| download: | GWSetup.exe |
| Full analysis: | https://app.any.run/tasks/01ea2832-8a12-4c82-816b-23b9f1f492f1 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2019, 12:45:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | DA5CAFC3825FA9582CC0C2E2B9CD155C |
| SHA1: | 5EE54C27F73315593AA2EBB683462ACA1BBA45E5 |
| SHA256: | 16E45CA2059C5D02015F9F37F53D02492AE64F8E8B0875D4696836C21BFC8C17 |
| SSDEEP: | 98304:ySZHKSlISIpJ53Zo848+X+fcrBZCluuVJ8:EnSeJc0+NBoluuc |
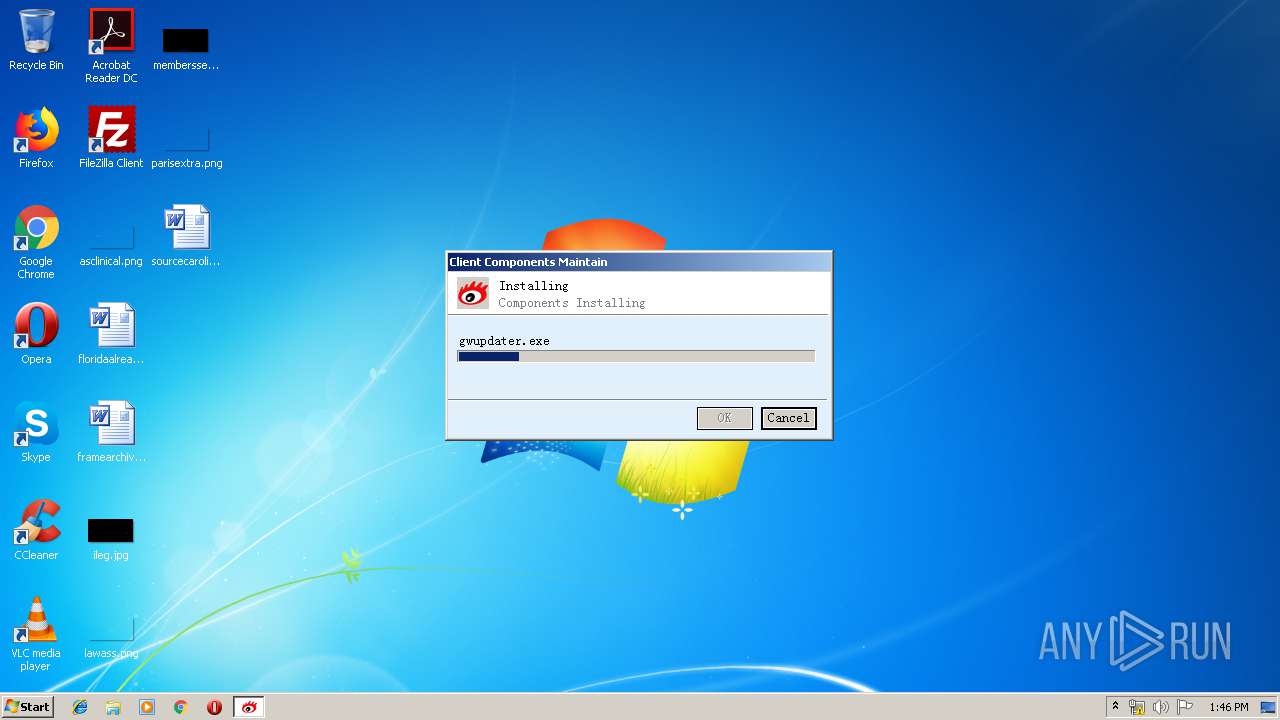
MALICIOUS
Application was dropped or rewritten from another process
- gwupdater.exe (PID: 3376)
- gwservice.exe (PID: 1240)
Loads dropped or rewritten executable
- GWSetup.exe (PID: 2536)
- gwservice.exe (PID: 1240)
SUSPICIOUS
Creates files in the program directory
- GWSetup.exe (PID: 2536)
Executed as Windows Service
- gwupdater.exe (PID: 3376)
- gwservice.exe (PID: 1240)
Creates COM task schedule object
- GWSetup.exe (PID: 2536)
Creates a software uninstall entry
- GWSetup.exe (PID: 2536)
Executable content was dropped or overwritten
- GWSetup.exe (PID: 2536)
Creates or modifies windows services
- GWSetup.exe (PID: 2536)
Low-level read access rights to disk partition
- gwservice.exe (PID: 1240)
INFO
Dropped object may contain Bitcoin addresses
- GWSetup.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:06 04:51:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 17408 |
| InitializedDataSize: | 27136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.1.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GWSetup |
| FileVersion: | 0, 0, 1, 0 |
| InternalName: | GWSetup |
| LegalCopyright: | Copyright 2011 |
| LegalTrademarks: | - |
| OriginalFileName: | SetupStub.exe |
| PrivateBuild: | - |
| ProductName: | - |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Sep-2018 02:51:27 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GWSetup |
| FileVersion: | 0, 0, 1, 0 |
| InternalName: | GWSetup |
| LegalCopyright: | Copyright 2011 |
| LegalTrademarks: | - |
| OriginalFilename: | SetupStub.exe |
| PrivateBuild: | - |
| ProductName: | - |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 06-Sep-2018 02:51:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000439A | 0x00004400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51342 |
.rdata | 0x00006000 | 0x00000BC0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.83472 |
.data | 0x00007000 | 0x00001D00 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.45501 |
.rsrc | 0x00009000 | 0x00003F38 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.27749 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.29437 | 768 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 3.29663 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.68803 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
102 | 2.45849 | 48 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCRT.dll |
SETUPAPI.dll |
SHELL32.dll |
VERSION.dll |
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1240 | "C:\Program Files\Gateway\SSLVPN\gwservice.exe" | C:\Program Files\Gateway\SSLVPN\gwservice.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: gwservice Exit code: 0 Version: 0, 0, 1, 45 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\GWSetup.exe" | C:\Users\admin\AppData\Local\Temp\GWSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GWSetup Exit code: 0 Version: 0, 0, 1, 0 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\AppData\Local\Temp\GWSetup.exe" | C:\Users\admin\AppData\Local\Temp\GWSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GWSetup Exit code: 3221226540 Version: 0, 0, 1, 0 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Gateway\SSLVPN\gwupdater.exe" | C:\Program Files\Gateway\SSLVPN\gwupdater.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: gwservice Exit code: 0 Version: 0, 0, 1, 45 Modules
| |||||||||||||||
Total events
370
Read events
180
Write events
186
Delete events
4
Modification events
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | UpdaterFlag |
Value: 0 | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Gateway\SSLVPN | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | InstallPath64 |
Value: | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install\Shortcut |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Debug |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Gwieplug.IeAx.1 |
| Operation: | write | Name: | |
Value: IeAx Class | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Gwieplug.IeAx.1\CLSID |
| Operation: | write | Name: | |
Value: {100C2765-1362-4CCF-AB02-56D916BB8732} | |||
| (PID) Process: | (2536) GWSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Gwieplug.IeAx |
| Operation: | write | Name: | |
Value: IeAx Class | |||
Executable files
75
Suspicious files
4
Text files
8
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwupdater.dll.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwclient.exe.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwtrayclient.exe.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\vsdagent.exe.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwupdater.exe.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwservice.exe.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwvnic.sys.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwvnic.sys.64.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwvnic.cat.64.cab | — | |
MD5:— | SHA256:— | |||
| 2536 | GWSetup.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwvnic.inf.cab | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
GWSetup.exe | [06-10 13:46:31][INF][GWUPDLL]DLL_PROCESS_ATTACH
|
gwupdater.exe | [06-10 13:46:32][EMG][GWSERVICE]Loadlibrary 'gwlog.dll' Error(126).
|
gwupdater.exe | [06-10 13:46:32][WAR][GWSERVICE]GWService can't open gwlog.dll.
|
gwupdater.exe | [06-10 13:46:32][WAR][GWSERVICE]CEventDataList(UNNAMED)::Pop() Failed!
|
gwupdater.exe | [06-10 13:46:32][WAR][GWSERVICE]CEventDataList(UNNAMED)::Pop() Failed!
|
GWSetup.exe | [06-10 13:46:35][WAR][GWUPDLL]CreateUnderPrograms(Gateway SSLVPN,Sina VPN,C:\Program Files\Gateway\SSLVPN\gwclient.exe,,%ProgramFiles%\Gateway\SSLVPN\gwclient.exe)
|
GWSetup.exe | [06-10 13:46:35][WAR][GWUPDLL]CreateUnderPrograms(Gateway SSLVPN,File Cabinet,C:\Program Files\Gateway\SSLVPN\gwclient.exe,filecabinet,%ProgramFiles%\Gateway\SSLVPN\gwclient.exe)
|
gwservice.exe | [session]DLL_PROCESS_ATTACH.
|
gwservice.exe | logger config file: C:\Windows\gwlogger.cfg
|
gwservice.exe | Wow64Redirection::disabler>>>>> |