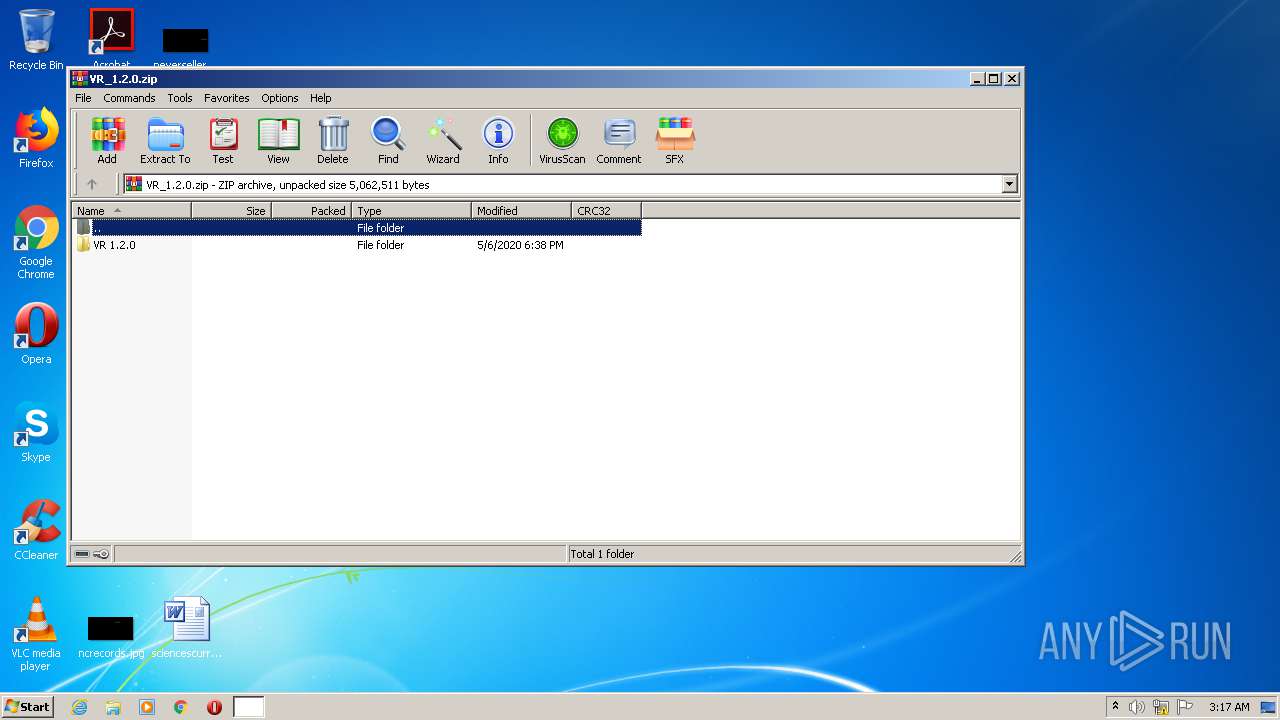
| File name: | VR_1.2.0.zip |
| Full analysis: | https://app.any.run/tasks/918a7290-9c7d-4f9b-831b-9ec03ec56810 |
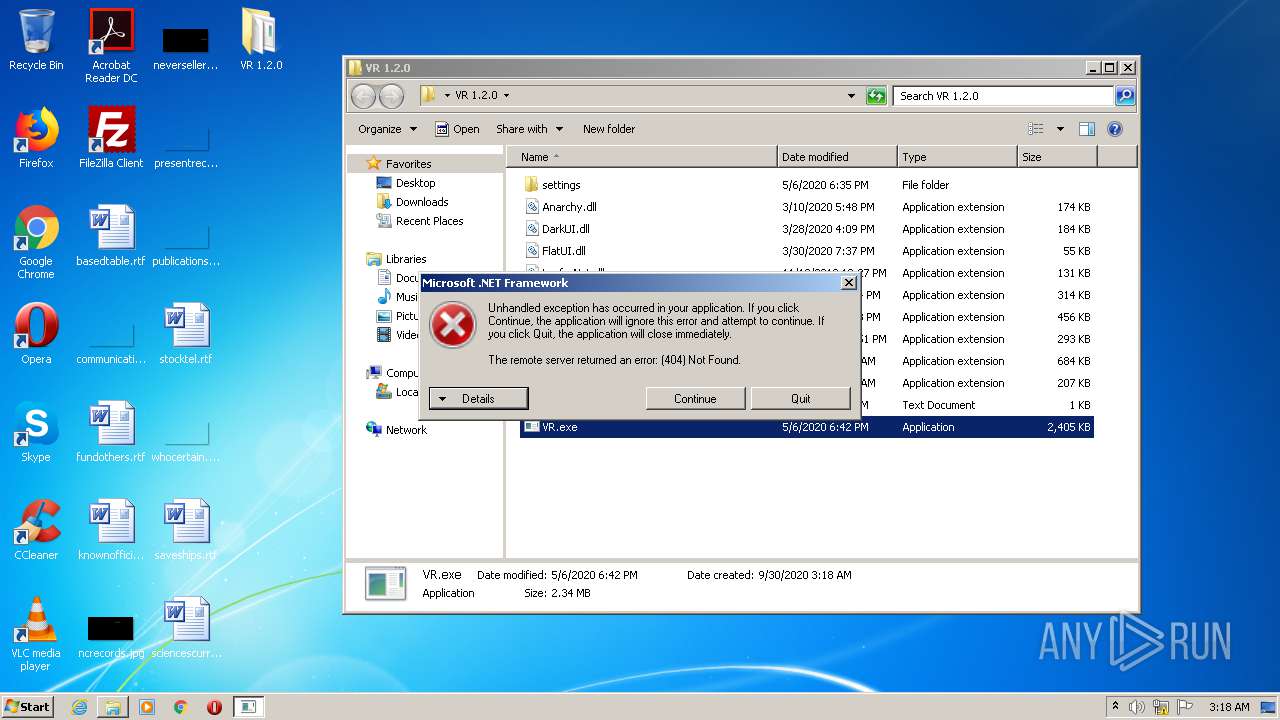
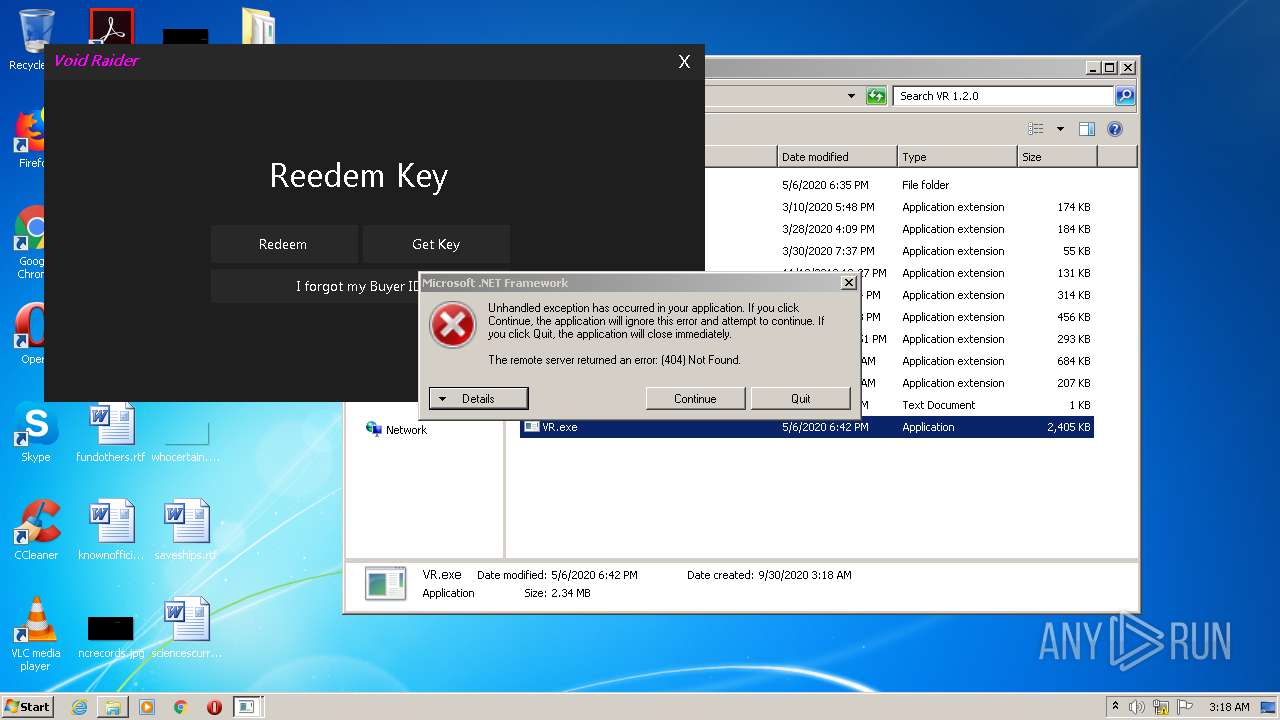
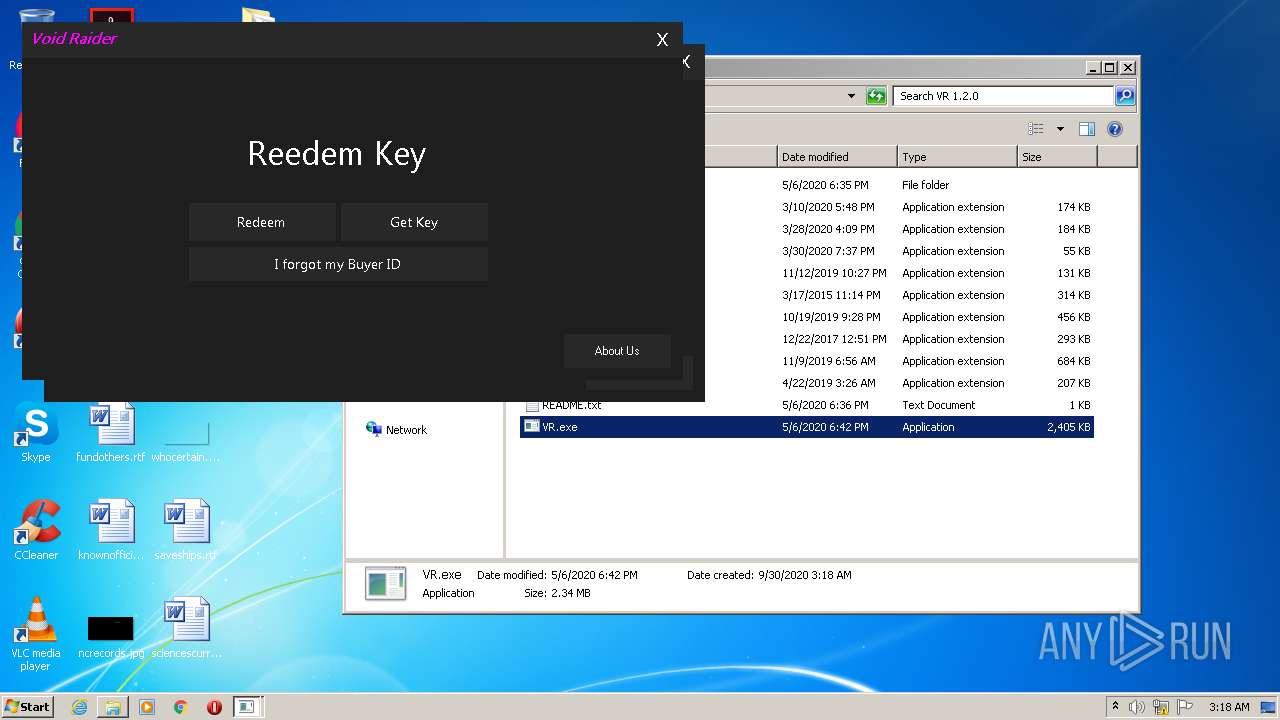
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 02:17:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 775DEEDB30E5C52C90F708D7284FB85B |
| SHA1: | 87A724A186925326CD839BF48A2F545A14A6602C |
| SHA256: | 1645F945BF477252FE1B4D89EA31CA7A2A8E7B26A08855A35FD70ACE15C8ABA8 |
| SSDEEP: | 98304:mcOtX8surz4S1BnFzl4D3WPxAkqTzRFWhmN0N:HOtXsrcS1BnP47mxAPTSx |
MALICIOUS
Application was dropped or rewritten from another process
- VR.exe (PID: 1208)
- VR.exe (PID: 2752)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3888)
- VR.exe (PID: 2752)
- VR.exe (PID: 1208)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1684)
Reads Internet Cache Settings
- rundll32.exe (PID: 3160)
Creates files in the user directory
- rundll32.exe (PID: 3160)
Uses RUNDLL32.EXE to load library
- VR.exe (PID: 1208)
- VR.exe (PID: 2752)
INFO
Manual execution by user
- VR.exe (PID: 2752)
- VR.exe (PID: 1208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:05:06 19:38:13 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | VR 1.2.0/ |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Users\admin\Desktop\VR 1.2.0\VR.exe" | C:\Users\admin\Desktop\VR 1.2.0\VR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
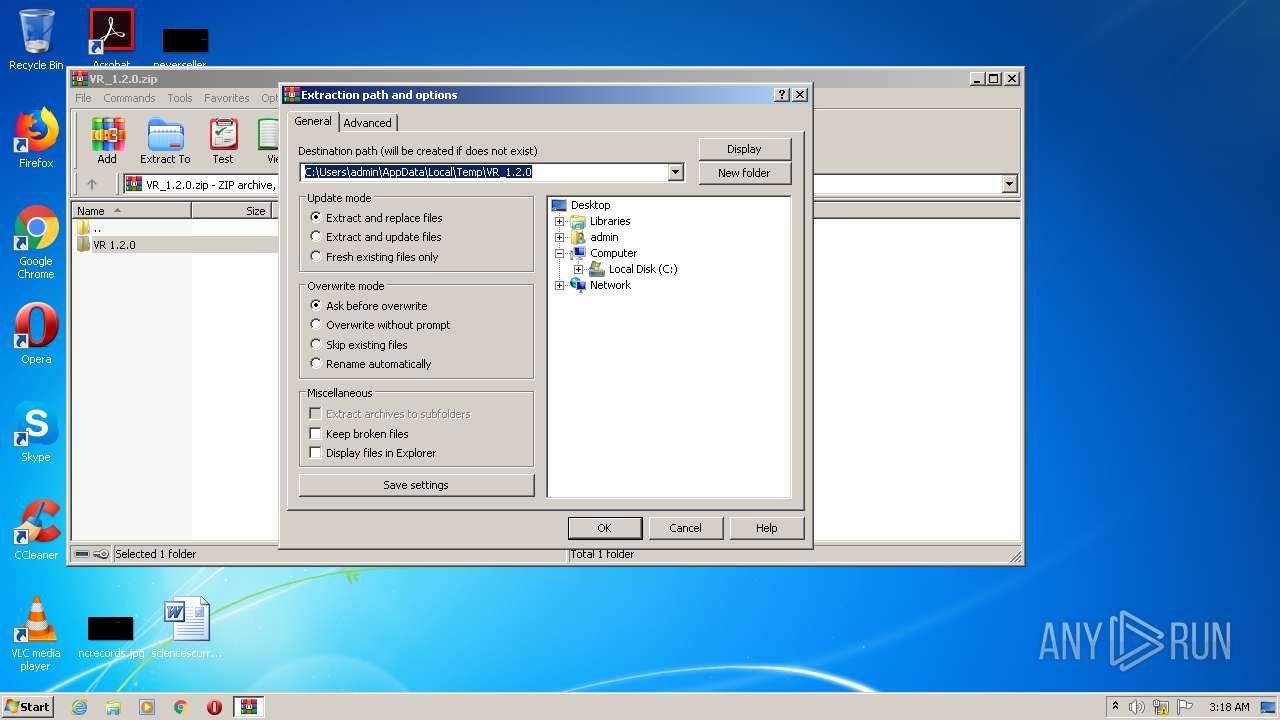
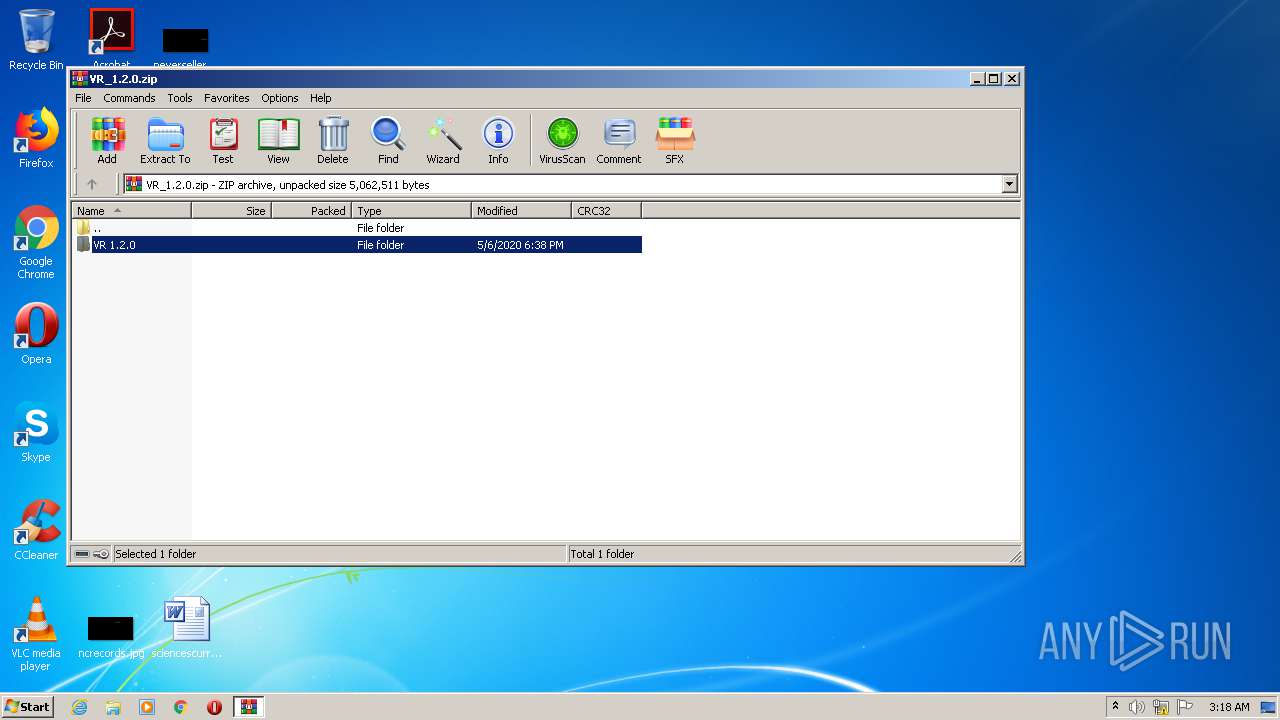
| 1684 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\VR_1.2.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\Desktop\VR 1.2.0\VR.exe" | C:\Users\admin\Desktop\VR 1.2.0\VR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3160 | C:\Windows\system32\rundll32.exe C:\Windows\system32\gameux.dll,GameUXShim {c69b7a85-0b83-401b-881a-3df6a3934000};C:\Users\admin\Desktop\VR 1.2.0\VR.exe;1208 | C:\Windows\system32\rundll32.exe | VR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3688 | C:\Windows\system32\rundll32.exe C:\Windows\system32\gameux.dll,GameUXShim {c69b7a85-0b83-401b-881a-3df6a3934000};C:\Users\admin\Desktop\VR 1.2.0\VR.exe;2752 | C:\Windows\system32\rundll32.exe | — | VR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3888 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 097
Read events
1 051
Write events
46
Delete events
0
Modification events
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VR_1.2.0.zip | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
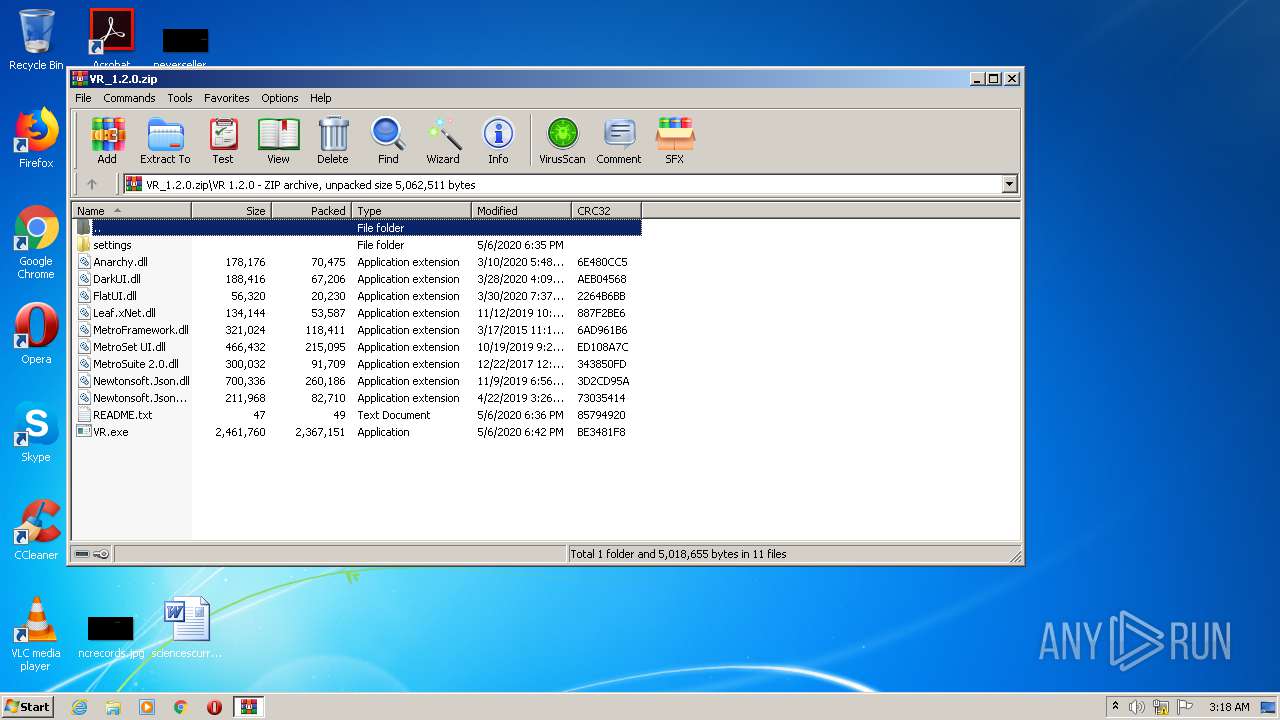
Executable files
9
Suspicious files
0
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
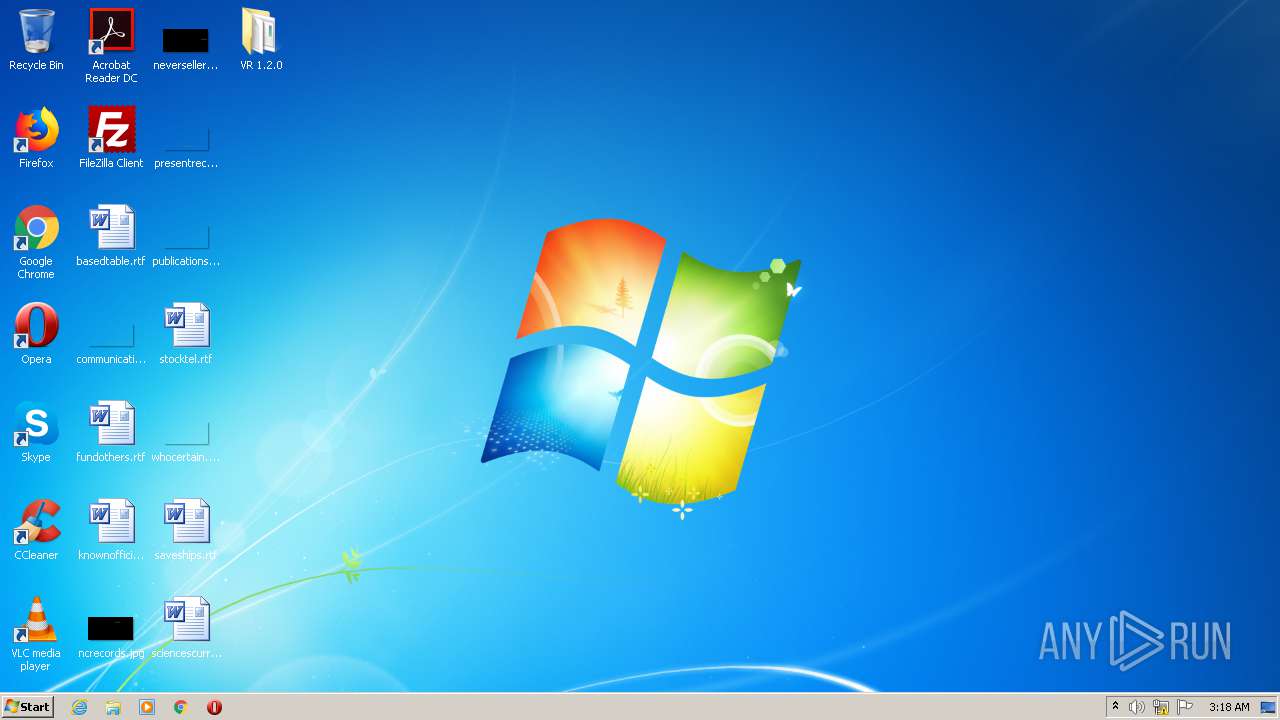
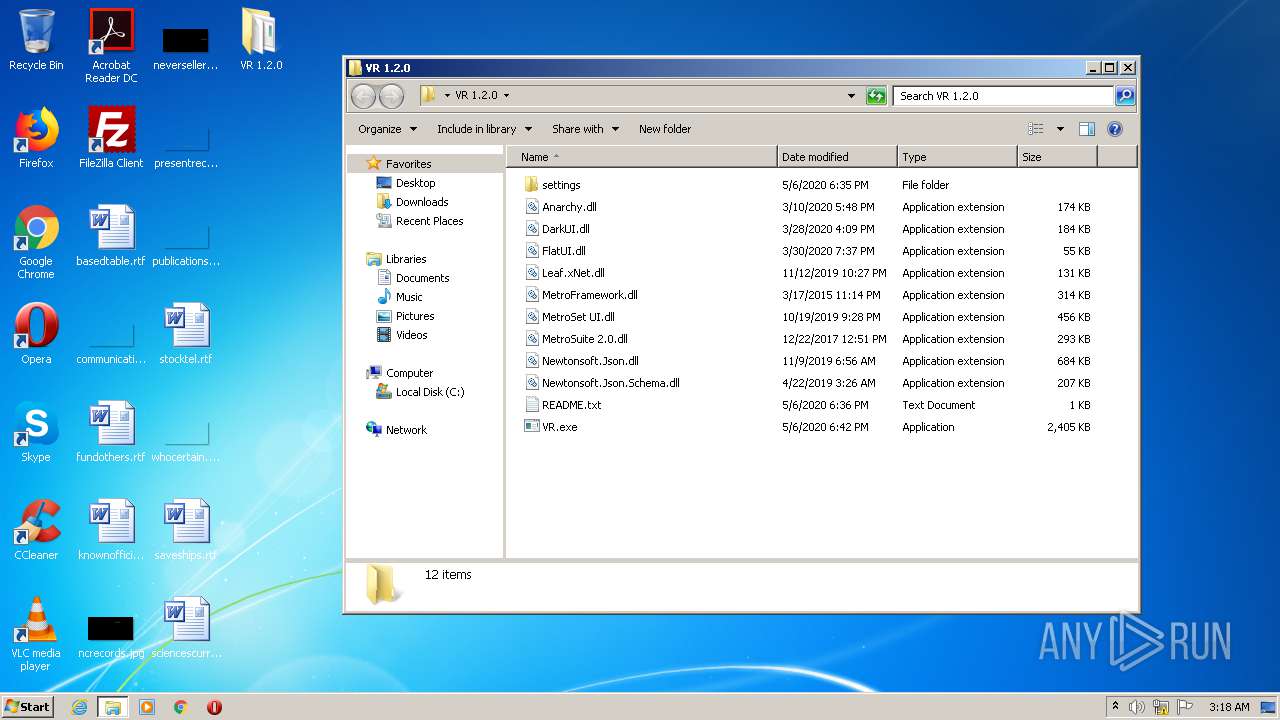
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\DarkUI.dll | executable | |
MD5:— | SHA256:— | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\MetroSuite 2.0.dll | executable | |
MD5:— | SHA256:— | |||
| 3160 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\GameExplorer\{818C2F35-4F49-4B27-A54A-BC8EB434AA63}\PlayTasks\0\Play.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3160 | rundll32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Games\Vietnam Med+Evac™.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\FlatUI.dll | executable | |
MD5:B63F5C816F8799857B9B8F95B6E2A9B0 | SHA256:058C926A8818479B06AB9402F2A6C85EB0F64626C2956102D6699AD413AFE2FB | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\Anarchy.dll | executable | |
MD5:— | SHA256:— | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\Leaf.xNet.dll | executable | |
MD5:4E7C24575ADFB677BF5772757A912A67 | SHA256:B6A74D45788815E285DD2700894847009AD5599CF8900297CE453E634547BDE5 | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\MetroFramework.dll | executable | |
MD5:— | SHA256:— | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\README.txt | text | |
MD5:— | SHA256:— | |||
| 1684 | WinRAR.exe | C:\Users\admin\Desktop\VR 1.2.0\VR.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
5
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1208 | VR.exe | GET | 404 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/updateState | US | html | 13.1 Kb | shared |
2752 | VR.exe | GET | 200 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/whitelist | US | text | 221 b | shared |
1208 | VR.exe | GET | 200 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/whitelist | US | text | 221 b | shared |
1208 | VR.exe | GET | 200 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/newestVersion | US | text | 5 b | shared |
1208 | VR.exe | GET | 200 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/whitelist | US | text | 221 b | shared |
2752 | VR.exe | GET | 200 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/newestVersion | US | text | 5 b | shared |
3160 | rundll32.exe | GET | 302 | 104.111.238.86:80 | http://go.microsoft.com/fwlink?linkid=30219&locale=en-US&clientType=VISTA_GAMES&clientVersion=6.1.2 | NL | — | — | whitelisted |
3160 | rundll32.exe | GET | — | 65.55.186.115:80 | http://movie.metaservices.microsoft.com/locater/WMServiceLocater.asmx/GetServiceLocationsForClient?locale=en-US&clientType=VISTA_GAMES&clientVersion=6.1.2 | US | — | — | whitelisted |
2752 | VR.exe | GET | 404 | 145.14.144.222:80 | http://voidata.000webhostapp.com/voidraider/updateState | US | html | 13.1 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3160 | rundll32.exe | 104.111.238.86:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
3160 | rundll32.exe | 65.55.186.115:80 | movie.metaservices.microsoft.com | Microsoft Corporation | US | whitelisted |
2752 | VR.exe | 145.14.144.222:80 | voidata.000webhostapp.com | Hostinger International Limited | US | shared |
— | — | 145.14.144.222:80 | voidata.000webhostapp.com | Hostinger International Limited | US | shared |
1208 | VR.exe | 145.14.144.222:80 | voidata.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
movie.metaservices.microsoft.com |
| whitelisted |
voidata.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |