| URL: | http://servebeer.com |
| Full analysis: | https://app.any.run/tasks/3a062213-480d-4342-a5c5-aaba9ef51ec5 |
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2021, 13:30:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E27CD5CC202CDF9528C19B995EEE6D92 |
| SHA1: | 91A0FFCACCB4BC93BF75CC42F1F3A8585C860A8F |
| SHA256: | 1640D7EDB4C38D5370D01B96100D57FC96C804099A803B5BDFE9B58A281C66AC |
| SSDEEP: | 3:N1KNAXGN2n:CSy2n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1020)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3176)
Checks supported languages
- iexplore.exe (PID: 1020)
- iexplore.exe (PID: 3176)
Reads the computer name
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1020)
Application launched itself
- iexplore.exe (PID: 3176)
Reads settings of System Certificates
- iexplore.exe (PID: 1020)
- iexplore.exe (PID: 3176)
Checks Windows Trust Settings
- iexplore.exe (PID: 1020)
- iexplore.exe (PID: 3176)
Creates files in the user directory
- iexplore.exe (PID: 1020)
Reads internet explorer settings
- iexplore.exe (PID: 1020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3176 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://servebeer.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 976
Read events
4 790
Write events
186
Delete events
0
Modification events
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30916662 | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30916662 | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
11
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\6xKydSBYKcSV-LCoeQqfX1RYOo3i54rwlxdo[1].woff | — | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\6xKydSBYKcSV-LCoeQqfX1RYOo3ik4zwlxdo[1].woff | — | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\3SB08SVV.htm | html | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8HTT5JFY.txt | text | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\memSYaGs126MiZpBA-UvWbX2vVnXBbObj2OVZyOOSr4dVJWUgsiH0B4gaVQ[1].woff | — | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PNG2C3PE.txt | text | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3S2CEZUX.txt | text | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\shortstar[1].css | text | |
MD5:— | SHA256:— | |||
| 1020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\shortstar[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
145
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1020 | iexplore.exe | GET | 301 | 8.23.224.108:80 | http://servebeer.com/ | US | — | — | suspicious |
1020 | iexplore.exe | GET | 301 | 172.217.18.110:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | — | — | whitelisted |
1020 | iexplore.exe | GET | 200 | 18.66.242.64:80 | http://d2np5nlsc31ci5.cloudfront.net/assets/build/css/shortstar.css?id=aa47fdabaf8e1d9e87fe | US | text | 82.3 Kb | whitelisted |
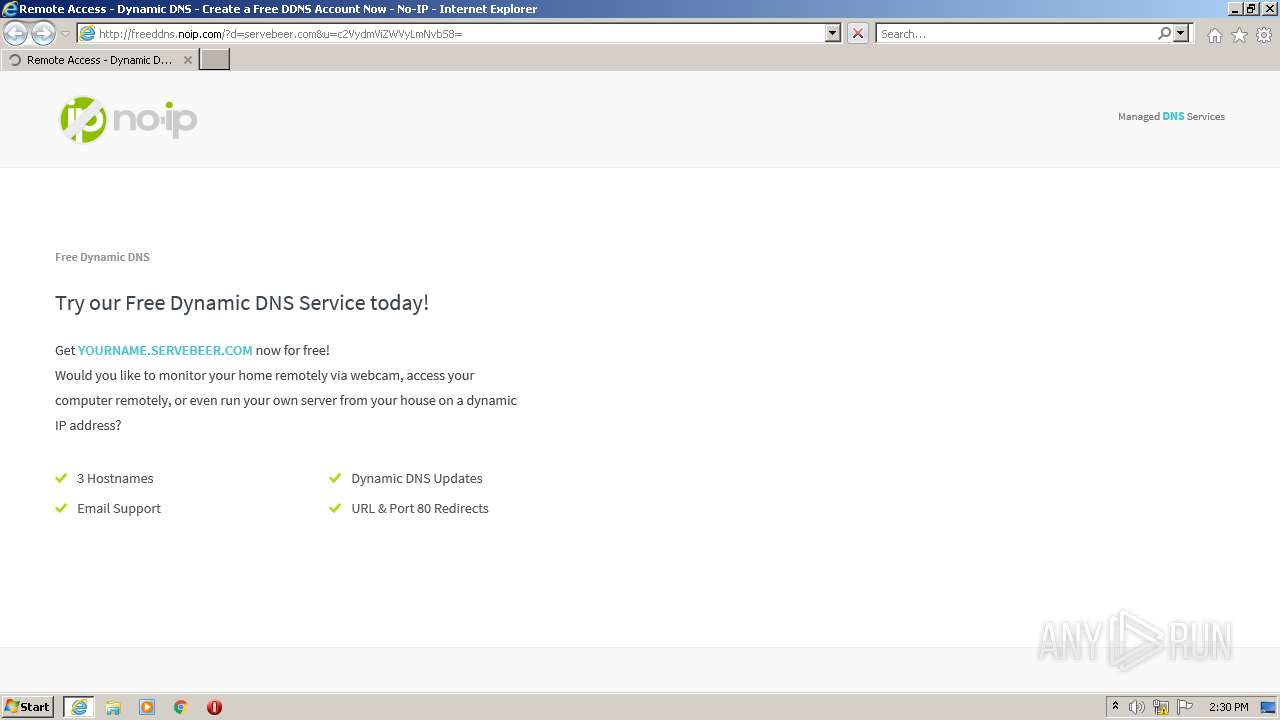
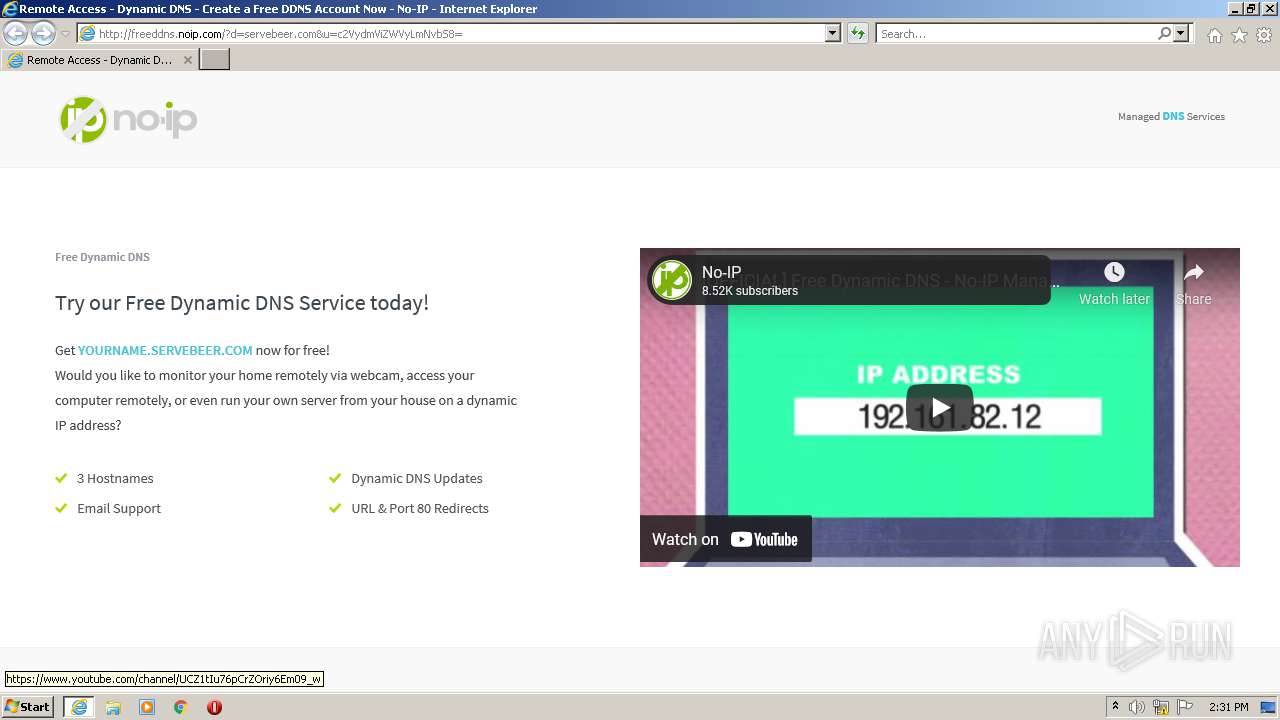
1020 | iexplore.exe | GET | 200 | 8.23.224.108:80 | http://freeddns.noip.com/?d=servebeer.com&u=c2VydmViZWVyLmNvbS8= | US | html | 12.6 Kb | suspicious |
1020 | iexplore.exe | GET | 200 | 18.66.242.64:80 | http://d2np5nlsc31ci5.cloudfront.net/assets/build/js/shortstar.js?id=57e6b0602fcdf4276226 | US | text | 70.8 Kb | whitelisted |
1020 | iexplore.exe | GET | 200 | 142.250.185.162:80 | http://www.googleadservices.com/pagead/conversion.js | US | text | 17.2 Kb | whitelisted |
1020 | iexplore.exe | GET | 200 | 142.250.185.170:80 | http://fonts.googleapis.com/css?family=Source+Sans+Pro:300,400,600,700|Open+Sans:400,300,600,700|Dosis:300,400|Roboto+Slab:400 | US | text | 457 b | whitelisted |
1020 | iexplore.exe | GET | 200 | 104.18.10.207:80 | http://maxcdn.bootstrapcdn.com/font-awesome/4.7.0/css/font-awesome.min.css | US | text | 7.62 Kb | whitelisted |
1020 | iexplore.exe | GET | 200 | 18.66.242.64:80 | http://d2np5nlsc31ci5.cloudfront.net/assets/img/logo/logo-grey.png | US | image | 1.52 Kb | whitelisted |
1020 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://fonts.gstatic.com/s/sourcesanspro/v14/6xKydSBYKcSV-LCoeQqfX1RYOo3ik4zwlxdo.woff | US | woff | 19.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1020 | iexplore.exe | 8.23.224.108:80 | servebeer.com | Vitalwerks Internet Solutions, LLC | US | suspicious |
1020 | iexplore.exe | 13.224.193.102:443 | perfalytics.com | — | US | suspicious |
1020 | iexplore.exe | 142.250.184.232:80 | www.googletagmanager.com | Google Inc. | US | suspicious |
1020 | iexplore.exe | 142.250.184.232:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1020 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1020 | iexplore.exe | 142.250.185.162:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
— | — | 20.73.194.208:443 | — | — | US | whitelisted |
1020 | iexplore.exe | 142.250.185.162:80 | www.googleadservices.com | Google Inc. | US | whitelisted |
1020 | iexplore.exe | 18.66.242.64:80 | d2np5nlsc31ci5.cloudfront.net | Massachusetts Institute of Technology | US | whitelisted |
1020 | iexplore.exe | 172.217.18.110:80 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
servebeer.com |
| suspicious |
freeddns.noip.com |
| suspicious |
d2np5nlsc31ci5.cloudfront.net |
| whitelisted |
www.googleadservices.com |
| whitelisted |
translate.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |