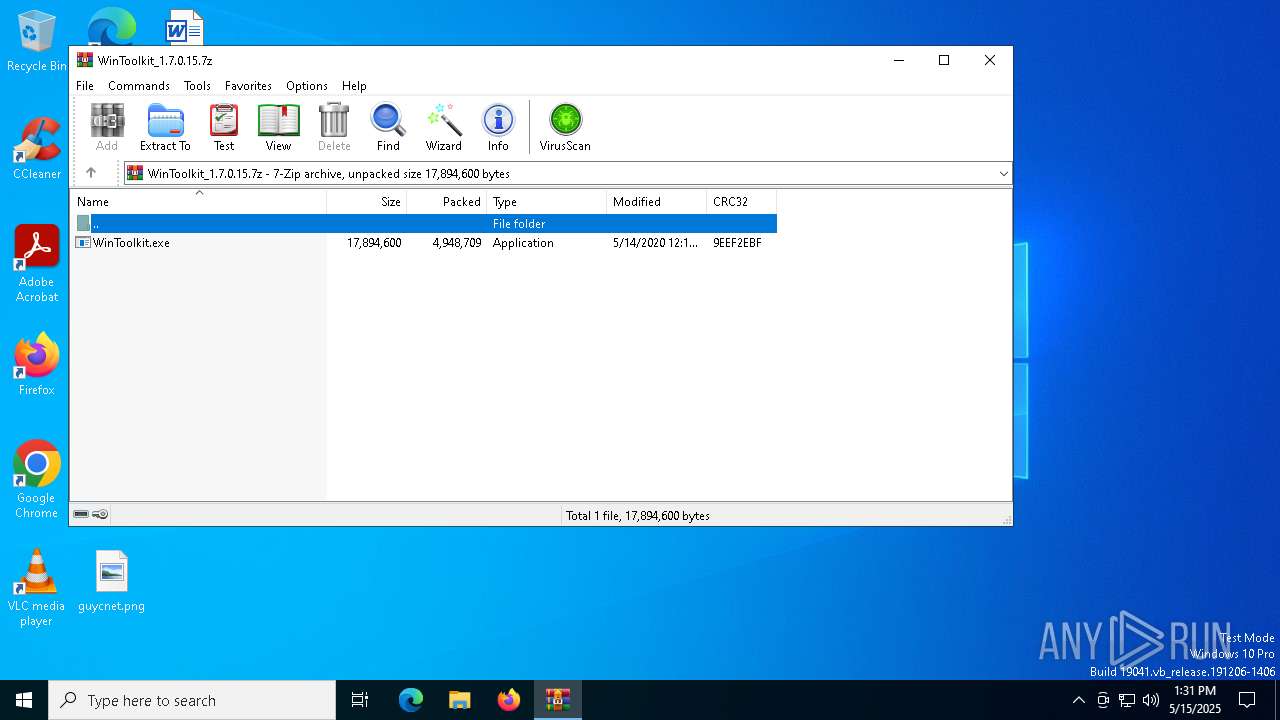
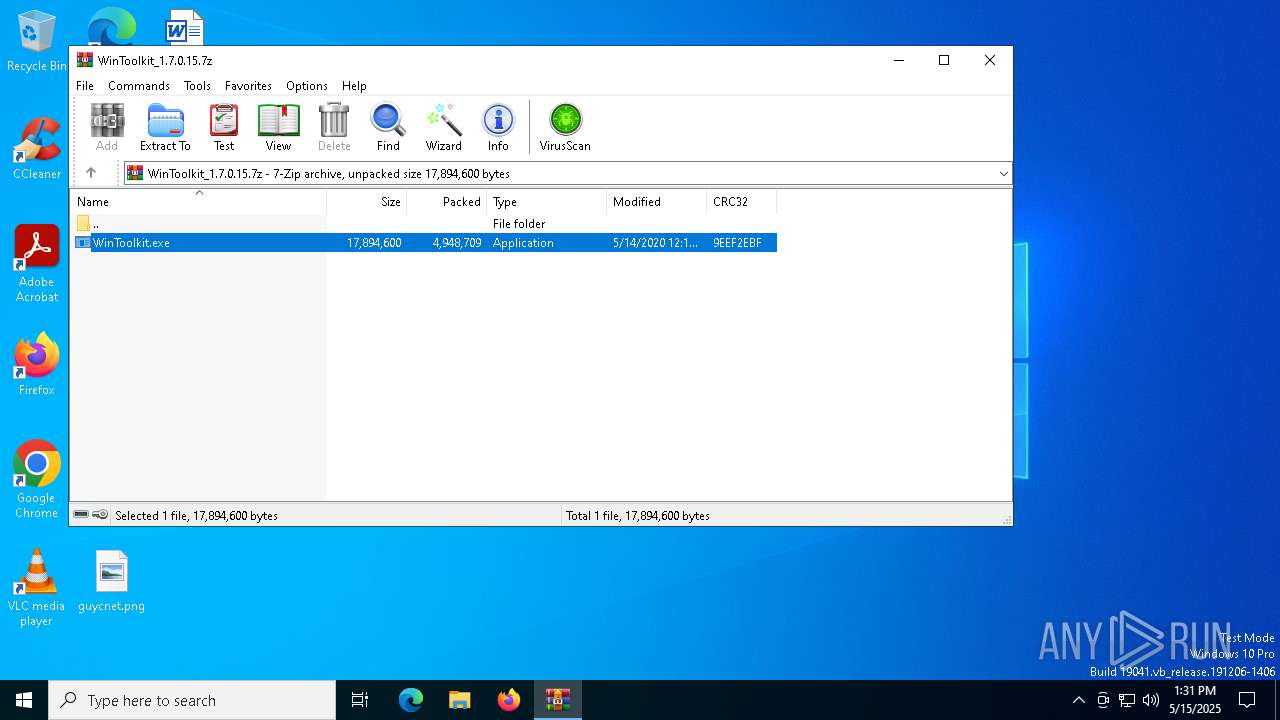
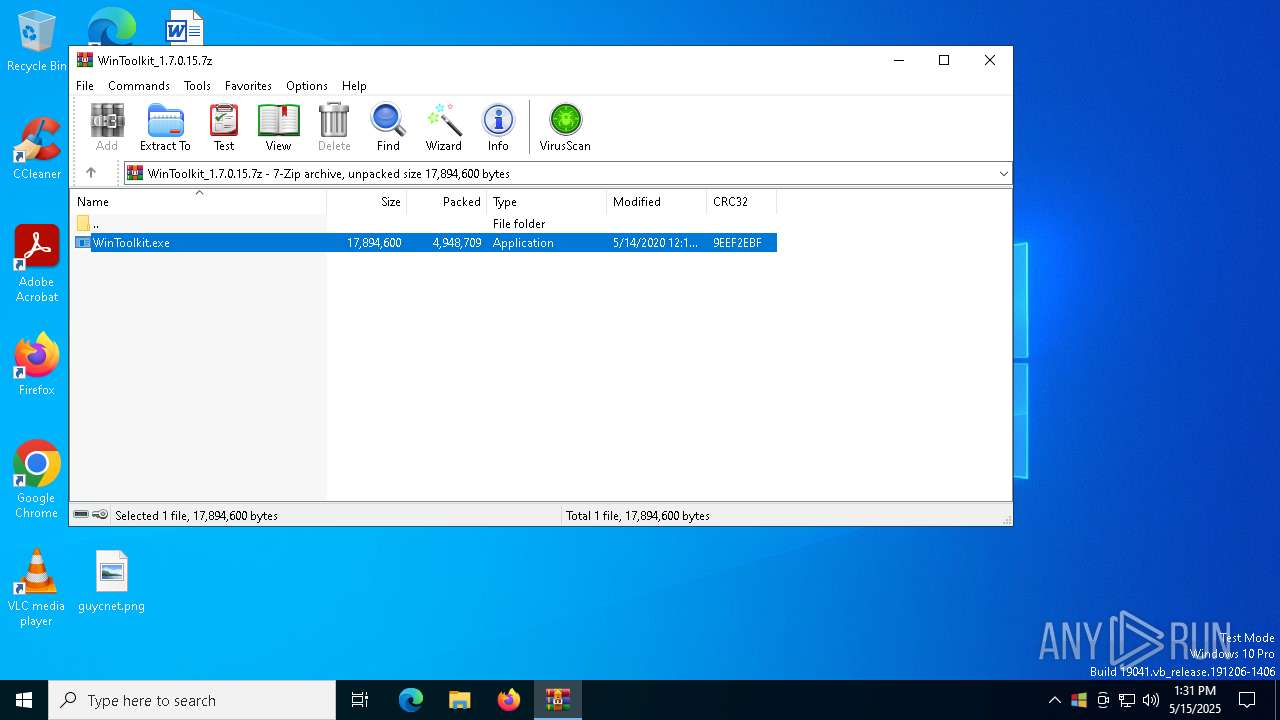
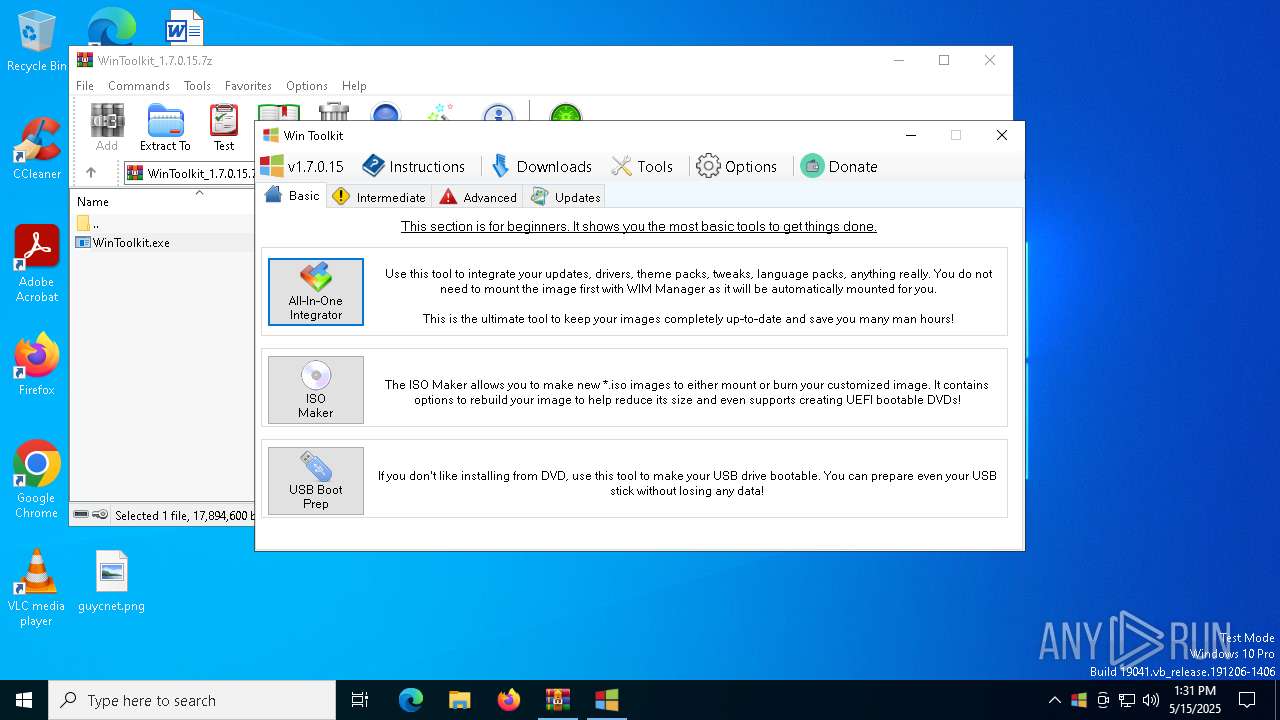
| File name: | WinToolkit_1.7.0.15.7z |
| Full analysis: | https://app.any.run/tasks/e95dfb83-b7e7-428f-84bc-8bee99bf7080 |
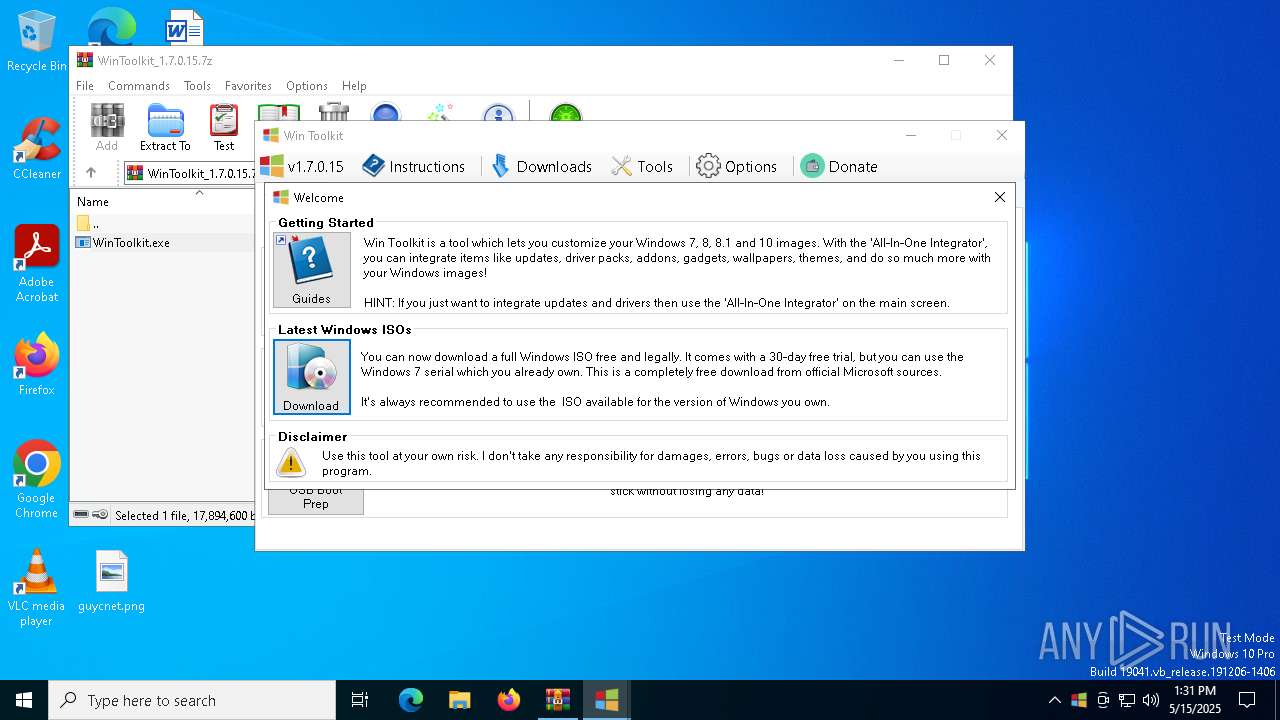
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 13:30:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 255655CEDD7CAFBDD7C97CD673686EC2 |
| SHA1: | 2A4E6B779152BDCA9DE39EF65A876C0A3143F687 |
| SHA256: | 1689F64E86DDD497DCB845F9F4A41D09804A4599192D0827E734ADC8659AE847 |
| SSDEEP: | 98304:GyesnpSvBM2CgZiP+jgMi7DcjsZR/RfoJhdrNzxn85FpOQcP3Y4COrhTe/w/xtR4:utx05xmHM |
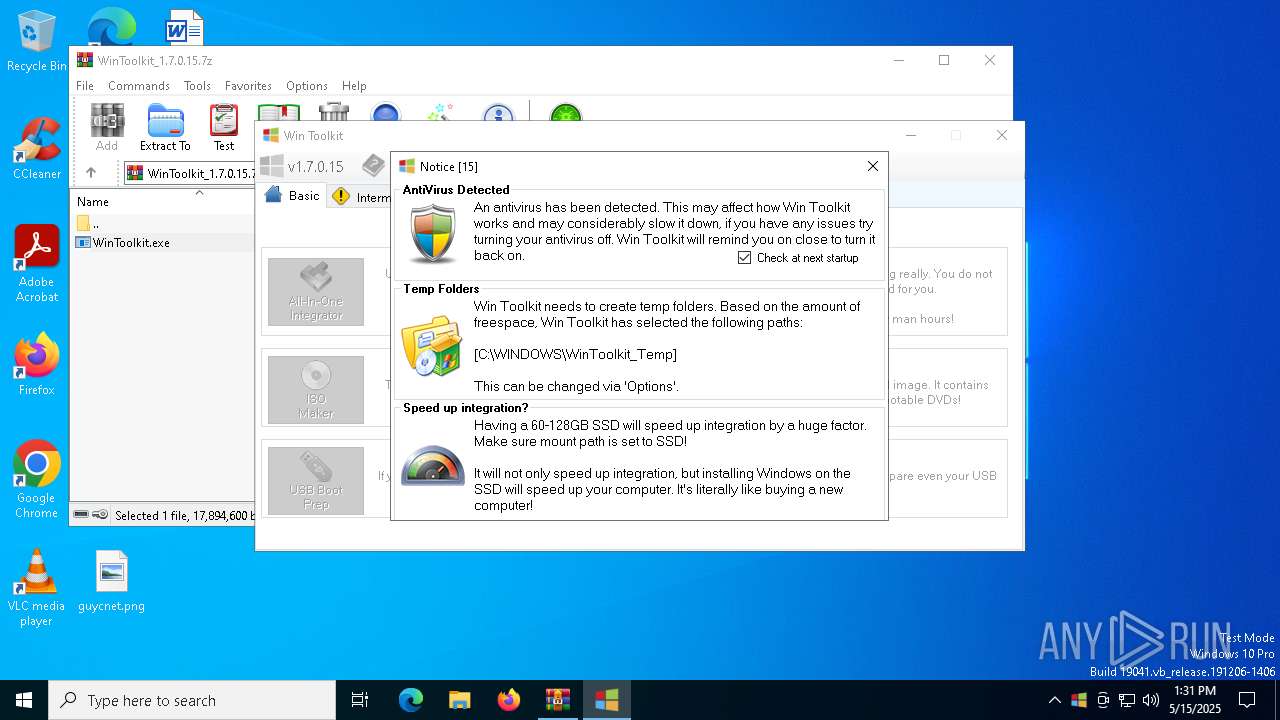
MALICIOUS
Executing a file with an untrusted certificate
- WinToolkit.exe (PID: 3888)
- WinToolkit.exe (PID: 4896)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3768)
- WinToolkit.exe (PID: 4896)
Reads the date of Windows installation
- WinToolkit.exe (PID: 4896)
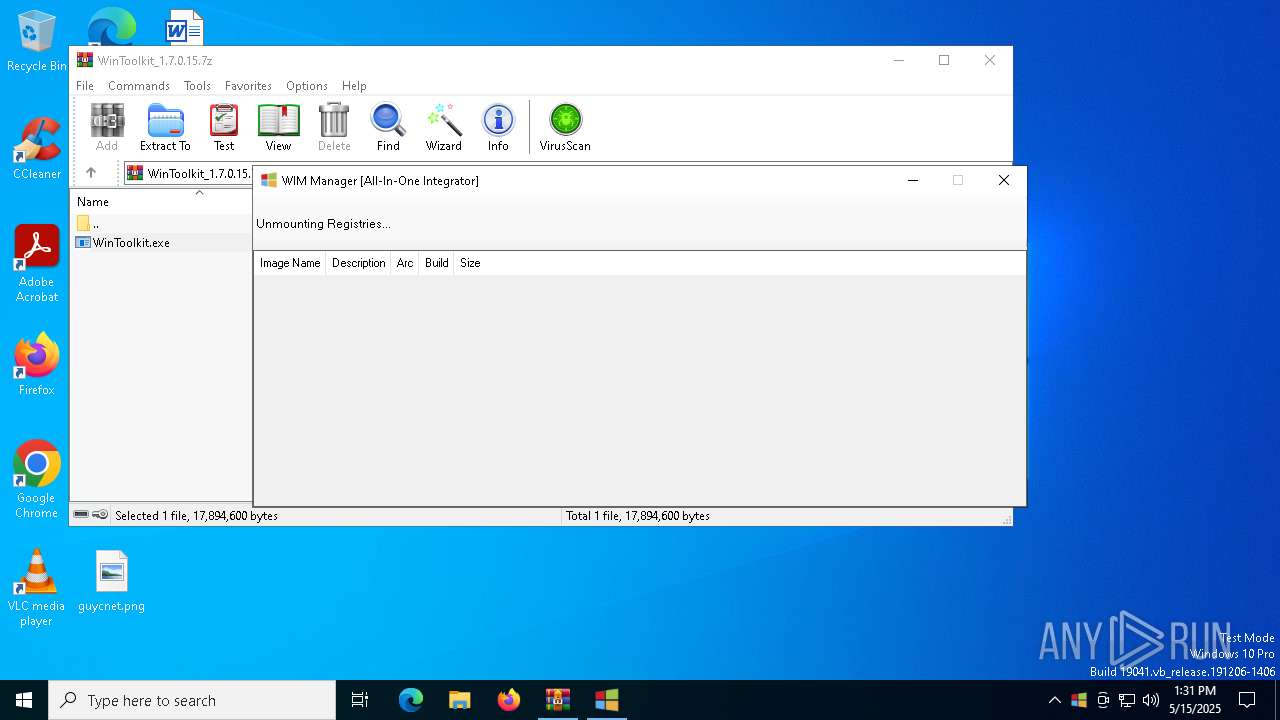
Uses REG/REGEDIT.EXE to modify registry
- WinToolkit.exe (PID: 4896)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 920)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 4812)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 6416)
Adds/modifies Windows certificates
- regedit.exe (PID: 6228)
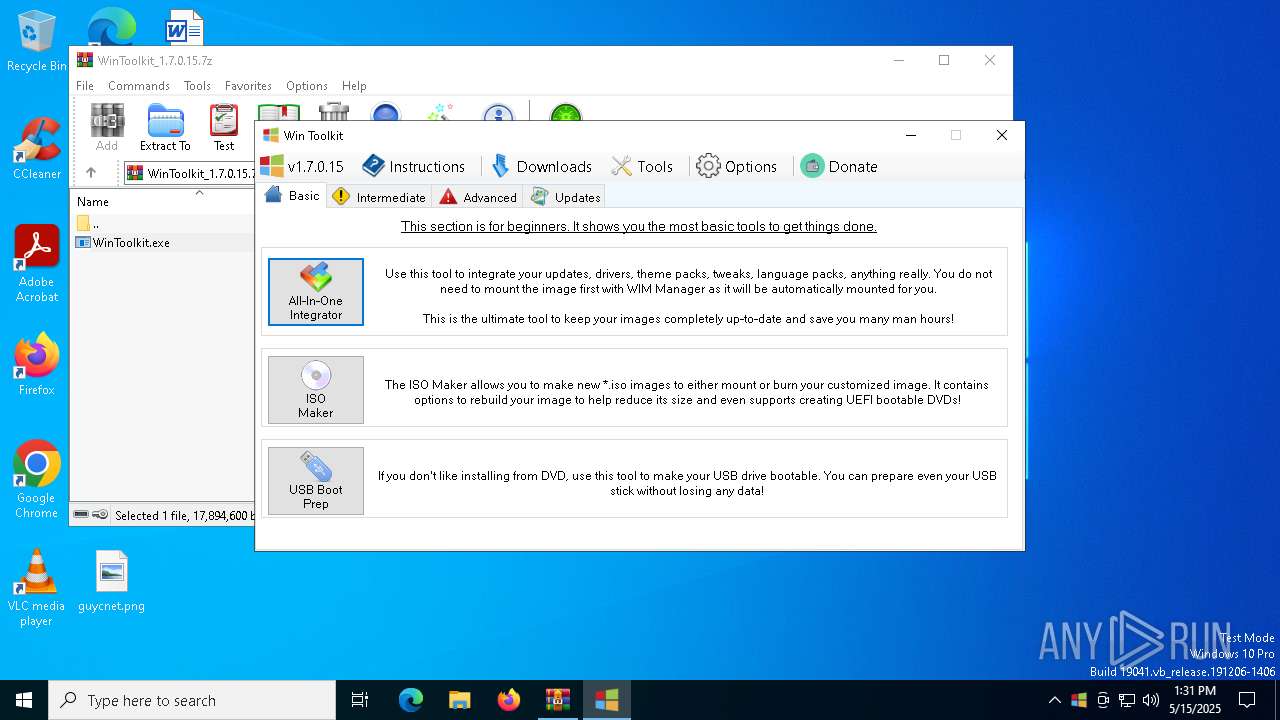
Executable content was dropped or overwritten
- WinToolkit.exe (PID: 4896)
Process drops legitimate windows executable
- WinToolkit.exe (PID: 4896)
Starts CMD.EXE for commands execution
- WinToolkit.exe (PID: 4896)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3768)
Checks supported languages
- WinToolkit.exe (PID: 4896)
Reads the computer name
- WinToolkit.exe (PID: 4896)
Reads the machine GUID from the registry
- WinToolkit.exe (PID: 4896)
Create files in a temporary directory
- WinToolkit.exe (PID: 4896)
Process checks computer location settings
- WinToolkit.exe (PID: 4896)
The sample compiled with english language support
- WinToolkit.exe (PID: 4896)
Compiled with Borland Delphi (YARA)
- WinToolkit.exe (PID: 4896)
Checks proxy server information
- slui.exe (PID: 900)
Reads the software policy settings
- slui.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:05:14 12:14:02+00:00 |
| ArchivedFileName: | WinToolkit.exe |
Total processes
178
Monitored processes
44
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "cmd.exe" | C:\Windows\System32\cmd.exe | — | WinToolkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | "C:\WINDOWS\System32\reg.exe" unload "HKLM\SAM" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\System32\reg.exe" unload "HKLM\SECURITY" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\WINDOWS\System32\reg.exe" unload "HKLM\SAM" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\WINDOWS\System32\reg.exe" unload "HKLM\HARDWARE" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\WINDOWS\System32\reg.exe" unload "HKLM\SYSTEM" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 818
Read events
2 809
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\WinToolkit_1.7.0.15.7z | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6228) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\B19E4C59E30113AD86EBCF90F3DB3E8DBD8D42FD |
| Operation: | write | Name: | Blob |
Value: 19000000010000001000000056577B941424F2C0912A87E53F3A1B9A0F000000010000002000000067A00D9CC4229C07AF2CFE0DAFDE32B8B6F98868291168C84F6867DC33B1C740030000000100000014000000B19E4C59E30113AD86EBCF90F3DB3E8DBD8D42FD14000000010000001400000073A2C2E96C39043A2F1DB93BC7C90B350E8FA8C02000000001000000BD030000308203B9308202A1A0030201020210442490AF760533BC4FDDB13EA25EE56D300D06092A864886F70D01010B0500304D310B30090603550406130244453125302306092A864886F70D0109011616696E666F4077696E2D756E617474656E6465642E6465311730150603550403130E57696E2D556E617474656E646564301E170D3139313232343139353335345A170D3339313233313233353935395A304D310B30090603550406130244453125302306092A864886F70D0109011616696E666F4077696E2D756E617474656E6465642E6465311730150603550403130E57696E2D556E617474656E64656430820122300D06092A864886F70D01010105000382010F003082010A0282010100CF48BCAA62E562636474806BC37E38E326606E9C71152834D3D7D504FE047266220BBE8D90CF49ABD0CAA97CF58B2033F34E11111A6CF2DDAEEF0C7BA4EA598B44487B0E46664A588AC2654F8A5298E4B67E9D331F1F54898CF7A965B831C56447F668B94C29D522088C4F7C712D0FDA5A4F85A14793F6859507D3B2F1BBD35836C89362B7F825C907D4DAFA2E84C9EE150D17F04C0D1CAD6F6C524D34A4042EF099C4F12F2D98C1508931DA732F5900AC5DC8A391135F7D9E7DC9F3F7CC71CBB56849AE236CCCAD2B26B89CEAAF6B918DDD3AE27690D5EC929788774B1B0A15716631D2113865B98E38C497FA8DEE7418687F969F936B8BC7A15B8AAFB43C4D0203010001A38194308191300F0603551D130101FF040530030101FF307E0603551D01047730758010858A3E3FEE262AF1AB4FD82EA3C71674A14F304D310B30090603550406130244453125302306092A864886F70D0109011616696E666F4077696E2D756E617474656E6465642E6465311730150603550403130E57696E2D556E617474656E6465648210442490AF760533BC4FDDB13EA25EE56D300D06092A864886F70D01010B05000382010100CC28685797DBC19C73FF4440CC81E976729BB0254A001522828274C3D7C684D89926AC448D39EBAF441B9147D429D551A53B9F6376DBD7F2823907F55F3F72523BF031E79A5134EAA0ACB9C4A0BFEC4BDDCC055734FFE9548B3FA12AB5A8B6CB647002DD8AA6C511F6AE50FA58600EA142F9434A83F7681458349C25F1D1A3ACF668963A47DA3CC23D0A0049647E650383FFB3F3FFA5C9B008A4EDF95B97E22A10B6EF685CBC4EC4D894D0B86A9EE214BB44BCA8943E6E6CA016AFD49AE952A67DA162690430F2EF1A6E573C26DE8F0DC5F3D9E4B3B2EEEF36CDF3F613C23BB7C55120EE302AD6AAA4220C04185241349D17CE517AFCCF6E638BD820305EC58F | |||
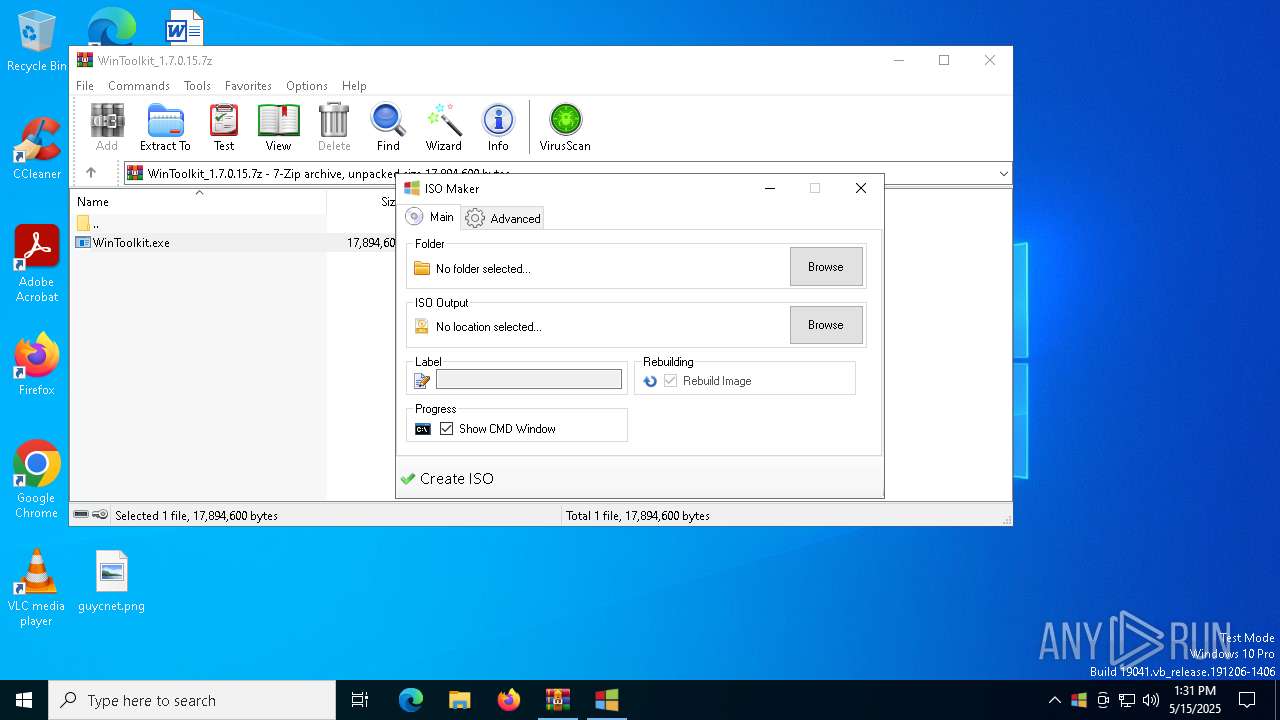
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3768.18301\WinToolkit.exe | executable | |
MD5:86E3765BD385C07EE8130BCC8818B0F7 | SHA256:9DF3185347EF7D85E2252DBB233369BD1183BF969E65413D07867CB6975509AB | |||
| 4896 | WinToolkit.exe | C:\Windows\WinToolkit_Temp\Files\Imagex.exe | executable | |
MD5:F7ED569CA894055142269EB21D6055FB | SHA256:F5C3C47B0D1683864A497248B97F5A99CEF8829CA922C88004D4D7F0F616D636 | |||
| 4896 | WinToolkit.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3768.18301\cert.reg | text | |
MD5:1E841F473F5AE2FD69FE63B97313E546 | SHA256:8BC6102C6EACB53B9E57CB3A73246635FA25B7C6D32DC59439BEB2D2240B44F9 | |||
| 4896 | WinToolkit.exe | C:\Windows\System32\WA.ico | image | |
MD5:8A074AF494080C051DB5C81EB5D09E7D | SHA256:B2CA34CCDACBEC343B2030A9C072EF81ADCA639E44A61BE4B421A494116962D1 | |||
| 4896 | WinToolkit.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3768.18301\Settings.txt | text | |
MD5:404E9FABA5D31CD197BA0B14B95B815C | SHA256:75A2442D412E898ED3CFDD7AC2CF315172280C9BEC222101A00E35E800751BD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3896 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3896 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.211.123.250:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
6544 | svchost.exe | 20.190.159.73:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |