| File name: | FIX-BAN-GAMELOOP_Muahackvn.exe |
| Full analysis: | https://app.any.run/tasks/04744091-214c-449c-976b-d2d5b5411e9d |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 00:49:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A4A103E2A392E29D21E2656137B40C94 |
| SHA1: | 2E1F58FEAD312874FDF6C84BA393D46451CDAC71 |
| SHA256: | 16DA6AF08FD8E29A1626D5C52DBE7EC5A05990B5BE0E80DDA505820F378BF60B |
| SSDEEP: | 24576:kA3O3/d9ud9sfJjbgL4YQviaSIoIiYPpx0I:qd9m9sfJjbDNaaSpIiEp6I |
MALICIOUS
Starts CMD.EXE for self-deleting
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Starts NET.EXE for service management
- cmd.exe (PID: 4080)
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- net.exe (PID: 1636)
- net.exe (PID: 2200)
- net.exe (PID: 3492)
- net.exe (PID: 3040)
- cmd.exe (PID: 3152)
- net.exe (PID: 3692)
- net.exe (PID: 3652)
- net.exe (PID: 2928)
- net.exe (PID: 1796)
- net.exe (PID: 944)
- net.exe (PID: 3048)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 1900)
- cmd.exe (PID: 3736)
Creates a writable file the system directory
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Application was dropped or rewritten from another process
- DismHost.exe (PID: 3052)
SUSPICIOUS
Reads the Internet Settings
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- rundll32.exe (PID: 3136)
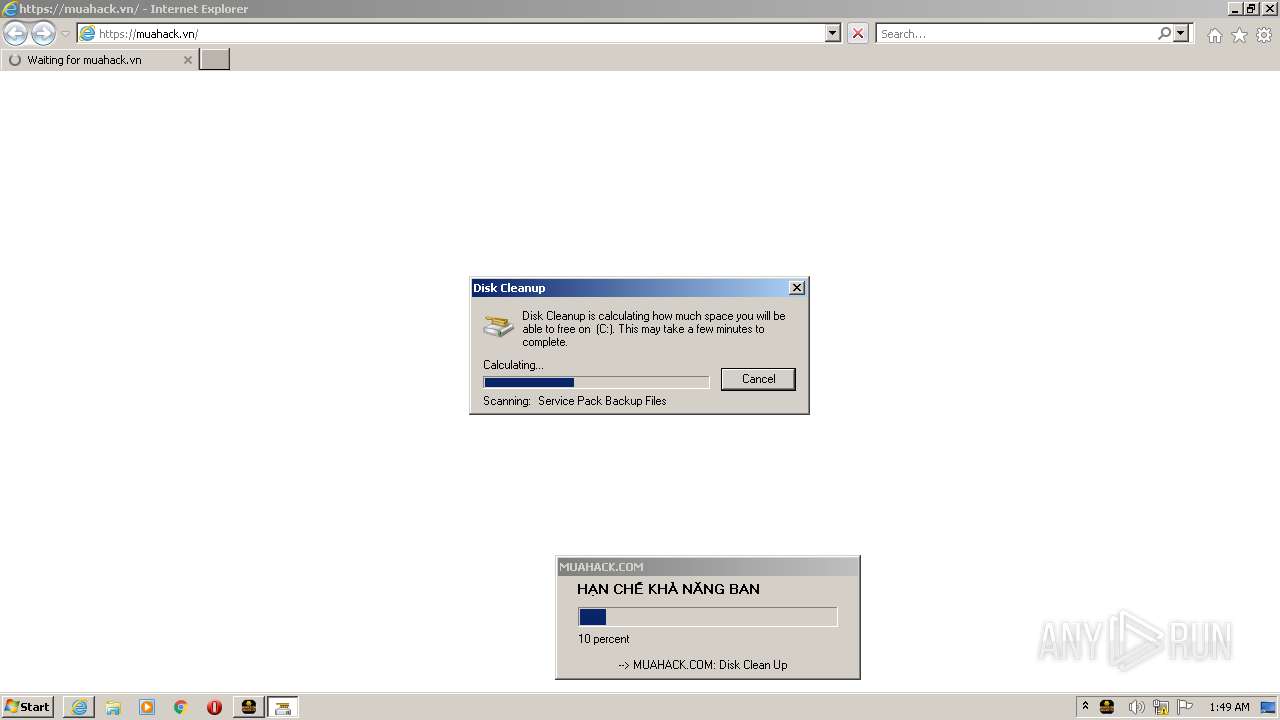
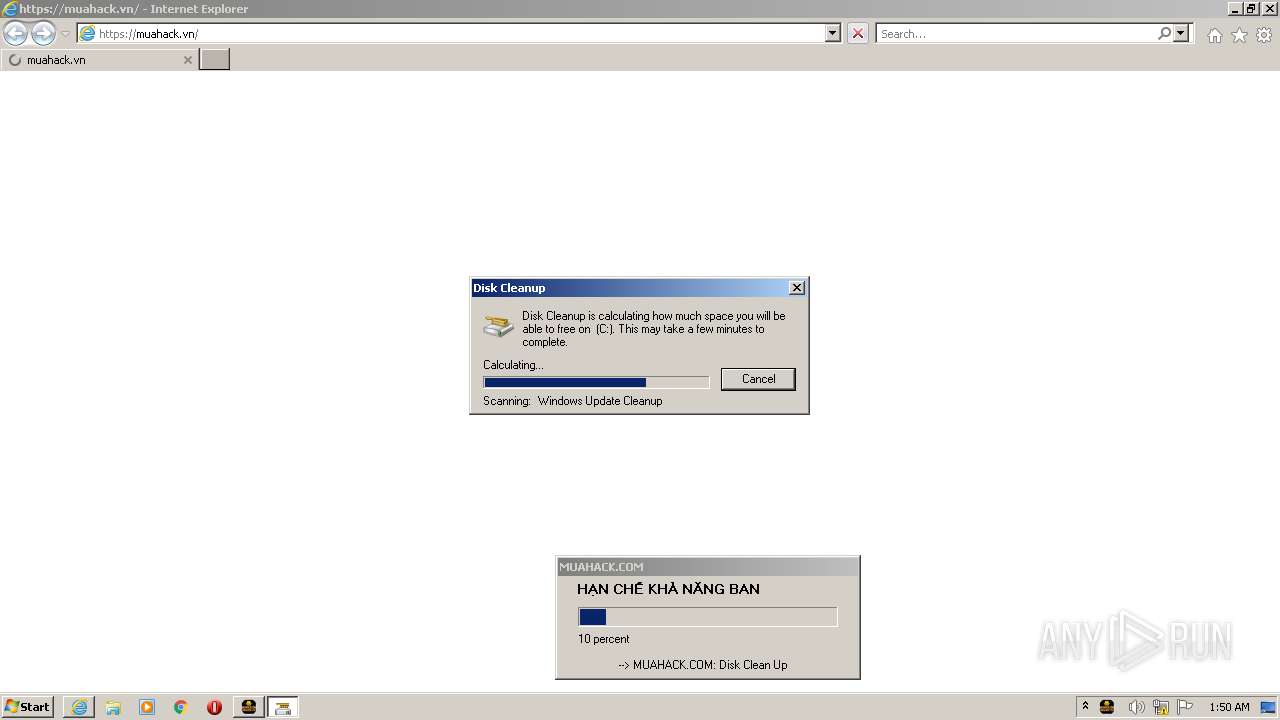
- cleanmgr.exe (PID: 2720)
Starts CMD.EXE for commands execution
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Creates files in the driver directory
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Starts SC.EXE for service management
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 2468)
- cmd.exe (PID: 584)
- cmd.exe (PID: 1888)
Uses RUNDLL32.EXE to load library
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Reads Microsoft Outlook installation path
- rundll32.exe (PID: 3136)
The process creates files with name similar to system file names
- cleanmgr.exe (PID: 2720)
Executable content was dropped or overwritten
- cleanmgr.exe (PID: 2720)
INFO
Checks supported languages
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- DismHost.exe (PID: 3052)
Reads mouse settings
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
Reads the machine GUID from the registry
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- DismHost.exe (PID: 3052)
Create files in a temporary directory
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- iexplore.exe (PID: 3684)
- rundll32.exe (PID: 3136)
- cleanmgr.exe (PID: 2720)
The process checks LSA protection
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- rundll32.exe (PID: 3136)
- cleanmgr.exe (PID: 2720)
- DismHost.exe (PID: 3052)
Reads the computer name
- FIX-BAN-GAMELOOP_Muahackvn.exe (PID: 3228)
- DismHost.exe (PID: 3052)
Application launched itself
- iexplore.exe (PID: 3684)
Checks proxy server information
- rundll32.exe (PID: 3136)
Reads Microsoft Office registry keys
- cleanmgr.exe (PID: 2720)
Creates files or folders in the user directory
- cleanmgr.exe (PID: 2720)
- rundll32.exe (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductName: | AUTOFIX-ANTIBAN |
|---|---|
| LegalCopyright: | MUAHACK.COM |
| CompanyName: | MUAHACK.COM |
| FileDescription: | AUTOFIX-ANTIBAN |
| InternalName: | 1.exe |
| OriginalFileName: | 1.exe |
| ProductVersion: | 1.0.1.2 |
| FileVersion: | 0.0.1.2 |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.1.2 |
| FileVersionNumber: | 0.0.1.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x29ab7 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 576512 |
| CodeSize: | 580096 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| TimeStamp: | 2022:03:14 11:56:06+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Mar-2022 11:56:06 |
| Detected languages: |
|
| FileVersion: | 0.0.1.2 |
| ProductVersion: | 1.0.1.2 |
| OriginalFilename: | 1.exe |
| InternalName: | 1.exe |
| FileDescription: | AUTOFIX-ANTIBAN |
| CompanyName: | MUAHACK.COM |
| LegalCopyright: | MUAHACK.COM |
| ProductName: | AUTOFIX-ANTIBAN |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Mar-2022 11:56:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008D9DD | 0x0008DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67059 |
.rdata | 0x0008F000 | 0x0002CC42 | 0x0002CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76834 |
.data | 0x000BC000 | 0x00009D54 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.98252 |
.rsrc | 0x000C6000 | 0x0004F491 | 0x0004F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.36353 |
.reloc | 0x00116000 | 0x0000A57A | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.27728 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37425 | 953 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 7.99136 | 50306 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 4.7064 | 67624 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 5.03994 | 16936 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
105
Monitored processes
45
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\Windows\system32\net1 stop Tessafe | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | C:\Windows\system32\cmd.exe /c sc delete vgk | C:\Windows\System32\cmd.exe | — | FIX-BAN-GAMELOOP_Muahackvn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 944 | "C:\Windows\System32\net.exe" stop QMemulatorService | C:\Windows\System32\net.exe | — | FIX-BAN-GAMELOOP_Muahackvn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | sc delete vgk | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1636 | net stop FACEIT | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1660 | C:\Windows\system32\net1 stop aow_drv | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1796 | net stop vgk | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1800 | C:\Windows\system32\net1 stop vgk | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1864 | C:\Windows\system32\net1 stop FACEIT | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1888 | C:\Windows\system32\cmd.exe /c sc delete vgc | C:\Windows\System32\cmd.exe | — | FIX-BAN-GAMELOOP_Muahackvn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
28 926
Read events
28 604
Write events
312
Delete events
10
Modification events
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3684) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
62
Suspicious files
32
Text files
18
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Users\admin\AppData\Local\Temp\autF86A.tmp | image | |
MD5:— | SHA256:— | |||
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Users\admin\AppData\Local\Temp\fixban1.jpg | image | |
MD5:— | SHA256:— | |||
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Users\admin\AppData\Local\Temp\~DF8C6435EB8B66BAD0.TMP | binary | |
MD5:— | SHA256:— | |||
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Users\admin\AppData\Local\Temp\autF956.tmp | binary | |
MD5:— | SHA256:— | |||
| 2720 | cleanmgr.exe | C:\Users\admin\AppData\Local\Temp\{32B04F75-10A0-4978-BE9C-451BA9536F29} | binary | |
MD5:— | SHA256:— | |||
| 2720 | cleanmgr.exe | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2720 | cleanmgr.exe | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{7546E245-99E0-43D0-91FC-2E16CC0B8C80}.FSD | binary | |
MD5:— | SHA256:— | |||
| 2720 | cleanmgr.exe | C:\Windows\Logs\DISM\dism.log | text | |
MD5:— | SHA256:— | |||
| 3228 | FIX-BAN-GAMELOOP_Muahackvn.exe | C:\Users\admin\AppData\Local\Temp\~DF485D5140A10A8D16.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3684 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fd5e1a044721289c | US | compressed | 4.70 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3684 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3684 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2776 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
— | — | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3684 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
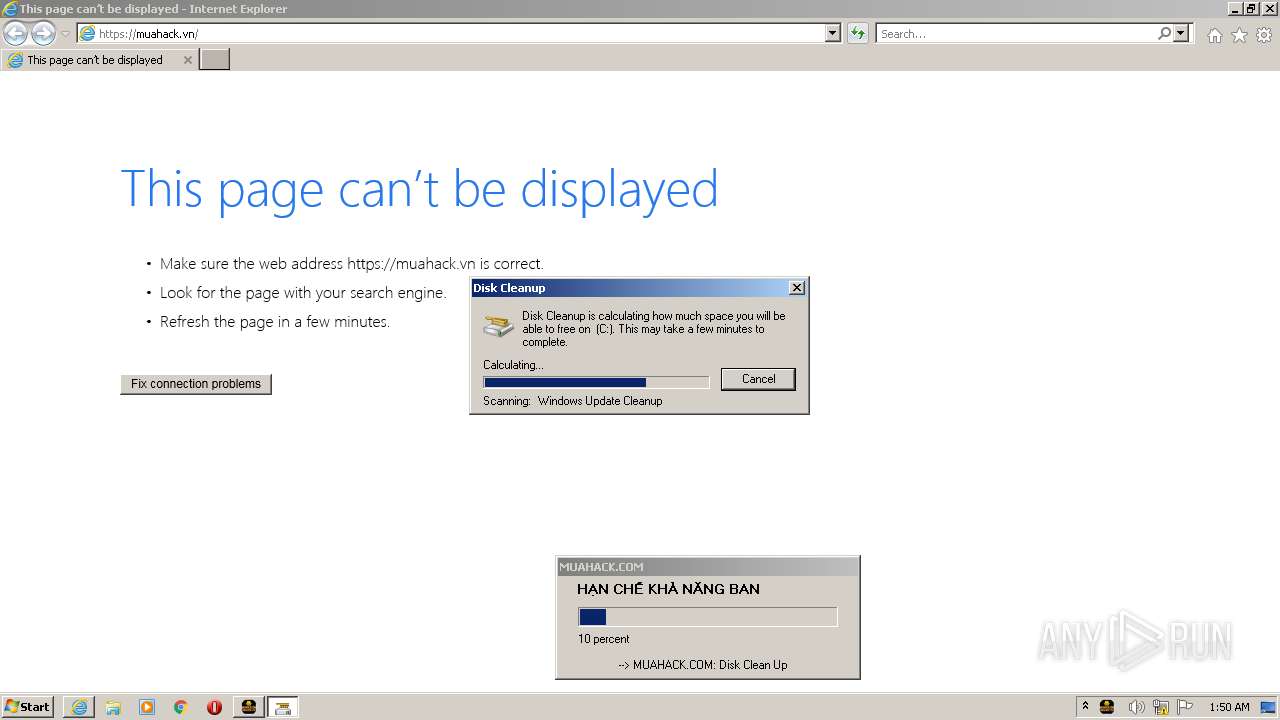
2776 | iexplore.exe | 188.114.97.3:443 | muahack.vn | CLOUDFLARENET | NL | malicious |
2776 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
muahack.vn |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
cleanmgr.exe | PID=2720 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
cleanmgr.exe | PID=2720 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
cleanmgr.exe | PID=2720 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
cleanmgr.exe | PID=2720 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
cleanmgr.exe | PID=2720 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
cleanmgr.exe | PID=2720 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
cleanmgr.exe | PID=2720 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |
cleanmgr.exe | PID=2720 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
cleanmgr.exe | PID=2720 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
cleanmgr.exe | PID=2720 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |