| File name: | WebAdvisorInstall.exe |
| Full analysis: | https://app.any.run/tasks/fa118b8e-6b21-46fe-addd-f5c181e2142f |
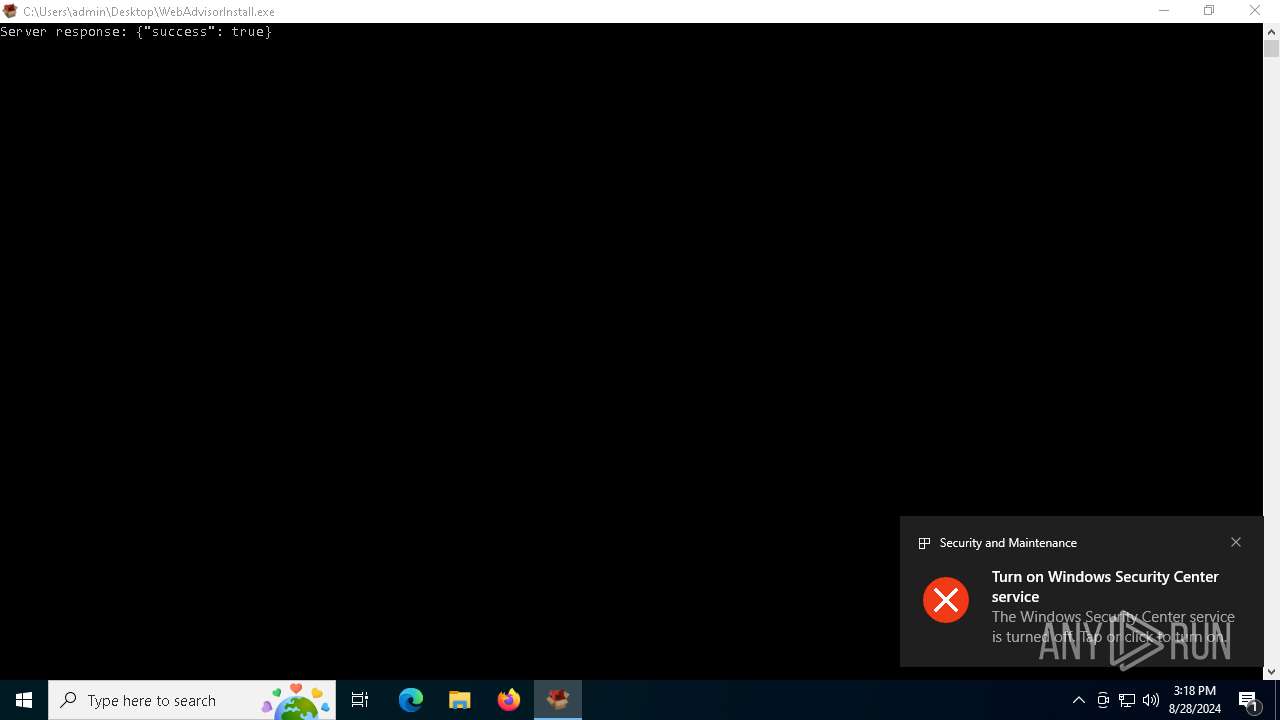
| Verdict: | Malicious activity |
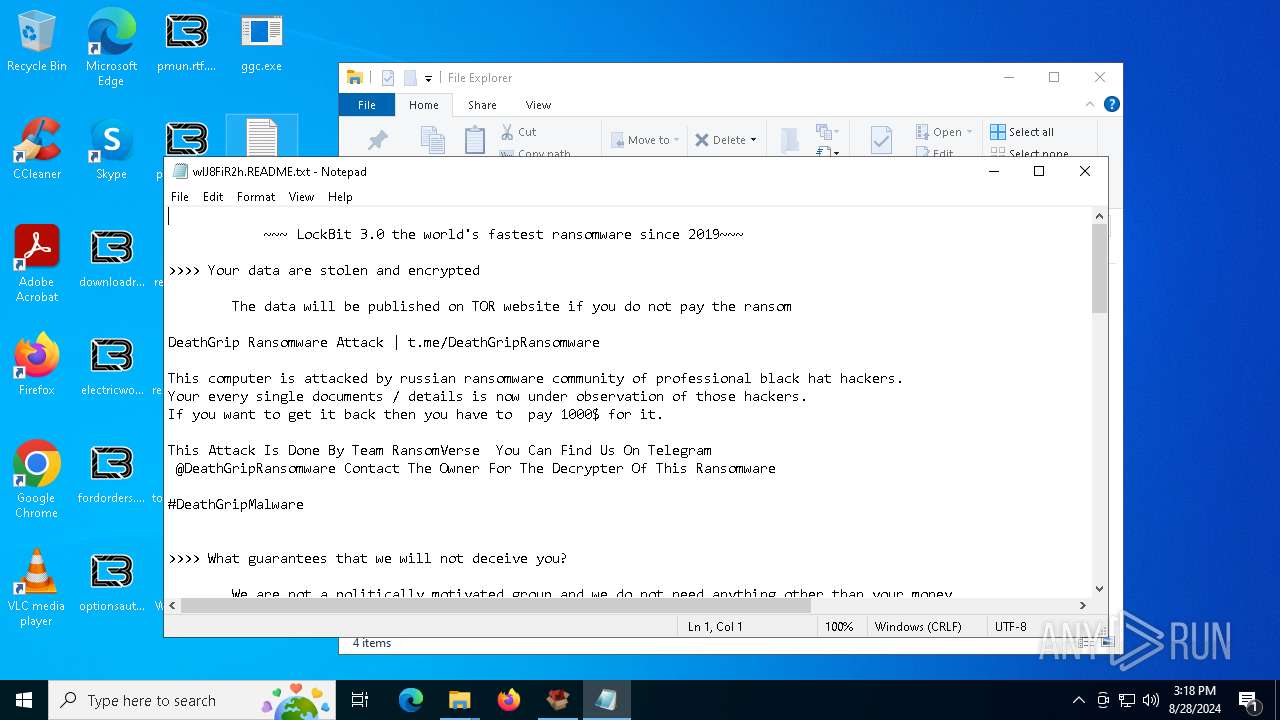
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | August 28, 2024, 15:17:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | BE8BF725892DDD7A200D0A1906B9387F |
| SHA1: | 582A24A72B29E70F2DE26A8D217492C7A6B983FF |
| SHA256: | 166BBA02413995AFF28FFEB27D3BF3D5A5F6A6CD36893E252C7B9A22836F4980 |
| SSDEEP: | 98304:ZrdcvhJJkZA8m0qRttZYtvrjba7WThiXt/BprciWR6rjba7WThiXt/BprciWRWrA:I |
MALICIOUS
Fake LOCKBIT has been detected
- ggc.exe (PID: 5276)
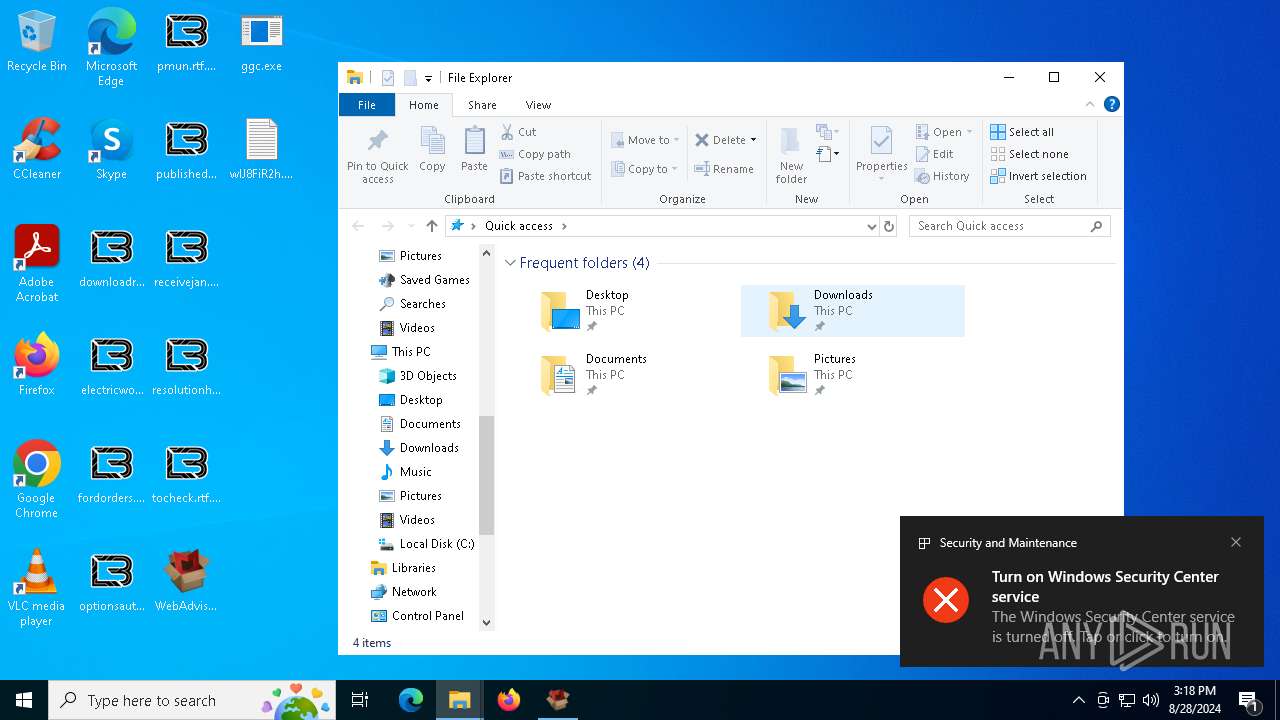
Renames files like ransomware
- ggc.exe (PID: 5276)
Actions looks like stealing of personal data
- ggc.exe (PID: 5276)
Steals credentials from Web Browsers
- ggc.exe (PID: 5276)
[YARA] LockBit is detected
- ggc.exe (PID: 5276)
SUSPICIOUS
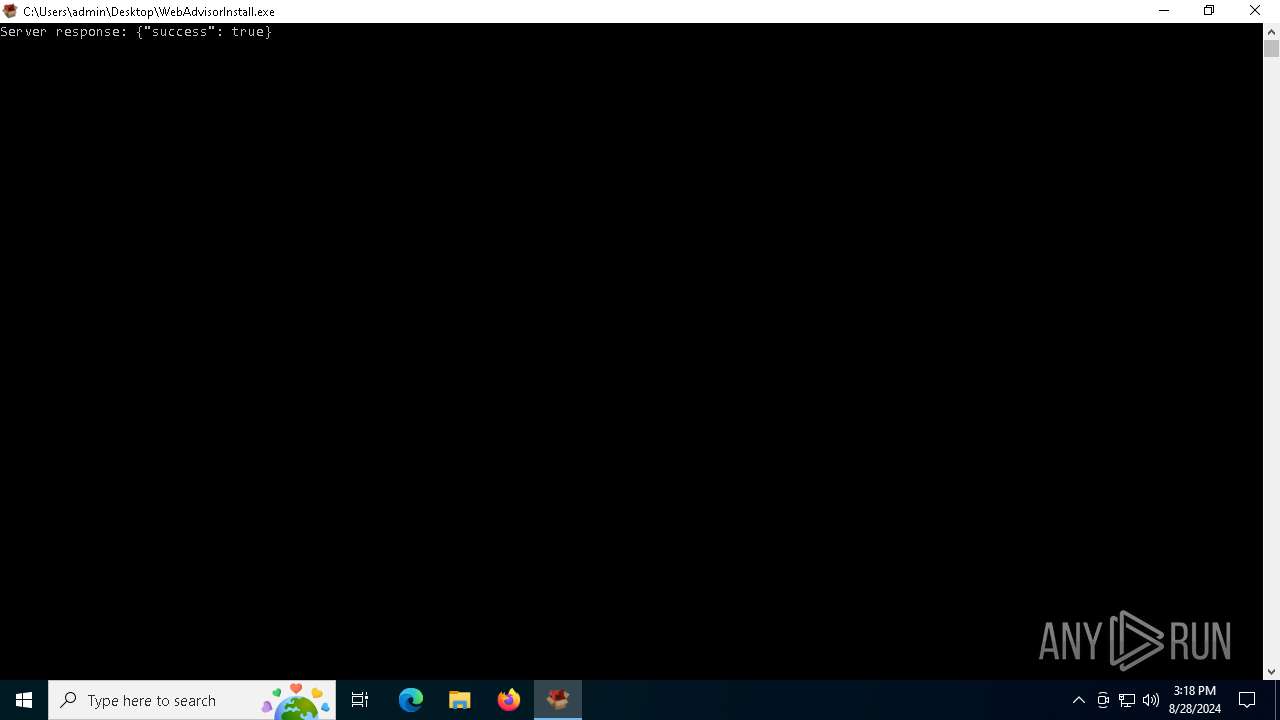
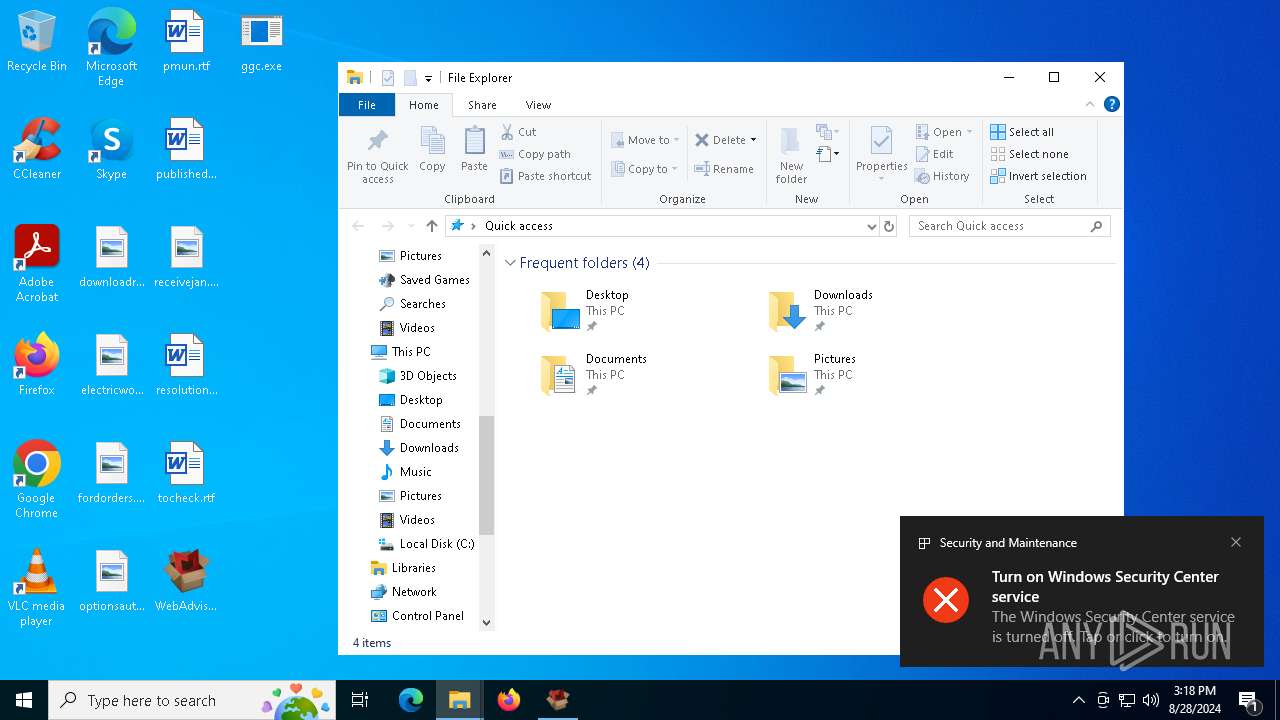
Drops the executable file immediately after the start
- WebAdvisorInstall.exe (PID: 3812)
- ggc.exe (PID: 5276)
Reads security settings of Internet Explorer
- WebAdvisorInstall.exe (PID: 3812)
- ShellExperienceHost.exe (PID: 2480)
Checks Windows Trust Settings
- WebAdvisorInstall.exe (PID: 3812)
Executable content was dropped or overwritten
- WebAdvisorInstall.exe (PID: 3812)
Reads the date of Windows installation
- WebAdvisorInstall.exe (PID: 3812)
Write to the desktop.ini file (may be used to cloak folders)
- ggc.exe (PID: 5276)
INFO
Reads the computer name
- WebAdvisorInstall.exe (PID: 3812)
- ggc.exe (PID: 5276)
- ShellExperienceHost.exe (PID: 2480)
Checks supported languages
- WebAdvisorInstall.exe (PID: 3812)
- ggc.exe (PID: 5276)
- ShellExperienceHost.exe (PID: 2480)
Checks proxy server information
- WebAdvisorInstall.exe (PID: 3812)
Reads the machine GUID from the registry
- WebAdvisorInstall.exe (PID: 3812)
Reads the software policy settings
- WebAdvisorInstall.exe (PID: 3812)
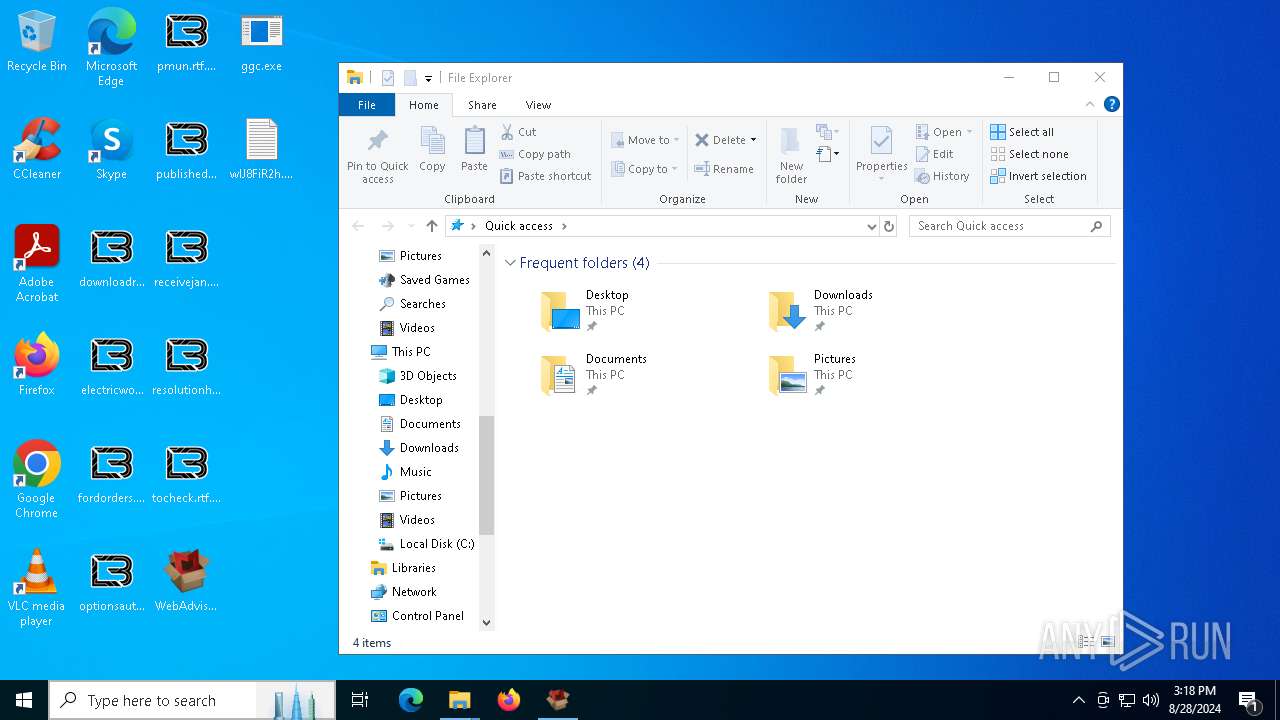
Creates files or folders in the user directory
- WebAdvisorInstall.exe (PID: 3812)
- ggc.exe (PID: 5276)
Process checks computer location settings
- WebAdvisorInstall.exe (PID: 3812)
Creates files in the program directory
- ggc.exe (PID: 5276)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6208)
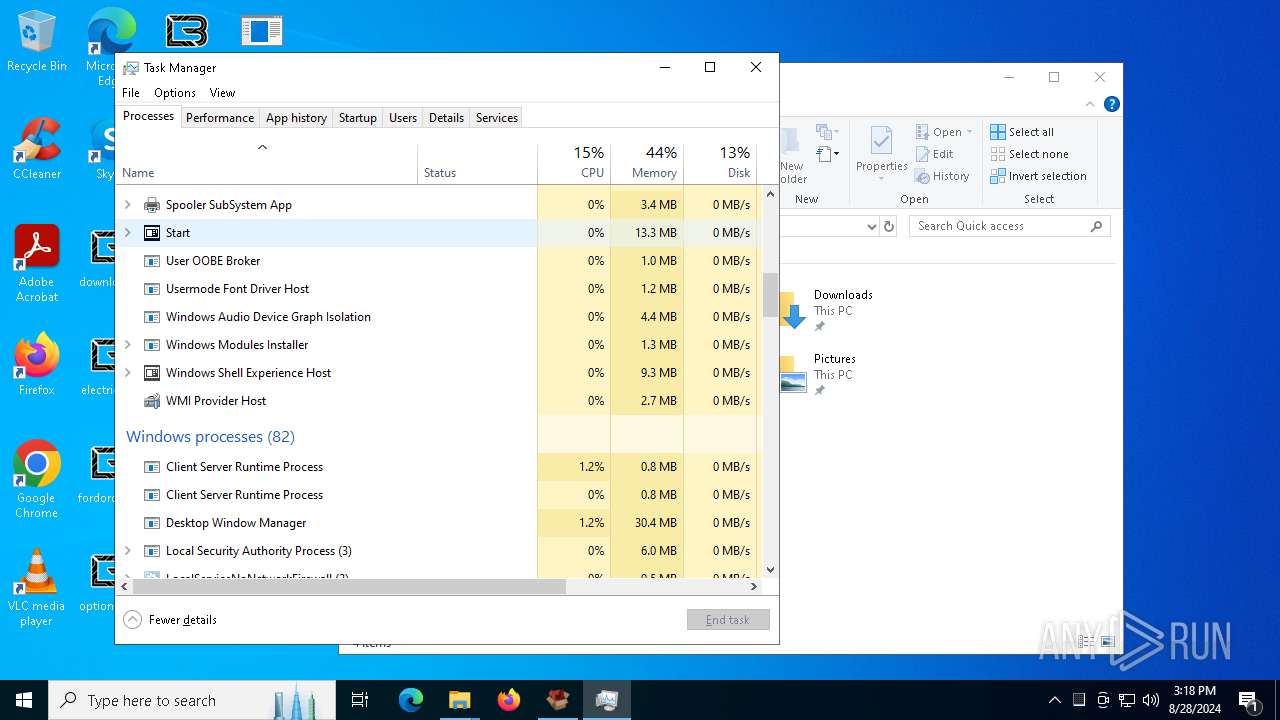
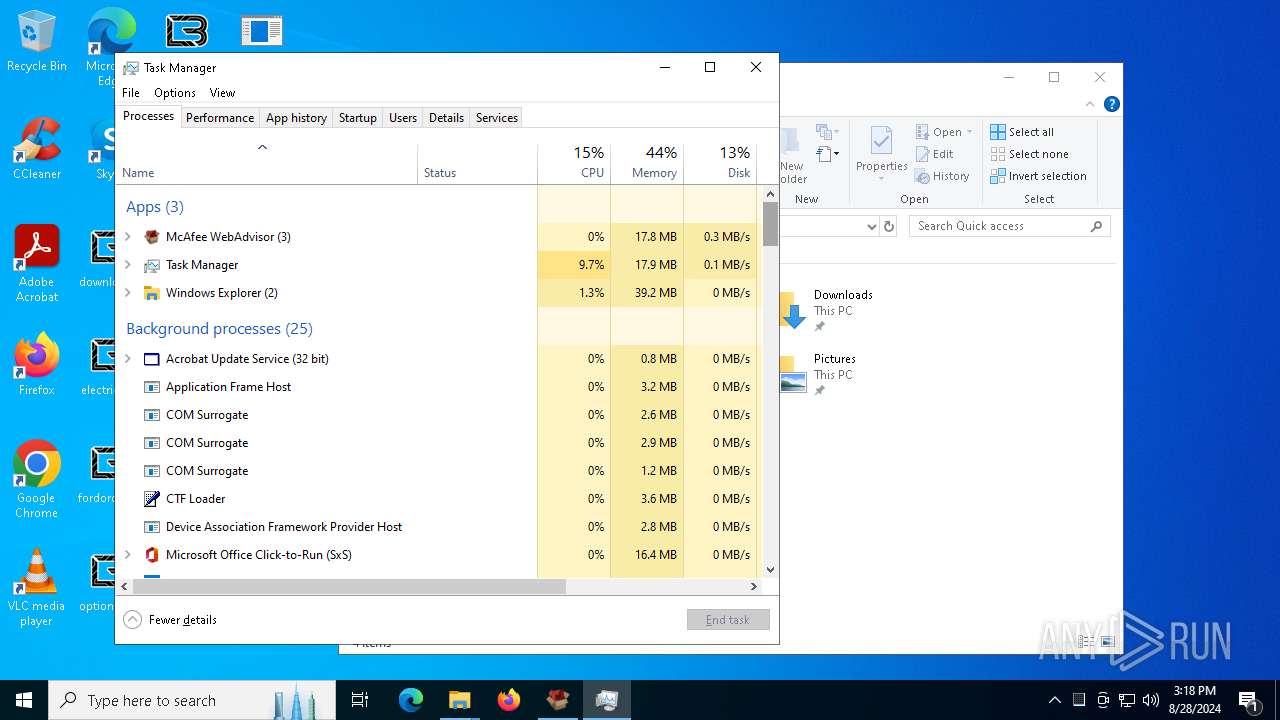
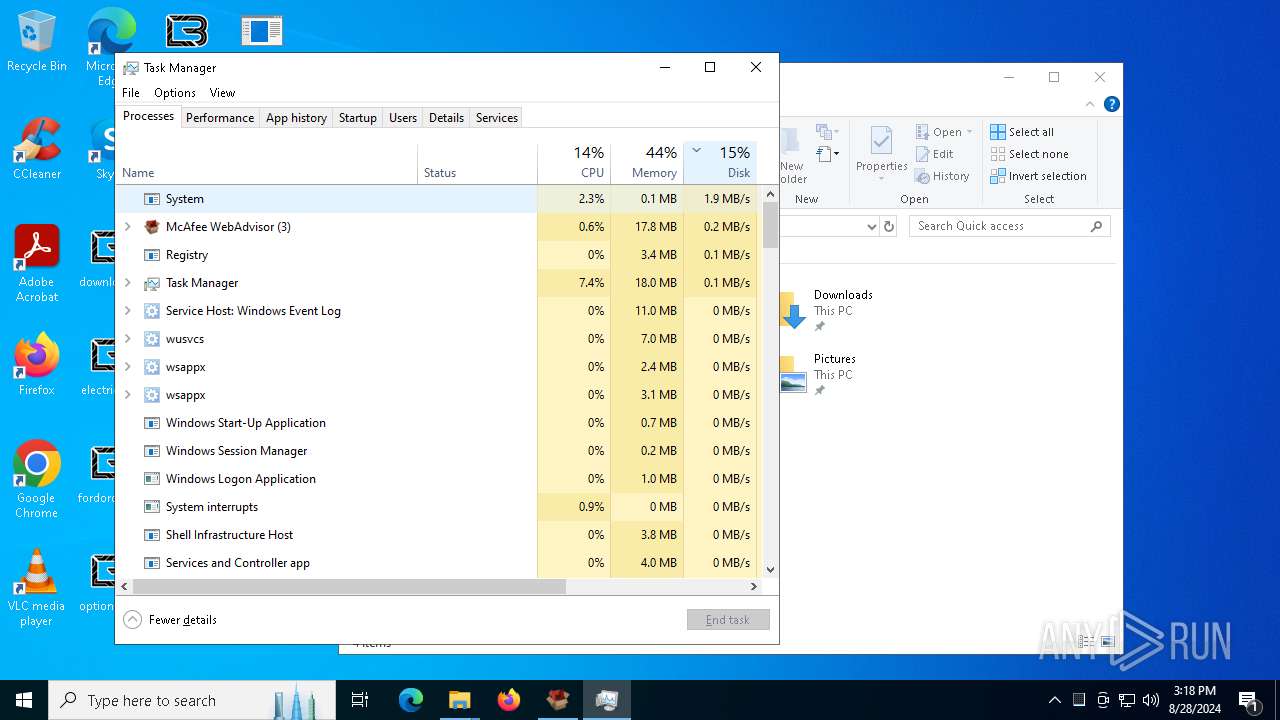
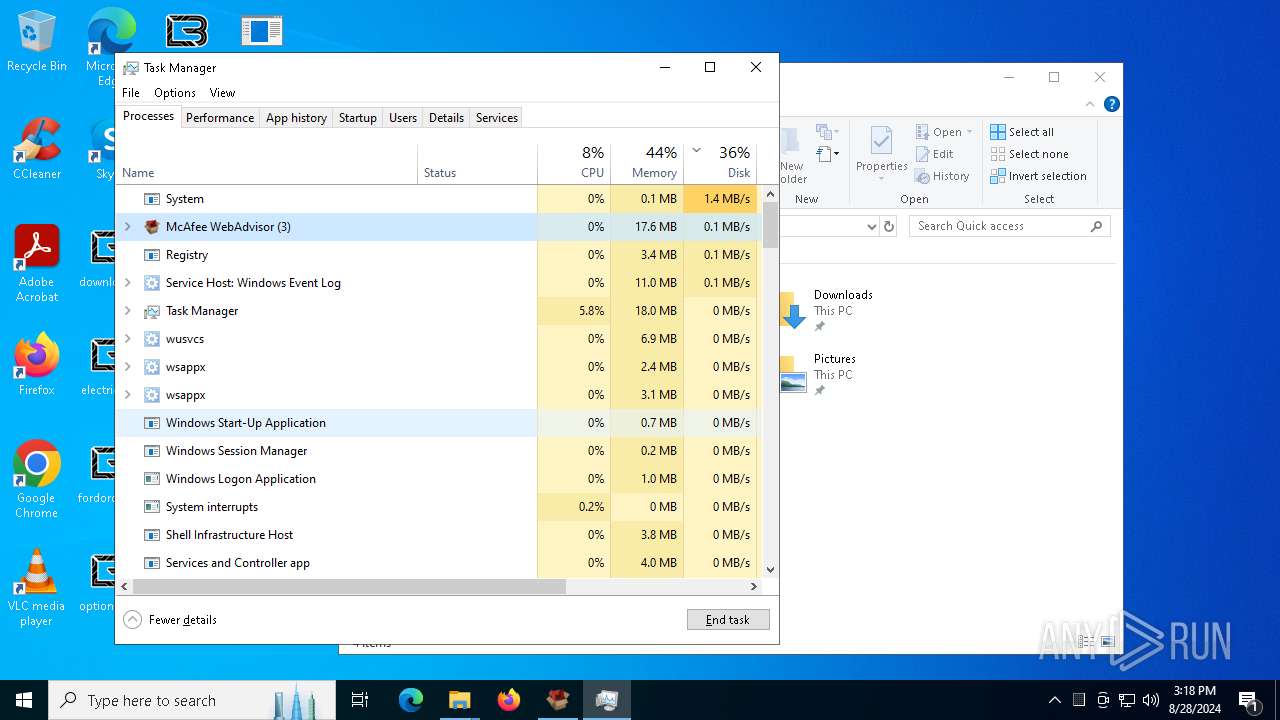
- Taskmgr.exe (PID: 4448)
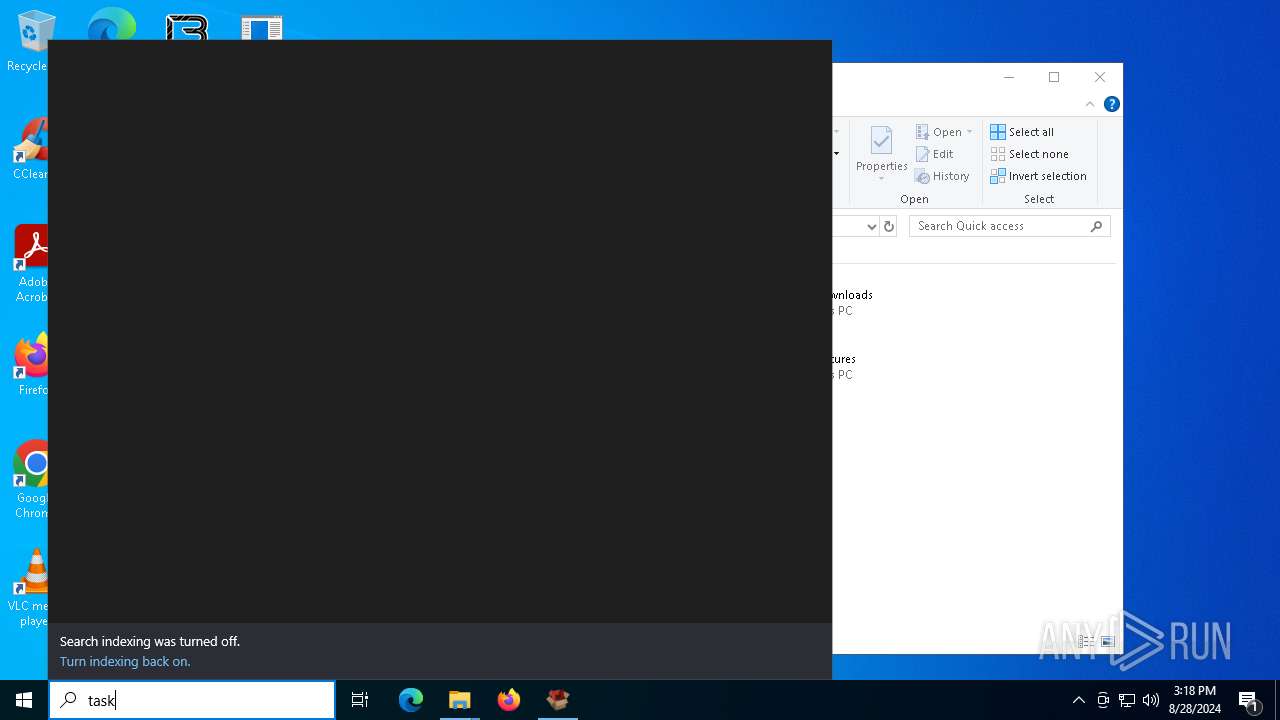
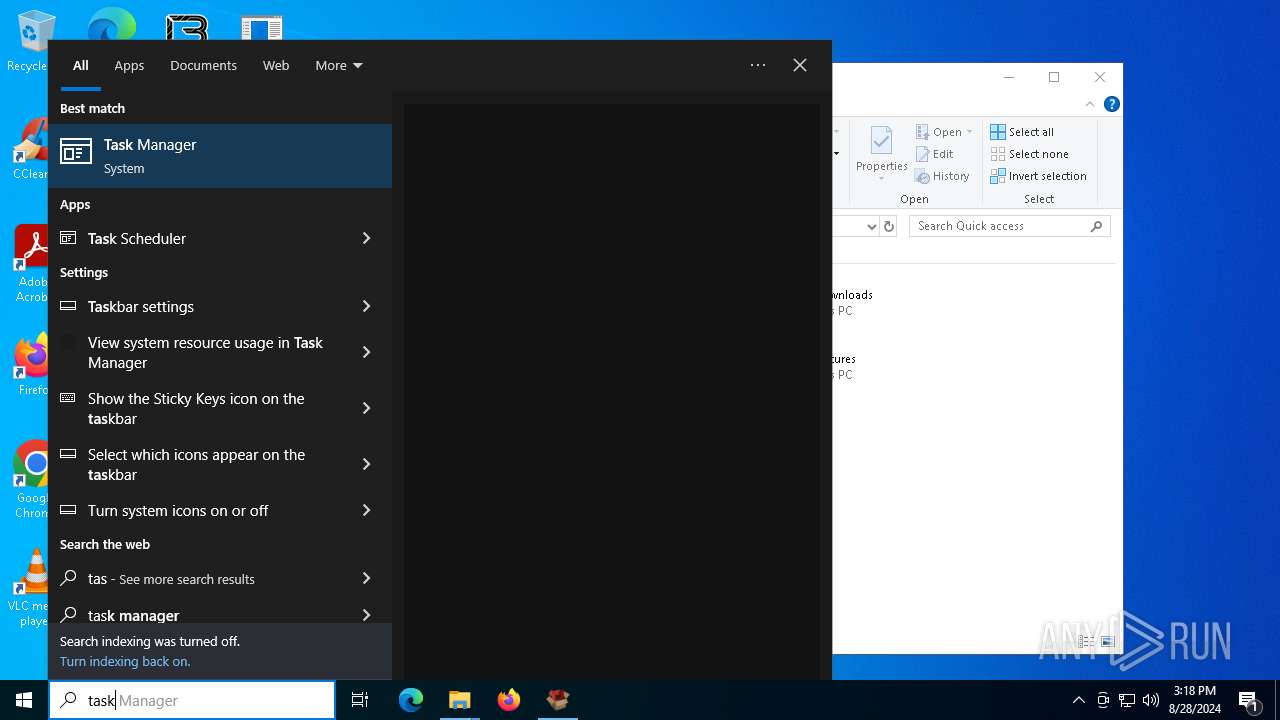
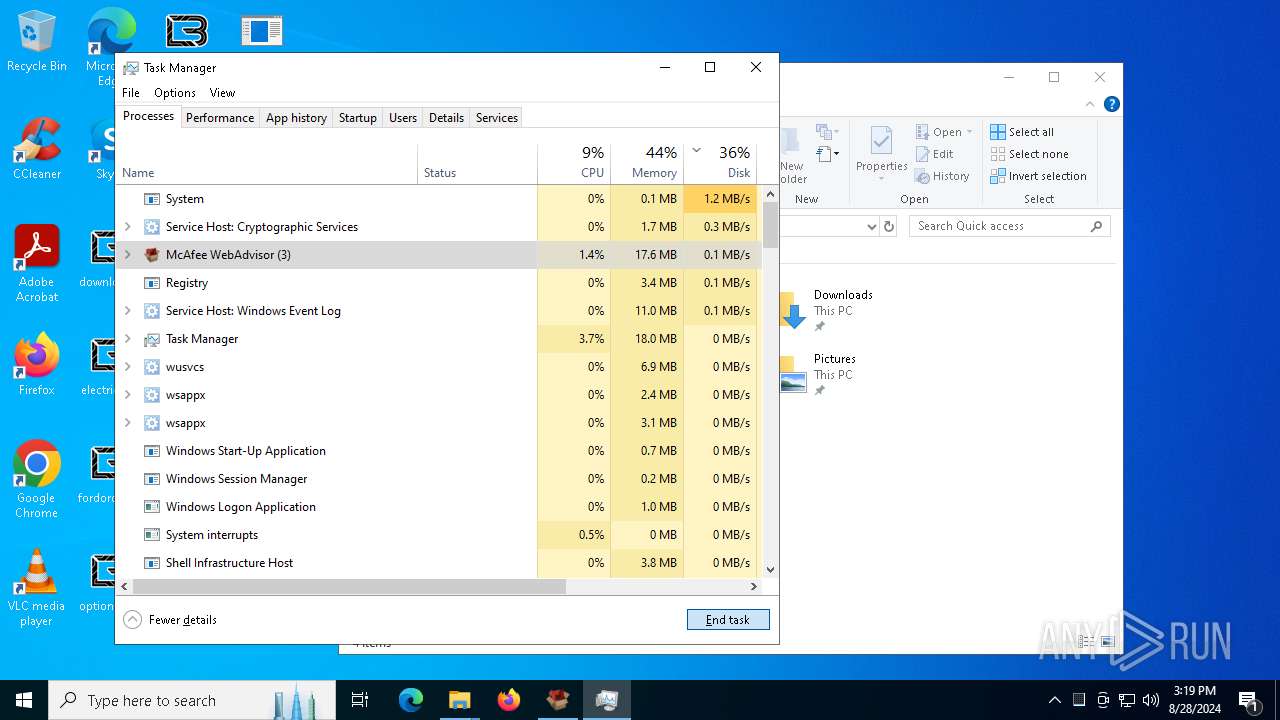
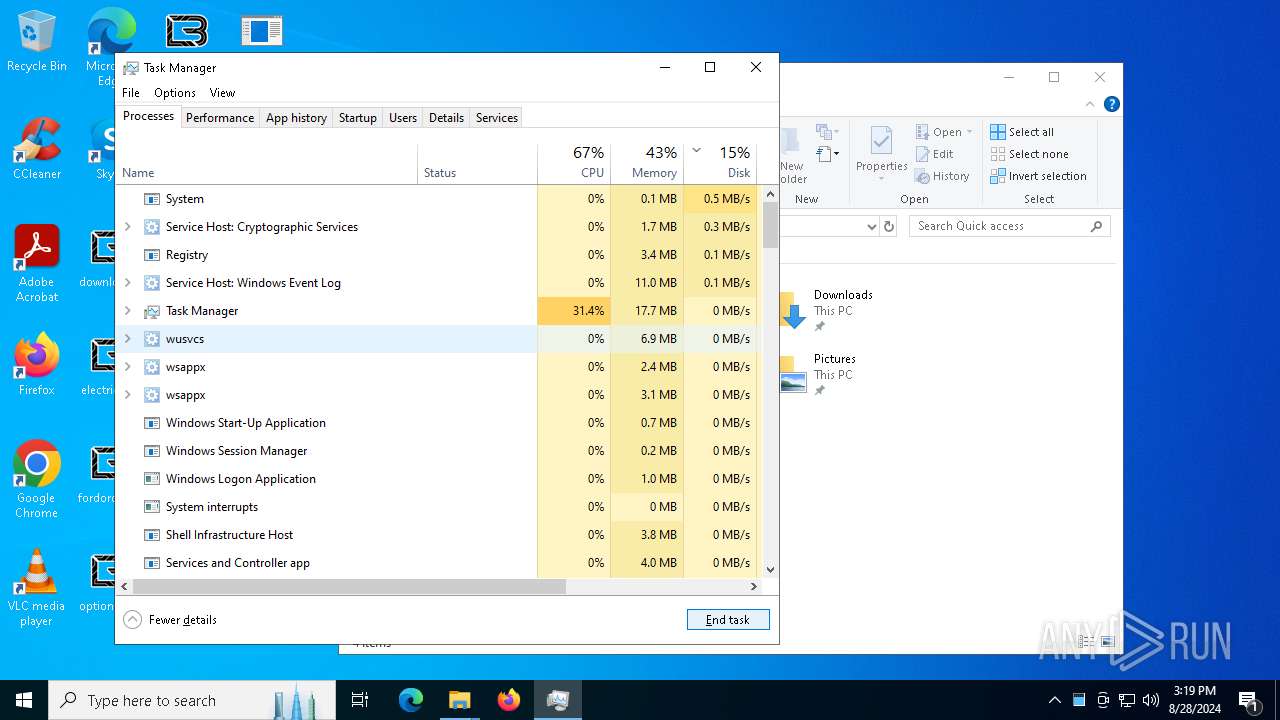
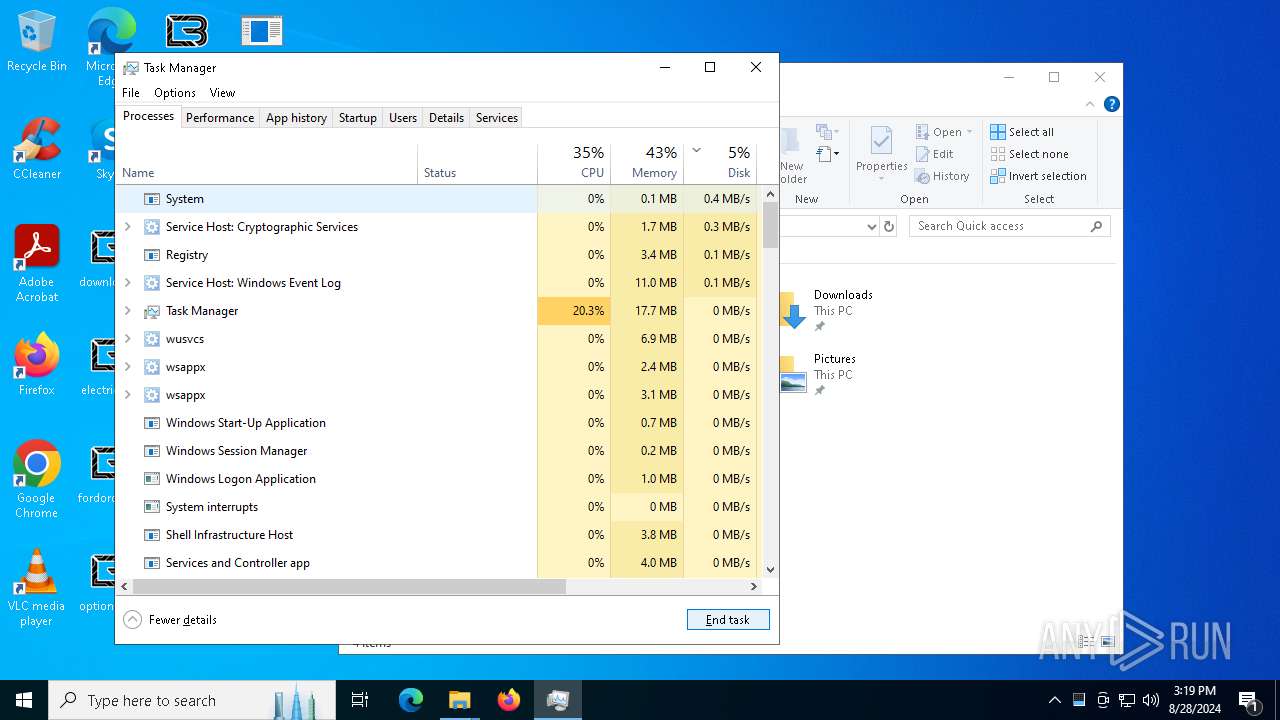
Manual execution by a user
- notepad.exe (PID: 6208)
- Taskmgr.exe (PID: 1084)
- notepad.exe (PID: 6944)
- Taskmgr.exe (PID: 4448)
Create files in a temporary directory
- ggc.exe (PID: 5276)
Dropped object may contain TOR URL's
- ggc.exe (PID: 5276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:28 12:39:45+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.42 |
| CodeSize: | 864768 |
| InitializedDataSize: | 1424896 |
| UninitializedDataSize: | 8704 |
| EntryPoint: | 0x13f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 4.1.1.851 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | McAfee WebAdvisor |
| ProductName: | McAfee WebAdvisor |
| FileVersion: | 4.1.1.851 |
| ProductVersion: | 4.1.1.851 |
| LegalCopyRight: | Copyright © 2023 McAfee, LLC |
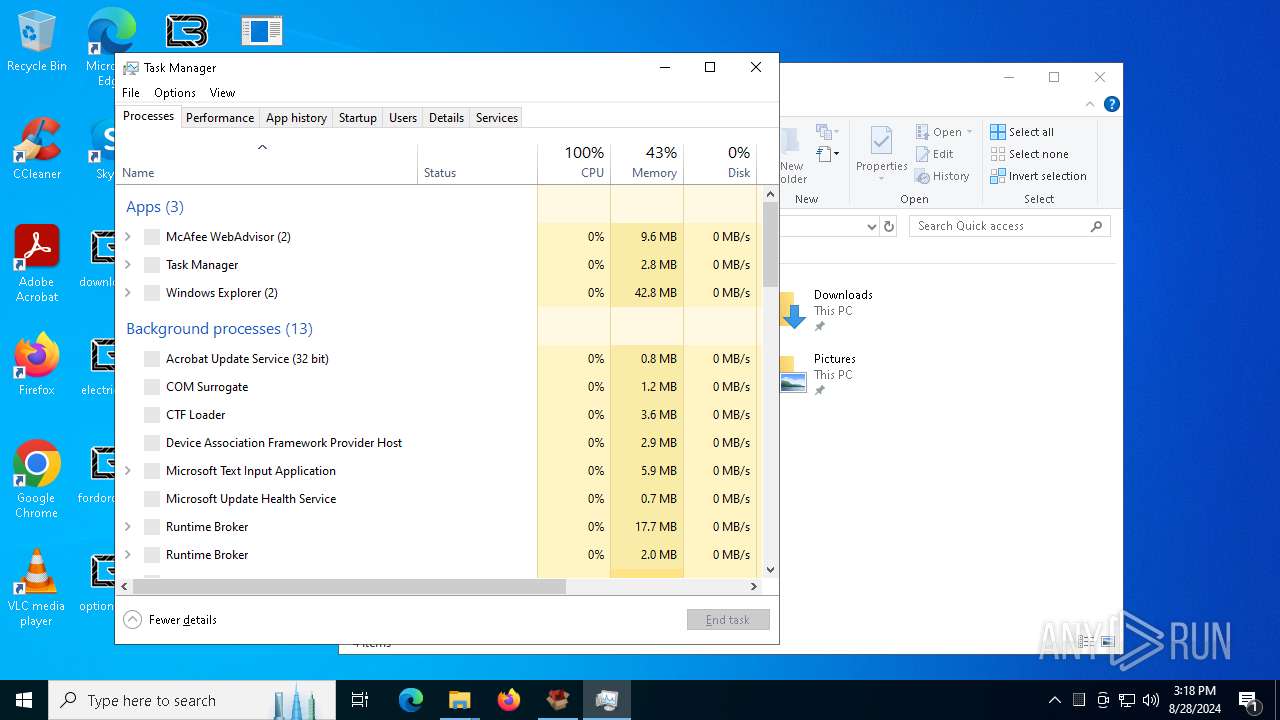
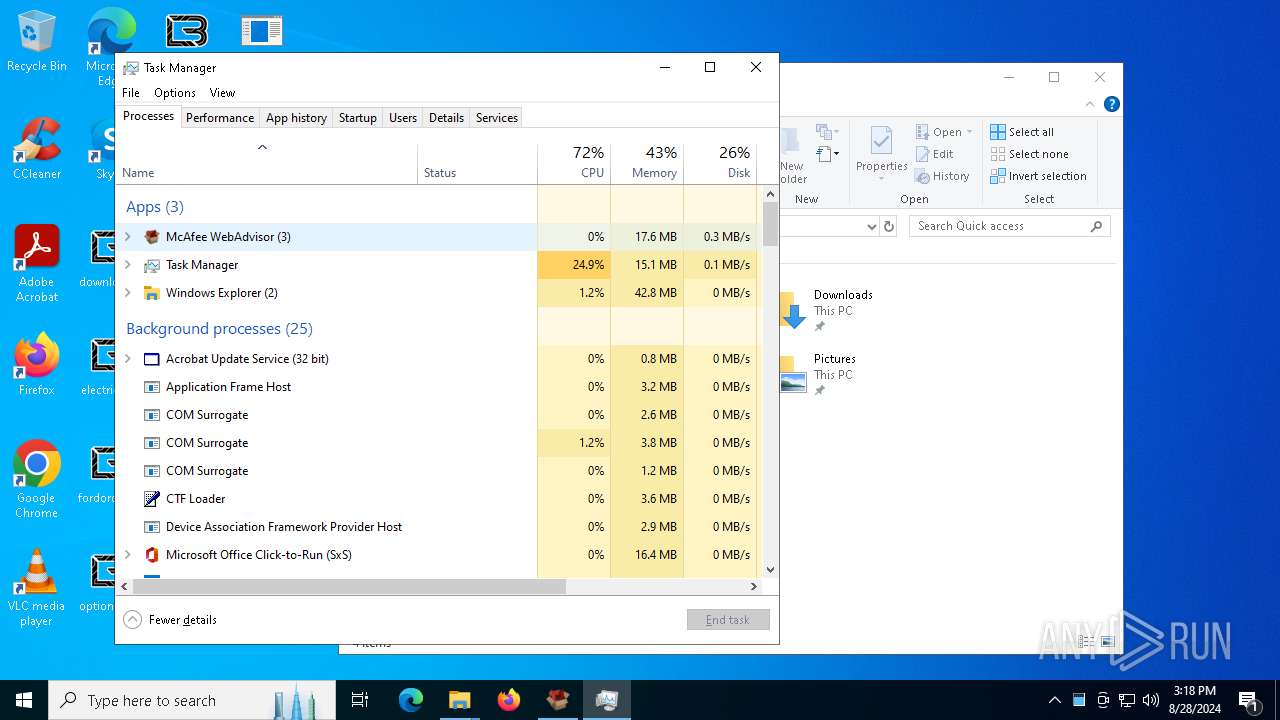
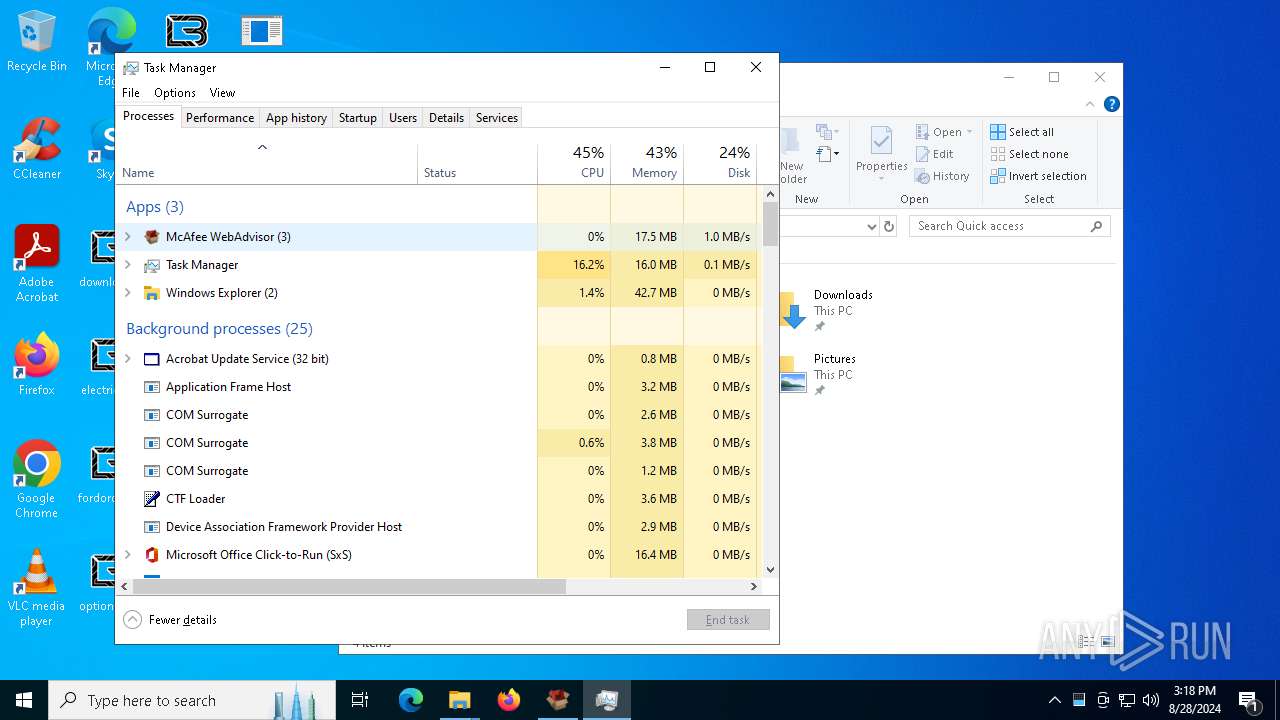
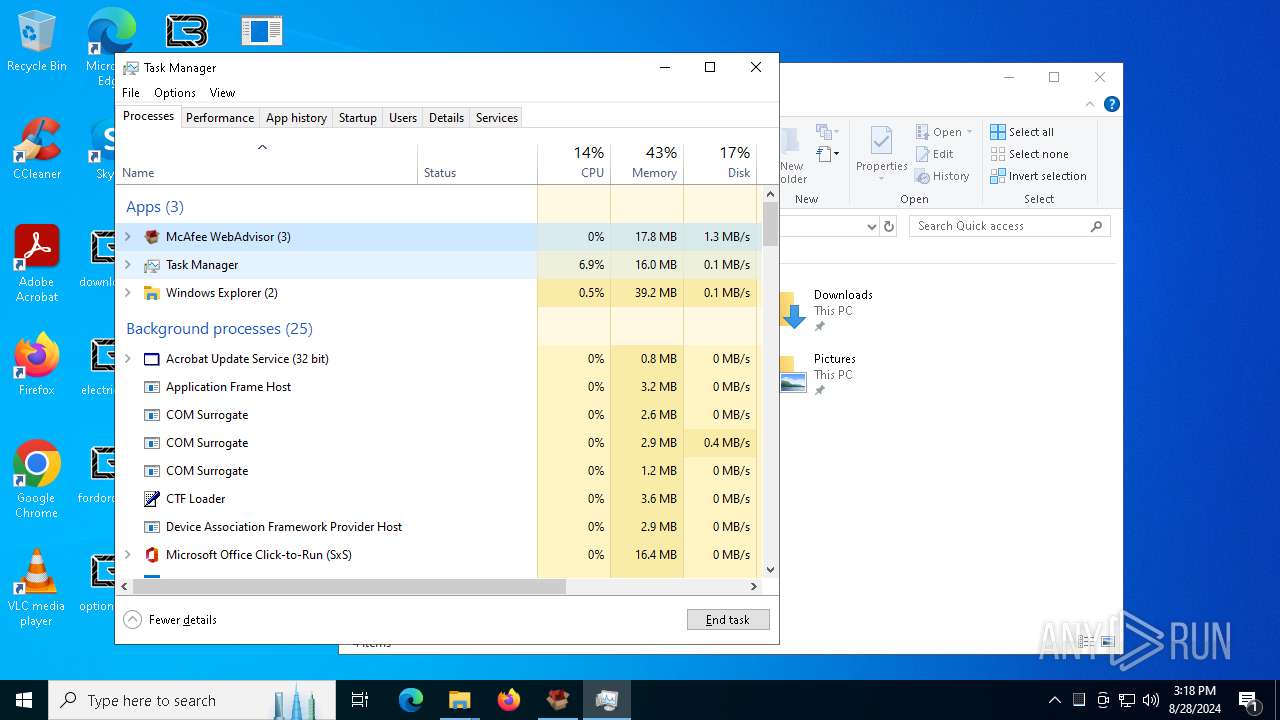
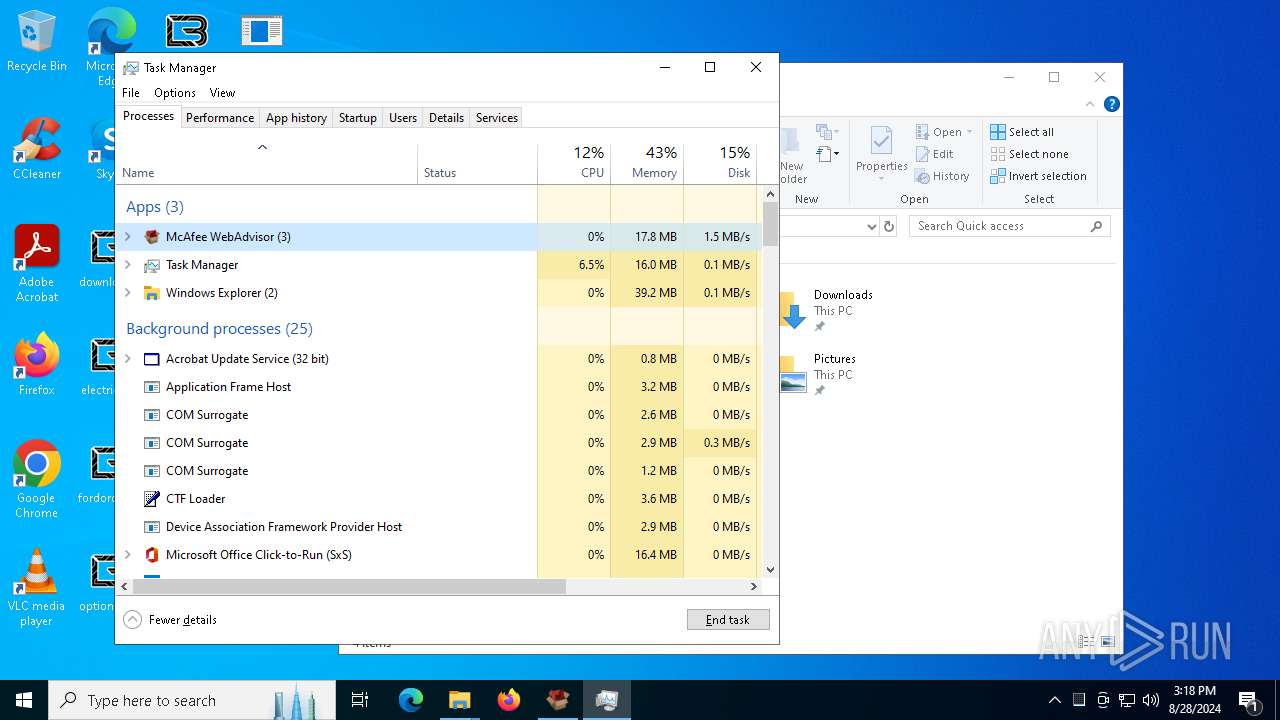
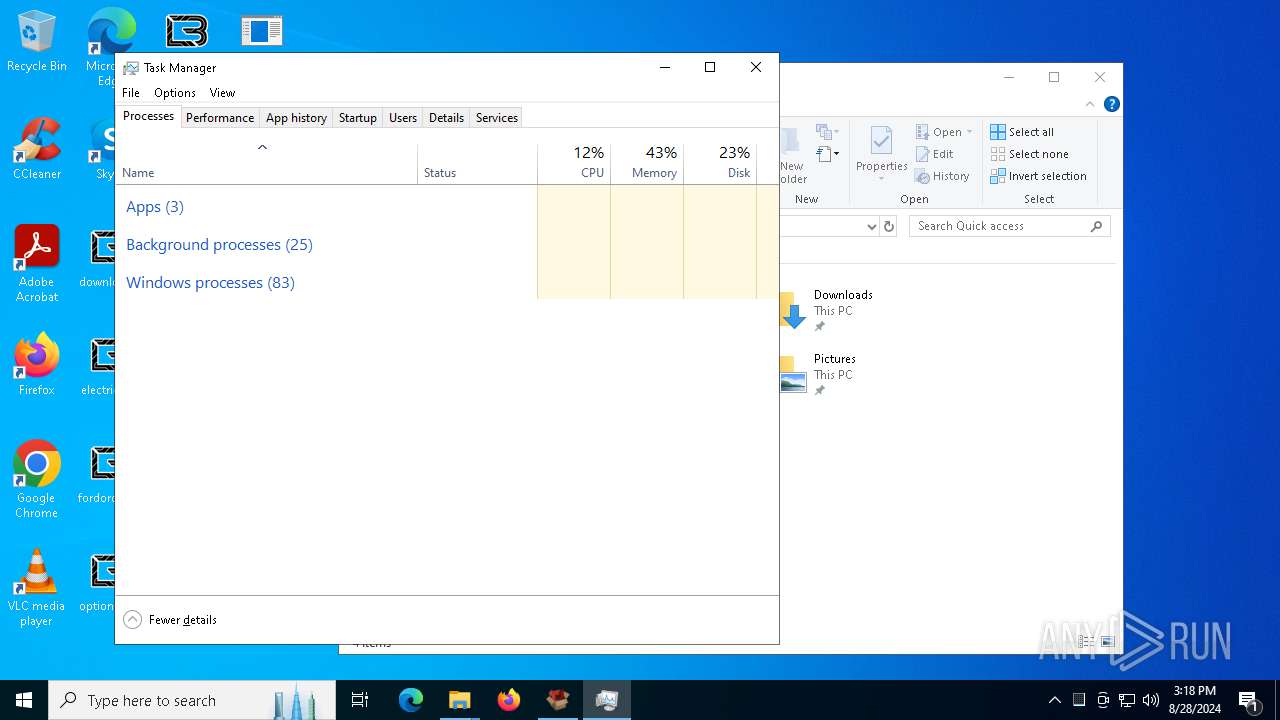
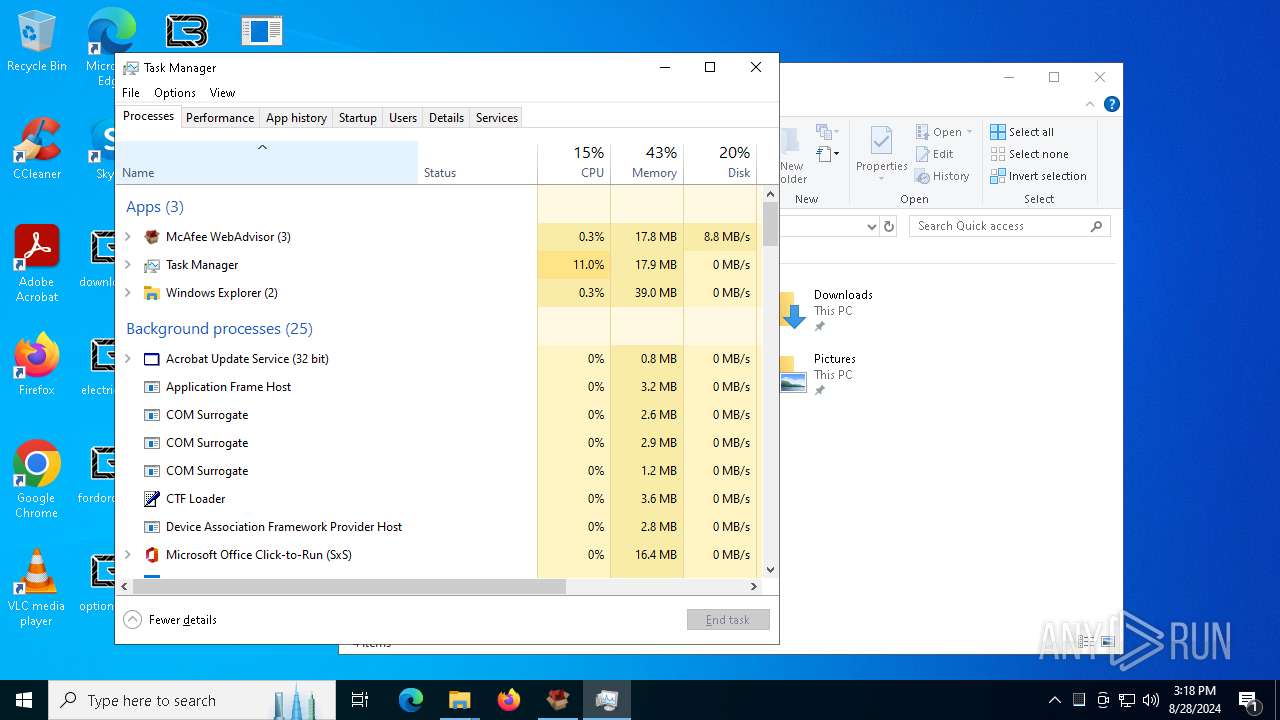
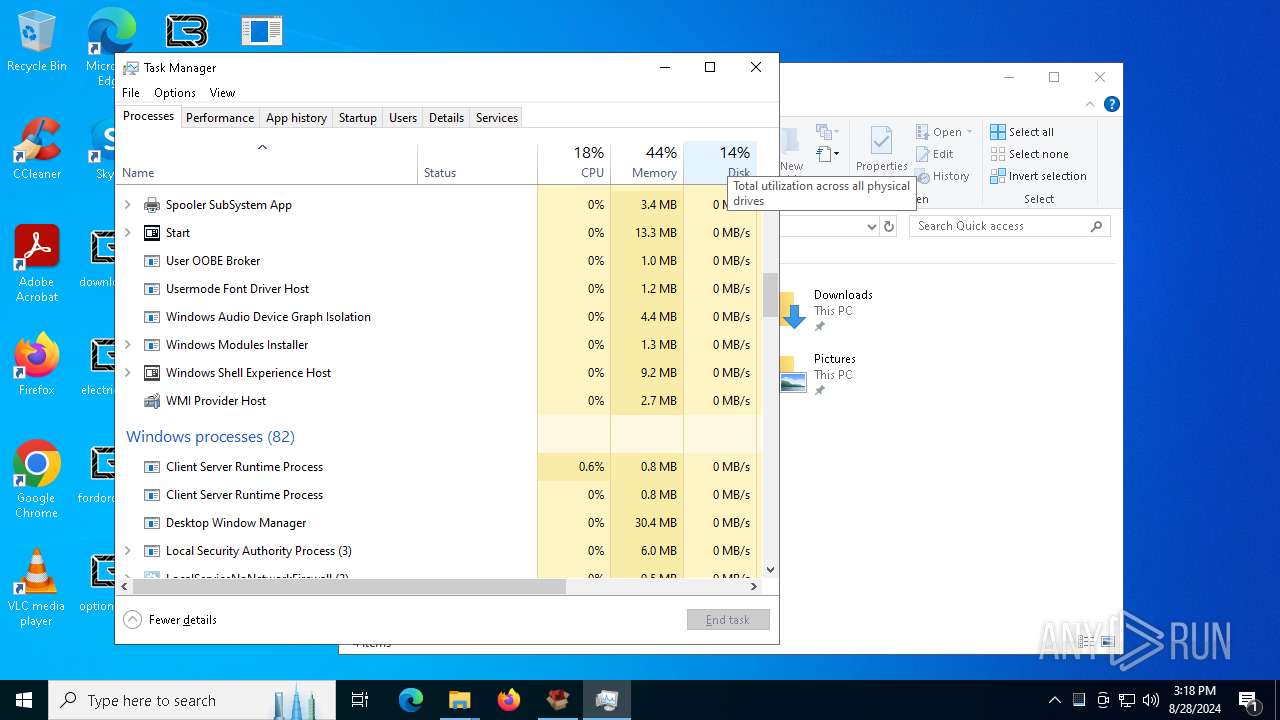
Total processes
139
Monitored processes
8
Malicious processes
2
Suspicious processes
0
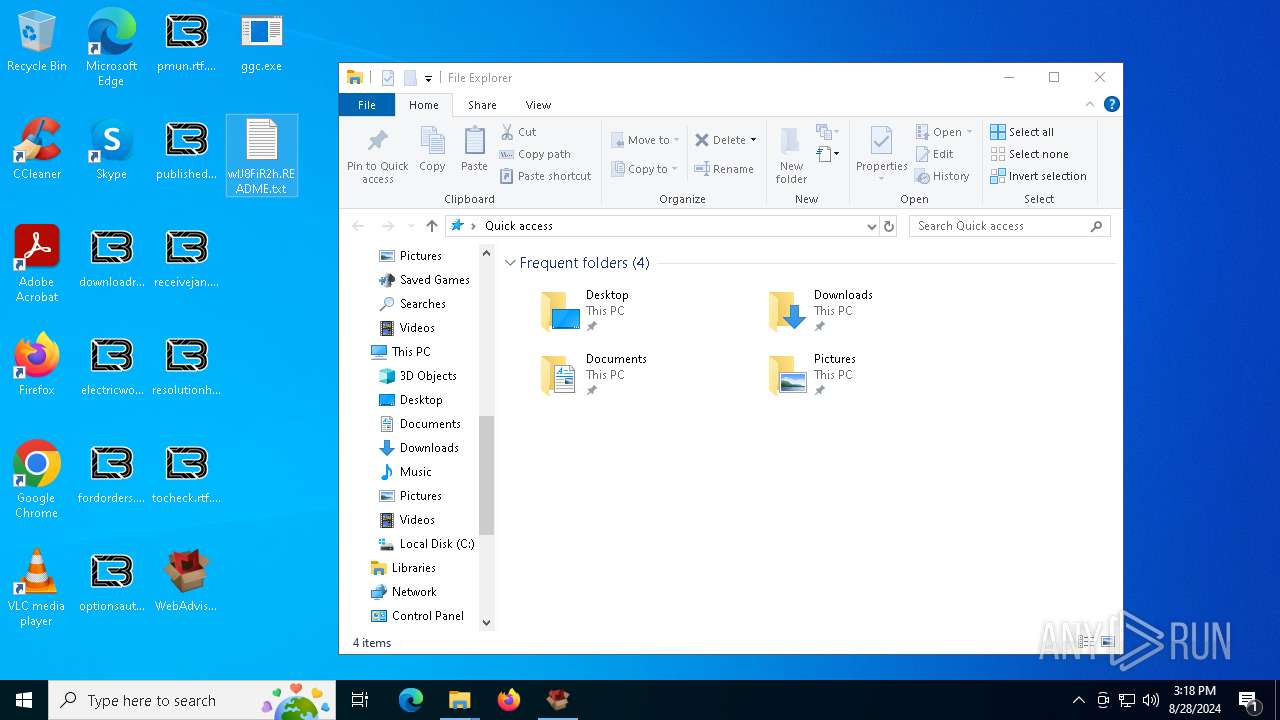
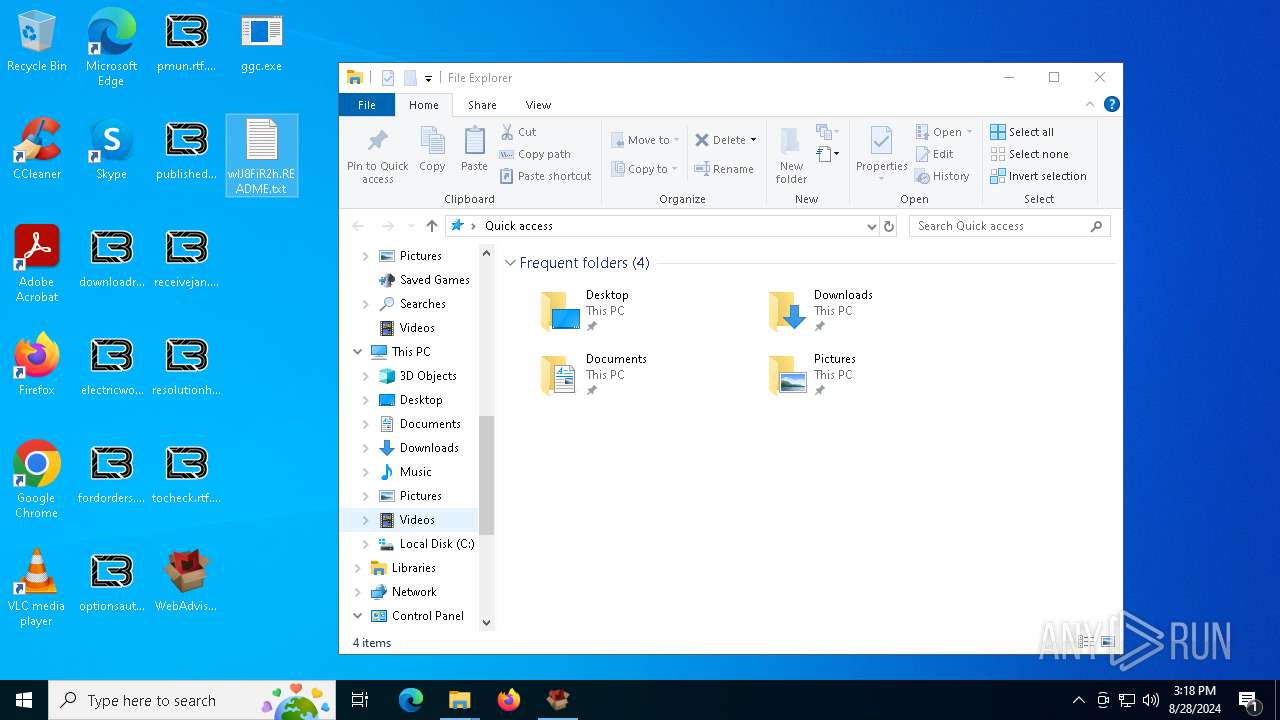
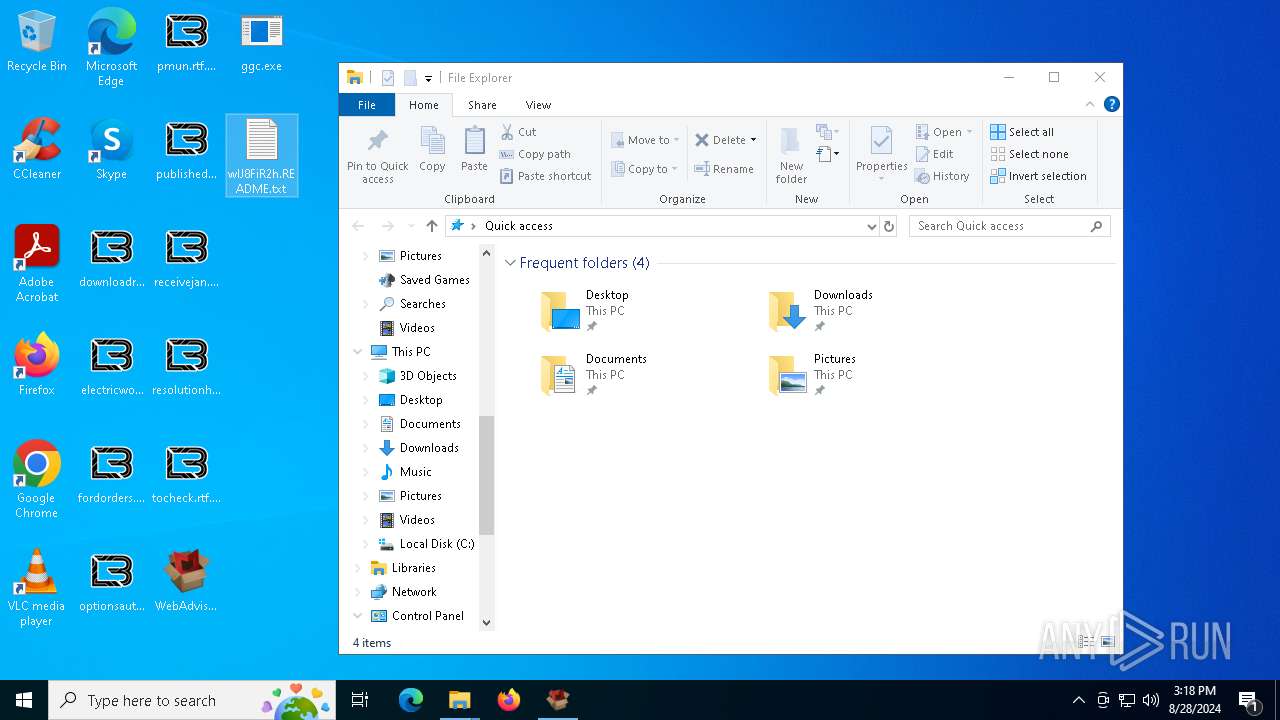
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2480 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\Desktop\WebAdvisorInstall.exe" | C:\Users\admin\Desktop\WebAdvisorInstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WebAdvisorInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
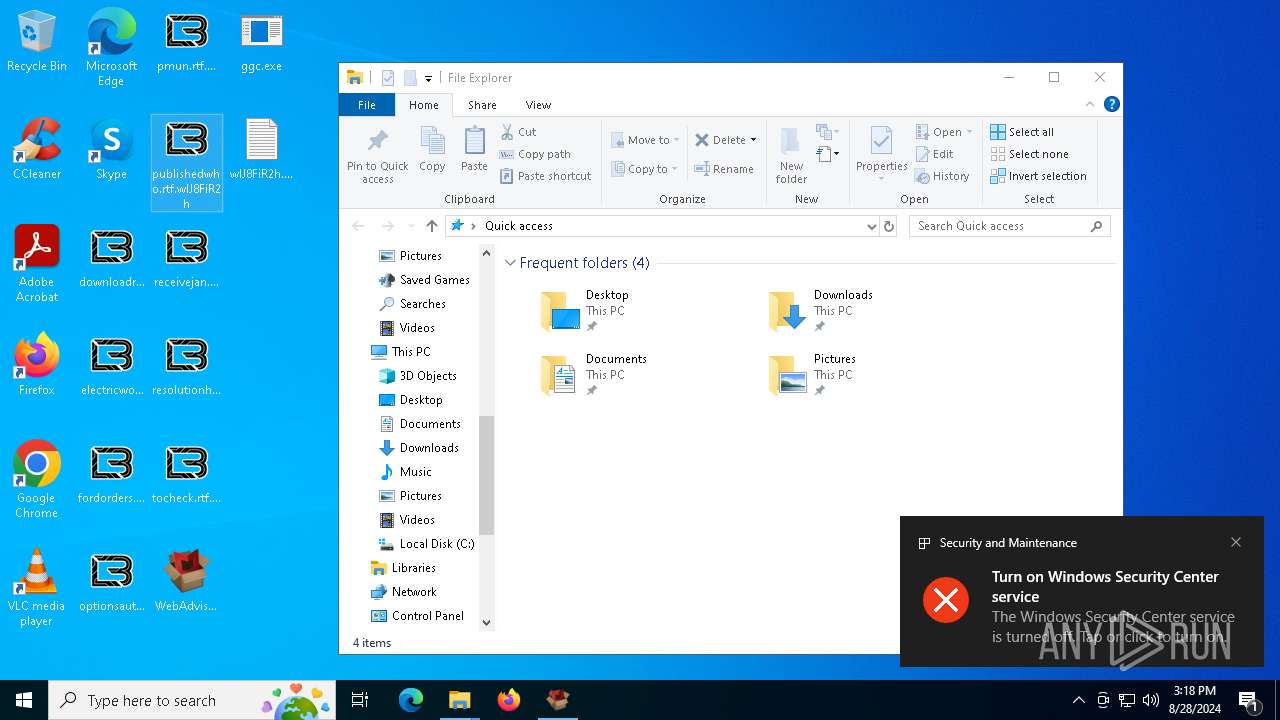
| 5276 | "C:\Users\admin\Desktop\ggc.exe" | C:\Users\admin\Desktop\ggc.exe | WebAdvisorInstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
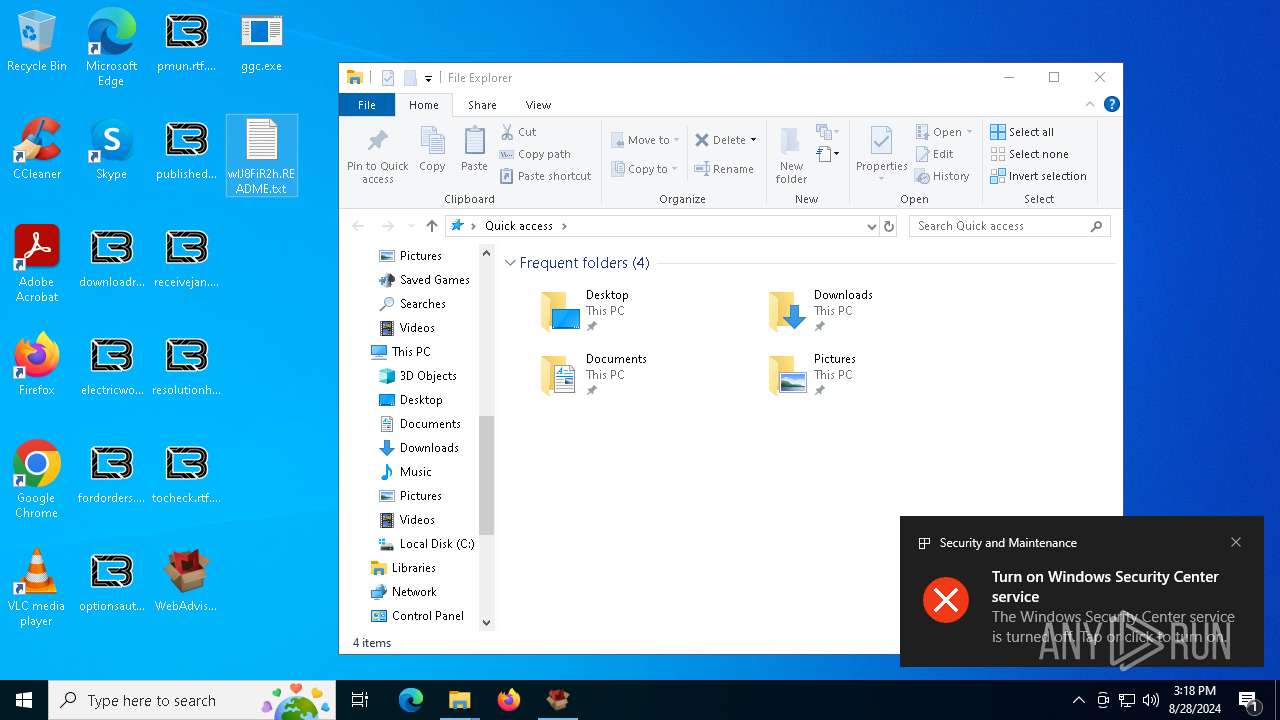
| 6208 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\wlJ8FiR2h.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\wlJ8FiR2h.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 111
Read events
7 095
Write events
15
Delete events
1
Modification events
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3812) WebAdvisorInstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5276) ggc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 12 | |||
| (PID) Process: | (2480) ShellExperienceHost.exe | Key: | \REGISTRY\A\{e596ee11-d288-6014-3580-04f152265310}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000A8A8B67F5DF9DA01 | |||
| (PID) Process: | (4448) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
Executable files
5
Suspicious files
738
Text files
769
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | WebAdvisorInstall.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\desktop.ini | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
| 5276 | ggc.exe | C:\ProgramData\wlJ8FiR2h.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
| 3812 | WebAdvisorInstall.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\server[1].scr | executable | |
MD5:7E503C206E57F0295DA017914A957D04 | SHA256:274844568A6A9CE334D71EFEAC21F528D7B54B2CD4377C978CC1270C6AD986C4 | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\EEEEEEEEEEE | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\DDDDDDDDDDD | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\CCCCCCCCCCC | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
| 3812 | WebAdvisorInstall.exe | C:\Users\admin\Desktop\ggc.exe | executable | |
MD5:7E503C206E57F0295DA017914A957D04 | SHA256:274844568A6A9CE334D71EFEAC21F528D7B54B2CD4377C978CC1270C6AD986C4 | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\AAAAAAAAAAA | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
| 5276 | ggc.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:5ED53D3EF3BF9D4CF326AA3BBDC1098A | SHA256:DFB3705F1BD9E237CDA2753297DA3F256F8D3BDF964EEB2C8F49A420D830C25C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
36
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4316 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6056 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3812 | WebAdvisorInstall.exe | 198.185.159.145:443 | www.kenesrakishevinfo.com | SQUARESPACE | US | malicious |
3812 | WebAdvisorInstall.exe | 76.76.21.241:443 | master-repogen.vercel.app | AMAZON-02 | US | malicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1944 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.kenesrakishevinfo.com |
| malicious |
master-repogen.vercel.app |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |