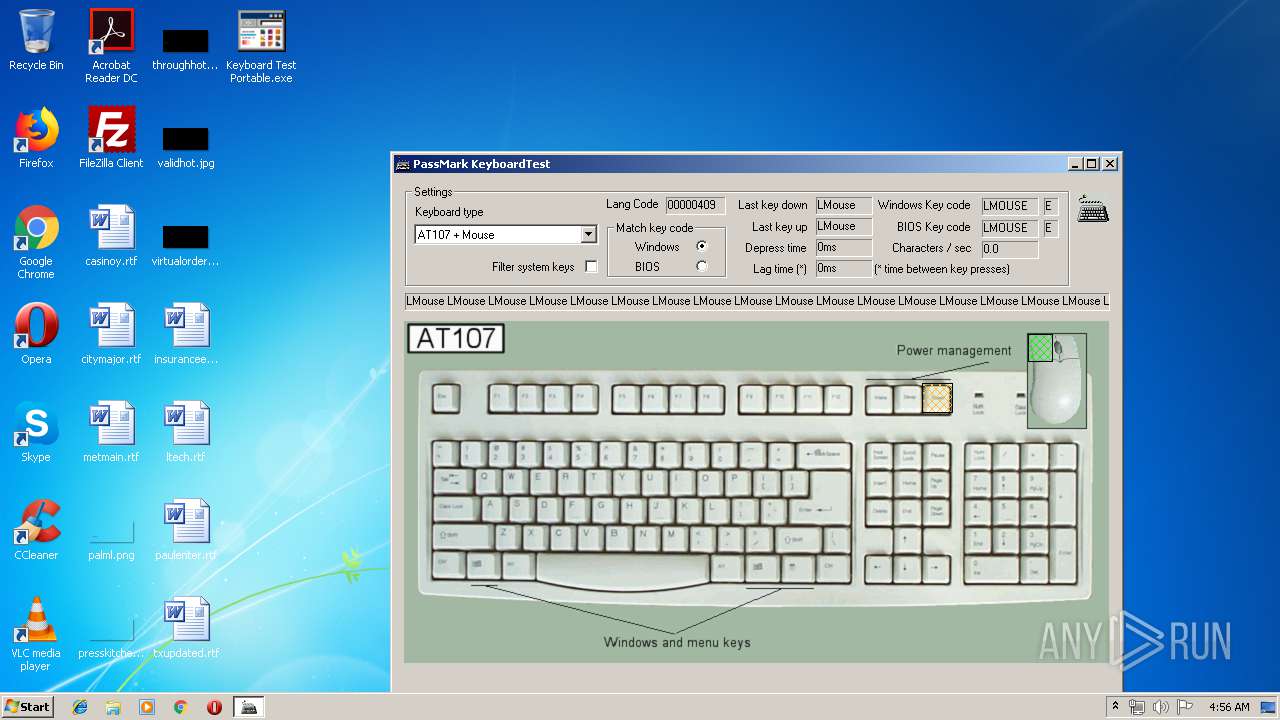
| File name: | Keyboard Test Portable.exe |
| Full analysis: | https://app.any.run/tasks/f03d8ec1-5500-44c5-a849-358d4423227b |
| Verdict: | No threats detected |
| Analysis date: | April 04, 2019, 03:53:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | D9C37EA3A5EA81394BCFBAB1BB299FA7 |
| SHA1: | C8A3678F142DBB0EFB9A7073DE2A6048BC3AF349 |
| SHA256: | 16DD2FB498AAE30261DAA5CCD52039503B1095F2981007555999EA50F3605D76 |
| SSDEEP: | 12288:y27/bTehEqclr0YzQiIVIUFREOIbRpwnLQfCnvpHbMooGHW9mW:yu/PWcx0TIMEOIbRKLdnvpwopW3 |
MALICIOUS
Loads dropped or rewritten executable
- KeyboardTest.exe (PID: 764)
Application was dropped or rewritten from another process
- KeyboardTest.exe (PID: 764)
SUSPICIOUS
Executable content was dropped or overwritten
- Keyboard Test Portable.exe (PID: 640)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:12 11:11:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 67584 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7cb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Dec-2009 10:11:36 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Dec-2009 10:11:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010733 | 0x00010800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57059 |
.rdata | 0x00012000 | 0x00001865 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32963 |
.data | 0x00014000 | 0x0000BFF4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5458 |
.CRT | 0x00020000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.219439 |
.rsrc | 0x00021000 | 0x00003E60 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24403 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 2.02306 | 76 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 1.81924 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | English - United States | RT_BITMAP |
ASKNEXTVOL | 3.42606 | 642 | Latin 1 / Western European | English - United States | RT_DIALOG |
GETPASSWORD1 | 3.33783 | 310 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Users\admin\Desktop\Keyboard Test Portable.exe" | C:\Users\admin\Desktop\Keyboard Test Portable.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
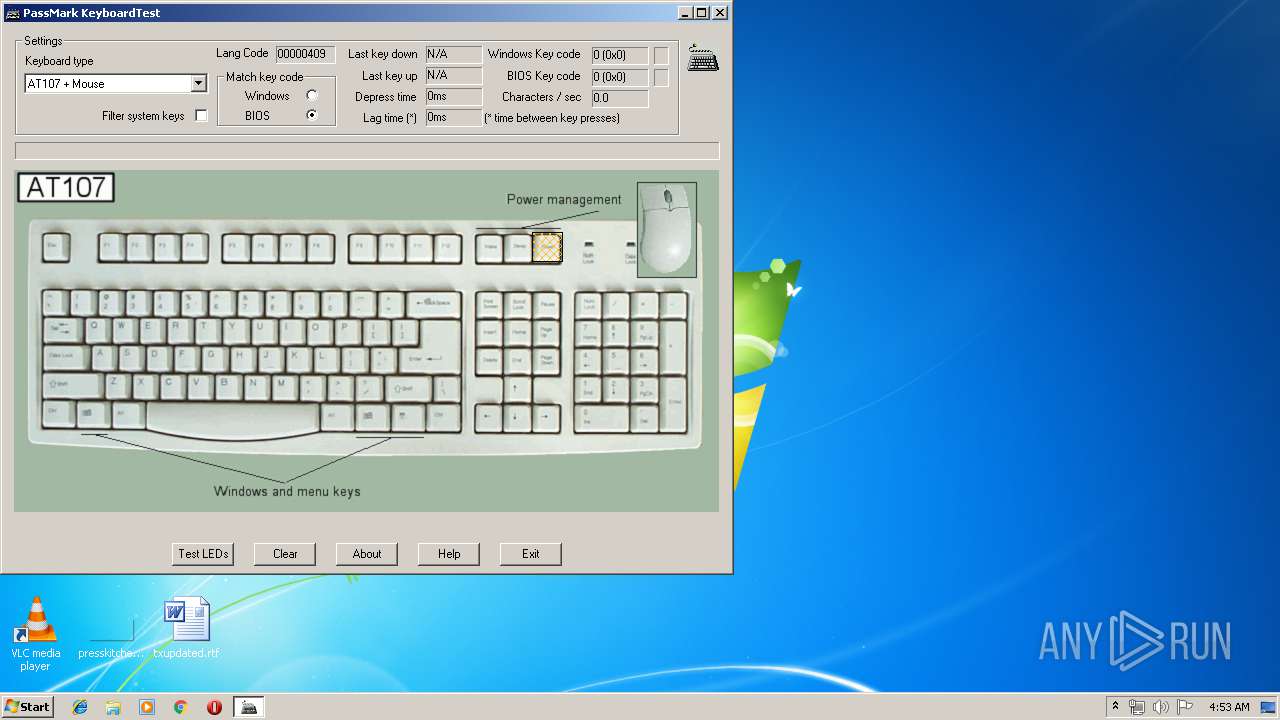
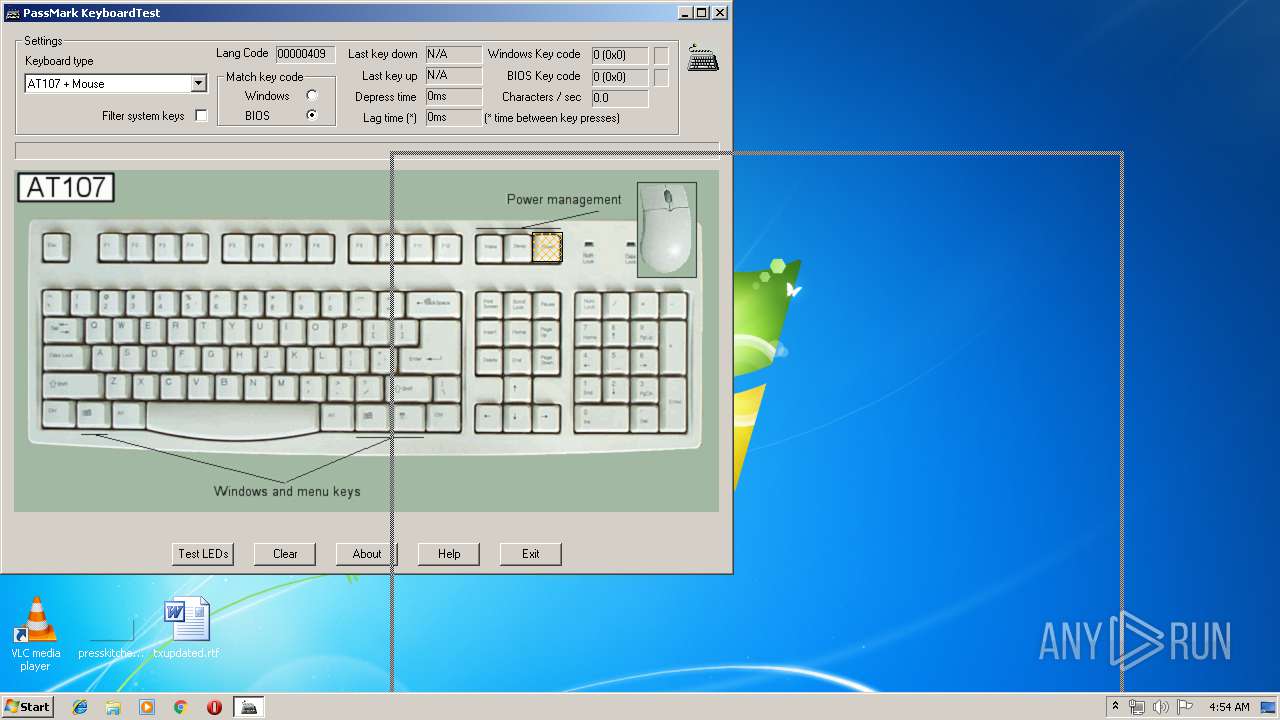
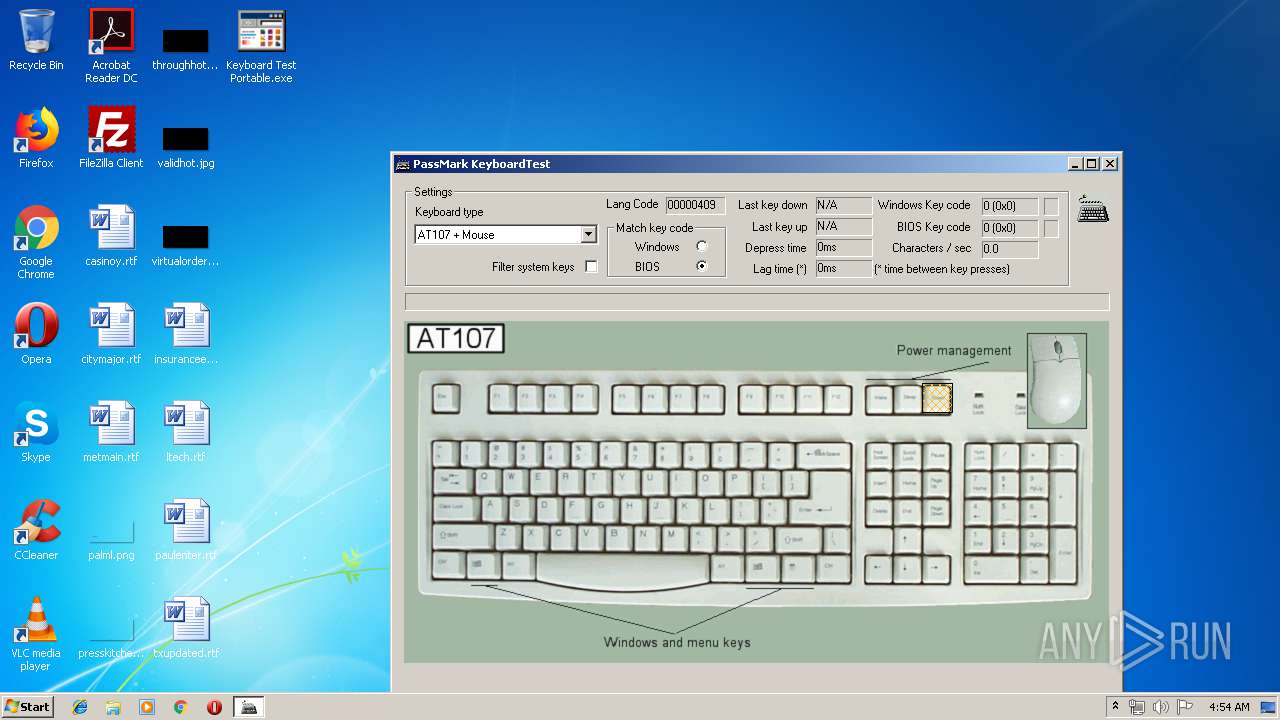
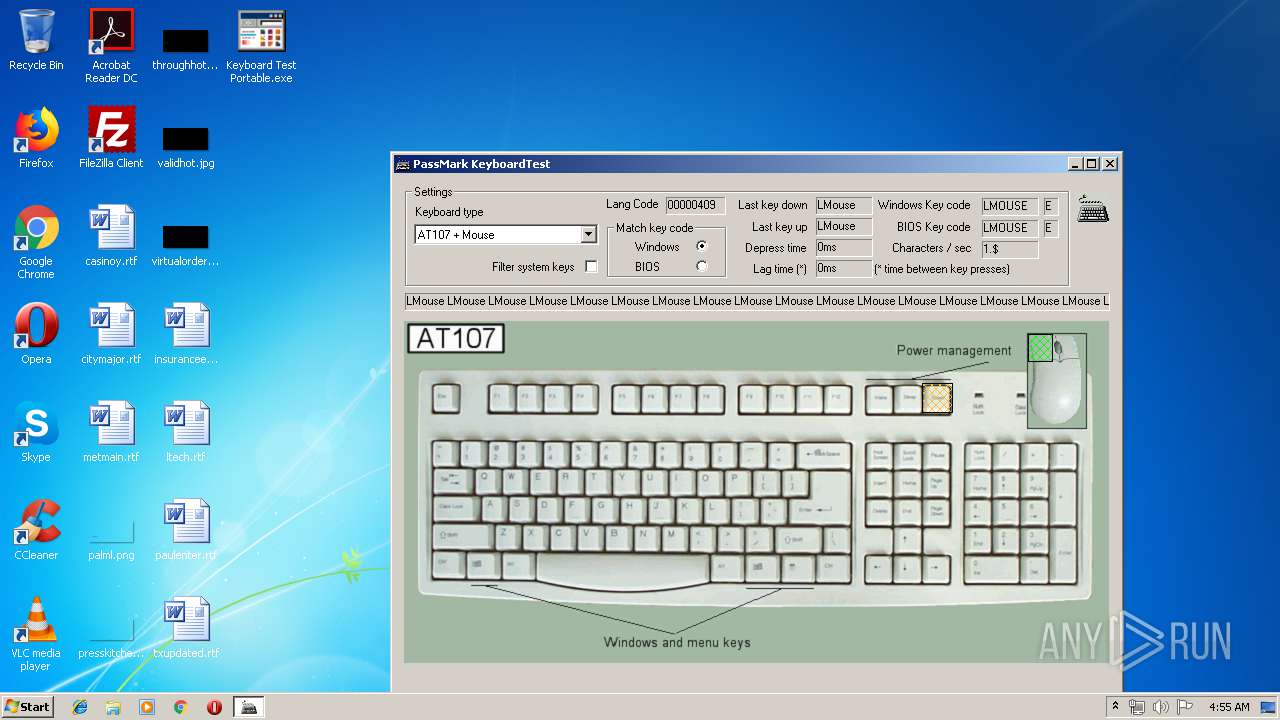
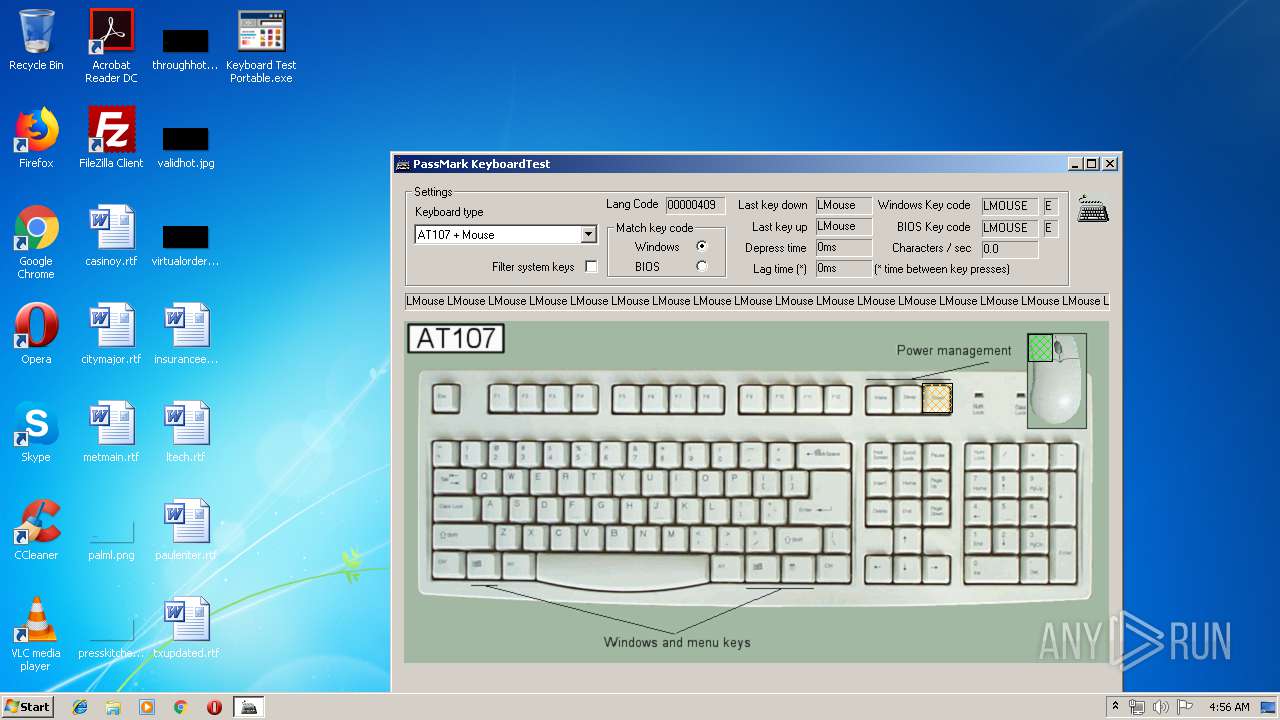
| 764 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\KeyboardTest.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\KeyboardTest.exe | — | Keyboard Test Portable.exe | |||||||||||
User: admin Company: PassMark Software (www.passmark.com) Integrity Level: MEDIUM Description: KeyboardTest Exit code: 0 Version: 2, 2, 0, 1011 Modules
| |||||||||||||||
Total events
357
Read events
353
Write events
4
Delete events
0
Modification events
| (PID) Process: | (640) Keyboard Test Portable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (640) Keyboard Test Portable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
1
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\DellPortInt.bmp | image | |
MD5:40A467F6A4E4AA0F02FD53A221897A80 | SHA256:C948025D468219CA83ED1BC1BCAD73E7BF1C3025C2228E40909CD89F6E03675C | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\##Attributes.ini | text | |
MD5:4F217194CB7B8E39D4DA192DBCE973DB | SHA256:A64C6613138A043991BB912EC65EEE22C0F563A69C07FD6BF862E17C81DB9B3B | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\AT107 + Mouse.bmp | image | |
MD5:F8F03D003B7088FD1D32D890A6112FA9 | SHA256:22CF2ACB66AD5636A1F64F928C712CE09F4ACEF5B67F4B778A4ADE82FA1A1234 | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\KeyboardTest.exe | executable | |
MD5:D9BAE57635326DF8ED56823C26AE107E | SHA256:5874007A2FD6DC7A56C527F8C41A28A363E9B68F49CC21C7F732503CB0885BD3 | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\key.dat | binary | |
MD5:C19EABA20654CBB20EF7F24344032EE5 | SHA256:6DA1941ADB50E1BA05198E19458AC467E9FB4063B1E4C4DC81E2E97E0DC6ECEB | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\DellPortUS.kbl | text | |
MD5:DD18F00A60D8512D24C52E5BB5CE5495 | SHA256:5A5729A235887C8640D630F413354B33EF1F4AF0705521627CF68F178641C4D1 | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\DellPortInt.kbl | text | |
MD5:70354C6BC74F25410F8A7CF54EA3565D | SHA256:B66D57E30DC315648075913642BEC3772019E3C5F2592CC57E002115460151FC | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\KeyboardTest.exe.manifest | xml | |
MD5:CE5B4530DA80104361162D39C7F24C1D | SHA256:3E5C5FD85A57761B6AC06E6ED35A3E047718BE9207E774FC7504A7A00A5C4641 | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\AT107 + Mouse.kbl | text | |
MD5:0DB3DBD6F0BDE1C5971ED54C9BA0C153 | SHA256:D1BBA3C1E9FD7D1F8C6358D28F30F2459D602F2D10FC78302182F83108E5B6F4 | |||
| 640 | Keyboard Test Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KeyboardTest\DellPortUS.bmp | image | |
MD5:0F2C87A17C601A97580AAABD2629C7DC | SHA256:8CC58F448A7DD196C67FDED95D94E43BB255680C161922B58238AA6F39DB2D3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report