| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/3e12e2c2-98a3-4c59-aada-346835df56c9 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 16:49:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | D58AE978AD0562995113EE96B0E7A02D |
| SHA1: | 1E682DA700B26A528E64FDD27A8327F3E0D0E2A0 |
| SHA256: | 1654A114726B421486B31BD3F23F7806046A58247DB275B78CA66B10E7D2A9B9 |
| SSDEEP: | 384:A0Q/nXIhg88WdufWZSC6PQ+5z9bsdDWXoIxMRyt:wIeWdzZLX+5RbsdDWXo7Ryt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 868)
Executed via COM
- OUTLOOK.EXE (PID: 3068)
Reads the computer name
- OUTLOOK.EXE (PID: 868)
Searches for installed software
- OUTLOOK.EXE (PID: 868)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3440)
Modifies files in Chrome extension folder
- chrome.exe (PID: 968)
INFO
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 868)
- chrome.exe (PID: 1264)
- iexplore.exe (PID: 3184)
Reads the computer name
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 3440)
- chrome.exe (PID: 968)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 660)
Checks supported languages
- iexplore.exe (PID: 3440)
- chrome.exe (PID: 968)
- iexplore.exe (PID: 3184)
- OUTLOOK.EXE (PID: 3068)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 592)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 660)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3412)
Reads internet explorer settings
- iexplore.exe (PID: 3440)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3068)
- OUTLOOK.EXE (PID: 868)
Changes internet zones settings
- iexplore.exe (PID: 3184)
Reads the date of Windows installation
- iexplore.exe (PID: 3184)
Application launched itself
- iexplore.exe (PID: 3184)
- chrome.exe (PID: 968)
Manual execution by user
- chrome.exe (PID: 968)
Checks Windows Trust Settings
- OUTLOOK.EXE (PID: 868)
- iexplore.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
60
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phish_alert_sp2_2.0.0.0.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1104 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6624176018639066621,17603949377392061395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 985
Read events
23 229
Write events
734
Delete events
22
Modification events
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (868) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
111
Text files
83
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR97AC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3068 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRADA5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_BA1F5B71312C8B4582513AB6206E1759.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 868 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_36D66A36E97BC74A8838C12526B9E650.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
44
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
868 | OUTLOOK.EXE | GET | 200 | 13.225.84.49:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
868 | OUTLOOK.EXE | GET | 200 | 13.225.84.142:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEApQTAHYfewVihAe3nxBvVw%3D | US | der | 471 b | whitelisted |
868 | OUTLOOK.EXE | GET | 200 | 13.225.84.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
868 | OUTLOOK.EXE | GET | 200 | 13.225.84.13:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
1264 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
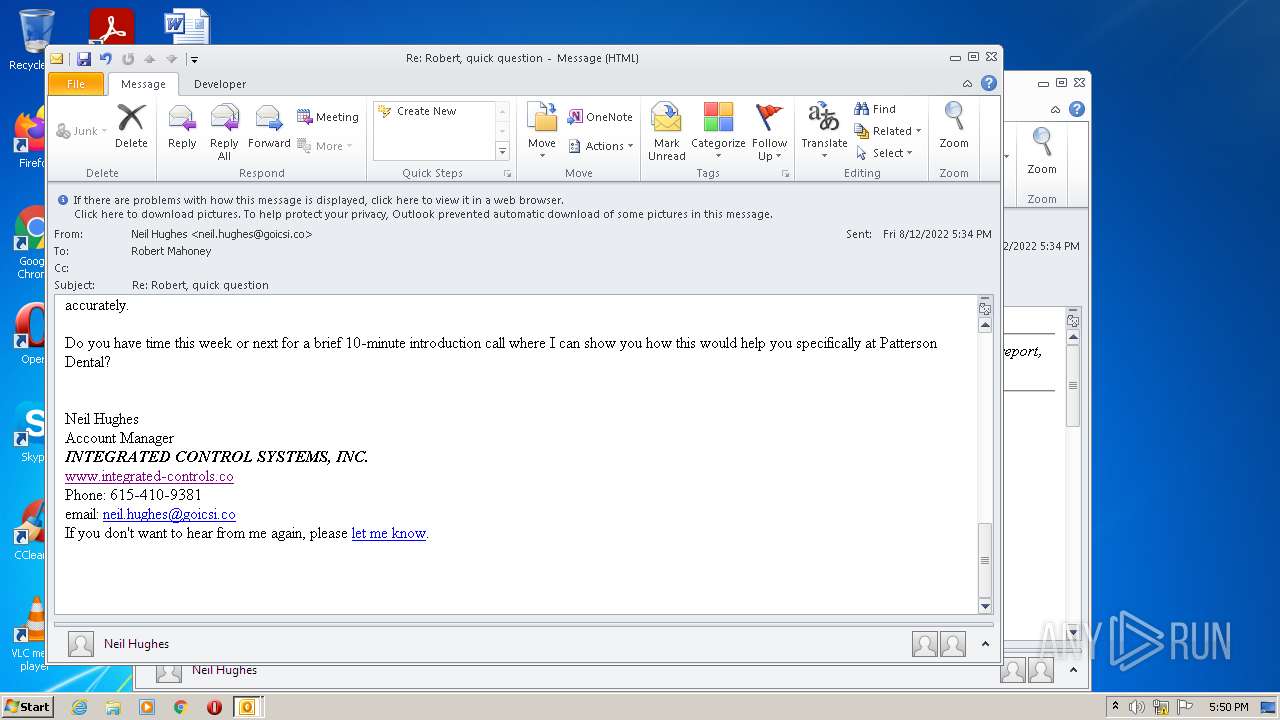
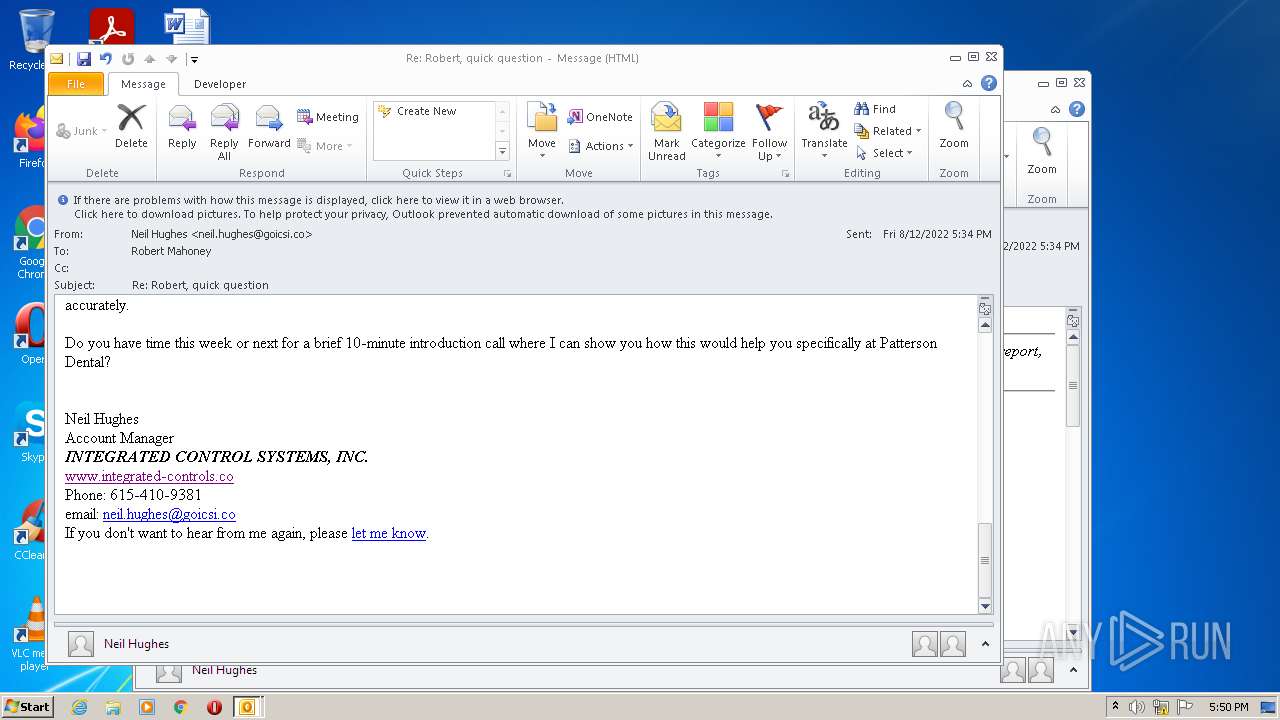
868 | OUTLOOK.EXE | GET | 200 | 167.89.118.52:80 | http://url9719.goicsi.co/wf/open?upn=onXnJGlRddgwjq9DW5HkbcE-2B5QP756FR-2FMFFVlyzwBlljnGDQVGm2JogKmOtF4vo103Gx3TcfjUuxjmFKyoBqPUUUqxDu7eSxVDQ1wSnVCg8fjYzfEDXv182tHhRydBdixaYQyux2TwVppqB8TGb6Z10dUXZD4p2ngMcUkkUUZHqyVXfYjK0UZ-2F-2Ft-2BierLlRdpdikVZtpueWZEJboMjRZDdxzsBX-2Bna-2BtKy7nr3NkrO8JSp1f9t6PXBstWs1kSvSmtzDSUbug4-2BYm1nImQyrx475IEfrSCxp9x-2BIJr4Xs3WhQqLy51dlwI6adbLYuu0iObjSBwhsrfhQz0IEcj1wO5SpvqDA138HAi-2FXJMQ-2BkVQoGCW8tUmEDk2vZLCGytf7HgN6Mm2ZjiwEAl-2BLDqvazU9imPBC10yIqx-2BvQfxk5NvQazKydxoJ3OxzP9mCaJon | US | image | 43 b | suspicious |
868 | OUTLOOK.EXE | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bb0f14d4a9e603db | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
868 | OUTLOOK.EXE | 167.89.118.52:80 | url9719.goicsi.co | SendGrid, Inc. | US | suspicious |
868 | OUTLOOK.EXE | 52.217.195.233:443 | public-files-aws.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
868 | OUTLOOK.EXE | 13.225.84.13:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
1264 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 13.225.84.142:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
3184 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1264 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.185.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
public-files-aws.s3.amazonaws.com |
| shared |
url9719.goicsi.co |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
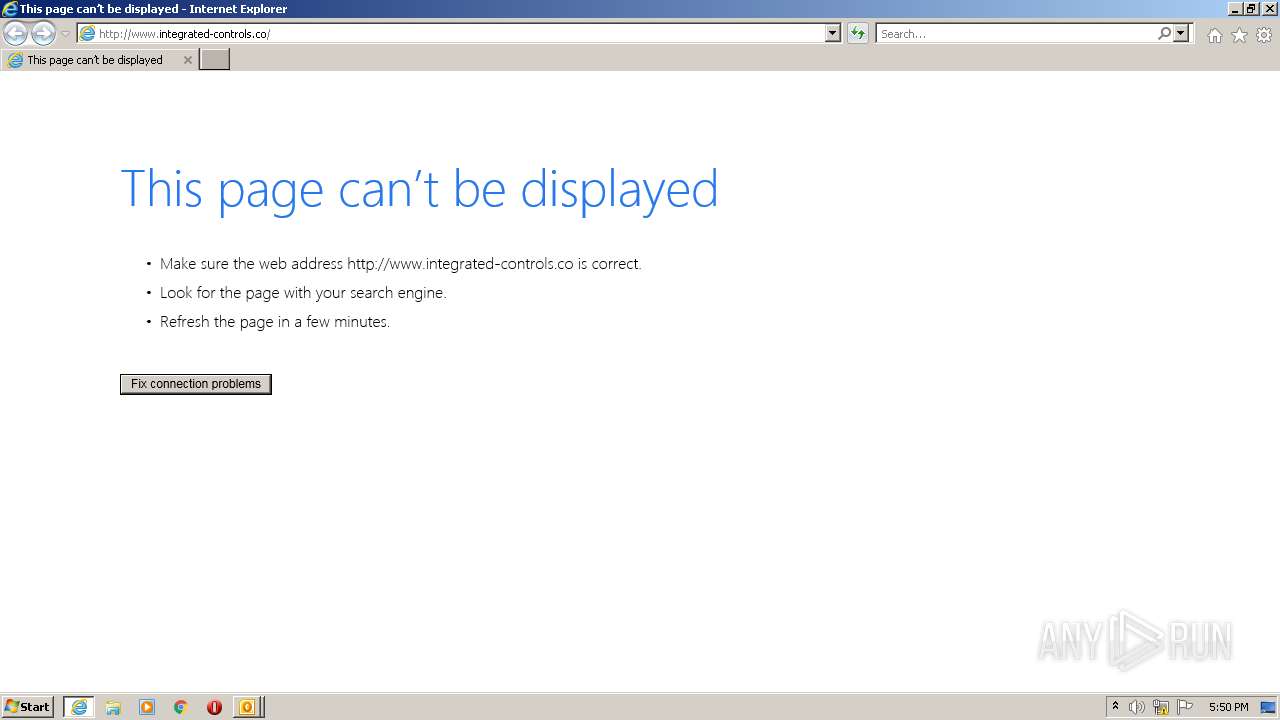
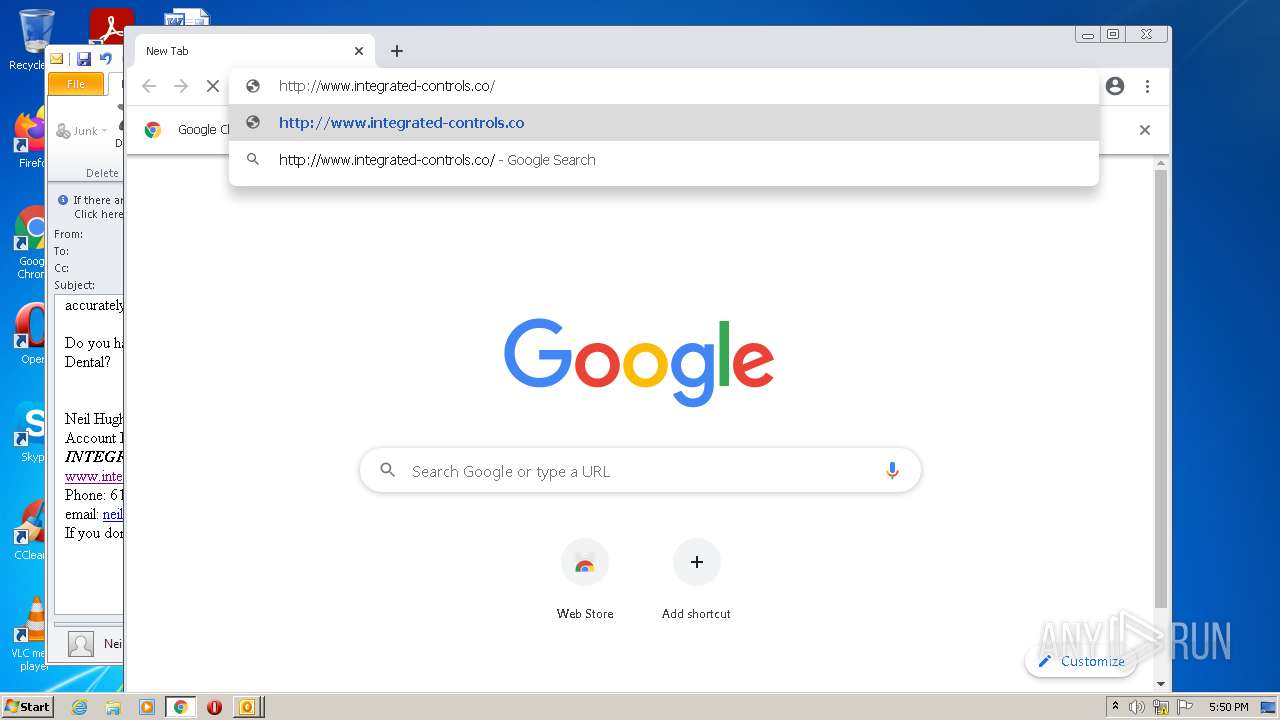
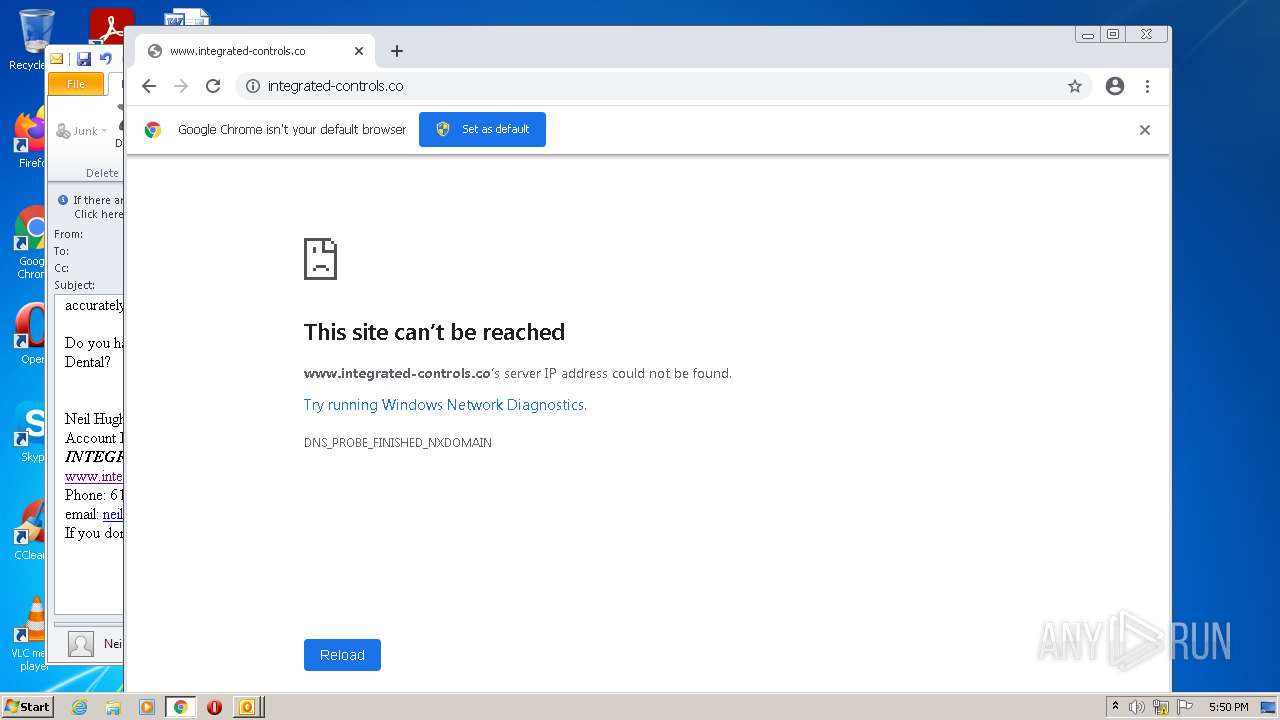
www.integrated-controls.co |
| unknown |
ocsp.sca1b.amazontrust.com |
| whitelisted |
api.bing.com |
| whitelisted |