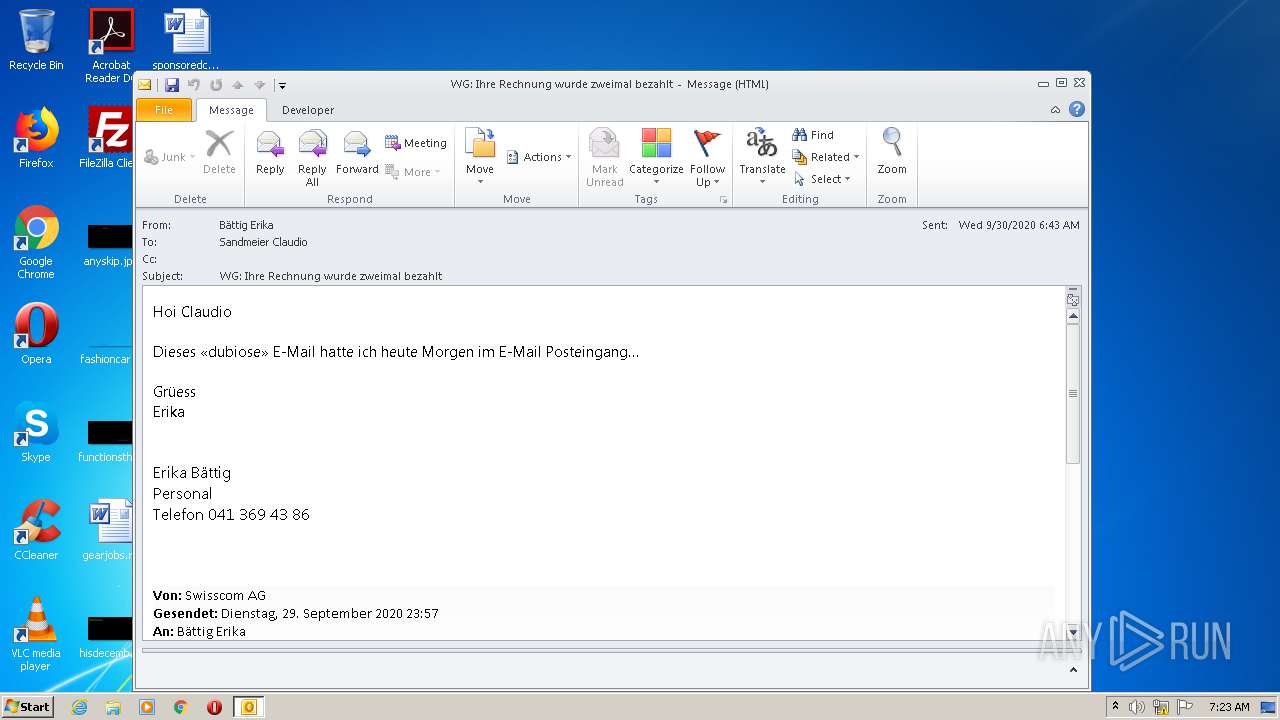
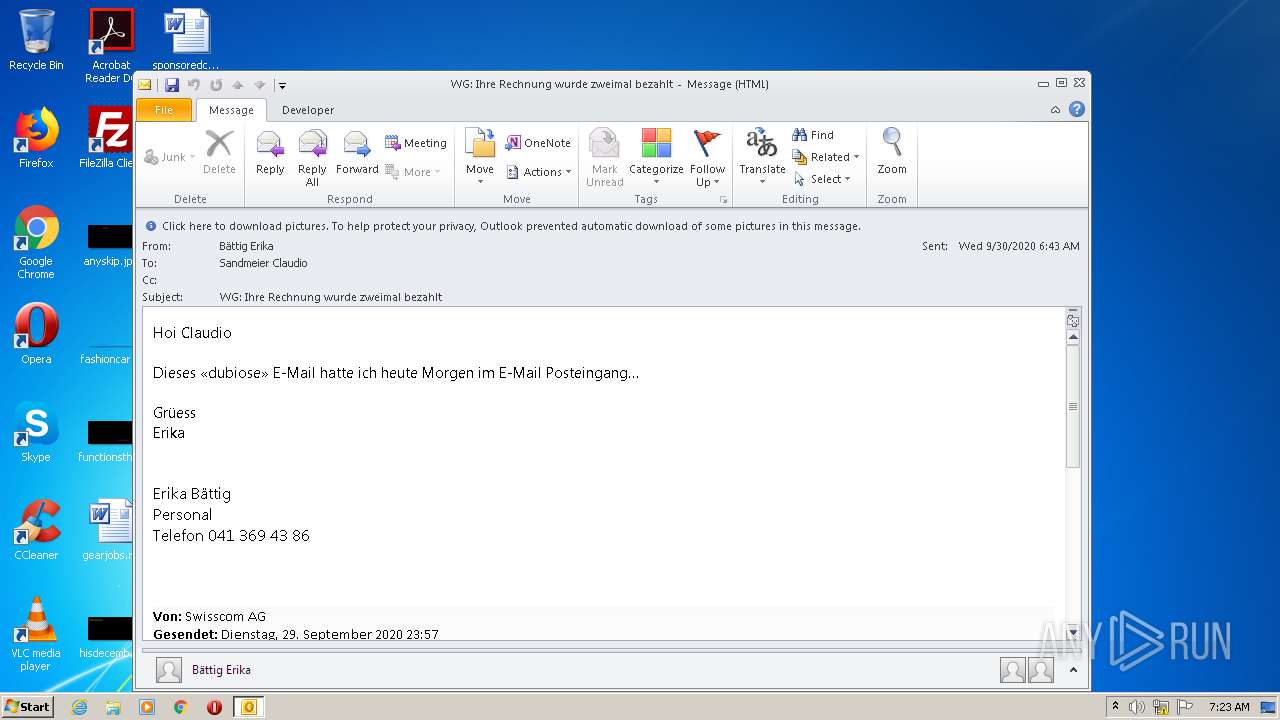
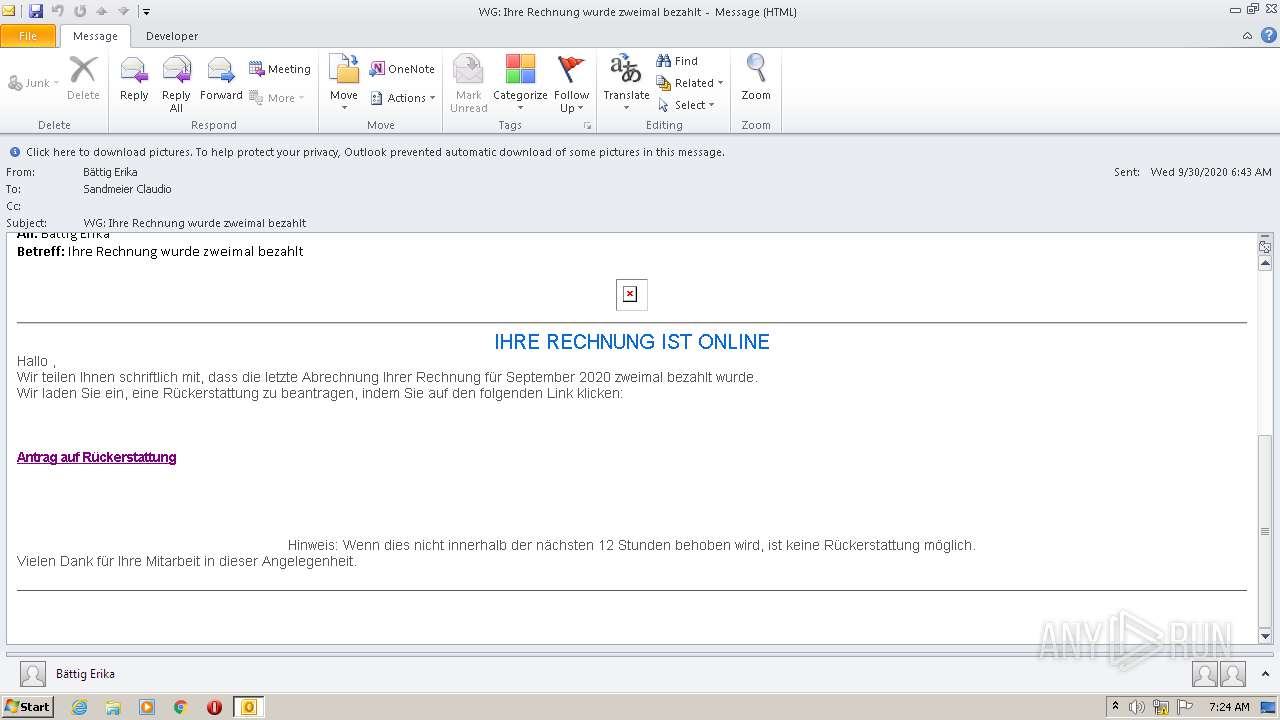
| File name: | WG Ihre Rechnung wurde zweimal bezahlt.msg |
| Full analysis: | https://app.any.run/tasks/feda6828-53d4-4a35-835d-3dd3a9a73eaf |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 06:23:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8EF38705940595A558D81C28970A720F |
| SHA1: | B4480242D76C5C1C822E04A58585ECE0D87AA079 |
| SHA256: | 167EC17B6E44678F037EC7CB968C9C33E2F8B987870F3C7DA0611B4F63F6705B |
| SSDEEP: | 768:Kg2CuvPKg1gXEwvsKgsKpXucKsKNsKqvg7RqxciPsK8sKURoncbLz4eMe:KRvSDXEcoHKVux08Ro |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1688)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1688)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1688)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1688)
- iexplore.exe (PID: 3960)
- iexplore.exe (PID: 668)
Application launched itself
- iexplore.exe (PID: 3960)
Changes internet zones settings
- iexplore.exe (PID: 3960)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3960 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
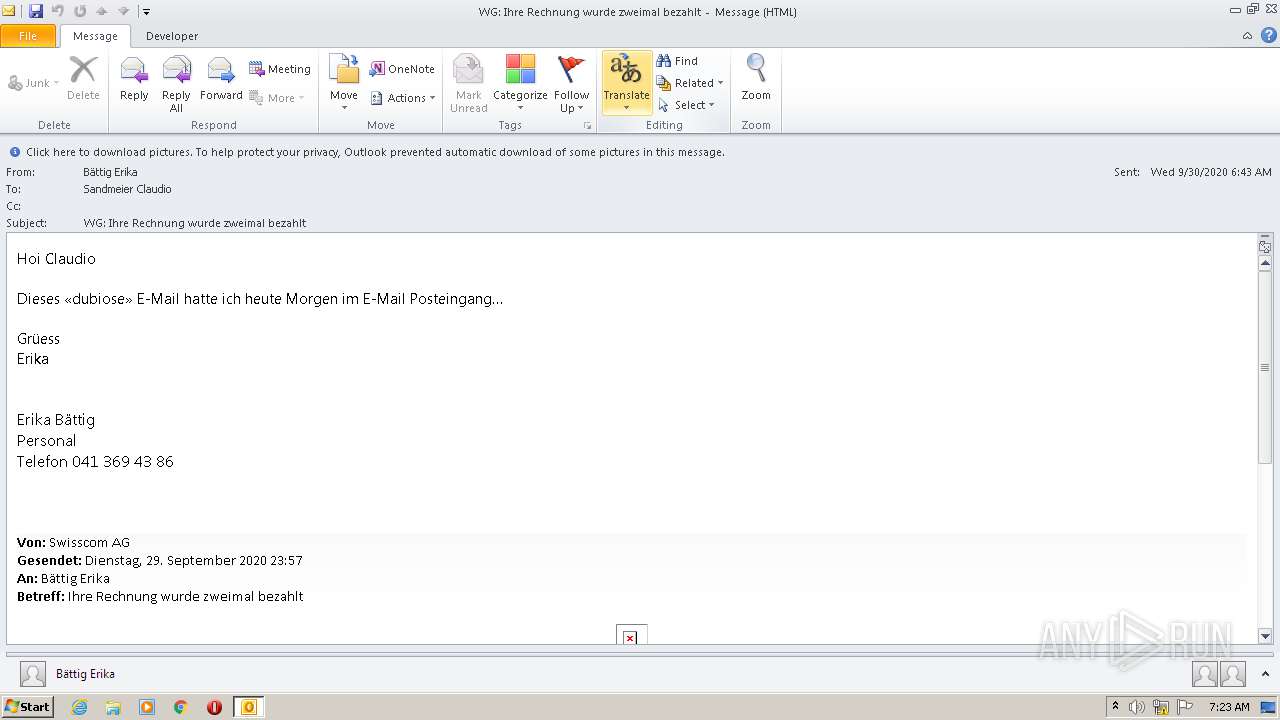
| 1688 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\WG Ihre Rechnung wurde zweimal bezahlt.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
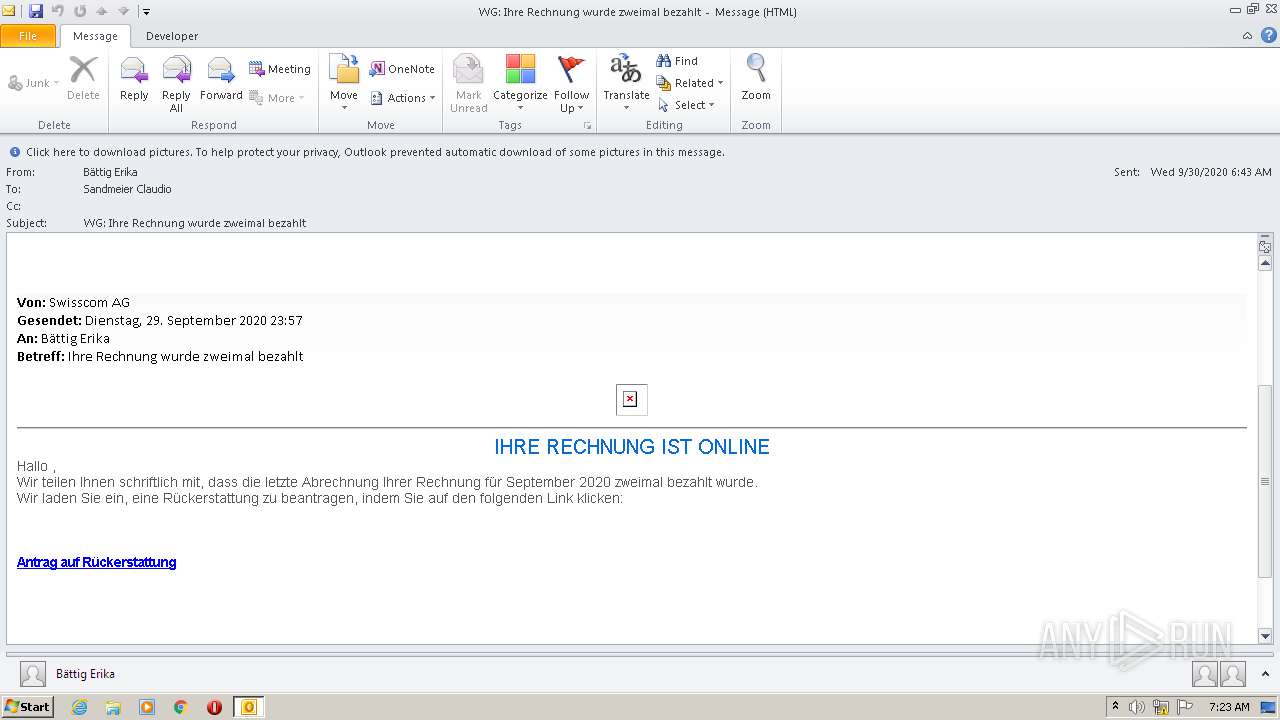
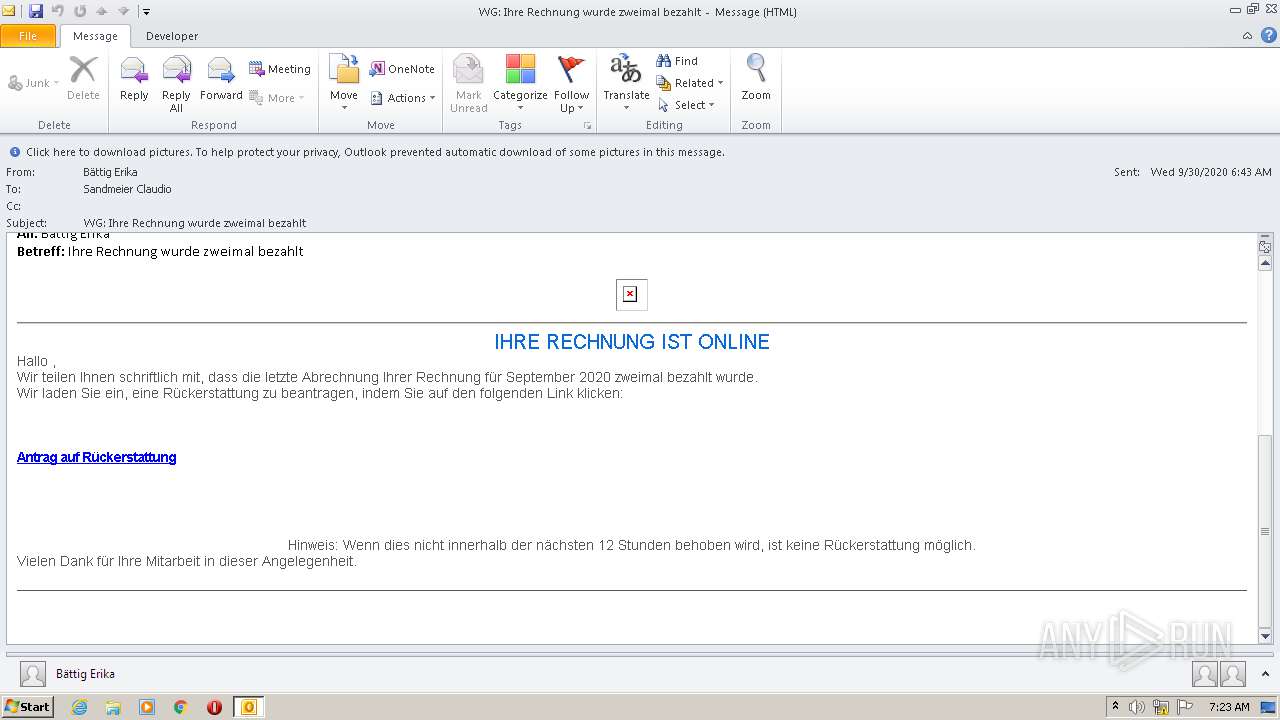
| 3960 | "C:\Program Files\Internet Explorer\iexplore.exe" https://slslskaikeie.mybigcommerce.com/y/ | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 072
Read events
1 096
Write events
956
Delete events
20
Modification events
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1688) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
26
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1688 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR7550.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBDD9FB36F158D989.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAB73EBAA97C9E2CA.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8F482BA94F62306C.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{885E1C8F-02E5-11EB-9060-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBD89AAFC80FD4067.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{885E1C8D-02E5-11EB-9060-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 1688 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1688 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1688 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{AADF1CE0-05AD-4423-A5BE-2B25B9F27DB5}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1688 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1688 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
668 | iexplore.exe | 35.227.210.197:443 | slslskaikeie.mybigcommerce.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
slslskaikeie.mybigcommerce.com |
| malicious |