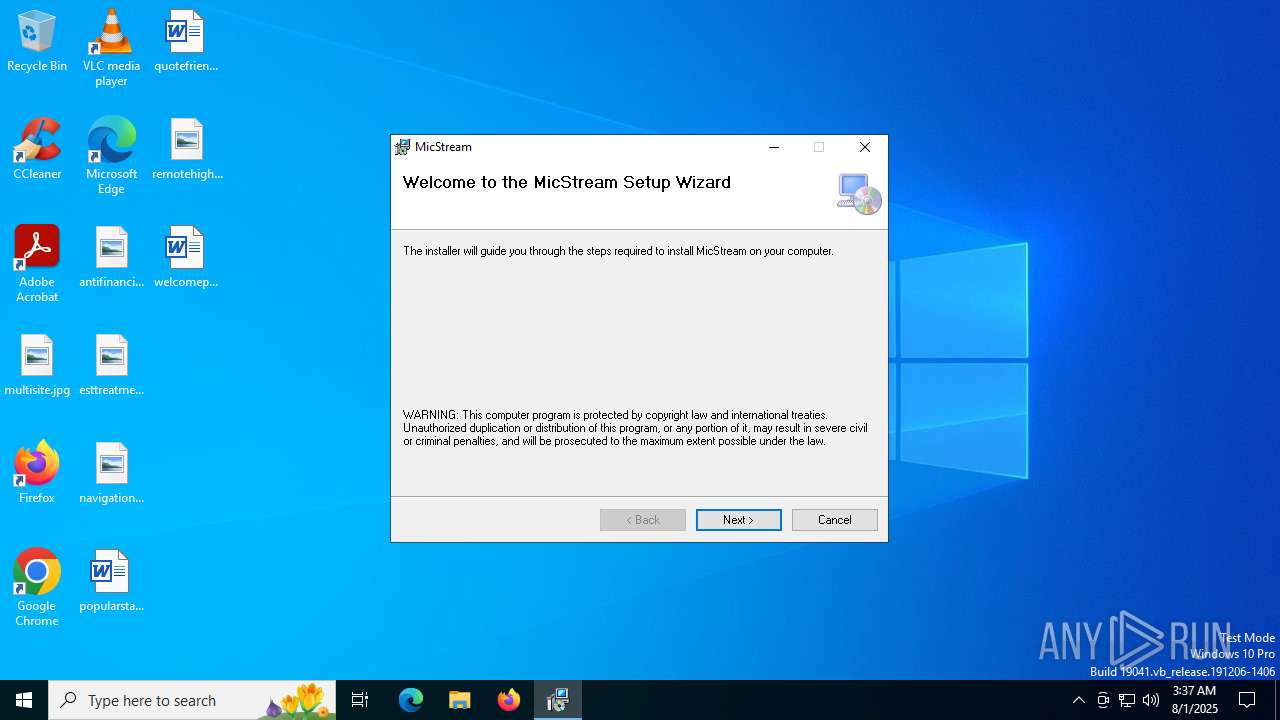
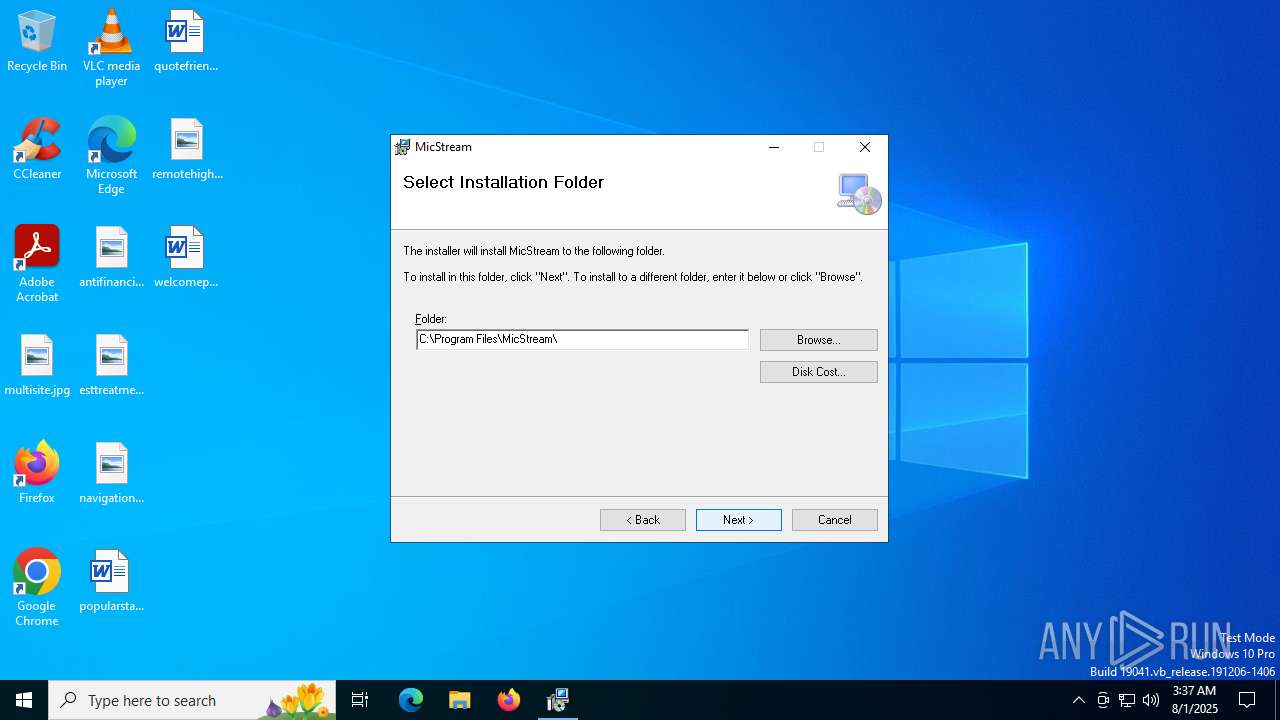
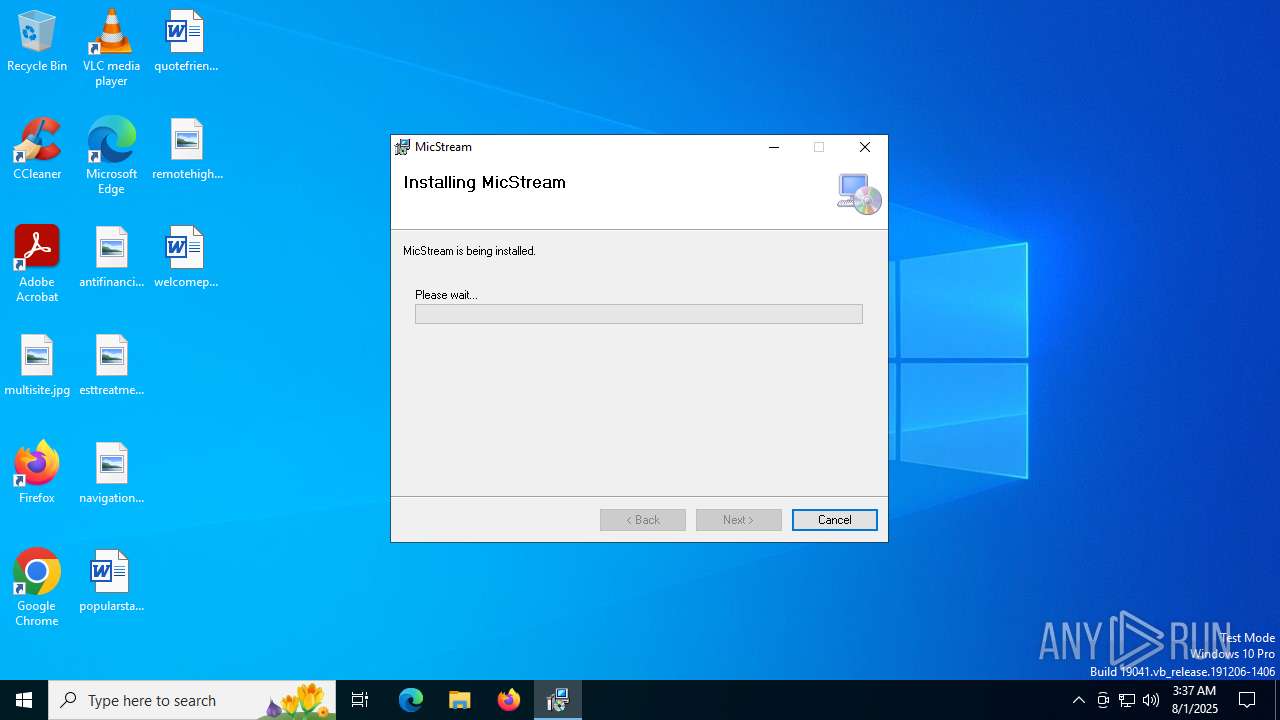
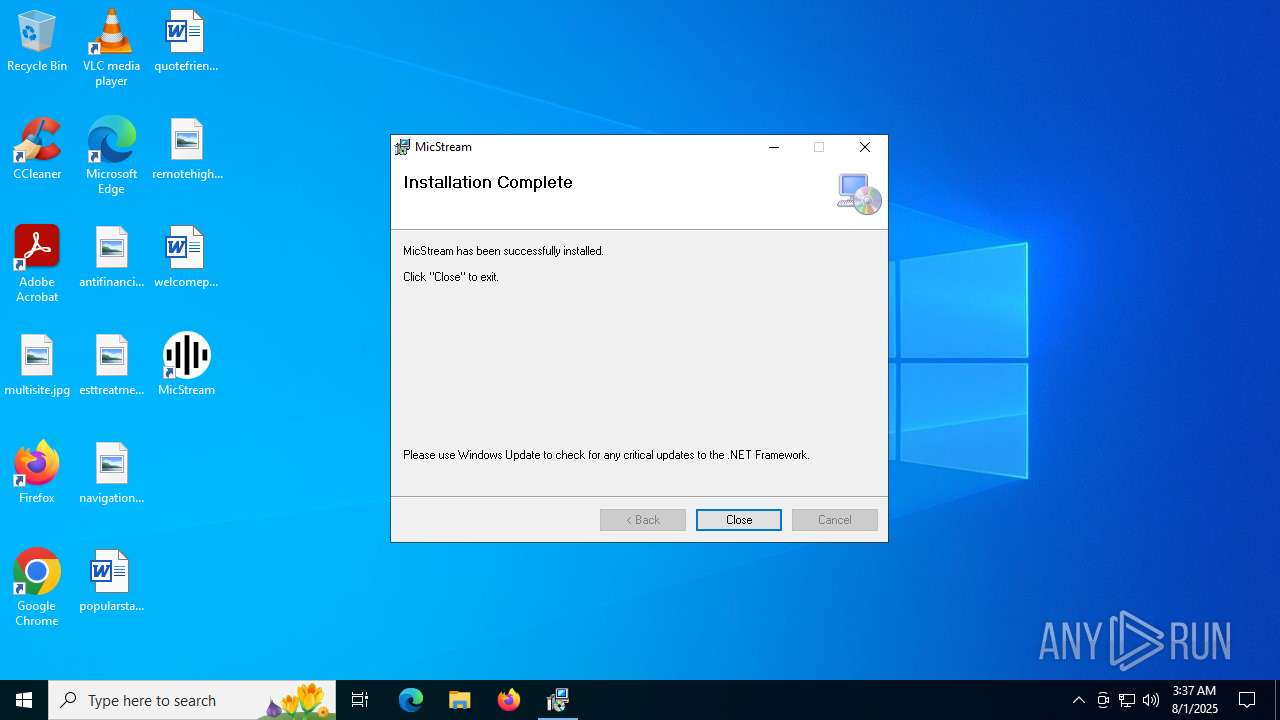
| File name: | micstream-setup-x64.exe |
| Full analysis: | https://app.any.run/tasks/1dfb67c6-c1ac-47a8-a231-d7b106663b4b |
| Verdict: | Malicious activity |
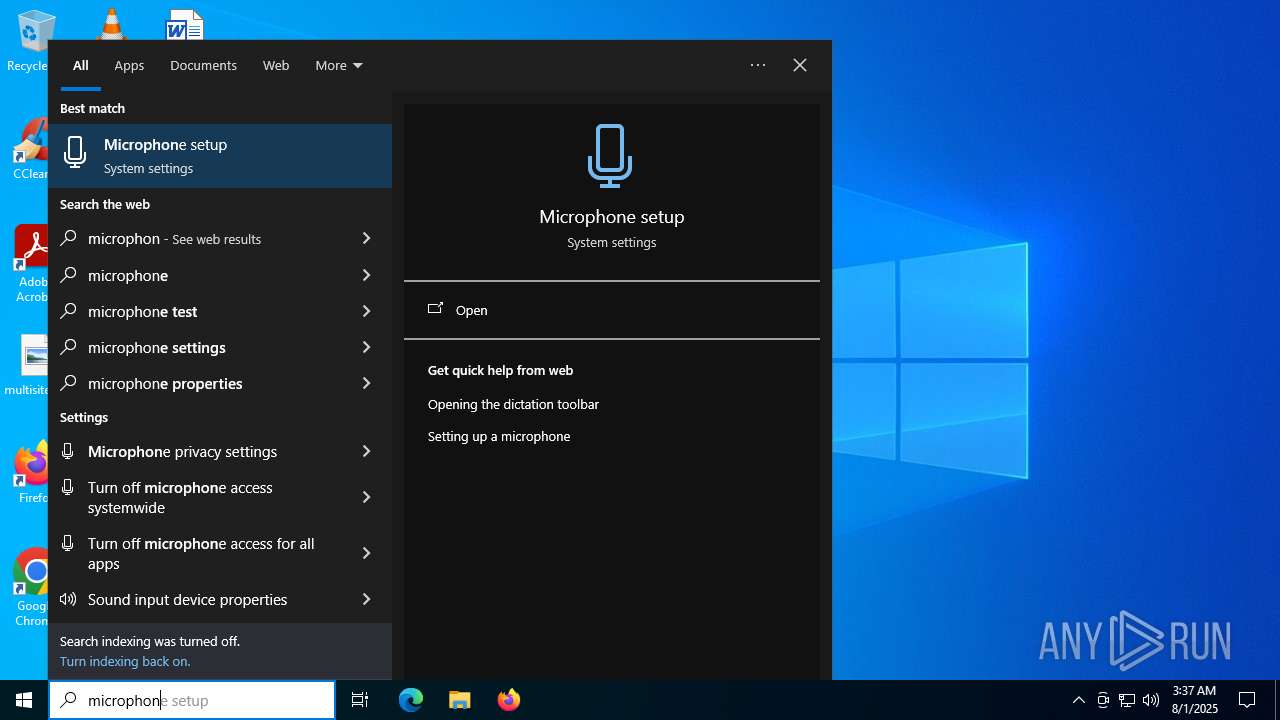
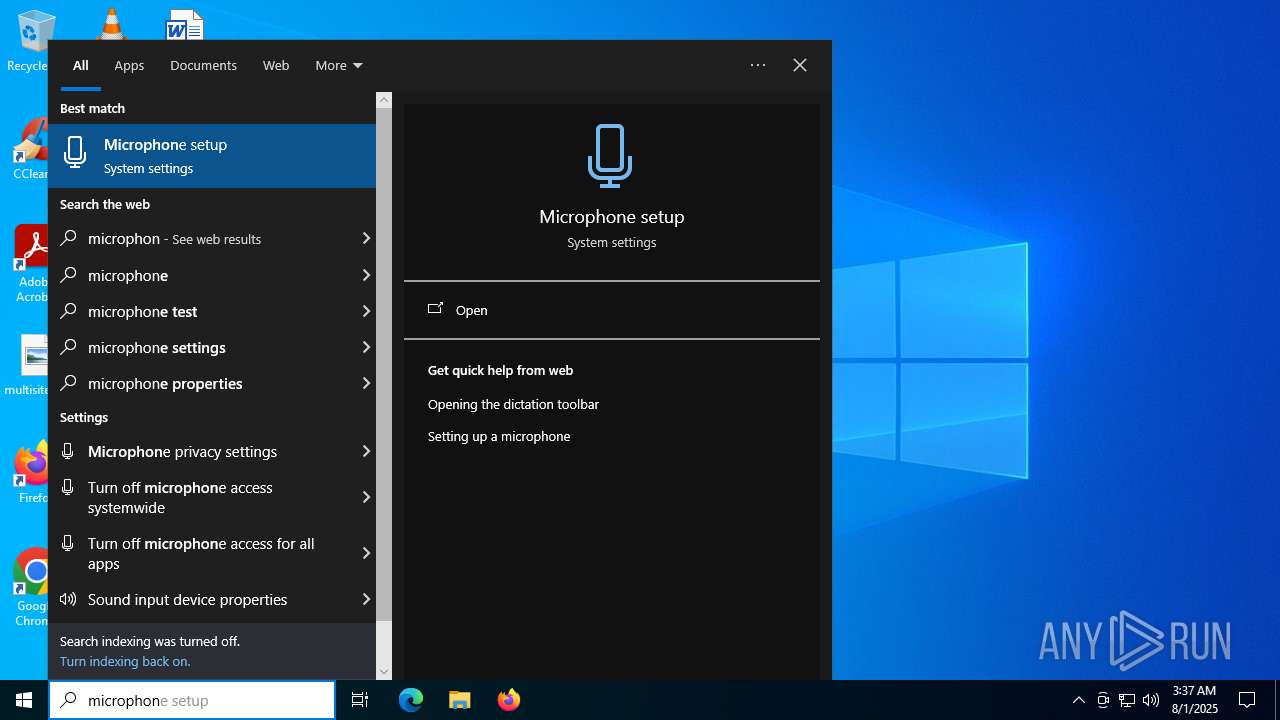
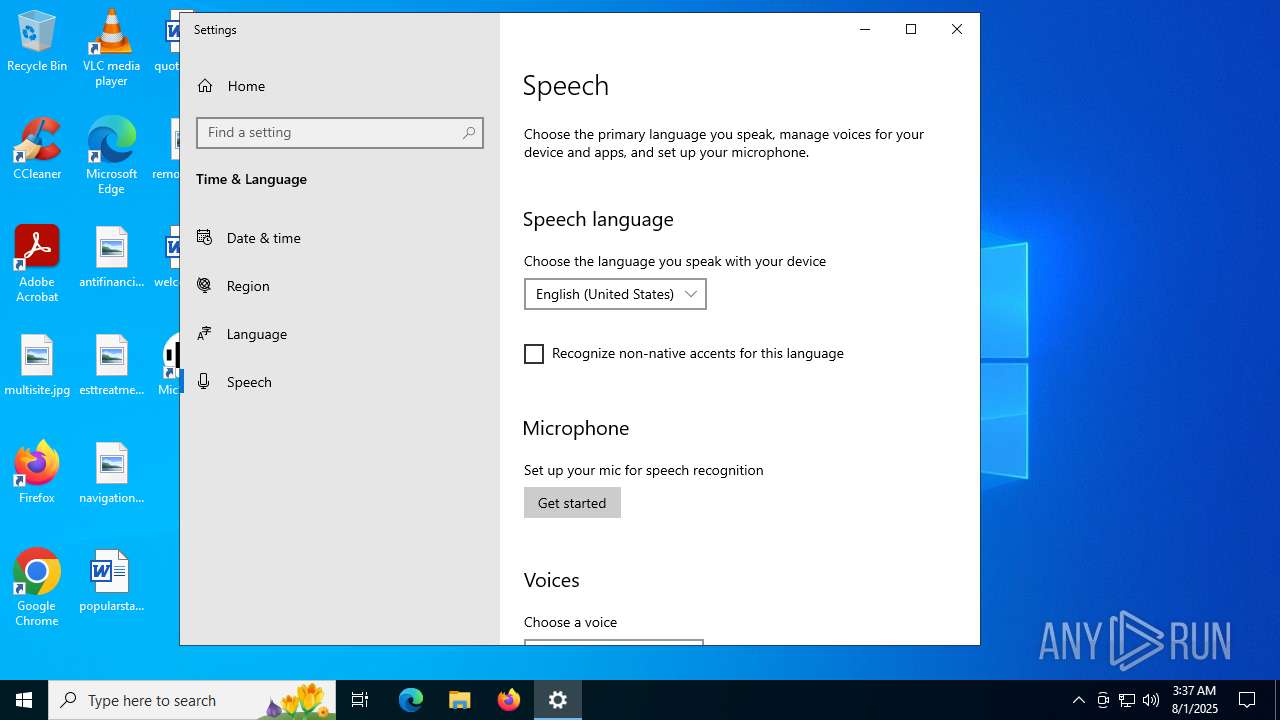
| Analysis date: | August 01, 2025, 03:37:05 |
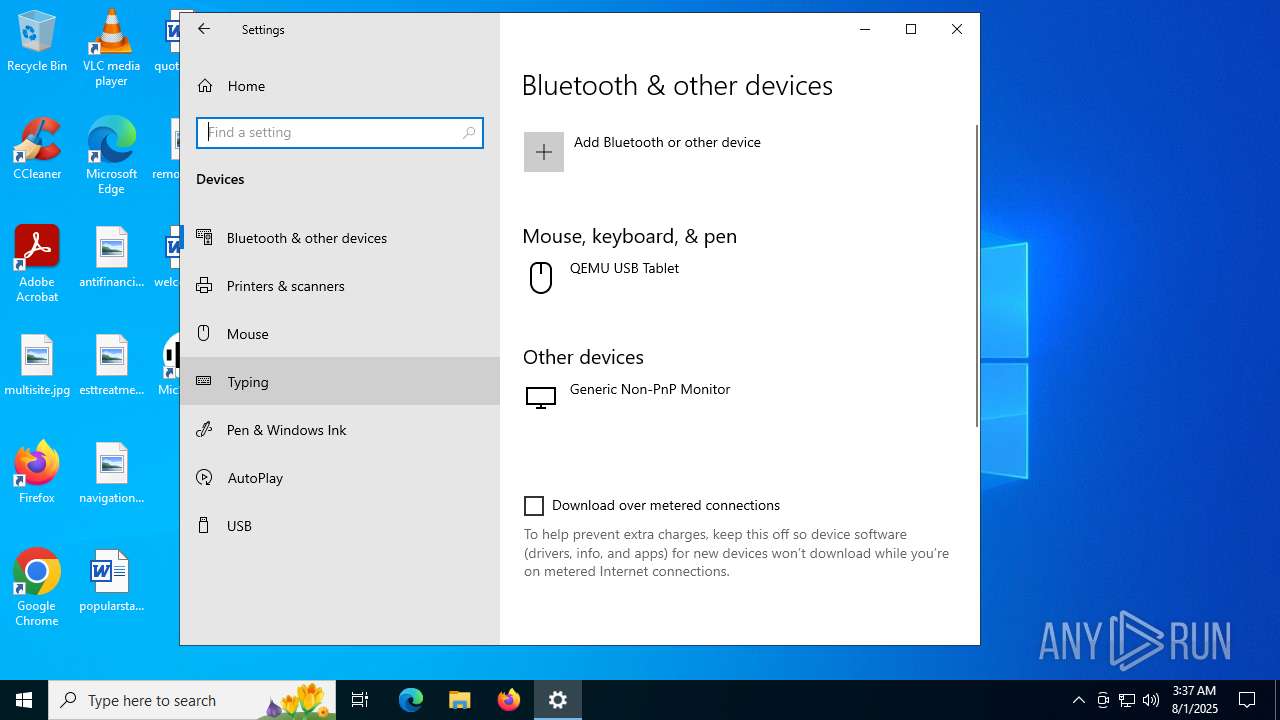
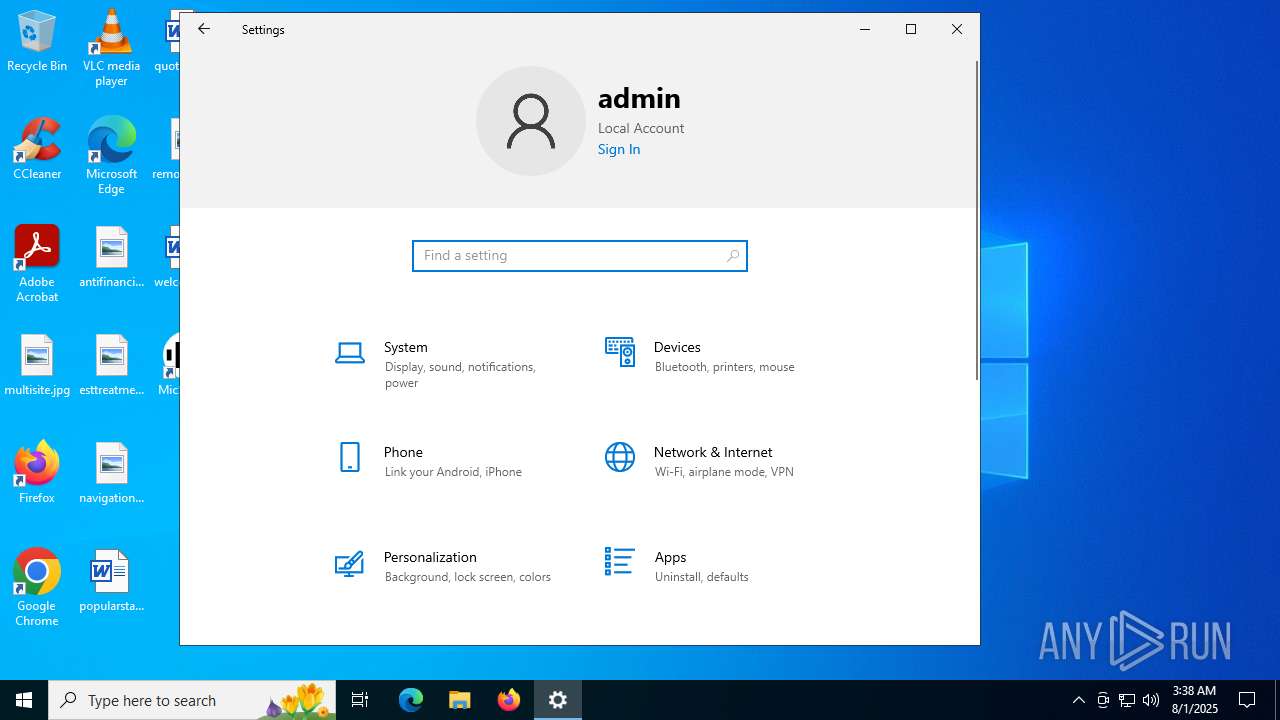
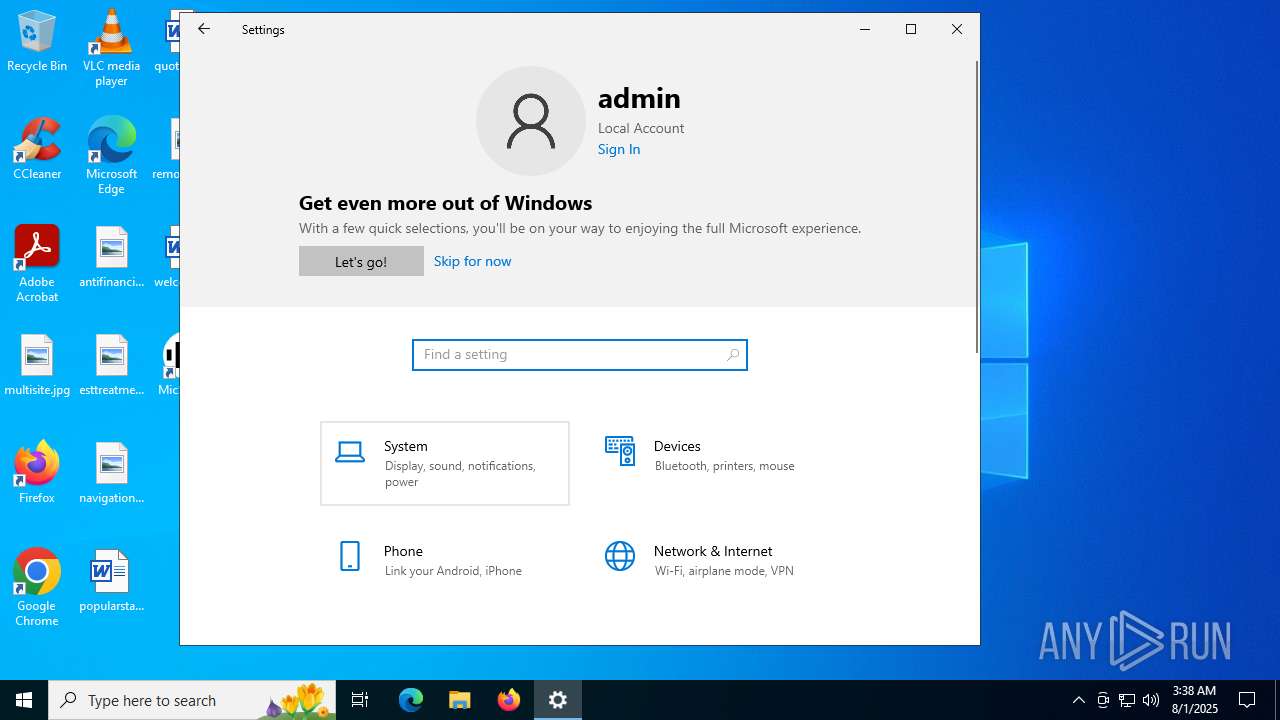
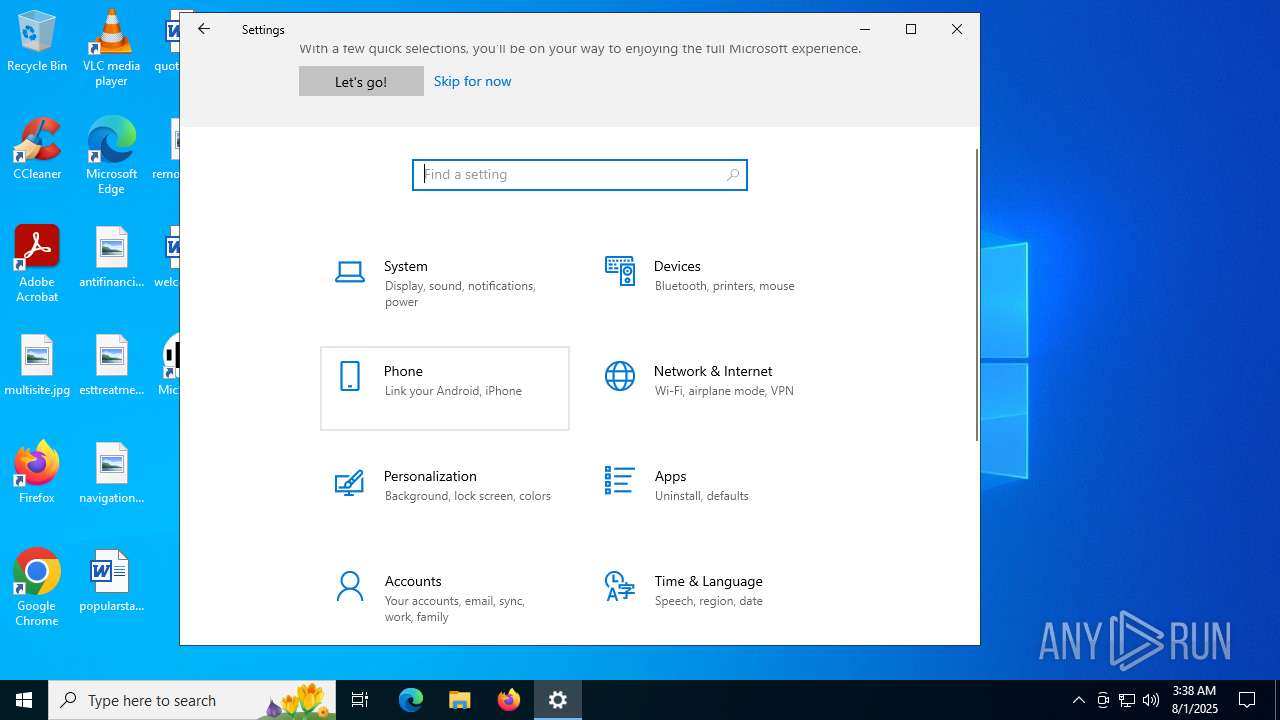
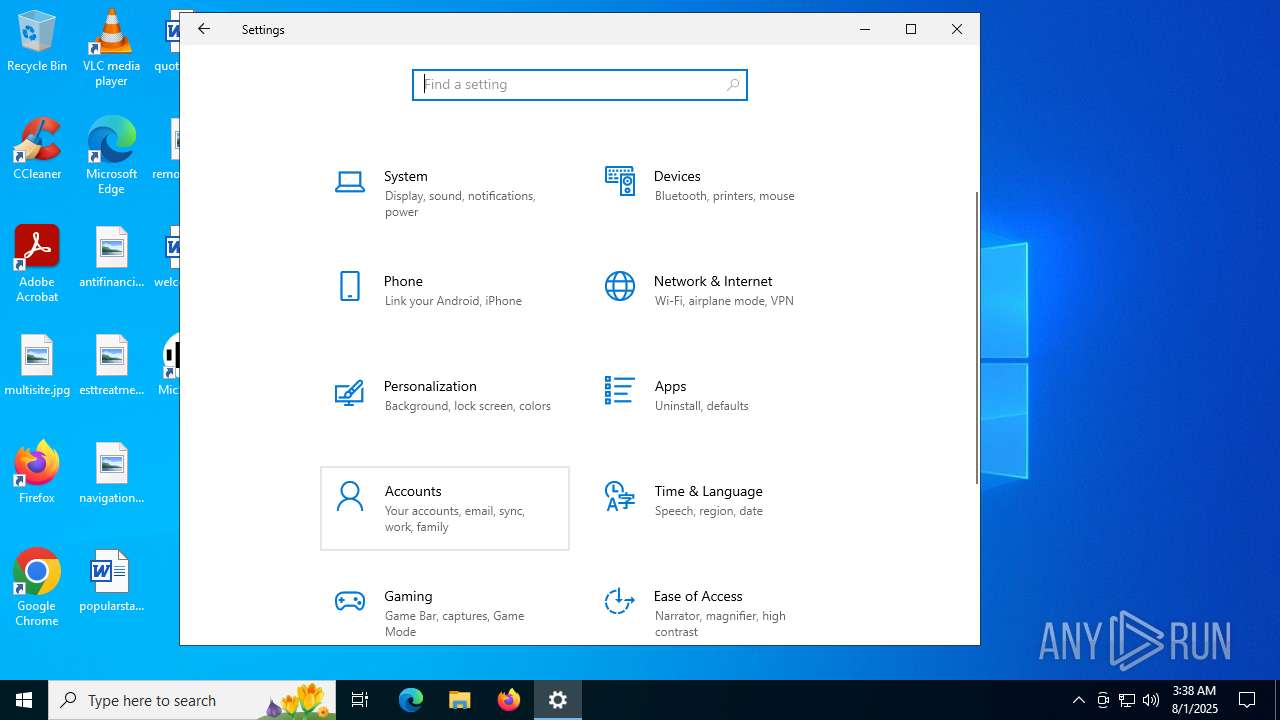
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | A4F86BEE27071FBA654CA442D52C6A5A |
| SHA1: | 90F947ECAFB26683842765A446E184A84869D36F |
| SHA256: | 16C665C37BBAF5563DE58CB57B97B75BDD5B319DB112633728BA41744FA48932 |
| SSDEEP: | 49152:SHufpipiRM4weWDS/I5r8EPw3UlfRiHyZfpwqp73JHGLGxkkwD6SY:SHiRM4i5rQ3afR+spHB3JHGpkwDtY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 1512)
Executable content was dropped or overwritten
- micstream-setup-x64.exe (PID: 1520)
- pnputil.exe (PID: 3572)
- drvinst.exe (PID: 2880)
Reads the date of Windows installation
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 6356)
Reads security settings of Internet Explorer
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 6356)
Executes as Windows Service
- VSSVC.exe (PID: 5432)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1512)
Application launched itself
- msiexec.exe (PID: 1512)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6356)
- pnputil.exe (PID: 3572)
- drvinst.exe (PID: 2880)
Creates files in the driver directory
- drvinst.exe (PID: 2880)
Creates or modifies Windows services
- drvinst.exe (PID: 5884)
- drvinst.exe (PID: 2504)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 6356)
INFO
The sample compiled with english language support
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 6788)
- msiexec.exe (PID: 1512)
- msiexec.exe (PID: 6356)
- pnputil.exe (PID: 3572)
- drvinst.exe (PID: 2880)
Reads the computer name
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 1512)
- msiexec.exe (PID: 2228)
- msiexec.exe (PID: 1880)
- msiexec.exe (PID: 6356)
- drvinst.exe (PID: 2880)
- drvinst.exe (PID: 2504)
- drvinst.exe (PID: 5884)
Create files in a temporary directory
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 2228)
- msiexec.exe (PID: 1880)
- msiexec.exe (PID: 6356)
- pnputil.exe (PID: 3572)
Checks supported languages
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 1512)
- msiexec.exe (PID: 2228)
- msiexec.exe (PID: 1880)
- drvinst.exe (PID: 2880)
- drvinst.exe (PID: 5884)
- drvinst.exe (PID: 2504)
- msiexec.exe (PID: 6356)
Process checks computer location settings
- micstream-setup-x64.exe (PID: 1520)
- msiexec.exe (PID: 6356)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6788)
- msiexec.exe (PID: 1512)
- msiexec.exe (PID: 6356)
Manages system restore points
- SrTasks.exe (PID: 6812)
Creates files or folders in the user directory
- msiexec.exe (PID: 1512)
Reads the machine GUID from the registry
- drvinst.exe (PID: 2880)
- msiexec.exe (PID: 6356)
Reads the software policy settings
- drvinst.exe (PID: 2880)
Creates a software uninstall entry
- msiexec.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2090:03:31 17:48:23+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 80 |
| CodeSize: | 1166848 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Installs MicStream client and driver |
| CompanyName: | Totrosh Technologies |
| FileDescription: | MicStream Installer |
| FileVersion: | 1.1.0.0 |
| InternalName: | micstream-setup-x64.exe |
| LegalCopyright: | (c) 2022 Totrosh Technologies |
| LegalTrademarks: | - |
| OriginalFileName: | micstream-setup-x64.exe |
| ProductName: | MicStream |
| ProductVersion: | 1.1.0.0 |
| AssemblyVersion: | 1.1.0.0 |
Total processes
193
Monitored processes
25
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\micstream-setup-x64.exe" | C:\Users\admin\AppData\Local\Temp\micstream-setup-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Totrosh Technologies Integrity Level: HIGH Description: MicStream Installer Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1880 | C:\Windows\syswow64\MsiExec.exe -Embedding 364D364BA852D56D61261C80C2BABE36 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name="MicStream Client" dir=in action=allow program="C:\Program Files\MicStream\micstream-client.exe" | C:\Windows\System32\netsh.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | C:\Windows\syswow64\MsiExec.exe -Embedding 318750F9FC7B86D49E4A6A750CE0AF47 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | DrvInst.exe "2" "1" "ROOT\MICSTREAM\0000" "C:\WINDOWS\System32\DriverStore\FileRepository\micstream.inf_amd64_865a472466378a26\micstream.inf" "oem1.inf:*:*:18.8.3.743:ROOT\MicStream," "4022fb013" "00000000000001D8" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2588 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2880 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{89a3c99c-4d9d-0f41-9840-615dd756daa0}\MicStream.inf" "9" "4022fb013" "00000000000001D8" "WinSta0\Default" "00000000000001E8" "208" "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pnputil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 858
Read events
13 219
Write events
1 512
Delete events
127
Modification events
| (PID) Process: | (1520) micstream-setup-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1520) micstream-setup-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1520) micstream-setup-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1520) micstream-setup-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000003E592C949502DC01E805000060060000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000016FA30949502DC01E805000060060000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000D16F08949502DC01E805000060060000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000D16F08949502DC01E805000060060000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000079DE29949502DC01E805000060060000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1512) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000079DE29949502DC01E805000060060000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
16
Suspicious files
11
Text files
10
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1512 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1520 | micstream-setup-x64.exe | C:\Users\admin\AppData\Local\Temp\micstream-setup.msi | executable | |
MD5:6D88AEE5F872C03A654690C5E56BAB10 | SHA256:DFE45D904AB74BDE2331849EB886010CD920C899CBD68C34BF2EA2F18E4245CF | |||
| 1512 | msiexec.exe | C:\Windows\Installer\190ce7.msi | executable | |
MD5:6D88AEE5F872C03A654690C5E56BAB10 | SHA256:DFE45D904AB74BDE2331849EB886010CD920C899CBD68C34BF2EA2F18E4245CF | |||
| 1512 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:D078C66A6649894CA7E85DED57260248 | SHA256:E51894BDF437AE3529861C16776F1A768010ADB1FB246F5D76195C2C1FC79F9D | |||
| 1512 | msiexec.exe | C:\Windows\Installer\MSID64.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 1512 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:AB23E5EF16634A4EB28671573A6676F6 | SHA256:424C3BC1E25B18153CC2CF706B8BF764F0B68EE6315DE65A19E0284EA25C3769 | |||
| 1512 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a6a055c3-9b48-44d0-8d54-b9607805e118}_OnDiskSnapshotProp | binary | |
MD5:D078C66A6649894CA7E85DED57260248 | SHA256:E51894BDF437AE3529861C16776F1A768010ADB1FB246F5D76195C2C1FC79F9D | |||
| 1512 | msiexec.exe | C:\Windows\Installer\MSIE50.tmp | binary | |
MD5:724F9D73197E3AF789A9B0D7EDEA56DD | SHA256:6474E60F08150402AD1DD5BD1971BCCB96C6E50608E99E21E96611B04E5C92AD | |||
| 1512 | msiexec.exe | C:\Windows\Installer\MSIE01.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 1512 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:B25D4F58E14FFA52A9E517B81DE16C3D | SHA256:0678B5427F87AB5FADA702BA54F039269F7D42B67953093C4E07DE3A43A5B00B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6664 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5040 | SystemSettings.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA8fFXWCzc0zc0vcX82UGjM%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5040 | SystemSettings.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1268 | svchost.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1964 | RUXIMICS.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6664 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |