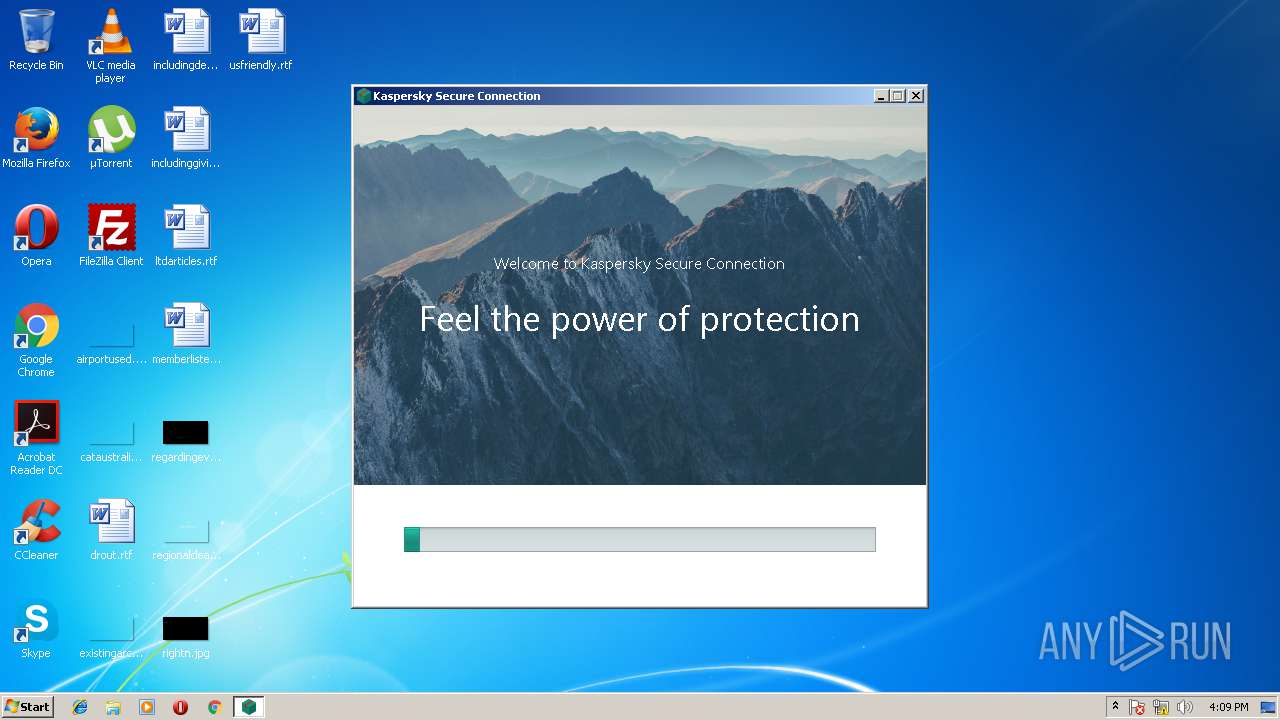
| download: | ksde19.0.0.1088_en-gb_full.exe |
| Full analysis: | https://app.any.run/tasks/ebe72581-4e6c-4afa-a25b-2ceee345feb6 |
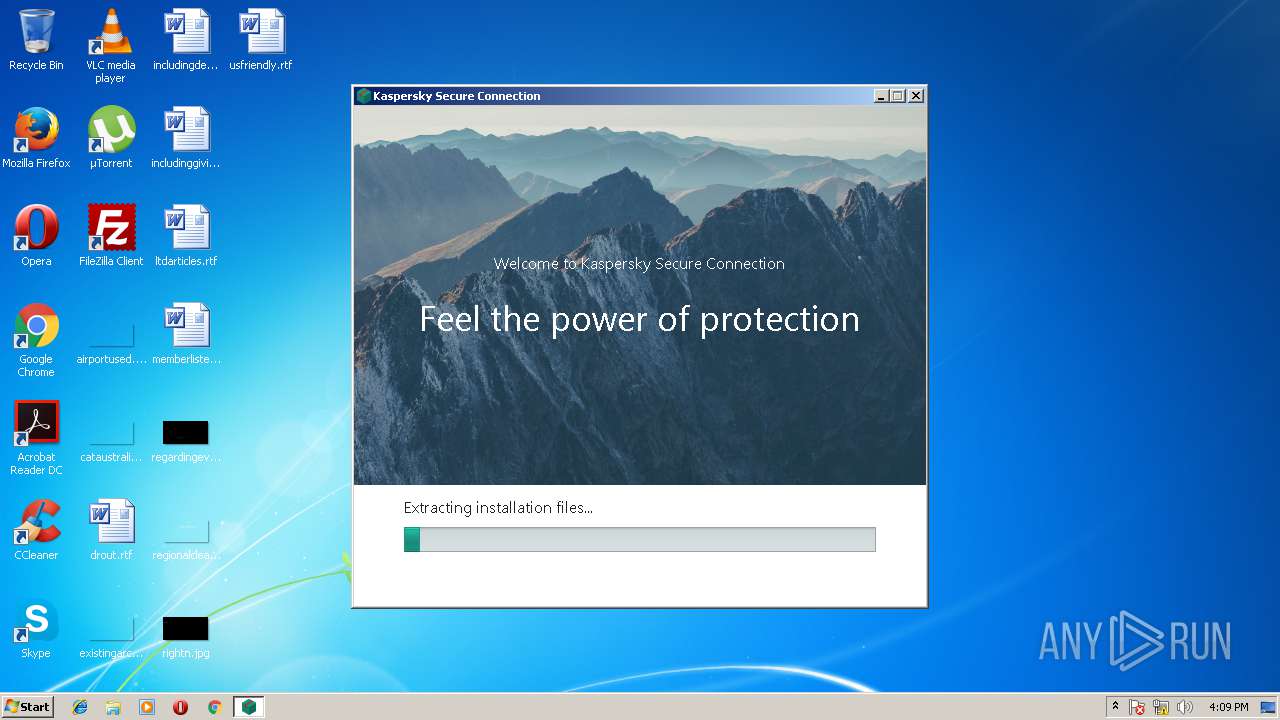
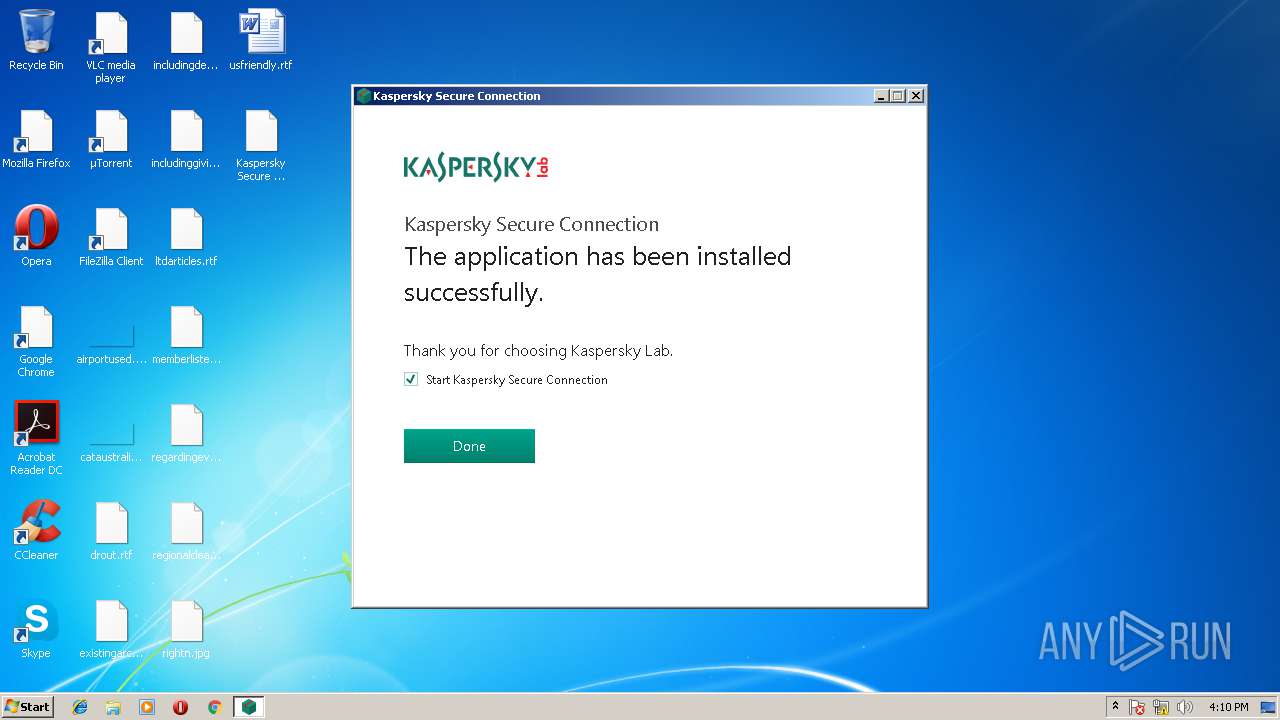
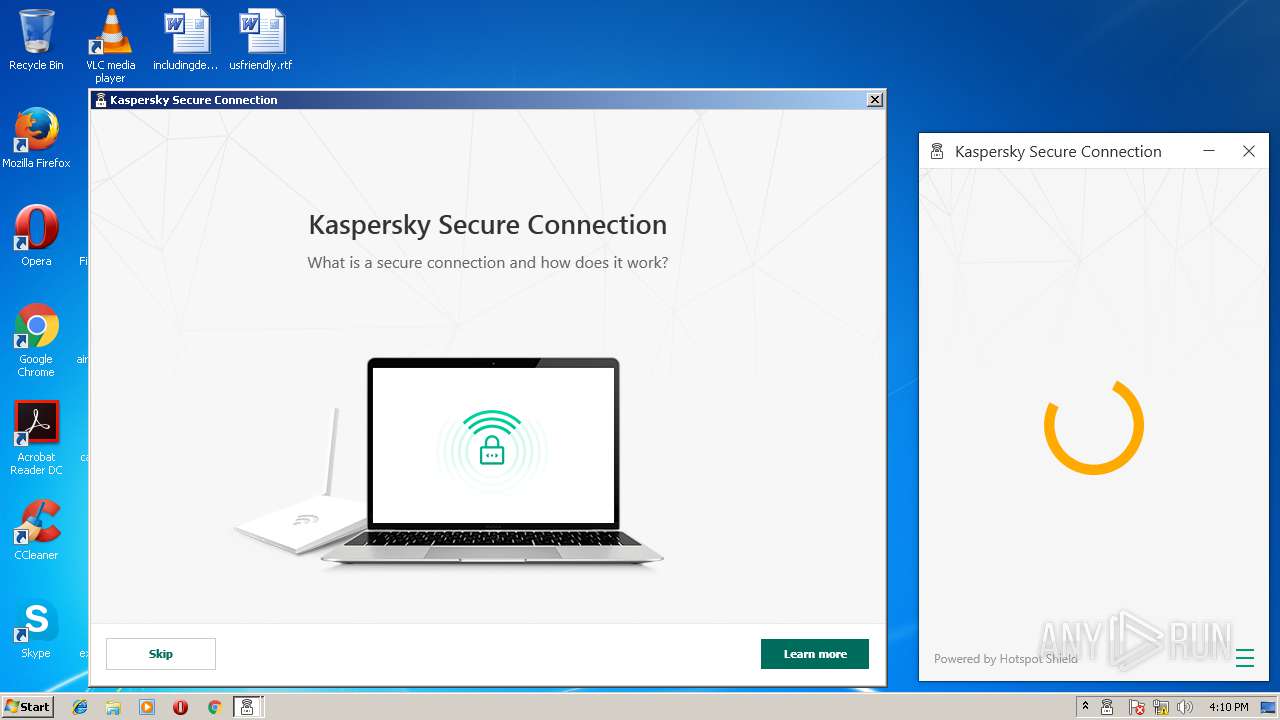
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2018, 15:09:01 |
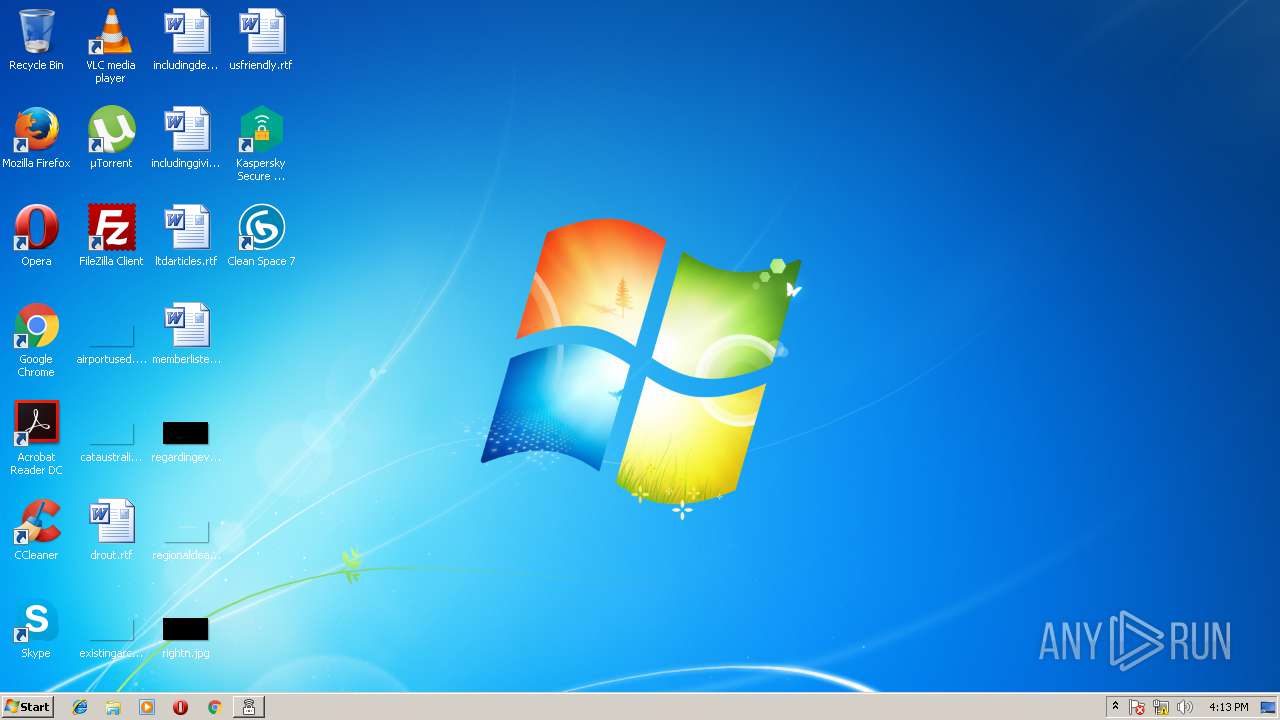
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8220C1D1803C371B96BC26332E4F0200 |
| SHA1: | EBF7B8E5B14741D7ABA6B66B975C042CA06BE8D9 |
| SHA256: | 1644AB458B180979AACC0EC3A5E0BBE61E429F07F1C8DF4BC6611F04690CB7D3 |
| SSDEEP: | 393216:V0N3dtRRx11VphFGN2+MWIb0Oej0yGFmbxEJ5klS/z5EFfQK:ETx11rvG03yjLGFmtE3z5EFfj |
MALICIOUS
Changes settings of System certificates
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- ksde.exe (PID: 804)
Loads dropped or rewritten executable
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- TEST_WPF.EXE (PID: 2820)
- ksdeui.exe (PID: 2876)
- ksde.exe (PID: 804)
- ksdeui.exe (PID: 3548)
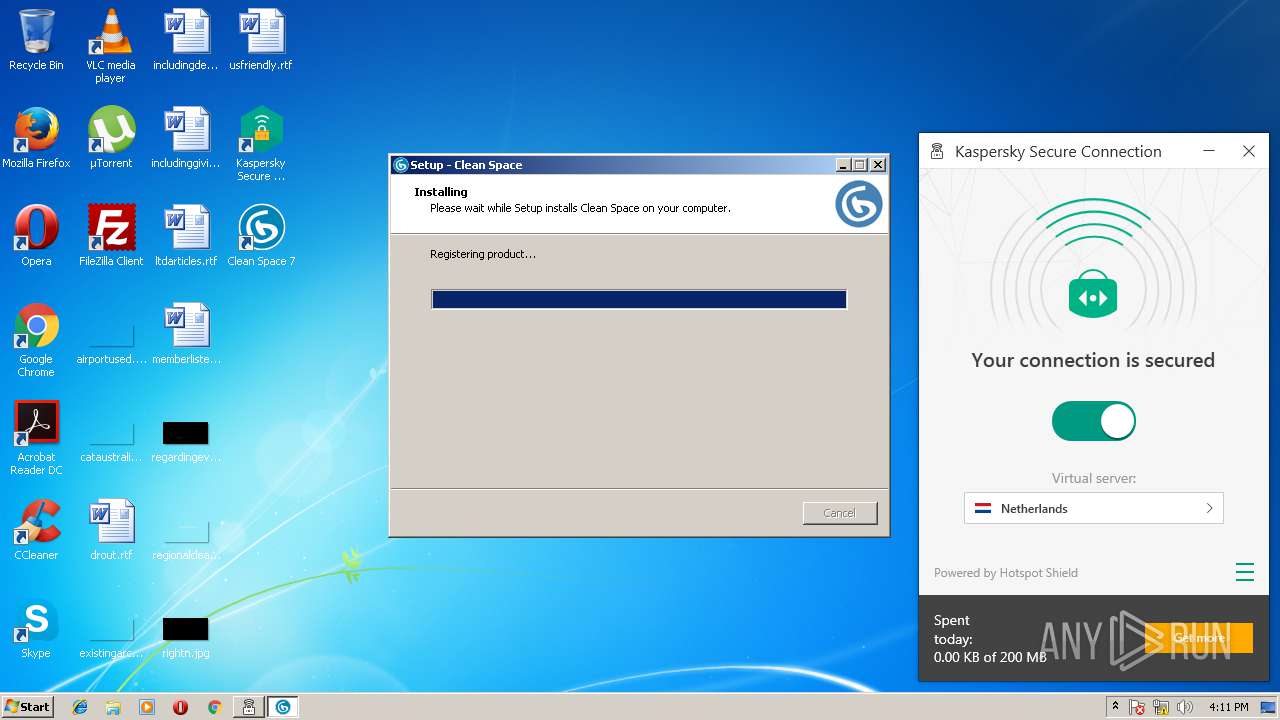
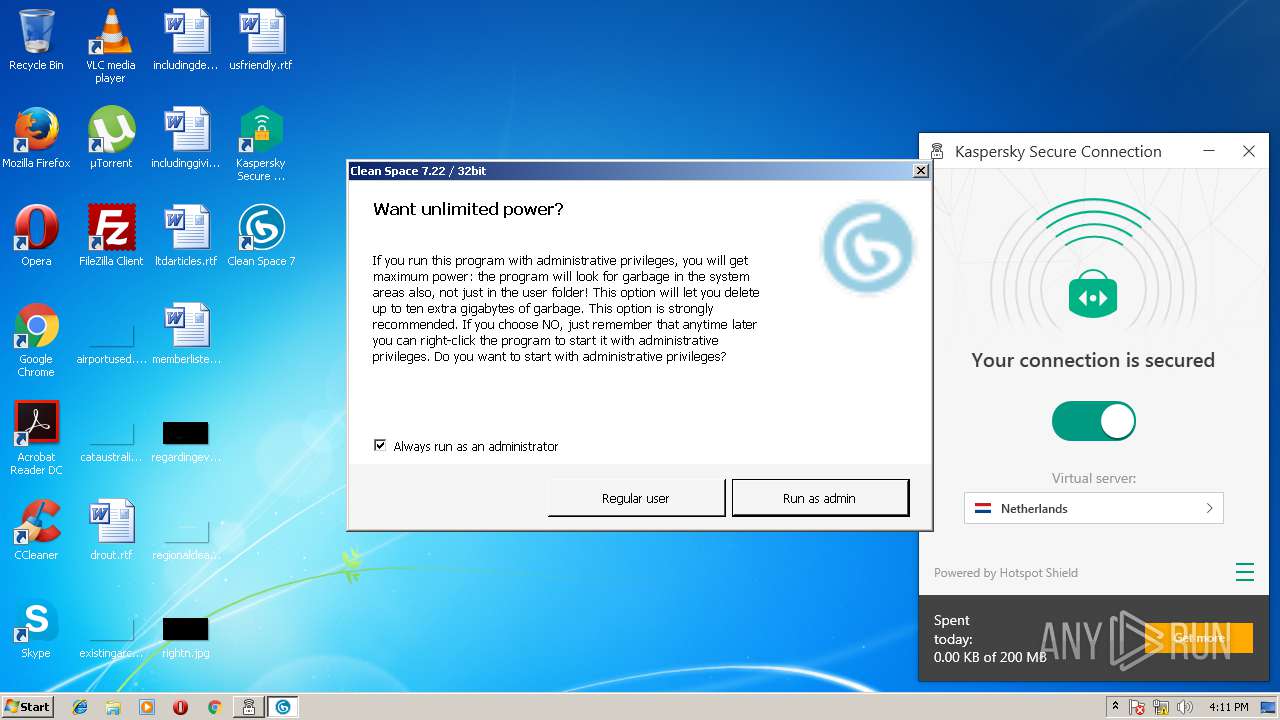
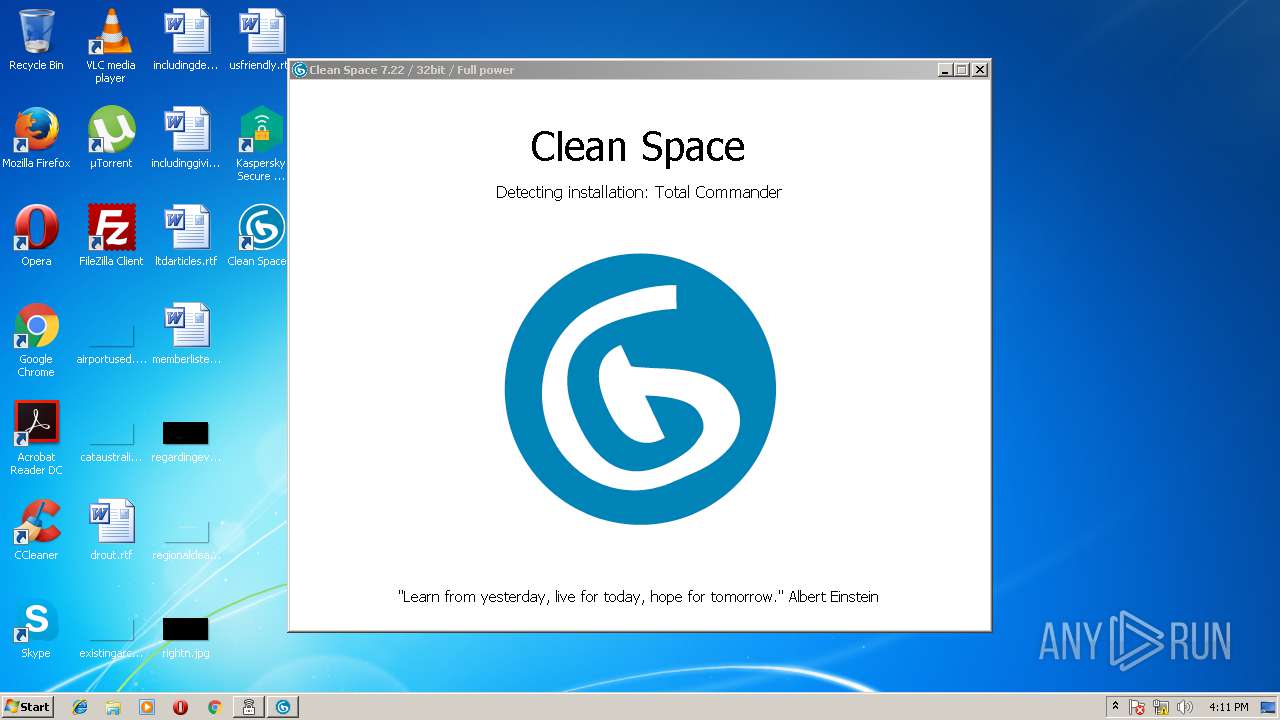
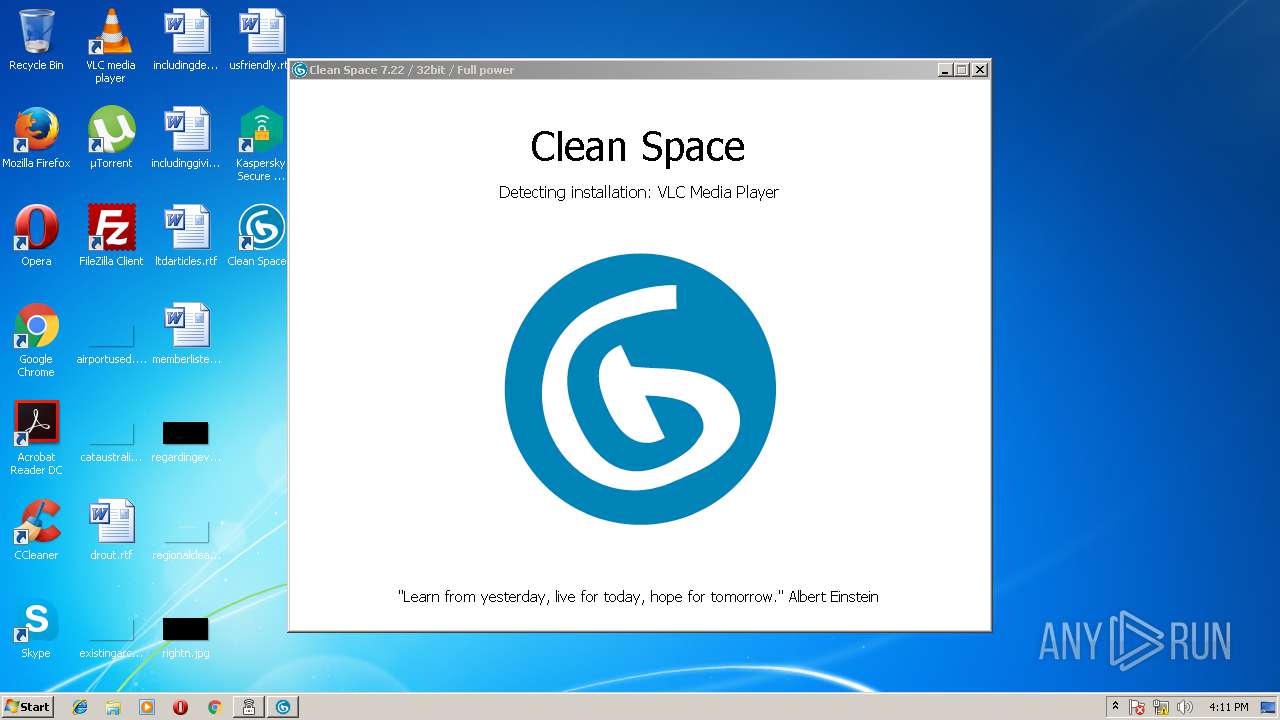
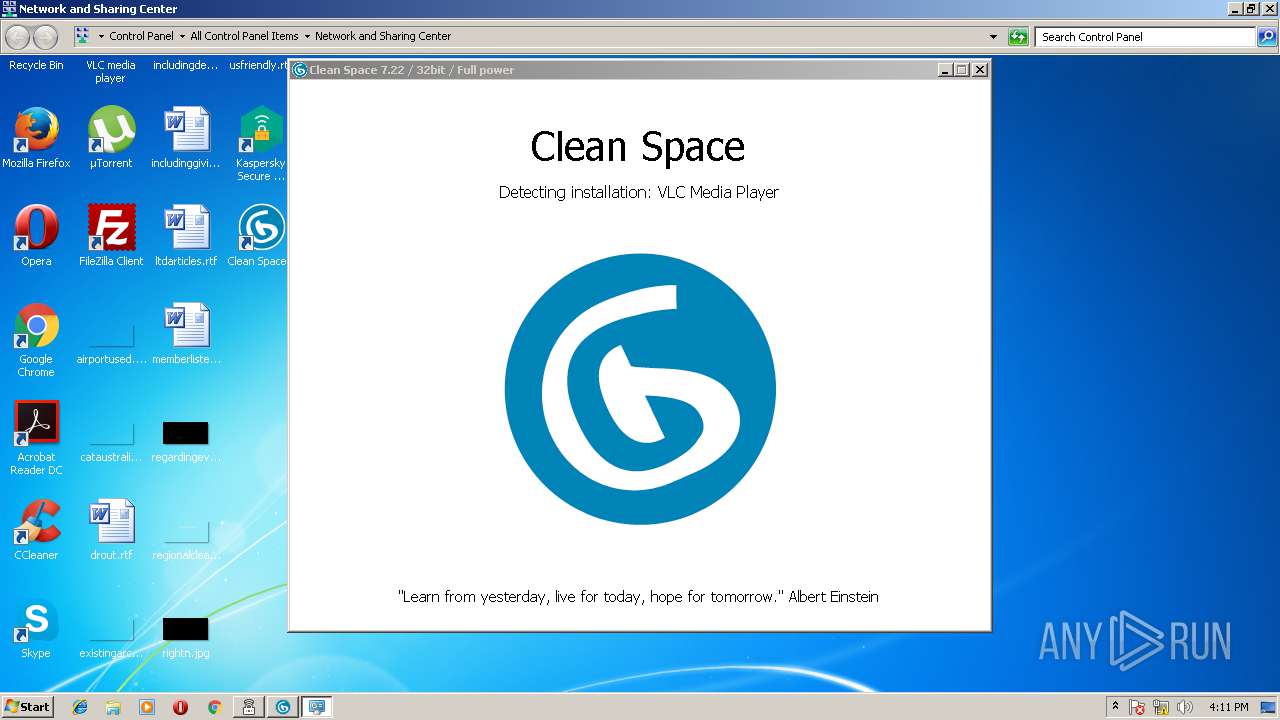
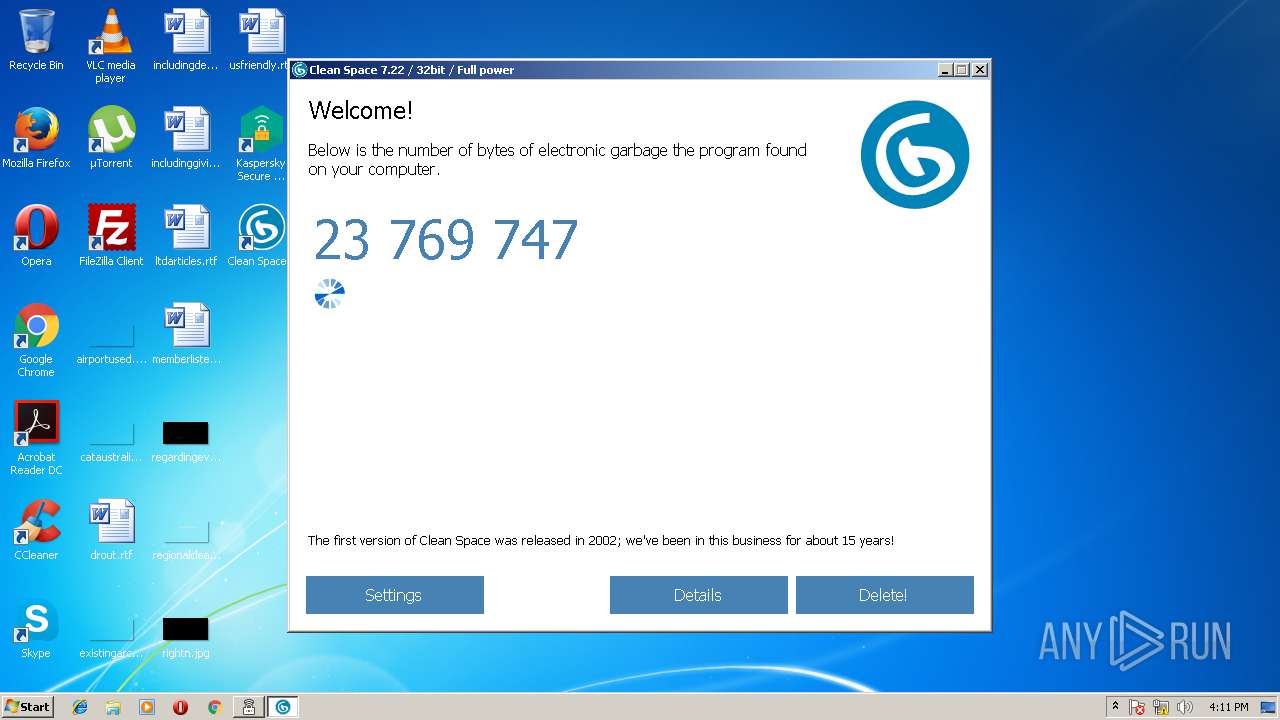
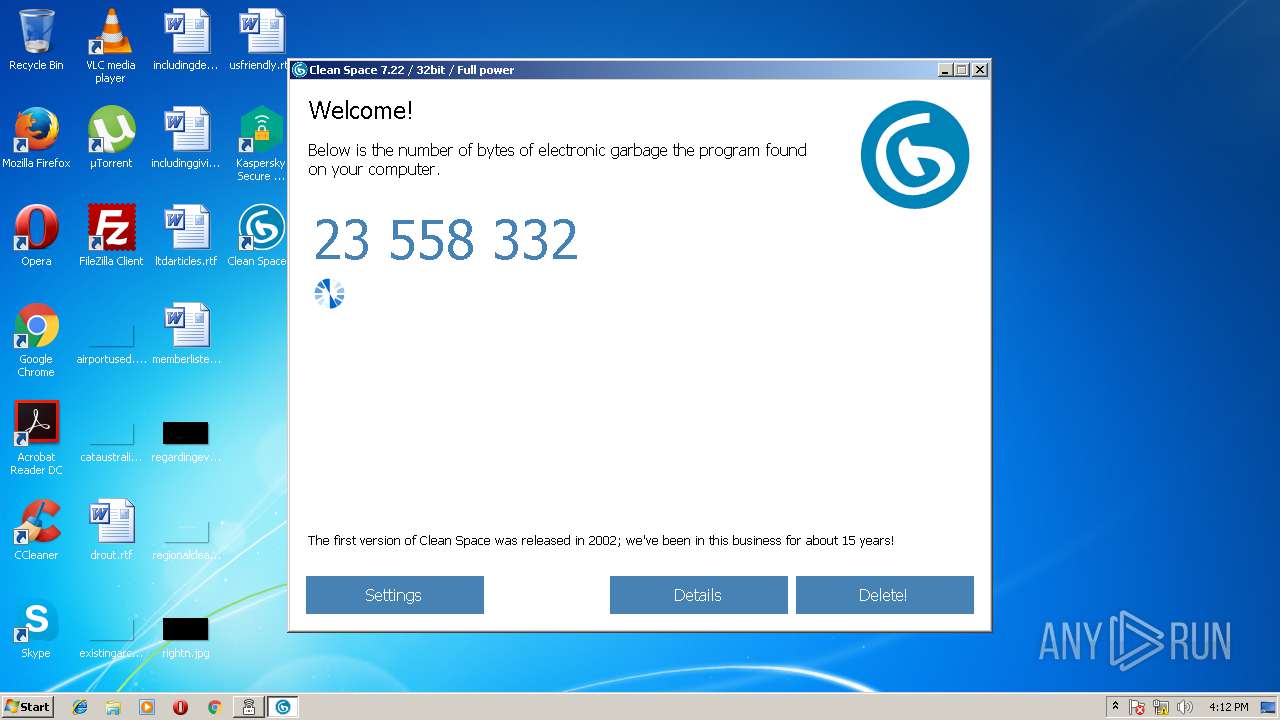
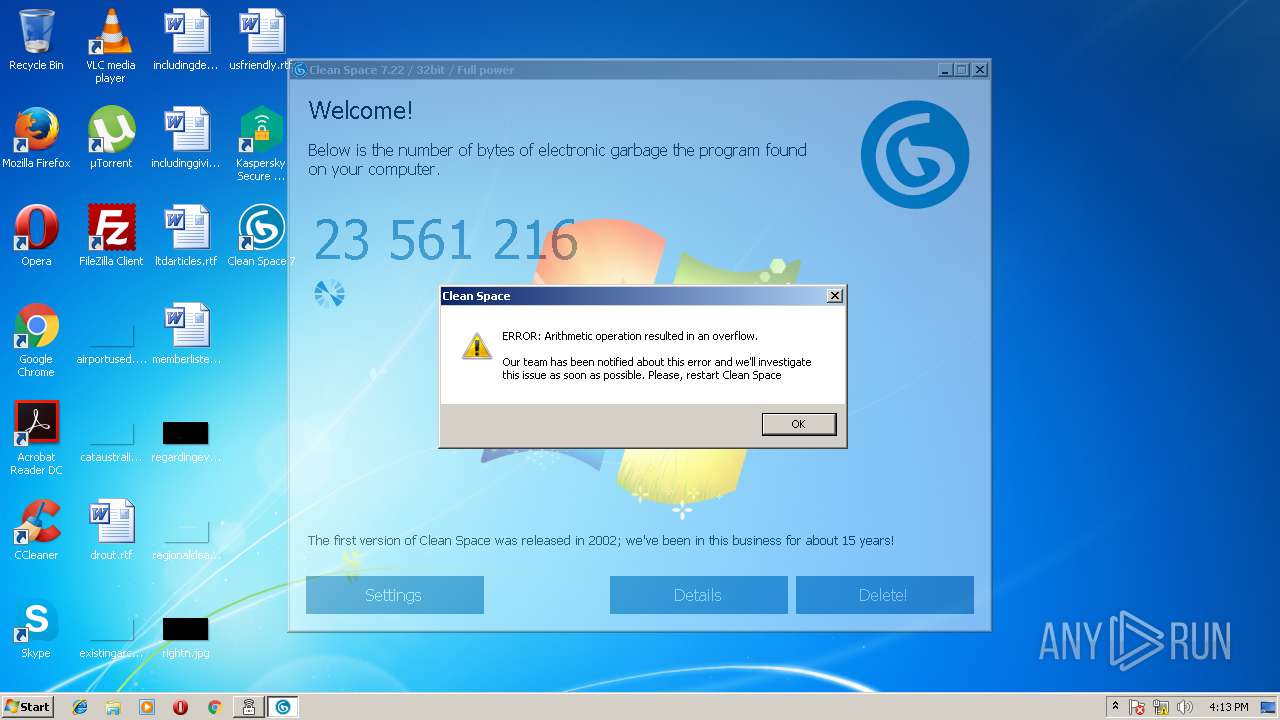
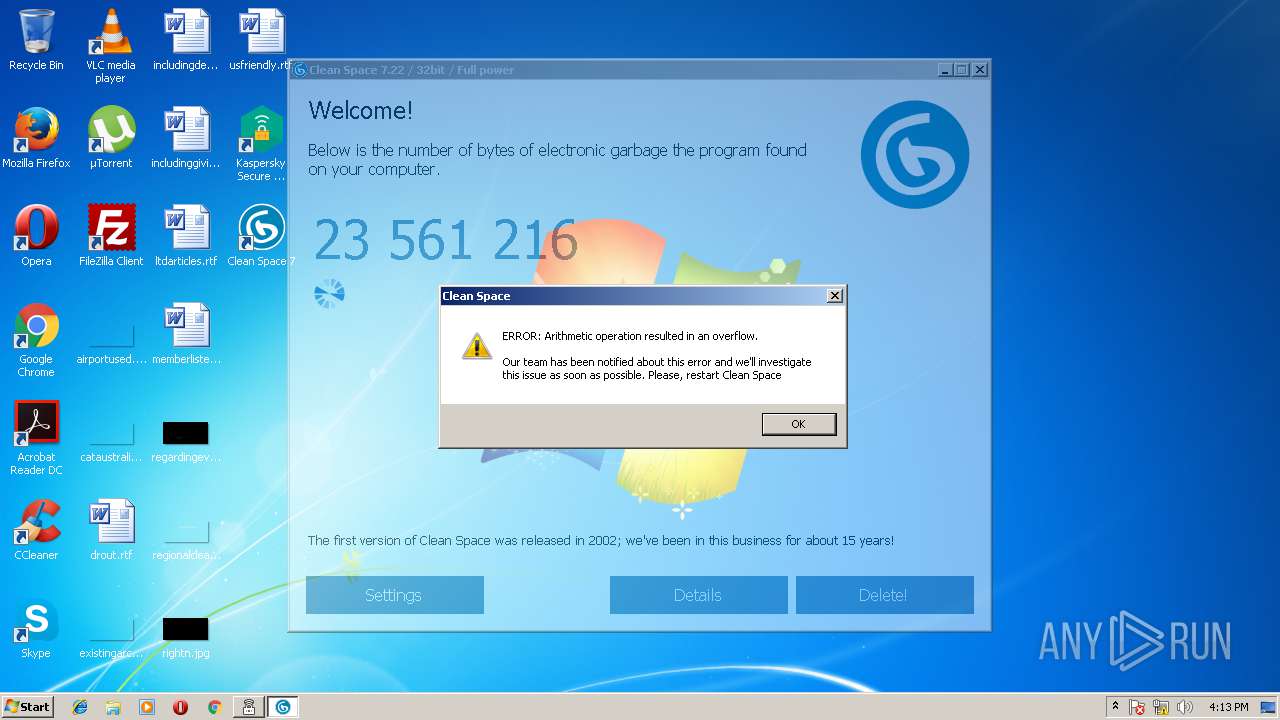
- cleanspace.exe (PID: 2688)
- cleanspace.exe (PID: 1524)
- cleanspace.exe (PID: 2272)
- cleanspace.exe (PID: 3912)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 560)
- cleanspace.exe (PID: 4080)
Application was dropped or rewritten from another process
- TEST_WPF.EXE (PID: 2820)
- ksdeui.exe (PID: 2876)
- ksde.exe (PID: 804)
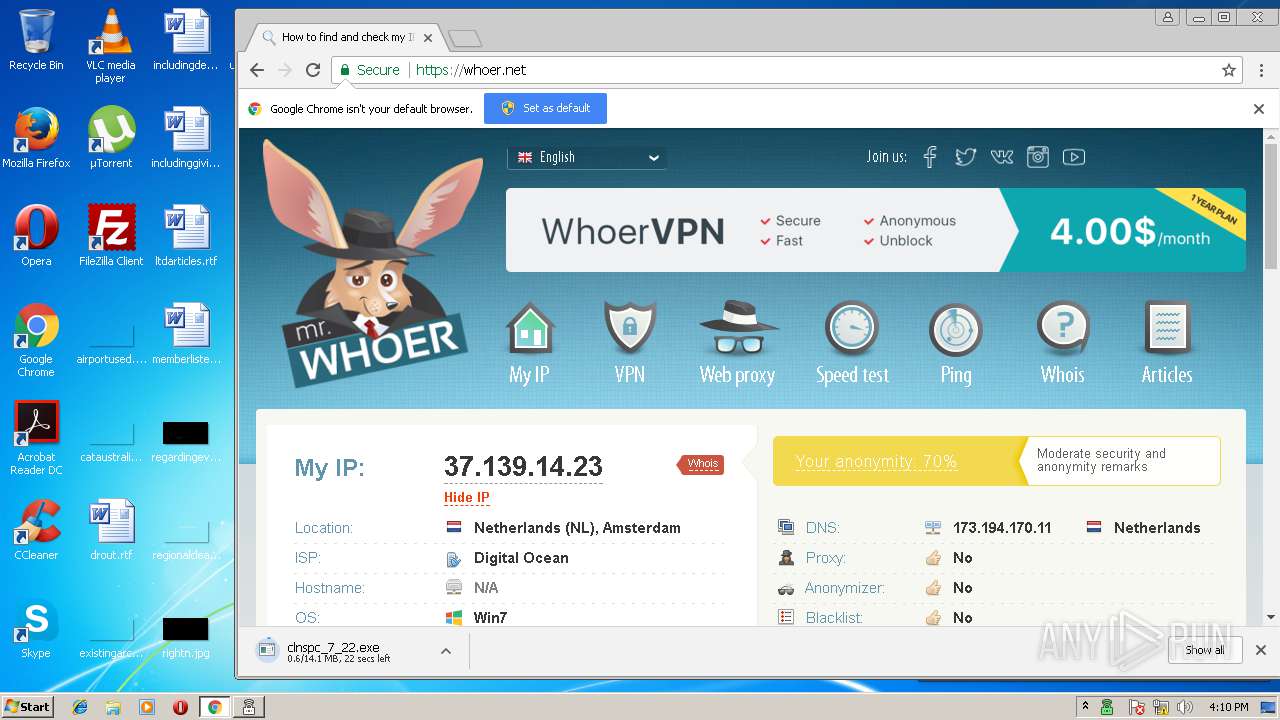
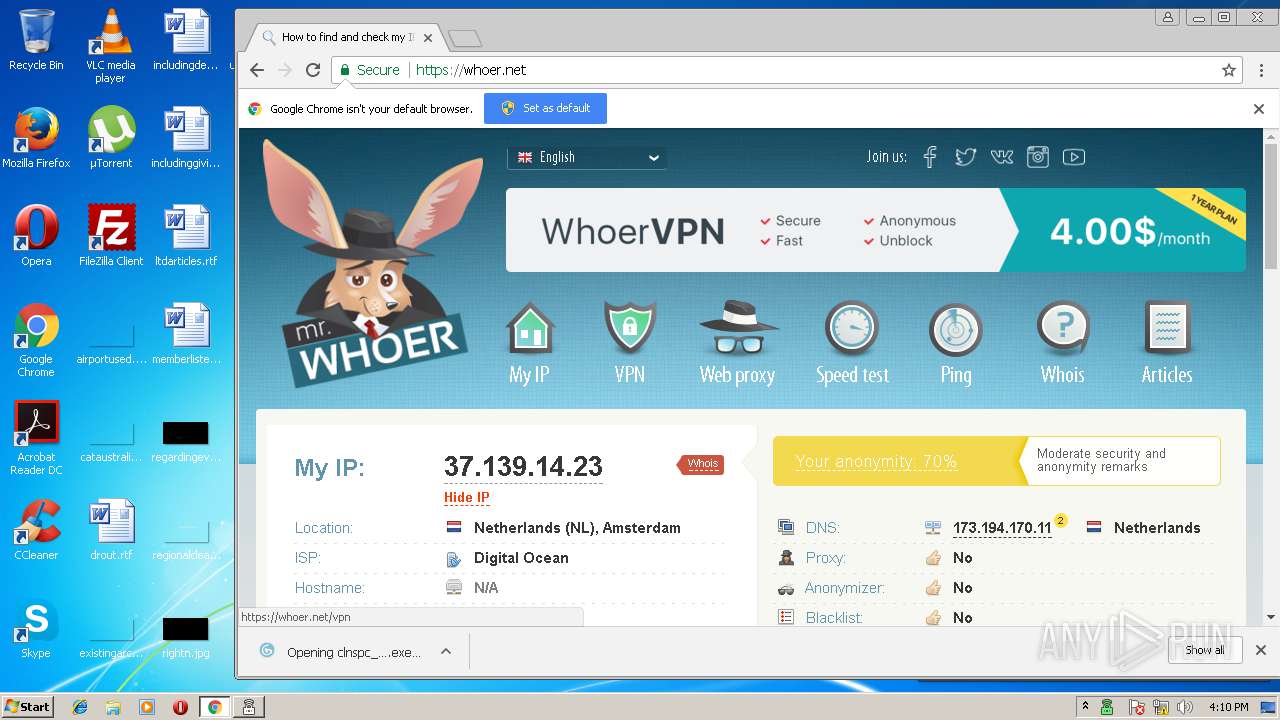
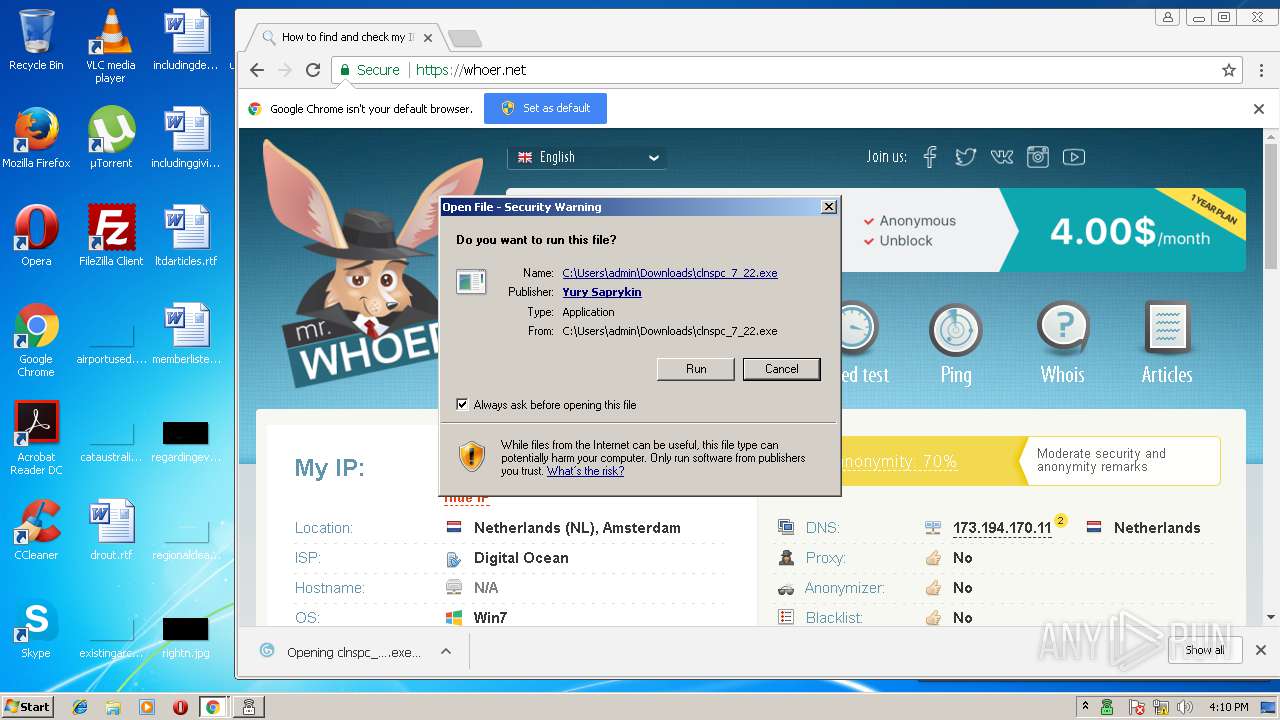
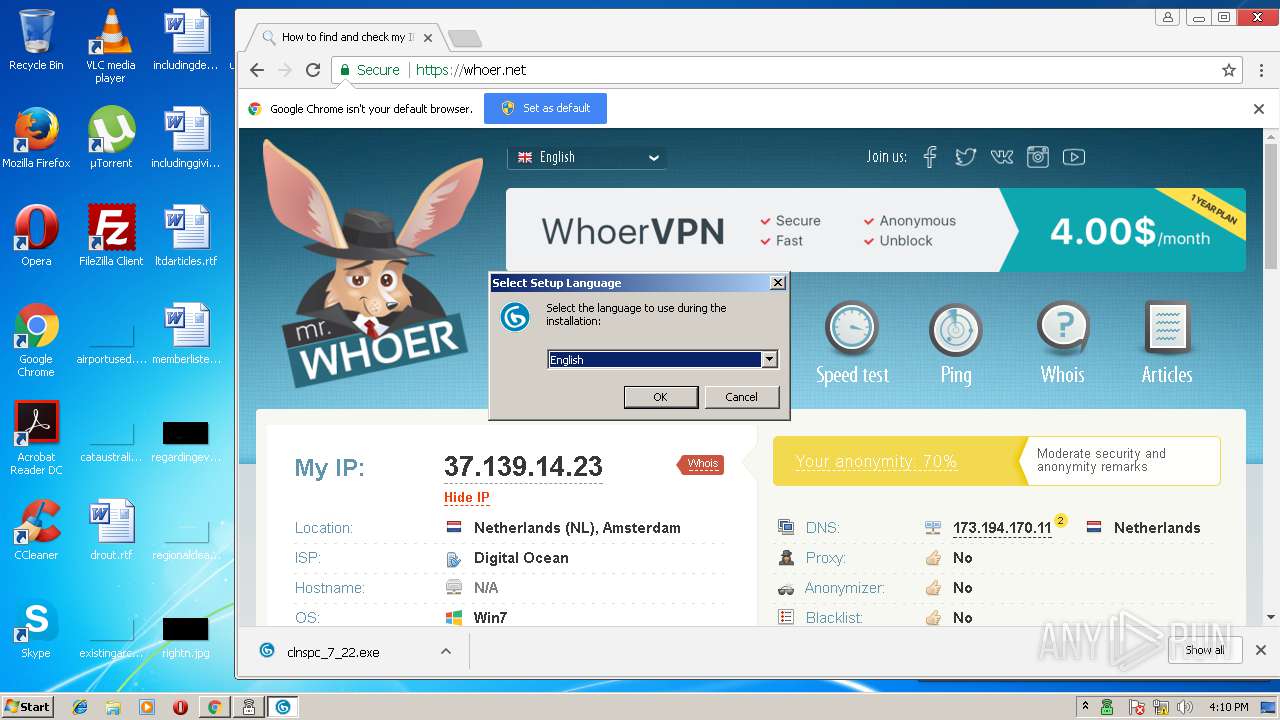
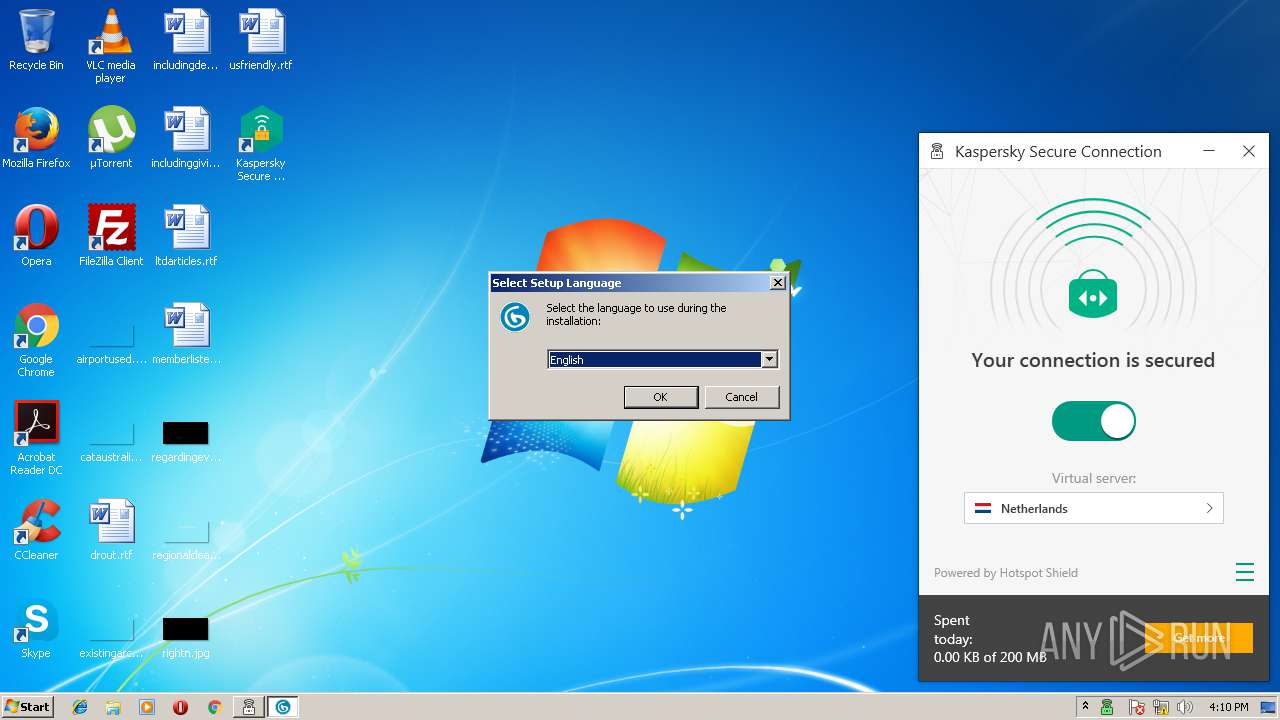
- clnspc_7_22.exe (PID: 3188)
- clnspc_7_22.exe (PID: 1400)
- cleanspace.exe (PID: 1524)
- cleanspace.exe (PID: 2688)
- cleanspace.exe (PID: 2272)
- cleanspace.exe (PID: 3912)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 560)
- cleanspace.exe (PID: 4080)
- ksdeui.exe (PID: 3548)
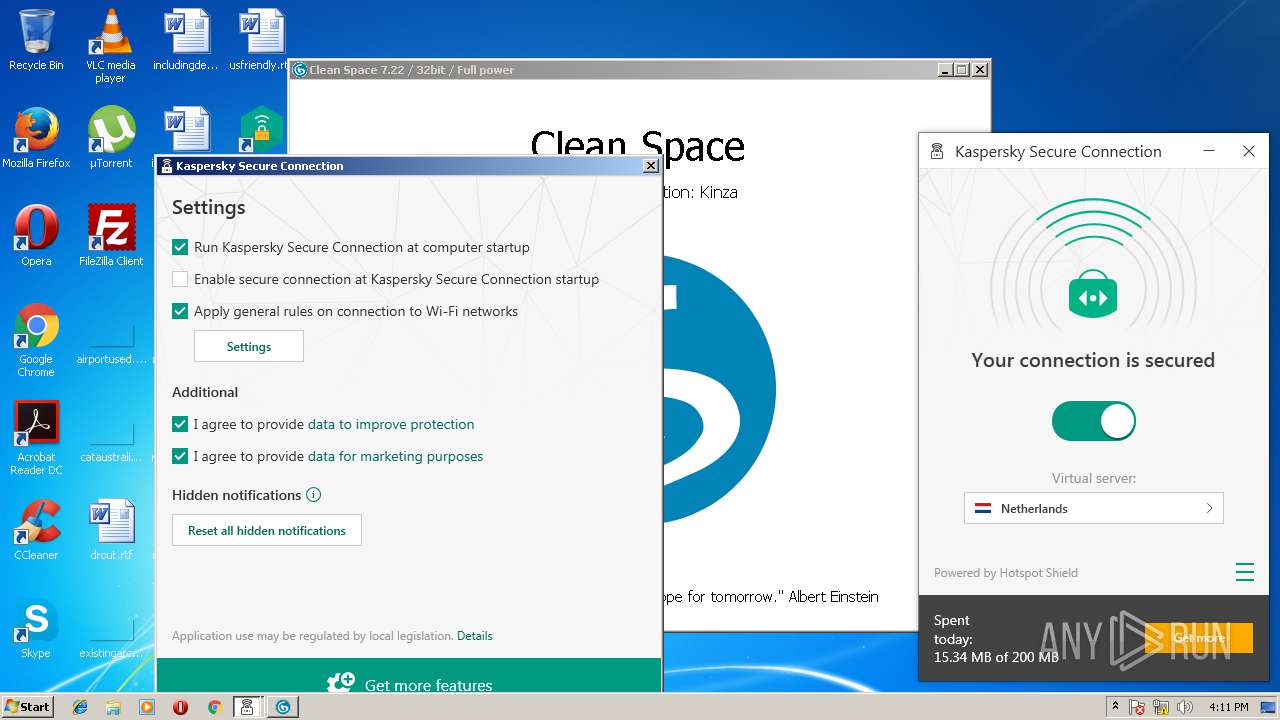
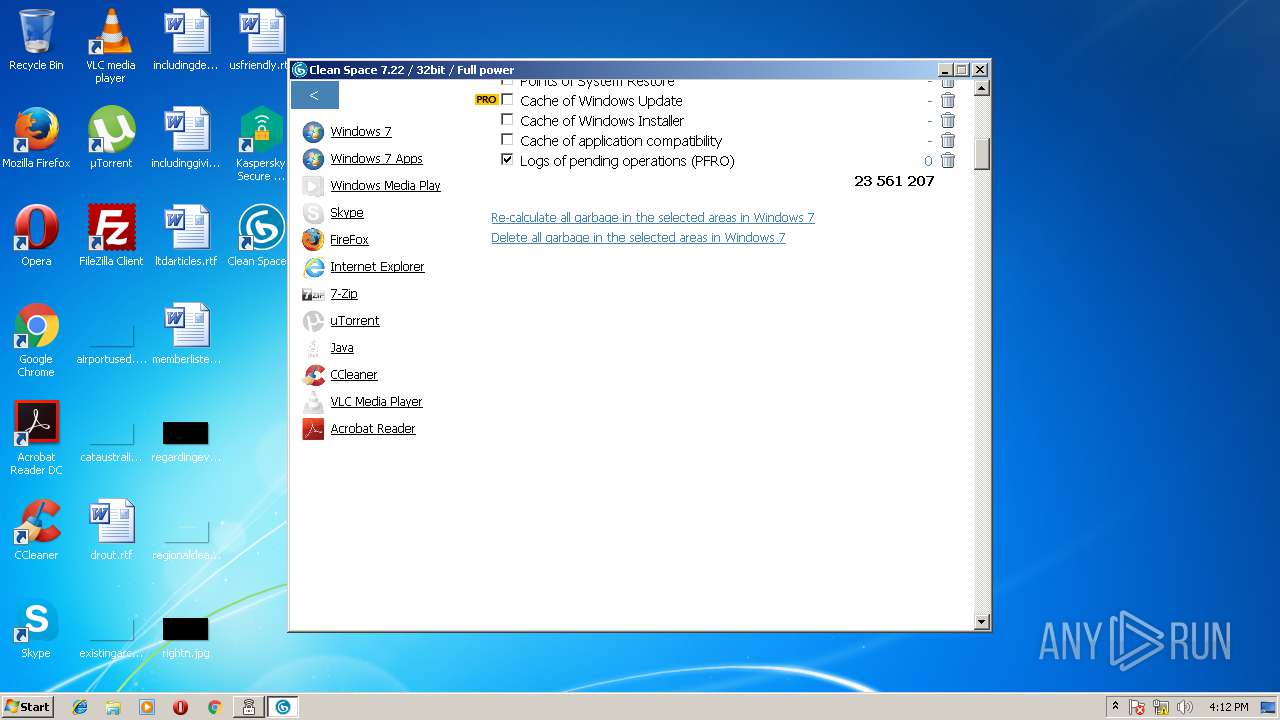
Changes the autorun value in the registry
- cleanspace.exe (PID: 2688)
- cleanspace.exe (PID: 1524)
- cleanspace.exe (PID: 2272)
- cleanspace.exe (PID: 3912)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 560)
- cleanspace.exe (PID: 4080)
SUSPICIOUS
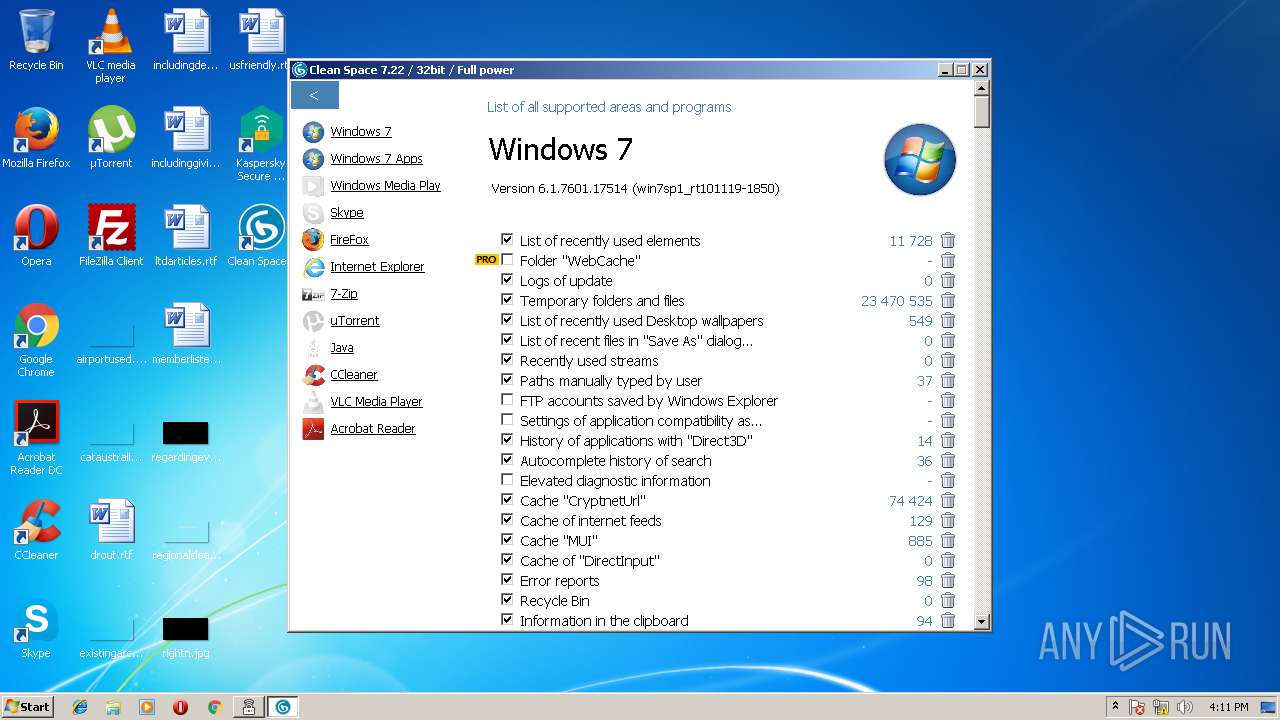
Reads Internet Cache Settings
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
Application launched itself
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- cleanspace.exe (PID: 3912)
- cleanspace.exe (PID: 560)
Creates files in the program directory
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- ksdeui.exe (PID: 2876)
- ksde.exe (PID: 804)
- ksdeui.exe (PID: 3548)
Executable content was dropped or overwritten
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- msiexec.exe (PID: 4076)
- MsiExec.exe (PID: 2120)
- DrvInst.exe (PID: 1508)
- clnspc_7_22.exe (PID: 1400)
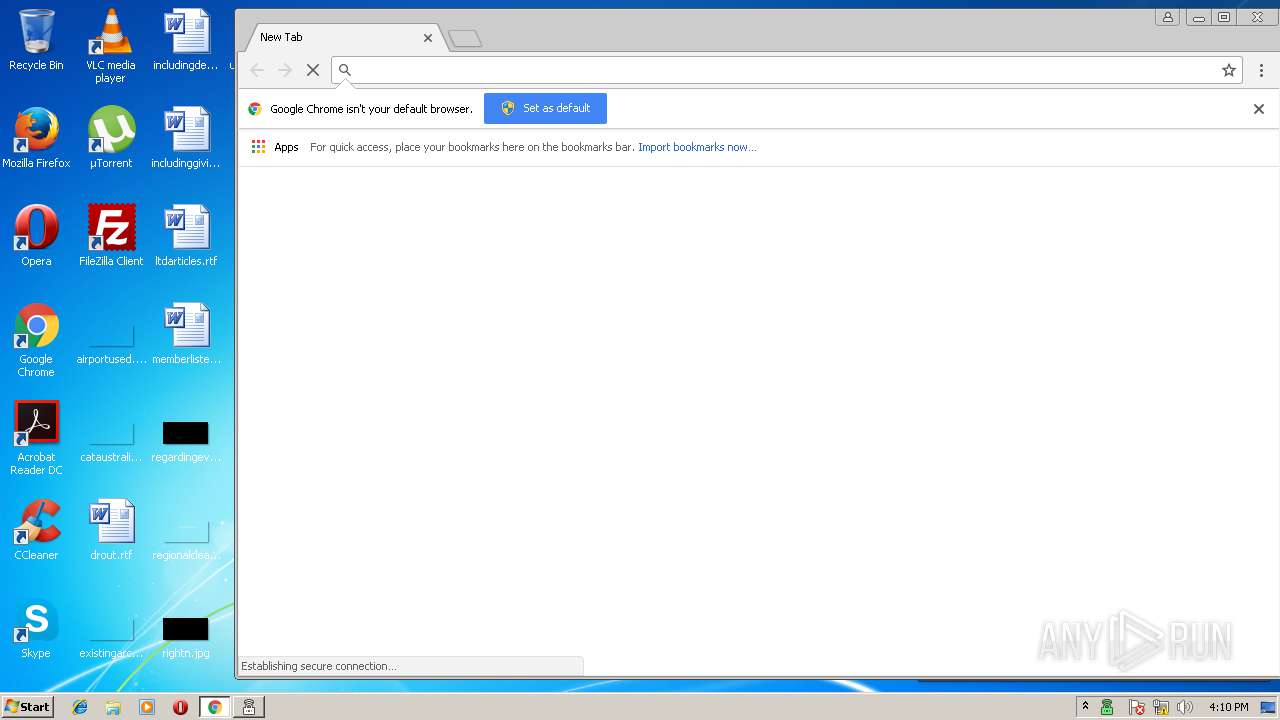
- chrome.exe (PID: 4016)
- clnspc_7_22.exe (PID: 3188)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 4080)
- clnspc_7_22.tmp (PID: 1488)
Creates files in the user directory
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 4080)
Adds / modifies Windows certificates
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
Creates files in the Windows directory
- MsiExec.exe (PID: 3712)
- DrvInst.exe (PID: 1516)
- DrvInst.exe (PID: 1508)
Creates files in the driver directory
- DrvInst.exe (PID: 1516)
- DrvInst.exe (PID: 1508)
Removes files from Windows directory
- DrvInst.exe (PID: 1516)
- DrvInst.exe (PID: 1508)
Modifies the open verb of a shell class
- MsiExec.exe (PID: 3712)
Reads the machine GUID from the registry
- ksde.exe (PID: 804)
Creates or modifies windows services
- ksde.exe (PID: 804)
- DrvInst.exe (PID: 1508)
- DllHost.exe (PID: 3144)
- DllHost.exe (PID: 2880)
Reads the Windows organization settings
- clnspc_7_22.tmp (PID: 1488)
Reads Windows owner settings
- clnspc_7_22.tmp (PID: 1488)
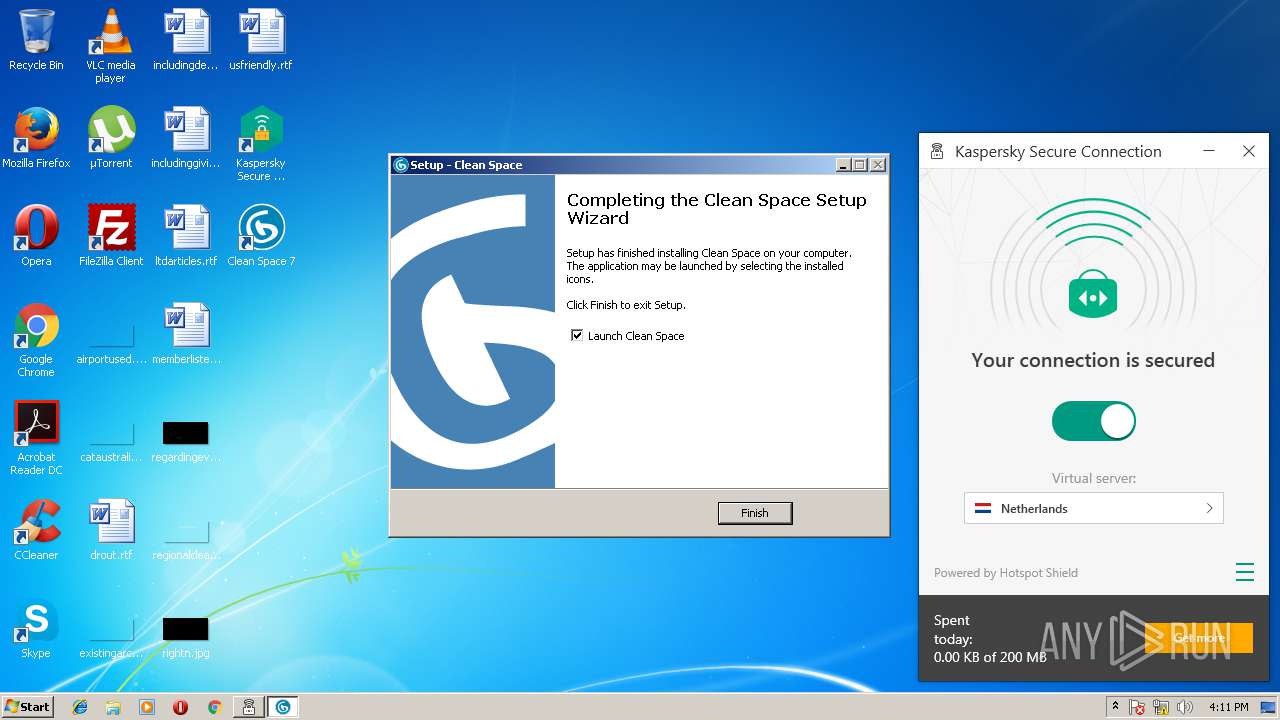
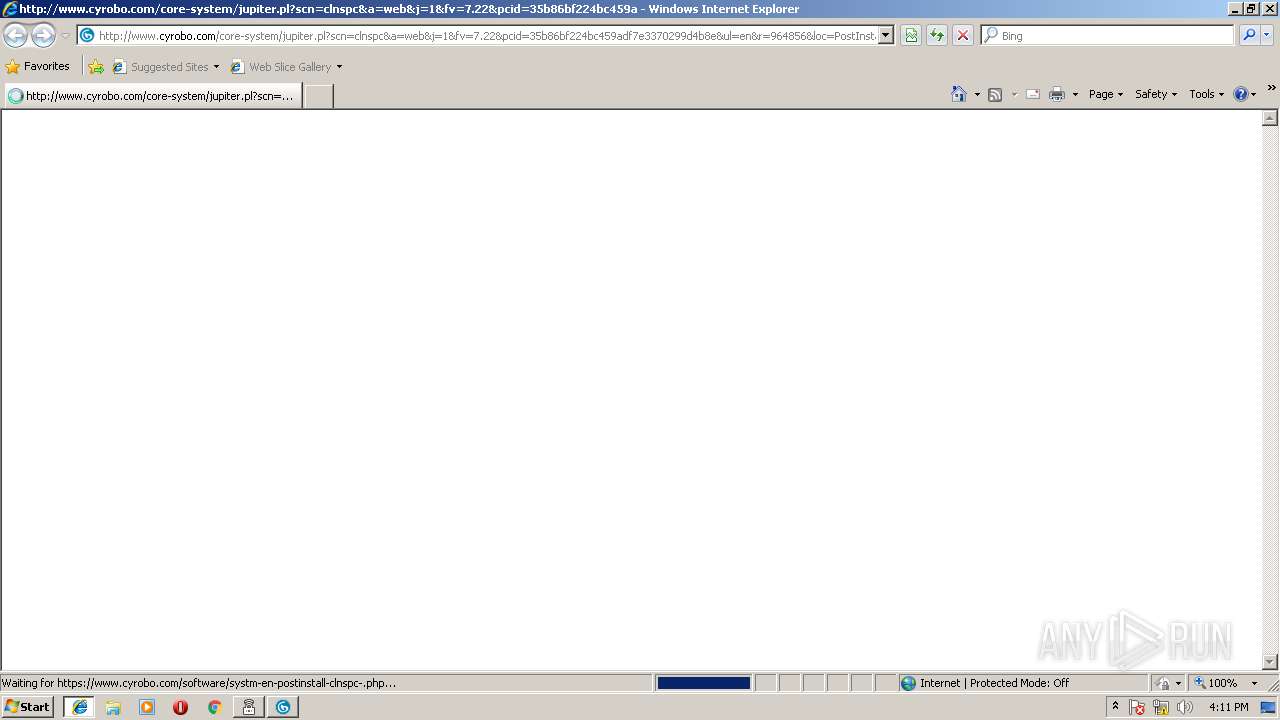
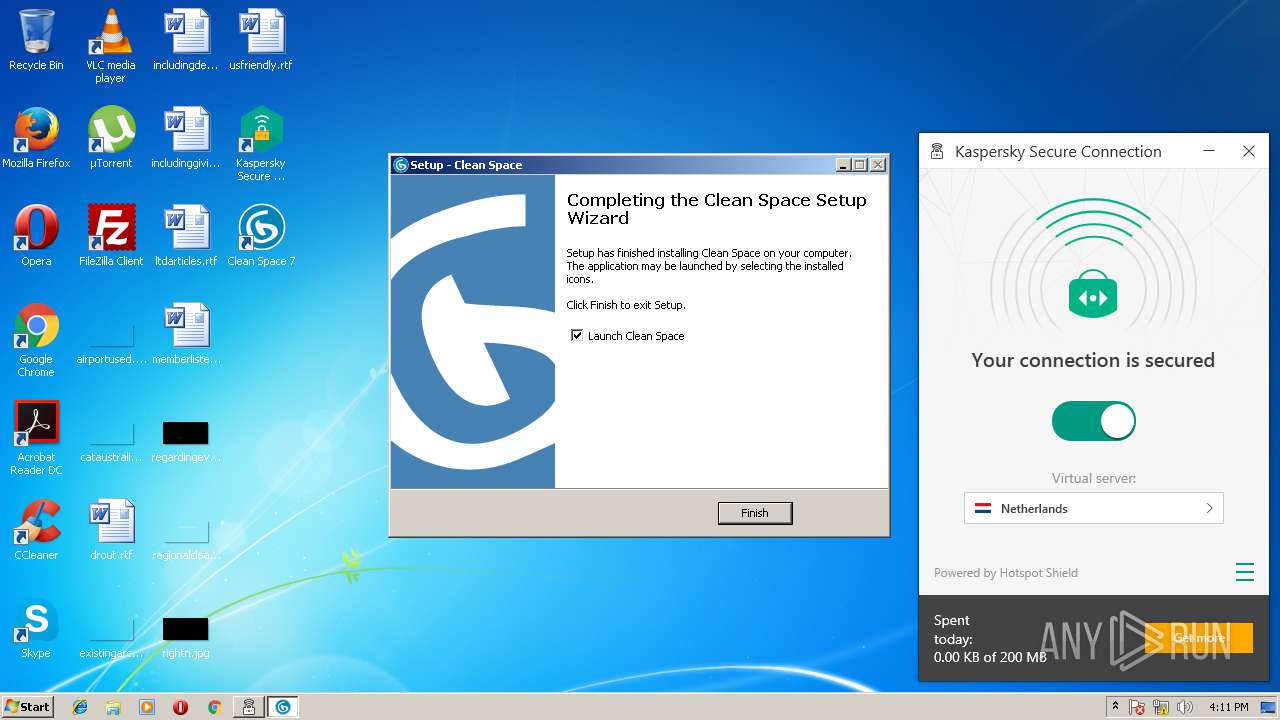
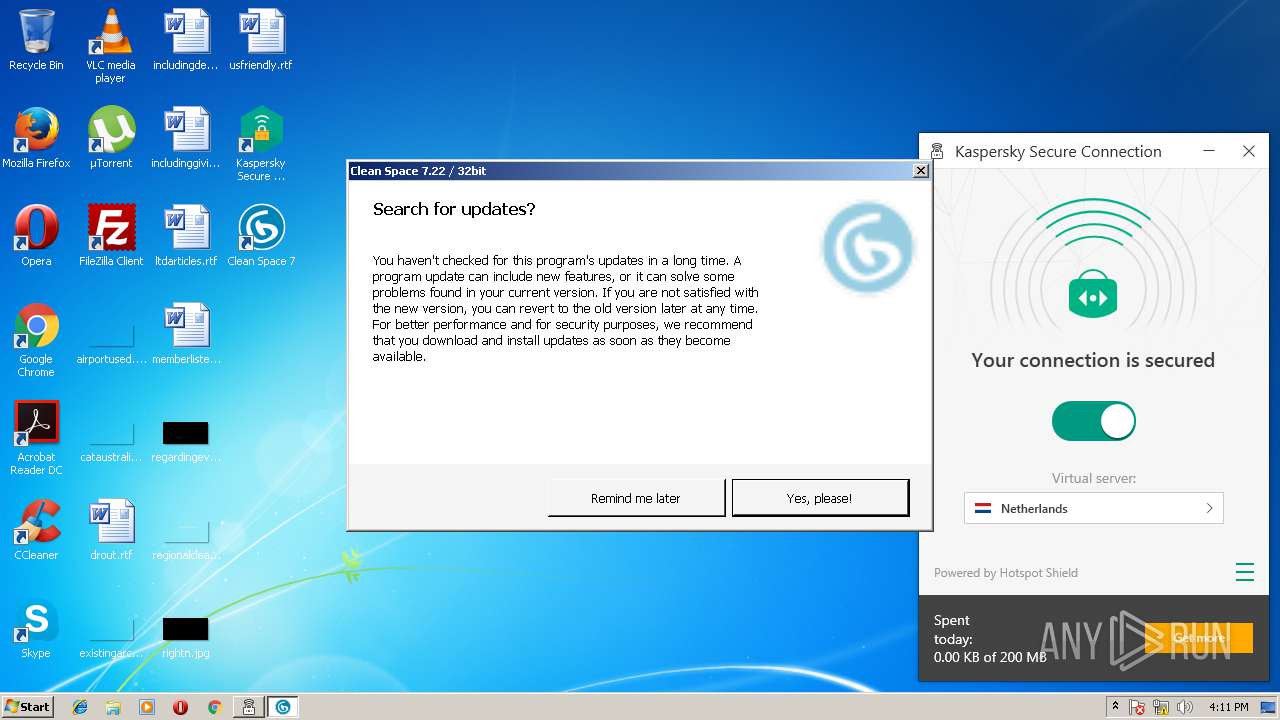
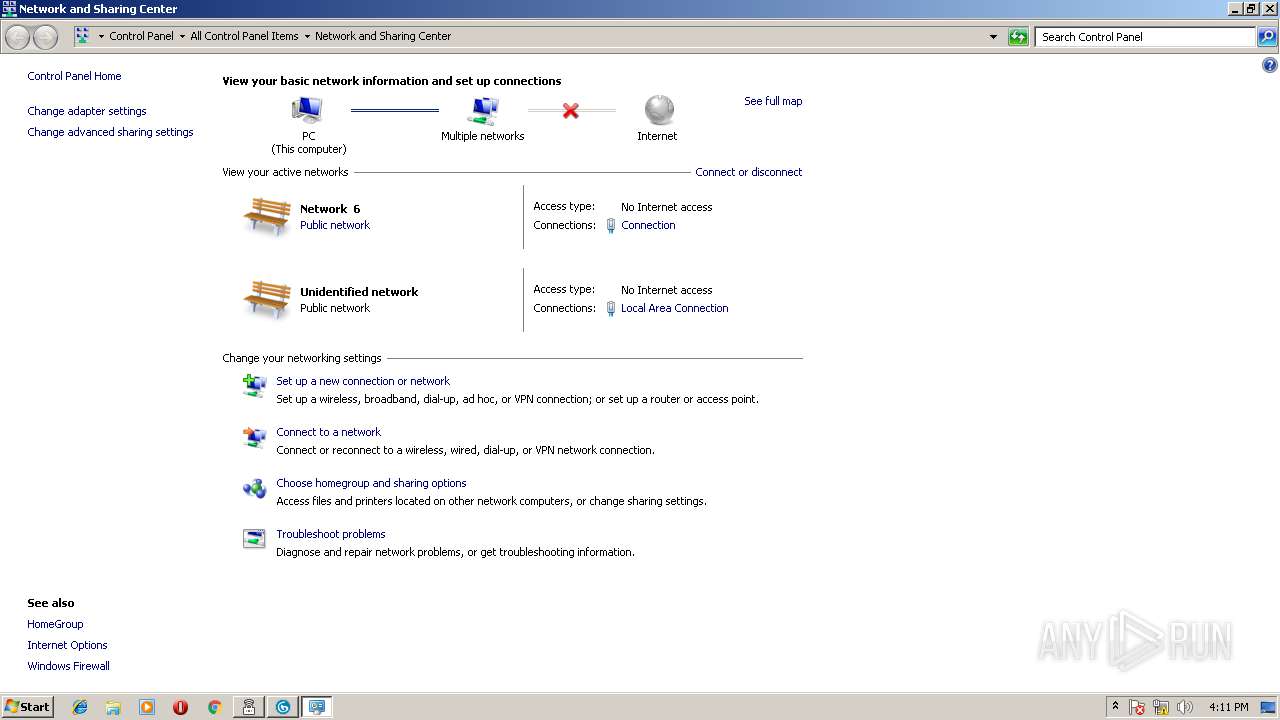
Starts Internet Explorer
- cleanspace.exe (PID: 1524)
- cleanspace.exe (PID: 2272)
Low-level read access rights to disk partition
- ksde.exe (PID: 804)
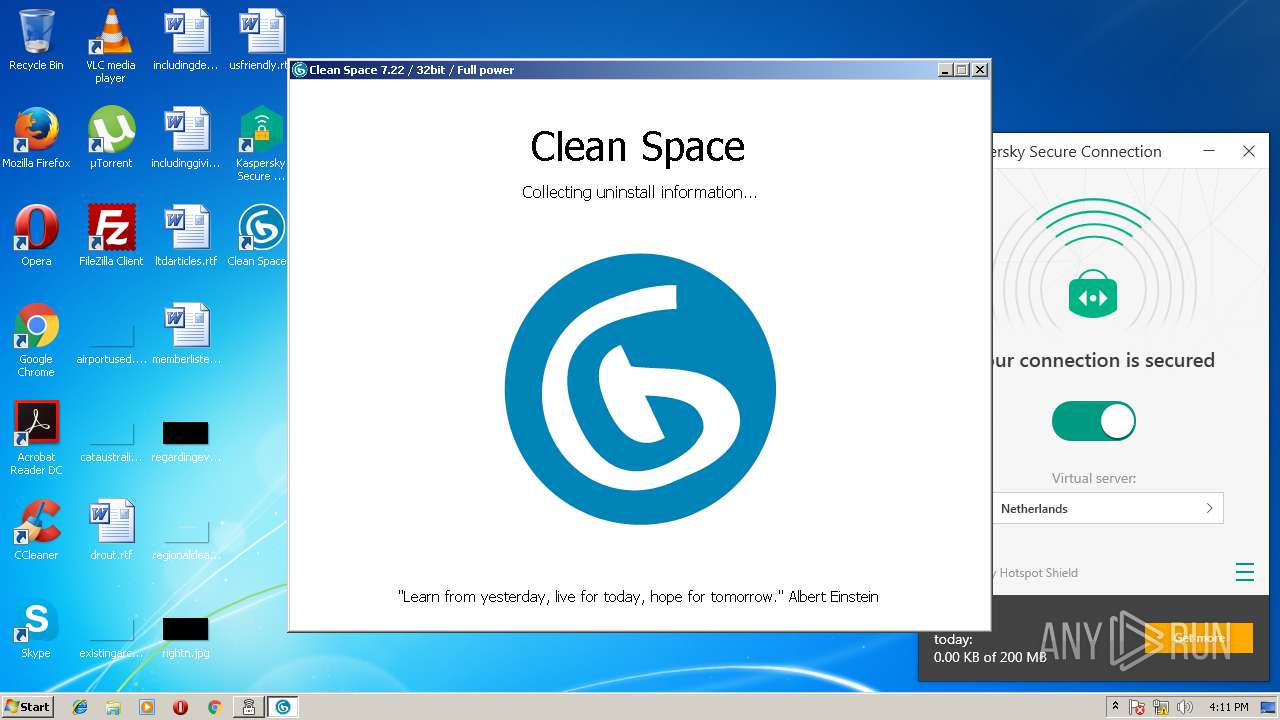
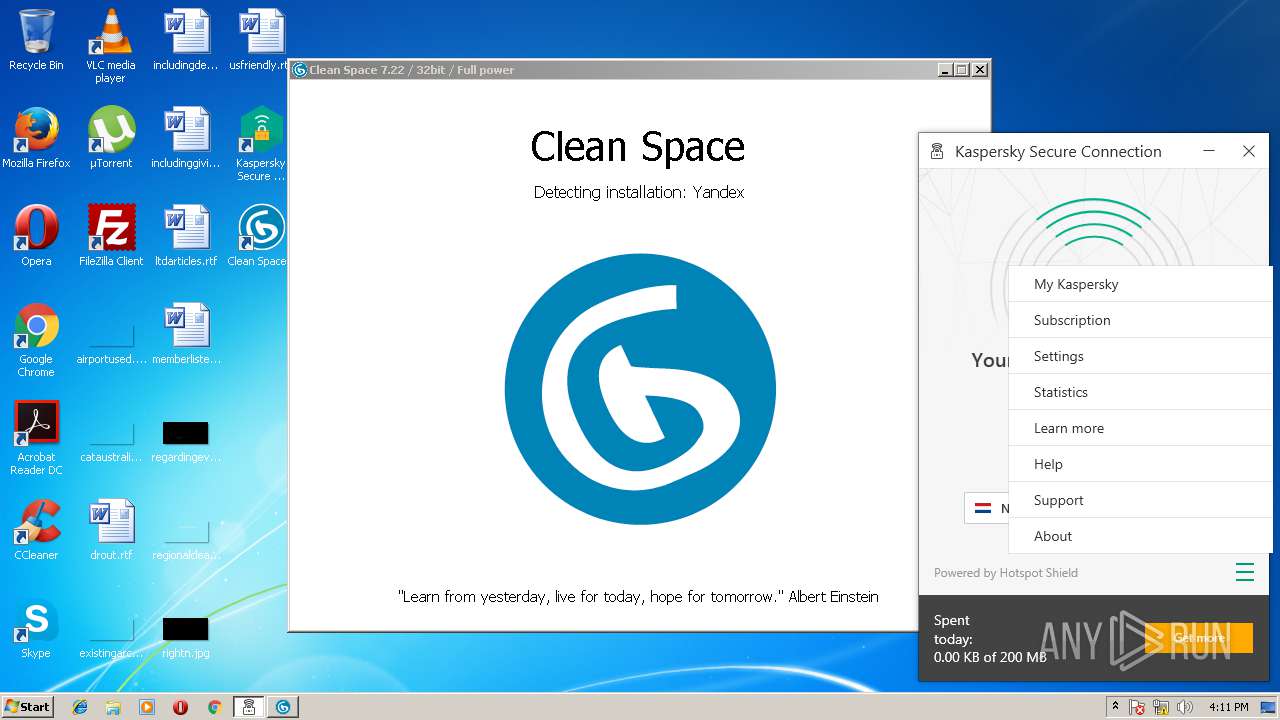
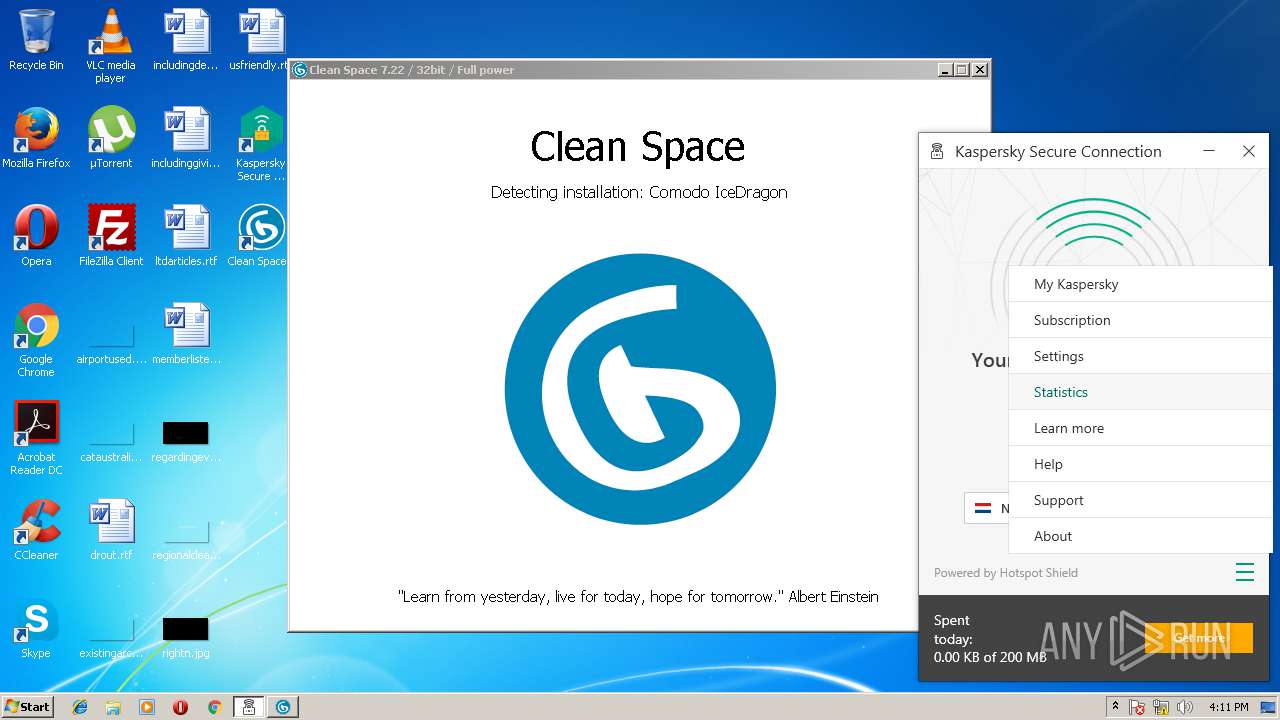
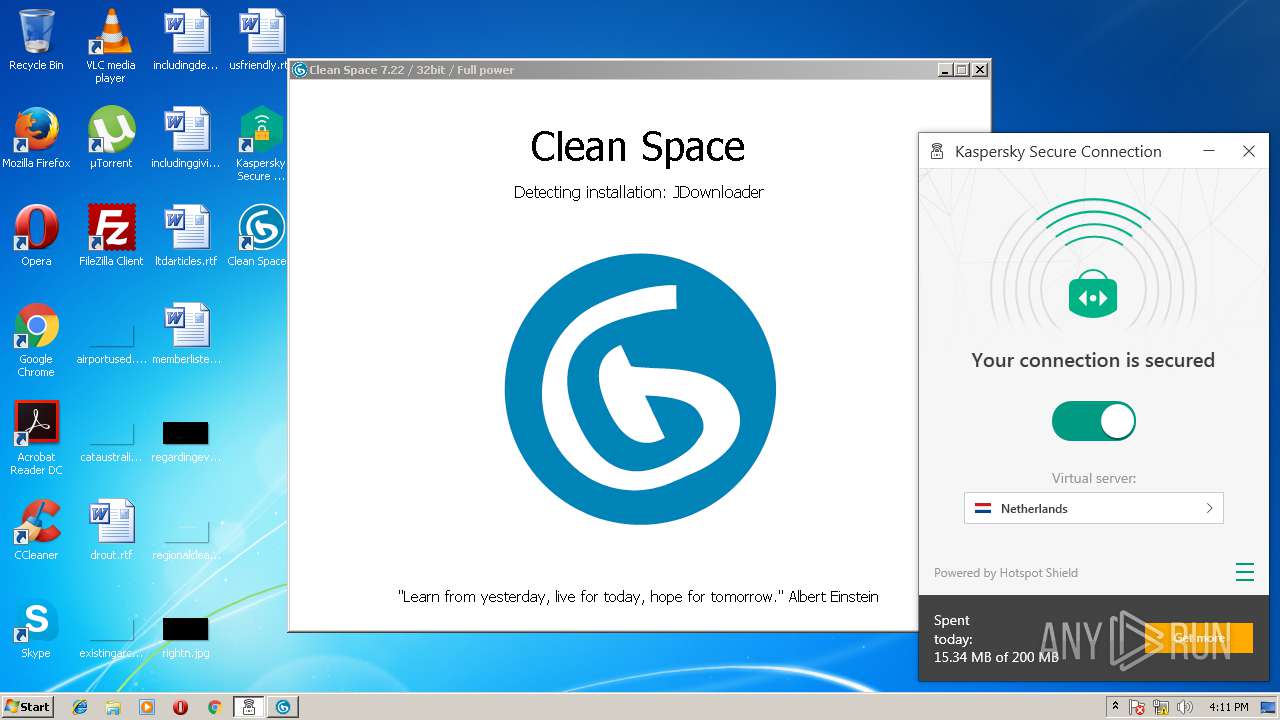
Searches for installed software
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 4080)
INFO
Reads settings of System Certificates
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
Dropped object may contain URL's
- ksde19.0.0.1088_en-gb_full.exe (PID: 3924)
- ksde19.0.0.1088_en-gb_full.exe (PID: 3500)
- DrvInst.exe (PID: 1508)
- DrvInst.exe (PID: 1516)
- msiexec.exe (PID: 4076)
- clnspc_7_22.tmp (PID: 1488)
- chrome.exe (PID: 4016)
- MsiExec.exe (PID: 2120)
- iexplore.exe (PID: 2668)
- iexplore.exe (PID: 1896)
- iexplore.exe (PID: 2796)
- cleanspace.exe (PID: 3820)
- cleanspace.exe (PID: 4080)
Application launched itself
- msiexec.exe (PID: 4076)
- chrome.exe (PID: 4016)
- iexplore.exe (PID: 628)
Creates files in the program directory
- msiexec.exe (PID: 4076)
- MsiExec.exe (PID: 3712)
- MsiExec.exe (PID: 2120)
- clnspc_7_22.tmp (PID: 1488)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3712)
- MsiExec.exe (PID: 2120)
- msiexec.exe (PID: 4076)
- clnspc_7_22.tmp (PID: 1488)
Dropped object may contain Bitcoin addresses
- MsiExec.exe (PID: 2120)
Creates a software uninstall entry
- msiexec.exe (PID: 4076)
- clnspc_7_22.tmp (PID: 1488)
Changes settings of System certificates
- chrome.exe (PID: 4016)
- iexplore.exe (PID: 2668)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3112)
Reads Internet Cache Settings
- chrome.exe (PID: 4016)
- iexplore.exe (PID: 2668)
- iexplore.exe (PID: 2796)
Application was dropped or rewritten from another process
- clnspc_7_22.tmp (PID: 2288)
- clnspc_7_22.tmp (PID: 1488)
Changes internet zones settings
- iexplore.exe (PID: 1896)
- iexplore.exe (PID: 628)
Creates files in the user directory
- iexplore.exe (PID: 2668)
Reads internet explorer settings
- iexplore.exe (PID: 2668)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:28 21:21:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 187392 |
| InitializedDataSize: | 16733696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3009 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.1088 |
| ProductVersionNumber: | 19.0.0.1088 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Kaspersky Lab |
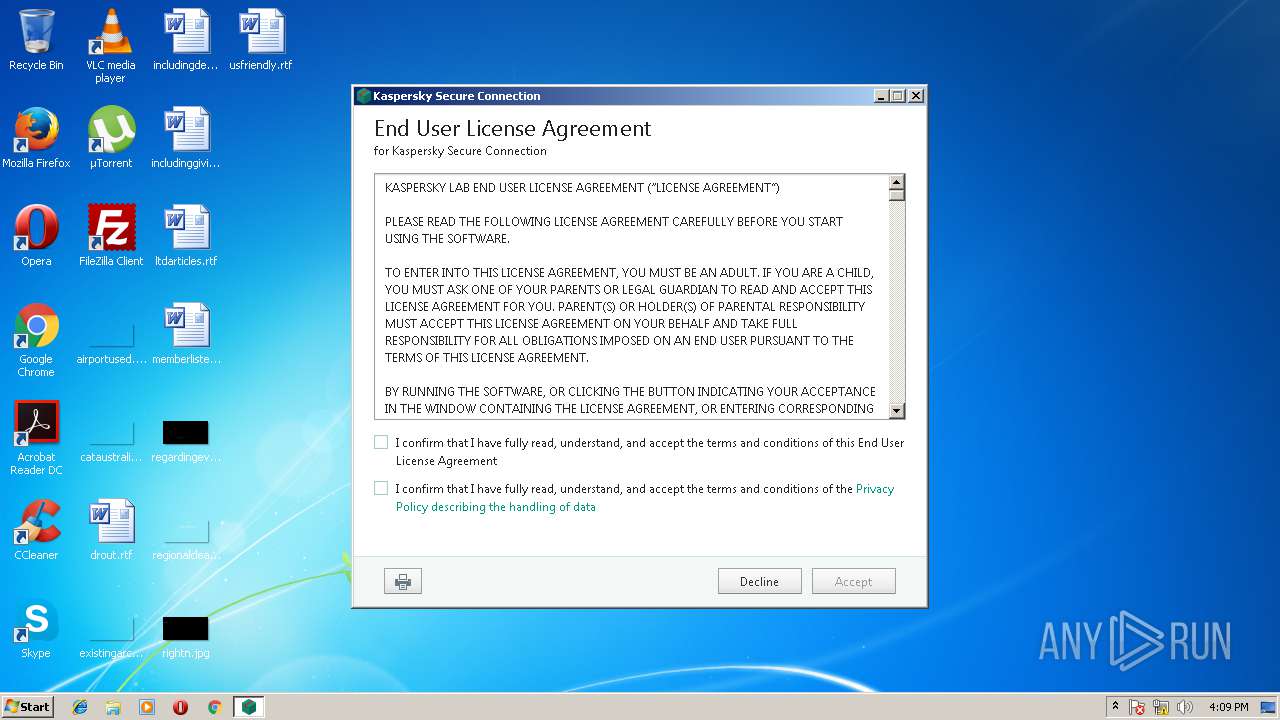
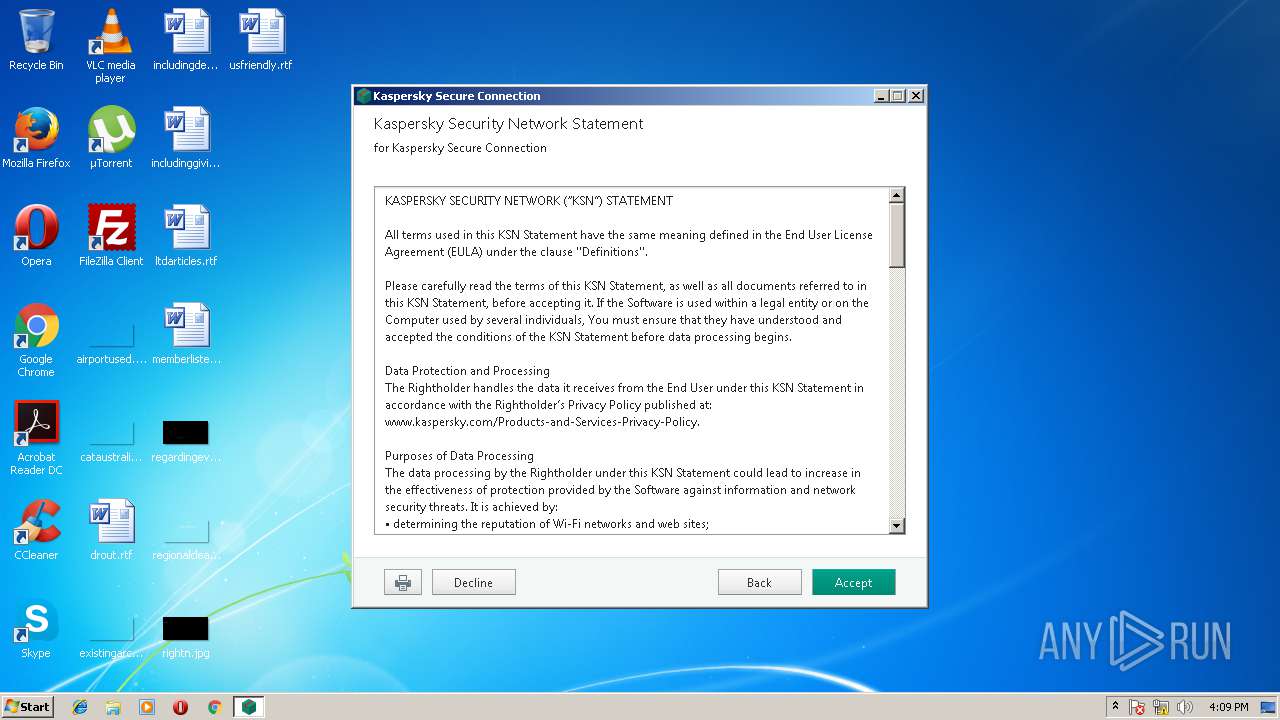
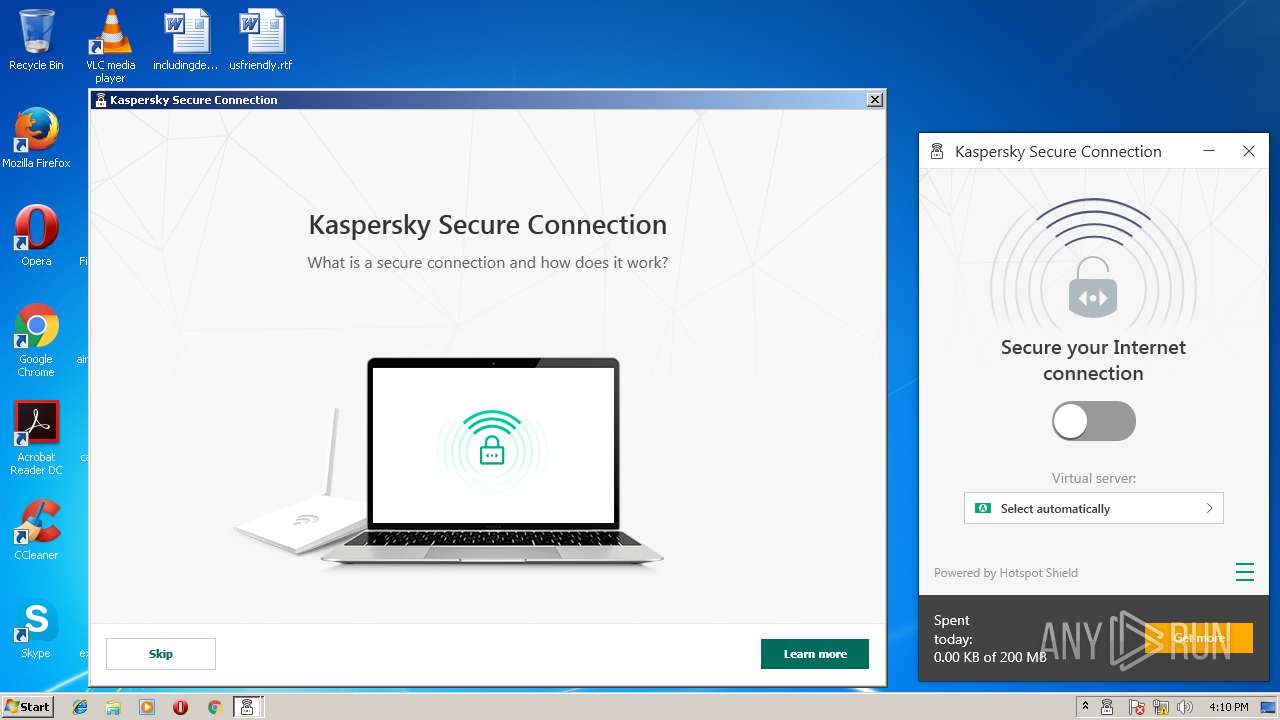
| FileDescription: | Kaspersky Secure Connection [19.0.0.1088.0.56.0] |
| FileVersion: | 19.0.0.1088 |
| LegalCopyright: | © 2018 AO Kaspersky Lab. All Rights Reserved. |
| LegalTrademarks: | Registered trademarks and service marks are the property of their respective owners |
| ProductName: | Kaspersky Secure Connection |
| ProductVersion: | 19.0.0.1088 |
| InternalName: | Setup |
| OriginalFileName: | Setup.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2018 20:21:57 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Kaspersky Lab |
| FileDescription: | Kaspersky Secure Connection [19.0.0.1088.0.56.0] |
| FileVersion: | 19.0.0.1088 |
| LegalCopyright: | © 2018 AO Kaspersky Lab. All Rights Reserved. |
| LegalTrademarks: | Registered trademarks and service marks are the property of their respective owners |
| ProductName: | Kaspersky Secure Connection |
| ProductVersion: | 19.0.0.1088 |
| InternalName: | Setup |
| OriginalFilename: | Setup.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 28-Feb-2018 20:21:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DA69 | 0x0002DC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66643 |
.rdata | 0x0002F000 | 0x0000FC8E | 0x0000FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.46821 |
.data | 0x0003F000 | 0x00004064 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.39849 |
.gfids | 0x00044000 | 0x00000228 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.41875 |
.rsrc | 0x00045000 | 0x00FE1E00 | 0x00FE1E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9977 |
.reloc | 0x01027000 | 0x00002730 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54398 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28788 | 1351 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.19556 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.04315 | 1736 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 2.40839 | 1384 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 3.09332 | 174 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
6 | 3.50356 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 4.14647 | 38056 | Latin 1 / Western European | Process Default Language | RT_ICON |
8 | 3.77256 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
9 | 3.89914 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
10 | 4.15612 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
Imports
KERNEL32.dll |
RPCRT4.dll (delay-loaded) |
Total processes
92
Monitored processes
41
Malicious processes
18
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Clean Space 7\cleanspace.exe" | C:\Program Files\Clean Space 7\cleanspace.exe | explorer.exe | ||||||||||||
User: admin Company: CyRobo S.R.O. Integrity Level: MEDIUM Description: Clean Space Exit code: 0 Version: 7.22.0.0 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | cleanspace.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 804 | "C:\Program Files\Kaspersky Lab\Kaspersky Secure Connection 3.0\ksde.exe" -r | C:\Program Files\Kaspersky Lab\Kaspersky Secure Connection 3.0\ksde.exe | services.exe | ||||||||||||
User: SYSTEM Company: AO Kaspersky Lab Integrity Level: SYSTEM Description: Kaspersky Secure Connection Exit code: 0 Version: 19.0.0.1088 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\Downloads\clnspc_7_22.exe" | C:\Users\admin\Downloads\clnspc_7_22.exe | chrome.exe | ||||||||||||
User: admin Company: CYROBO S.R.O. Integrity Level: MEDIUM Description: Clean Space Setup Exit code: 0 Version: 7.22 Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\AppData\Local\Temp\is-CU71S.tmp\clnspc_7_22.tmp" /SL5="$9021E,14252342,299008,C:\Users\admin\Downloads\clnspc_7_22.exe" /SPAWNWND=$60246 /NOTIFYWND=$A01E0 | C:\Users\admin\AppData\Local\Temp\is-CU71S.tmp\clnspc_7_22.tmp | clnspc_7_22.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1508 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "kltap.inf:kltap:kltap.ndi:15.59.46.455:kltap" "6a39d1357" "0000057C" "000005EC" "000005F0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{1ad4655a-56fa-1075-cd4a-756c9e31847a}\kltap.inf" "0" "6a39d1357" "0000057C" "WinSta0\Default" "000005D4" "208" "c:\program files\kaspersky lab\kaspersky secure connection 3.0\kltapx86\600" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=23.129.0 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0x118c42c,0x118c43c,0x118c44c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 23.129.0 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Clean Space 7\cleanspace.exe" protocol12 | C:\Program Files\Clean Space 7\cleanspace.exe | clnspc_7_22.tmp | ||||||||||||
User: admin Company: CyRobo S.R.O. Integrity Level: HIGH Description: Clean Space Exit code: 0 Version: 7.22.0.0 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1596,4118943770188030738,4074117580293782379,131072 --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=9,12,13,22,23,24,27,49,84 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-accelerated-video-decode --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --service-request-channel-token=E5F97802642106D815CD742273366DF9 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
42 604
Read events
39 952
Write events
2 556
Delete events
96
Modification events
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | Enable Browser Extensions |
Value: no | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | UseSWRender |
Value: 1 | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\SetupKSDE19.0.0.1088.0.56.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\KSDE19.0.0.1088.0.56.0
| |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\SetupKSDE19.0.0.1088.0.56.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\KSDE19.0.0.1088.0.56.0
C:\ProgramData\Kaspersky Lab Setup Files
| |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060420180605 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018060420180605 | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060420180605 |
| Operation: | write | Name: | CachePrefix |
Value: :2018060420180605: | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060420180605 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (3924) ksde19.0.0.1088_en-gb_full.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060420180605 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
Executable files
138
Suspicious files
240
Text files
634
Unknown types
175
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Cab244F.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Tar2460.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Cab2461.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Tar2462.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Cab254D.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Tar254E.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Cab257E.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Tar257F.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Cab25ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | ksde19.0.0.1088_en-gb_full.exe | C:\Users\admin\AppData\Local\Temp\Tar25EE.tmp | — | |
MD5:— | SHA256:— | |||
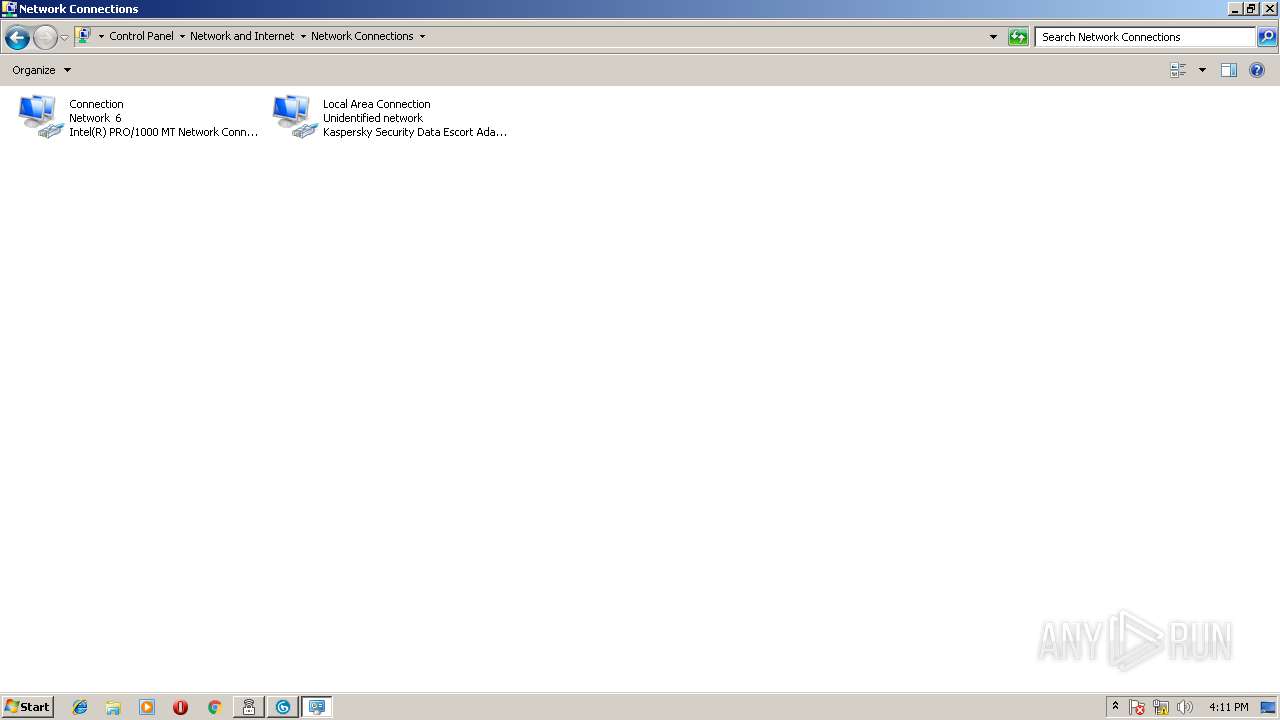
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3924 | ksde19.0.0.1088_en-gb_full.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3924 | ksde19.0.0.1088_en-gb_full.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3924 | ksde19.0.0.1088_en-gb_full.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3924 | ksde19.0.0.1088_en-gb_full.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3924 | ksde19.0.0.1088_en-gb_full.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
804 | ksde.exe | 40.85.136.68:443 | sdeconfig.kaspersky-labs.com | Microsoft Corporation | IE | whitelisted |
3924 | ksde19.0.0.1088_en-gb_full.exe | 195.122.169.10:443 | dm.s.kaspersky-labs.com | Level 3 Communications, Inc. | GB | suspicious |
3924 | ksde19.0.0.1088_en-gb_full.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
804 | ksde.exe | 13.32.210.200:443 | dt4oxny0f90is.cloudfront.net | Amazon.com, Inc. | US | unknown |
804 | ksde.exe | 77.74.181.28:443 | ksn-crypto-stat-geo.kaspersky-labs.com | Kaspersky Lab AO | RU | unknown |
804 | ksde.exe | 62.128.100.47:443 | ksn-crypto-stat-geo.kaspersky-labs.com | Linx Telecommunications B.V. | RU | unknown |
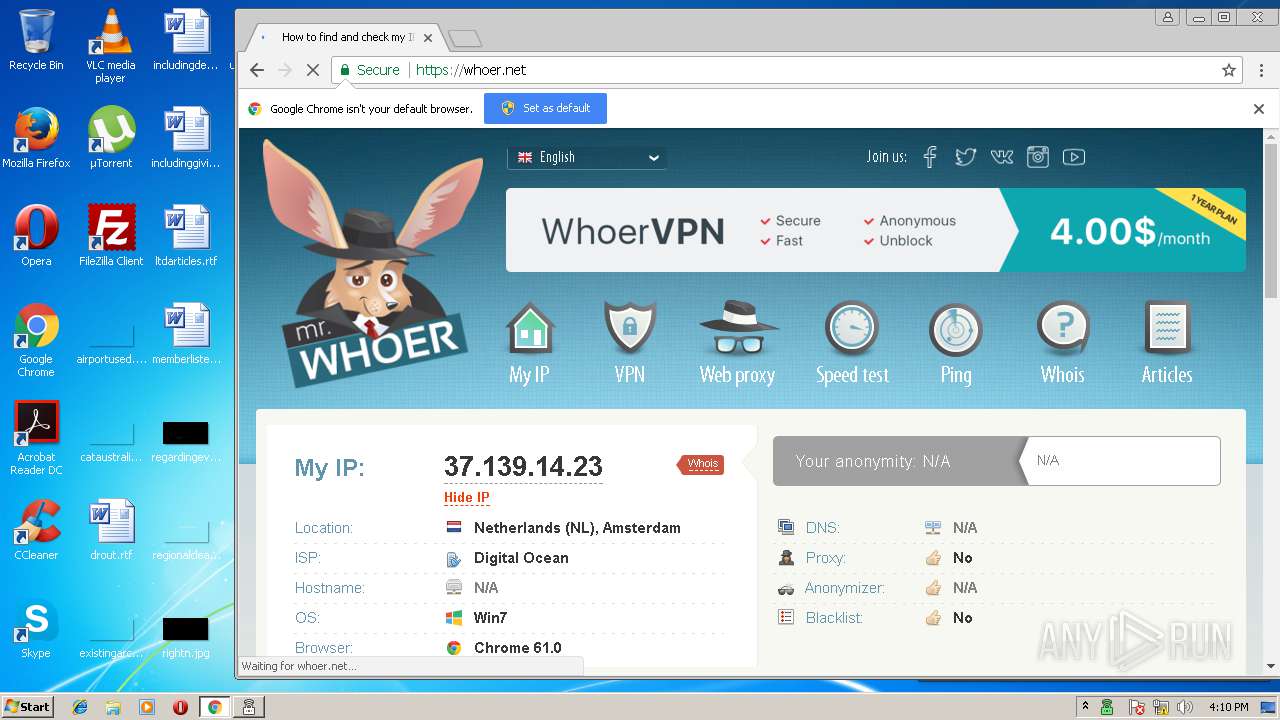
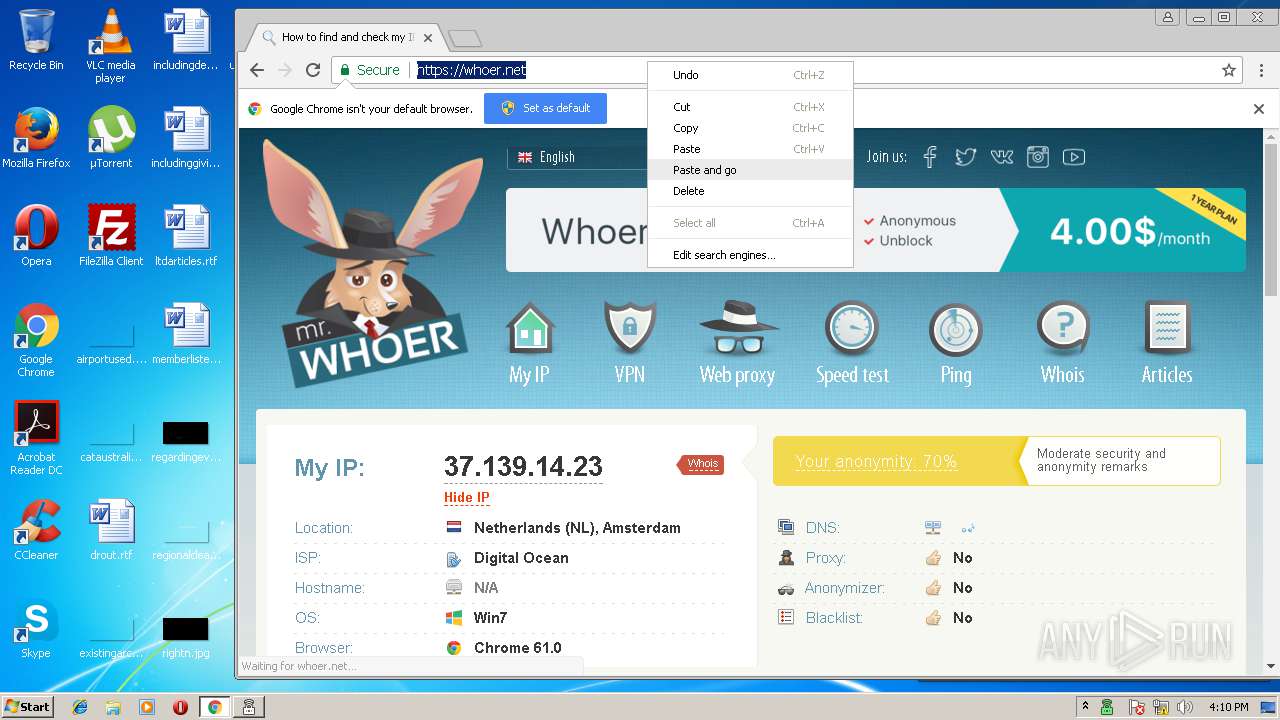
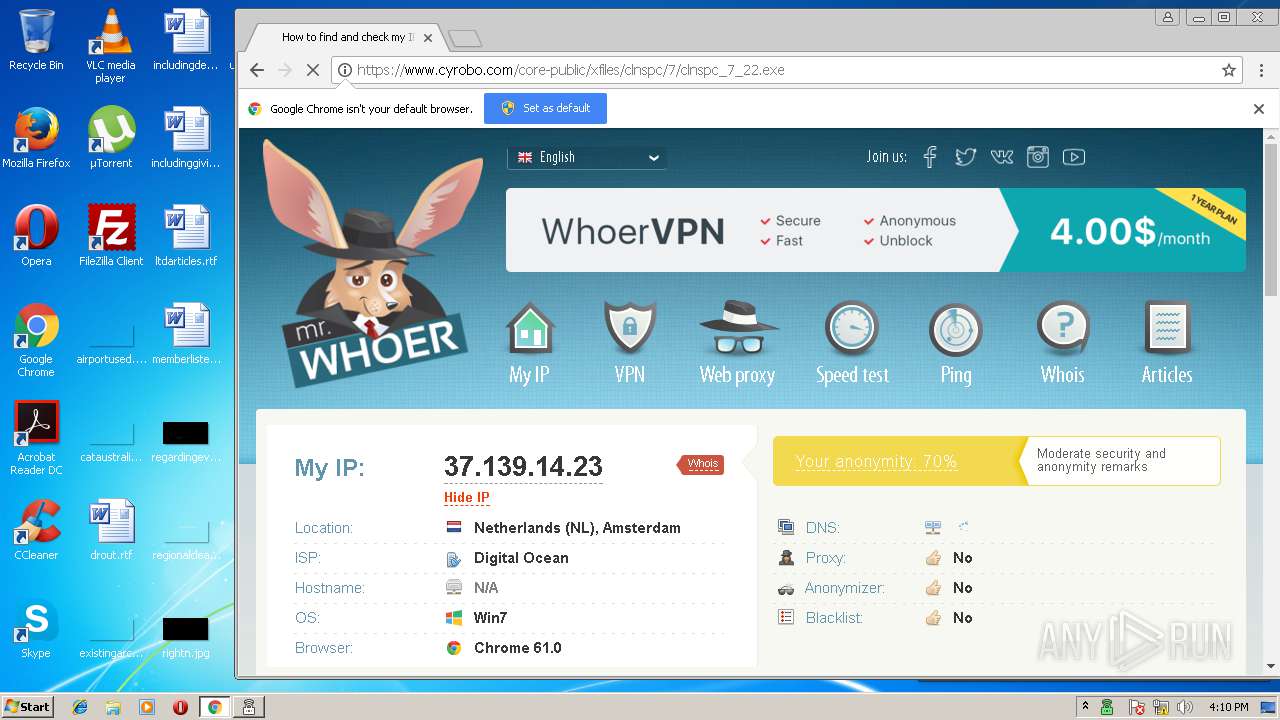
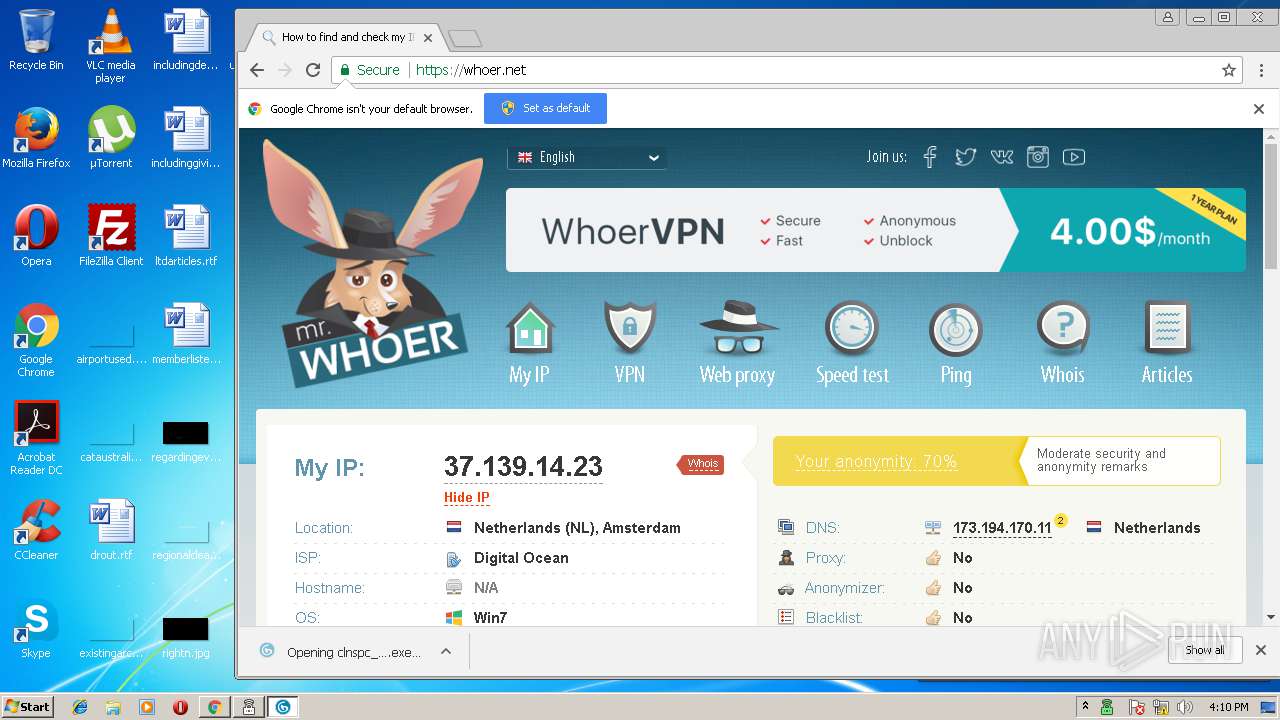
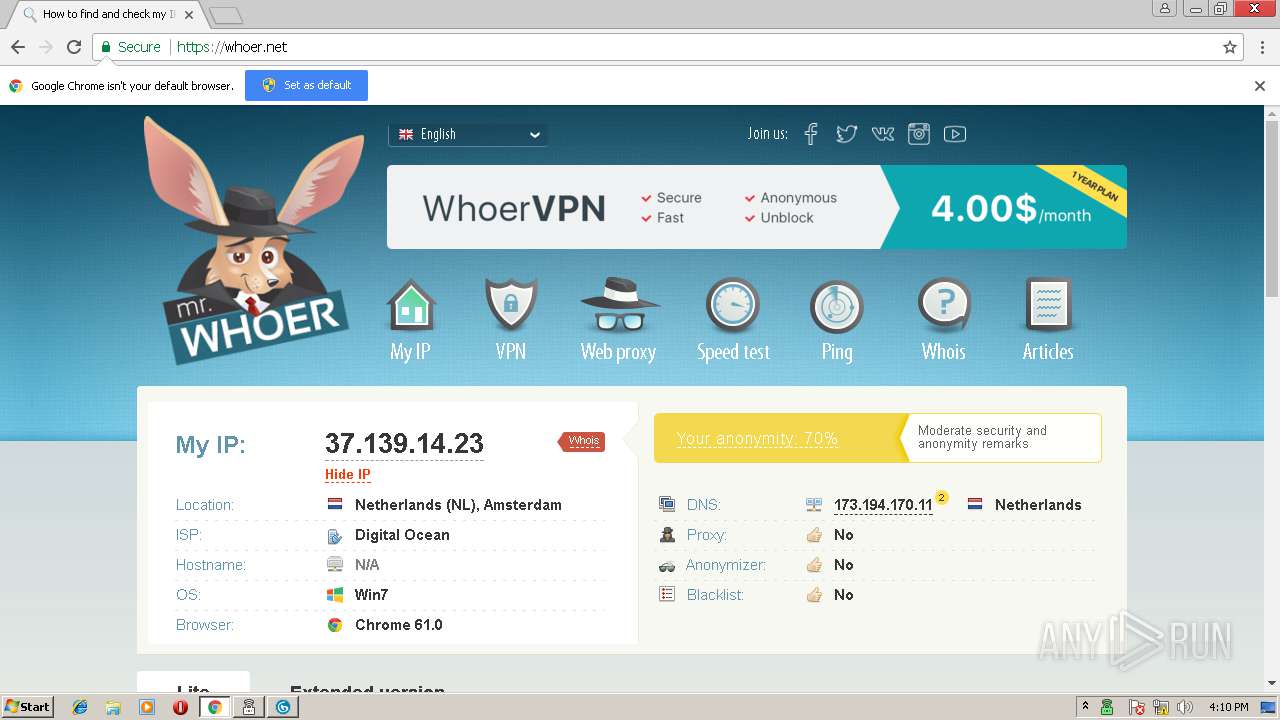
804 | ksde.exe | 37.139.14.23:443 | — | Digital Ocean, Inc. | NL | unknown |
3500 | ksde19.0.0.1088_en-gb_full.exe | 62.128.100.206:443 | ksn-stat-install.kaspersky-labs.com | Linx Telecommunications B.V. | RU | unknown |
804 | ksde.exe | 37.48.82.67:80 | dnl-02.geo.kaspersky.com | LeaseWeb Netherlands B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dm.s.kaspersky-labs.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
ksn-stat-install.kaspersky-labs.com |
| suspicious |
dnl-02.geo.kaspersky.com |
| malicious |
sdeconfig.kaspersky-labs.com |
| whitelisted |
dt4oxny0f90is.cloudfront.net |
| whitelisted |
ksn-crypto-stat-geo.kaspersky-labs.com |
| unknown |
teredo.ipv6.microsoft.com |
| whitelisted |
ksn-crypto-tcert-geo.kaspersky-labs.com |
| suspicious |
ksn-crypto-wifiplus-geo.kas-labs.com |
| unknown |
Threats
Process | Message |
|---|---|
MsiExec.exe | Service: |
MsiExec.exe | Service: |
MsiExec.exe | KSDE3.0.0 |
MsiExec.exe | |
MsiExec.exe | Group: |
MsiExec.exe | <default> |
MsiExec.exe | |
MsiExec.exe | SetServiceDACL succeeded
|
ksdeui.exe | |
ksdeui.exe | |