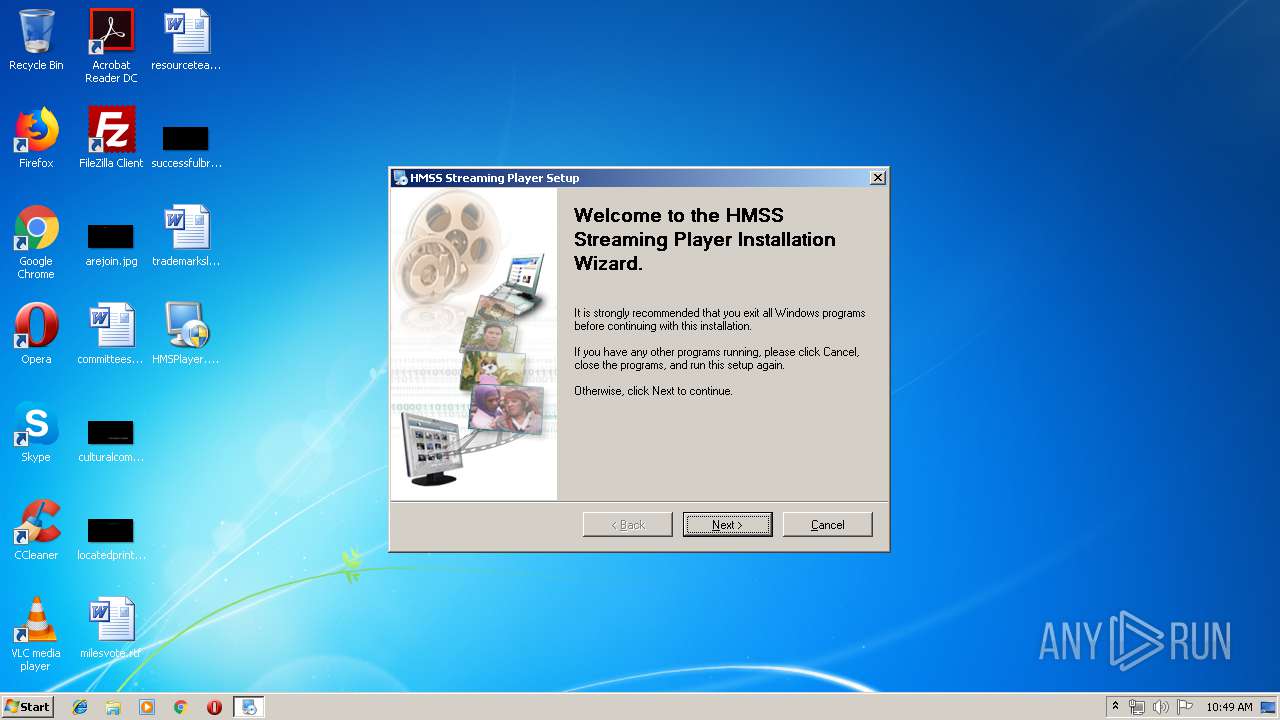
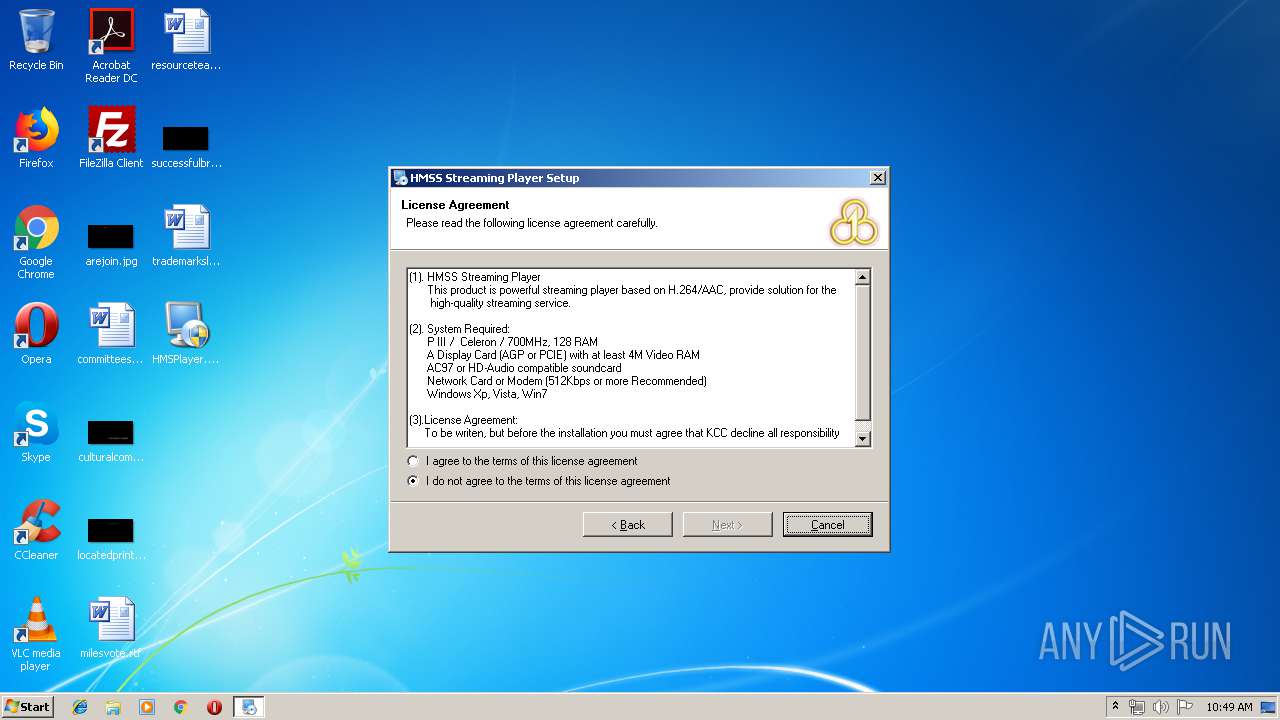
| File name: | HMSPlayer.exe |
| Full analysis: | https://app.any.run/tasks/ca0e8fb2-70b1-4c5f-af71-3d9f9d89f73d |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 09:49:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3A8FB8650431091EED653D51C23344EB |
| SHA1: | 6AE507E706F859129DF3D2E390A65A04877D8E28 |
| SHA256: | 169FB6966F3830380C2F0A70F683D53E694706C20F4390C57E99E4284F4B3C76 |
| SSDEEP: | 98304:vVffkDbJ9Dld6uxc0IqEN1xwR1f/pOOngiOg10QxBn/B6hxvWbrtUTrUHOA:vKDNRj6uGFqENQpz/bxhkx+NcIOA |
MALICIOUS
Application was dropped or rewritten from another process
- @AE3F29.tmp.exe (PID: 392)
- WdExt.exe (PID: 948)
- HMSPlayer.exe (PID: 1556)
- irsetup.exe (PID: 3100)
- launch.exe (PID: 1336)
- wtmps.exe (PID: 2536)
- support.exe (PID: 2112)
- HMSPlayer.exe (PID: 4060)
Application was injected by another process
- explorer.exe (PID: 2044)
Loads dropped or rewritten executable
- wtmps.exe (PID: 2536)
- WdExt.exe (PID: 948)
- mscaps.exe (PID: 1700)
- irsetup.exe (PID: 3100)
- explorer.exe (PID: 2044)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 252)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 1496)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 944)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 1464)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 908)
- @AE3F29.tmp.exe (PID: 392)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 636)
- chrome.exe (PID: 1356)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 2500)
Changes the autorun value in the registry
- launch.exe (PID: 1336)
- mscaps.exe (PID: 1700)
- support.exe (PID: 2112)
Runs injected code in another process
- launch.exe (PID: 1336)
SUSPICIOUS
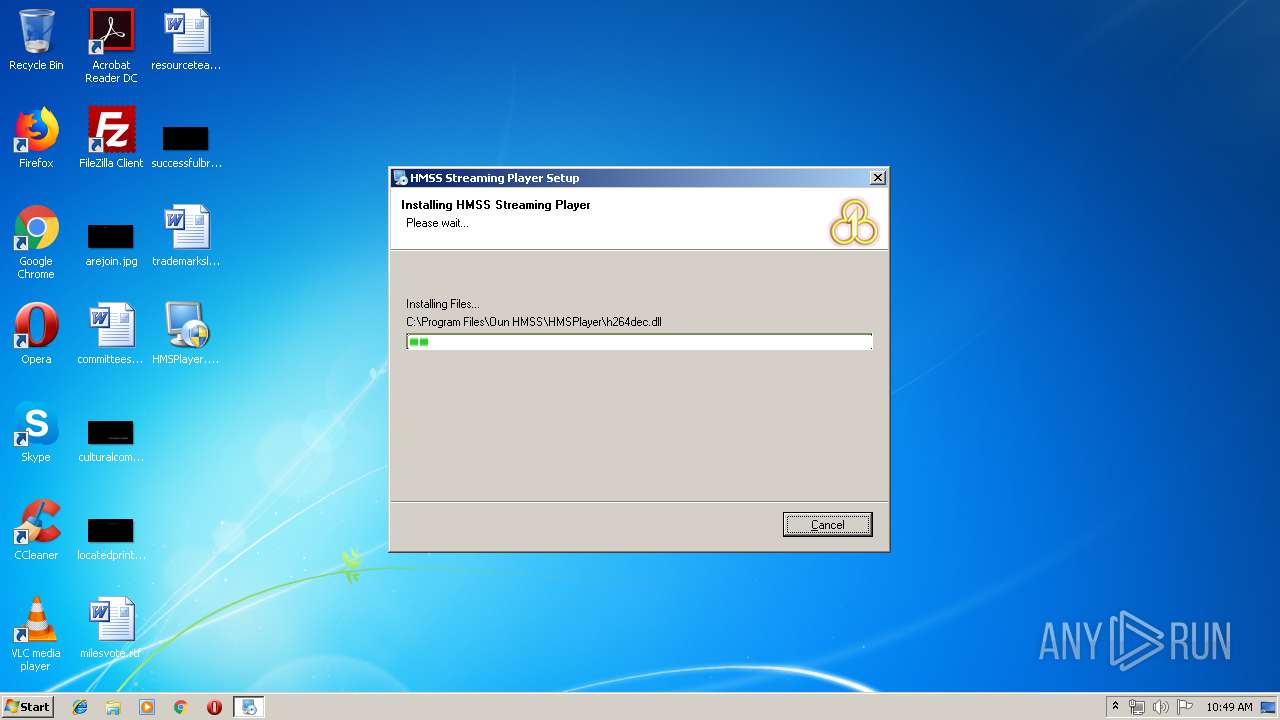
Executable content was dropped or overwritten
- explorer.exe (PID: 808)
- HMSPlayer.exe (PID: 1556)
- WdExt.exe (PID: 948)
- irsetup.exe (PID: 3100)
- mscaps.exe (PID: 1700)
- support.exe (PID: 2112)
- msiexec.exe (PID: 3332)
- @AE3F29.tmp.exe (PID: 392)
Creates files in the user directory
- @AE3F29.tmp.exe (PID: 392)
- launch.exe (PID: 1336)
- WdExt.exe (PID: 948)
- wtmps.exe (PID: 2536)
- mscaps.exe (PID: 1700)
- irsetup.exe (PID: 3100)
Starts CMD.EXE for commands execution
- @AE3F29.tmp.exe (PID: 392)
- WdExt.exe (PID: 948)
- launch.exe (PID: 1336)
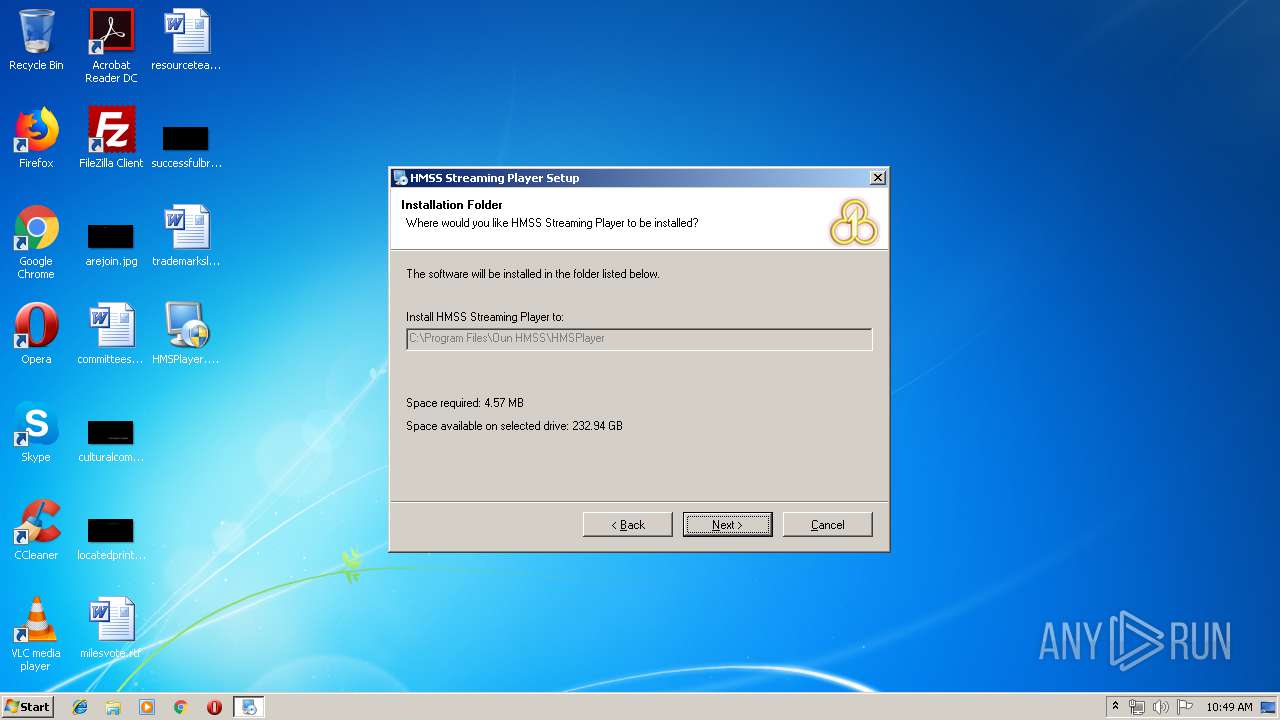
Creates files in the program directory
- irsetup.exe (PID: 3100)
Modifies the open verb of a shell class
- irsetup.exe (PID: 3100)
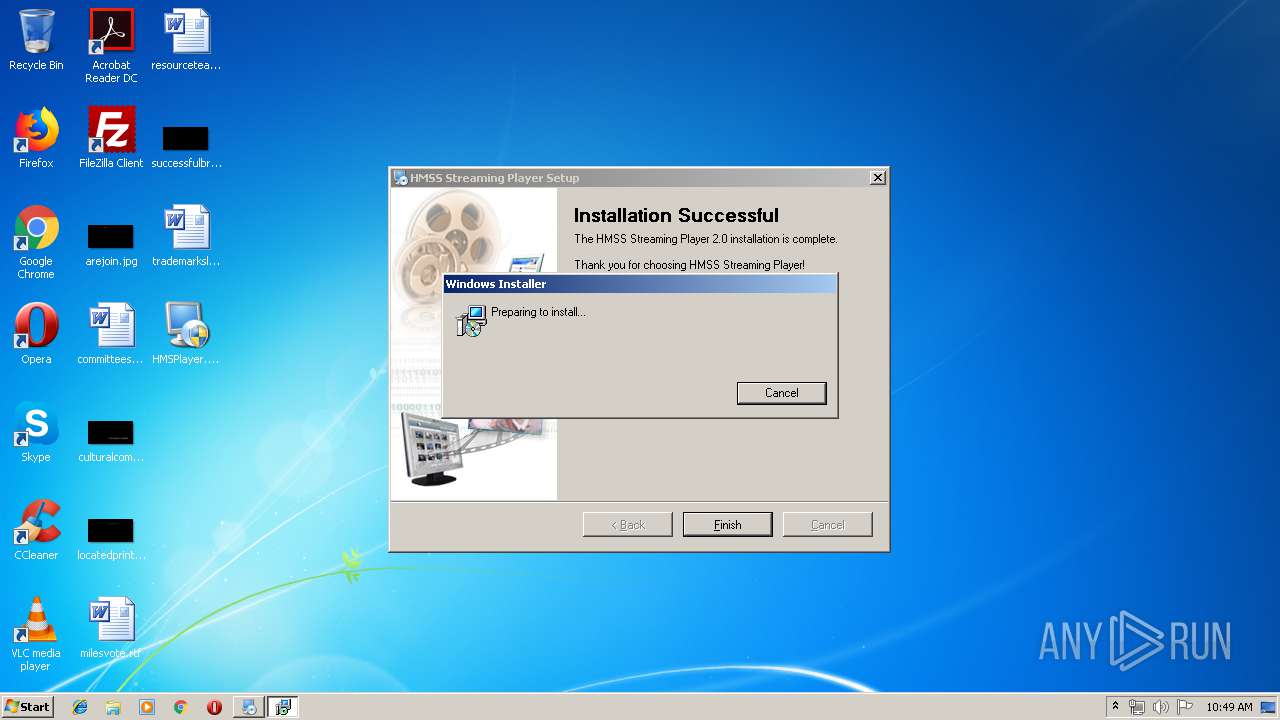
Creates a software uninstall entry
- irsetup.exe (PID: 3100)
Removes files from Windows directory
- msiexec.exe (PID: 3332)
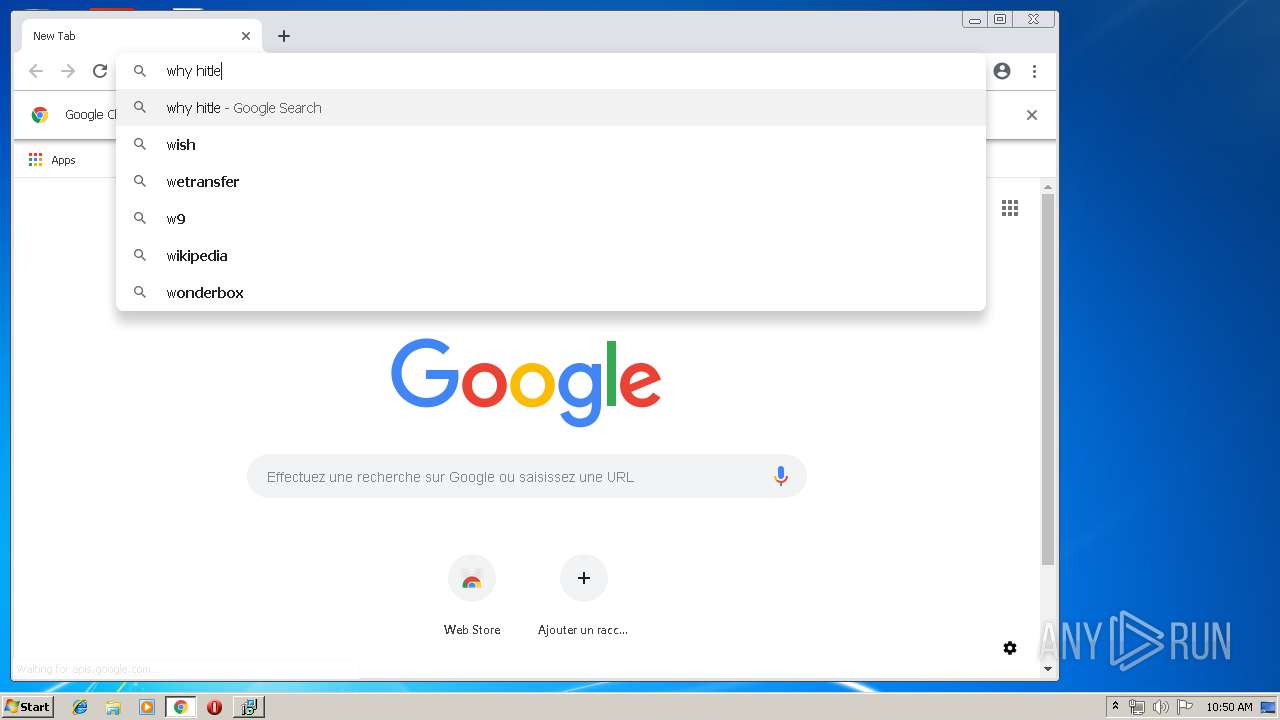
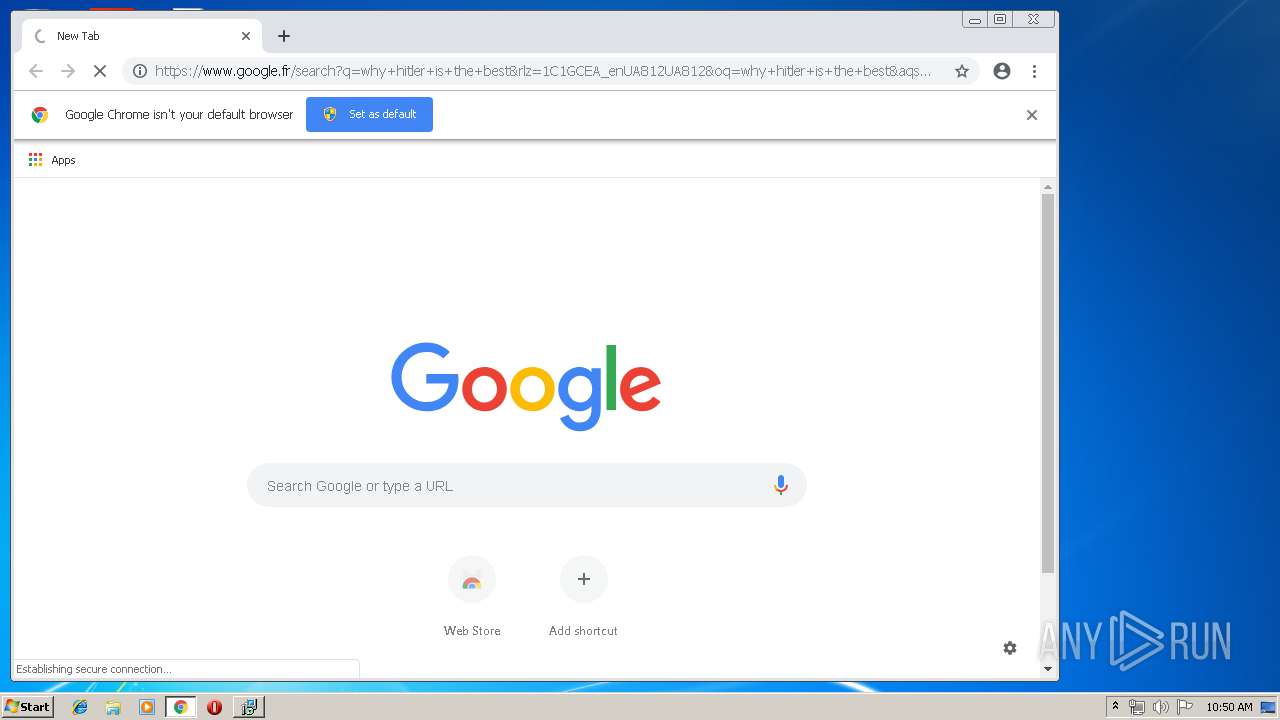
Modifies files in Chrome extension folder
- chrome.exe (PID: 3404)
Creates files in the Windows directory
- msiexec.exe (PID: 3332)
INFO
Dropped object may contain Bitcoin addresses
- irsetup.exe (PID: 3100)
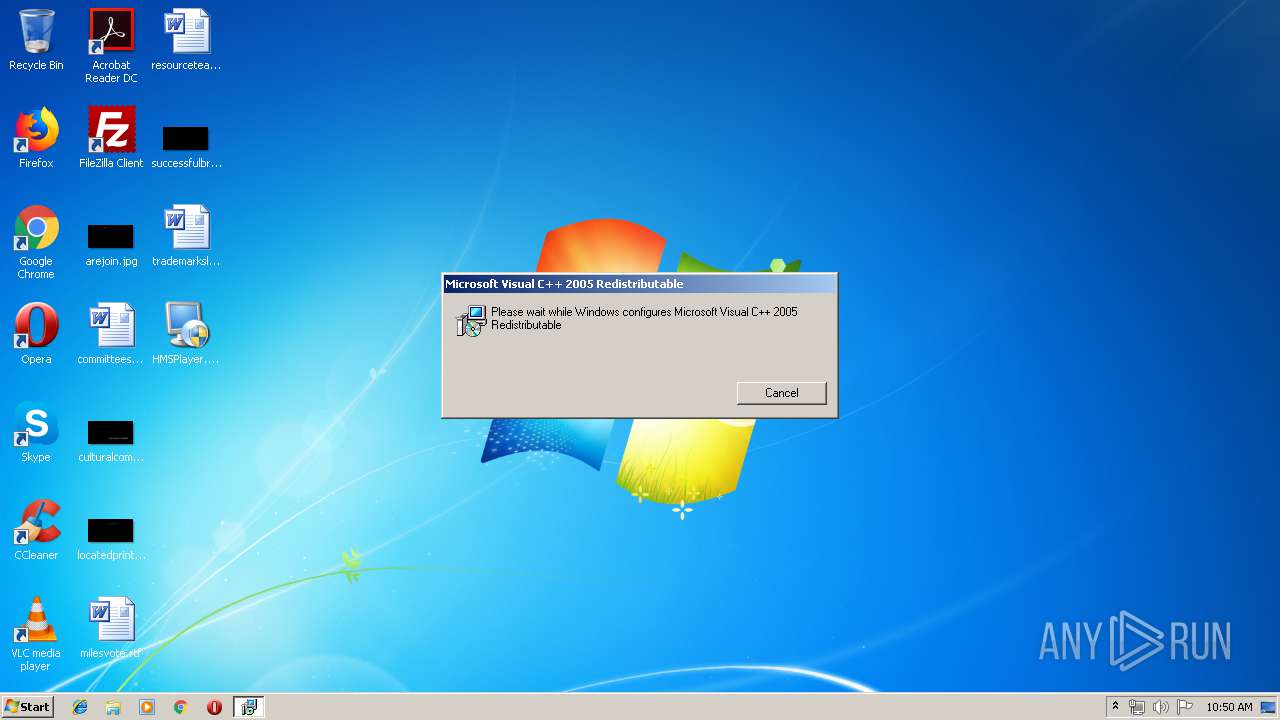
Searches for installed software
- msiexec.exe (PID: 3332)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1140)
Application launched itself
- chrome.exe (PID: 3404)
- msiexec.exe (PID: 3332)
Changes settings of System certificates
- DrvInst.exe (PID: 1804)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1804)
Creates files in the program directory
- msiexec.exe (PID: 3332)
Creates a software uninstall entry
- msiexec.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (29.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (21.7) |
| .exe | | | Win64 Executable (generic) (19.2) |
| .exe | | | Win32 EXE Yoda's Crypter (18.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:03:05 09:37:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2560 |
| InitializedDataSize: | 30208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x167f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.4.0 |
| ProductVersionNumber: | 9.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.0.4.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2012 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.0.4.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Mar-2012 08:37:55 |
| Detected languages: |
|
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.0.4.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2012 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.0.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Mar-2012 08:37:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000083C | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.43891 |
.rdata | 0x00002000 | 0x000005C6 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.85919 |
.data | 0x00003000 | 0x00009000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.545274 |
.rsrc | 0x0000C000 | 0x00006D70 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.82138 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87635 | 328 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.31421 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.9477 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.78233 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.14953 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.83714 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.64397 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.84115 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.41049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
Total processes
79
Monitored processes
40
Malicious processes
13
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11654373416833993870,17861553878684113587,131072 --enable-features=PasswordImport --service-pipe-token=14579171150579117157 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14579171150579117157 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\@AE3F29.tmp.exe" | C:\Users\admin\AppData\Local\Temp\@AE3F29.tmp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender Extension Exit code: 1 Version: 6.1.7600.16385 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11654373416833993870,17861553878684113587,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14854597162281665442 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14854597162281665442 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 704 | "C:\Users\admin\Desktop\HMSPlayer.exe" | C:\Users\admin\Desktop\HMSPlayer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 1 Version: 9.0.4.0 Modules
| |||||||||||||||
| 808 | explorer.exe | C:\Windows\explorer.exe | HMSPlayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11654373416833993870,17861553878684113587,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9258511998512242207 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9258511998512242207 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11654373416833993870,17861553878684113587,131072 --enable-features=PasswordImport --service-pipe-token=5125275783499320114 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5125275783499320114 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 948 | "C:\Users\admin\AppData\Roaming\Microsoft\Messenger\Extension\WdExt.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Messenger\Extension\WdExt.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender Extension Exit code: 1 Version: 6.1.7600.16385 Modules
| |||||||||||||||
| 960 | cmd /c ""C:\Users\admin\AppData\Roaming\Temp\admin0.bat" " | C:\Windows\system32\cmd.exe | — | @AE3F29.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1140 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 747
Read events
4 039
Write events
690
Delete events
18
Modification events
| (PID) Process: | (808) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (808) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (392) @AE3F29.tmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\@AE3F29_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
64
Suspicious files
731
Text files
268
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 392 | @AE3F29.tmp.exe | C:\Users\admin\AppData\Local\Temp\tmp418A.tmp | — | |
MD5:— | SHA256:— | |||
| 392 | @AE3F29.tmp.exe | C:\Users\admin\AppData\Local\Temp\Sp43ED.tmp | — | |
MD5:— | SHA256:— | |||
| 392 | @AE3F29.tmp.exe | C:\Users\admin\AppData\Local\Temp\Se43EE.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp48ED.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp490D.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp491E.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp491F.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp492F.tmp | — | |
MD5:— | SHA256:— | |||
| 948 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp4930.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
45
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3404 | chrome.exe | GET | 200 | 173.194.135.102:80 | http://r1---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.234.157.254&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1556012532&mv=u&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3404 | chrome.exe | GET | 302 | 172.217.20.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2044 | explorer.exe | 151.80.13.35:53 | a.gwas.perl.sh | OVH SAS | FR | malicious |
3404 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.212.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.17.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.168.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.20.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.168.196:443 | www.google.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.17.67:443 | www.google.fr | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.17.98:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.211.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windowsupdate.microsoft.com |
| malicious |
update.microsoft.com |
| whitelisted |
a.gwas.perl.sh |
| malicious |
a6ppymYKqCxnxmeGBgaG6AaG6Ek.g.s |
| unknown |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |