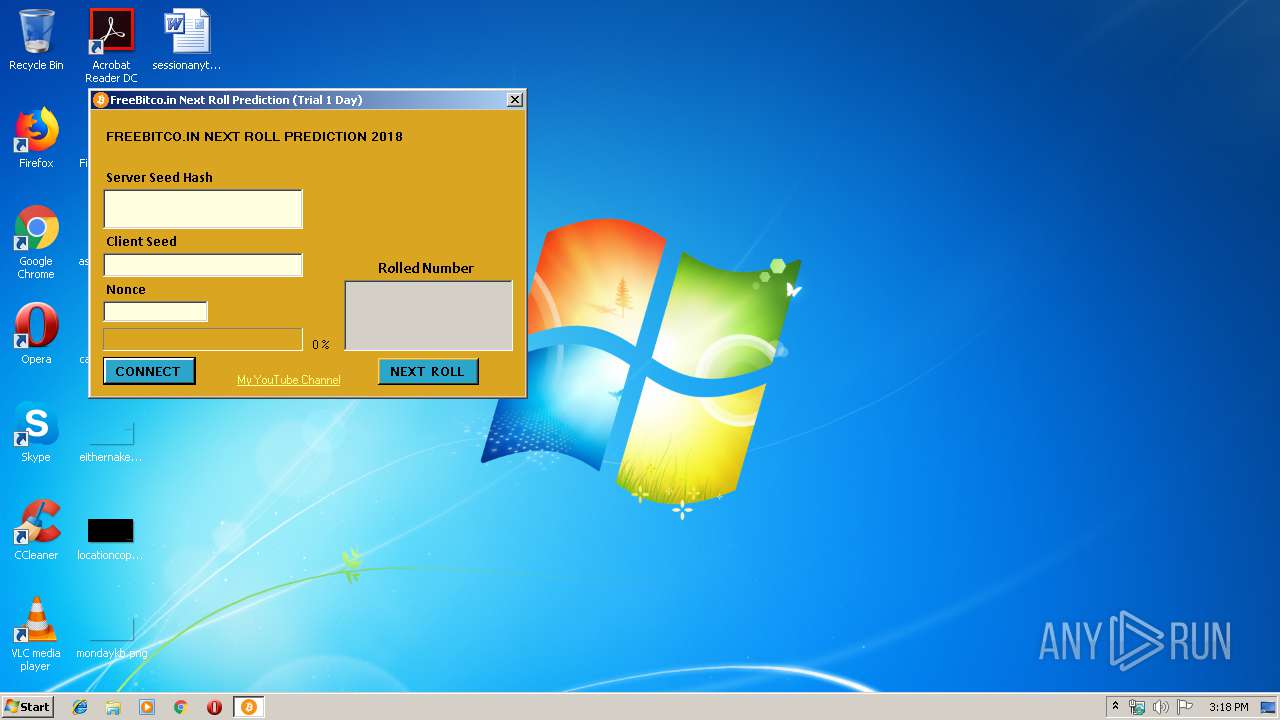
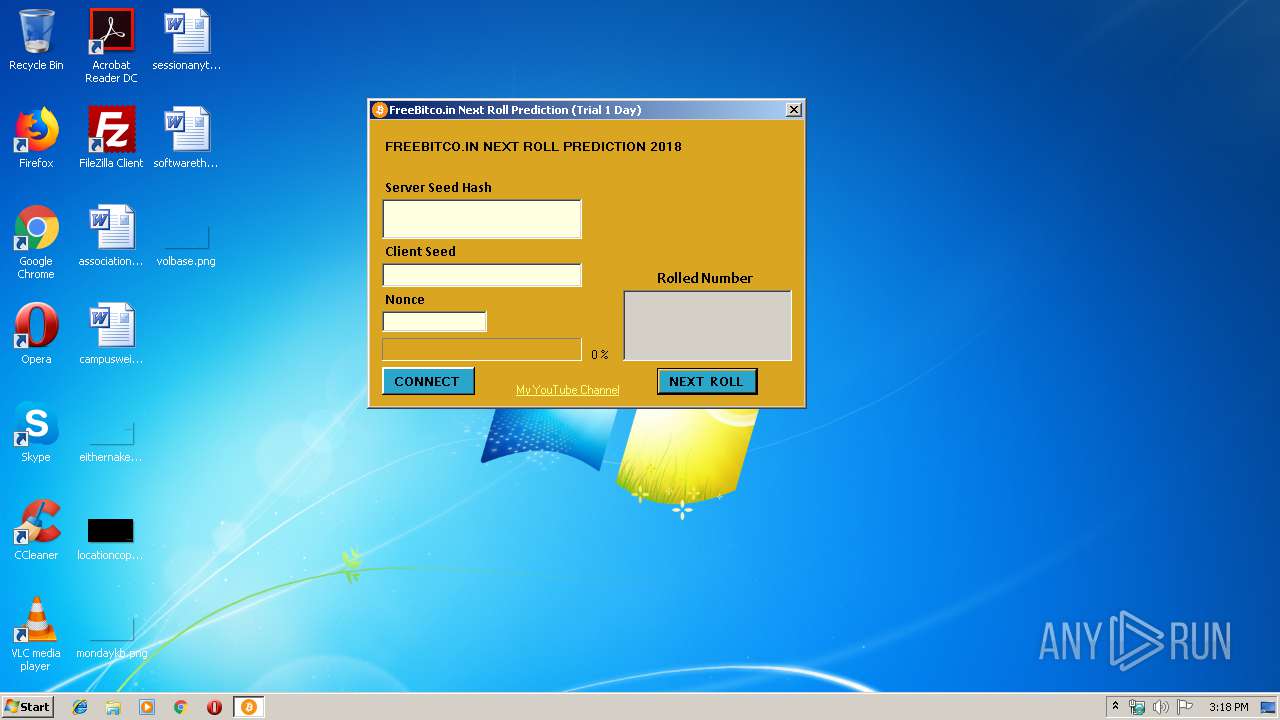
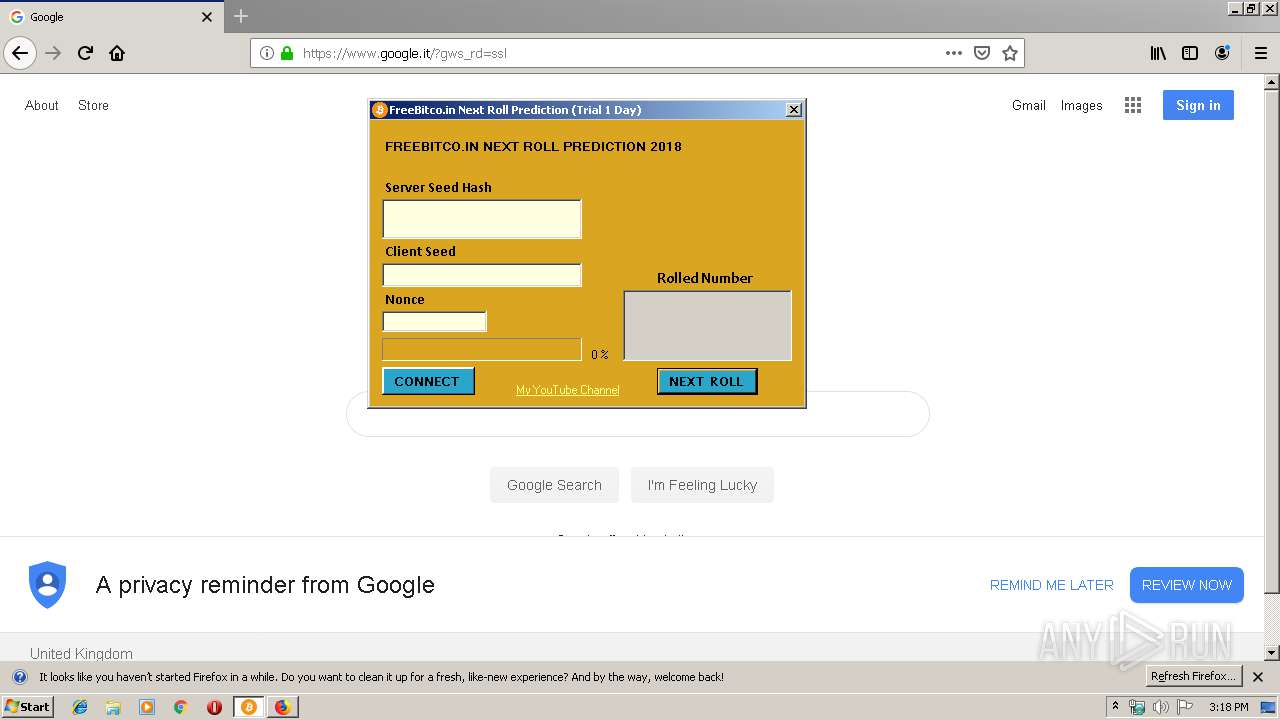
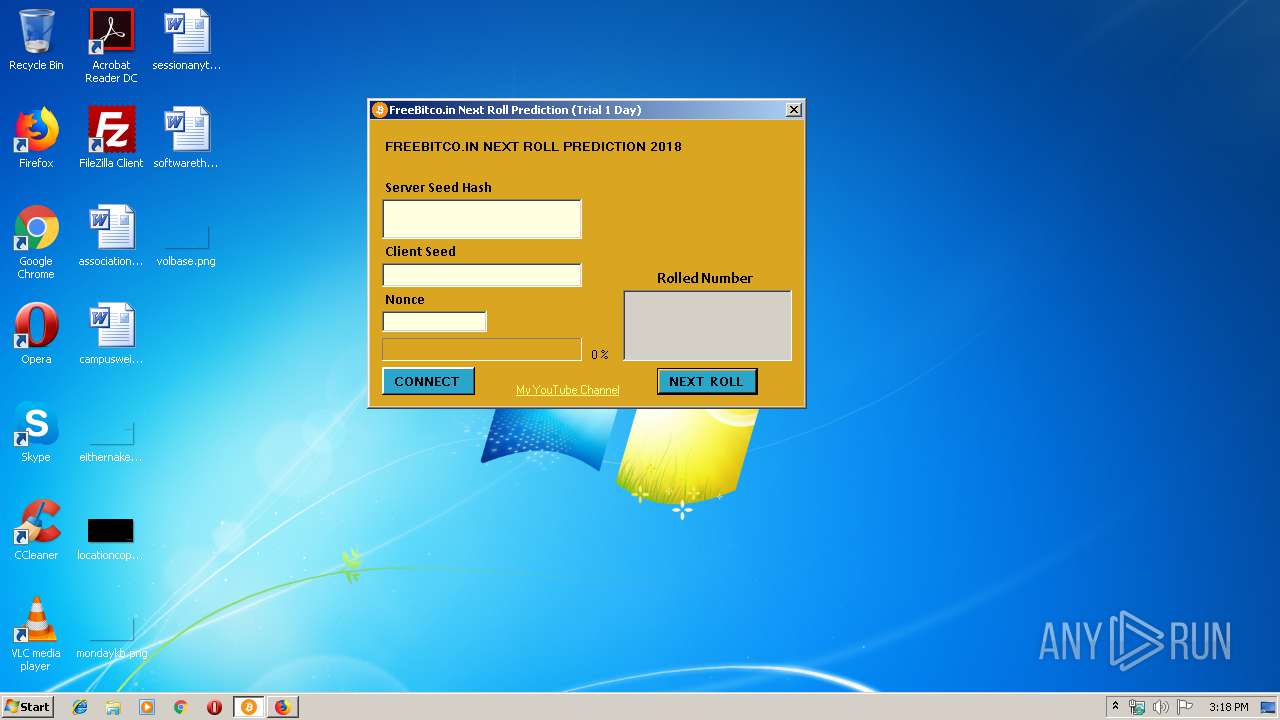
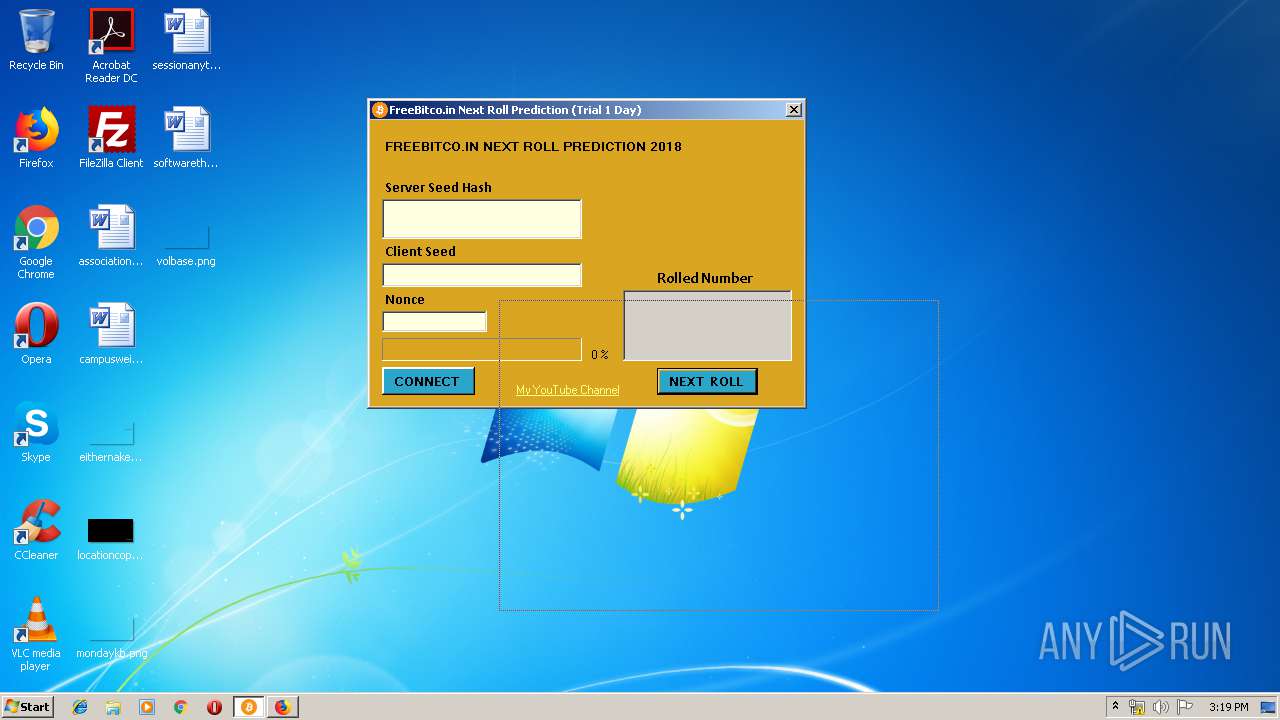
| File name: | FreeBitco.in Next Roll Prediction (Trial 1 Day).exe |
| Full analysis: | https://app.any.run/tasks/fcc87ca0-7021-4b61-b77e-1332b519ec7e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 14:17:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AFB30FED336E9B1E5E8EA5D941691B2A |
| SHA1: | AFEB330EA75DA11608BC4F32D3490ED38CFD4C11 |
| SHA256: | 16B4664969CE27B9914DC9D41B5BAA16A341E00F442527EFFFD478A73A014FA1 |
| SSDEEP: | 24576:MAHnh+eWsN3skA4RV1Hom2KXMmHaYfNZ8tvDej5:rh+ZkldoPK8YaYlZ81q |
MALICIOUS
Application was dropped or rewritten from another process
- gons.exe (PID: 2812)
- temp5789e.exe (PID: 2936)
SUSPICIOUS
Creates files in the user directory
- FreeBitco.in Next Roll Prediction (Trial 1 Day).exe (PID: 2992)
Executable content was dropped or overwritten
- FreeBitco.in Next Roll Prediction (Trial 1 Day).exe (PID: 2992)
INFO
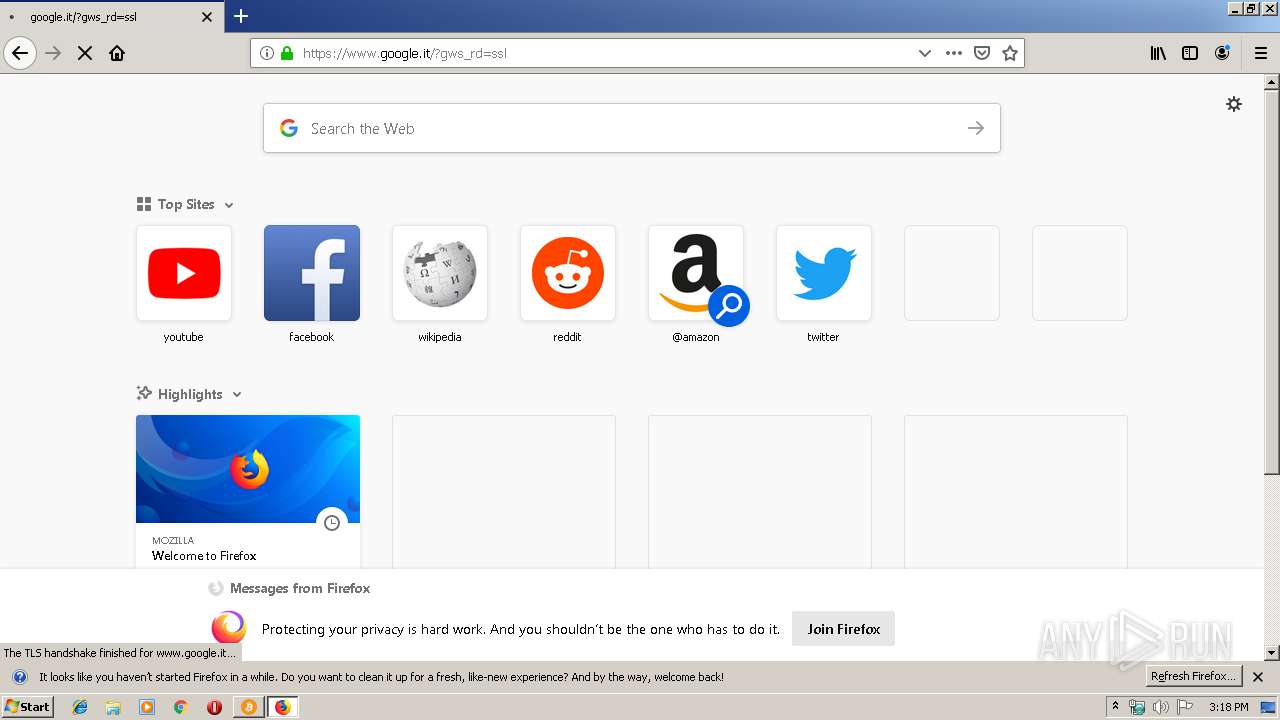
Manual execution by user
- firefox.exe (PID: 3596)
Application launched itself
- firefox.exe (PID: 3596)
Reads CPU info
- firefox.exe (PID: 3596)
Creates files in the user directory
- firefox.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:17 22:49:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 429568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2019 21:49:31 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Jan-2019 21:49:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x0002CA5F | 0x0002CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.92447 |
.reloc | 0x000F5000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
166 | 2.68292 | 80 | Latin 1 / Western European | English - United Kingdom | RT_MENU |
313 | 3.08572 | 344 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
32512 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
41
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2592 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3596.0.815785131\575403123" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3596 "\\.\pipe\gecko-crash-server-pipe.3596" 1160 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2812 | C:\Users\admin\AppData\Roaming\Microsoft\gons.exe | C:\Users\admin\AppData\Roaming\Microsoft\gons.exe | — | FreeBitco.in Next Roll Prediction (Trial 1 Day).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2936 | C:\Users\admin\AppData\Roaming\Microsoft\temp5789e.exe | C:\Users\admin\AppData\Roaming\Microsoft\temp5789e.exe | — | FreeBitco.in Next Roll Prediction (Trial 1 Day).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\FreeBitco.in Next Roll Prediction (Trial 1 Day).exe" | C:\Users\admin\AppData\Local\Temp\FreeBitco.in Next Roll Prediction (Trial 1 Day).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3596.20.2112329885\106043852" -childID 3 -isForBrowser -prefsHandle 3516 -prefMapHandle 3520 -prefsLen 6720 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3596 "\\.\pipe\gecko-crash-server-pipe.3596" 3532 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3596.13.566514545\1554117520" -childID 2 -isForBrowser -prefsHandle 2692 -prefMapHandle 2696 -prefsLen 5842 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3596 "\\.\pipe\gecko-crash-server-pipe.3596" 2708 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3596 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3788 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | temp5789e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3596.3.1996028407\62026843" -childID 1 -isForBrowser -prefsHandle 1276 -prefMapHandle 1608 -prefsLen 1 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3596 "\\.\pipe\gecko-crash-server-pipe.3596" 1584 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
Total events
478
Read events
475
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3596) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (3596) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3596) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
75
Text files
20
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | FreeBitco.in Next Roll Prediction (Trial 1 Day).exe | C:\Users\admin\AppData\Local\Temp\autDC58.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | FreeBitco.in Next Roll Prediction (Trial 1 Day).exe | C:\Users\admin\AppData\Local\Temp\autDC59.tmp | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\pluginreg.dat.tmp | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3596 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
36
DNS requests
89
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3596 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3596 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3596 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3596 | firefox.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3596 | firefox.exe | 172.217.16.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3596 | firefox.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3596 | firefox.exe | 172.217.16.163:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3596 | firefox.exe | 35.161.86.234:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3596 | firefox.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3596 | firefox.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3596 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod1-elb-eu-west-1.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |