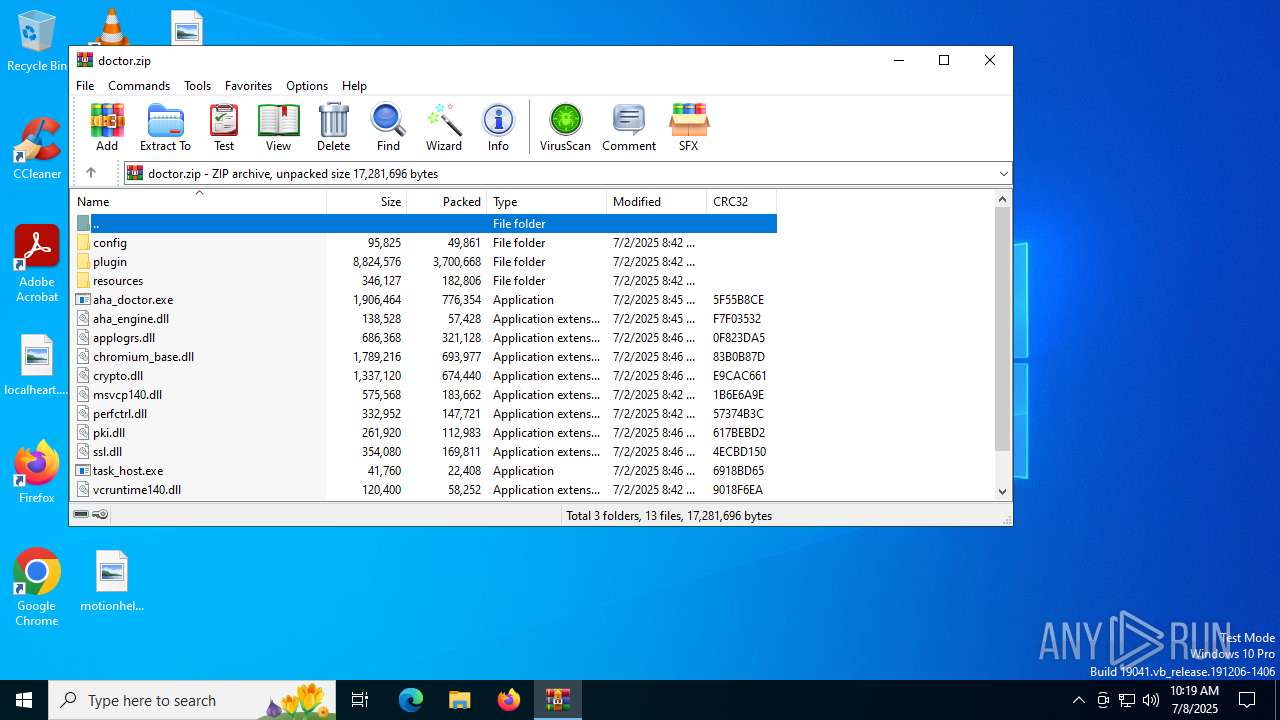
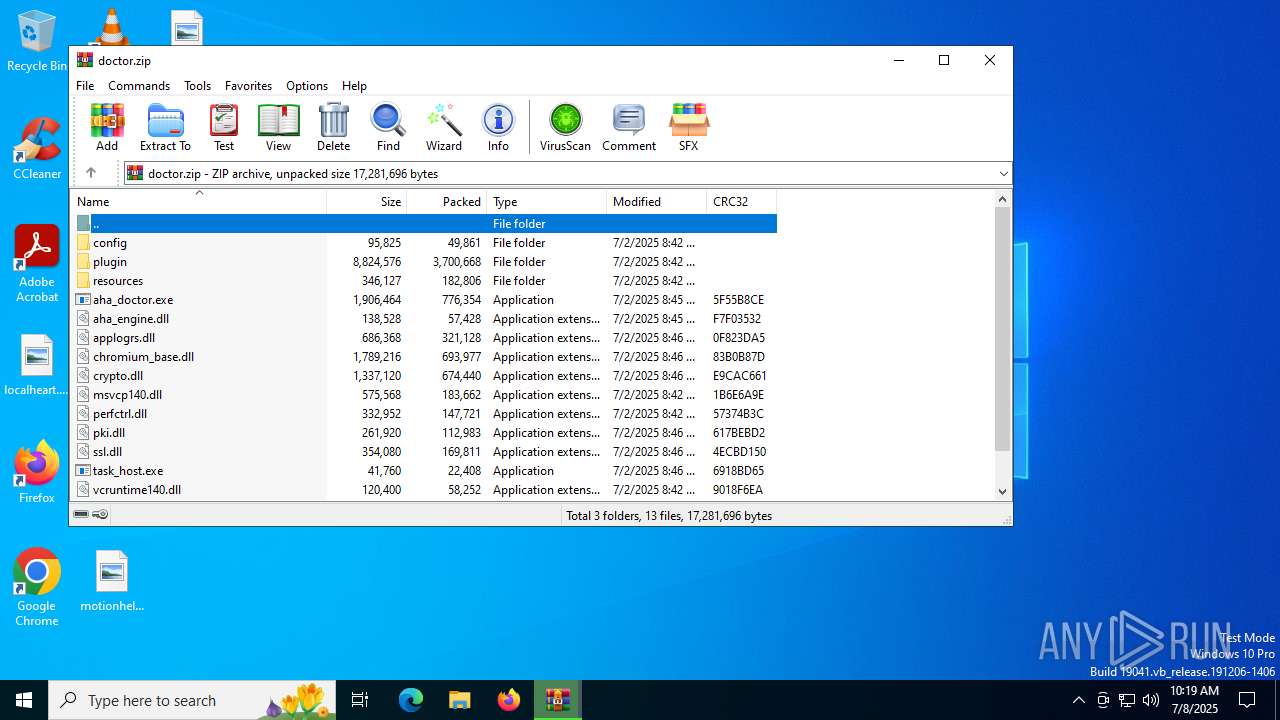
| File name: | doctor.zip |
| Full analysis: | https://app.any.run/tasks/1a1639c5-8a84-4005-ad8d-6f02836a4427 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 10:19:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B97D64E5F33E068AE8D8465D8DDD98A9 |
| SHA1: | 44EF5BFFB945BABF1BD010645FD55AA36D123E91 |
| SHA256: | 16750E5ECF5DB0EC2BE6950BB7176790644E63028968A062ADC3D8DF72988D5E |
| SSDEEP: | 98304:WMg2PN+DQgrkkYXQ9EqOSkHzPb/Zu9lMS/n2vARhcej966G/FPHo5nB4vuyvQUki:AL09jRfeZt9WB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3908)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6408)
- cmd.exe (PID: 2272)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3908)
Starts CMD.EXE for commands execution
- aha_doctor.exe (PID: 2288)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 4708)
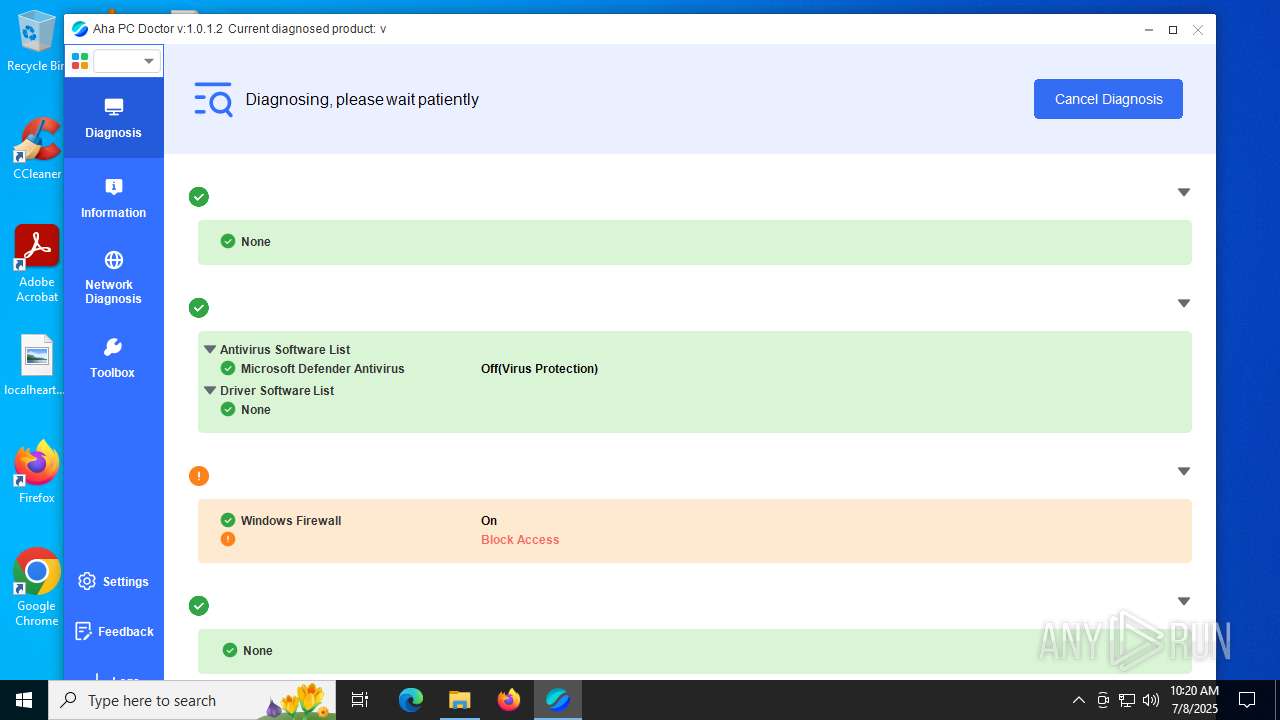
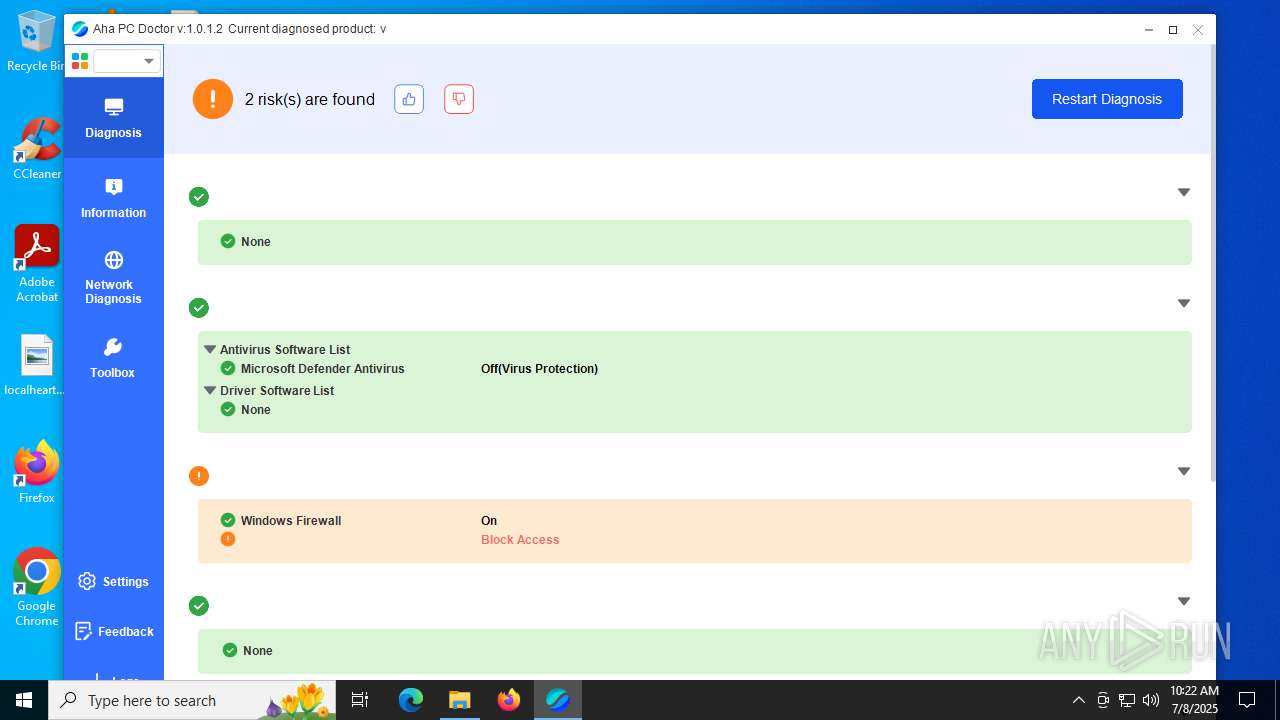
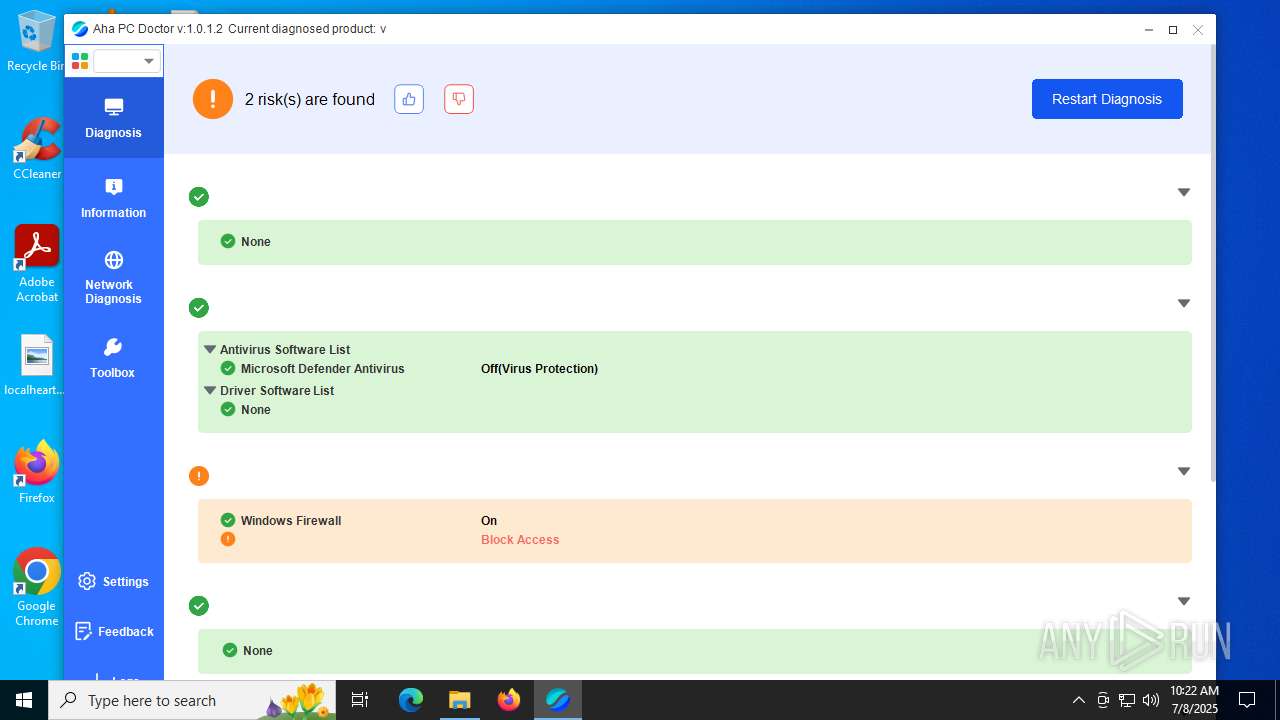
The process checks if it is being run in the virtual environment
- aha_doctor.exe (PID: 2288)
Reads the date of Windows installation
- aha_doctor.exe (PID: 2288)
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 5060)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3924)
Uses WMIC.EXE
- cmd.exe (PID: 6420)
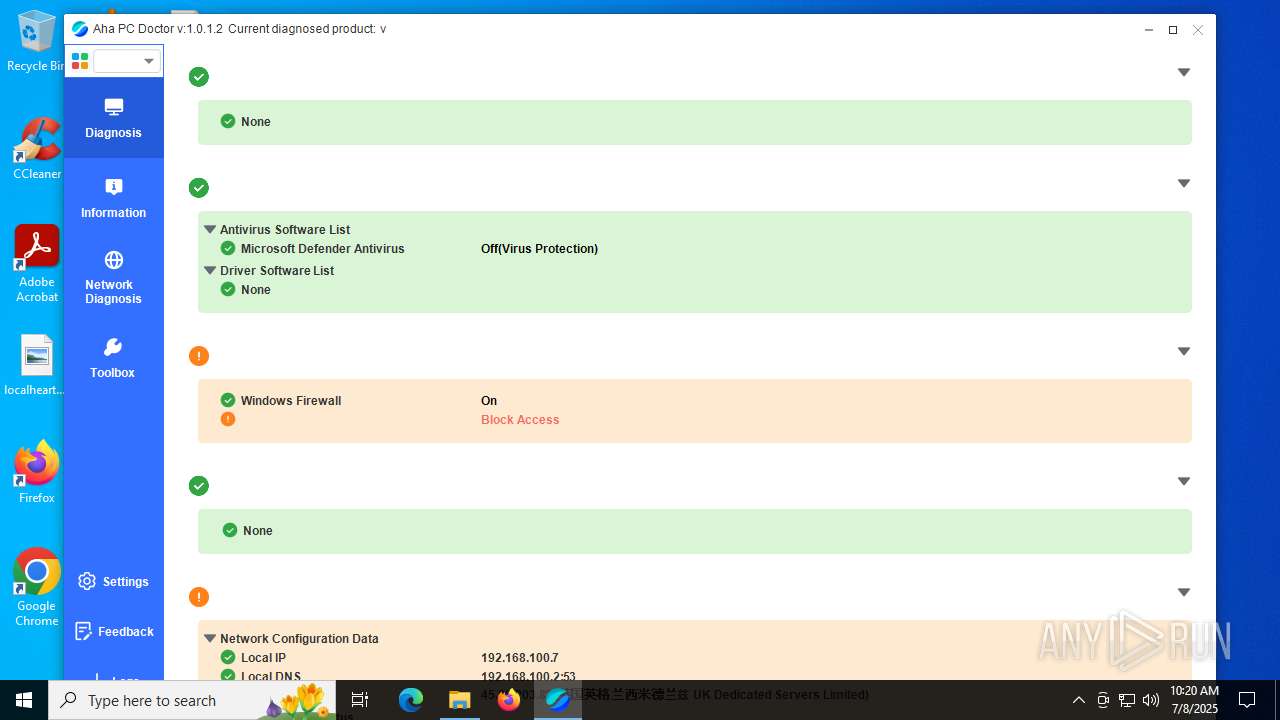
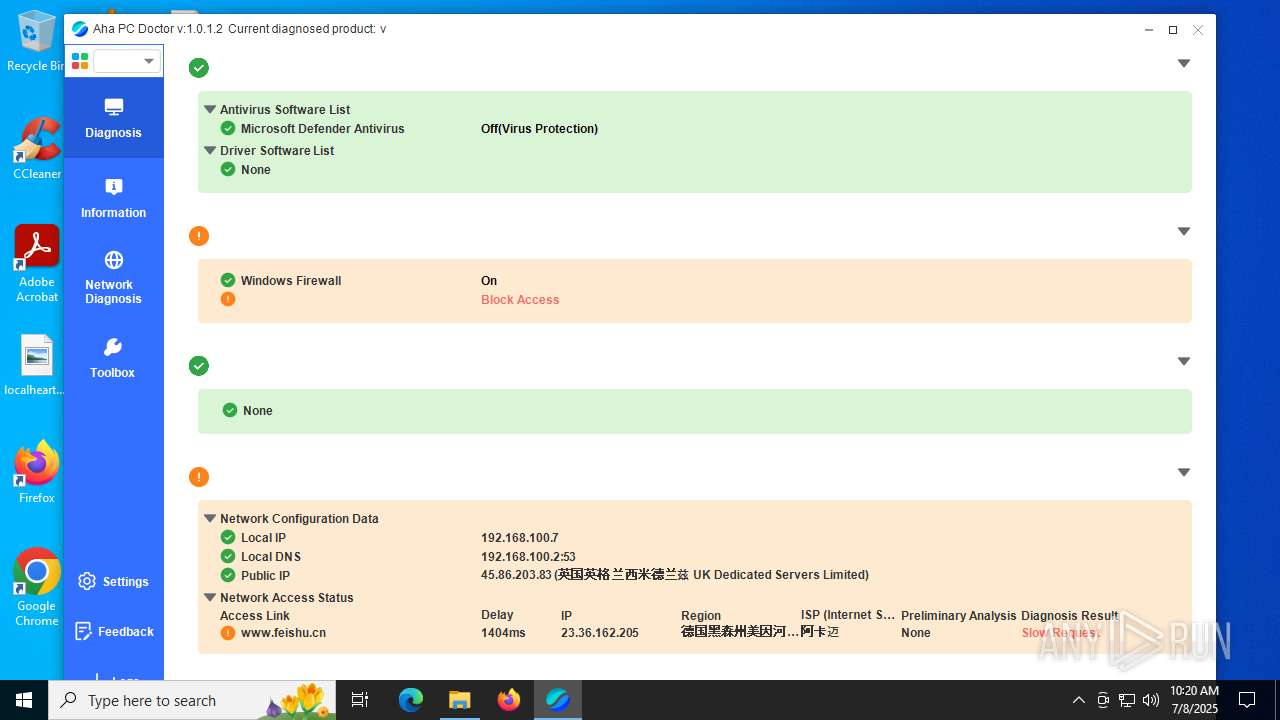
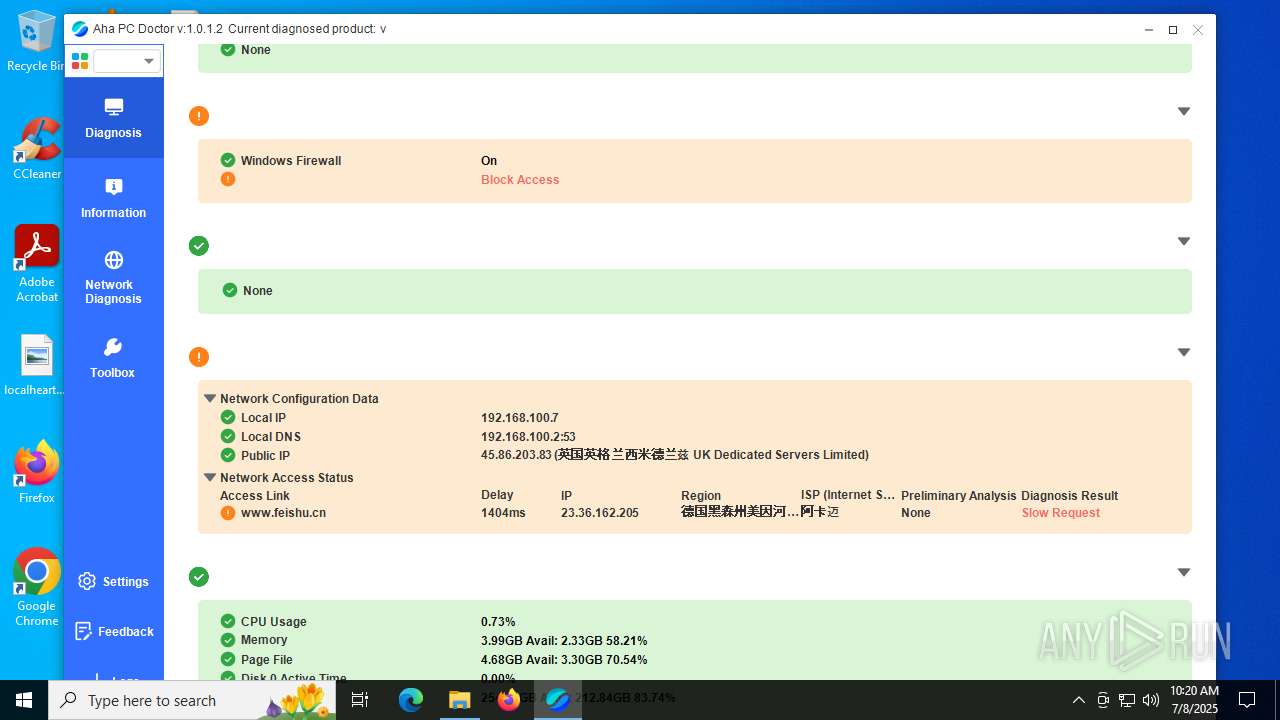
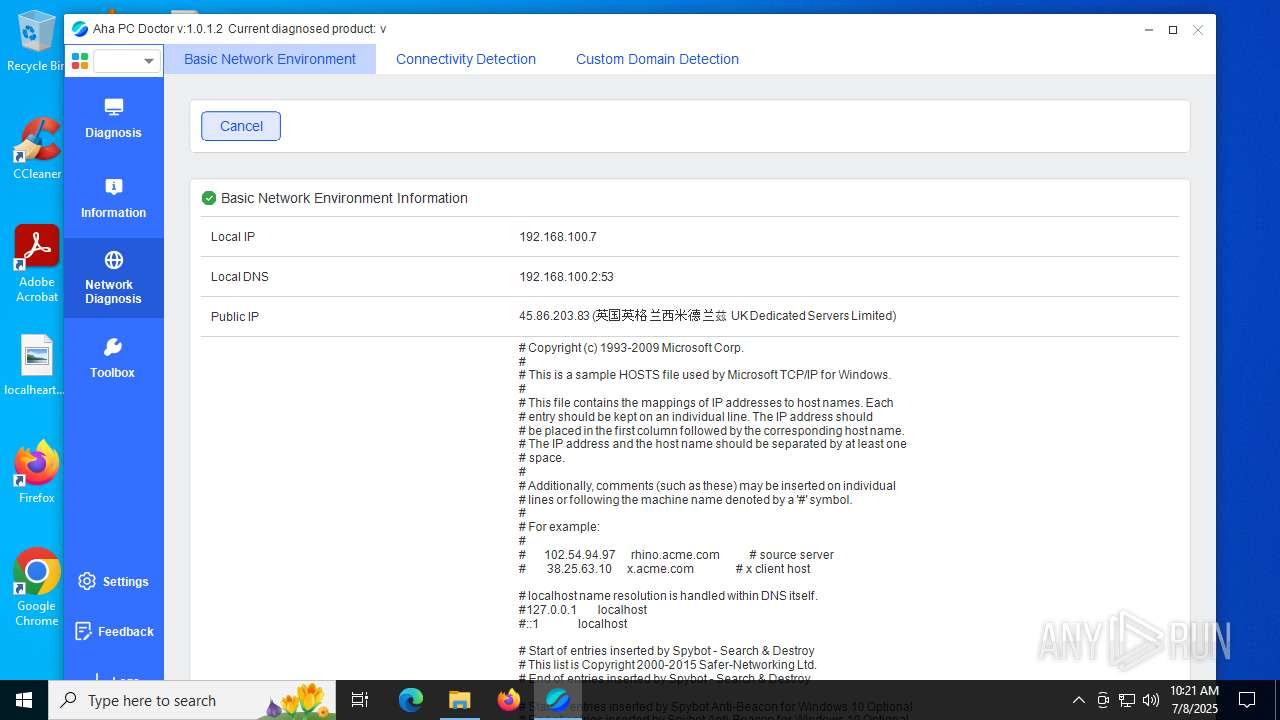
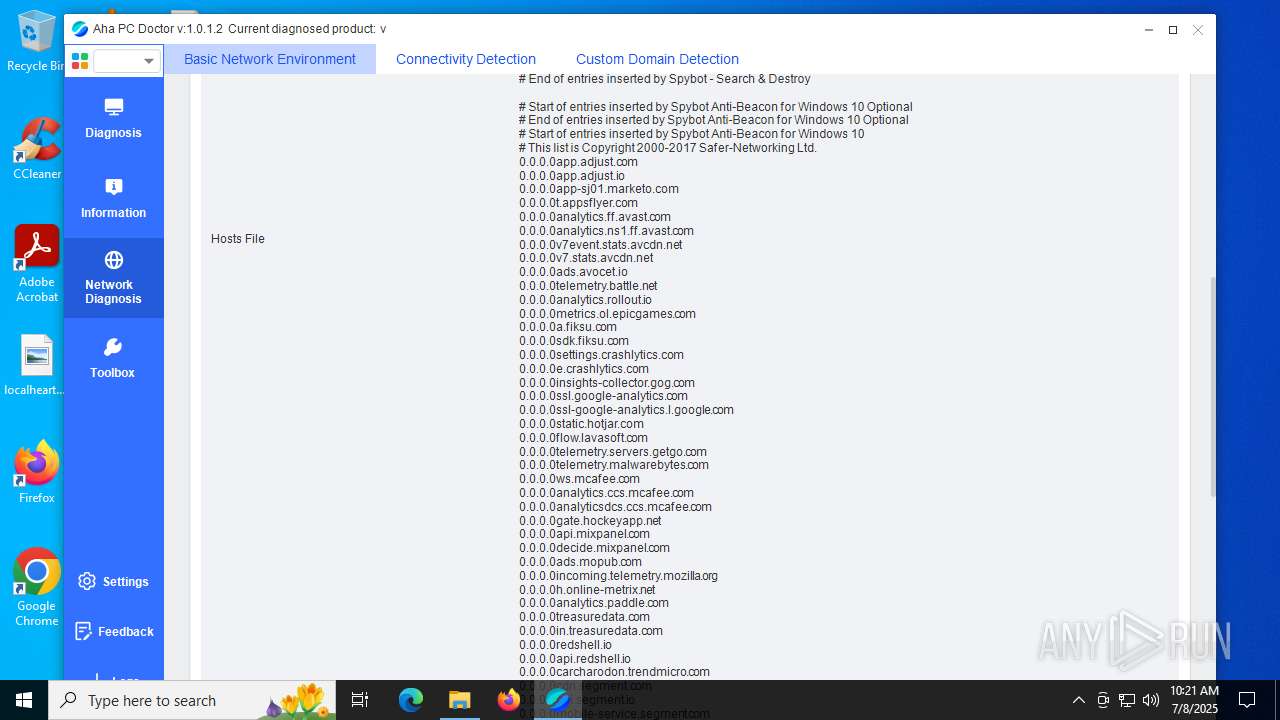
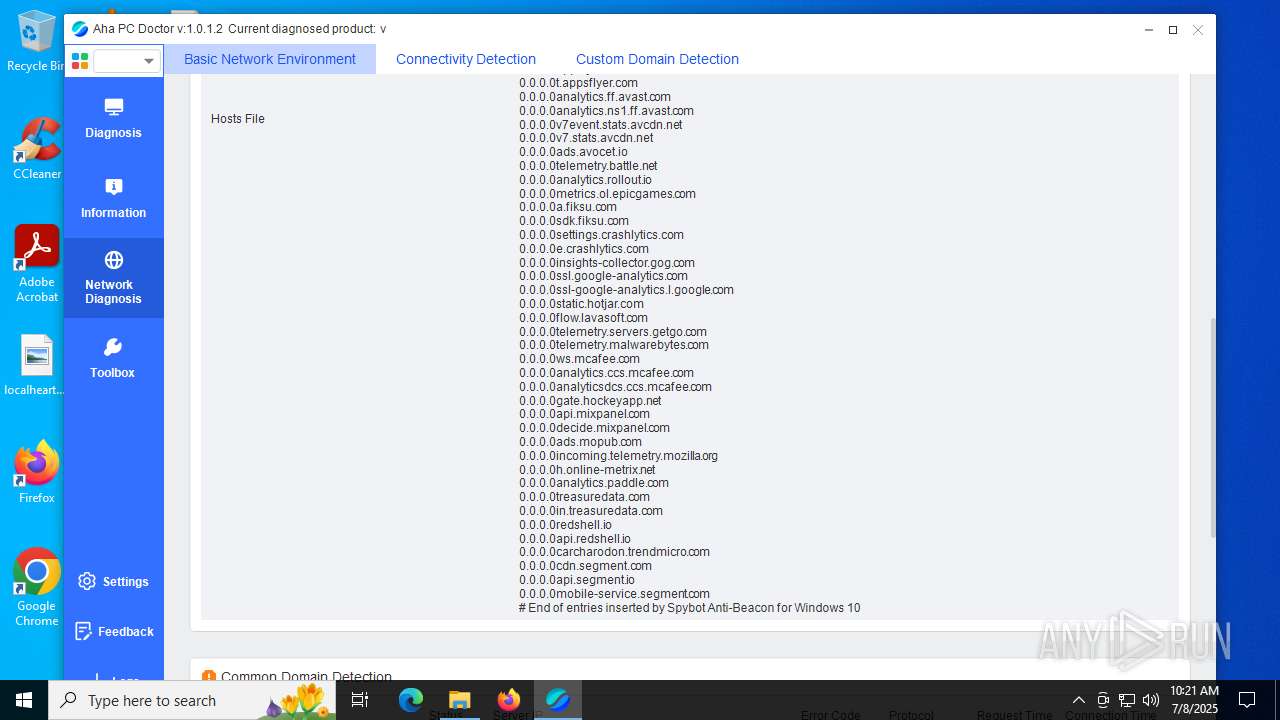
Checks for external IP
- svchost.exe (PID: 2200)
- aha_doctor.exe (PID: 2288)
There is functionality for capture public ip (YARA)
- aha_doctor.exe (PID: 2288)
INFO
Checks supported languages
- aha_doctor.exe (PID: 2288)
- task_host.exe (PID: 6180)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3908)
The sample compiled with english language support
- WinRAR.exe (PID: 3908)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1948)
- WMIC.exe (PID: 3504)
- WMIC.exe (PID: 6472)
- WMIC.exe (PID: 6936)
- WMIC.exe (PID: 2348)
- WMIC.exe (PID: 1632)
Reads the computer name
- aha_doctor.exe (PID: 2288)
Reads Environment values
- aha_doctor.exe (PID: 2288)
Reads product name
- aha_doctor.exe (PID: 2288)
Creates files or folders in the user directory
- aha_doctor.exe (PID: 2288)
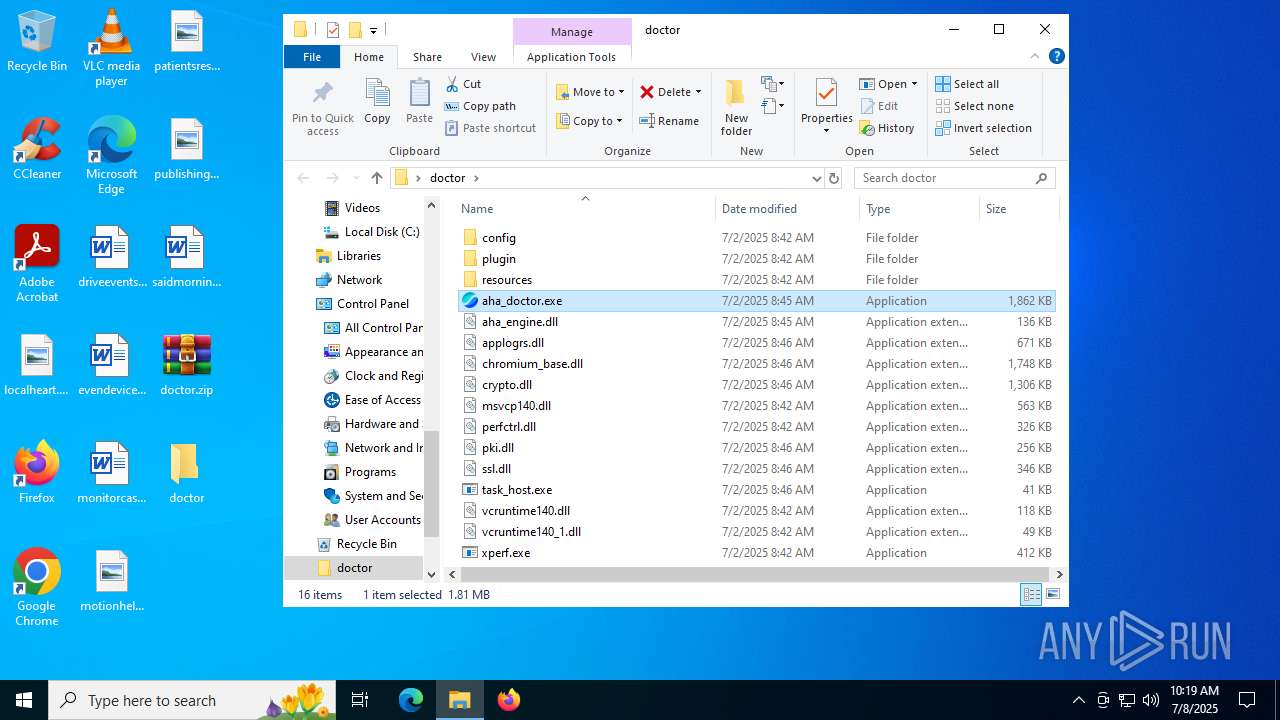
Manual execution by a user
- aha_doctor.exe (PID: 2288)
Application based on Rust
- aha_doctor.exe (PID: 2288)
Checks proxy server information
- aha_doctor.exe (PID: 2288)
- slui.exe (PID: 4084)
Reads the machine GUID from the registry
- aha_doctor.exe (PID: 2288)
Reads the software policy settings
- slui.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:07:02 16:45:50 |
| ZipCRC: | 0x5f55b8ce |
| ZipCompressedSize: | 776354 |
| ZipUncompressedSize: | 1906464 |
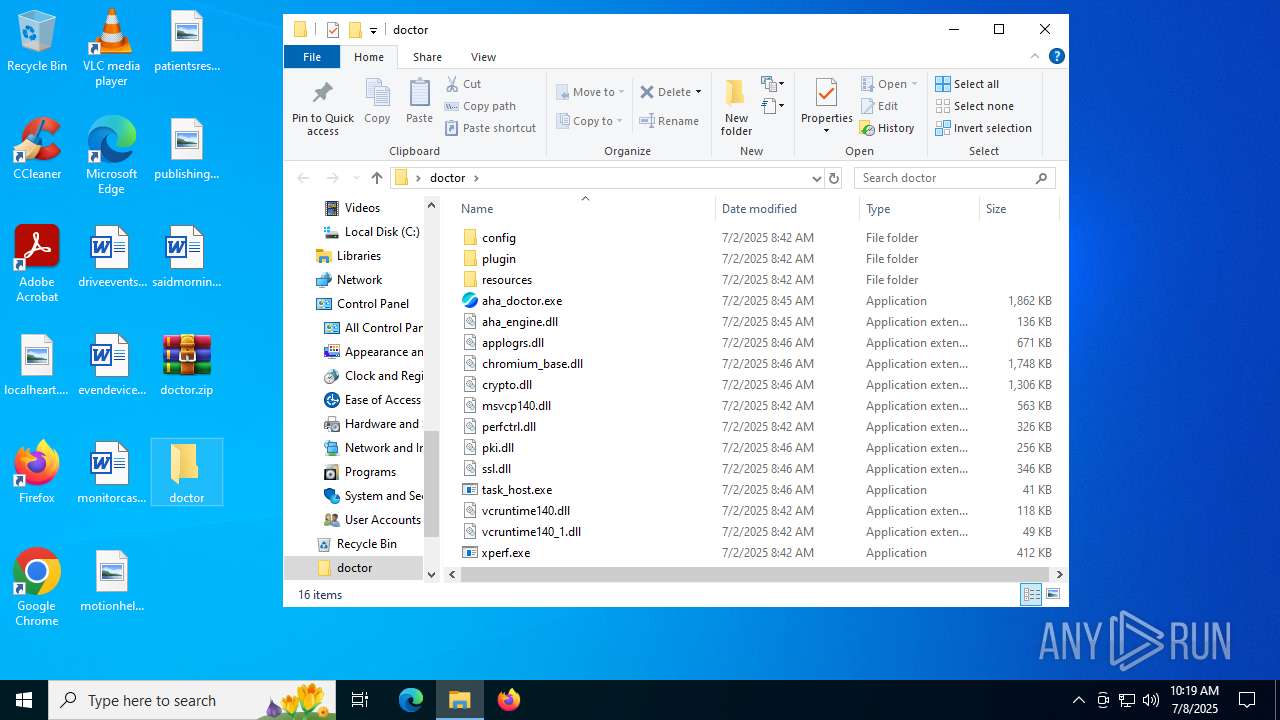
| ZipFileName: | aha_doctor.exe |
Total processes
159
Monitored processes
24
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | wmic Path Win32_PhysicalMemory Get Capacity /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | wmic csproduct get UUID /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2272 | "cmd" /C "wmic csproduct get UUID /value" | C:\Windows\System32\cmd.exe | — | aha_doctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\doctor\aha_doctor.exe" | C:\Users\admin\Desktop\doctor\aha_doctor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Aha Doctor Version: 1.0.1.2 Modules
| |||||||||||||||
| 2348 | wmic os get Version /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 830
Read events
5 796
Write events
21
Delete events
13
Modification events
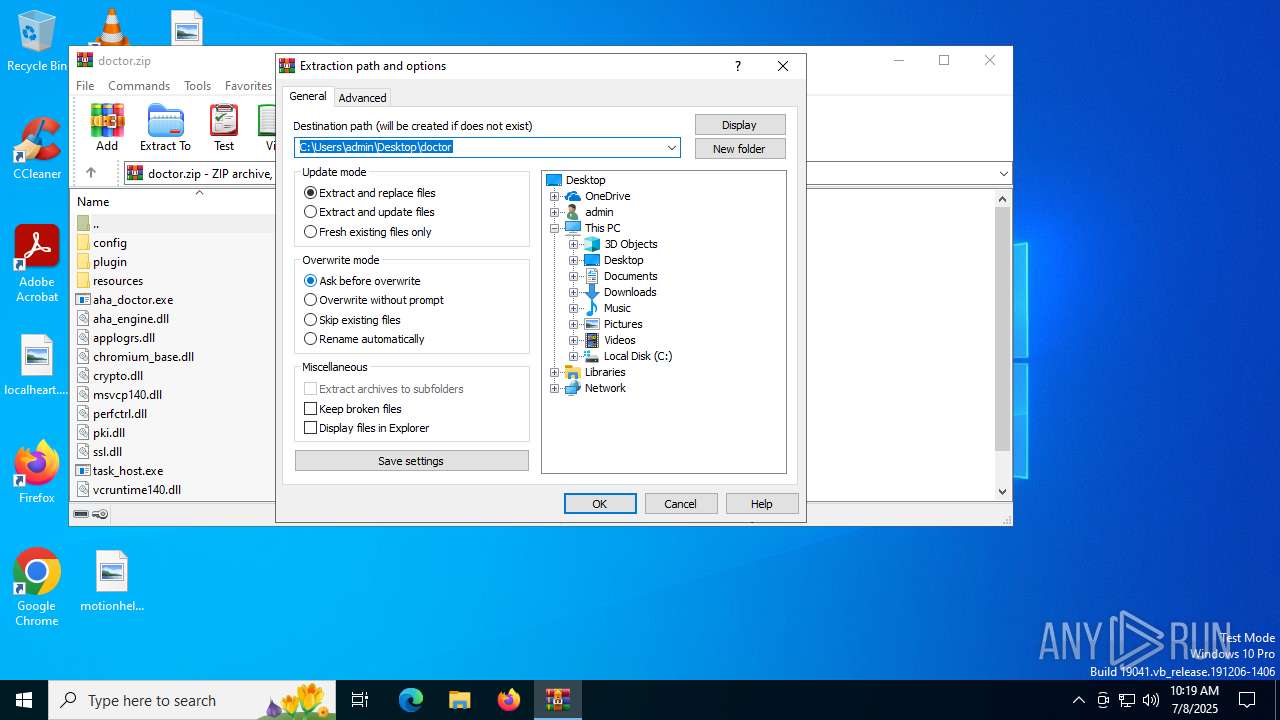
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\doctor.zip | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (3908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
21
Suspicious files
11
Text files
178
Unknown types
10
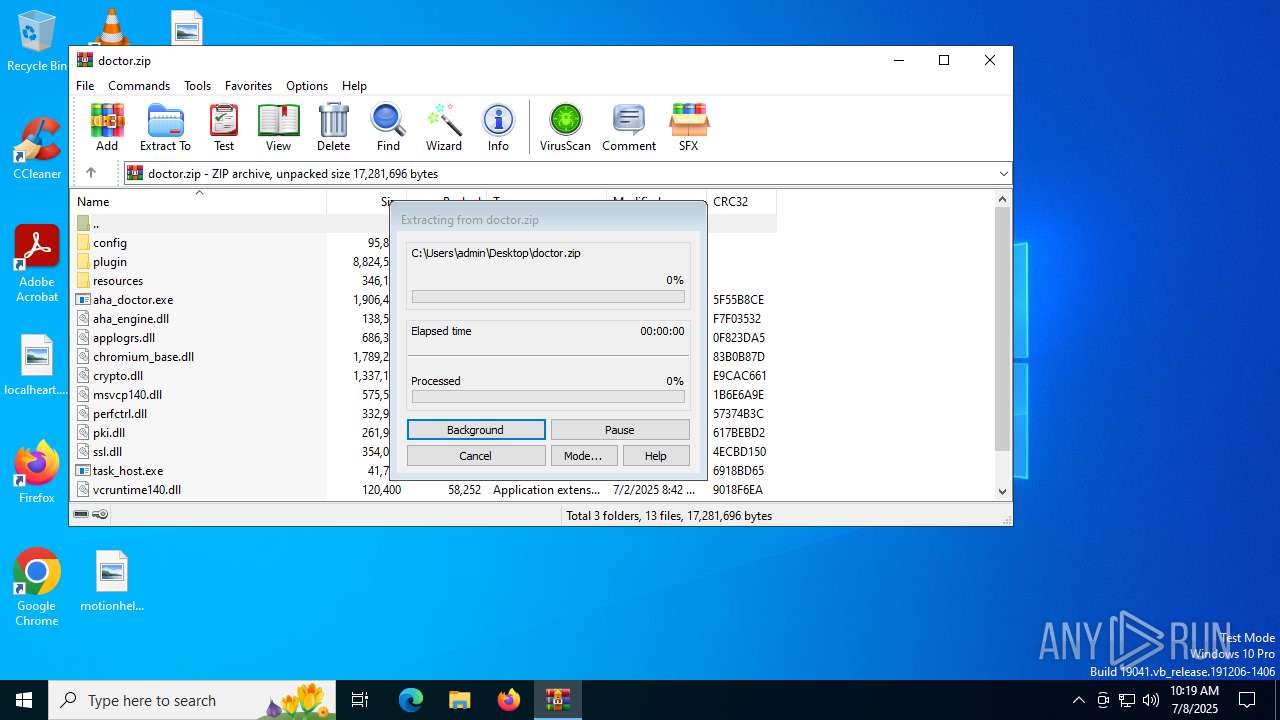
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\applogrs.dll | executable | |
MD5:5A71328C02BE015114D5C1DC33575CC8 | SHA256:9BB915E83F91801CE90D74DA956B711A3ABE8EEDDD6D06FDA27A2651700BBE7A | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\chromium_base.dll | executable | |
MD5:83B8F0E3A7EDF161F9F534E1C4EB6107 | SHA256:22AE64F67064340C0C928C9160F65921D786E230D92488FC0613AAF9401CEC02 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\config\21b2c27ce49c45626ed7515783e4b6262cb8c071ee | binary | |
MD5:0BDD9F8CF55690CDA915C35E876CCA01 | SHA256:83CCFB40BB3327CD496C334058EC62489BE4D9948E15860E33800418A9BDAFD7 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\config\third_party_feature.json | binary | |
MD5:24B96DAEFD82D213C11CEDAE1E0D3B93 | SHA256:6F5A9BF44E77CA35AFC0F6430CD62FCA0A59CEC53967B8F4A6E1C1AF5D8DB368 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\msvcp140.dll | executable | |
MD5:7ACBC57D268A691247B4A94FECFA42B4 | SHA256:00E9BCDAA386942DFA7631079C450E702D6CE96E1D0A6ADED91D2F9436855320 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\config\brand_db.json | binary | |
MD5:A96100A464273CF60669777A1609FE98 | SHA256:0F11288AC17064EA4E4B0619F7AF4A930D04CAD281B19C3793A40AA762385EC4 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\aha_doctor.exe | executable | |
MD5:5AB1727361F9A95428A6E63AB8BFCC8D | SHA256:CEC76AC8F504188E12531706AF5CAA2B1687C55AC524F3F9A25BB764090BF95D | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\perfctrl.dll | executable | |
MD5:1A30A5CB16B97BE962F81F0592E293C0 | SHA256:14BFCBD518546275D042B7D2A35227452577921D6E2C6310B3EEBC029A00D3B6 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\plugin\brand_info.dll | executable | |
MD5:017B902508FD4A9B1D3F147A14D9690F | SHA256:AFA9FA4858AB73828D2FD80558C81C4AFB0AA101B412C511354F96BB9D659A28 | |||
| 3908 | WinRAR.exe | C:\Users\admin\Desktop\doctor\pki.dll | executable | |
MD5:95CD1A9145B7D3C9C8B25C798F1B6F99 | SHA256:64DC0A417E1D250A3B26A02E35410D9F5B8150F015684D35838601DC6DC0FD4A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
115
DNS requests
32
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6320 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6320 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2288 | aha_doctor.exe | 163.181.254.187:443 | log-klink.zijieapi.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
log-klink.zijieapi.com |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ifconfig .me) in DNS Lookup |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
2288 | aha_doctor.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ifconfig .me) in TLS SNI |