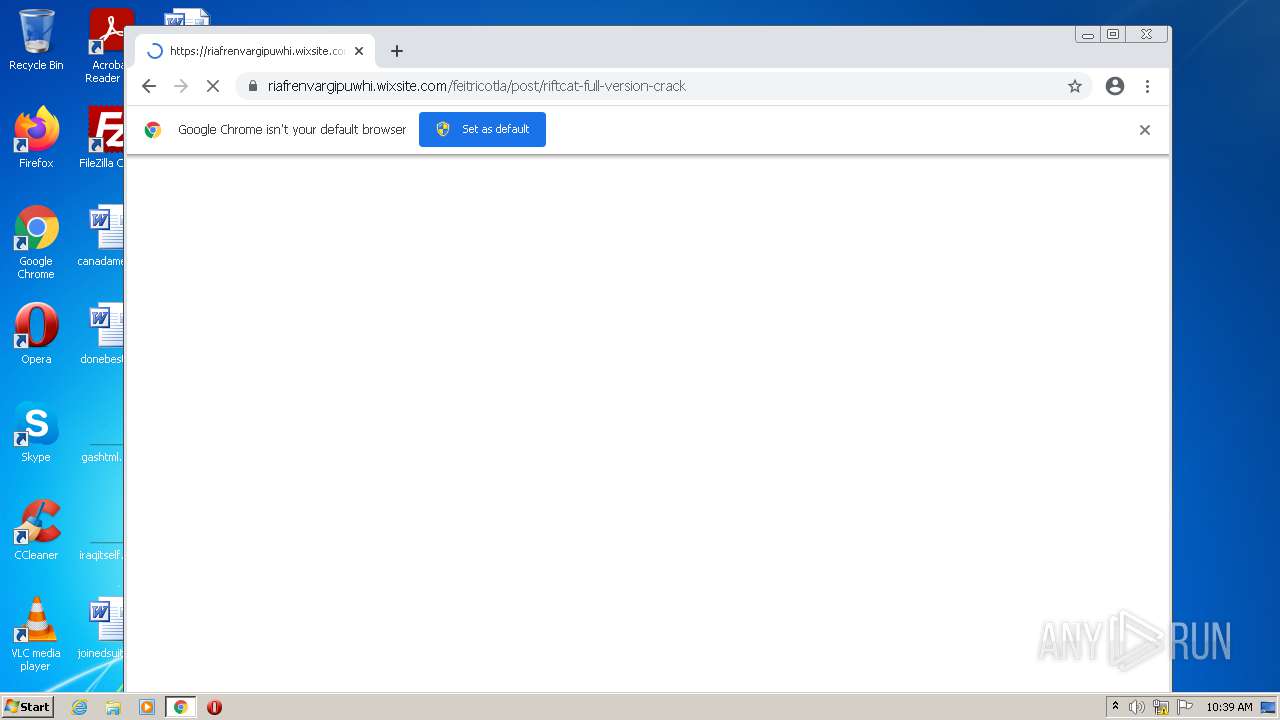
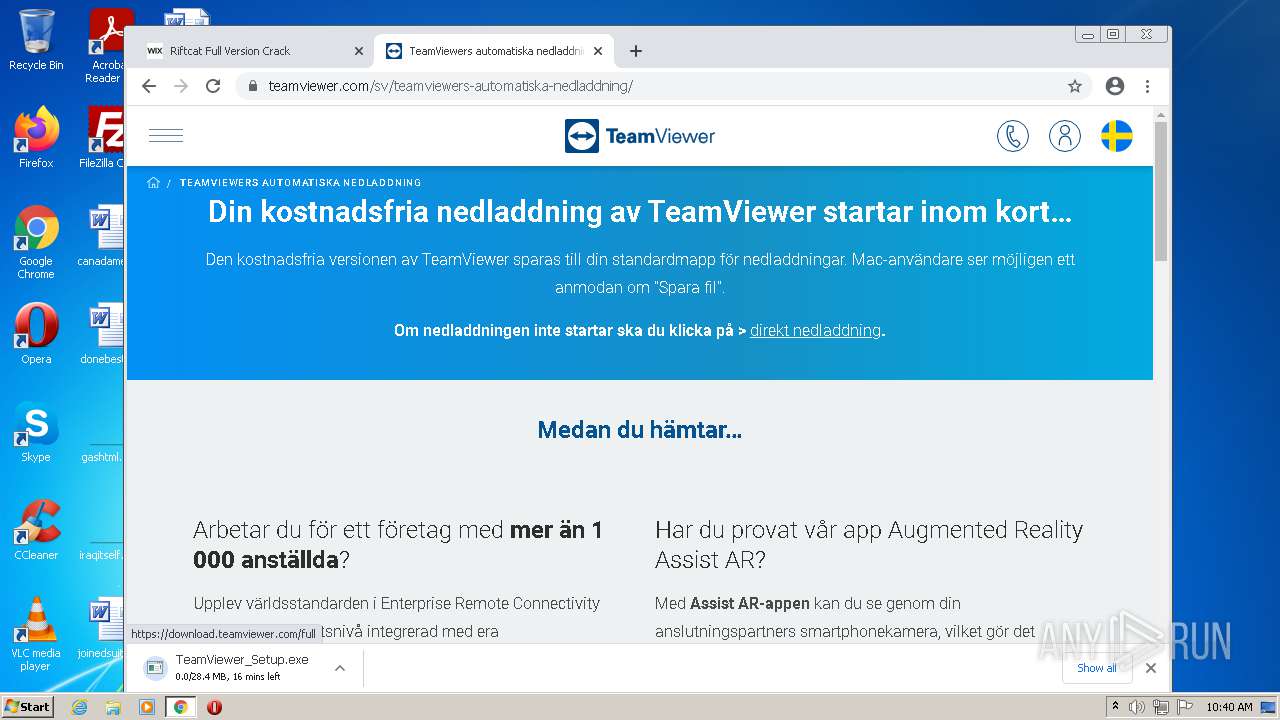
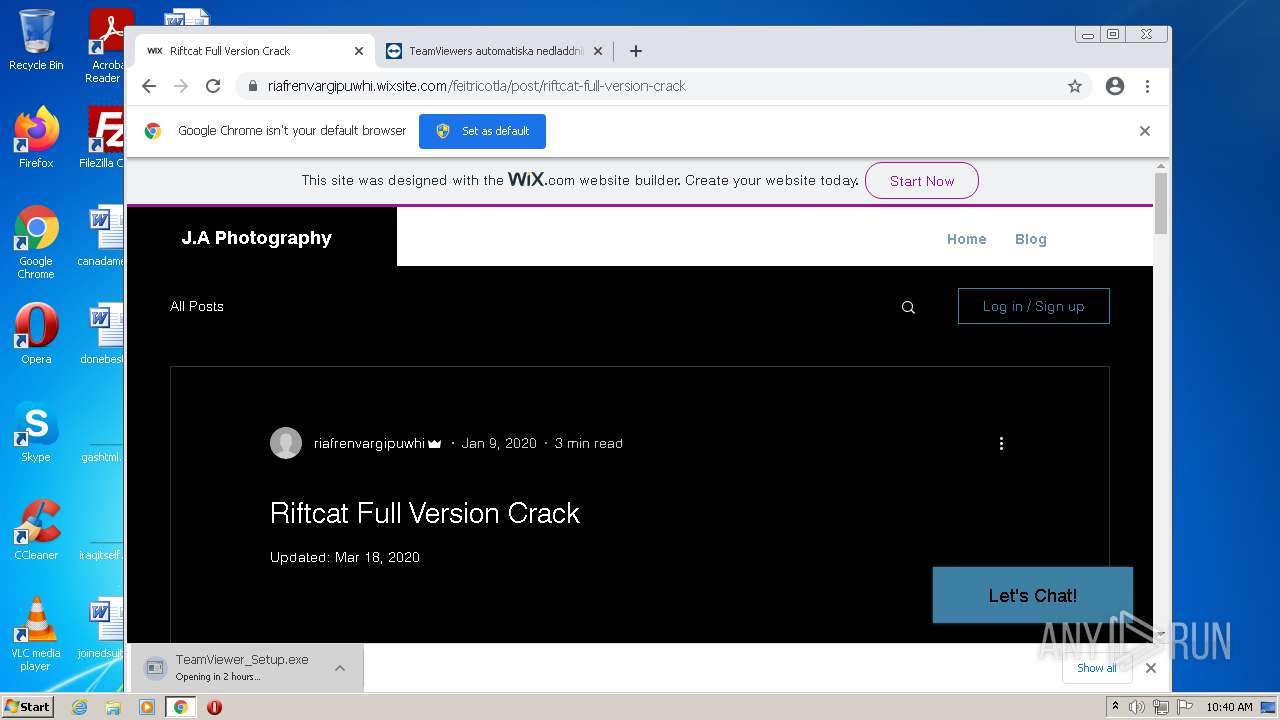
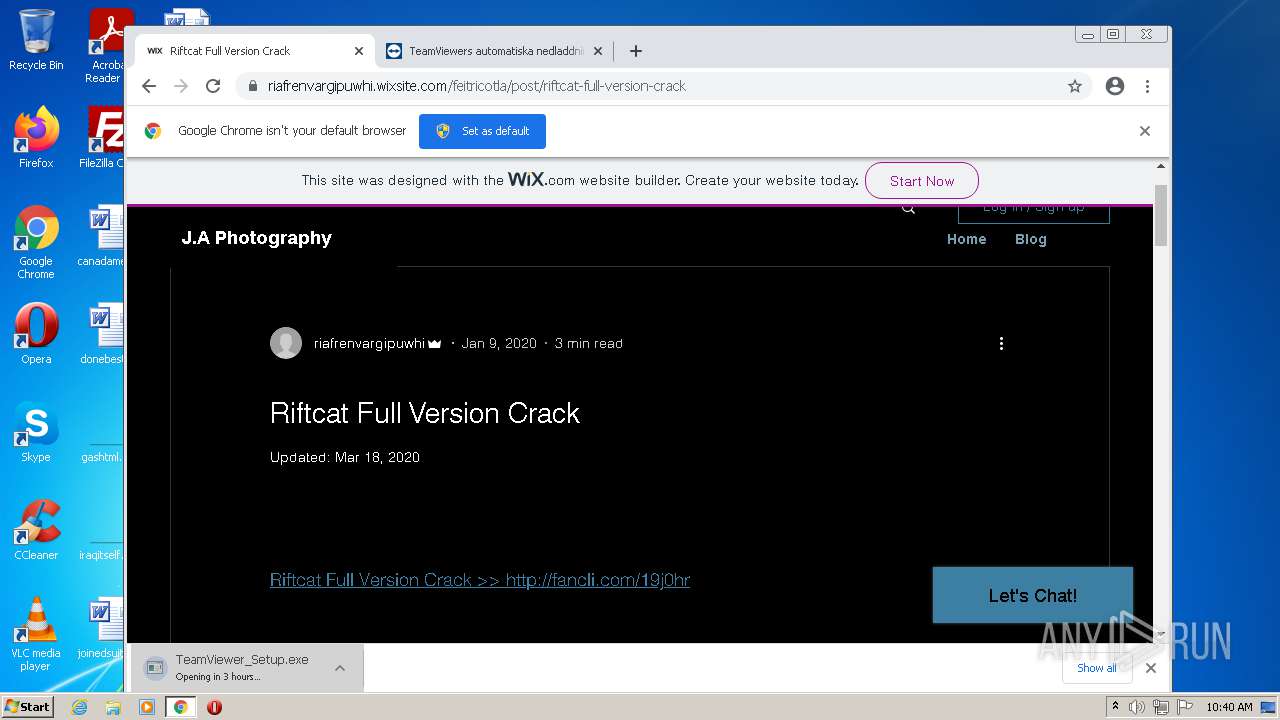
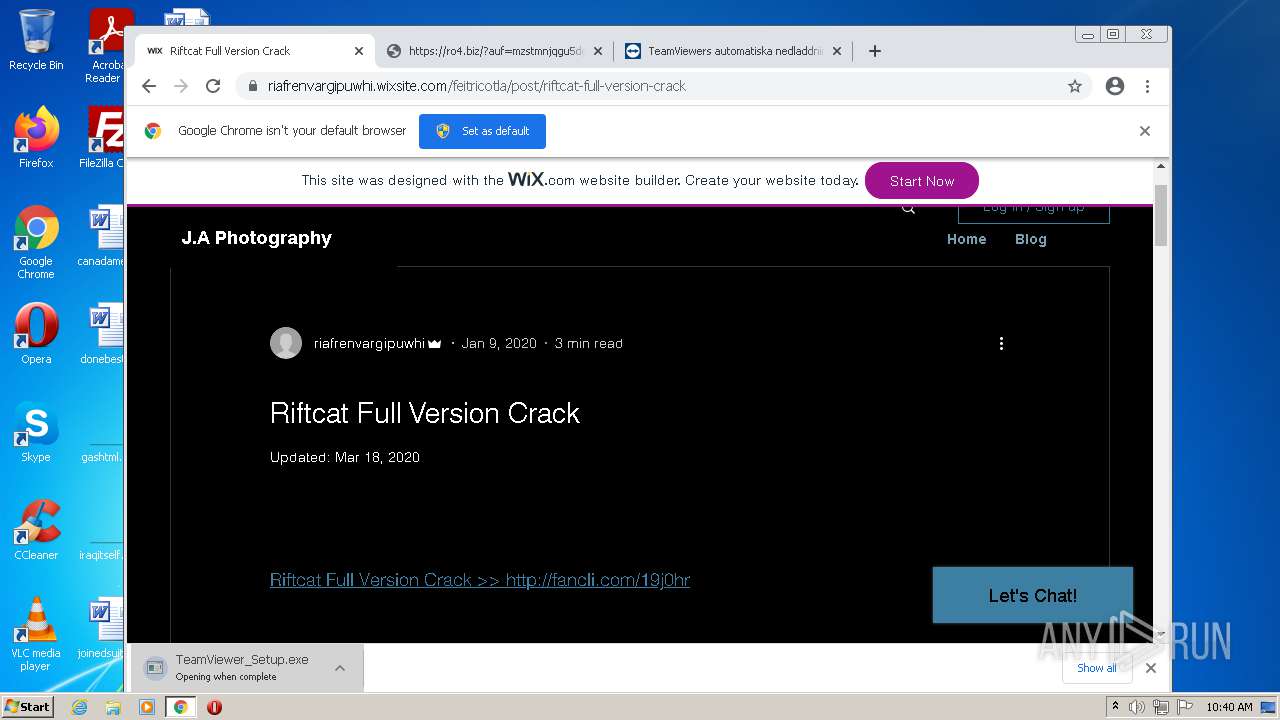
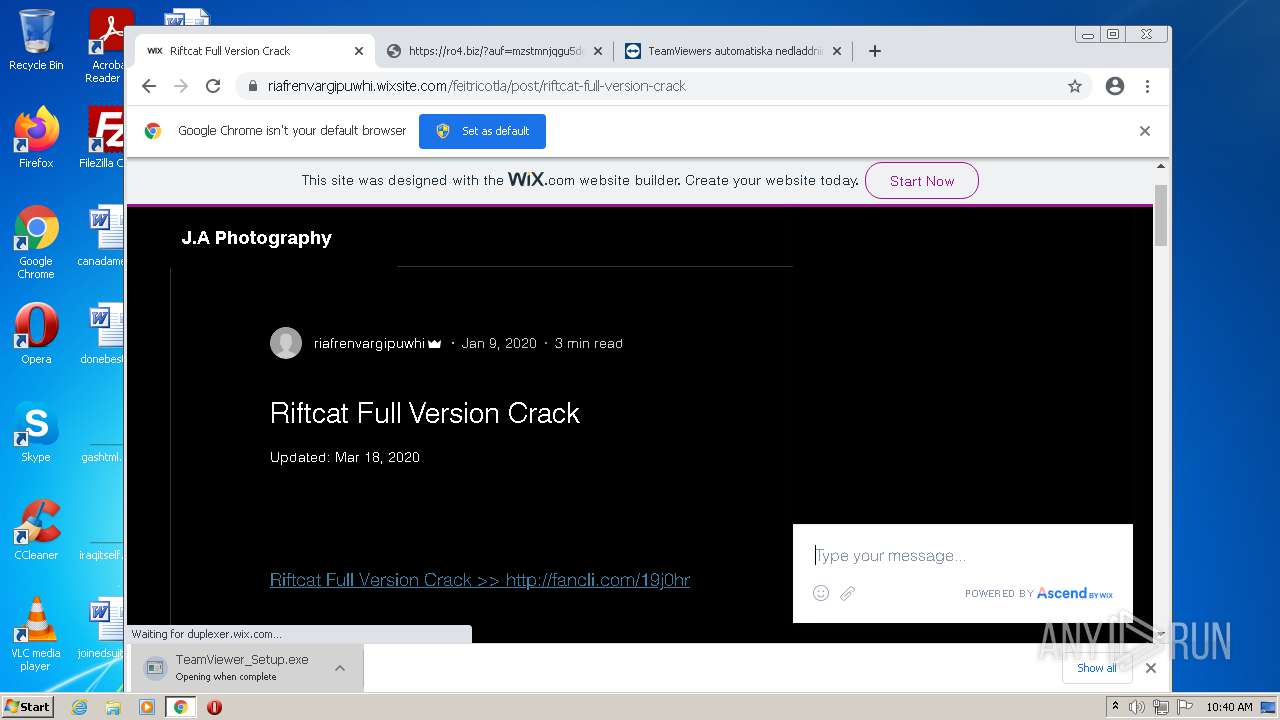
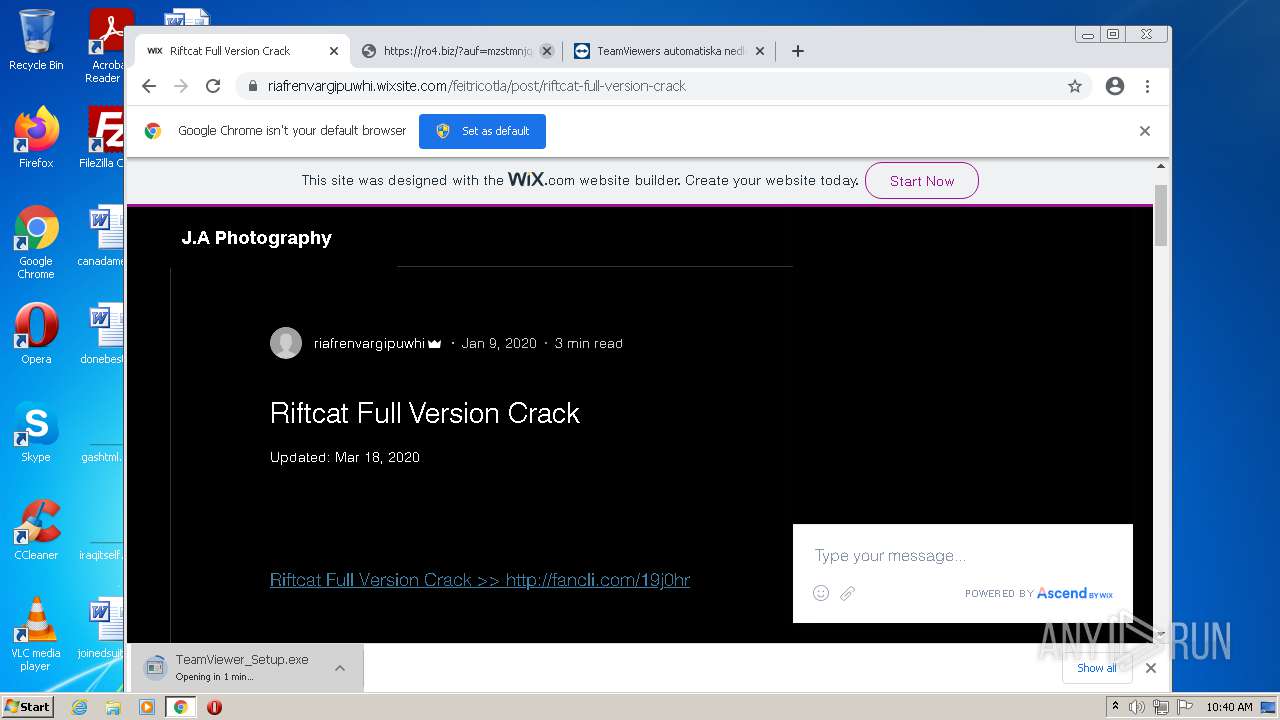
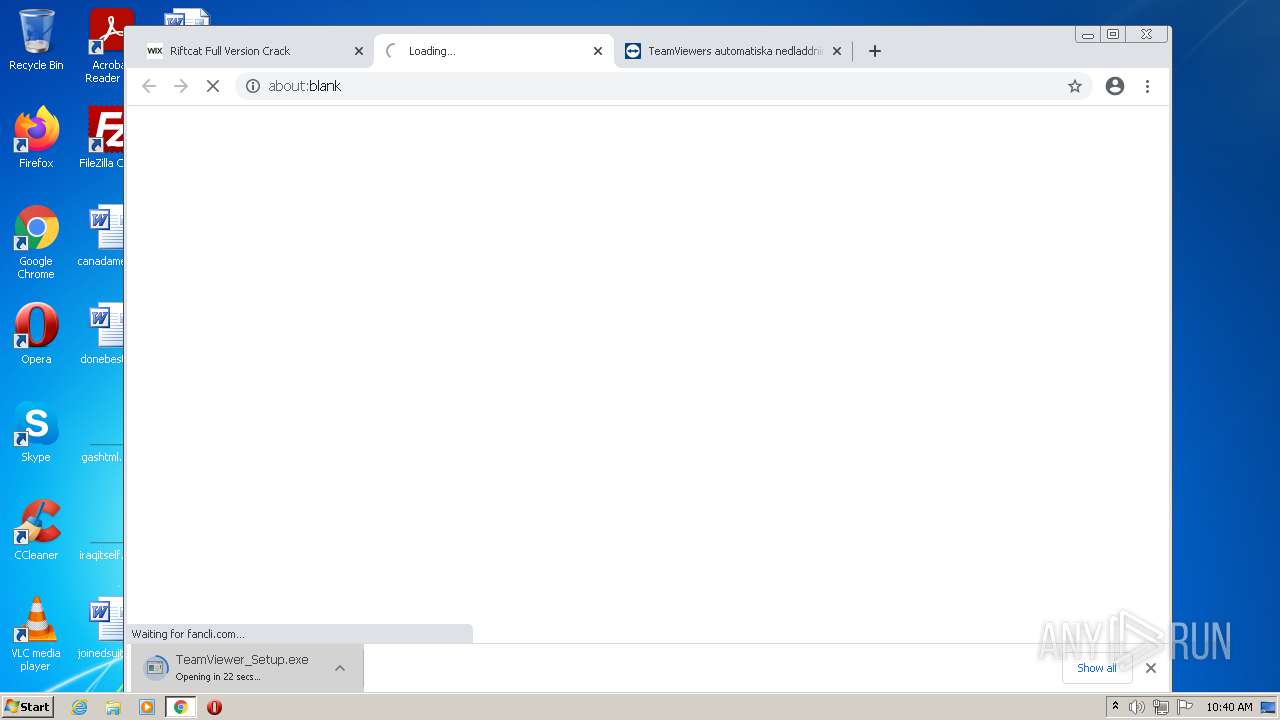
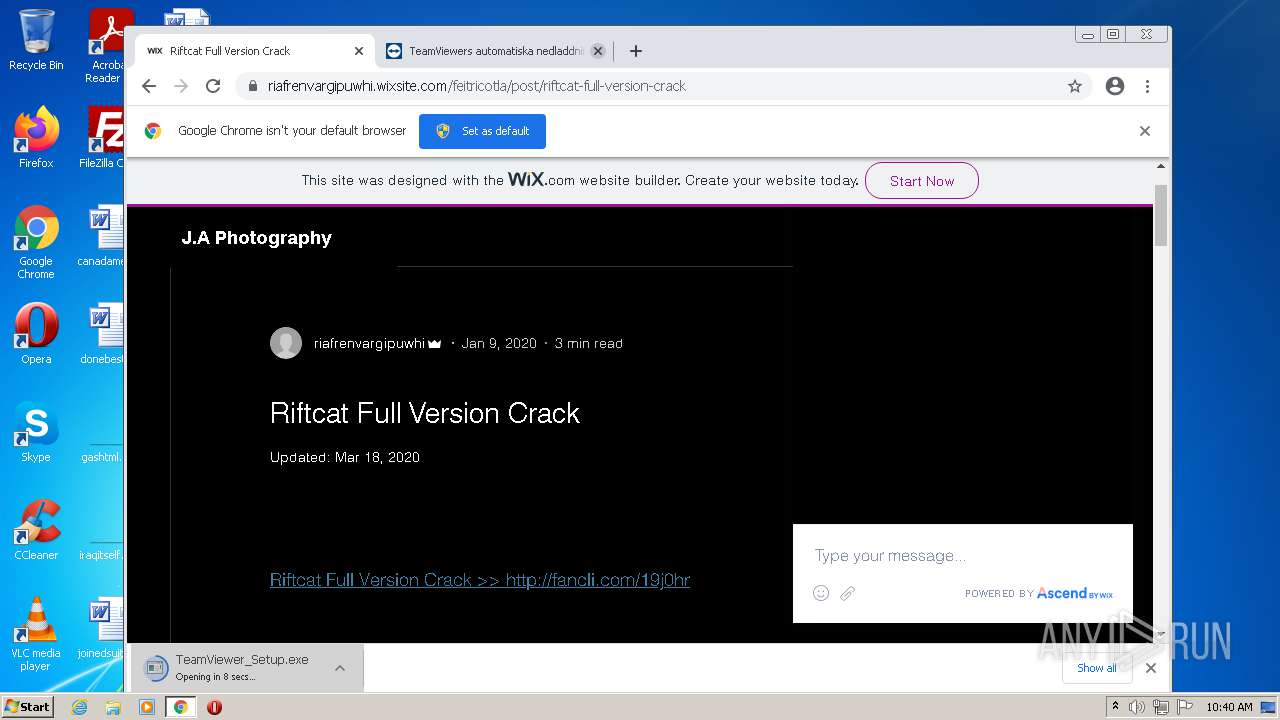
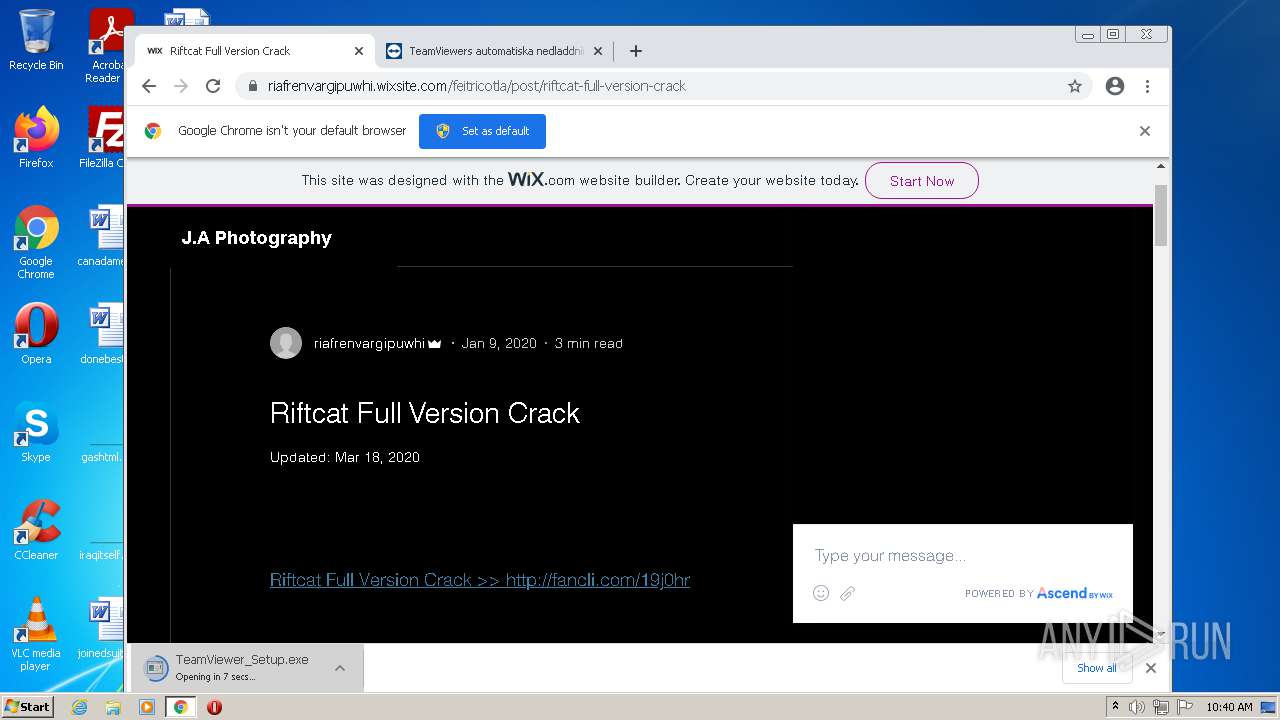
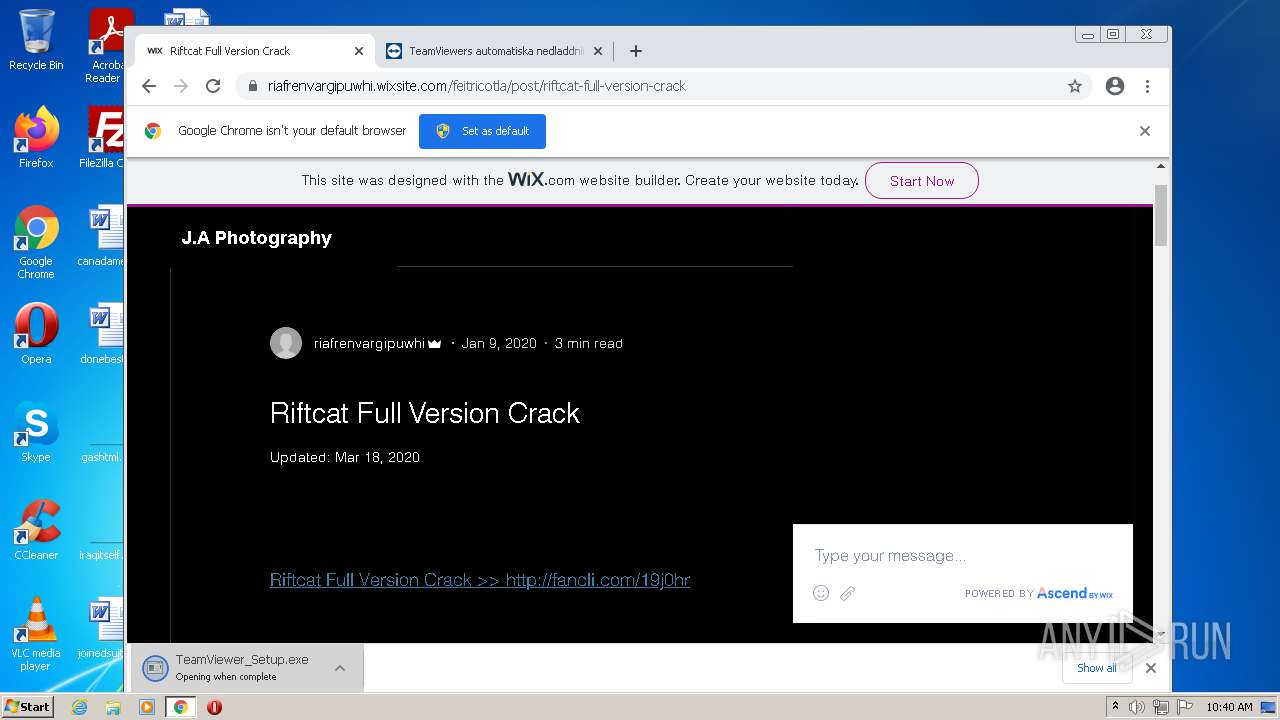
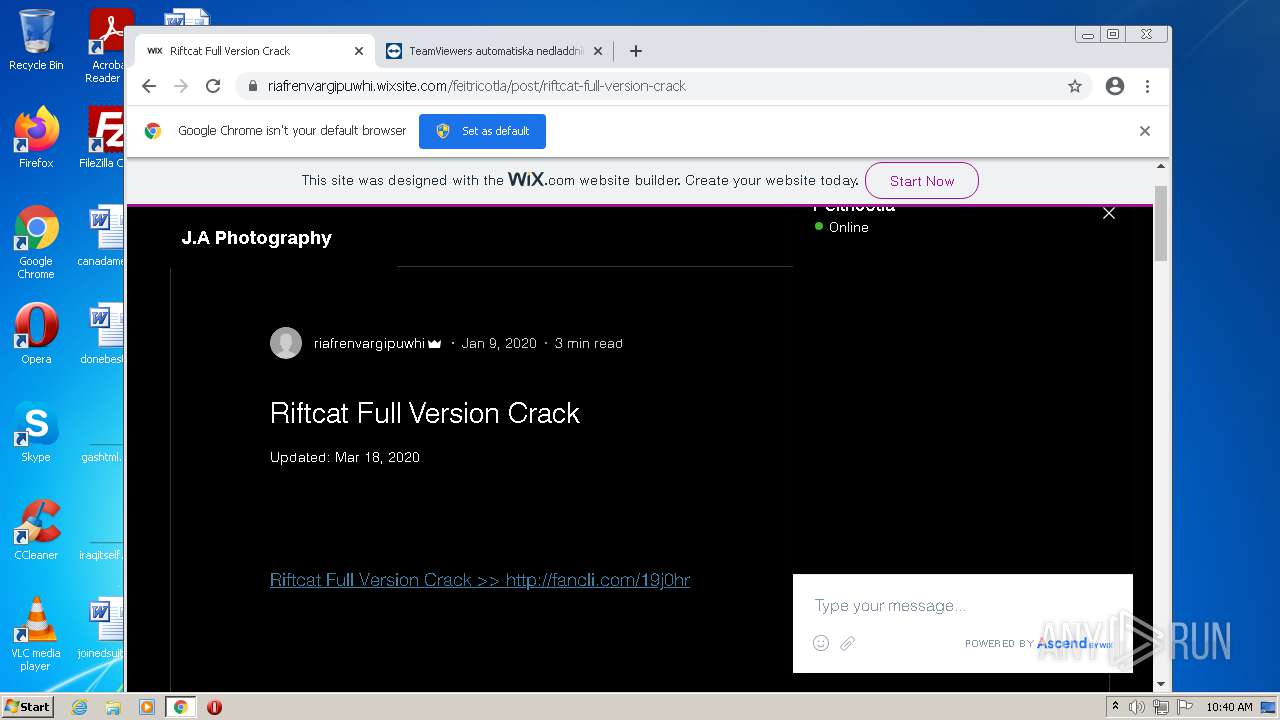
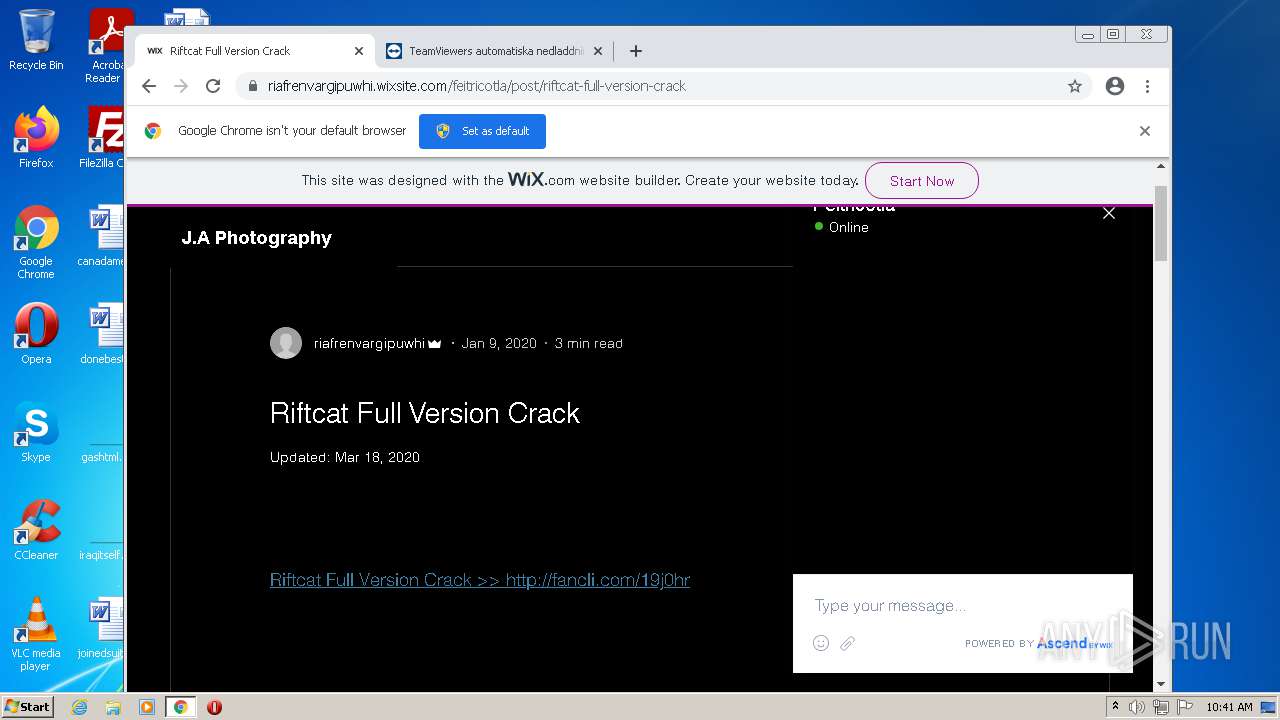
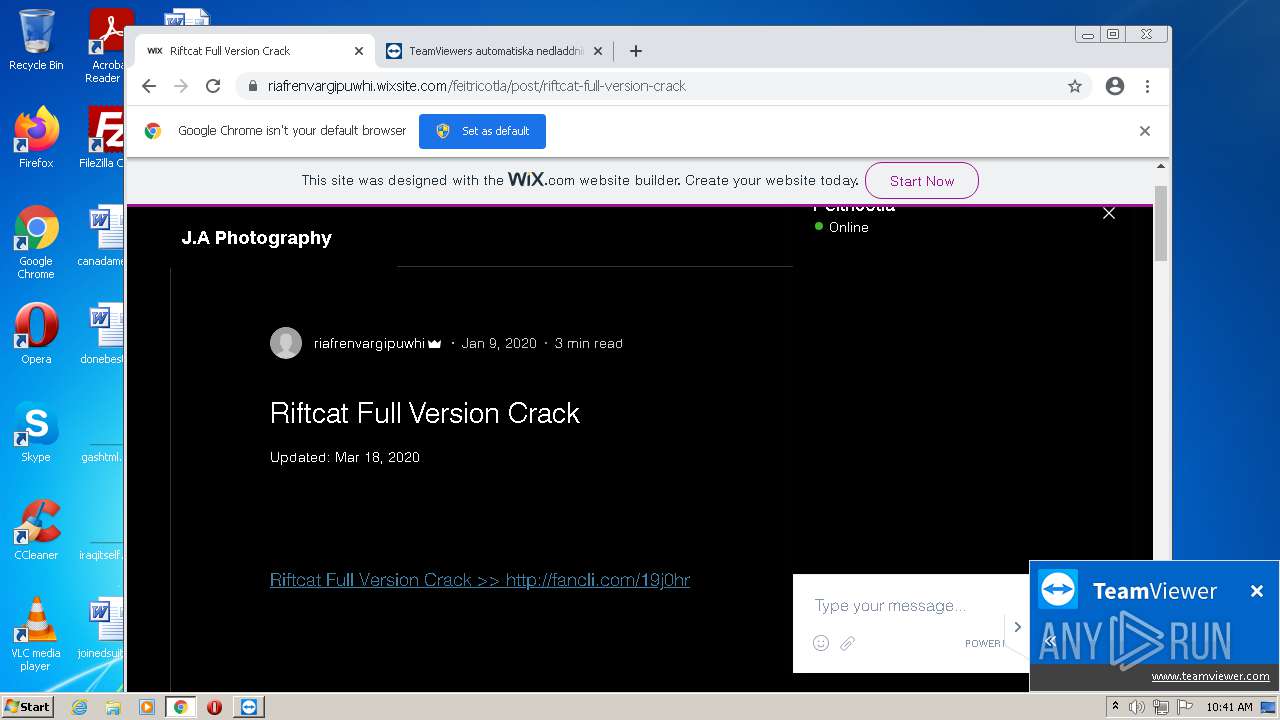
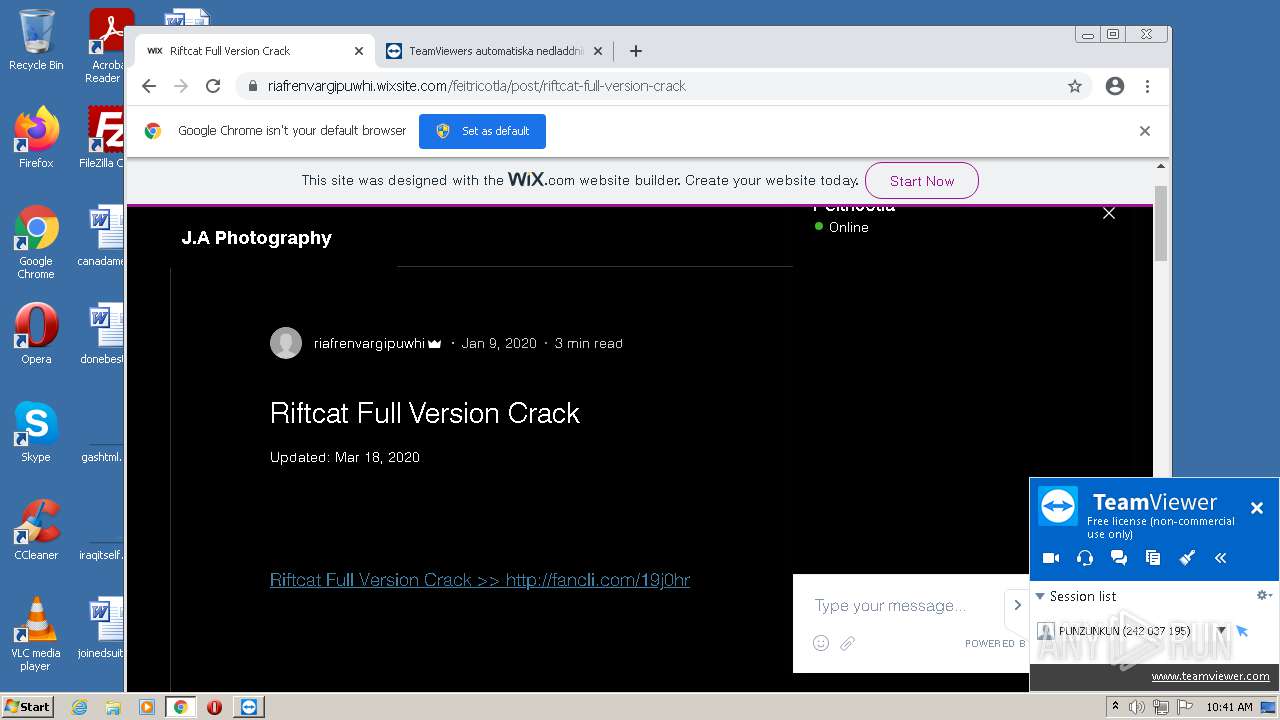
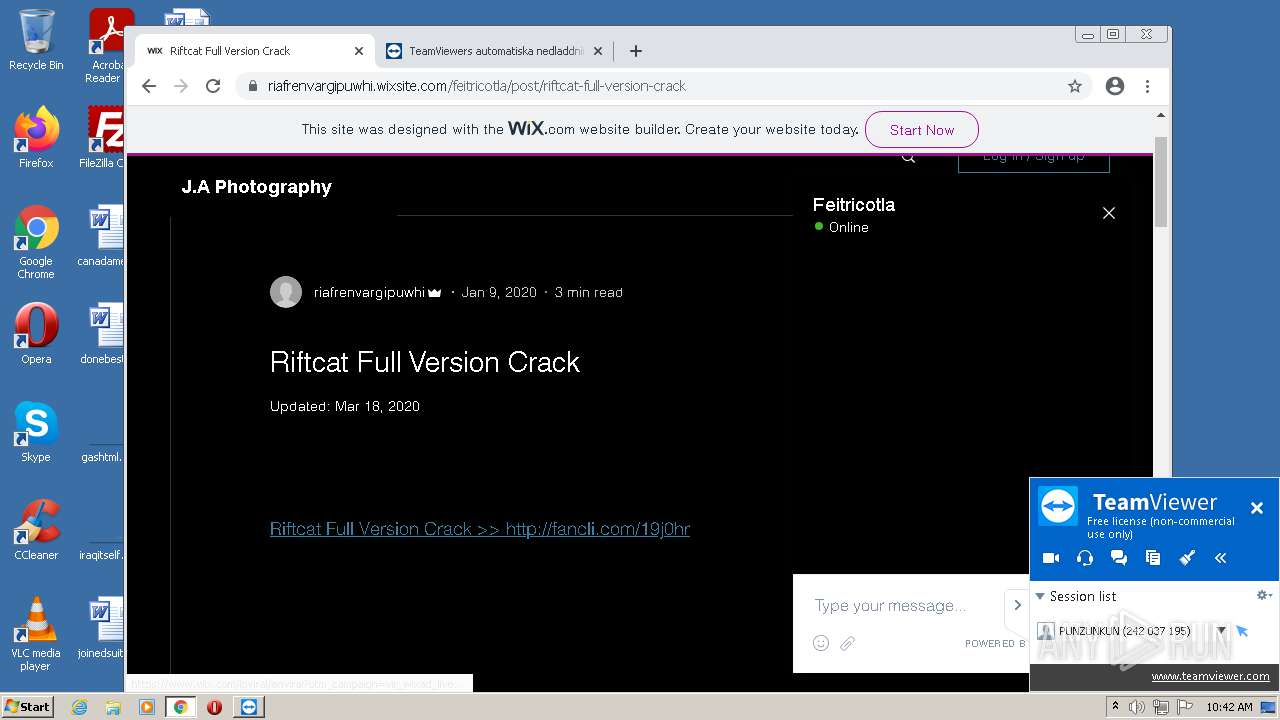
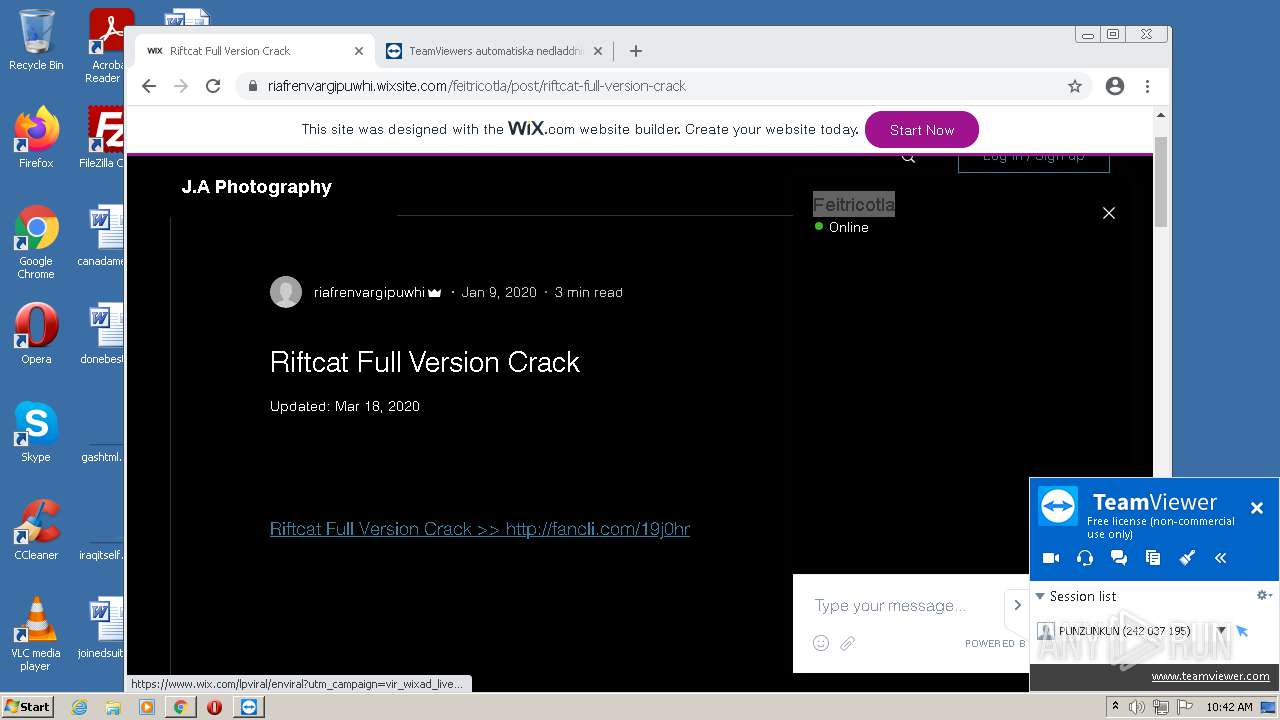
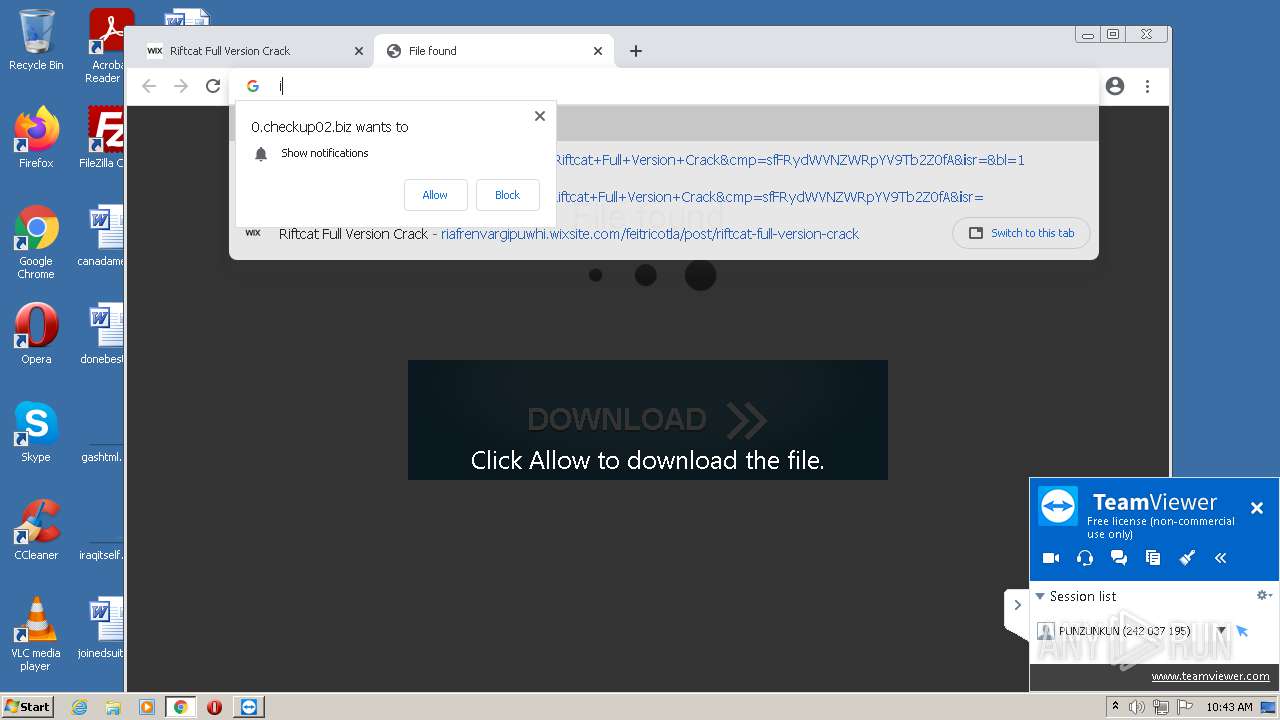
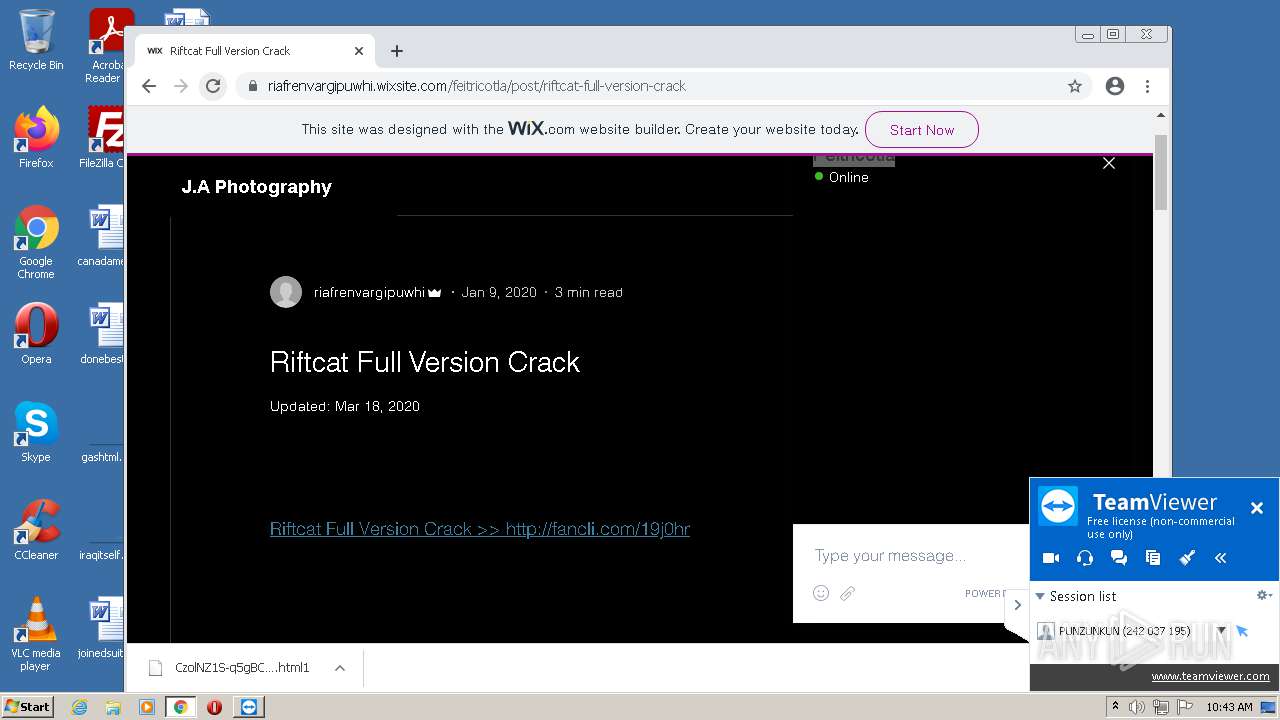
| URL: | https://riafrenvargipuwhi.wixsite.com/feitricotla/post/riftcat-full-version-crack |
| Full analysis: | https://app.any.run/tasks/18e9b763-7142-4ce7-9e6f-fef5a24c4db9 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2021, 09:38:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C85B6D8676D7B23DD04991AC448A985D |
| SHA1: | B1D9FDE78E9832C71AB63CC46460F3E0321A2496 |
| SHA256: | 161C8BE5083907C11441610790155F426B07B0C1EC29DB427189B00C1F460CF5 |
| SSDEEP: | 3:N8iS6ndRAx/3KcfFOJJPu8Gmn:2F6dmpKcfFmfn |
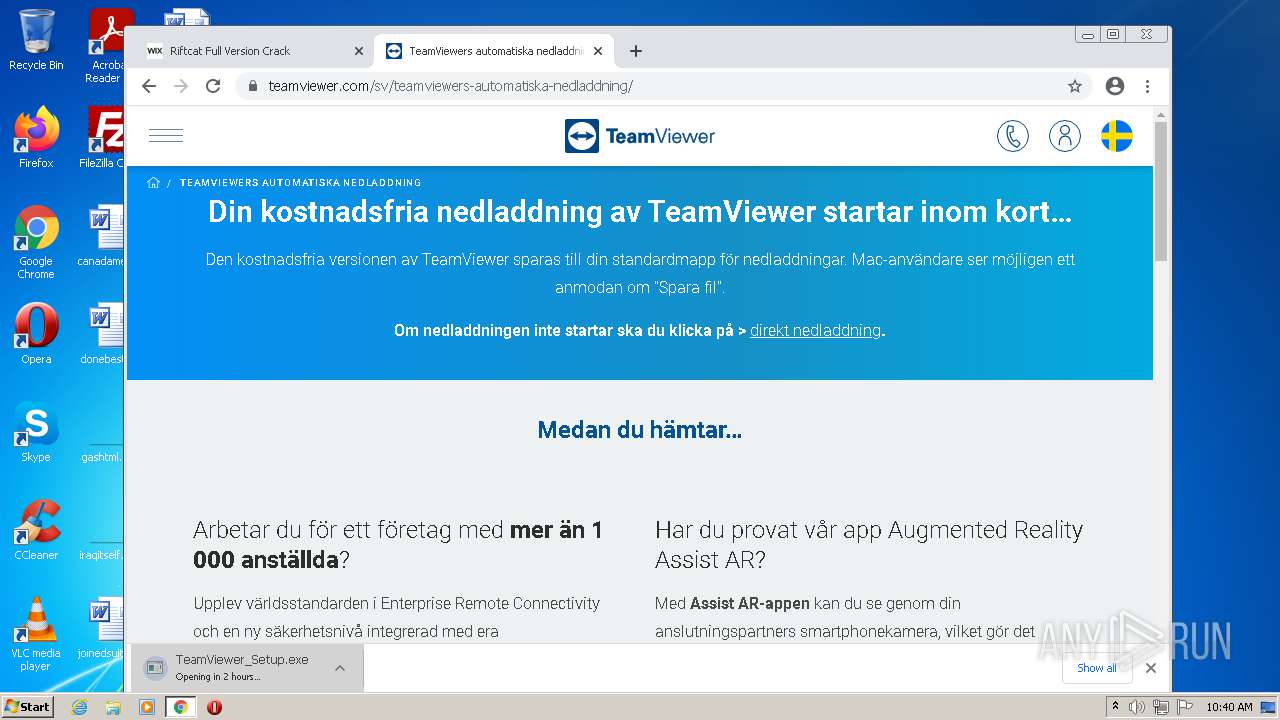
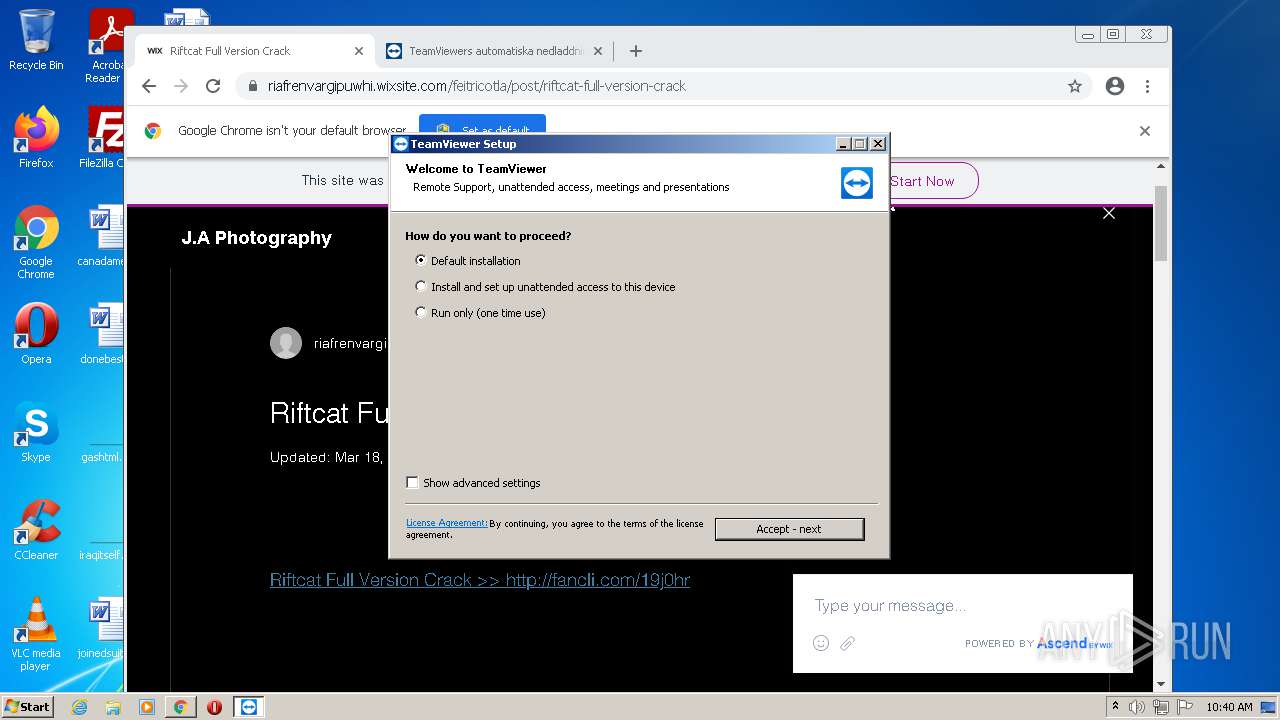
MALICIOUS
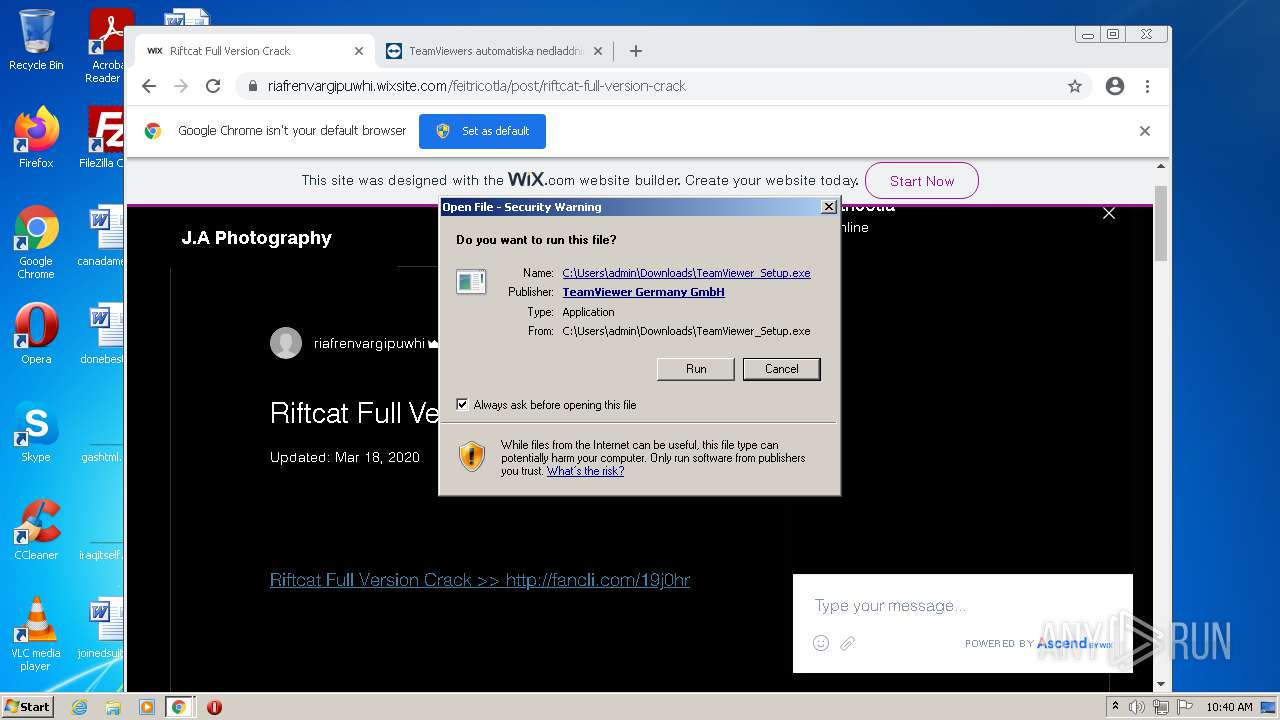
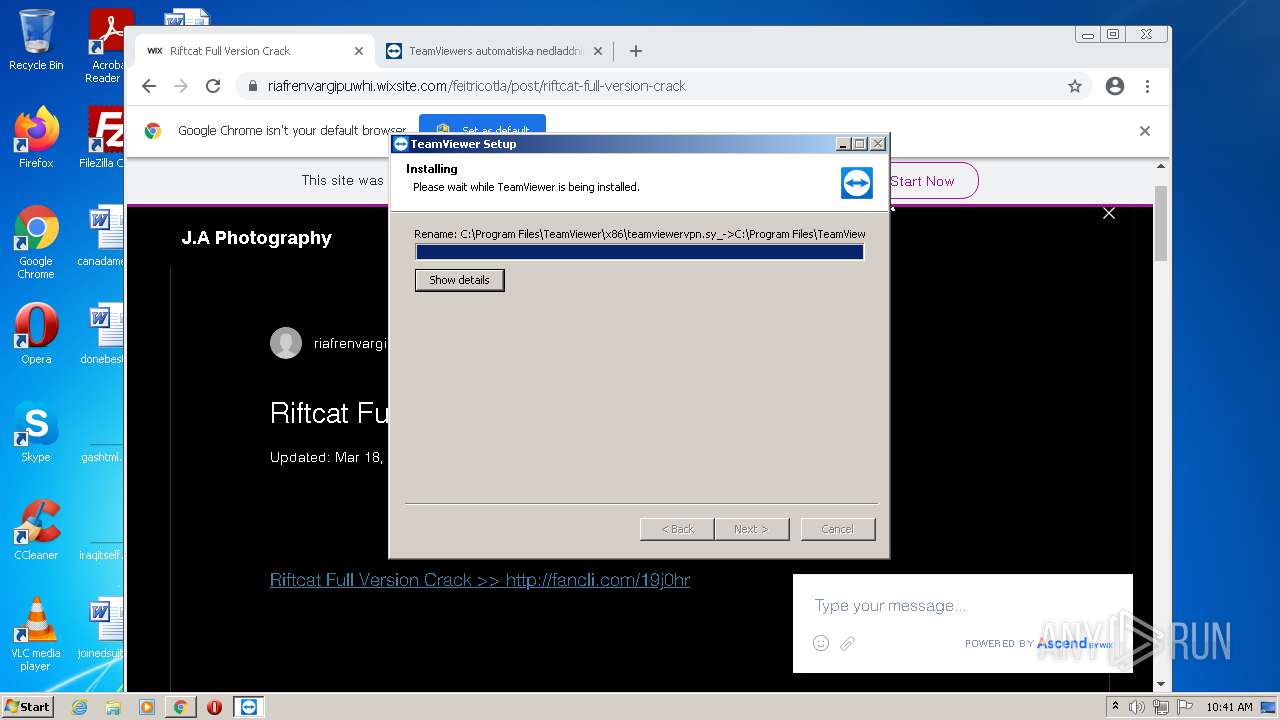
Application was dropped or rewritten from another process
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
- TeamViewer_Service.exe (PID: 2216)
- TeamViewer_Service.exe (PID: 3028)
- tv_w32.exe (PID: 2076)
- TeamViewer_Desktop.exe (PID: 1140)
Loads dropped or rewritten executable
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
- regsvr32.exe (PID: 1140)
- TeamViewer.exe (PID: 2180)
- TeamViewer_Desktop.exe (PID: 1140)
- tv_w32.exe (PID: 2076)
- chrome.exe (PID: 1472)
- Explorer.EXE (PID: 1896)
- chrome.exe (PID: 416)
- chrome.exe (PID: 3952)
- taskhost.exe (PID: 1684)
- Dwm.exe (PID: 600)
- taskeng.exe (PID: 776)
- ctfmon.exe (PID: 892)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2724)
Drops executable file immediately after starts
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
- chrome.exe (PID: 2372)
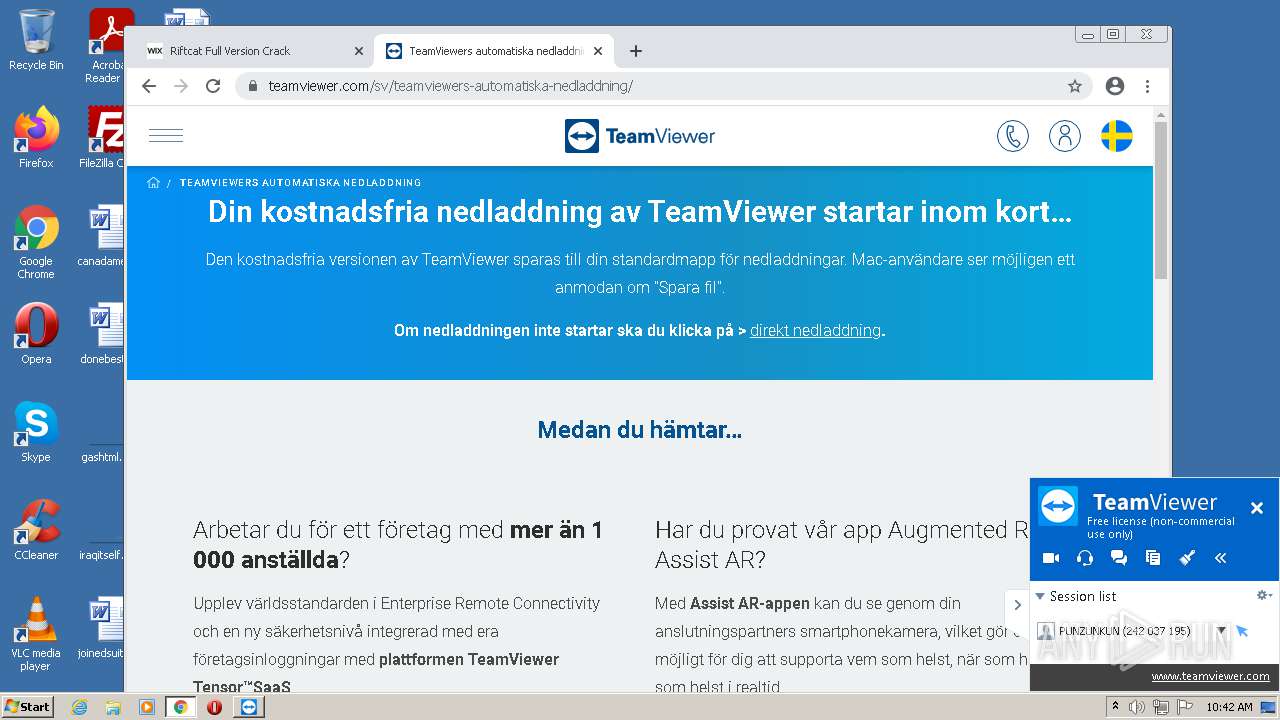
Uses Task Scheduler to autorun other applications
- ns5E19.tmp (PID: 3020)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3860)
- schtasks.exe (PID: 476)
Registers / Runs the DLL via REGSVR32.EXE
- ns81B1.tmp (PID: 908)
Uses Task Scheduler to run other applications
- ns89B1.tmp (PID: 2800)
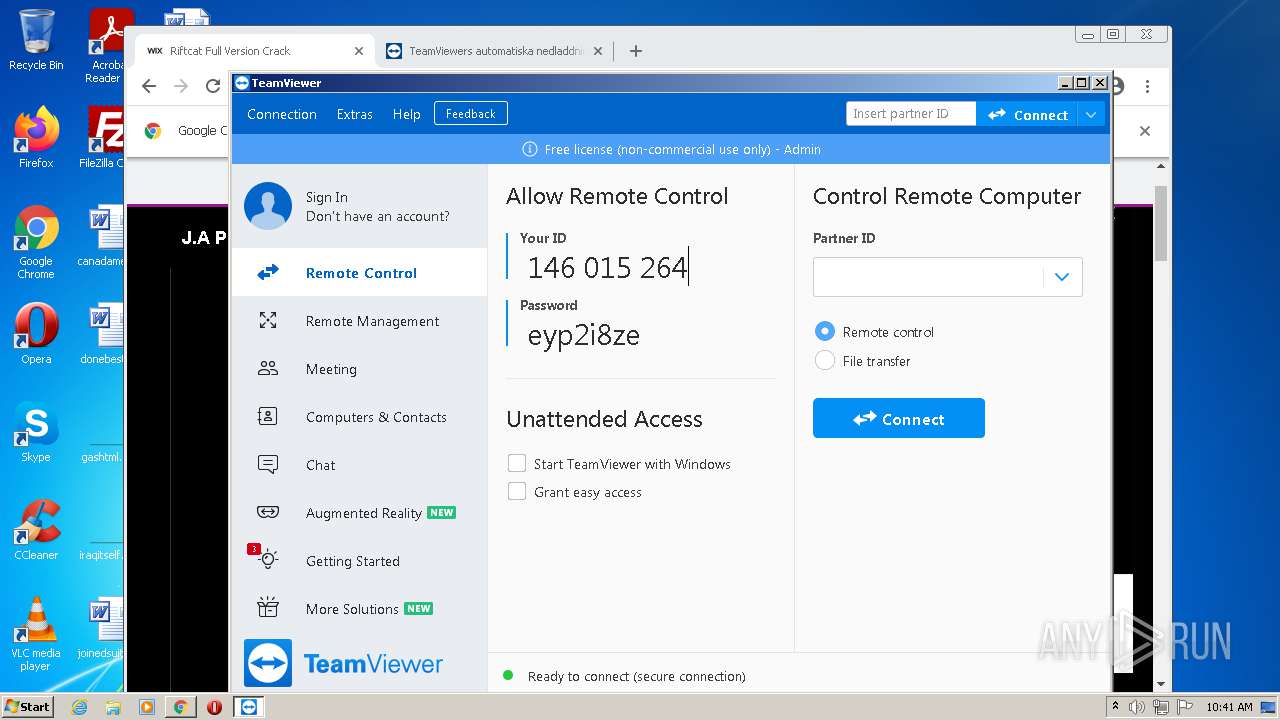
Steals credentials from Web Browsers
- TeamViewer.exe (PID: 2180)
Actions looks like stealing of personal data
- TeamViewer.exe (PID: 2180)
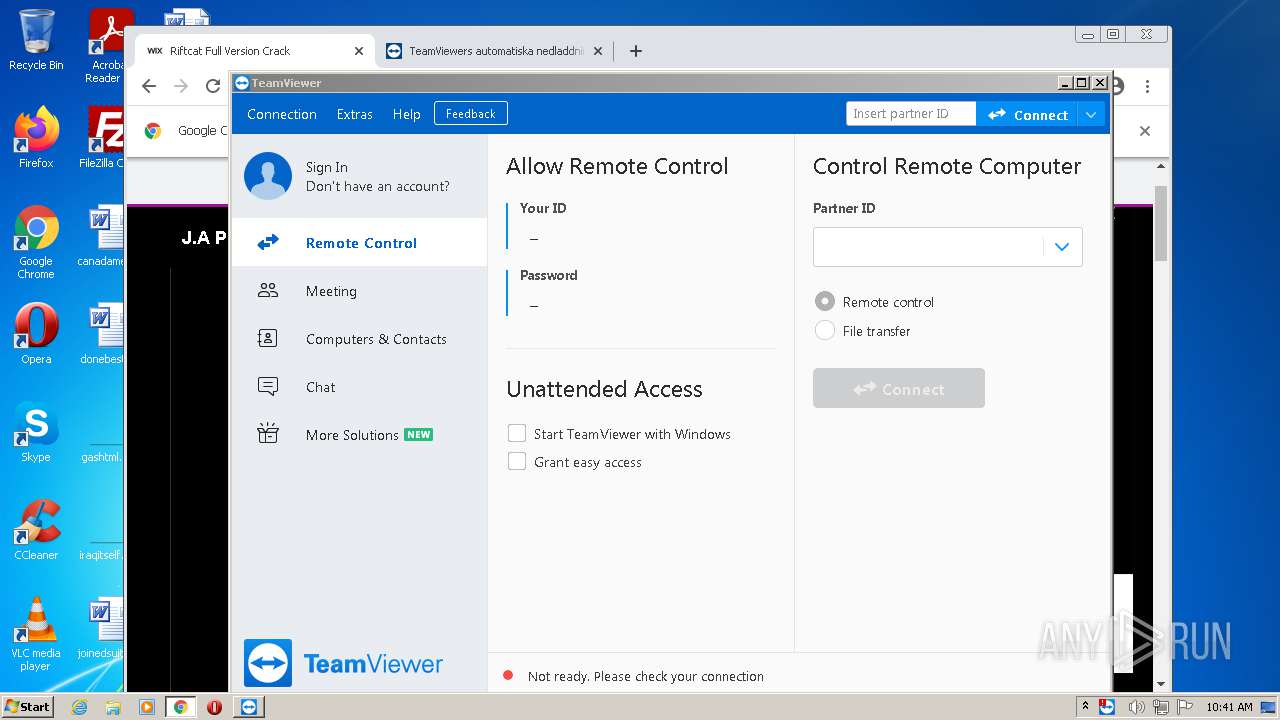
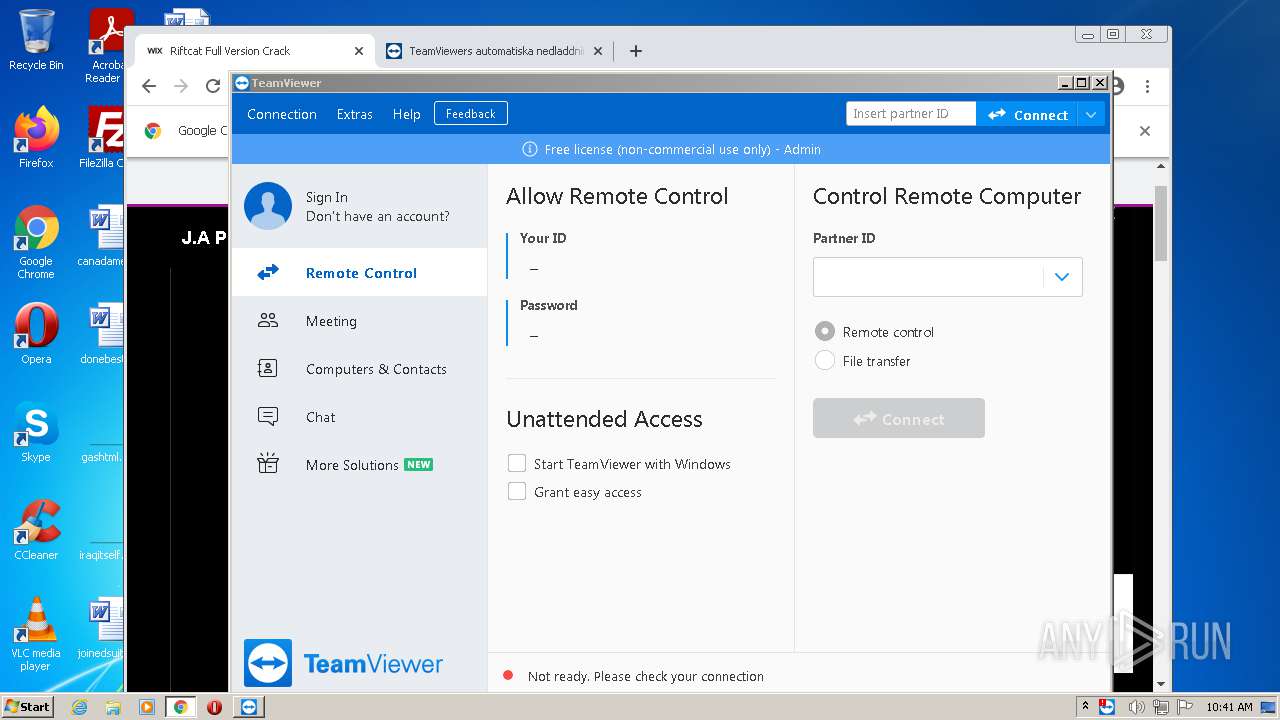
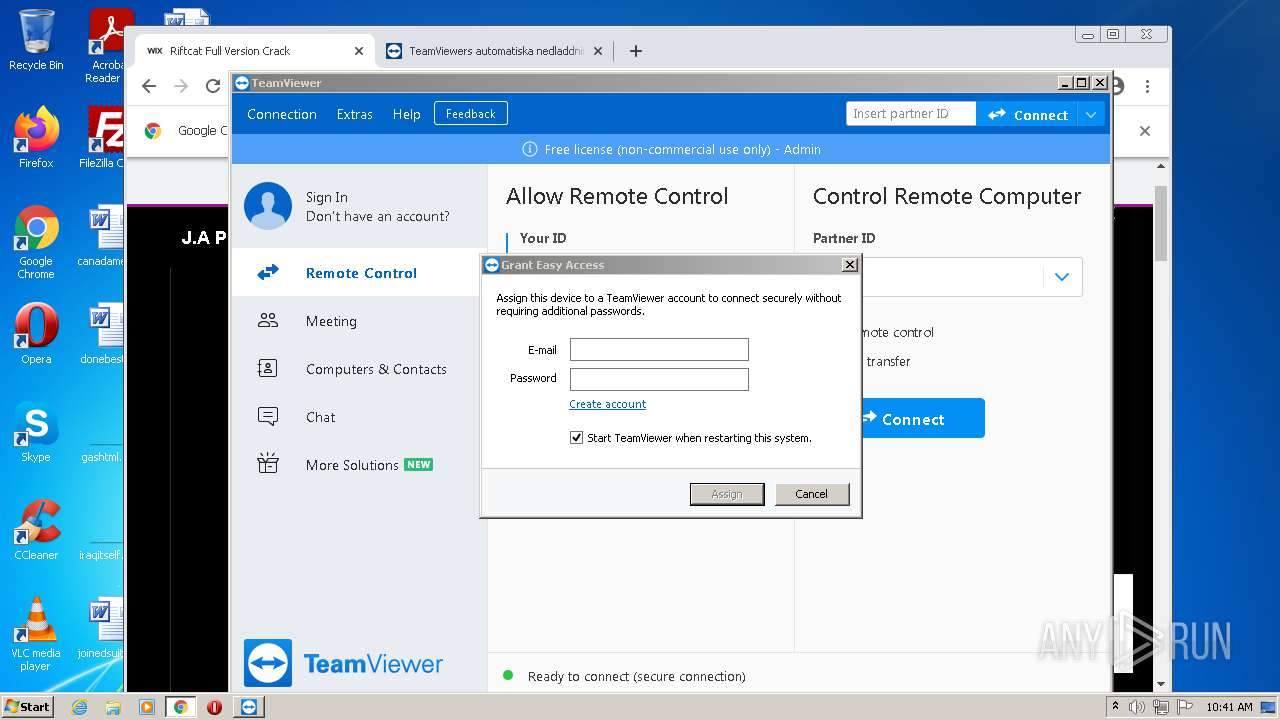
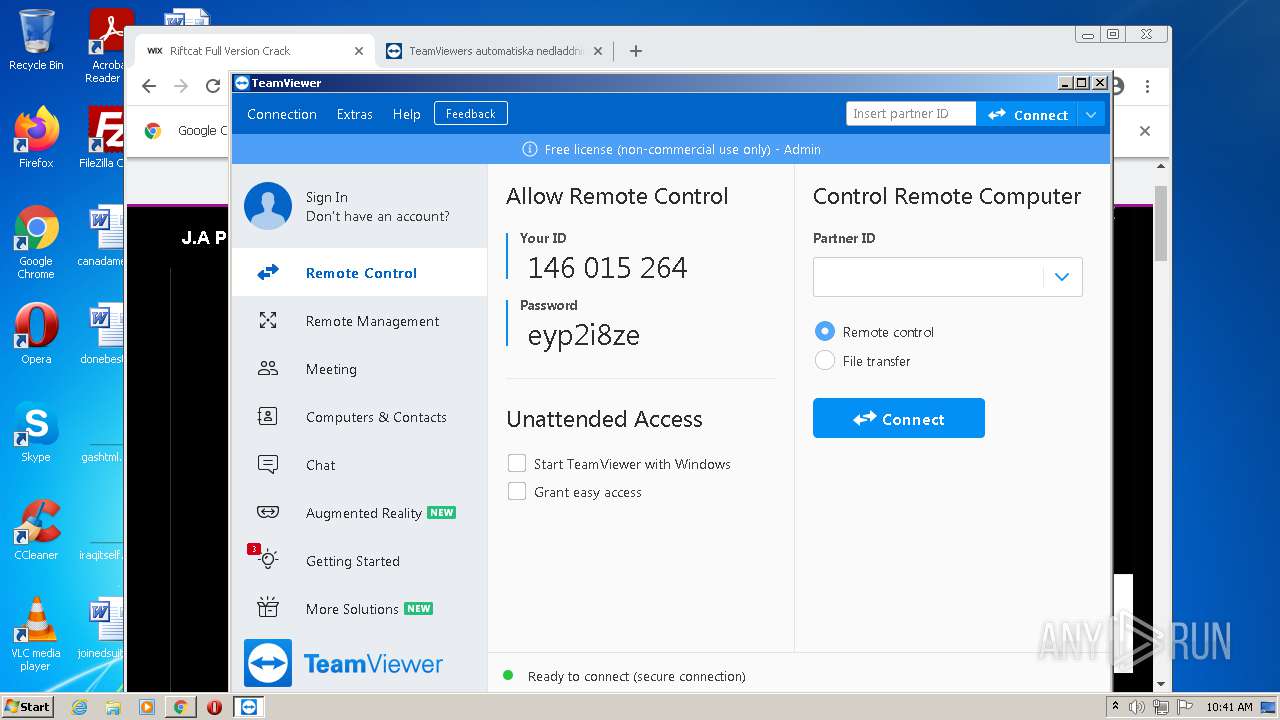
TEAMVIEWER was detected
- TeamViewer_Service.exe (PID: 3028)
SUSPICIOUS
Starts Internet Explorer
- Explorer.EXE (PID: 1896)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 404)
- TeamViewer.exe (PID: 2180)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1896)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1472)
Executable content was dropped or overwritten
- chrome.exe (PID: 1472)
- chrome.exe (PID: 2036)
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
- chrome.exe (PID: 2372)
Checks supported languages
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
- ns7DA8.tmp (PID: 1780)
- TeamViewer_Service.exe (PID: 2216)
- ns7F4F.tmp (PID: 2920)
- ns81B1.tmp (PID: 908)
- TeamViewer.exe (PID: 3008)
- ns89B1.tmp (PID: 2800)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 2180)
- tv_w32.exe (PID: 2076)
- TeamViewer_Desktop.exe (PID: 1140)
- ns5E19.tmp (PID: 3020)
Reads the computer name
- TeamViewer_.exe (PID: 3152)
- TeamViewer_Setup.exe (PID: 2616)
- TeamViewer_.exe (PID: 520)
- TeamViewer_Service.exe (PID: 2216)
- TeamViewer.exe (PID: 3008)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 2180)
- tv_w32.exe (PID: 2076)
- TeamViewer_Desktop.exe (PID: 1140)
Drops a file with too old compile date
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
Application launched itself
- TeamViewer_.exe (PID: 3152)
Starts application with an unusual extension
- TeamViewer_.exe (PID: 520)
Creates a directory in Program Files
- TeamViewer_.exe (PID: 520)
Drops a file that was compiled in debug mode
- TeamViewer_.exe (PID: 520)
- chrome.exe (PID: 2372)
Creates files in the program directory
- TeamViewer_.exe (PID: 520)
- TeamViewer_Service.exe (PID: 3028)
Drops a file with a compile date too recent
- TeamViewer_.exe (PID: 520)
Creates files in the user directory
- TeamViewer_.exe (PID: 520)
- TeamViewer_Service.exe (PID: 2216)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1140)
Creates files in the Windows directory
- TeamViewer_.exe (PID: 520)
- TeamViewer_Service.exe (PID: 3028)
Creates a software uninstall entry
- TeamViewer_.exe (PID: 520)
Changes default file association
- TeamViewer_.exe (PID: 520)
Executed as Windows Service
- TeamViewer_Service.exe (PID: 3028)
Reads the Windows organization settings
- TeamViewer.exe (PID: 2180)
Reads Windows owner or organization settings
- TeamViewer.exe (PID: 2180)
Reads CPU info
- TeamViewer_Desktop.exe (PID: 1140)
INFO
Checks supported languages
- iexplore.exe (PID: 2236)
- taskhost.exe (PID: 1684)
- iexplore.exe (PID: 404)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3768)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 1920)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 868)
- chrome.exe (PID: 1308)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 312)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2192)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 1384)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3528)
- schtasks.exe (PID: 3860)
- regsvr32.exe (PID: 1140)
- schtasks.exe (PID: 476)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 416)
- chrome.exe (PID: 468)
- chrome.exe (PID: 520)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 2596)
Reads the computer name
- iexplore.exe (PID: 2236)
- iexplore.exe (PID: 404)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 3880)
- schtasks.exe (PID: 3860)
- schtasks.exe (PID: 476)
- chrome.exe (PID: 416)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2724)
Application launched itself
- iexplore.exe (PID: 2236)
- chrome.exe (PID: 1472)
Changes internet zones settings
- iexplore.exe (PID: 2236)
Checks Windows Trust Settings
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 2236)
- chrome.exe (PID: 1472)
- TeamViewer_Service.exe (PID: 2216)
- TeamViewer.exe (PID: 3008)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 2180)
- tv_w32.exe (PID: 2076)
- TeamViewer_Desktop.exe (PID: 1140)
Reads settings of System Certificates
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 2236)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 1472)
- TeamViewer_Service.exe (PID: 2216)
- TeamViewer.exe (PID: 3008)
- TeamViewer_Service.exe (PID: 3028)
- TeamViewer.exe (PID: 2180)
- tv_w32.exe (PID: 2076)
- TeamViewer_Desktop.exe (PID: 1140)
Reads the date of Windows installation
- iexplore.exe (PID: 2236)
- chrome.exe (PID: 3080)
Manual execution by user
- chrome.exe (PID: 1472)
Reads the hosts file
- chrome.exe (PID: 1472)
- chrome.exe (PID: 2036)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1472)
Creates files in the user directory
- chrome.exe (PID: 1472)
Reads Microsoft Office registry keys
- TeamViewer_.exe (PID: 3152)
- TeamViewer_.exe (PID: 520)
Changes default file association
- chrome.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
99
Malicious processes
9
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4680 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2236 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4060 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3476 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 476 | C:\Windows\system32\schtasks /Delete /TN TVInstallRestore /F | C:\Windows\system32\schtasks.exe | — | ns89B1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 520 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_.exe" /UAC:30136 /NCRC | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_.exe | TeamViewer_.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: HIGH Description: TeamViewer Remote Control Application Installer Exit code: 0 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 600 | "C:\Windows\system32\Dwm.exe" | C:\Windows\system32\Dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3741616456602892420,5077145455231098977,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
62 209
Read events
60 811
Write events
1 374
Delete events
24
Modification events
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902950 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902950 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
125
Suspicious files
284
Text files
402
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1684 | taskhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-610D0350-5C0.pma | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF41B6D095FDB8554F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6B299EBC14FDDE20.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1684 | taskhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.log | binary | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{30273573-F69A-11EB-B39C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{27935FAC-F69A-11EB-B39C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
174
DNS requests
102
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | chrome.exe | GET | 302 | 5.149.248.70:80 | http://capabresume.com/ZG93bmxvYWR8bGw4TWpFM2ZIdzNOemQ4ZkRrNU9UbDhmRTFQVGxOVVJWSWdWMmw0SUZ0RGFHRnVaMlZrWFNCN2ZR/?dependablity=disciplines.distress.UmlmdGNhdCBGdWxsIFZlcnNpb24gQ3JhY2t0cm1kc2YUml.terms.outhitting | NL | — | — | malicious |
896 | svchost.exe | HEAD | 200 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=157.97.120.10&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1628242579&mv=m&mvi=6&pl=24&rmhost=r2---sn-5goeen7r.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
2036 | chrome.exe | GET | 302 | 5.149.248.70:80 | http://capabresume.com/ZG93bmxvYWR8bGw4TWpFM2ZIdzNOemQ4ZkRrNU9UbDhmRTFQVGxOVVJWSWdWMmw0SUZ0RGFHRnVaMlZrWFNCN2ZR/?dependablity=disciplines.distress.UmlmdGNhdCBGdWxsIFZlcnNpb24gQ3JhY2t0cm1kc2YUml.terms.outhitting | NL | — | — | malicious |
2036 | chrome.exe | GET | 302 | 5.149.248.70:80 | http://capabresume.com/ZG93bmxvYWR8bGw4TWpFM2ZIdzNOemQ4ZkRrNU9UbDhmRTFQVGxOVVJWSWdWMmw0SUZ0RGFHRnVaMlZrWFNCN2ZR/?dependablity=disciplines.distress.UmlmdGNhdCBGdWxsIFZlcnNpb24gQ3JhY2t0cm1kc2YUml.terms.outhitting | NL | — | — | malicious |
896 | svchost.exe | GET | 206 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=157.97.120.10&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1628242579&mv=m&mvi=6&pl=24&rmhost=r2---sn-5goeen7r.gvt1.com&shardbypass=yes | US | binary | 9.44 Kb | whitelisted |
896 | svchost.exe | GET | 206 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=157.97.120.10&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1628242579&mv=m&mvi=6&pl=24&rmhost=r2---sn-5goeen7r.gvt1.com&shardbypass=yes | US | binary | 9.42 Kb | whitelisted |
2236 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
896 | svchost.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 512 b | whitelisted |
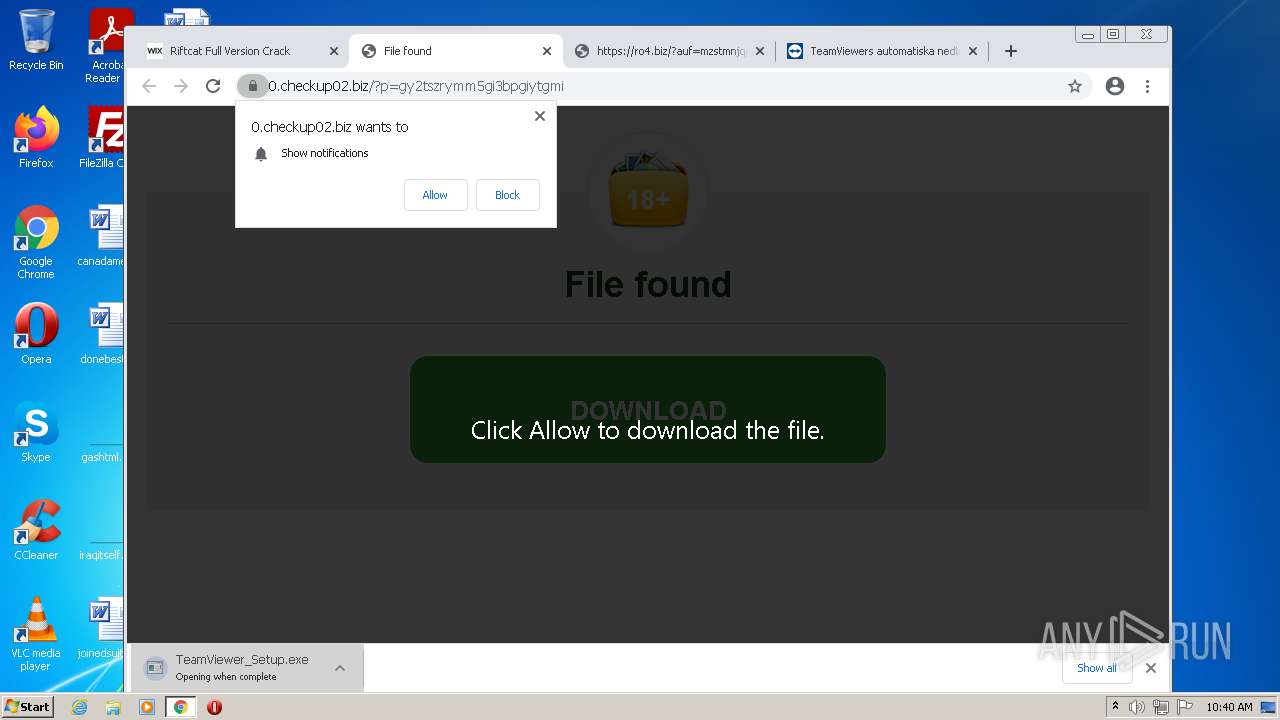
2036 | chrome.exe | GET | 302 | 5.149.248.110:80 | http://fancli.com/19j0hr | NL | html | 1.31 Kb | malicious |
896 | svchost.exe | GET | 206 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=157.97.120.10&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1628242821&mv=m&mvi=6&pl=24&rmhost=r2---sn-5goeen7r.gvt1.com&shardbypass=yes | US | binary | 5.76 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2036 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2036 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2036 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
404 | iexplore.exe | 35.242.251.130:443 | riafrenvargipuwhi.wixsite.com | — | US | malicious |
404 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
404 | iexplore.exe | 8.253.95.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2236 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2036 | chrome.exe | 185.230.61.163:443 | www.wix.com | — | — | suspicious |
2036 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2036 | chrome.exe | 172.217.20.46:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
riafrenvargipuwhi.wixsite.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
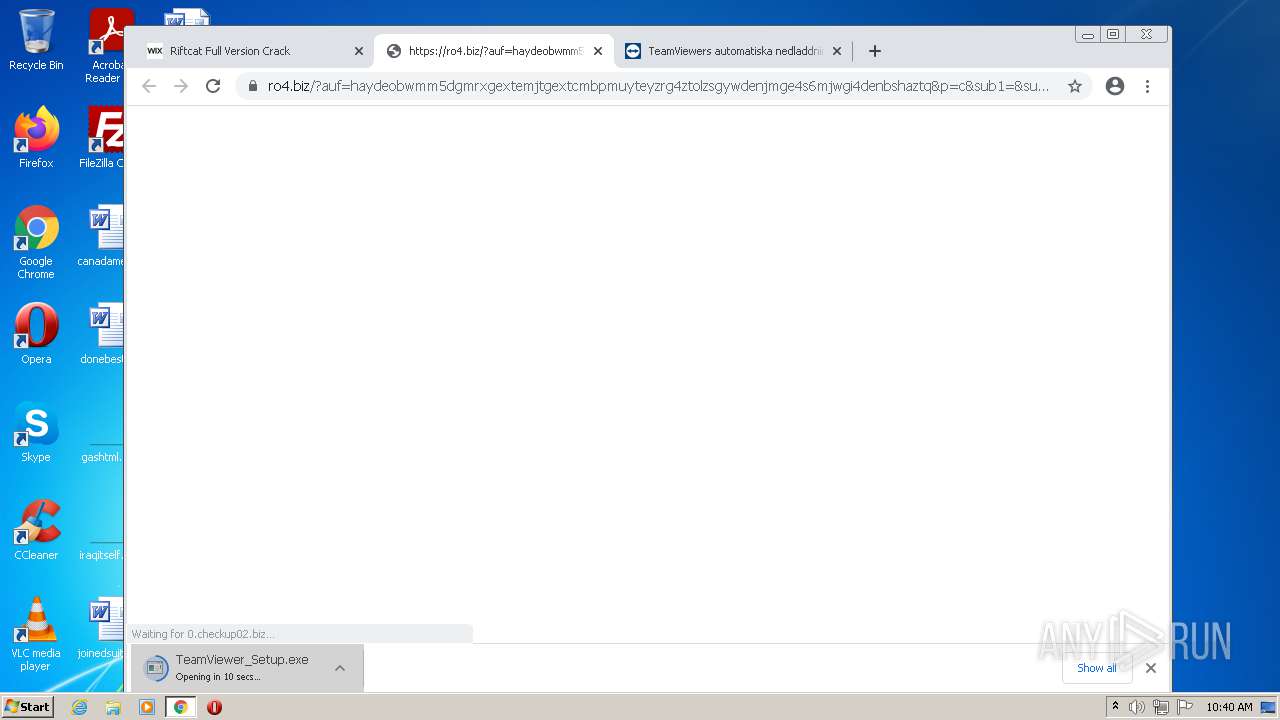
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3028 | TeamViewer_Service.exe | Misc activity | AV POLICY TeamViewer Keep-alive inbound |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
2036 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.cf) in TLS SNI |