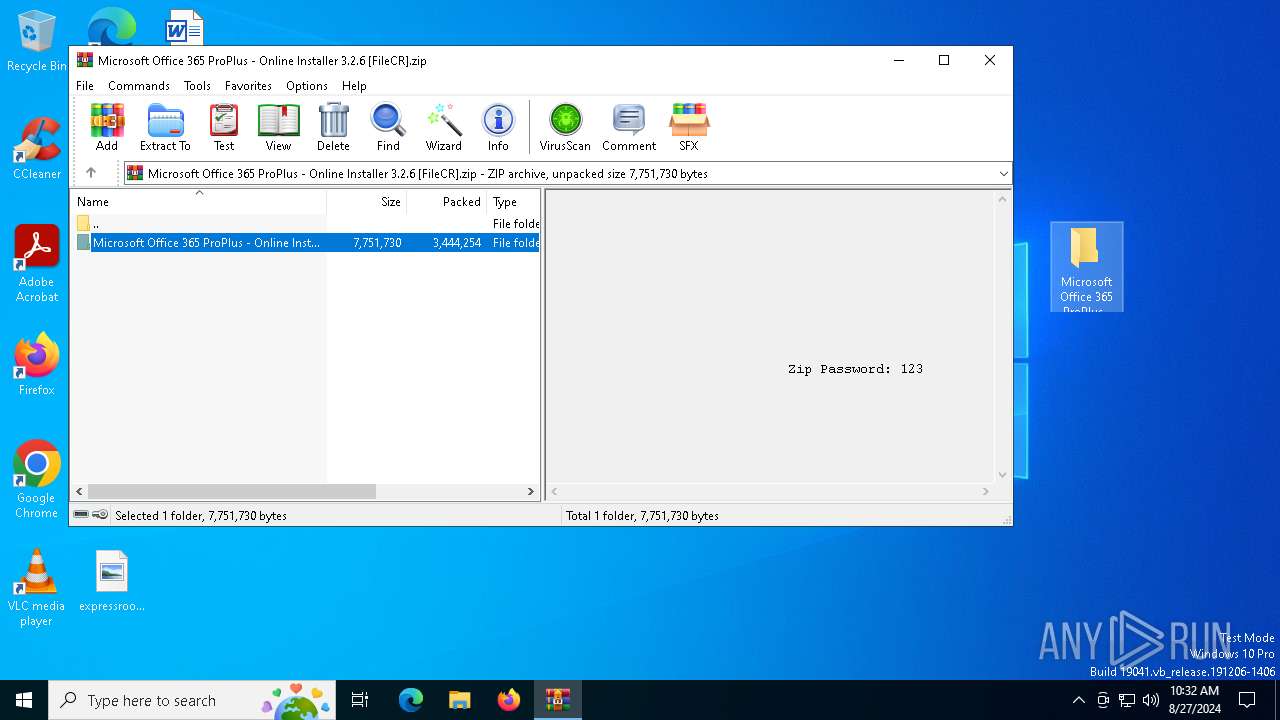
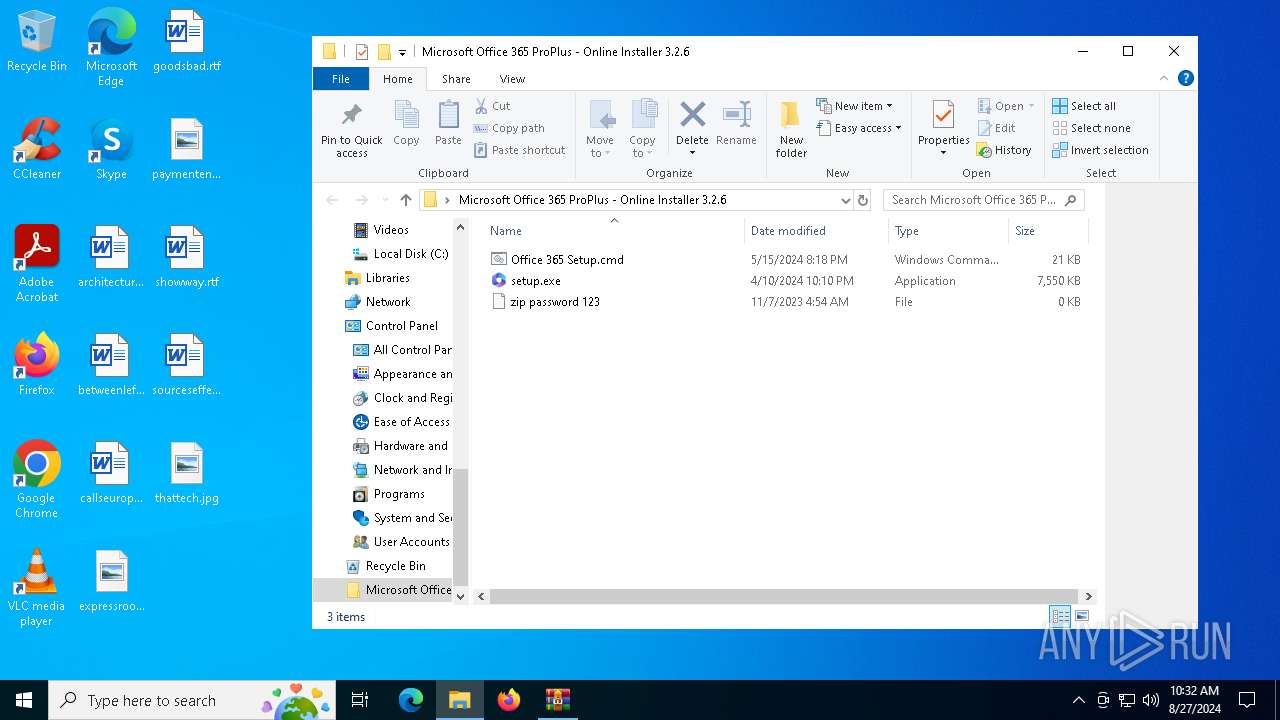
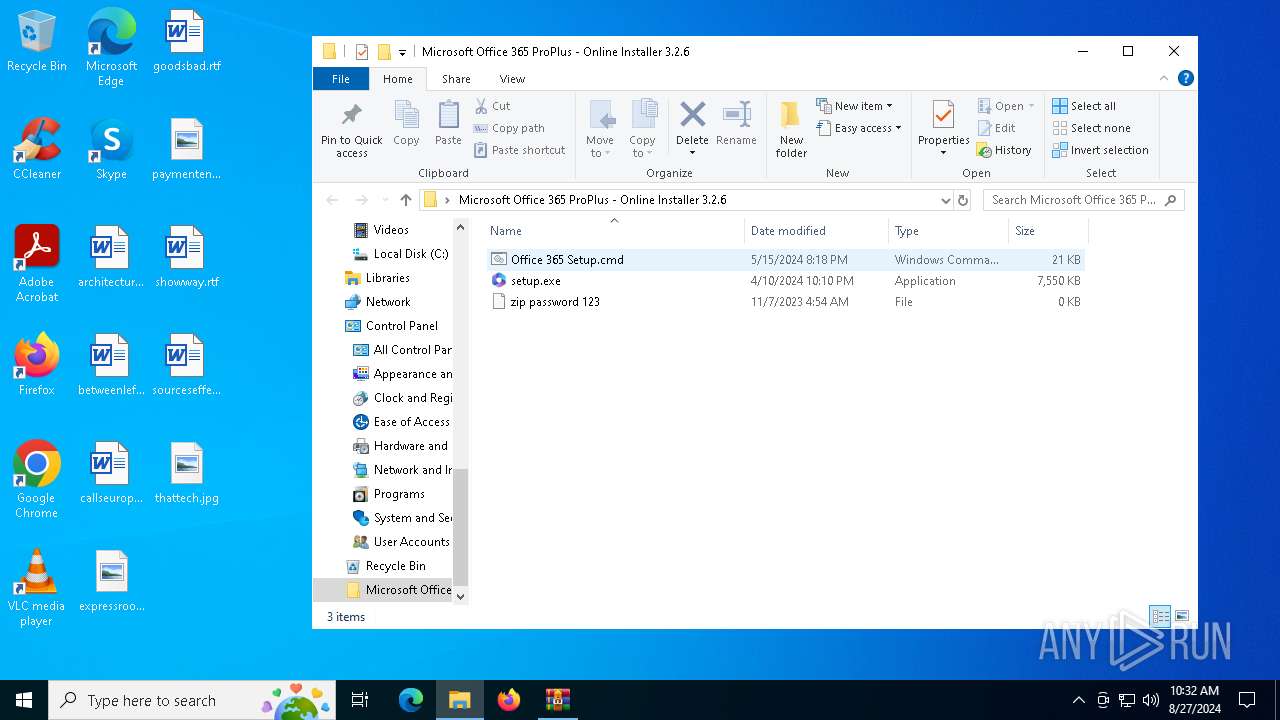
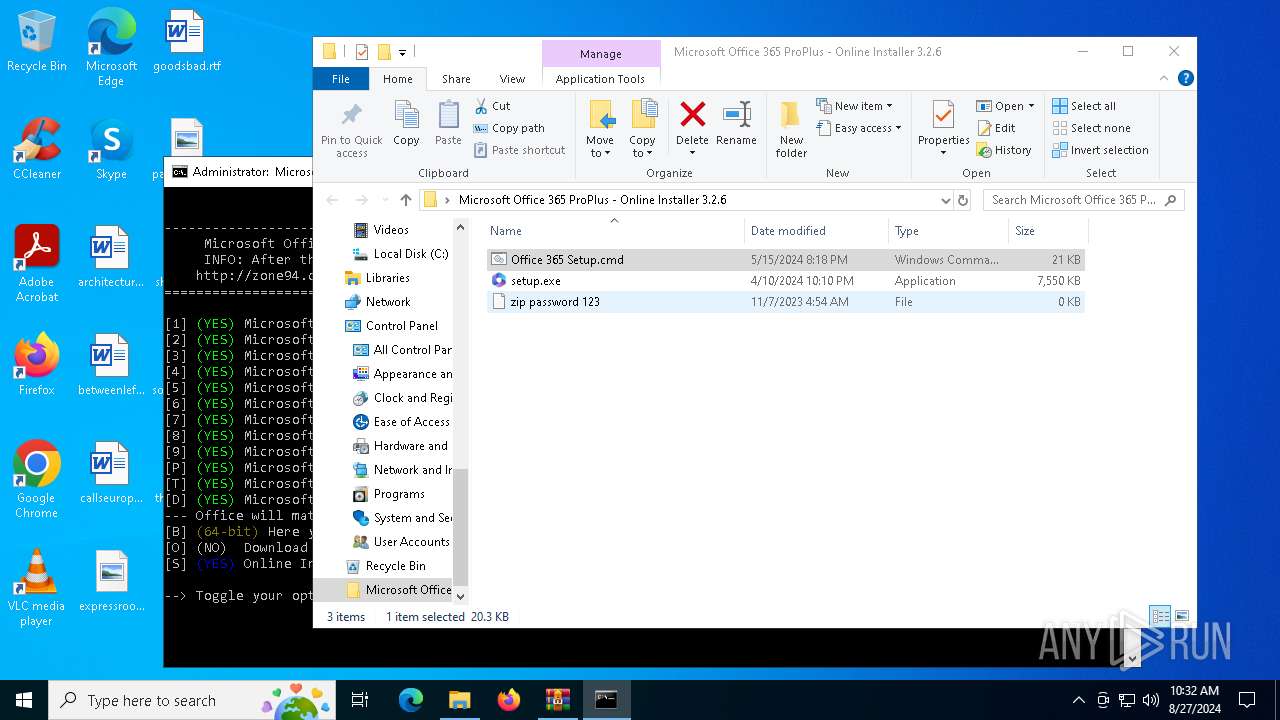
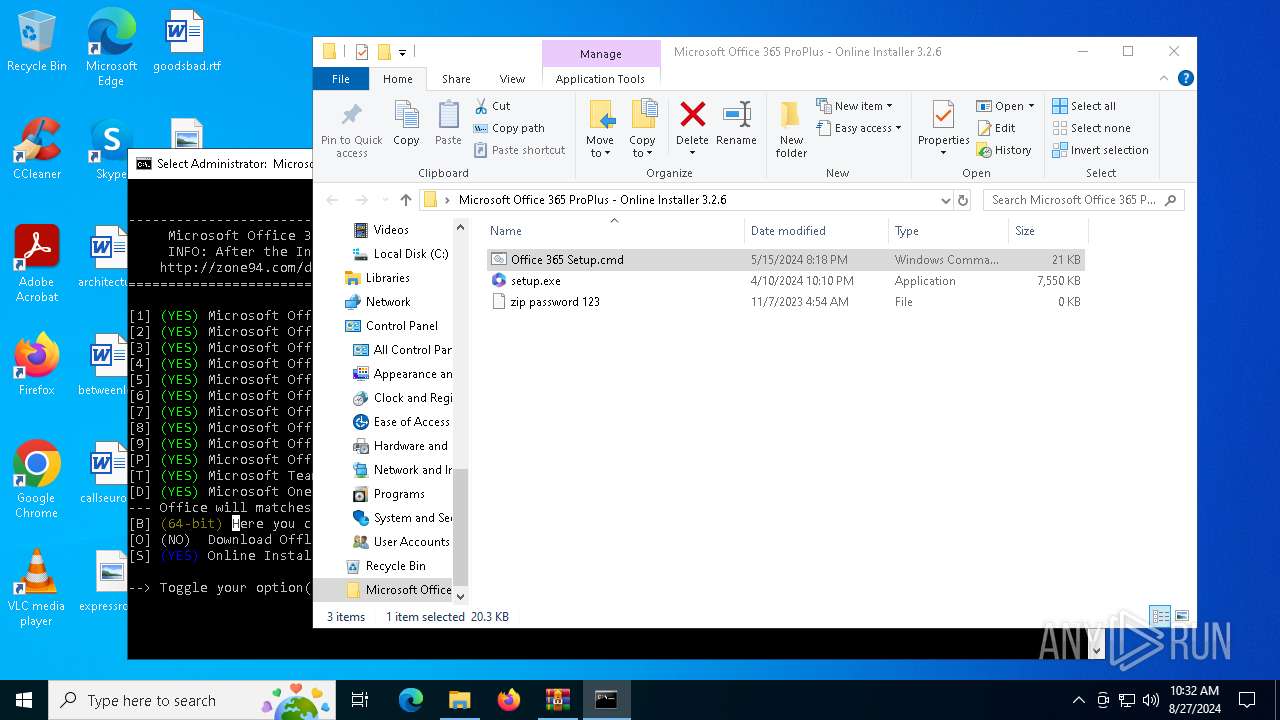
| File name: | Microsoft Office 365 ProPlus - Online Installer 3.2.6 [FileCR].zip |
| Full analysis: | https://app.any.run/tasks/03f82328-fa65-4cdf-ad77-ecd085ddecdb |
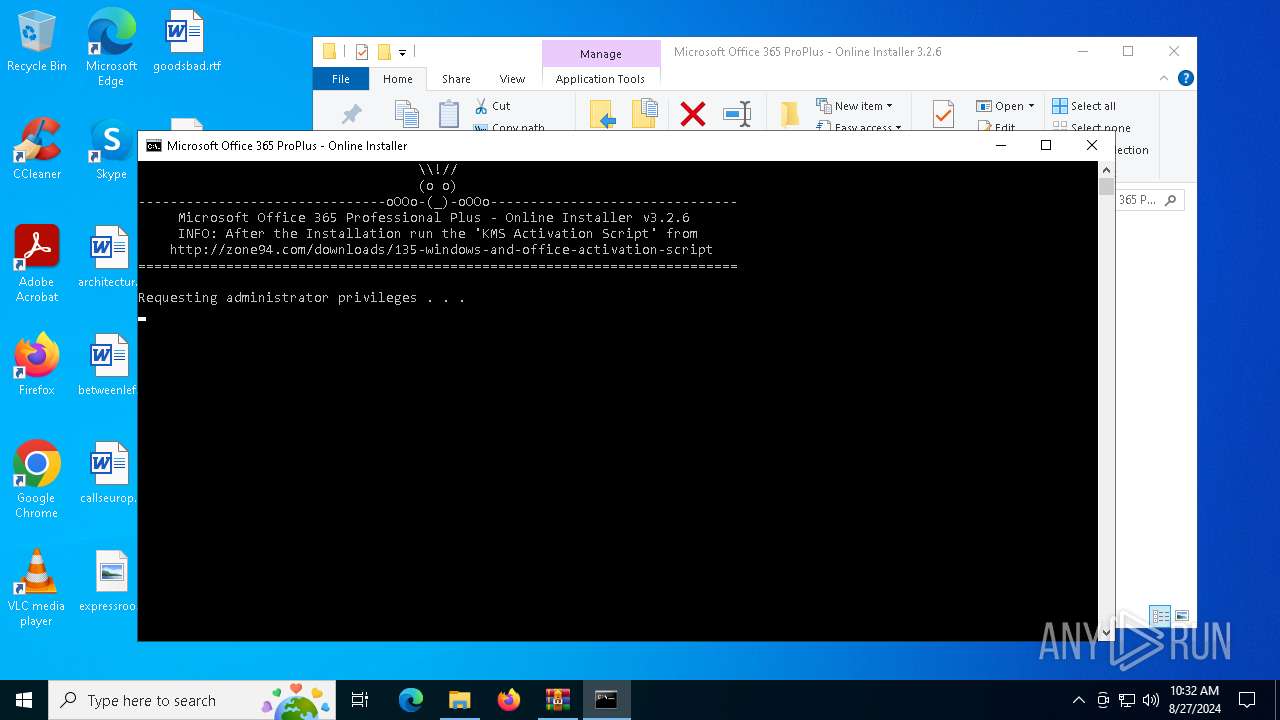
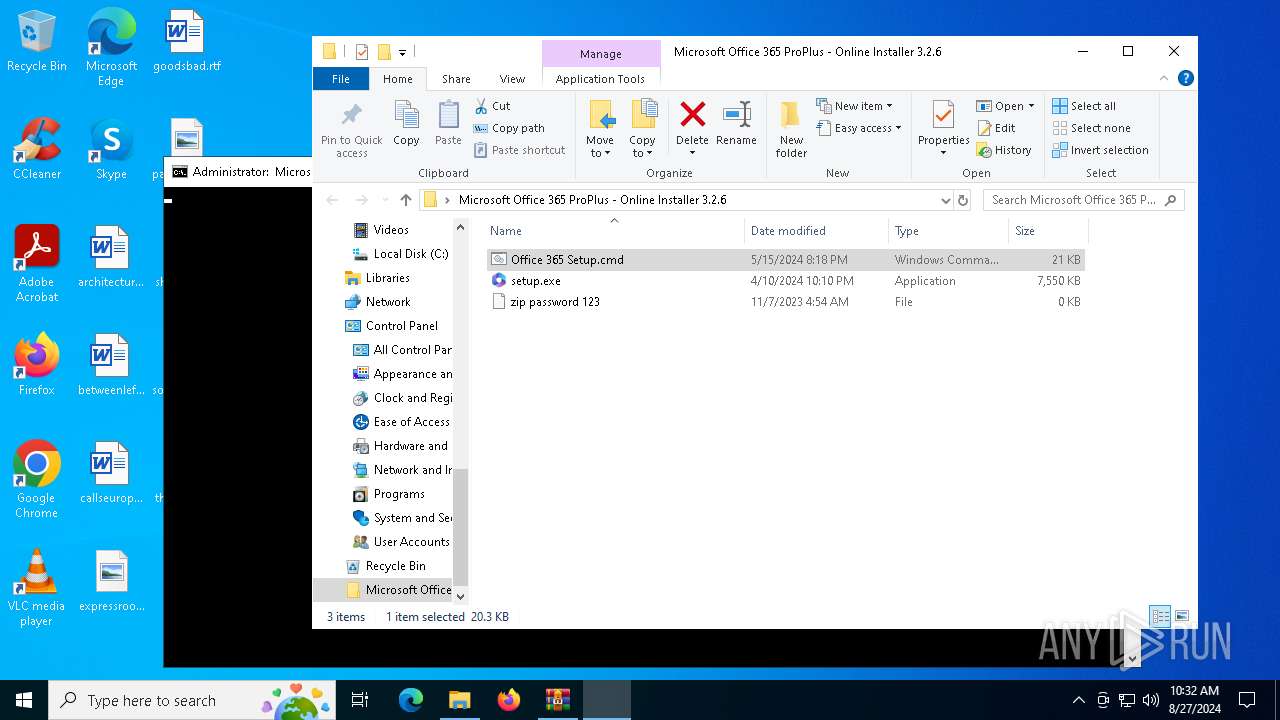
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2024, 10:32:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | A7A3607691E597A7940DE9580BB2EBE2 |
| SHA1: | 48EB3F31FB5055C3FCBA6819CBC40B537051A98E |
| SHA256: | 16E9F7231C4ED888FC2C374E1D40FBC3C97544EB5665750B8FC2581C4844804C |
| SSDEEP: | 98304:kTnXTeGs148KCDwE4Qwv9lXuu6/AHjEuCYQbKb4xGIrHg0ieY2n8nLDsiWONbEdK:1p7sVr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6556)
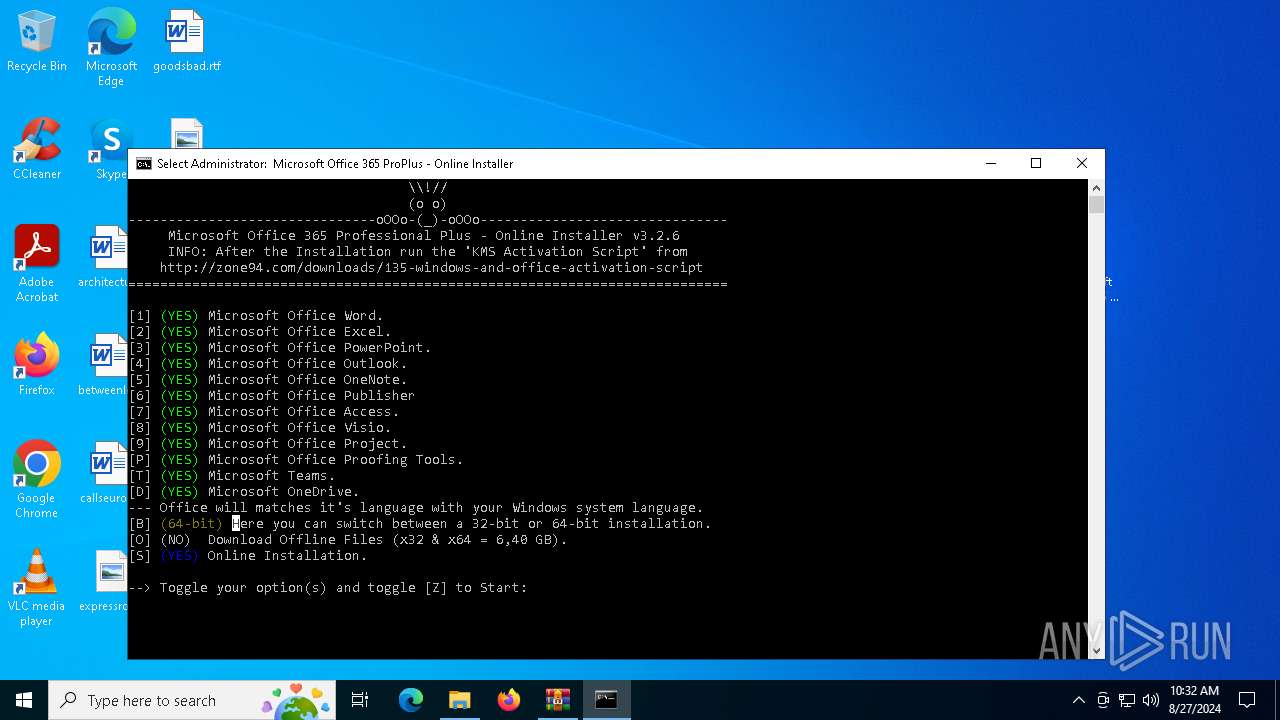
Starts application with an unusual extension
- cmd.exe (PID: 2588)
- cmd.exe (PID: 5284)
Executing commands from ".cmd" file
- powershell.exe (PID: 5372)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5372)
- cmd.exe (PID: 5284)
- cmd.exe (PID: 5140)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 936)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 780)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2588)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2588)
Application launched itself
- cmd.exe (PID: 5284)
- cmd.exe (PID: 5140)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 936)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 780)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5284)
INFO
Manual execution by a user
- cmd.exe (PID: 2588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6556)
Checks supported languages
- chcp.com (PID: 6140)
- chcp.com (PID: 6176)
Changes the display of characters in the console
- chcp.com (PID: 6140)
- chcp.com (PID: 6176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:05:16 11:27:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft Office 365 ProPlus - Online Installer 3.2.6/ |
Total processes
197
Monitored processes
69
Malicious processes
3
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\cmd.exe /S /D /c" Echo PROMPT $H " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | FindStr /l /i /b /p /a:0a /s /c:"_" ""(YES)"" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | FindStr /l /i /b /p /a:0a /s /c:"_" ""(YES)"" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\system32\cmd.exe /c Echo PROMPT $H | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\cmd.exe /c Echo PROMPT $H | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "CMD" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | FindStr /l /i /b /p /a:0a /s /c:"_" ""(YES)"" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 161
Read events
12 144
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft Office 365 ProPlus - Online Installer 3.2.6 [FileCR].zip | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5372) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
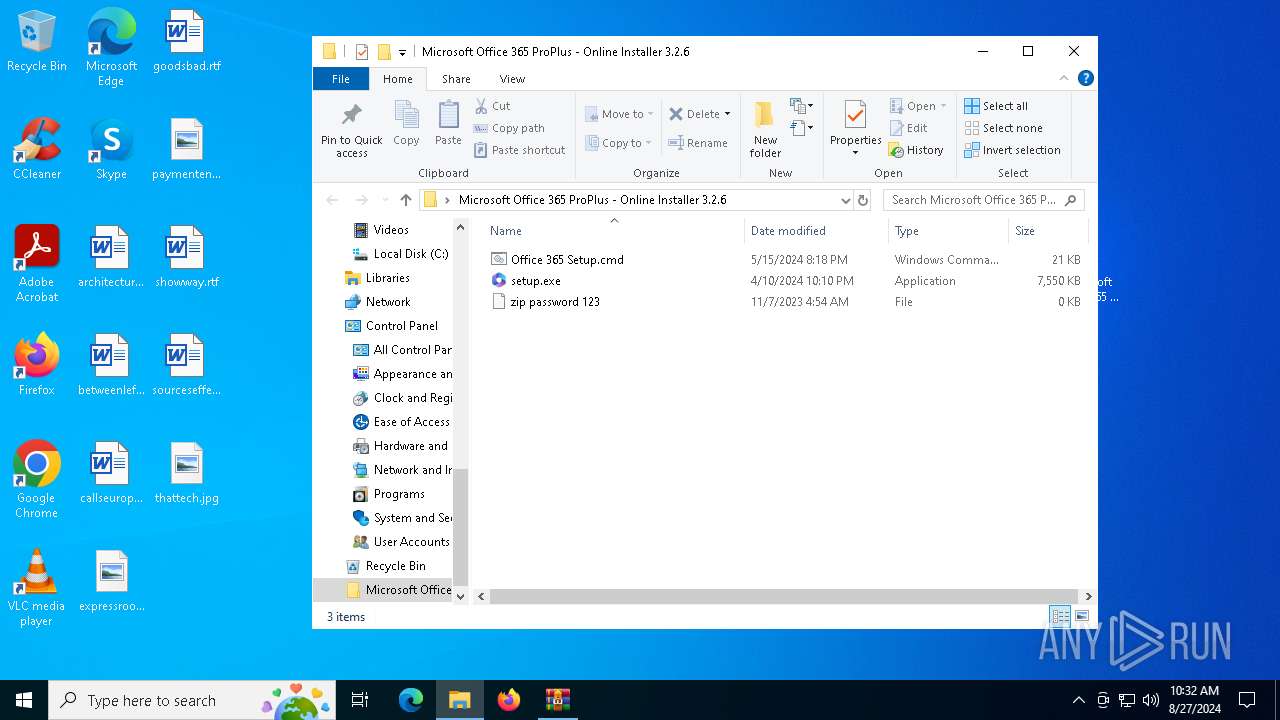
Executable files
1
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6556.5180\Microsoft Office 365 ProPlus - Online Installer 3.2.6\Office 365 Setup.cmd | text | |
MD5:C3BFBAAB698A4F4C6A77F54BBE30ACA7 | SHA256:88843969A25D7E8F1E54EC565DA655CD1ABF328677F52F0B3357E09E91C9EE37 | |||
| 5372 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F16D0F1AA35497ACADF047379343D534 | SHA256:CE6E6A789323078D2A866AEDD98FA389DCE24B1473FA7AC47227B4CF12965C37 | |||
| 5372 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5vb3rrw5.yzl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5372 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ujich0s2.fwf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5284 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_(YES)\(YES) | binary | |
MD5:B14A7B8059D9C055954C92674CE60032 | SHA256:— | |||
| 5284 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_(64-bit)\(64-bit) | binary | |
MD5:B14A7B8059D9C055954C92674CE60032 | SHA256:— | |||
| 6556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6556.5180\Microsoft Office 365 ProPlus - Online Installer 3.2.6\setup.exe | executable | |
MD5:7488D696F9A3D74E093B4C31EF7282C6 | SHA256:B03C4CC3C1377EE81B1F94DA126E58A30F484D4D935889538FAE1C650DD6828B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6112 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6112 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2144 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2144 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3104 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3352 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5644 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3352 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6112 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6112 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2144 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |