analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | Autoruns.zip |
| Full analysis: | https://app.any.run/tasks/b58ec727-4fdf-4b80-b980-9313a23190e7 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 11:41:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E0642B2779613DCA84F02A0A664F1504 |
| SHA1: | 16DA06A9D42660DC922F5DD90443953DF538EF6C |
| SHA256: | 16531D2F11568F466E43B0F850503D1999916BA28A68B64862173A14E7490479 |
| SSDEEP: | 24576:lNrRIn3YLKg21NuNjd4H1L+0EhzdbRRpG8o9pCnJRM5a4E2r:lNrXeNuASbpxo9pCnJx4hr |
MALICIOUS
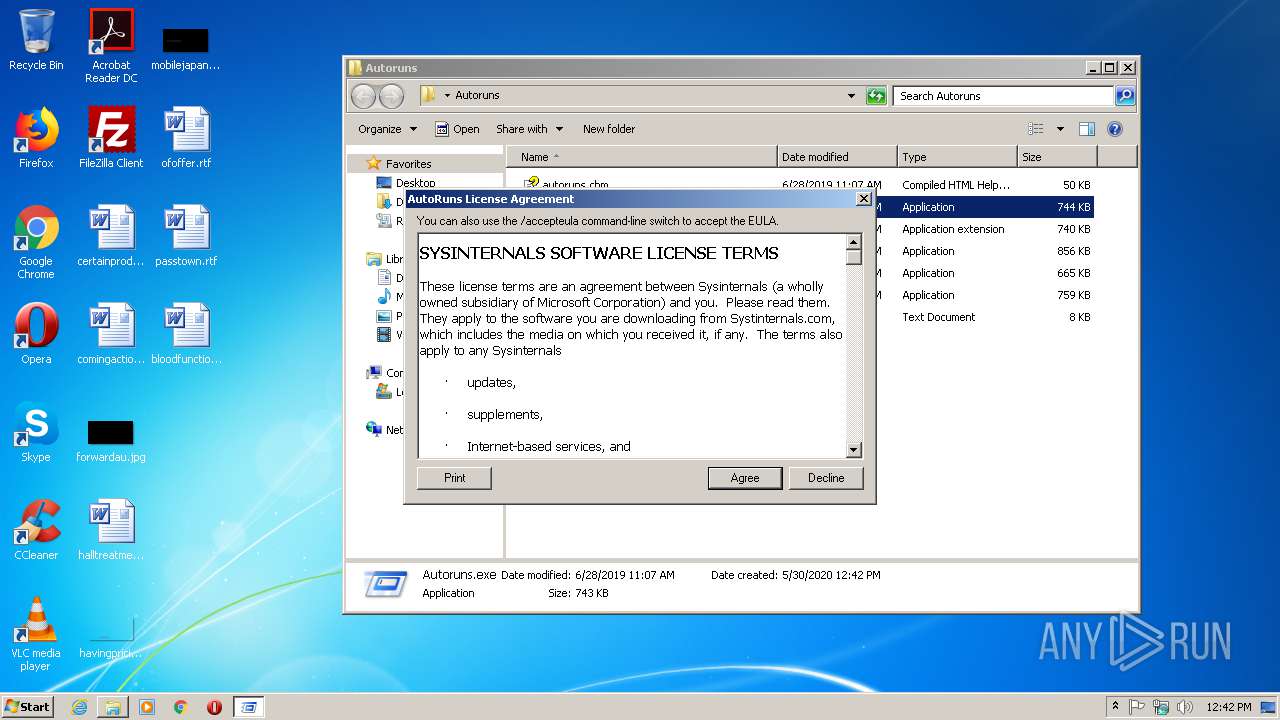
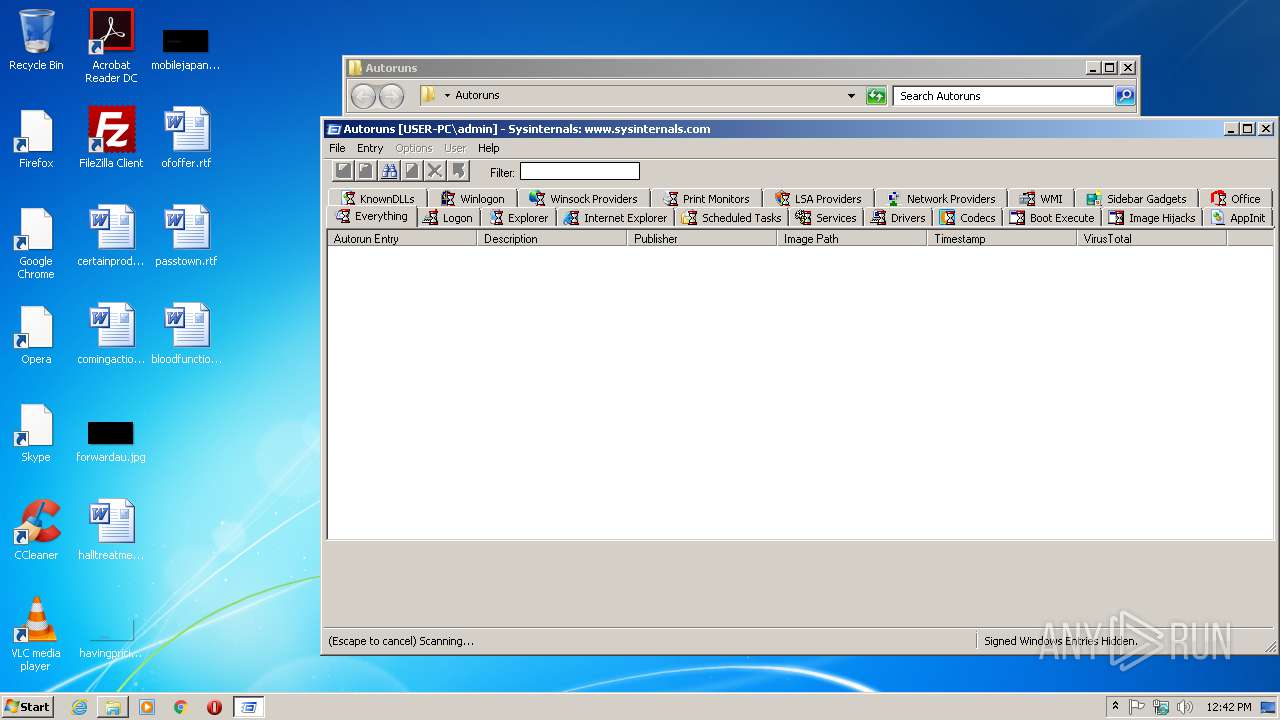
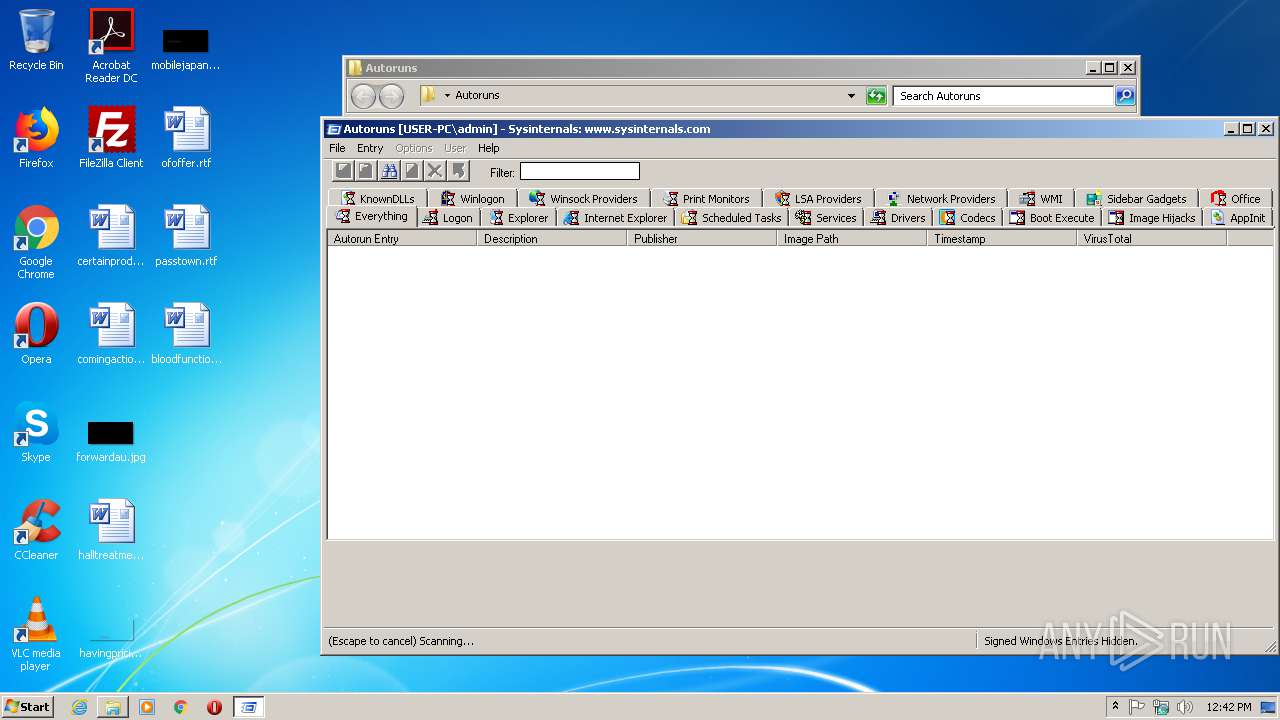
Loads the Task Scheduler COM API
- Autoruns.exe (PID: 2212)
Changes settings of System certificates
- Autoruns.exe (PID: 2212)
SUSPICIOUS
Modifies the open verb of a shell class
- Autoruns.exe (PID: 2212)
Adds / modifies Windows certificates
- Autoruns.exe (PID: 2212)
INFO
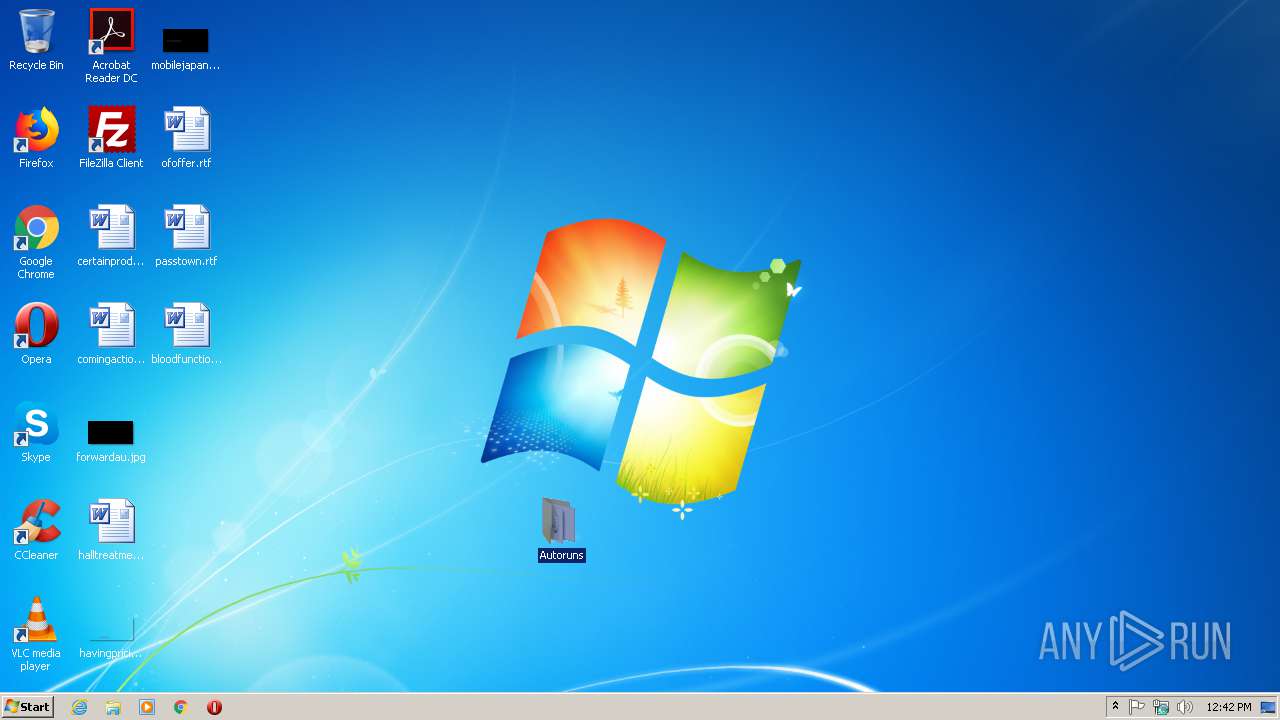
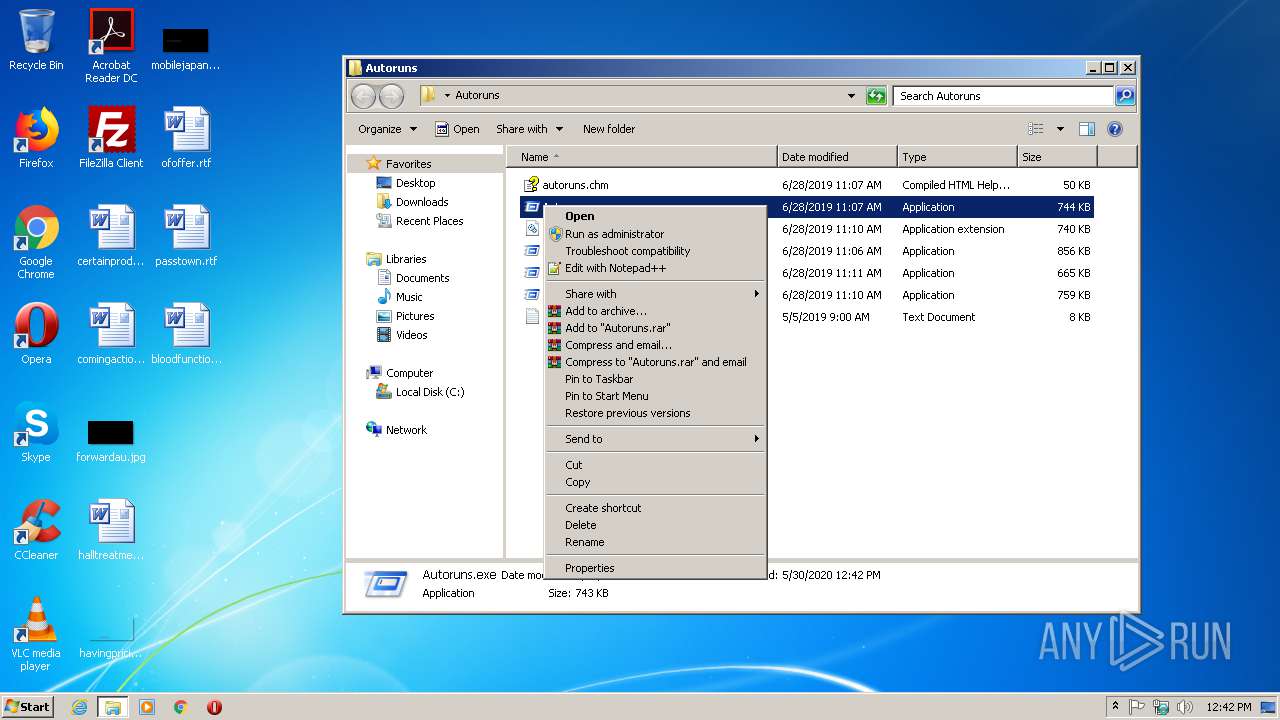
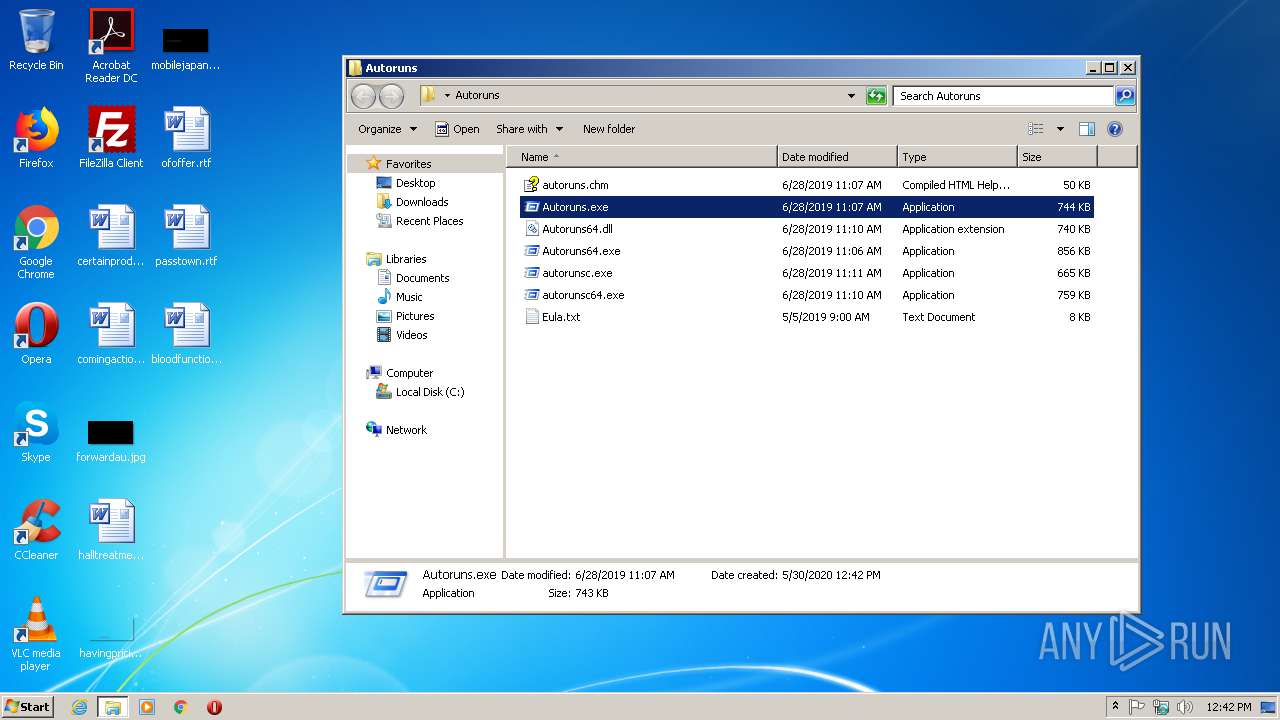
Manual execution by user
- Autoruns.exe (PID: 2212)
Reads settings of System Certificates
- Autoruns.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
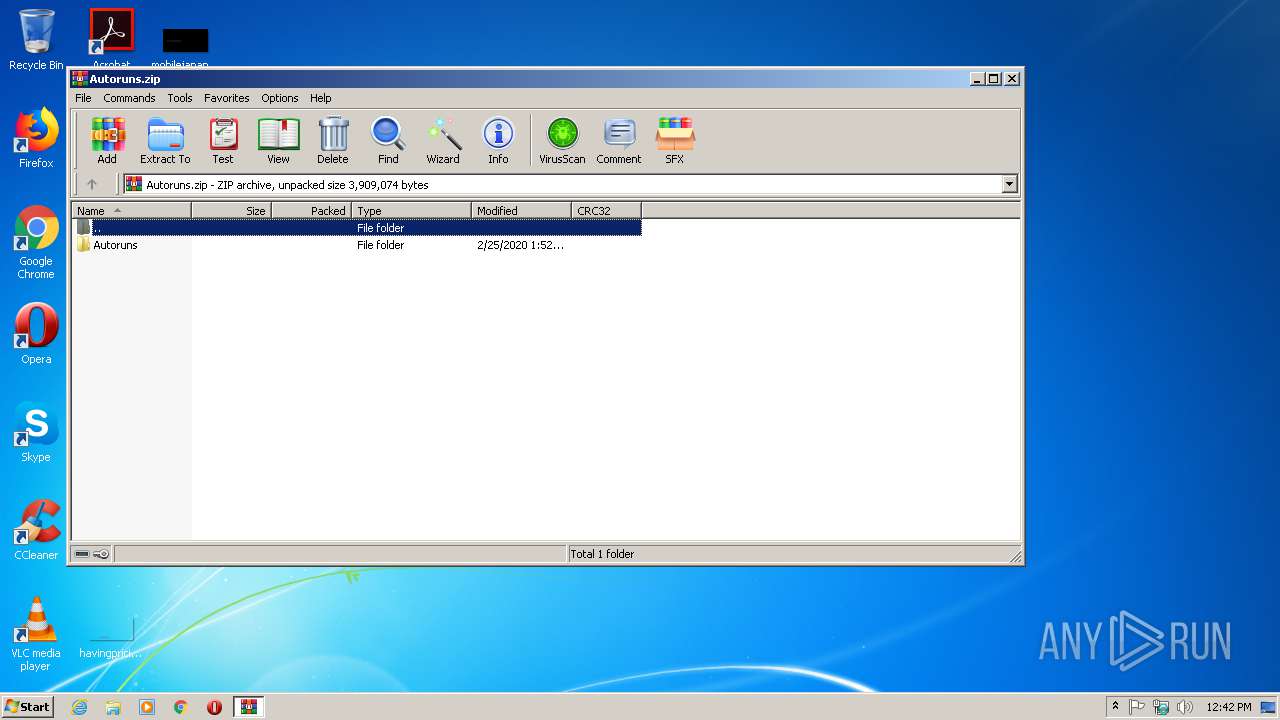
| ZipFileName: | Autoruns/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2020:02:25 16:52:28 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
42
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
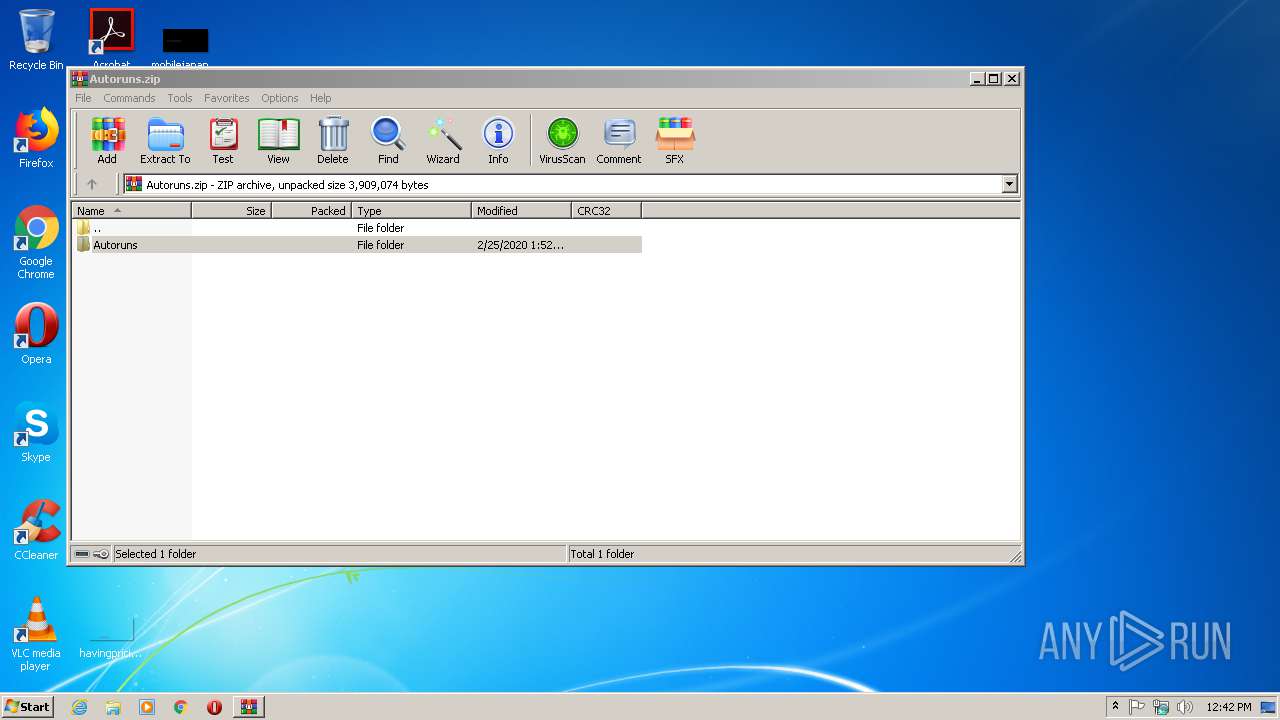
| 1944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Autoruns.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | ||||
| 2212 | "C:\Users\admin\Desktop\Autoruns\Autoruns.exe" | C:\Users\admin\Desktop\Autoruns\Autoruns.exe | explorer.exe | |
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Autostart program viewer Version: 13.96 | ||||
Total events
6 502
Read events
2 078
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
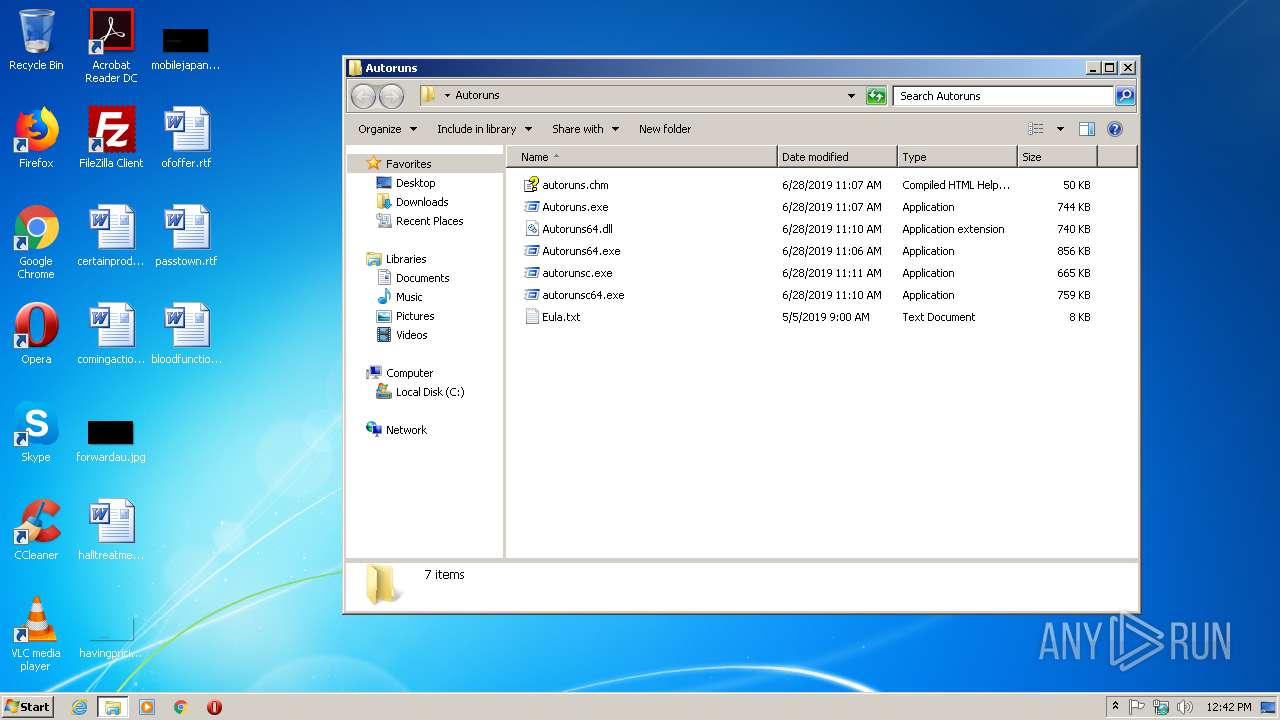
PID | Process | Filename | Type | |
|---|---|---|---|---|
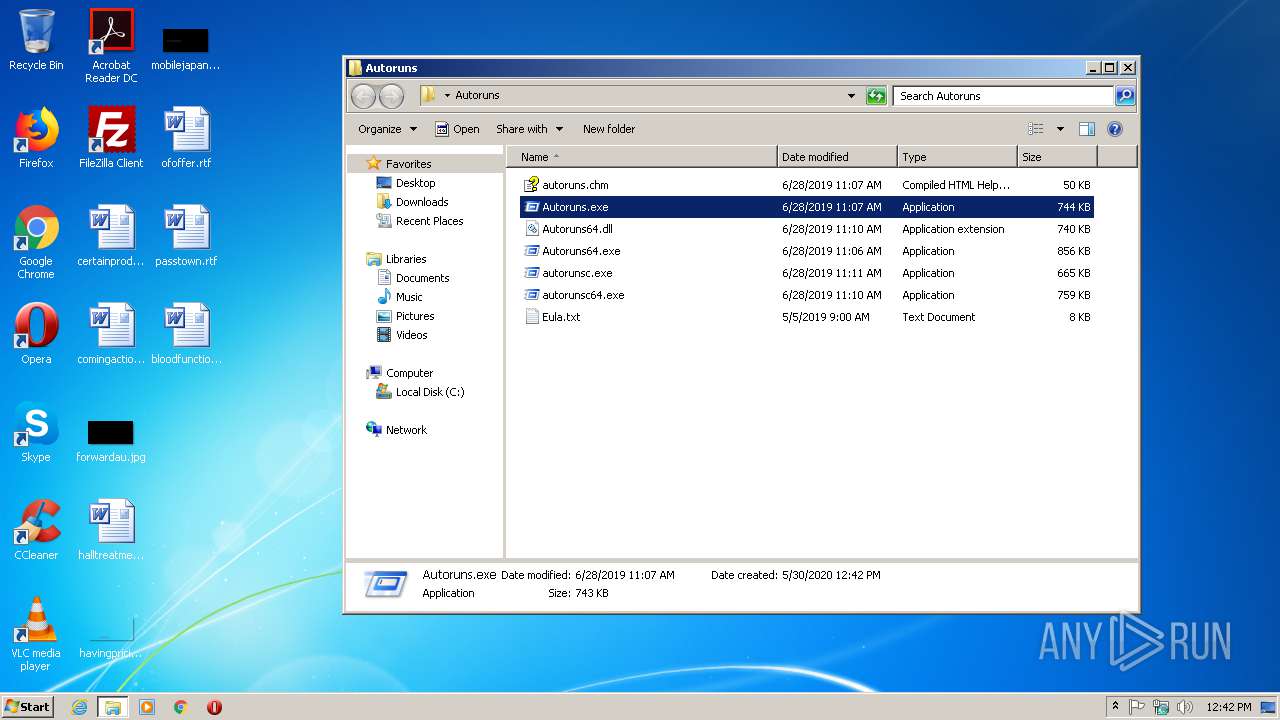
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\autoruns.chm | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\Autoruns.exe | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\Autoruns64.dll | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\Autoruns64.exe | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\autorunsc.exe | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\autorunsc64.exe | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1944.25372\Autoruns\Eula.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report