| download: | usf.exe |
| Full analysis: | https://app.any.run/tasks/bb69db3f-3a17-4b38-a4b0-851041902a5e |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 21:04:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 311D64E4892F75019EE257B8377C723E |
| SHA1: | 694C1C80280A031095CC2FA567526E88FD800BF4 |
| SHA256: | 168E625C7EB51720F5CE1922AEC6AD316B3AACA838BD864EE2BCDBD9B66171D0 |
| SSDEEP: | 49152:j6OV5mDYOgJXTr/xvsFZIUjHu0UaZHIIxB3zfEJUqi5:jV5mrgJX3xvkXi9aZRKc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- usf.exe (PID: 672)
Uses RUNDLL32.EXE to load library
- usf.exe (PID: 672)
Reads the computer name
- usf.exe (PID: 672)
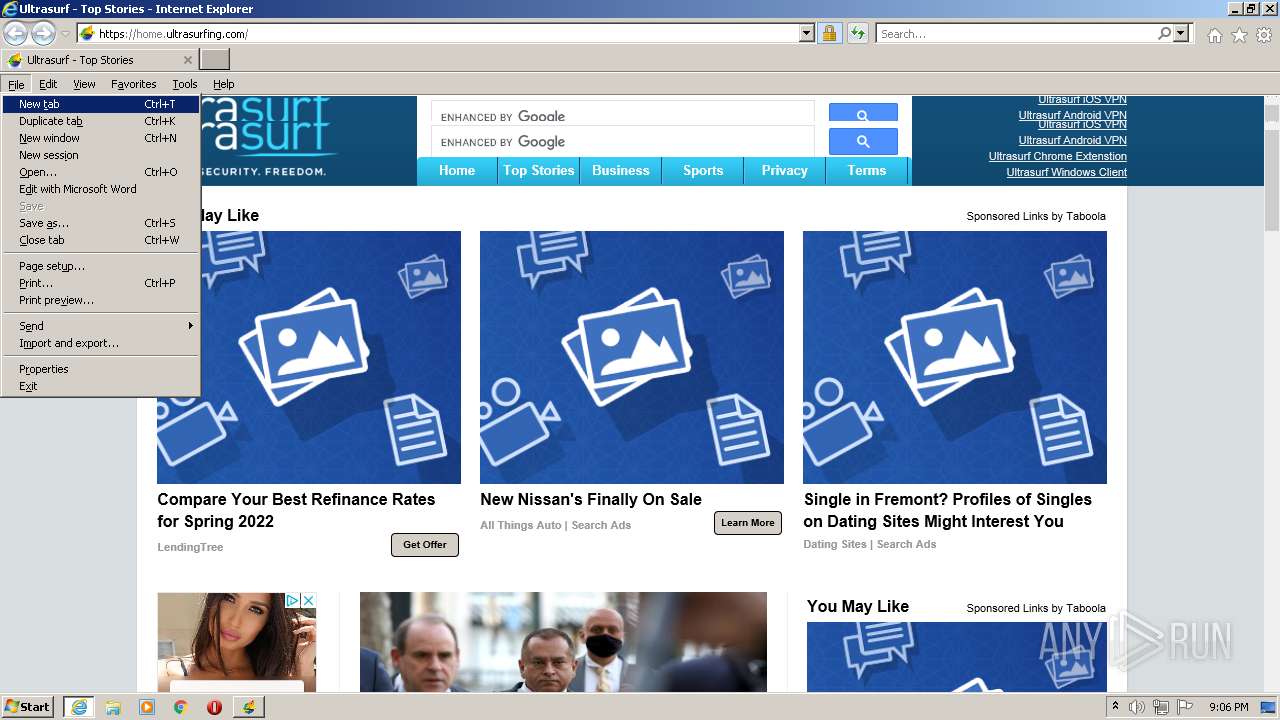
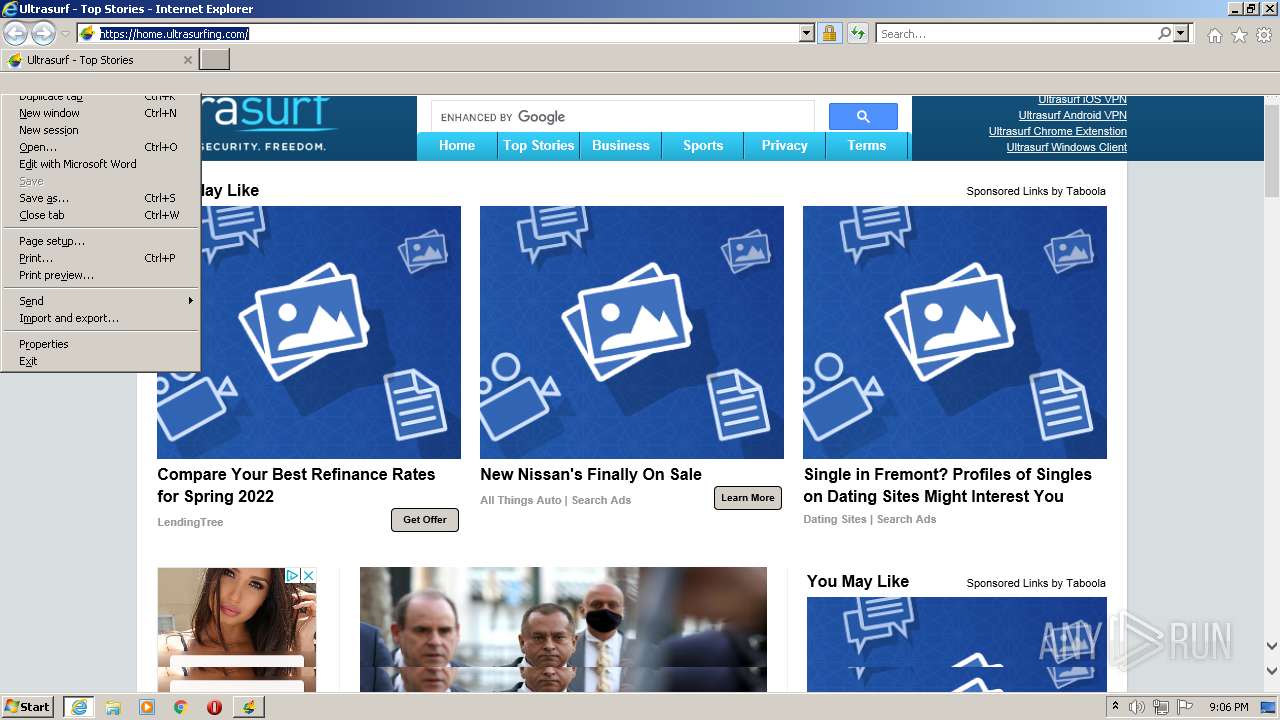
Starts Internet Explorer
- rundll32.exe (PID: 3704)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1148)
INFO
Checks supported languages
- rundll32.exe (PID: 3704)
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 1148)
Reads the computer name
- rundll32.exe (PID: 3704)
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 1148)
Changes internet zones settings
- iexplore.exe (PID: 3228)
Application launched itself
- iexplore.exe (PID: 3228)
Reads settings of System Certificates
- iexplore.exe (PID: 1148)
- iexplore.exe (PID: 3228)
Creates files in the user directory
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 1148)
Checks Windows Trust Settings
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 1148)
Reads internet explorer settings
- iexplore.exe (PID: 1148)
Changes settings of System certificates
- iexplore.exe (PID: 3228)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | 1 |
| OSVersion: | 5.1 |
| EntryPoint: | 0xcb4ac0 |
| UninitializedDataSize: | 10088448 |
| InitializedDataSize: | 155648 |
| CodeSize: | 3235840 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0004 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x008B |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00C18200 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0099F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x009A0000 | 0x00316000 | 0x00315800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.rsrc | 0x00CB6000 | 0x00026000 | 0x00025800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50977 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25784 | 828 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.47164 | 152104 | UNKNOWN | English - United States | RT_ICON |
3 | 2.22322 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
Total processes
43
Monitored processes
4
Malicious processes
0
Suspicious processes
1
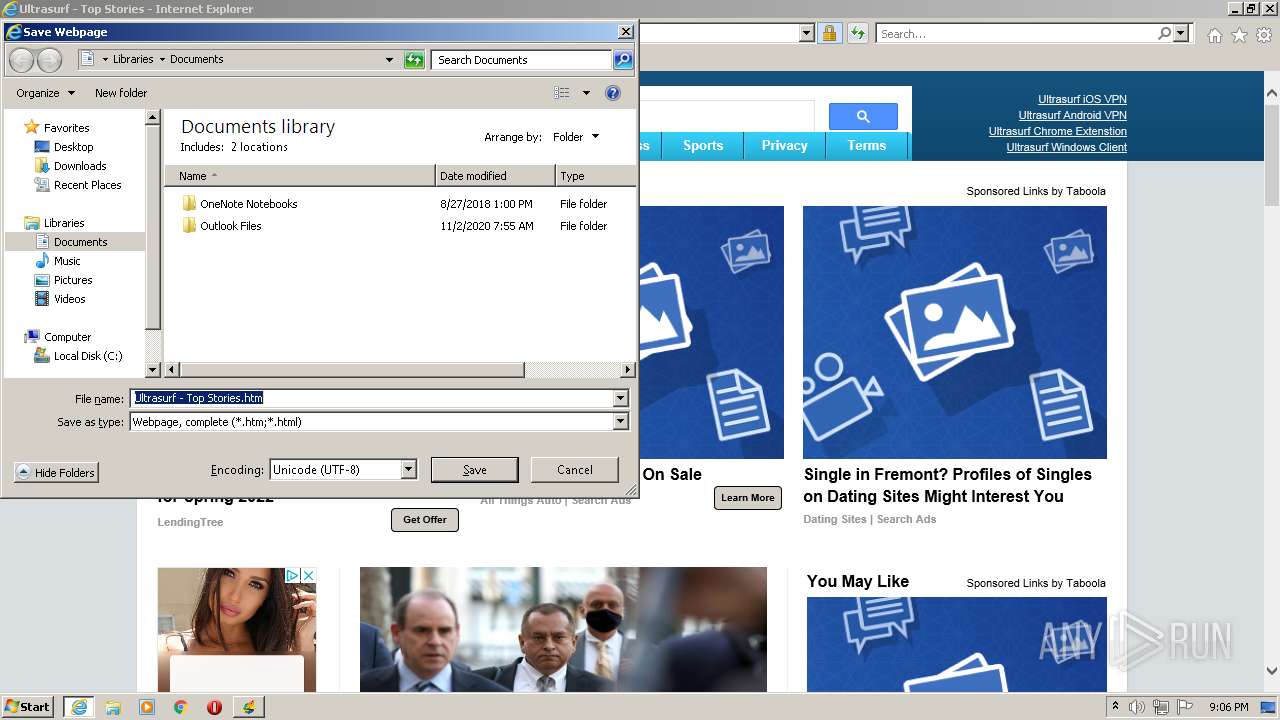
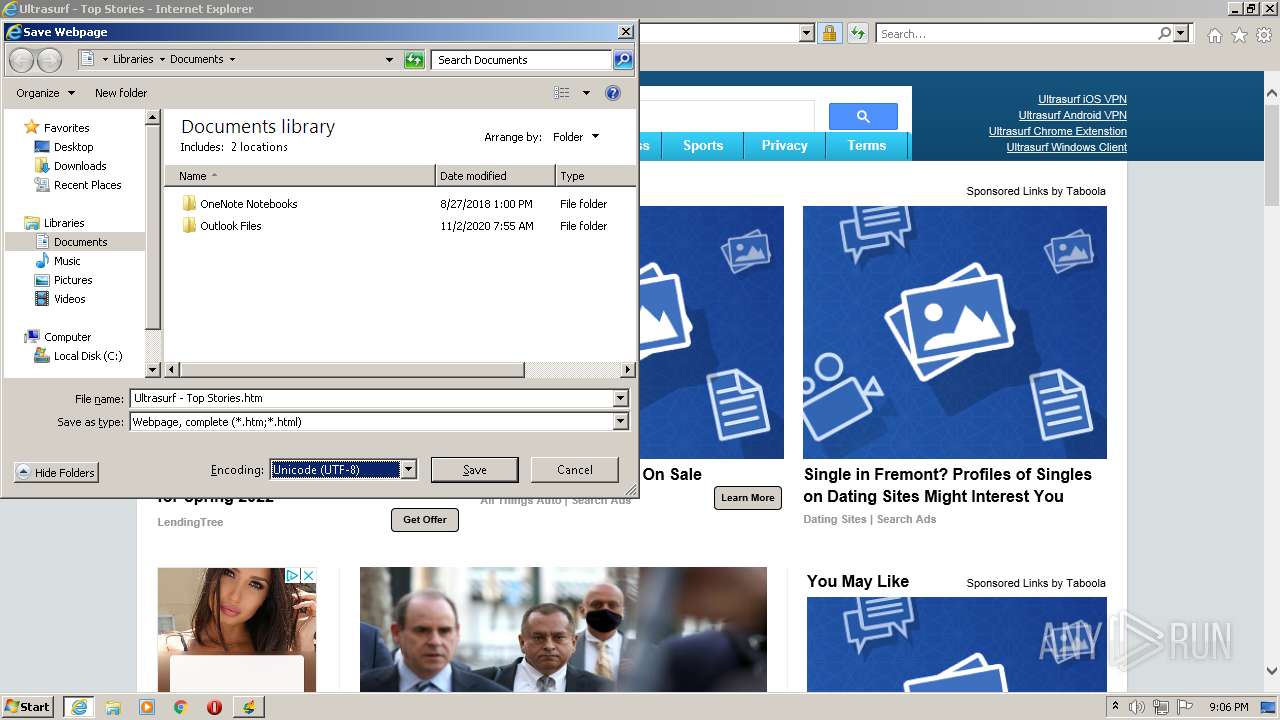
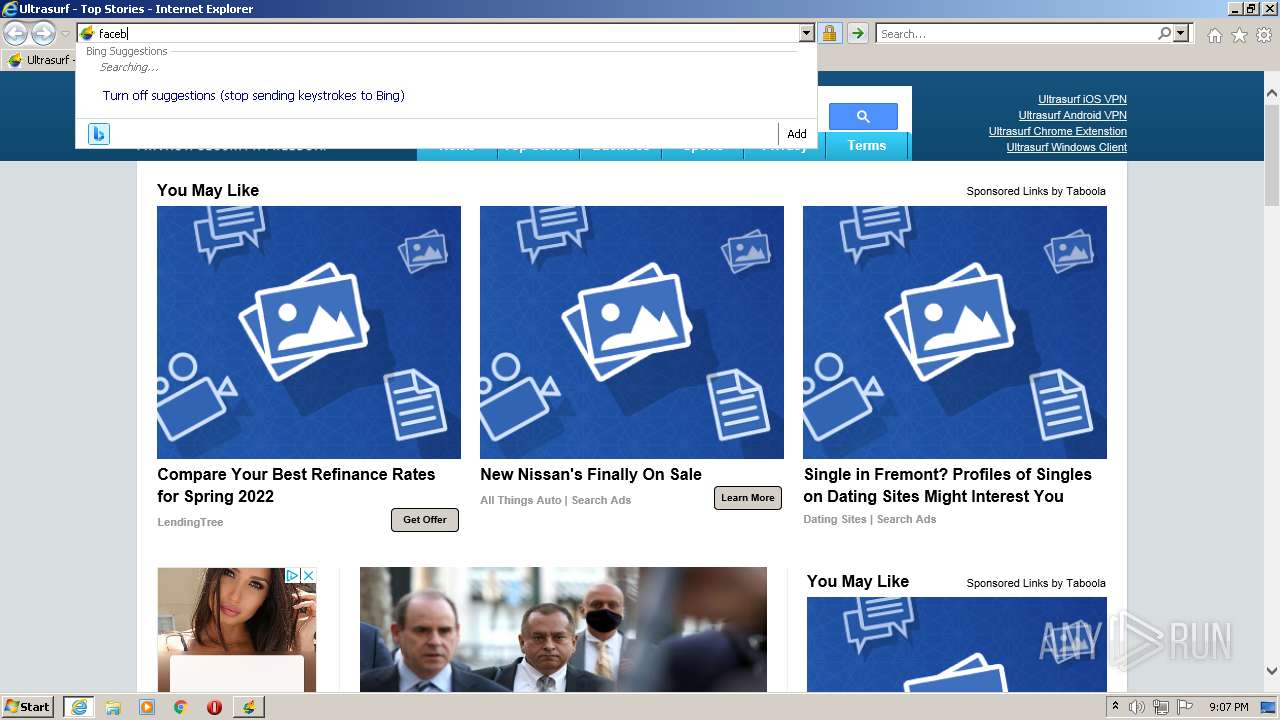
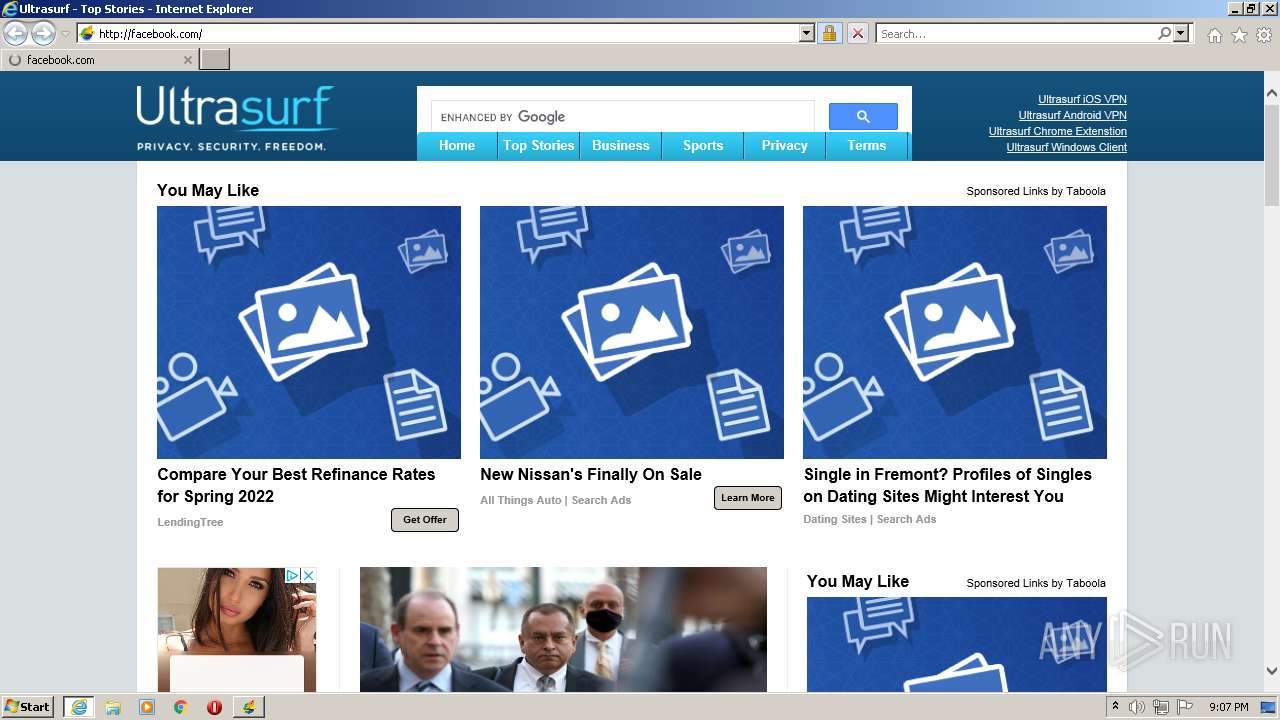
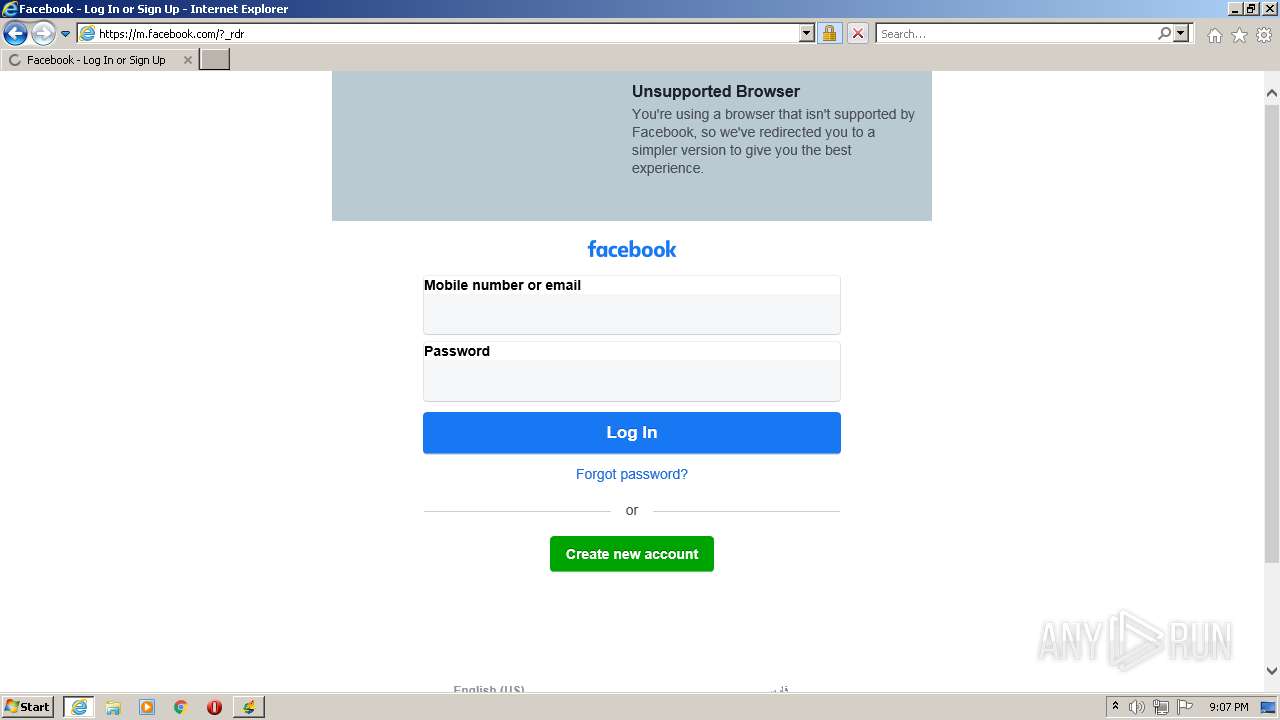
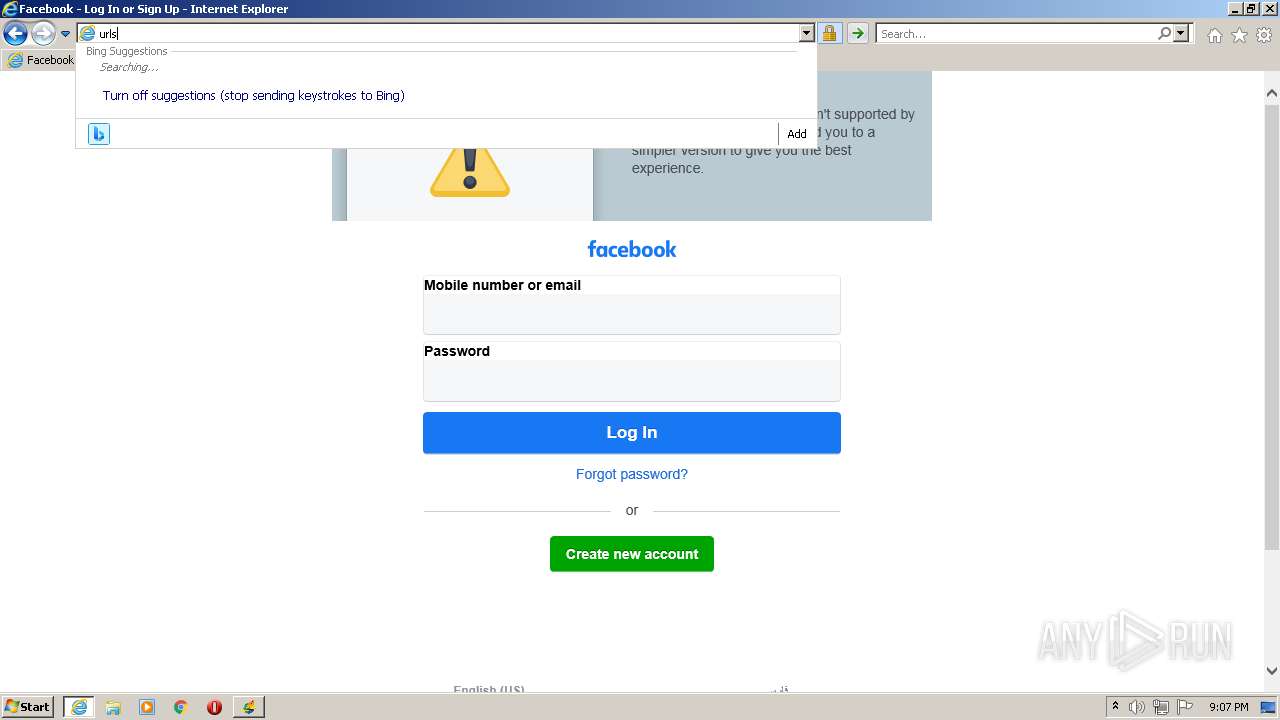
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Users\admin\Desktop\usf.exe" | C:\Users\admin\Desktop\usf.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3228 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
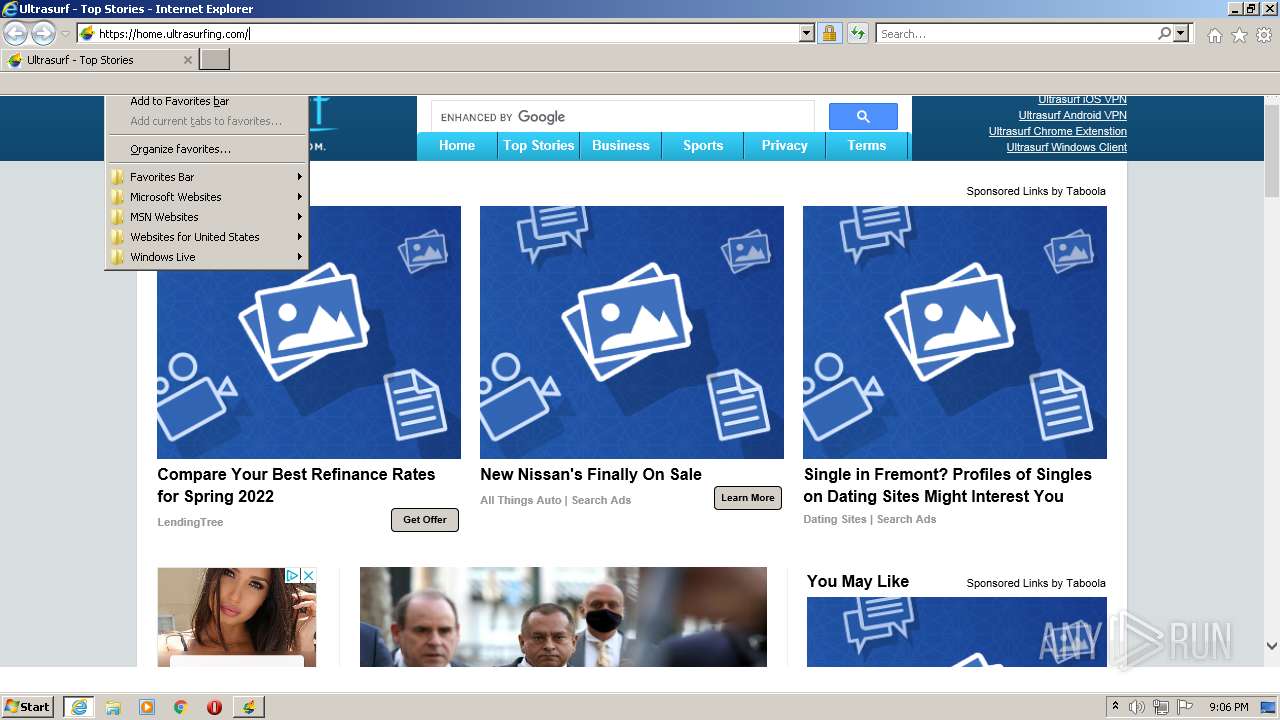
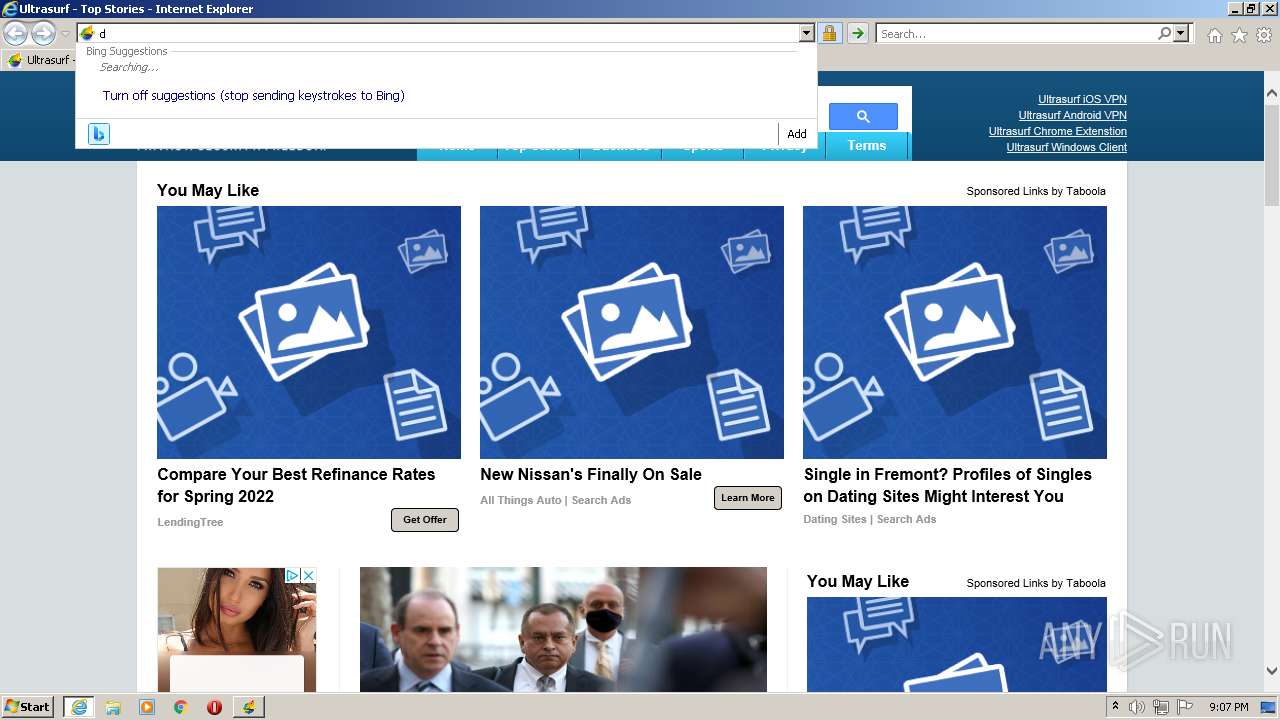
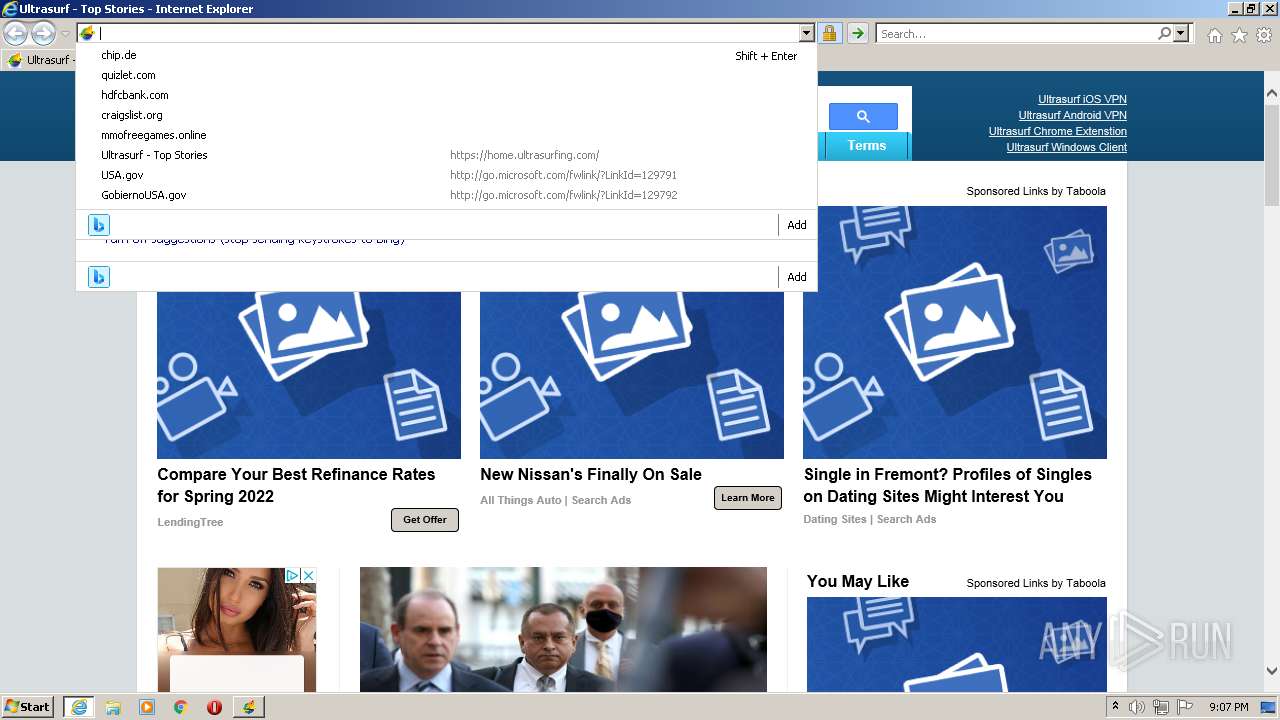
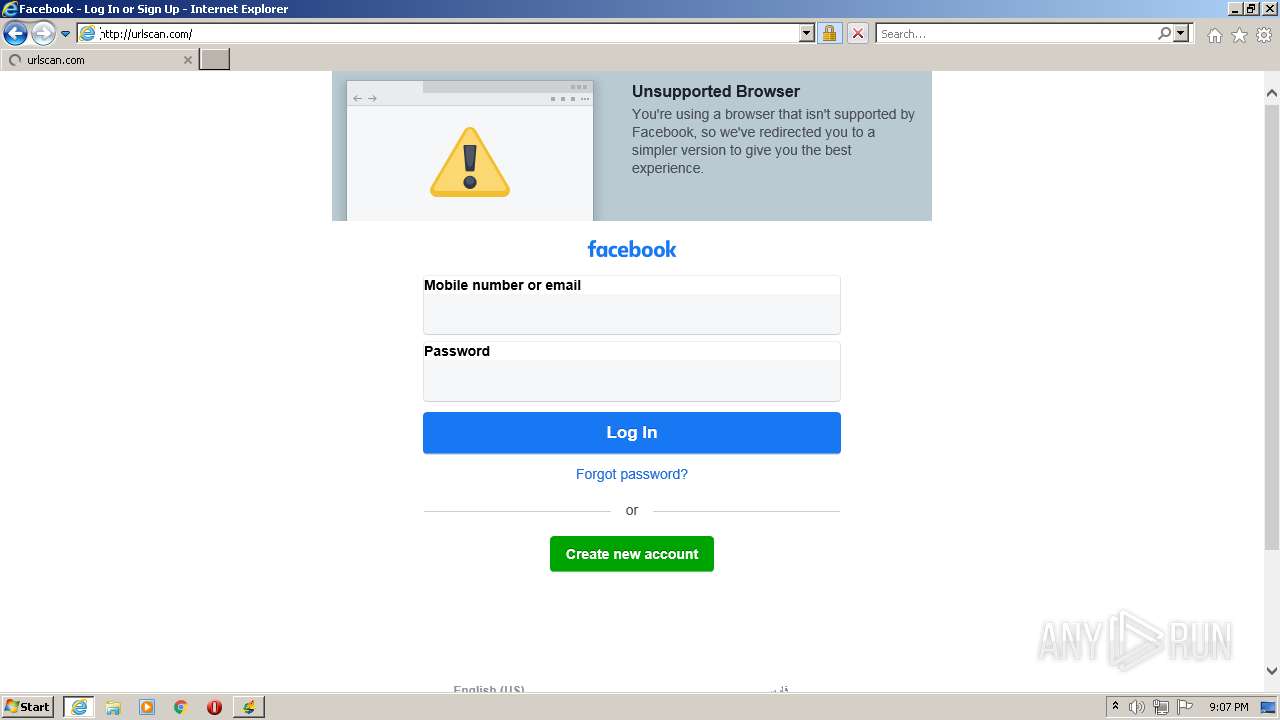
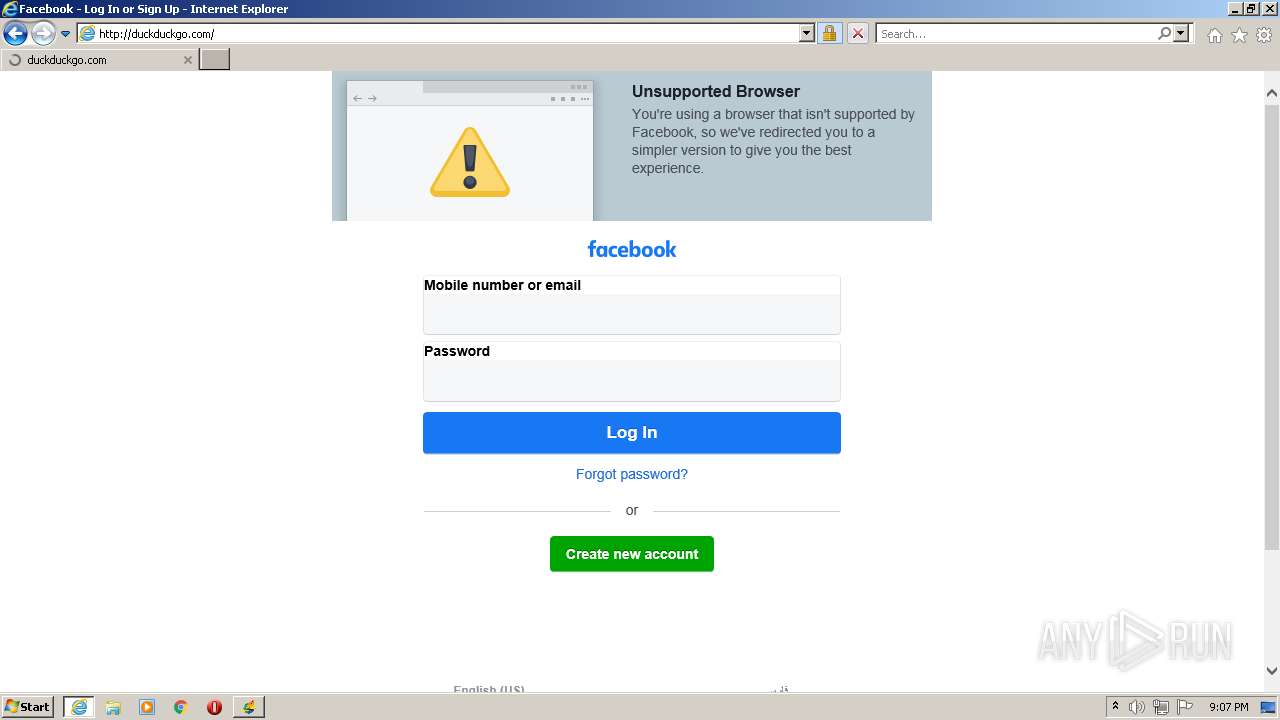
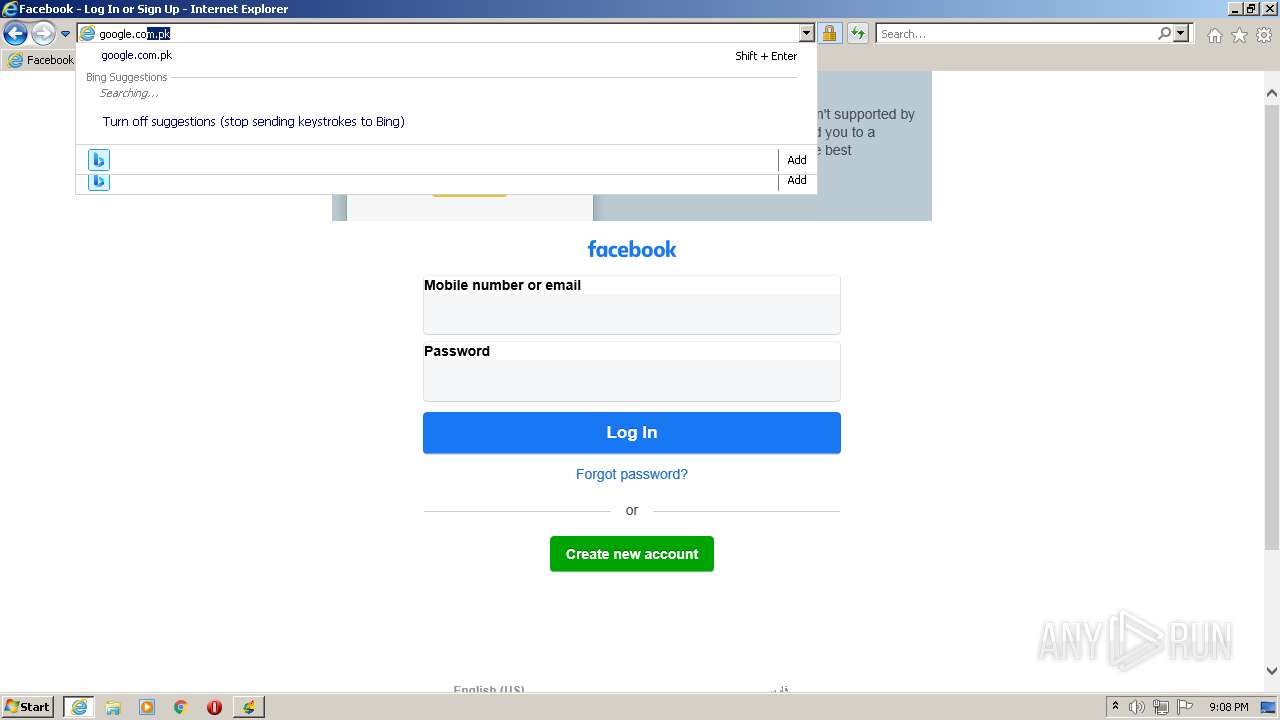
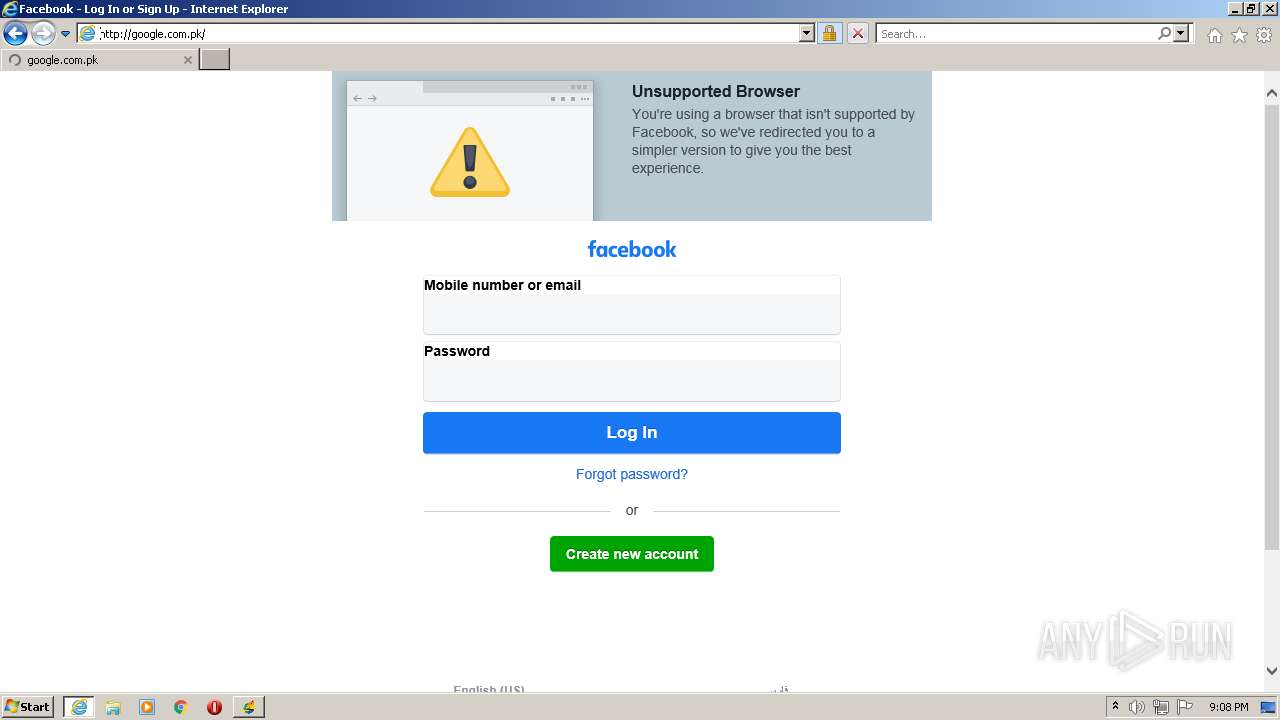
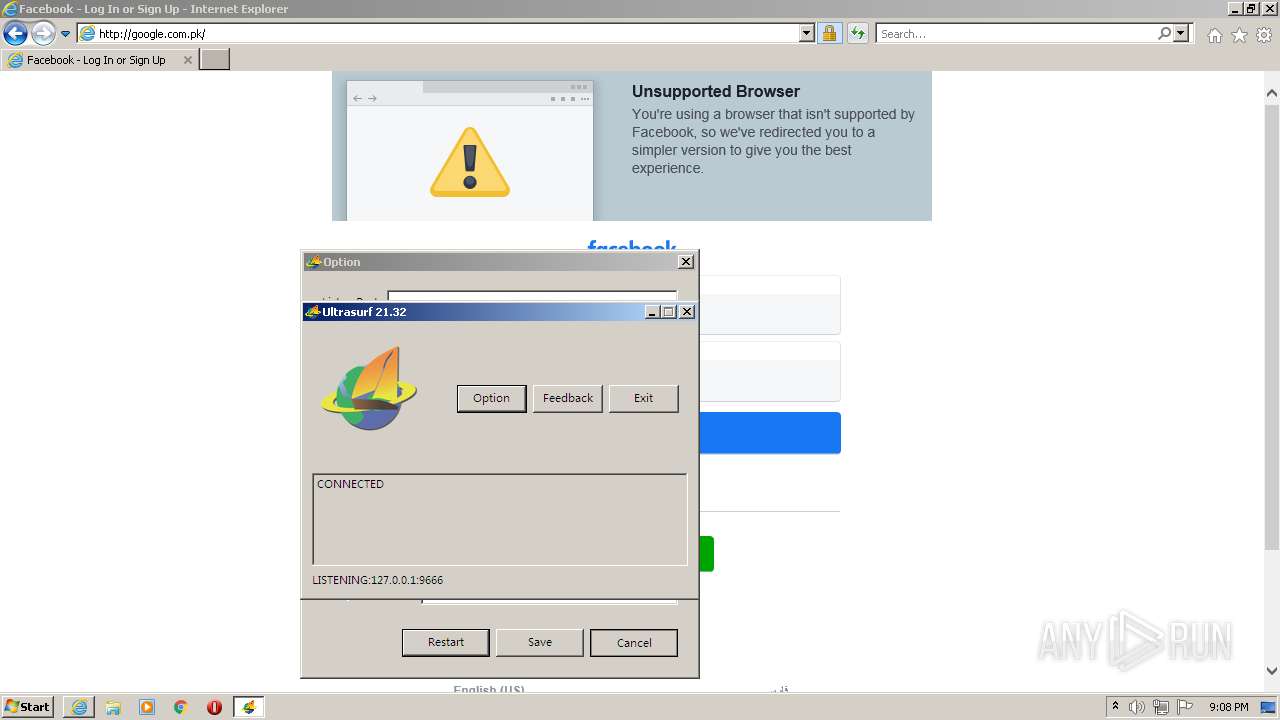
| 3228 | "C:\Program Files\Internet Explorer\iexplore.exe" https://home.ultrasurfing.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3704 | rundll32 url.dll,FileProtocolHandler https://home.ultrasurfing.com | C:\Windows\system32\rundll32.exe | — | usf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 197
Read events
29 712
Write events
477
Delete events
8
Modification events
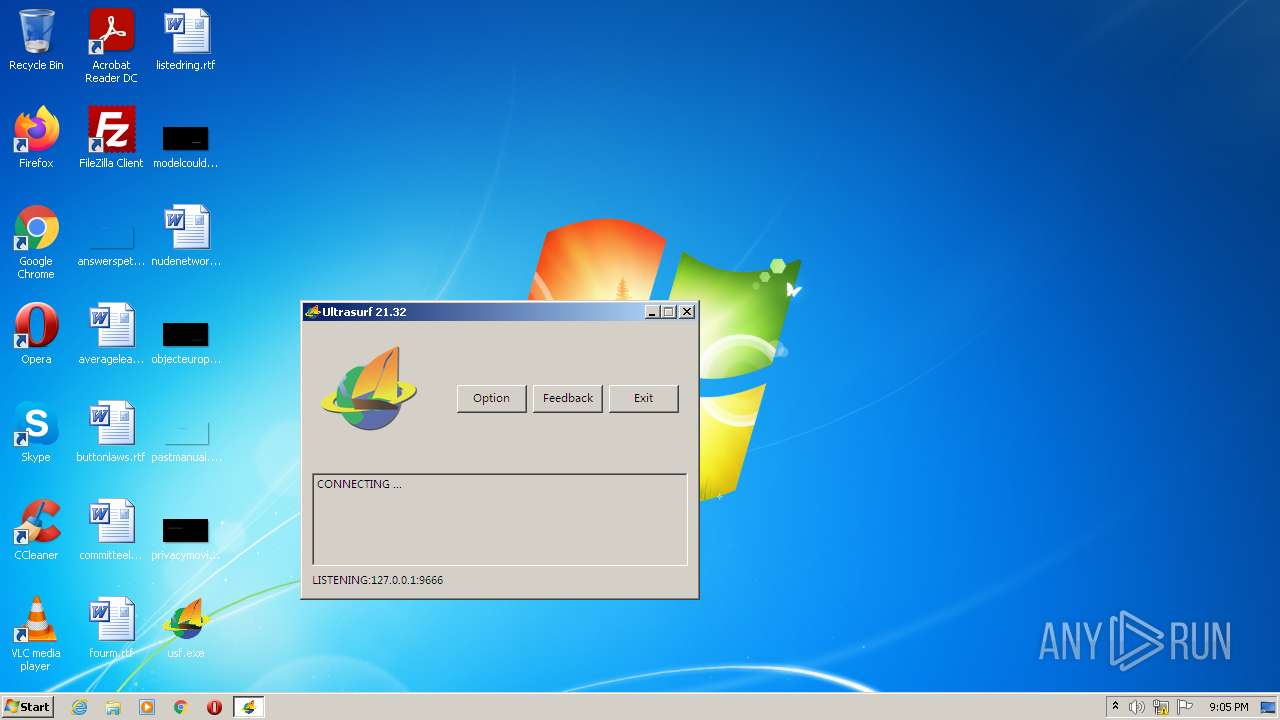
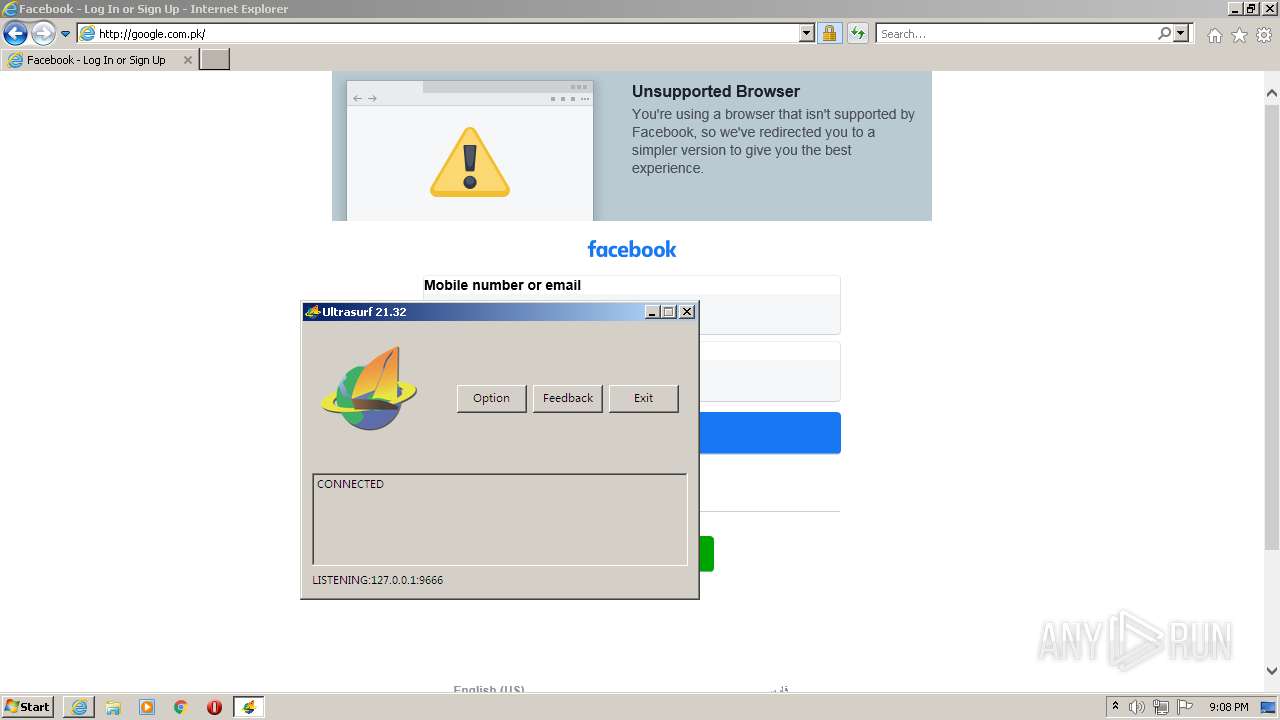
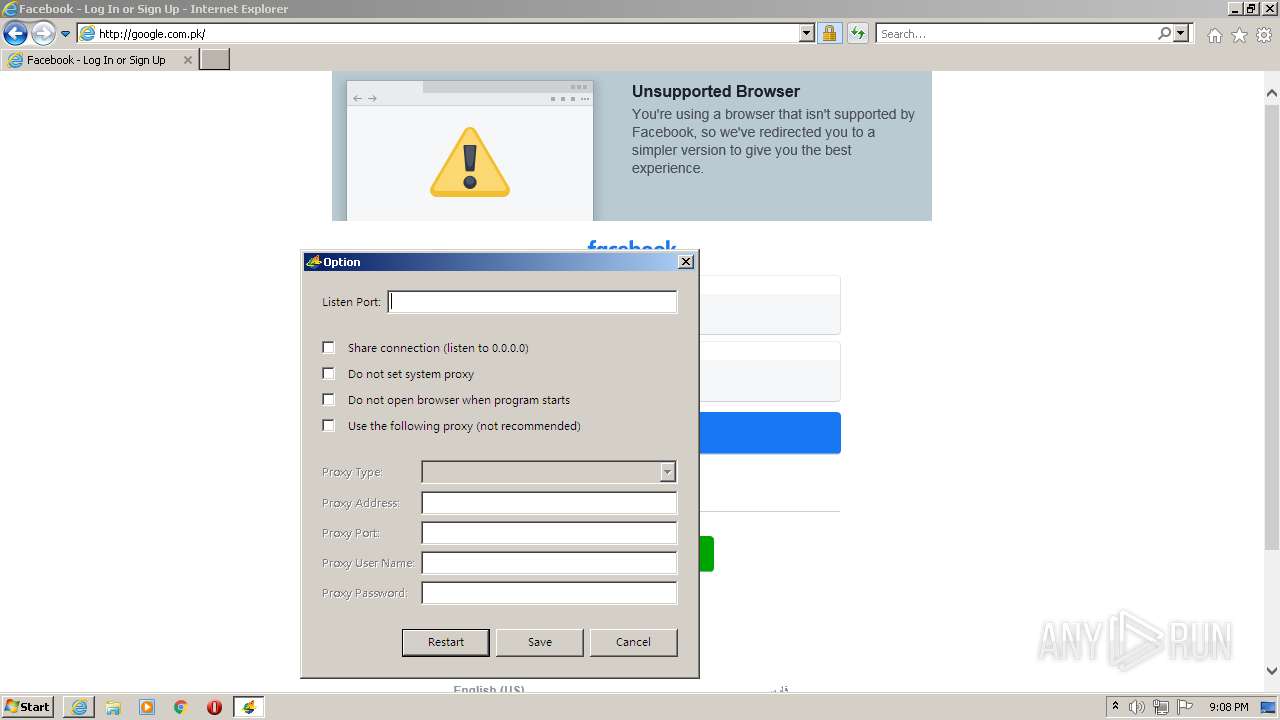
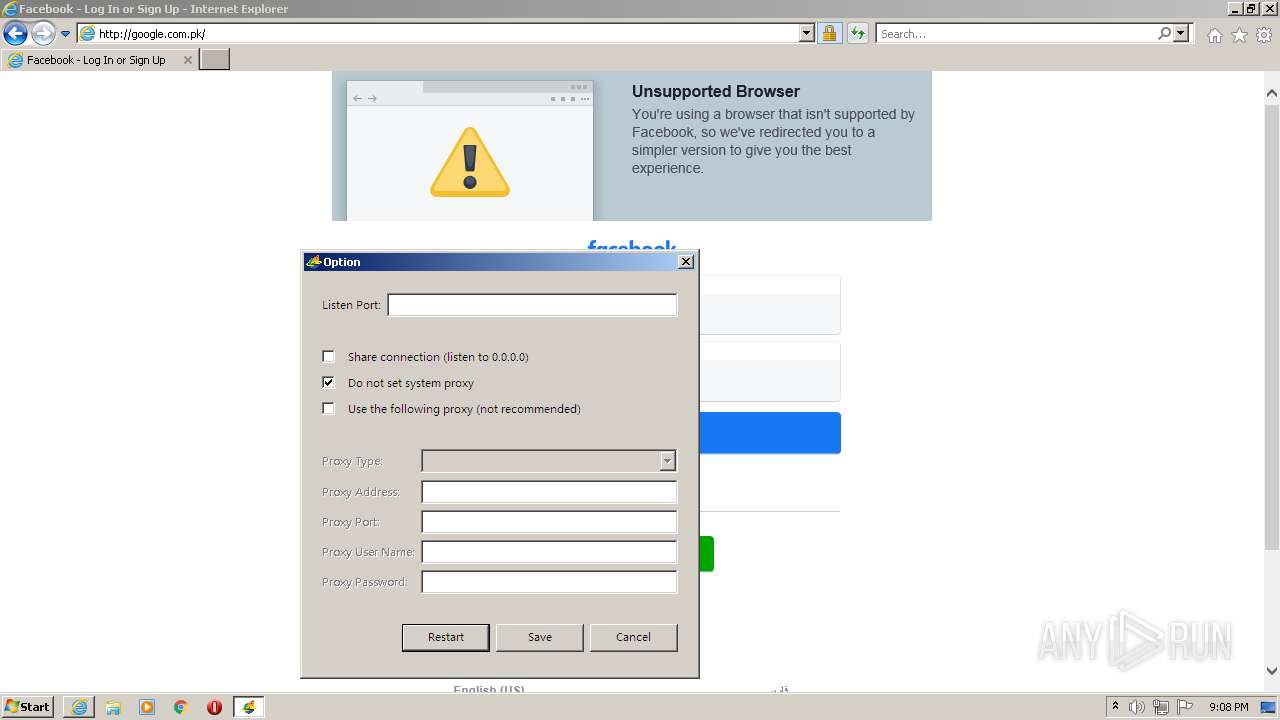
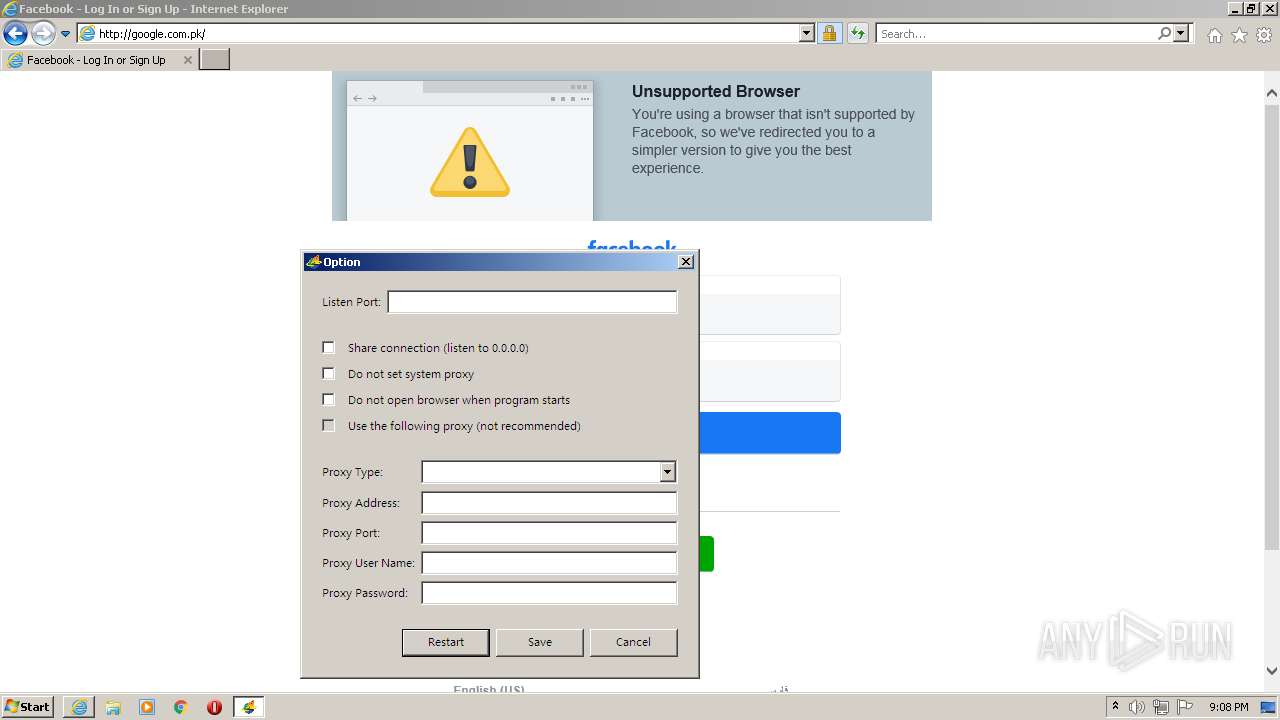
| (PID) Process: | (672) usf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyServer |
Value: 127.0.0.1:9666 | |||
| (PID) Process: | (672) usf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 1 | |||
| (PID) Process: | (672) usf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003C0100000B0000000E0000003132372E302E302E313A3936363600000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (672) usf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D0100000B0000000E0000003132372E302E302E313A3936363600000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30948912 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30948912 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
66
Text files
200
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 672 | usf.exe | C:\Users\admin\AppData\Local\Temp\.ilxa567jb | pz | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style6[1].css | text | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\bdd7a017_photo0_190[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ZB4ISV32.htm | html | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\2502b4ea_photo0_190[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\c1058bd2_photo0_190[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 1148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\a15f6ebb_photo0_190[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
672 | usf.exe | 65.49.2.66:14407 | — | Hurricane Electric, Inc. | US | unknown |
672 | usf.exe | 9.9.9.11:443 | — | — | US | unknown |
672 | usf.exe | 74.82.60.25:443 | — | Hurricane Electric, Inc. | US | unknown |
672 | usf.exe | 74.82.60.49:13260 | — | Hurricane Electric, Inc. | US | unknown |
672 | usf.exe | 65.49.2.63:443 | — | Hurricane Electric, Inc. | US | unknown |