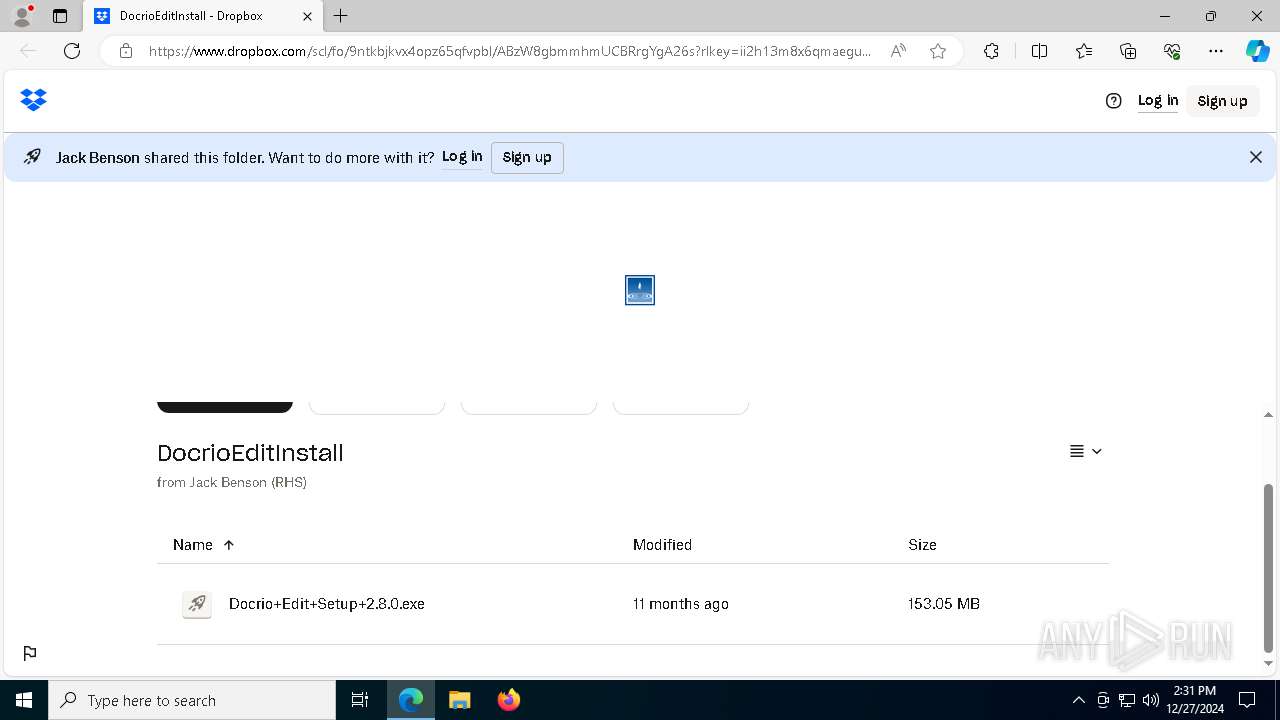
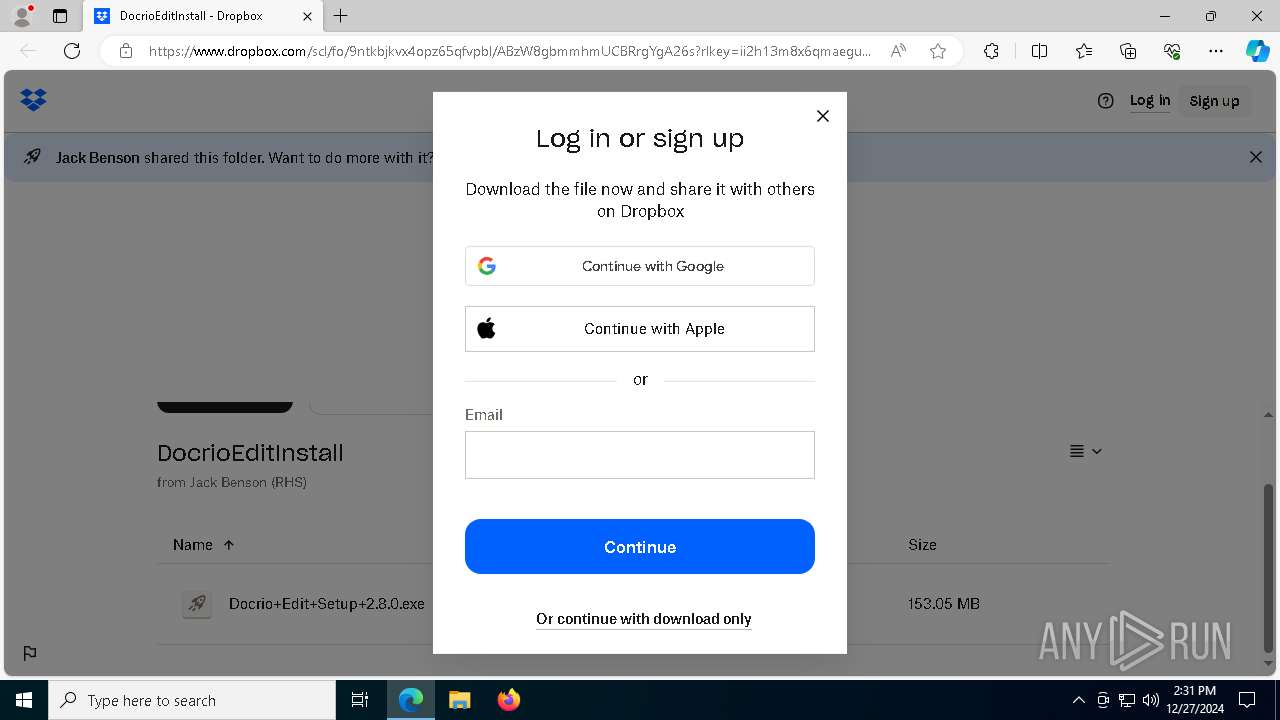
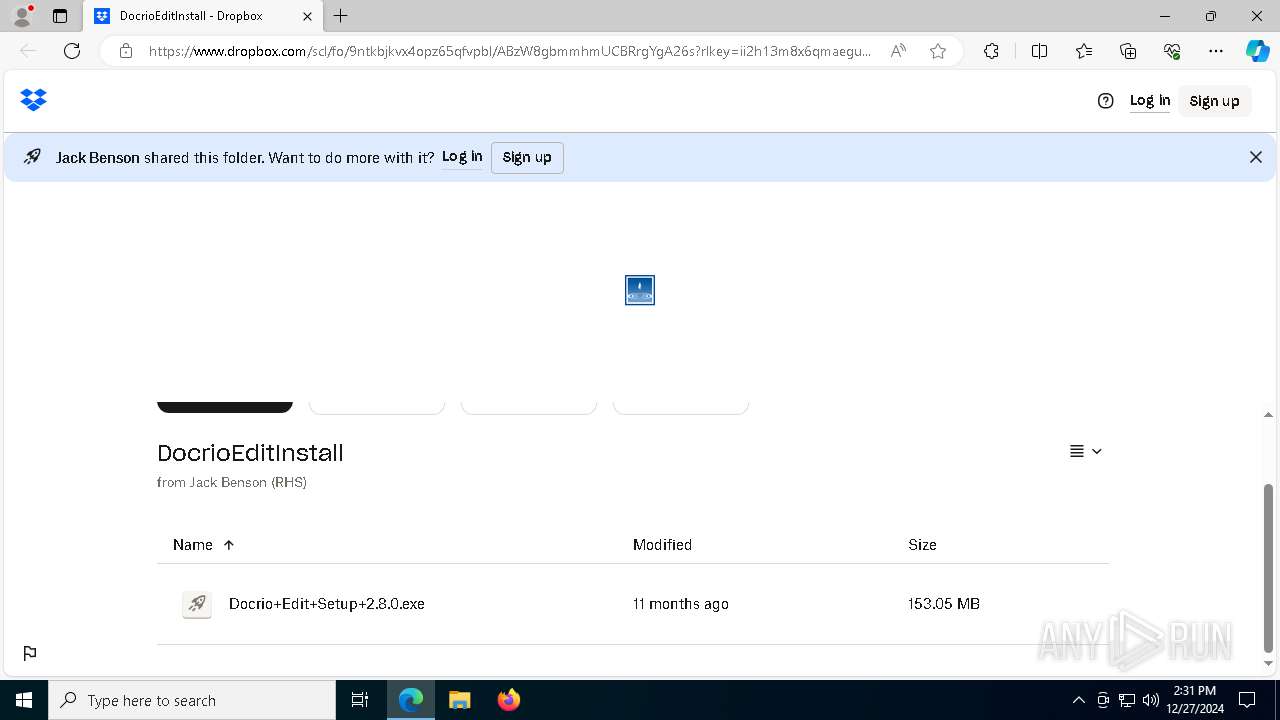
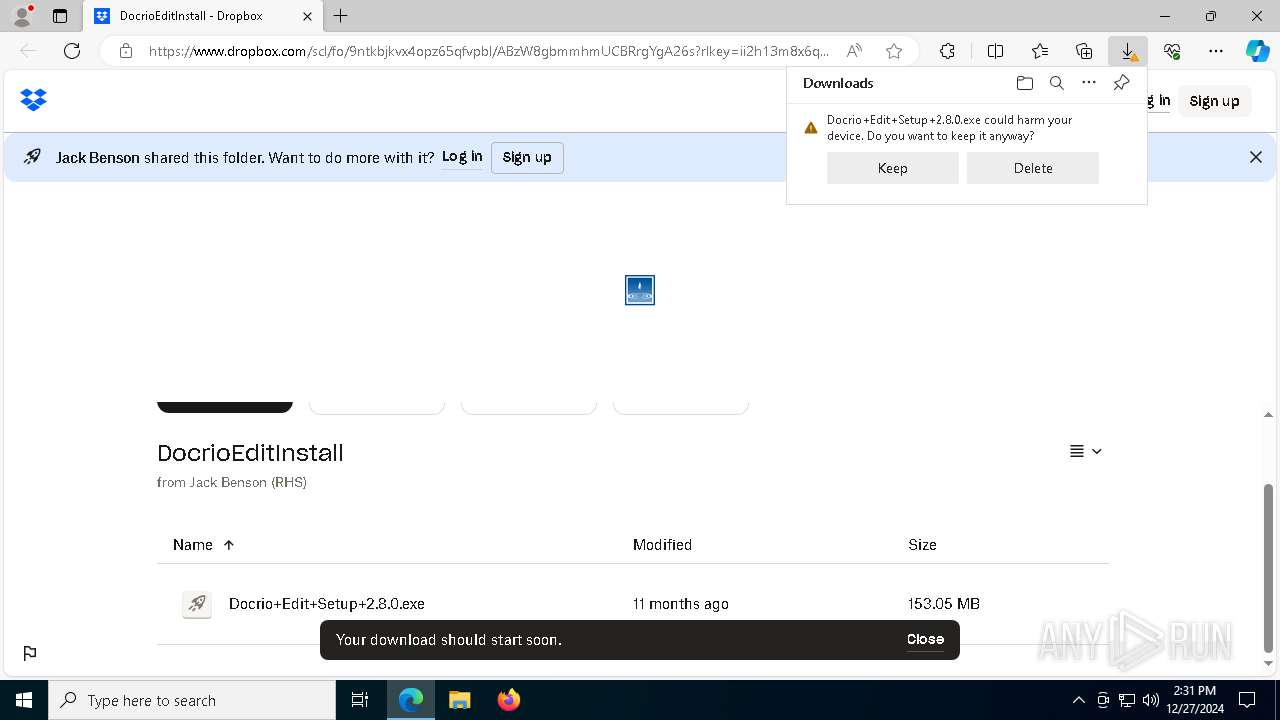
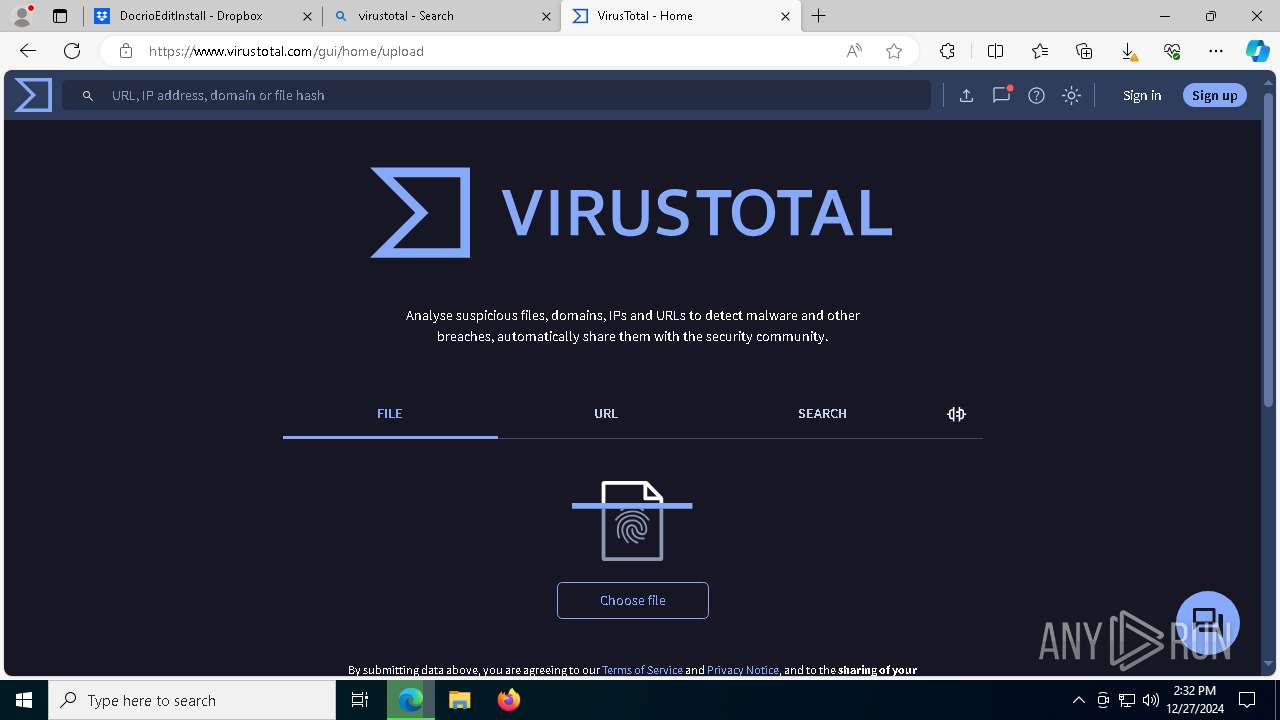
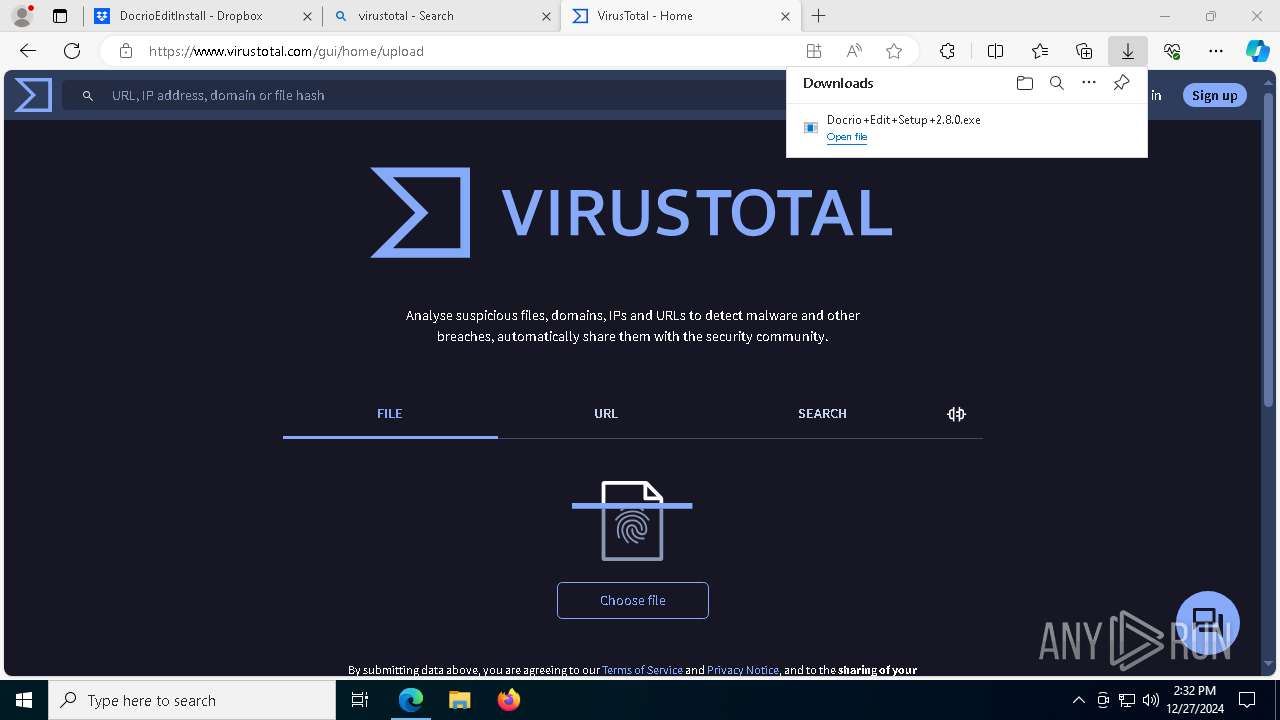
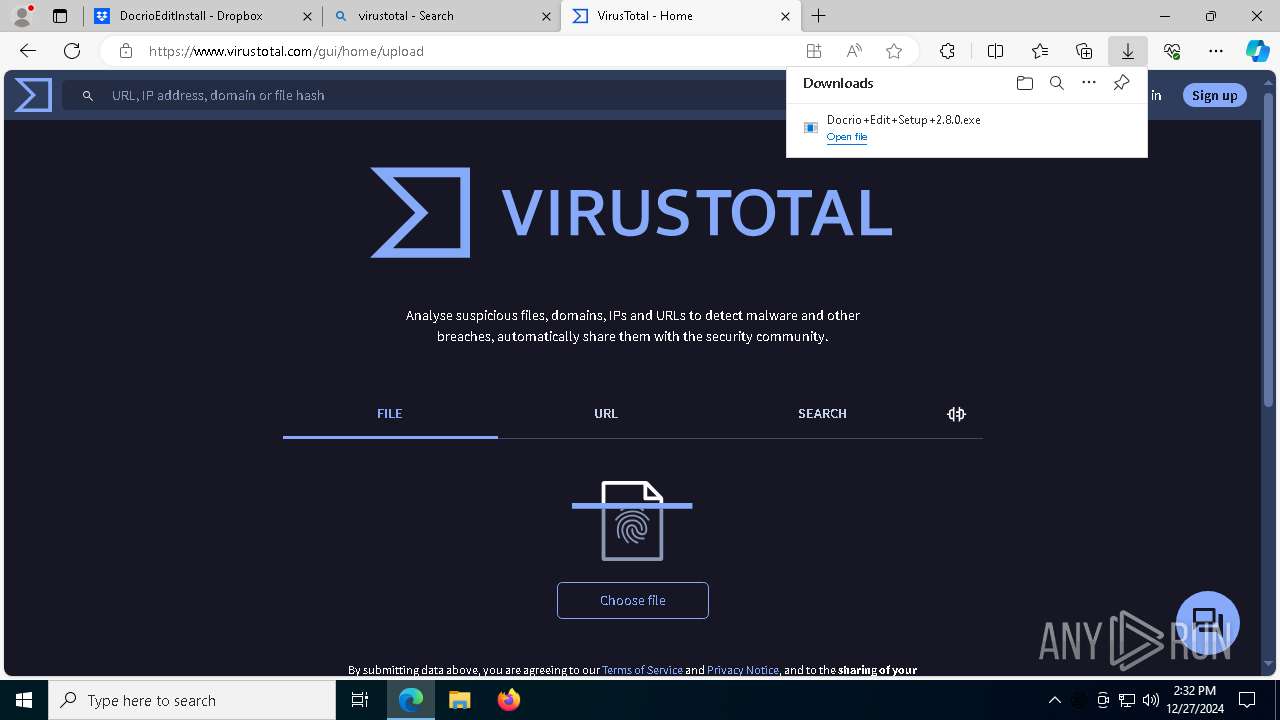
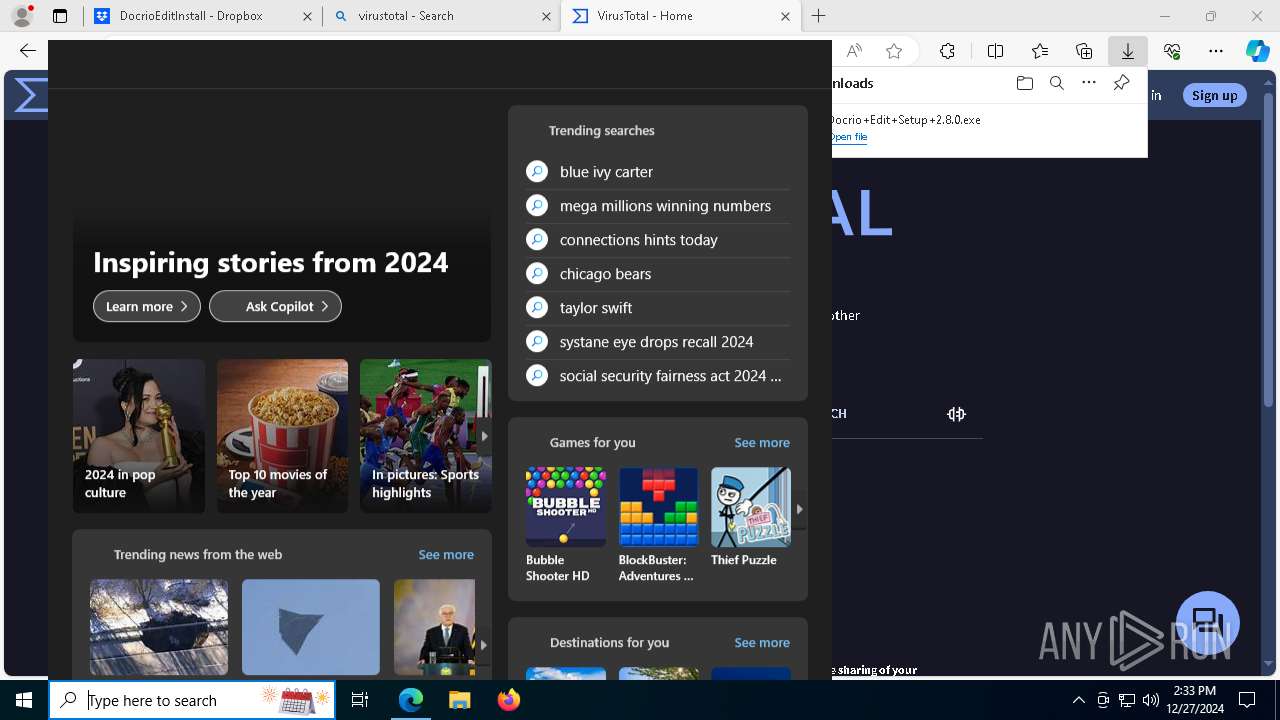
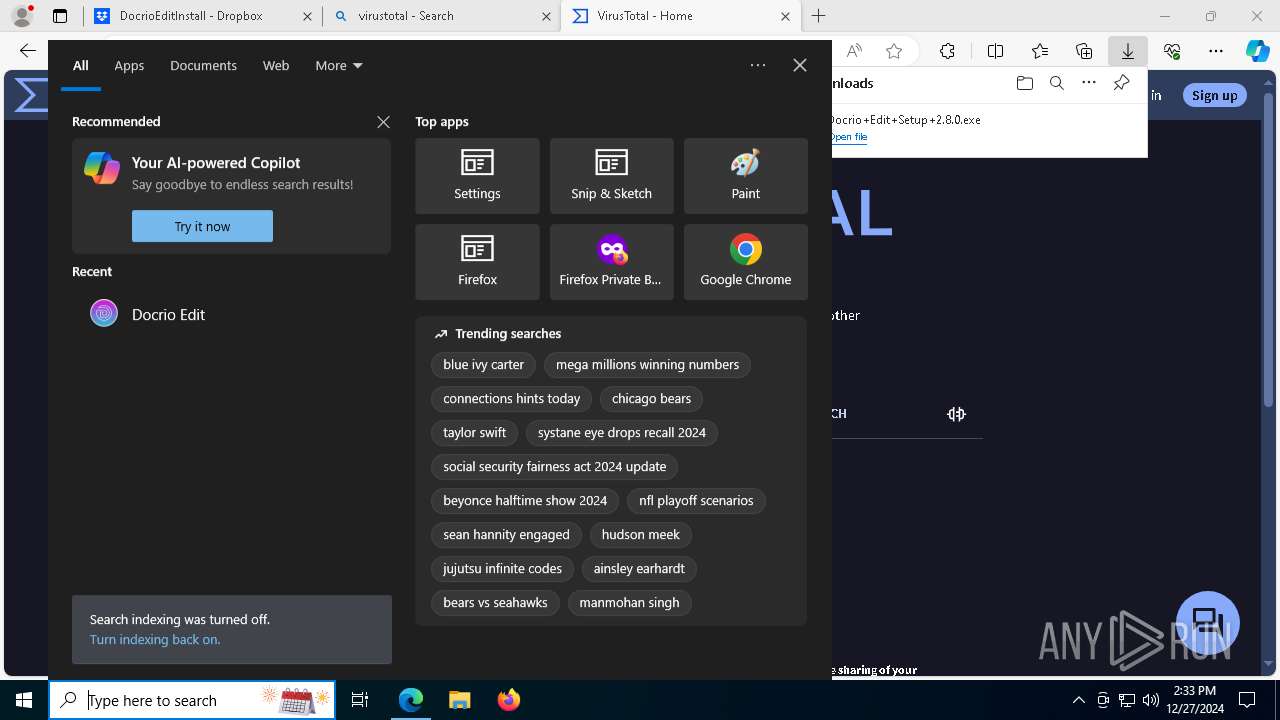
| URL: | https://www.dropbox.com/scl/fo/9ntkbjkvx4opz65qfvpbl/ABzW8gbmmhmUCBRrgYgA26s?rlkey=ii2h13m8x6qmaeguolaqmmokz&st=lr8j838b&dl=0 |
| Full analysis: | https://app.any.run/tasks/eca1db93-b7f8-4c65-8074-1820f4eaf5ce |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 14:31:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 703D0B579D276564FD89789B7972F658 |
| SHA1: | EECD7631DDF0948EEAF2947388A627E8DB652FF6 |
| SHA256: | 169E0018D78BB3CE3B01AB02CD749FF77FBBCB42A8D0E99C416A3E90EB1BC5C1 |
| SSDEEP: | 3:N8DSLcVHGkGMcUH1cUDTt4wIWKTdXP3PIfeAGKUI3OSed2DBSn:2OLHkRHuUDTt4wINffIffbR3pAn |
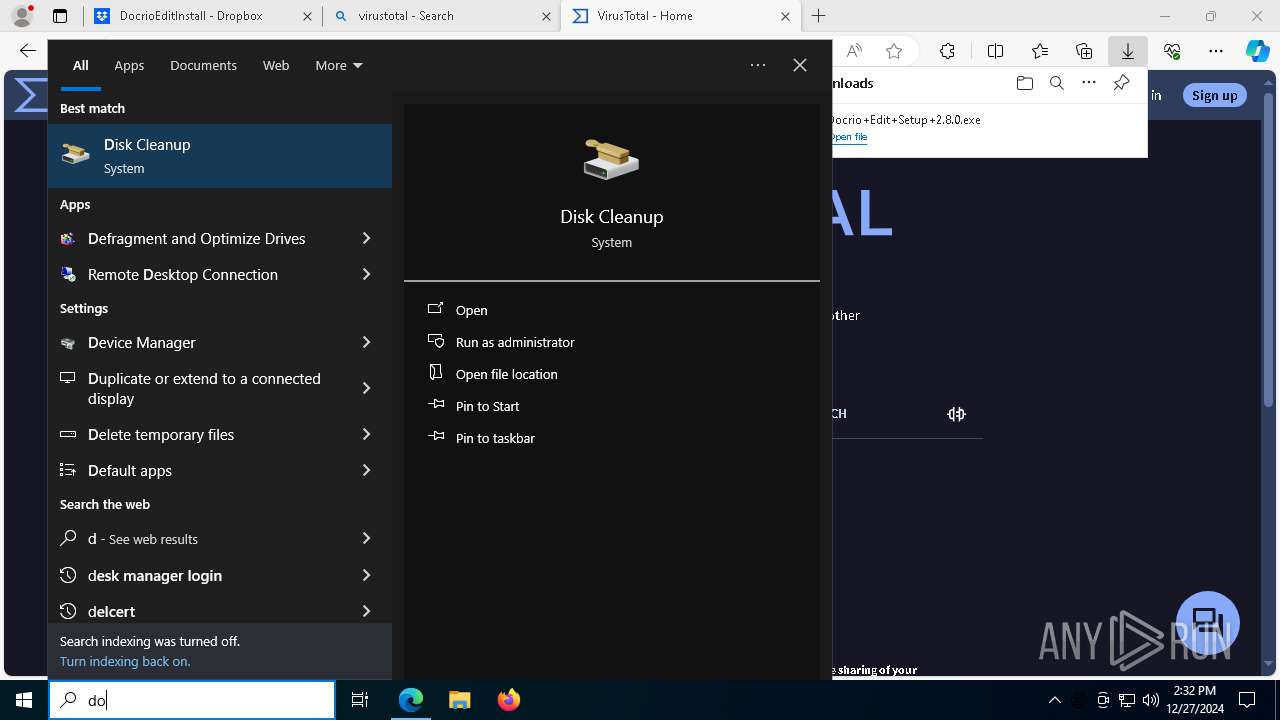
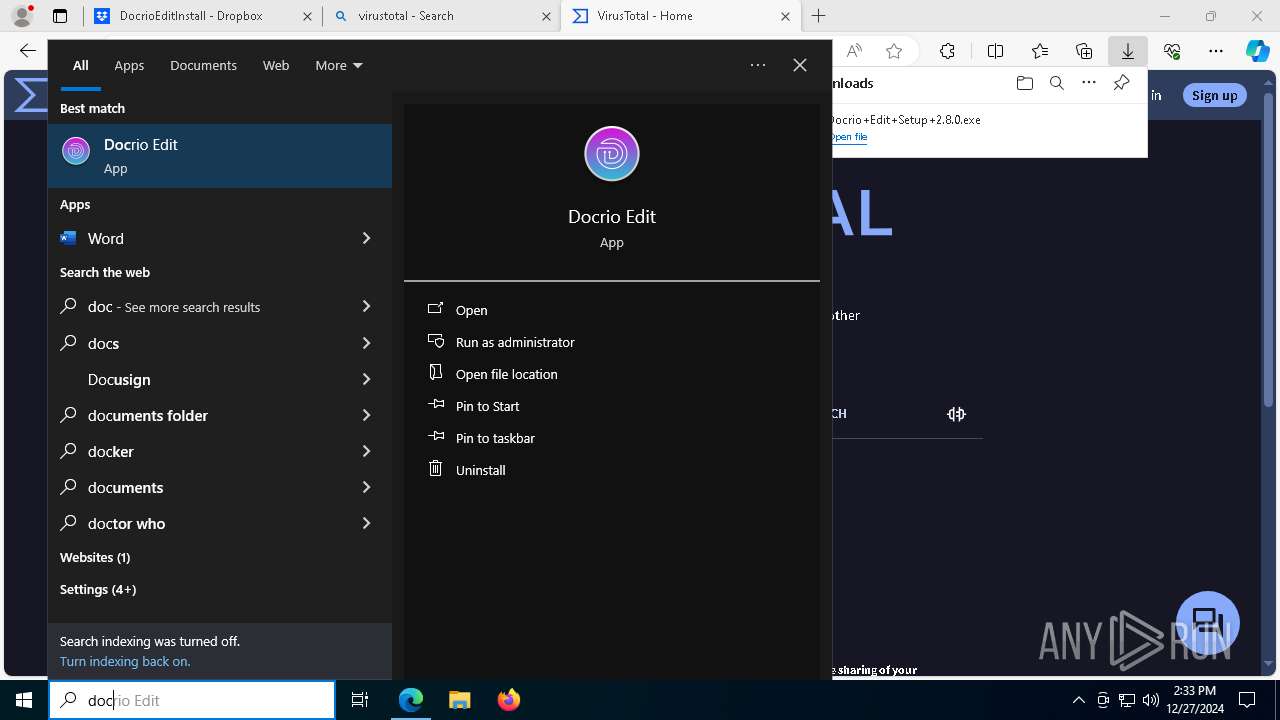
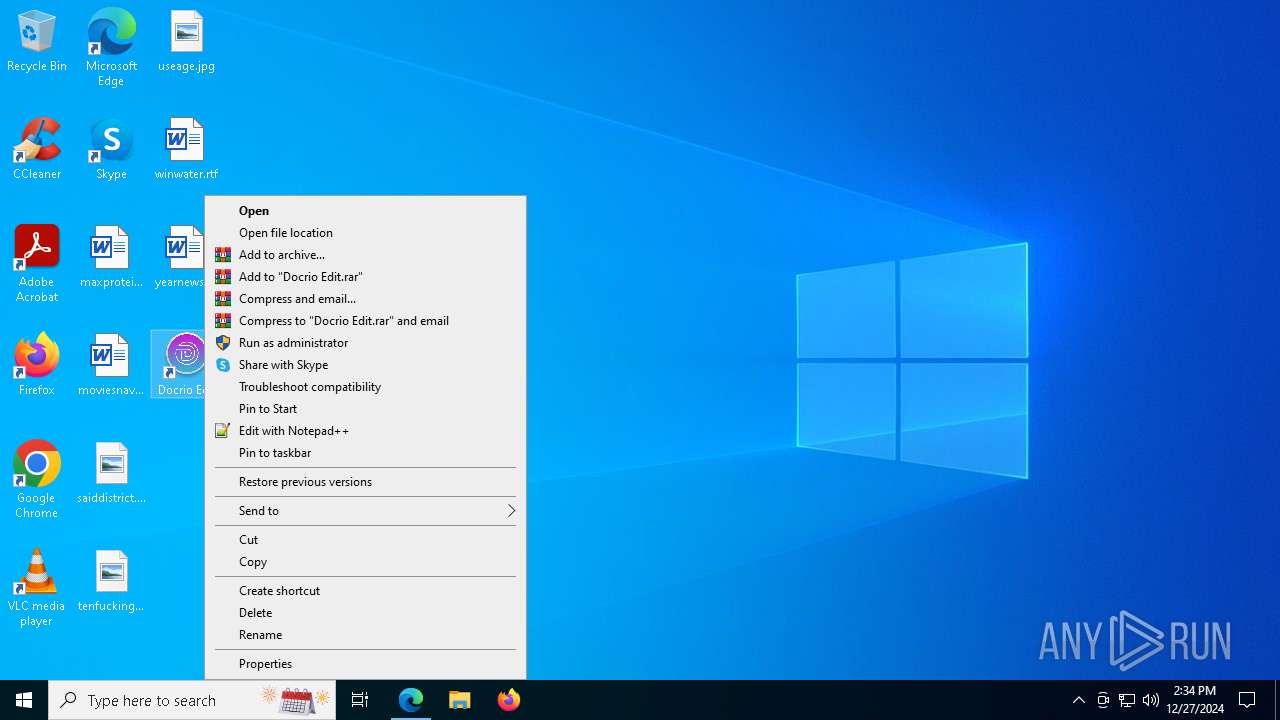
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 5096)
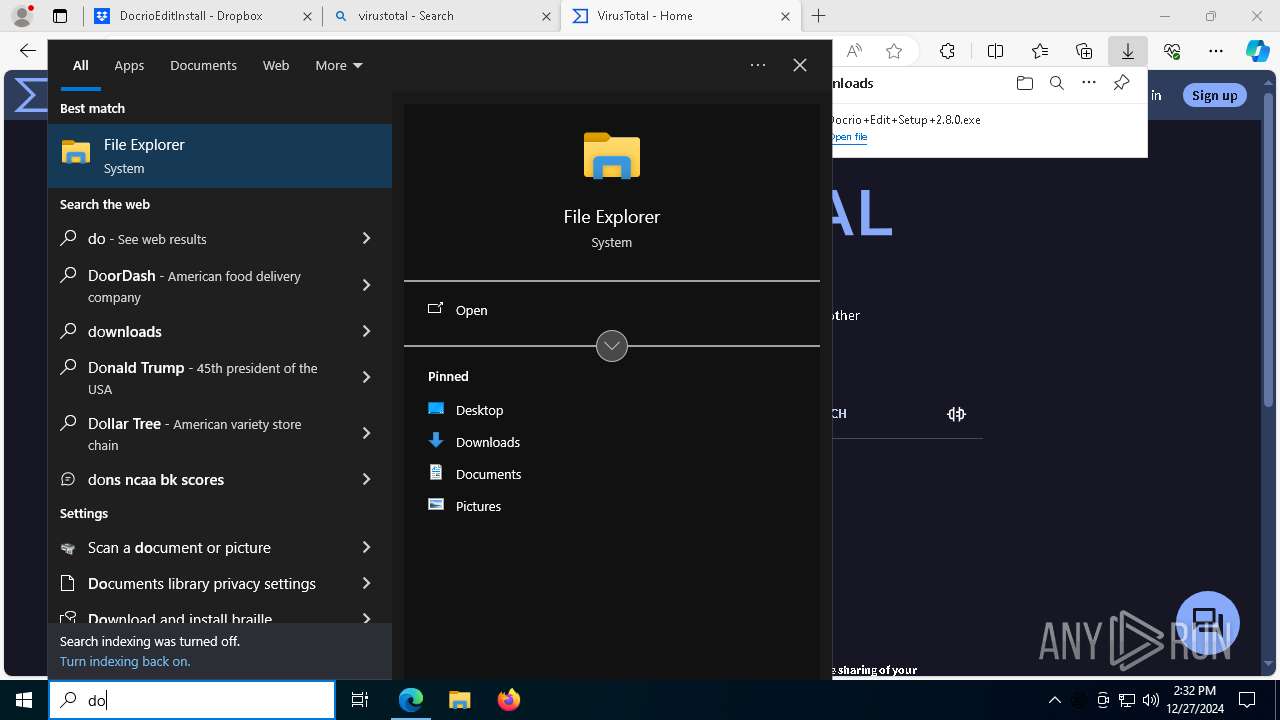
SUSPICIOUS
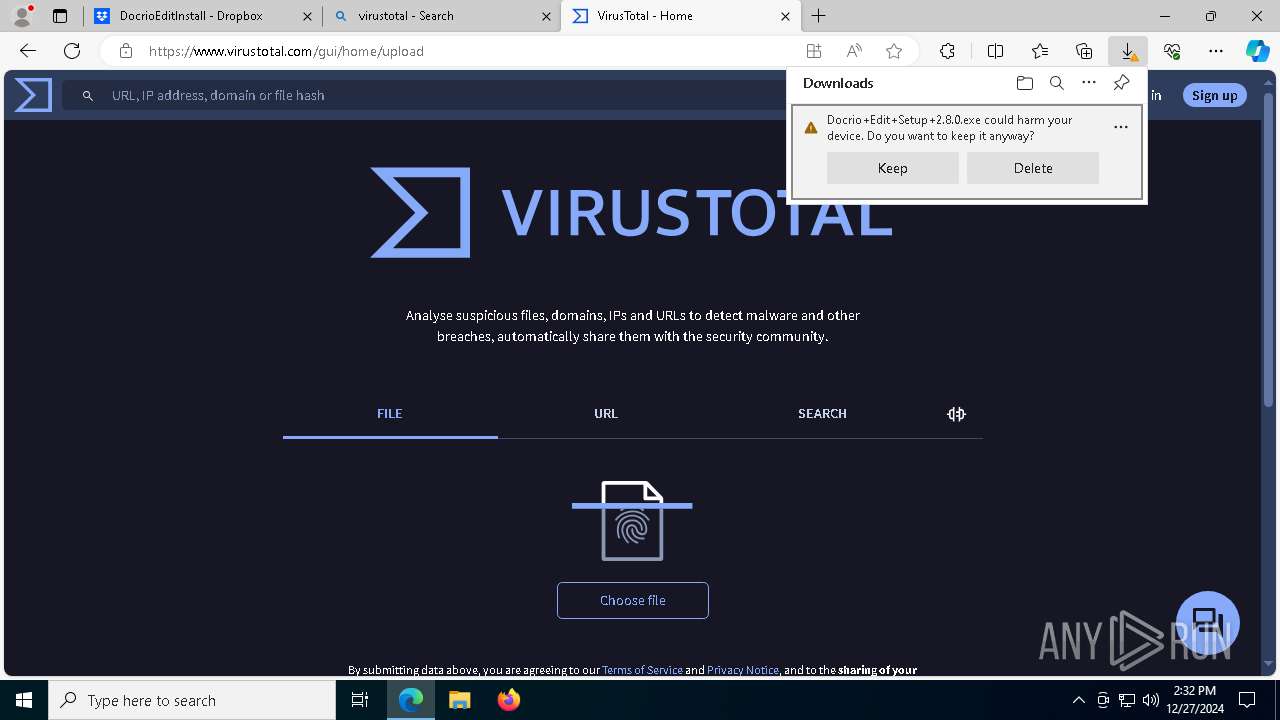
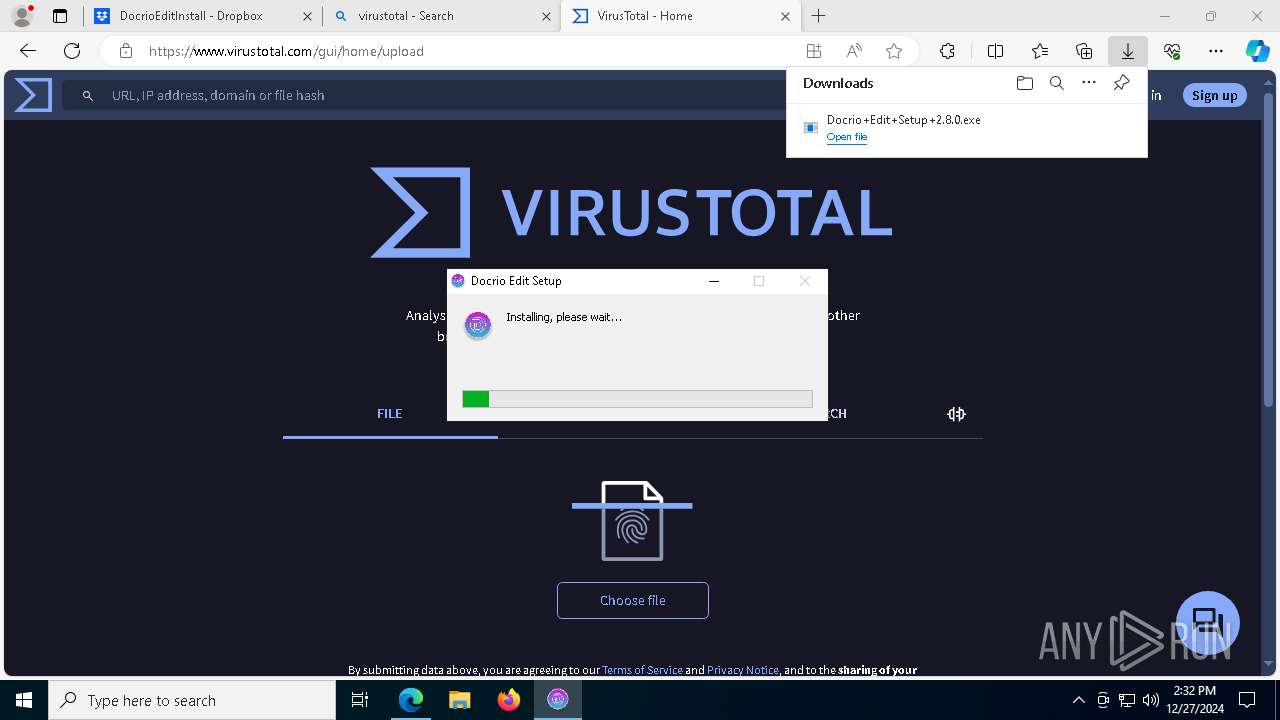
Malware-specific behavior (creating "System.dll" in Temp)
- Docrio+Edit+Setup+2.8.0.exe (PID: 7172)
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Executable content was dropped or overwritten
- Docrio+Edit+Setup+2.8.0.exe (PID: 7172)
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
The process creates files with name similar to system file names
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Reads security settings of Internet Explorer
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Drops 7-zip archiver for unpacking
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Process drops legitimate windows executable
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
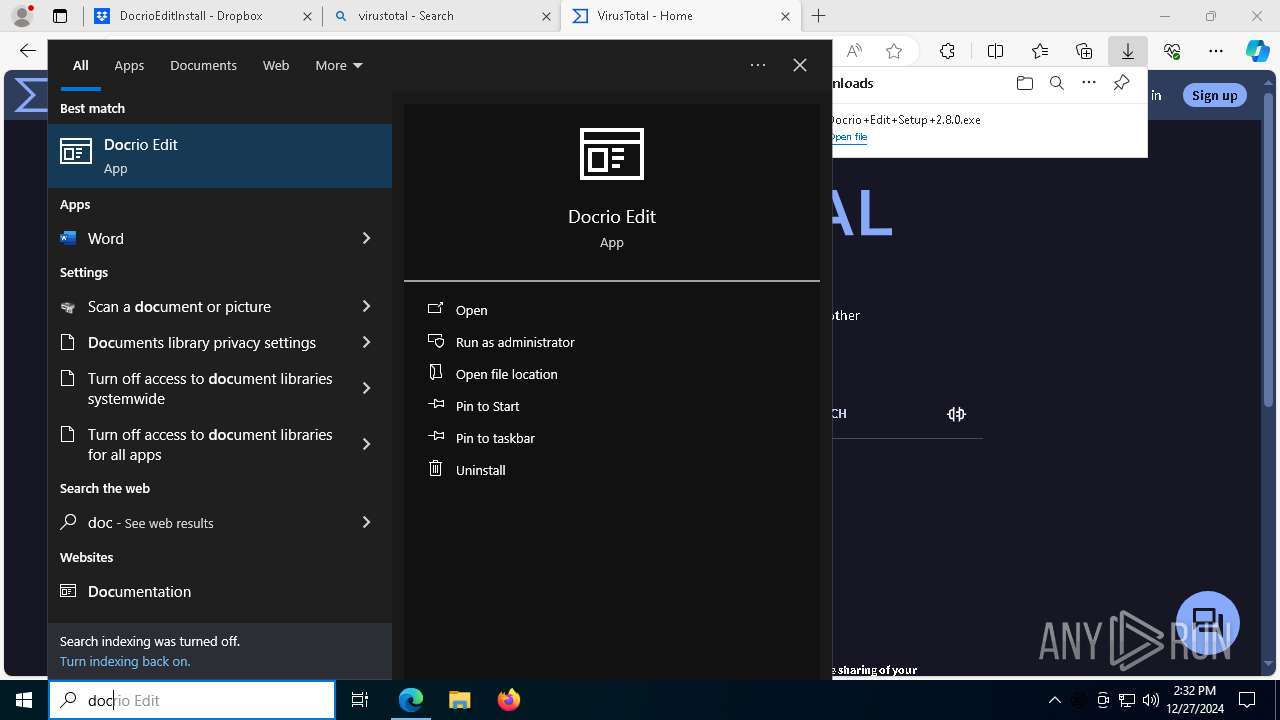
Application launched itself
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 2996)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 4388)
- Docrio Edit.exe (PID: 3544)
Uses REG/REGEDIT.EXE to modify registry
- Docrio Edit.exe (PID: 7584)
Get information on the list of running processes
- Docrio Edit.exe (PID: 7584)
Starts POWERSHELL.EXE for commands execution
- Docrio Edit.exe (PID: 7584)
INFO
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- Docrio Edit.exe (PID: 7748)
Checks supported languages
- identity_helper.exe (PID: 4716)
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
- Docrio+Edit+Setup+2.8.0.exe (PID: 7172)
- Docrio Edit.exe (PID: 5872)
- Docrio Edit.exe (PID: 7584)
- SearchApp.exe (PID: 5064)
- Docrio Edit.exe (PID: 2996)
- Docrio Edit.exe (PID: 4360)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 3544)
- Docrio Edit.exe (PID: 5096)
- Docrio Edit.exe (PID: 7748)
Reads Environment values
- identity_helper.exe (PID: 4716)
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 2996)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 3544)
- Docrio Edit.exe (PID: 4388)
Connects to unusual port
- msedge.exe (PID: 6372)
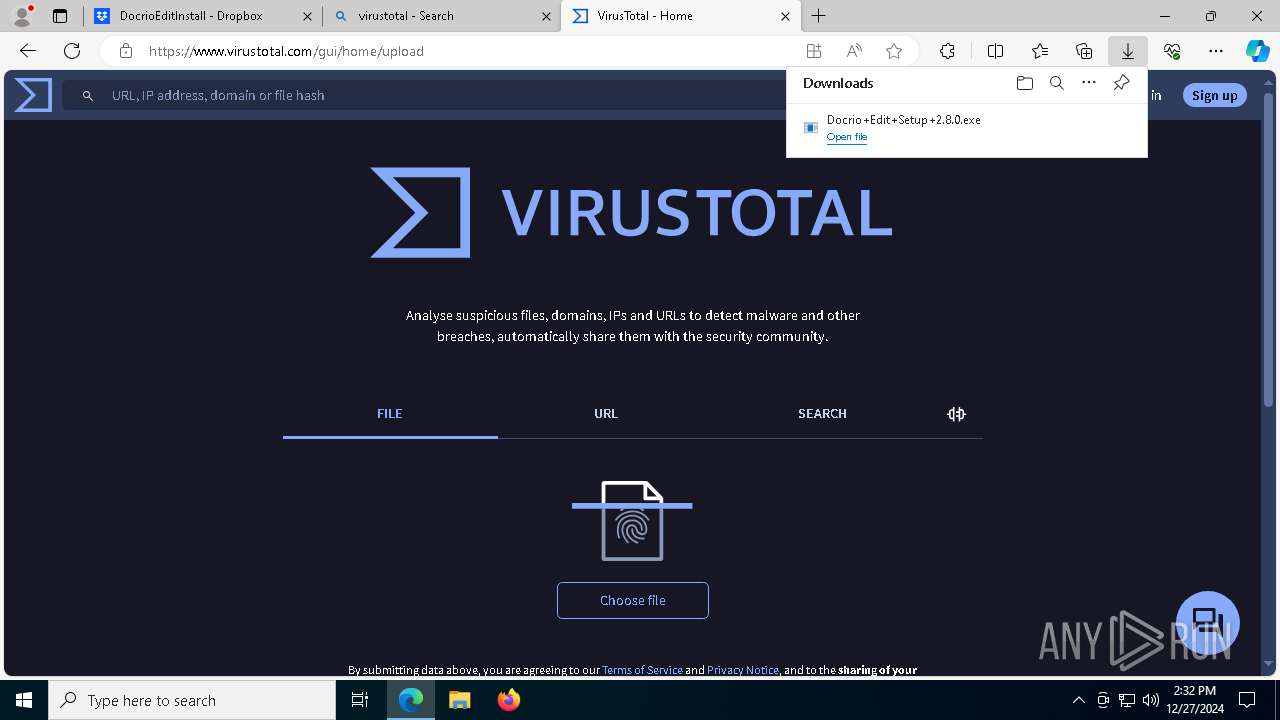
The process uses the downloaded file
- msedge.exe (PID: 4824)
- msedge.exe (PID: 6972)
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Reads the computer name
- identity_helper.exe (PID: 4716)
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 5872)
- Docrio Edit.exe (PID: 3172)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 4388)
- Docrio Edit.exe (PID: 7748)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- Docrio Edit.exe (PID: 7584)
The sample compiled with english language support
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
- msedge.exe (PID: 7524)
Create files in a temporary directory
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Application launched itself
- msedge.exe (PID: 4824)
Creates files in the program directory
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
Creates files or folders in the user directory
- Docrio+Edit+Setup+2.8.0.exe (PID: 5652)
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 5872)
- Docrio Edit.exe (PID: 2612)
- Docrio Edit.exe (PID: 4388)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 3544)
Reads product name
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 2996)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 3544)
- Docrio Edit.exe (PID: 4388)
Process checks computer location settings
- Docrio Edit.exe (PID: 7584)
- SearchApp.exe (PID: 5064)
Checks proxy server information
- Docrio Edit.exe (PID: 7584)
Manual execution by a user
- Docrio Edit.exe (PID: 7584)
- Docrio Edit.exe (PID: 2996)
- Docrio Edit.exe (PID: 7748)
- Docrio Edit.exe (PID: 3544)
- Docrio Edit.exe (PID: 4388)
Found Base64 encoded text manipulation via PowerShell (YARA)
- Docrio Edit.exe (PID: 7584)
Found Base64 encoded JSON usage via PowerShell (YARA)
- Docrio Edit.exe (PID: 7584)
Executable content was dropped or overwritten
- msedge.exe (PID: 7524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
115
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=8212 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 556 | powershell.exe /c "Get-CimInstance -className win32_process | select Name,ProcessId,ParentProcessId,CommandLine,ExecutablePath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Docrio Edit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5336 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\reg.exe QUERY HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Docrio Edit" | C:\Windows\System32\reg.exe | — | Docrio Edit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7488 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Docrio Edit\Docrio Edit.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\LitifyDocs" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1372 --field-trial-handle=1796,i,2037193597690957445,4383706437919949813,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files\Docrio Edit\Docrio Edit.exe | — | Docrio Edit.exe | |||||||||||
User: admin Company: Litify Integrity Level: LOW Description: Docrio Edit Exit code: 0 Version: 2.8.0 Modules
| |||||||||||||||
| 1304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8744 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7488 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4276 --field-trial-handle=2108,i,18264067479245504560,11067521716172883023,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 816
Read events
40 582
Write events
211
Delete events
23
Modification events
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 153E9298D7882F00 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 50111 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 000004BD6AF66B58DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 0000D6E66FF66B58DB01 | |||
Executable files
68
Suspicious files
1 790
Text files
390
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13549b.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1354ab.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
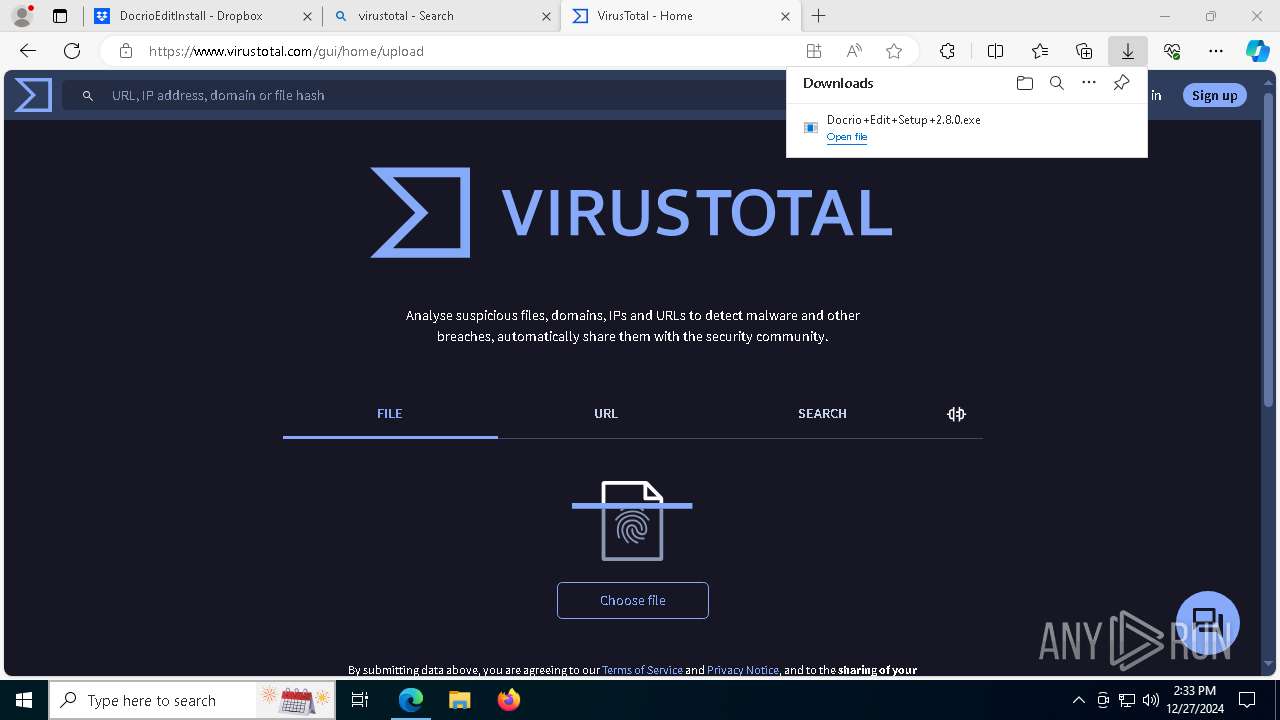
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
218
DNS requests
223
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
444 | svchost.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
444 | svchost.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7476 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7476 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6700 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
444 | svchost.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
444 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.110.139:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
4824 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |