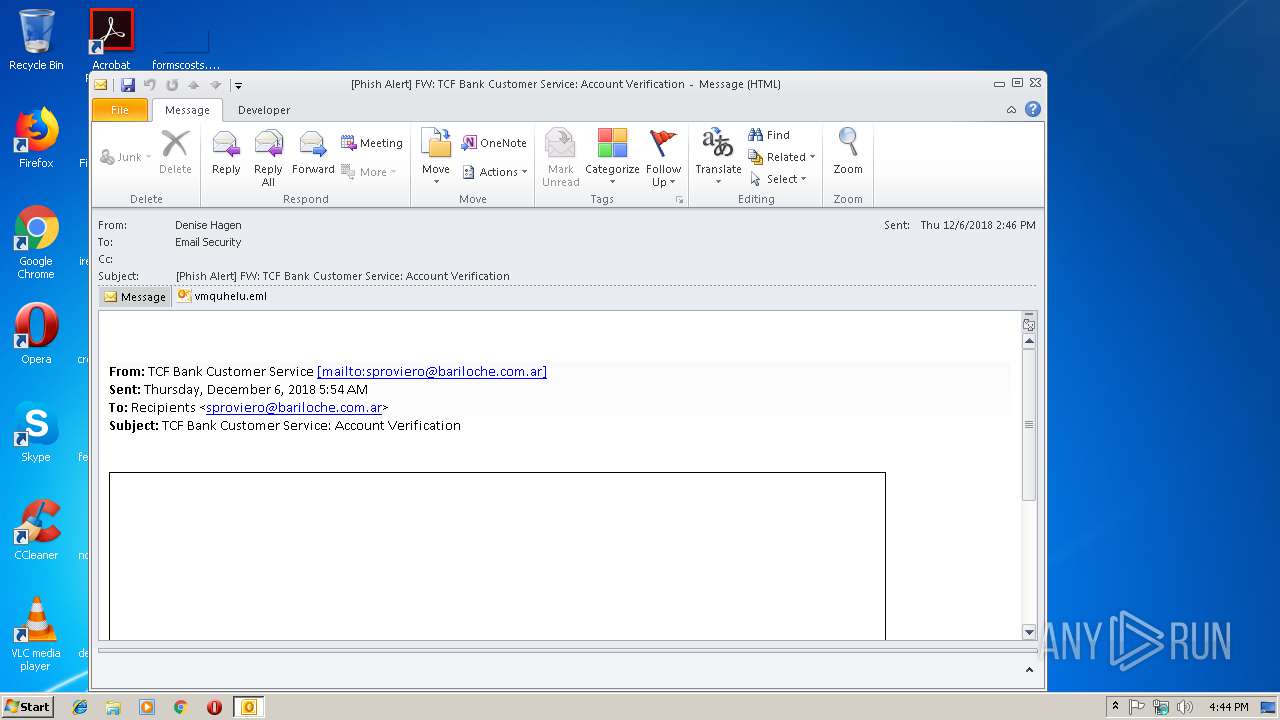
| File name: | TCF Bank Customer Service Account Verification.msg |
| Full analysis: | https://app.any.run/tasks/51bf86f7-2b7d-43a9-a3c2-42f996afe2ab |
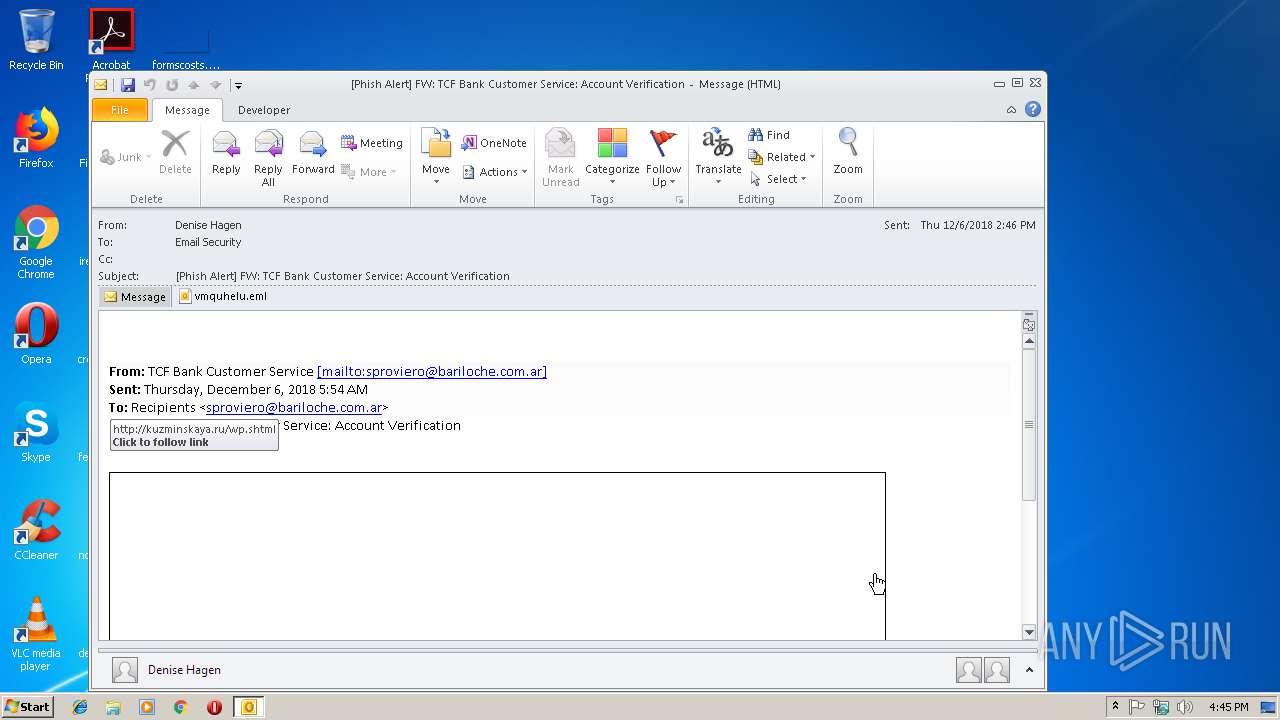
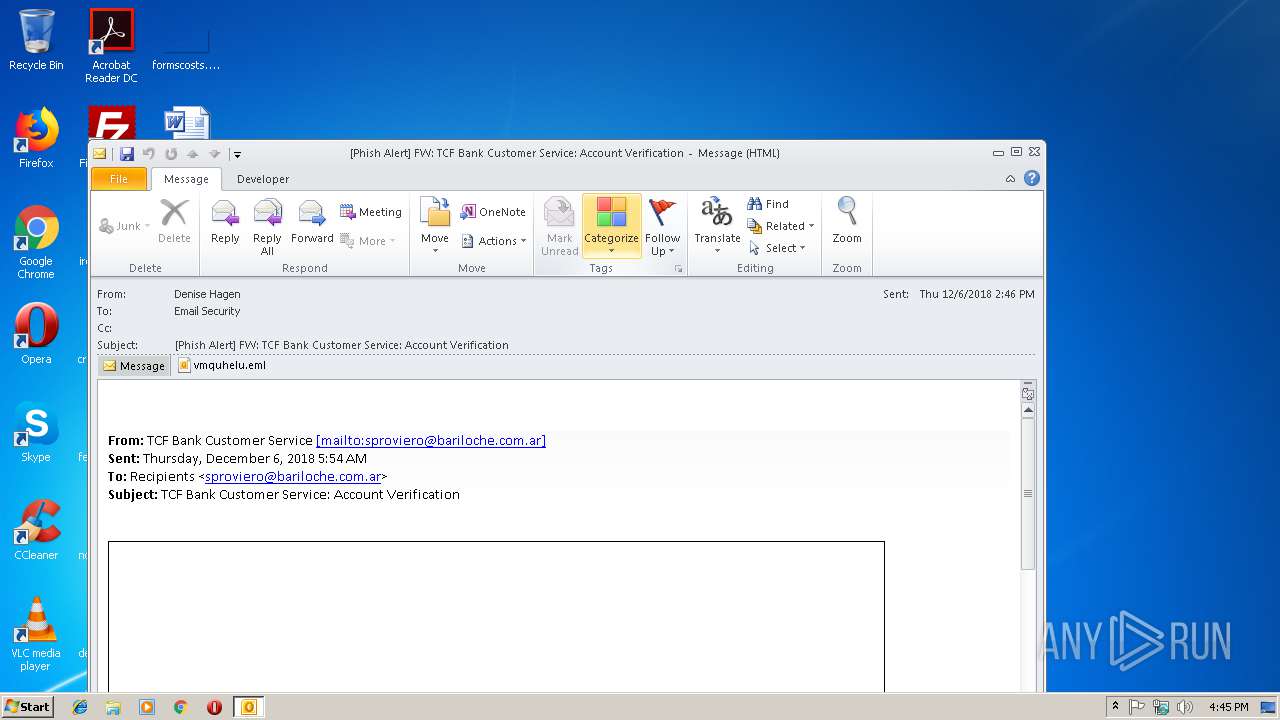
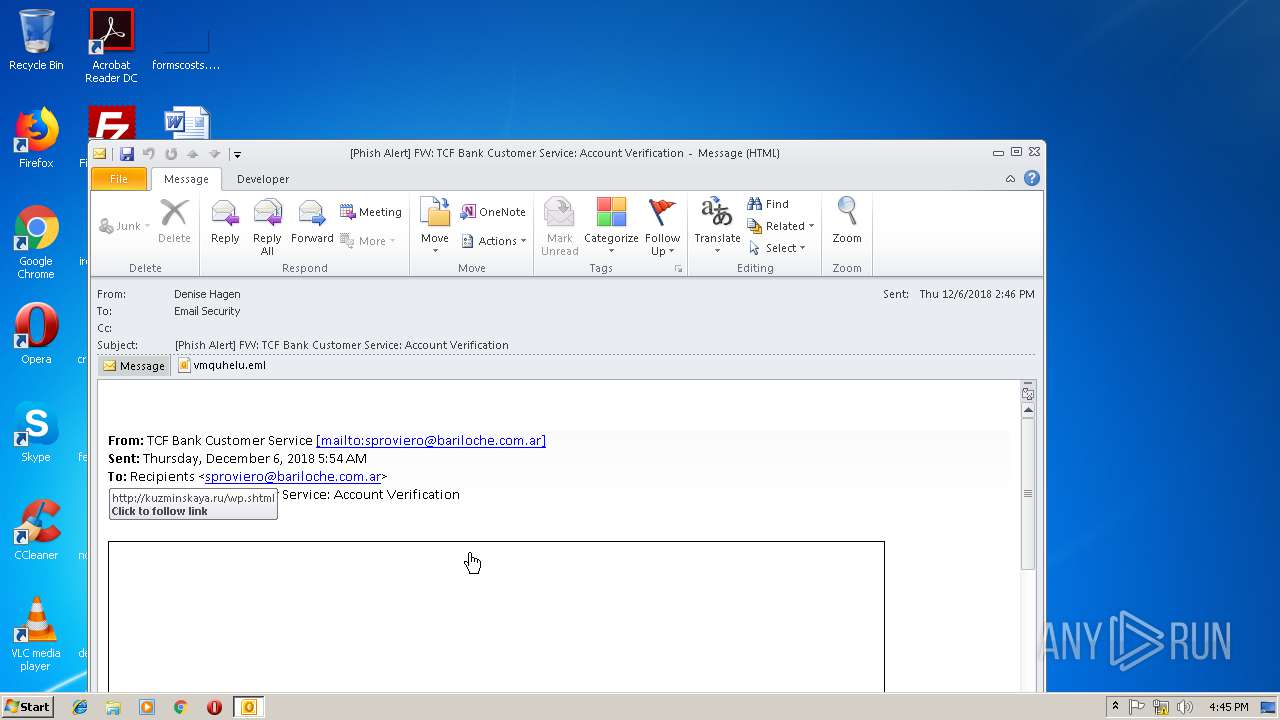
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 16:44:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | F519466A9F84D7AB5DA3DFB244DEF800 |
| SHA1: | E7300390AE1BB2C188D16B4BCCF562C2F4F4382B |
| SHA256: | 1624FE96189CB7A58E75013CEB45F7ED909C9070F3D89038241BDCAA08082EC1 |
| SSDEEP: | 3072:7Fp9Dp9OIl3fyjjjjjjjjj4tcssxzGtpn/mqDZvzu1+9nyEtOOZIXh+sdssct4jK:z9Dp9OIl3fyjjjjjjjjj4tcssxzGtpnR |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2812)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2812)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2812)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2812)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3164)
Application launched itself
- iexplore.exe (PID: 3164)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3616)
- iexplore.exe (PID: 1328)
Reads internet explorer settings
- iexplore.exe (PID: 1328)
Reads Internet Cache Settings
- iexplore.exe (PID: 1328)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2812)
Reads settings of System Certificates
- iexplore.exe (PID: 3164)
Changes settings of System certificates
- iexplore.exe (PID: 3164)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3164 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\TCF Bank Customer Service Account Verification.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
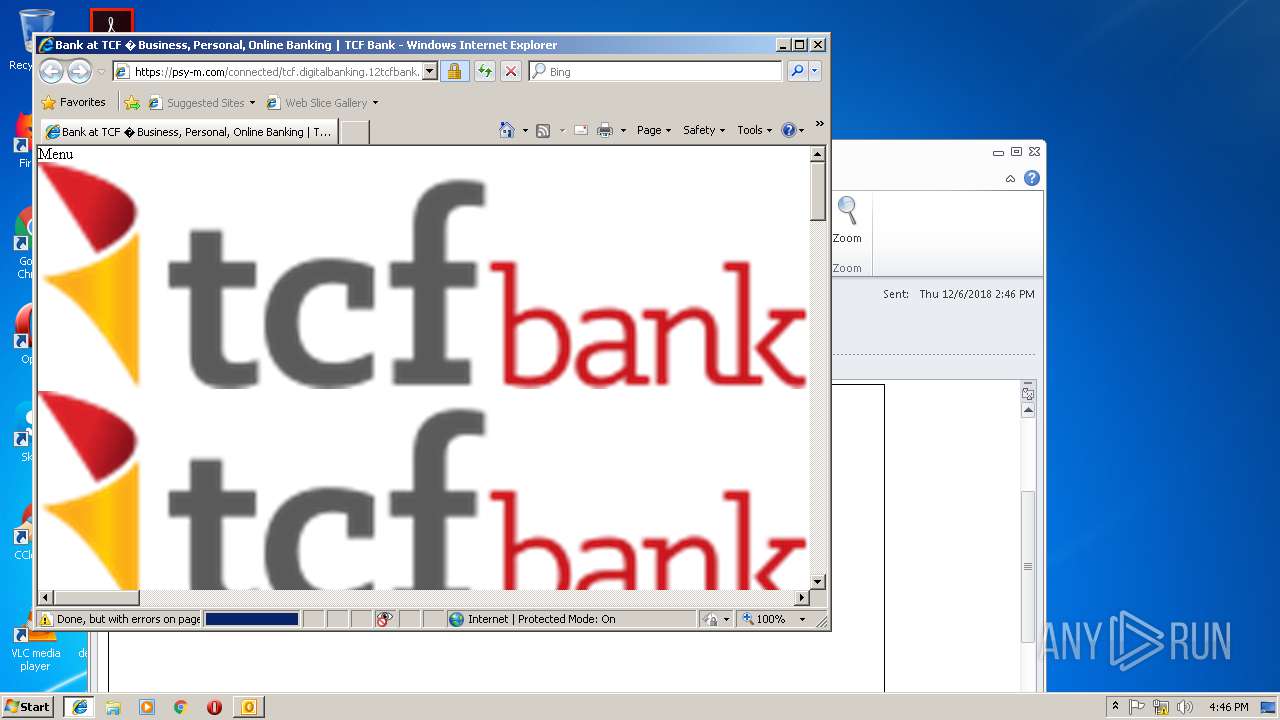
| 3164 | "C:\Program Files\Internet Explorer\iexplore.exe" http://kuzminskaya.ru/wp.shtml | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
1 882
Read events
1 351
Write events
506
Delete events
25
Modification events
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | )6$ |
Value: 29362400FC0A0000010000000000000000000000 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: FC0A000044CB3100838DD40100000000 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219808800 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2812) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1300627477 | |||
Executable files
0
Suspicious files
5
Text files
129
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9689.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018120620181207\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2812 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2812 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 1328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\hotjar-385430.js[1].download | text | |
MD5:— | SHA256:— | |||
| 1328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012018120620181207\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\iframe_api[1] | text | |
MD5:— | SHA256:— | |||
| 2812 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{8C15E15D-50F2-4A3E-8D4F-60F1BDD65E0A}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
83
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2812 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
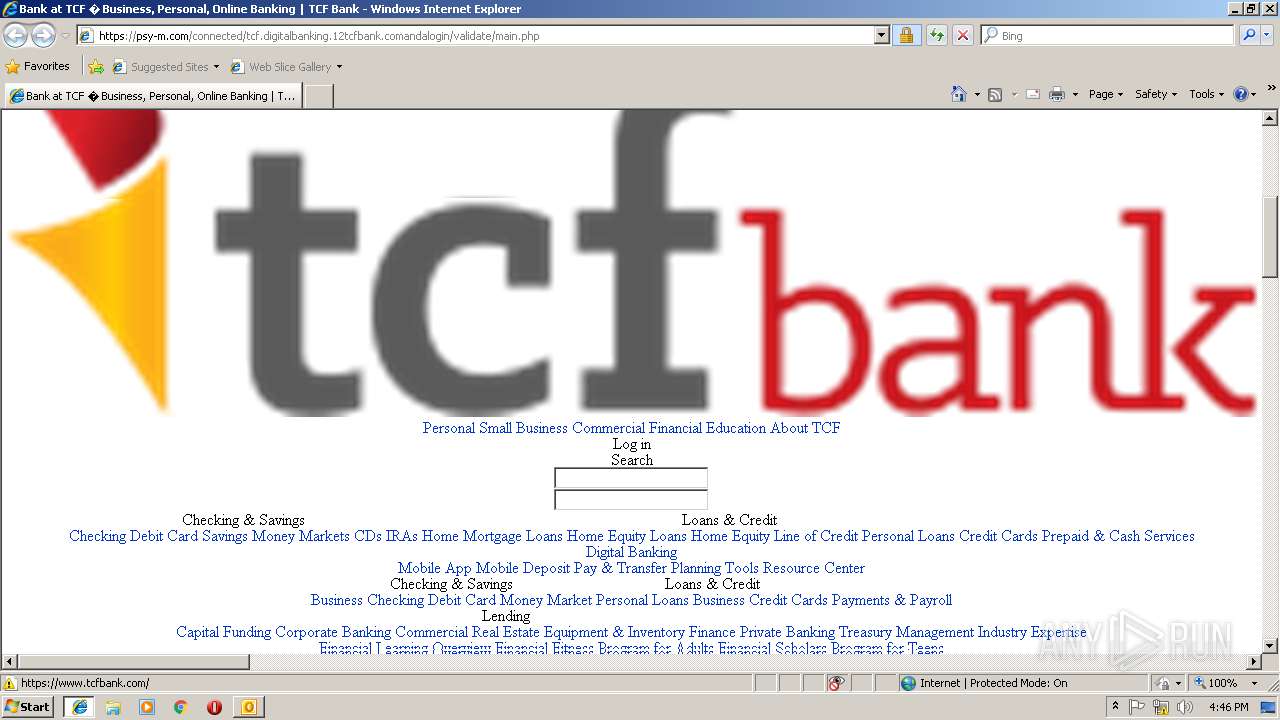
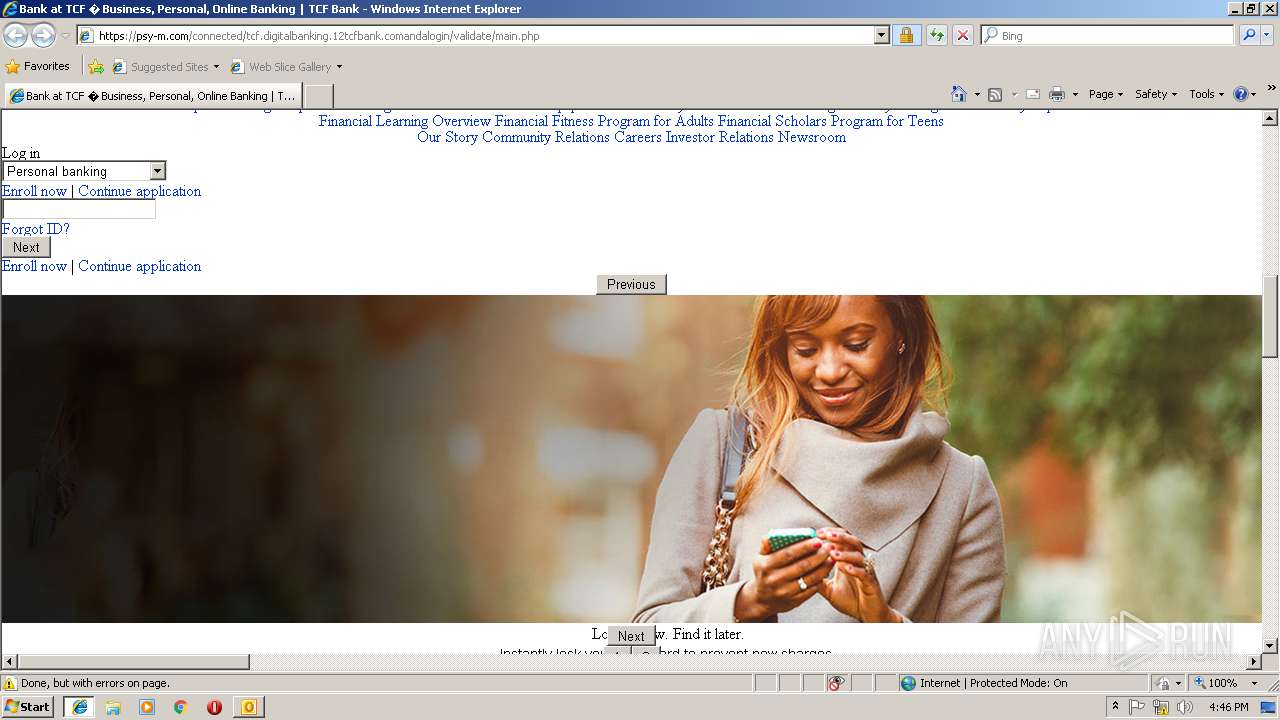
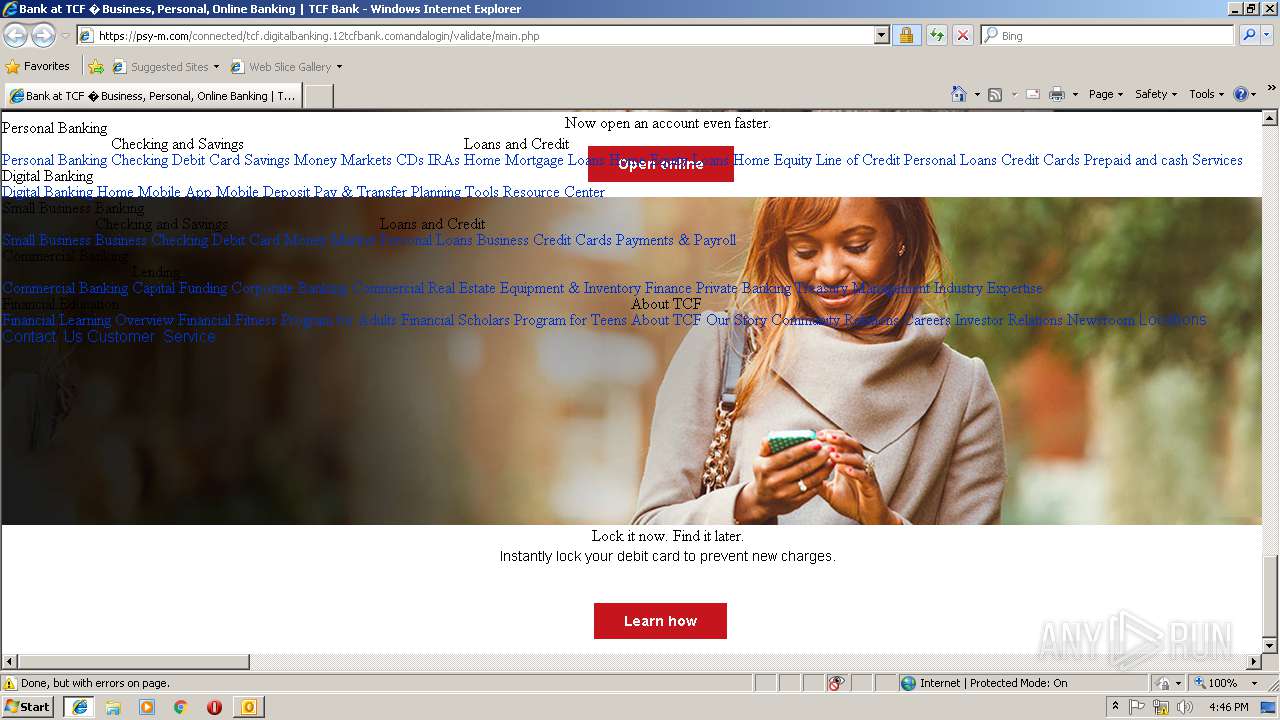
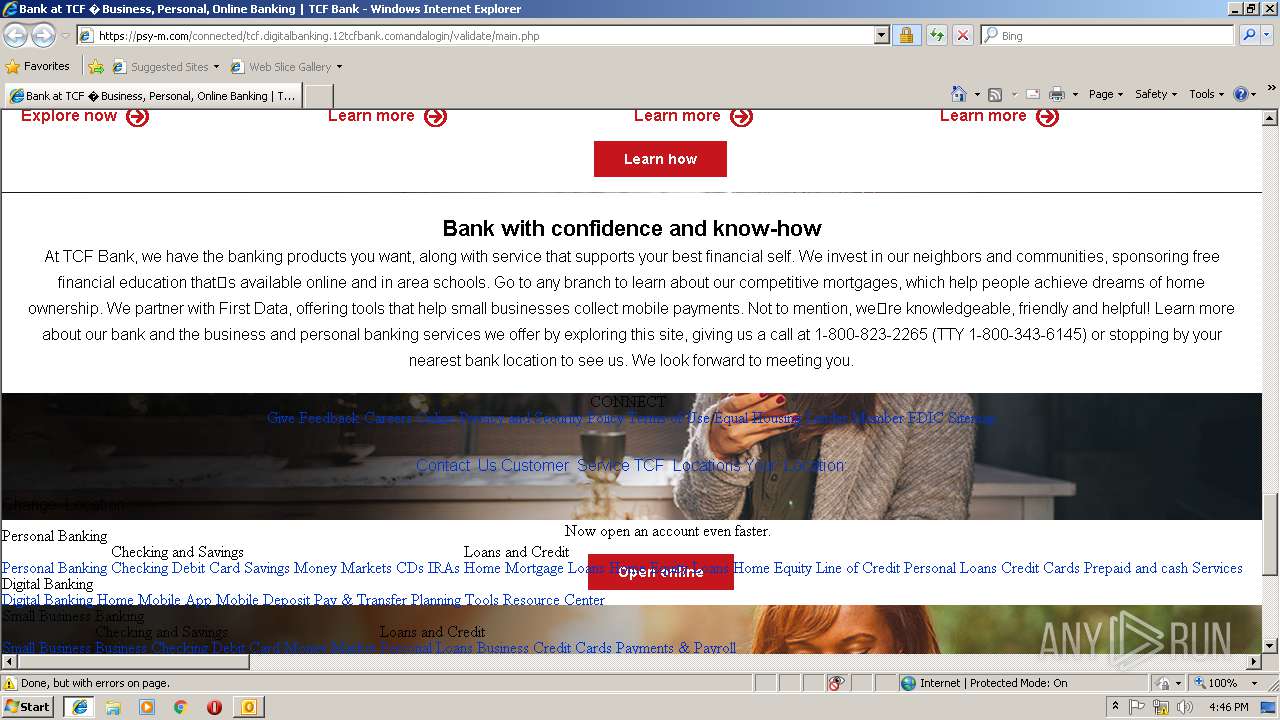
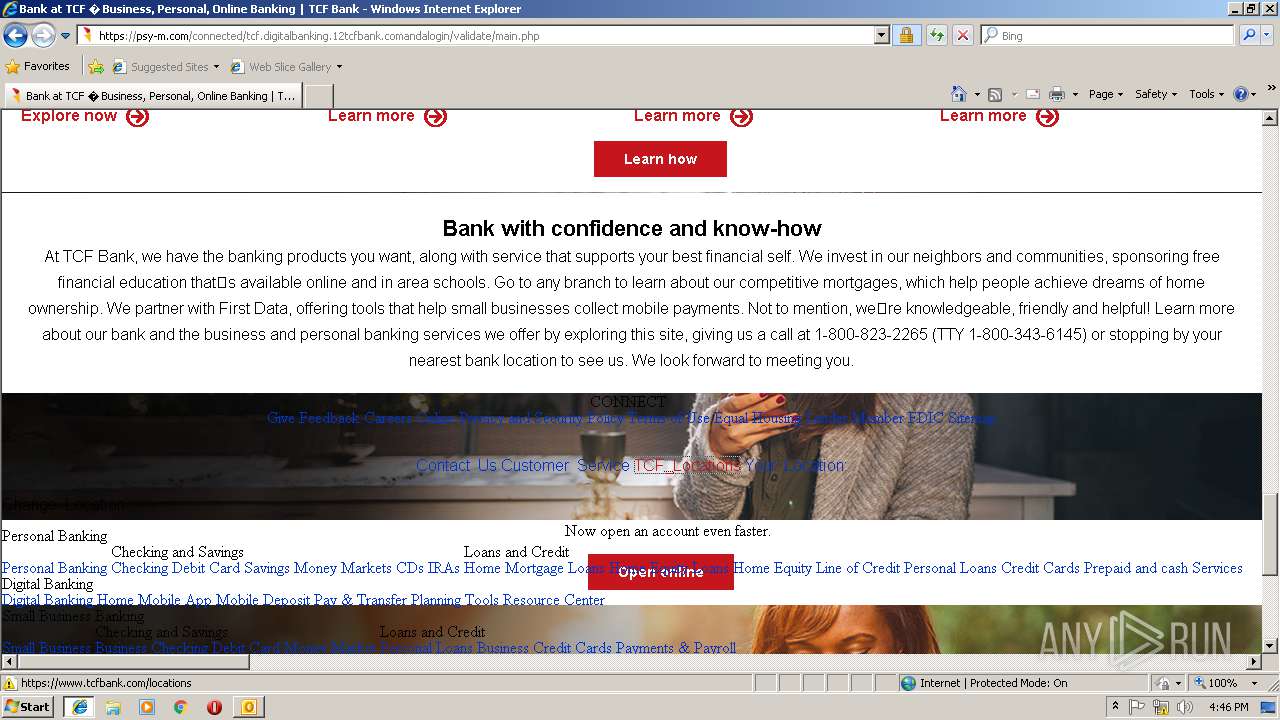
1328 | iexplore.exe | GET | 200 | 80.78.250.103:80 | http://kuzminskaya.ru/wp.shtml | RU | html | 149 b | malicious |
3164 | iexplore.exe | GET | 404 | 80.78.250.103:80 | http://kuzminskaya.ru/favicon.ico | RU | html | 1.19 Kb | malicious |
1328 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
— | — | GET | 200 | 104.109.73.63:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
3164 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2812 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1328 | iexplore.exe | 80.78.250.103:443 | kuzminskaya.ru | Domain names registrar REG.RU, Ltd | RU | suspicious |
1328 | iexplore.exe | 80.78.250.103:80 | kuzminskaya.ru | Domain names registrar REG.RU, Ltd | RU | suspicious |
3164 | iexplore.exe | 80.78.250.103:80 | kuzminskaya.ru | Domain names registrar REG.RU, Ltd | RU | suspicious |
3164 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1328 | iexplore.exe | 52.216.161.37:443 | s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
1328 | iexplore.exe | 172.217.168.14:443 | s.ytimg.com | Google Inc. | US | whitelisted |
1328 | iexplore.exe | 216.58.215.226:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
1328 | iexplore.exe | 172.217.168.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1328 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
kuzminskaya.ru |
| malicious |
psy-m.com |
| malicious |
www.bing.com |
| whitelisted |
s3.amazonaws.com |
| shared |
s.ytimg.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
bat.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |