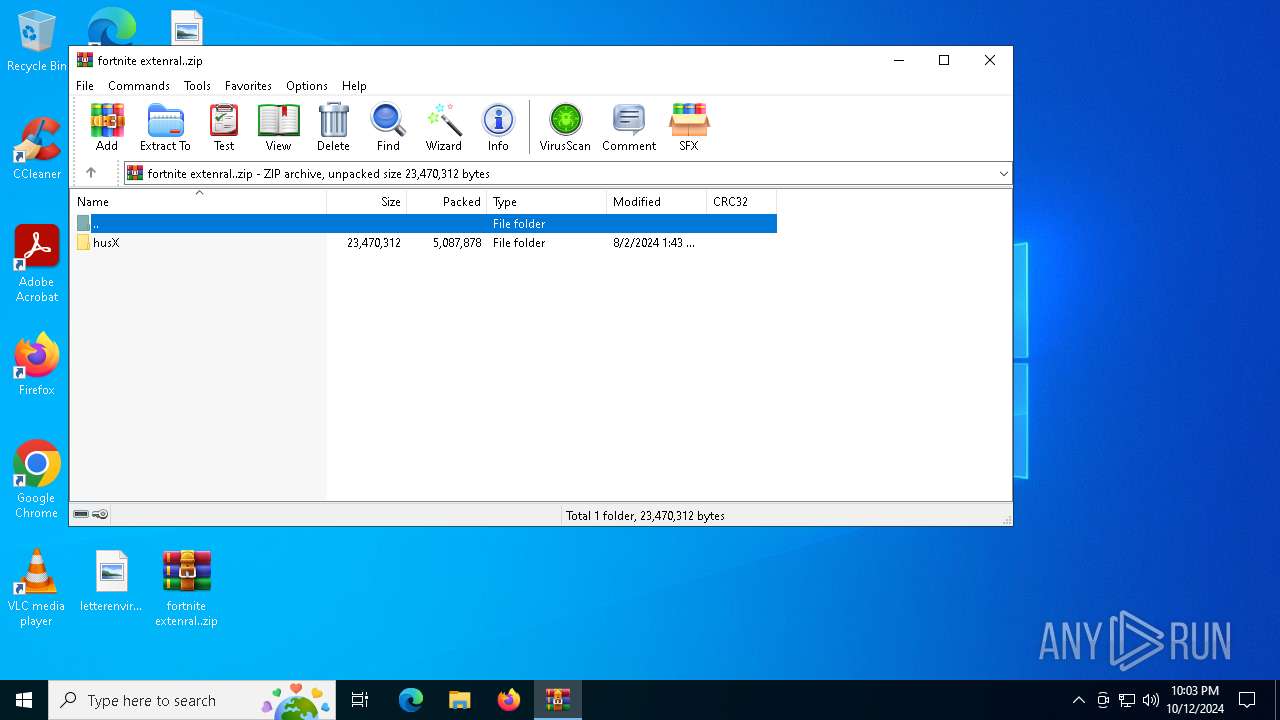
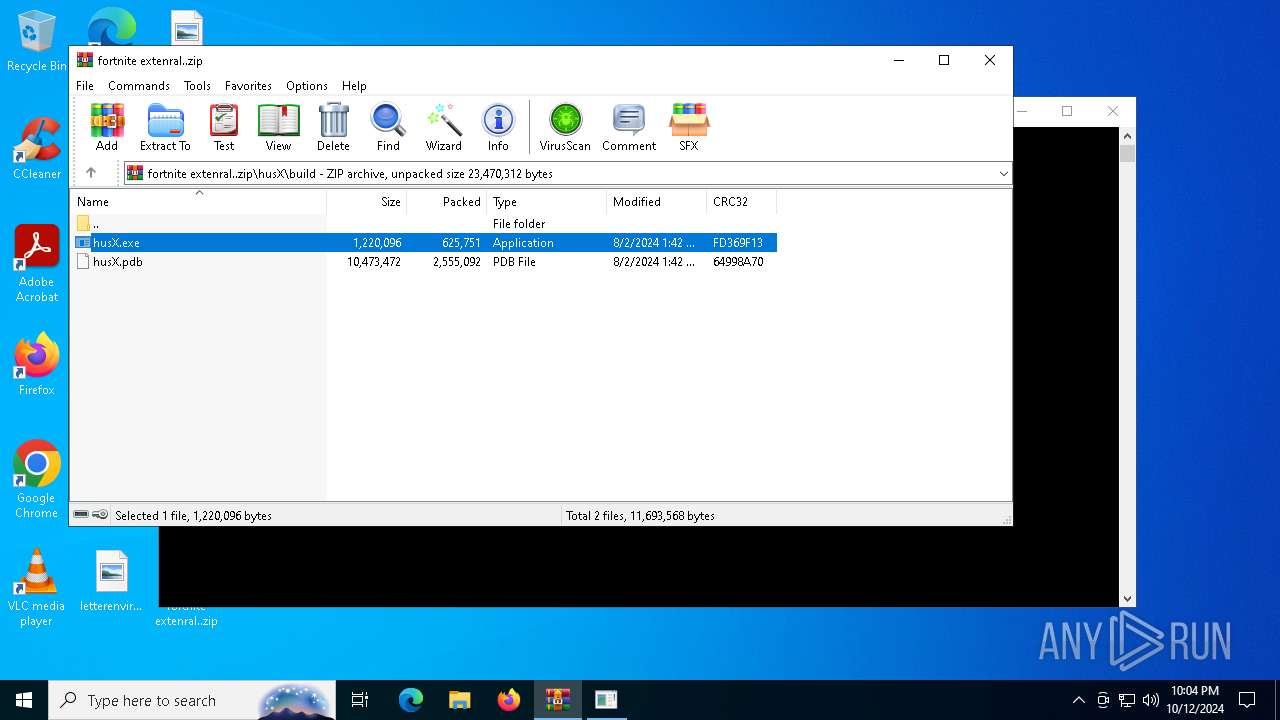
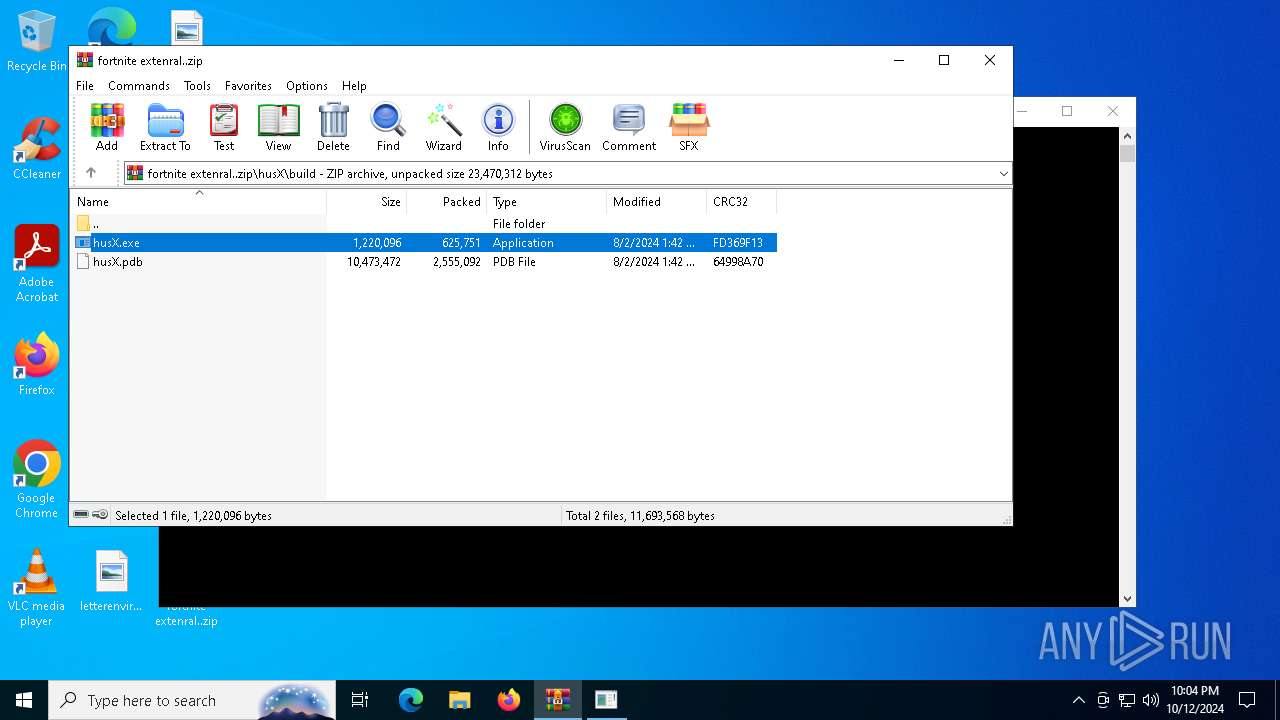
| File name: | fortnite extenral..zip |
| Full analysis: | https://app.any.run/tasks/b9d6b991-862a-4845-b876-42ce0d19f723 |
| Verdict: | Malicious activity |
| Analysis date: | October 12, 2024, 22:03:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E968B426EB108E46472DE02F1D263CB3 |
| SHA1: | 073E27E505E71CDD25CF285590DD04B27C989068 |
| SHA256: | 16D0CA2DCD0DA01D960C2145AA0F7A57F7BE6056EE8AC0090F2A8DA05E2B296D |
| SSDEEP: | 98304:dnJUD4IHrt5UGvJT/yPWs9TOUIOHWGg03gnXJvAqyWVxYq/RKSxxjxz2XqRKCts/:ZgXeukGW/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- bfsv.exe (PID: 3944)
- husX.exe (PID: 6160)
Starts CMD.EXE for commands execution
- husX.exe (PID: 6160)
- husX.exe (PID: 4828)
Connects to unusual port
- bfsv.exe (PID: 3944)
INFO
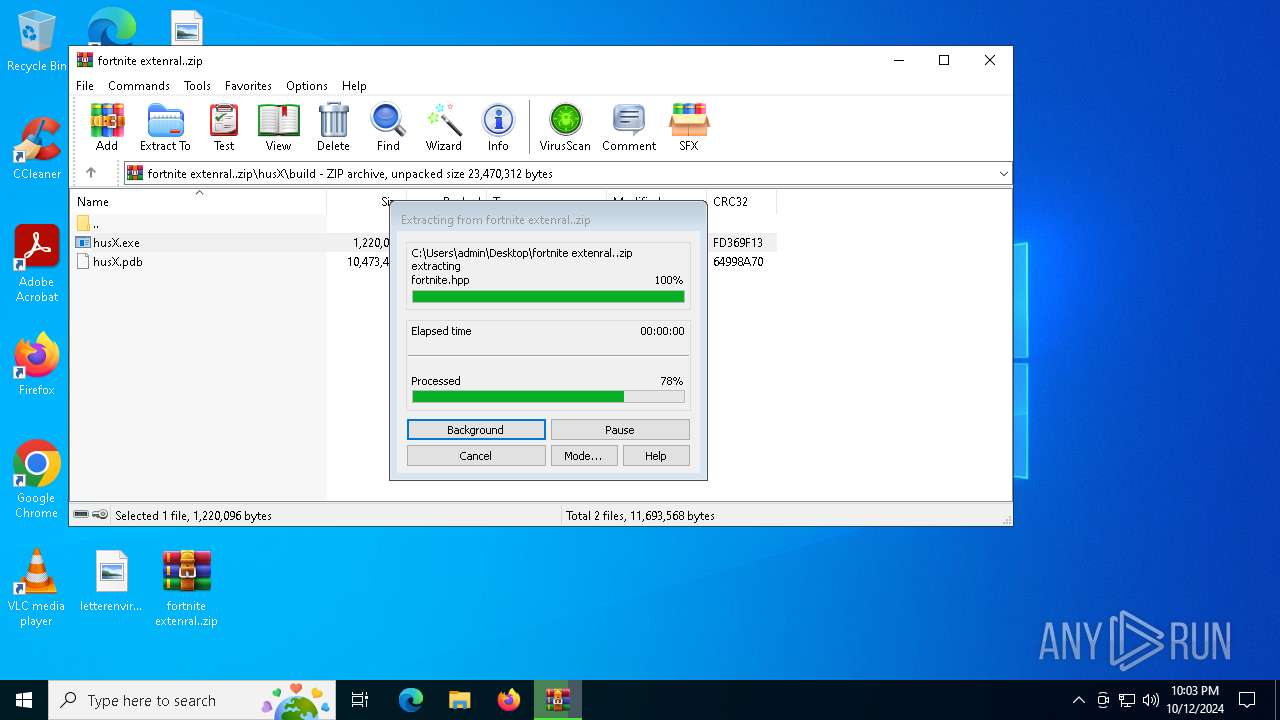
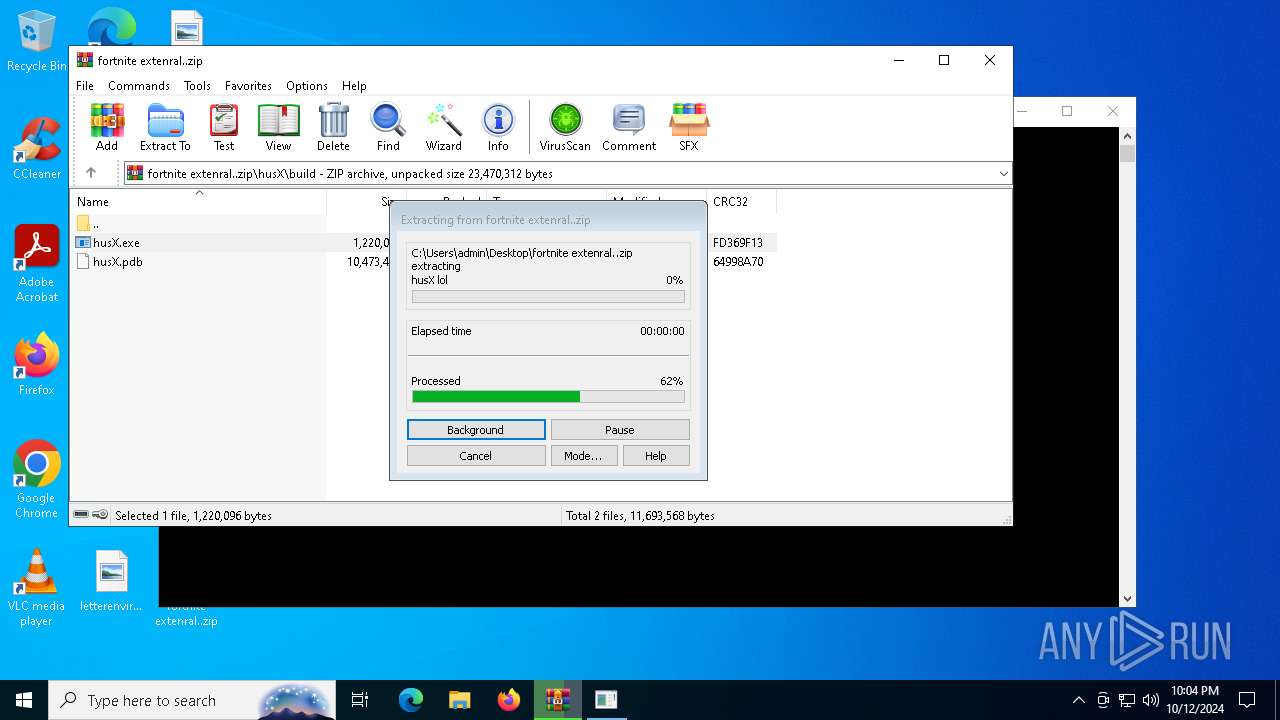
The process uses the downloaded file
- WinRAR.exe (PID: 5400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:02 03:43:36 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
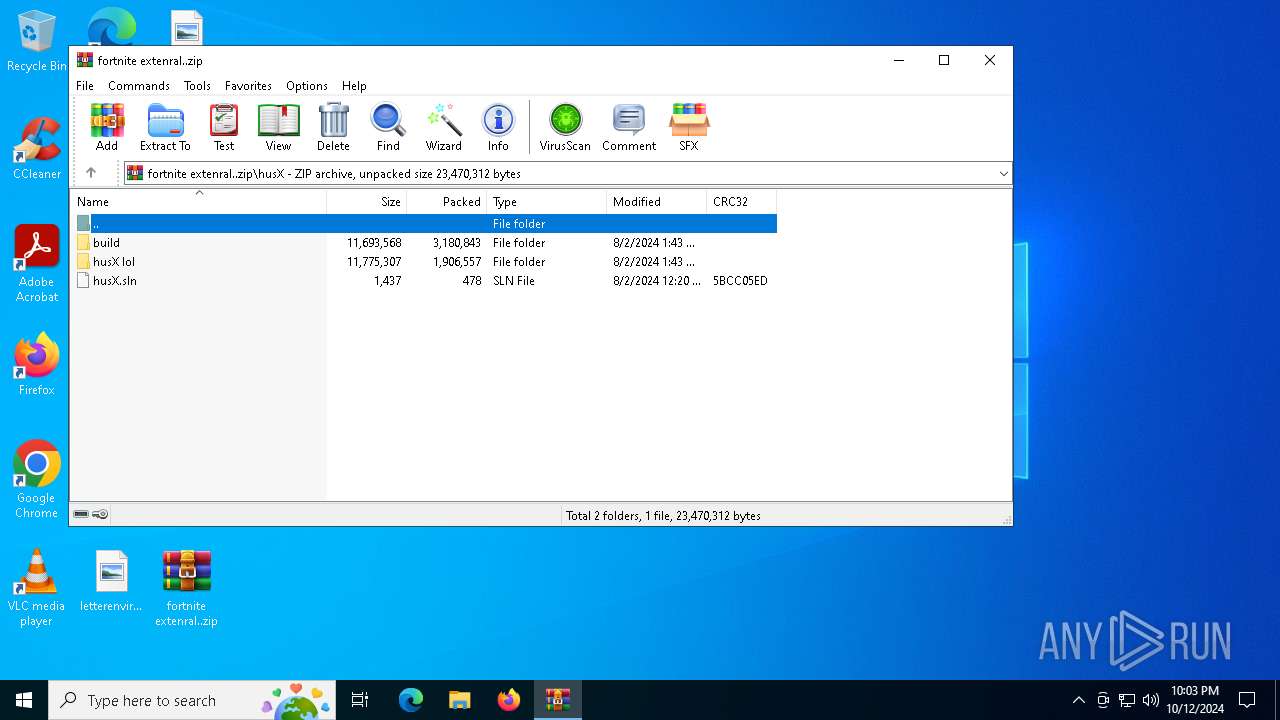
| ZipFileName: | husX/ |
Total processes
145
Monitored processes
13
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
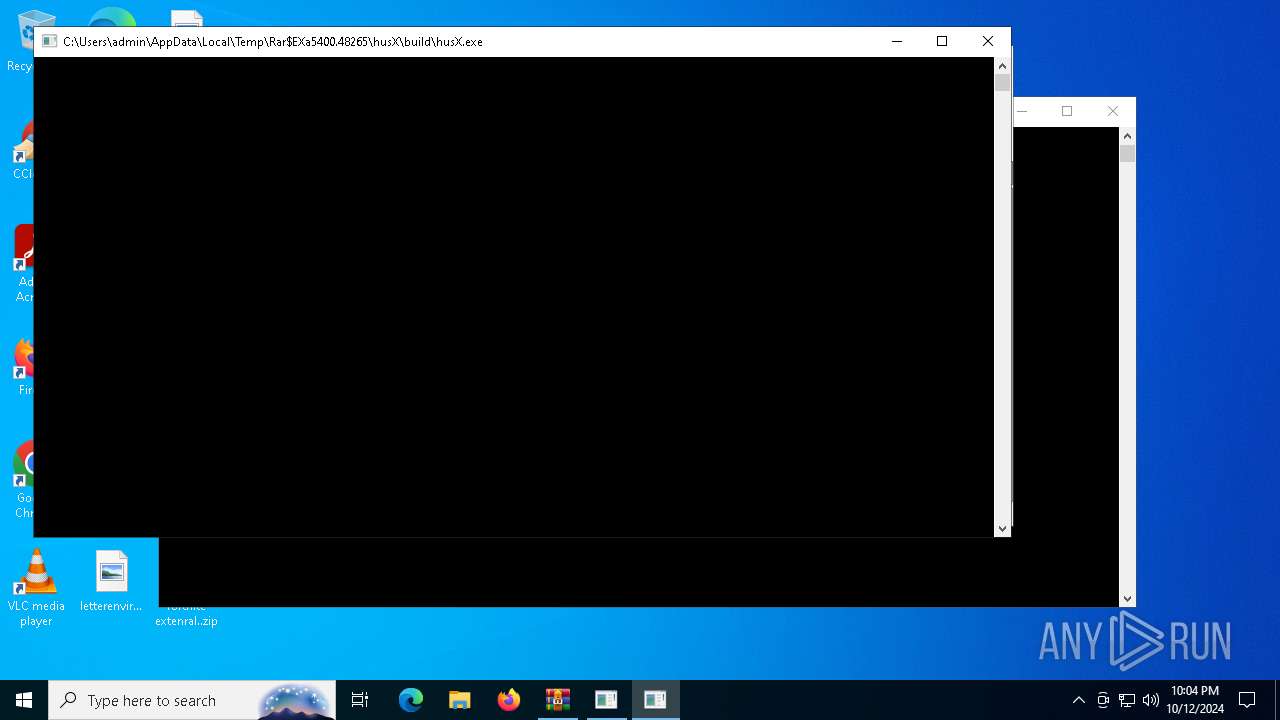
| 2576 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.48265\husX\build\husX.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.48265\husX\build\husX.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2784 | C:\WINDOWS\system32\cmd.exe /c C:\\Windows\\bfsv.exe | C:\Windows\System32\cmd.exe | — | husX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3944 | C:\\Windows\\bfsv.exe | C:\Windows\bfsv.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 1.0.0.0 Modules
| |||||||||||||||
| 4164 | C:\WINDOWS\system32\cmd.exe /c C:\\Windows\\bfsv.exe | C:\Windows\System32\cmd.exe | — | husX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4828 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.48265\husX\build\husX.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.48265\husX\build\husX.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
| 4868 | C:\\Windows\\bfsv.exe | C:\Windows\bfsv.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5400 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\fortnite extenral..zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | husX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | husX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\build\husX.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\build\husX.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
Total events
2 441
Read events
2 435
Write events
6
Delete events
0
Modification events
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\fortnite extenral..zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
6
Text files
297
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
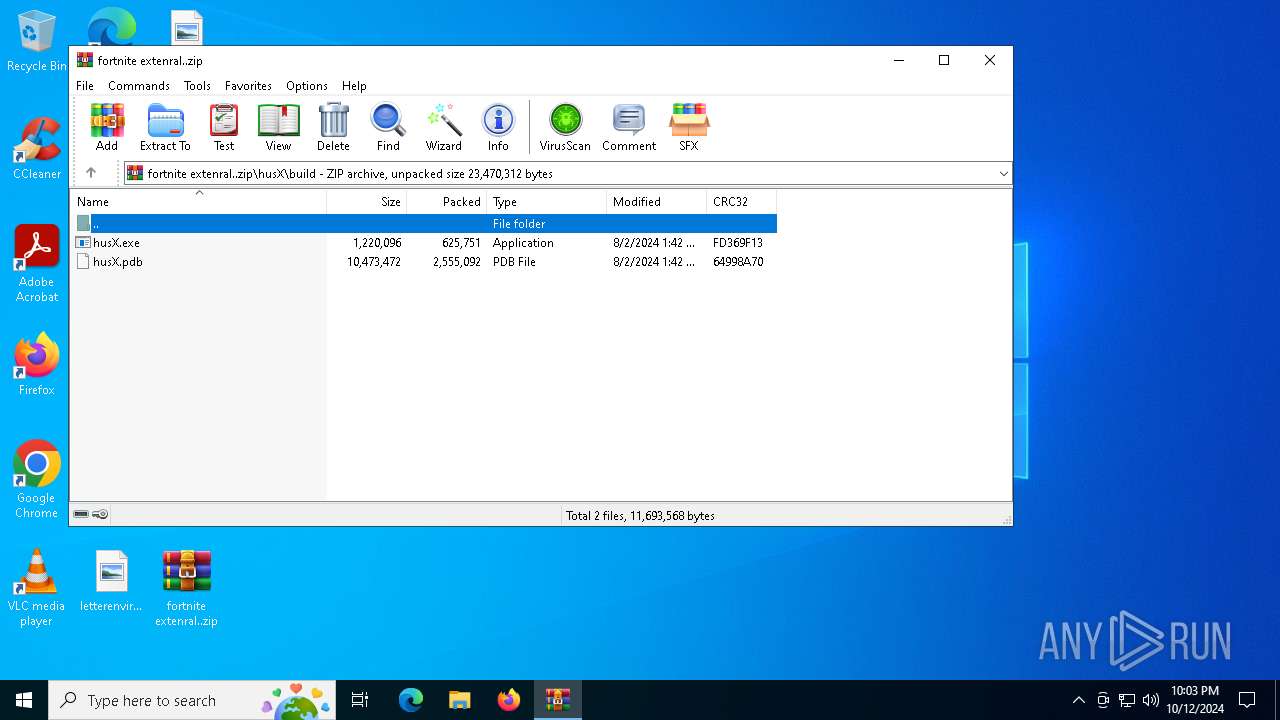
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\build\husX.pdb | — | |
MD5:— | SHA256:— | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\cache_helper.hpp | text | |
MD5:DC58448FE9AC8F57AACC9B4965B5600F | SHA256:3DD743C8BA96A325B950B1AC7BDCCEB5DB4DCCE64848FAF5A37496488E5DE9CC | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\aimbot.cpp | text | |
MD5:D6490A437E999D41BDC8623564E5673C | SHA256:4E6EC8D0867D2C645B4308F72B0FDBC0EDD7010A890DBE3B880E87F5825535C0 | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\build\husX.exe | odttf | |
MD5:7E9AF2C037DDD51D1D20D9E66FF43590 | SHA256:2A5E29A1AB926677DC017A6759BB4FC088A46A29C8489424CA543A1D1C144F46 | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\driver.hpp | text | |
MD5:B86FDED97AE703D0A20A1889DE73E10E | SHA256:FCE6E572B35FEDC32836B8F01A02DFD049745798CC1890E9F68A80C88A3A5A0D | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\elo\d2d1effectauthor.h | text | |
MD5:8E8664730D3E7A0C007F78EE70F2B3B3 | SHA256:6A963F8350BA43B115B2D2F6CD27CF35D20670F57975ACF31761CB81F6328AF1 | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\definitions.hpp | text | |
MD5:E62ECCB50100613F48F894B6C4C191E7 | SHA256:E973BE11647FE2B46BC8A4B1A897698E23FF5CFF1B05FD869612AC460B5CEC45 | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\direct.asm | text | |
MD5:A20C3F4B8A5410A8CC35695F4D7E506E | SHA256:D2D692AF3E8B9542E6B8C7A50694FD8D71B5D71B1D09C7EFC18B841FF94C7E29 | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\cache.cpp | text | |
MD5:B9726A4BA1EE6C4DA8BE1ADBD40735CF | SHA256:E0F830895852D9F0093730A7CF4D9D061D3AC8FE01777DBAD5A4100275232D6F | |||
| 5400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5400.44125\husX\husX lol\elo\d2d1.h | text | |
MD5:F368DB7A5EEF78600488446D9AABDAA6 | SHA256:EDAE8C901D038D422BADA1A36B0520ADAD79A5819CF40F7E5CF2504FD6720B96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
84
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6340 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6340 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4508 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |