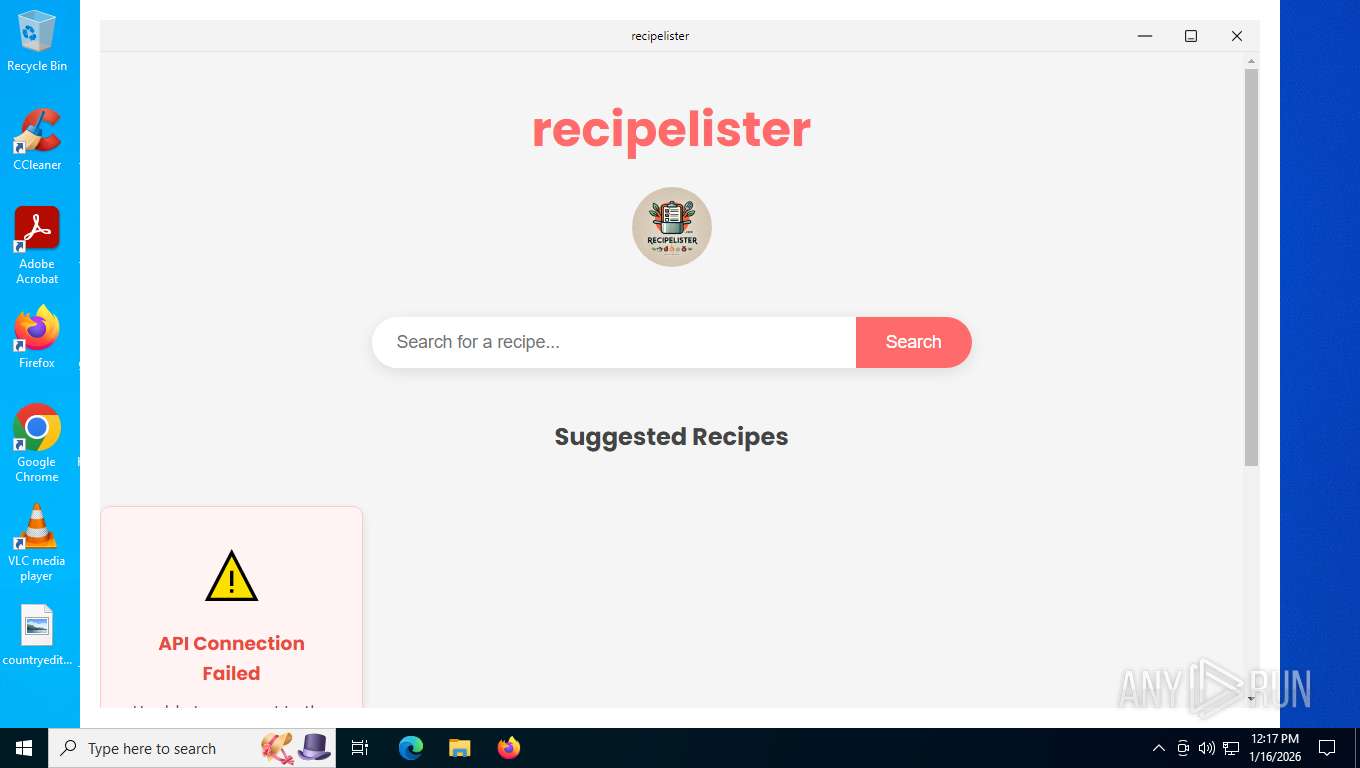
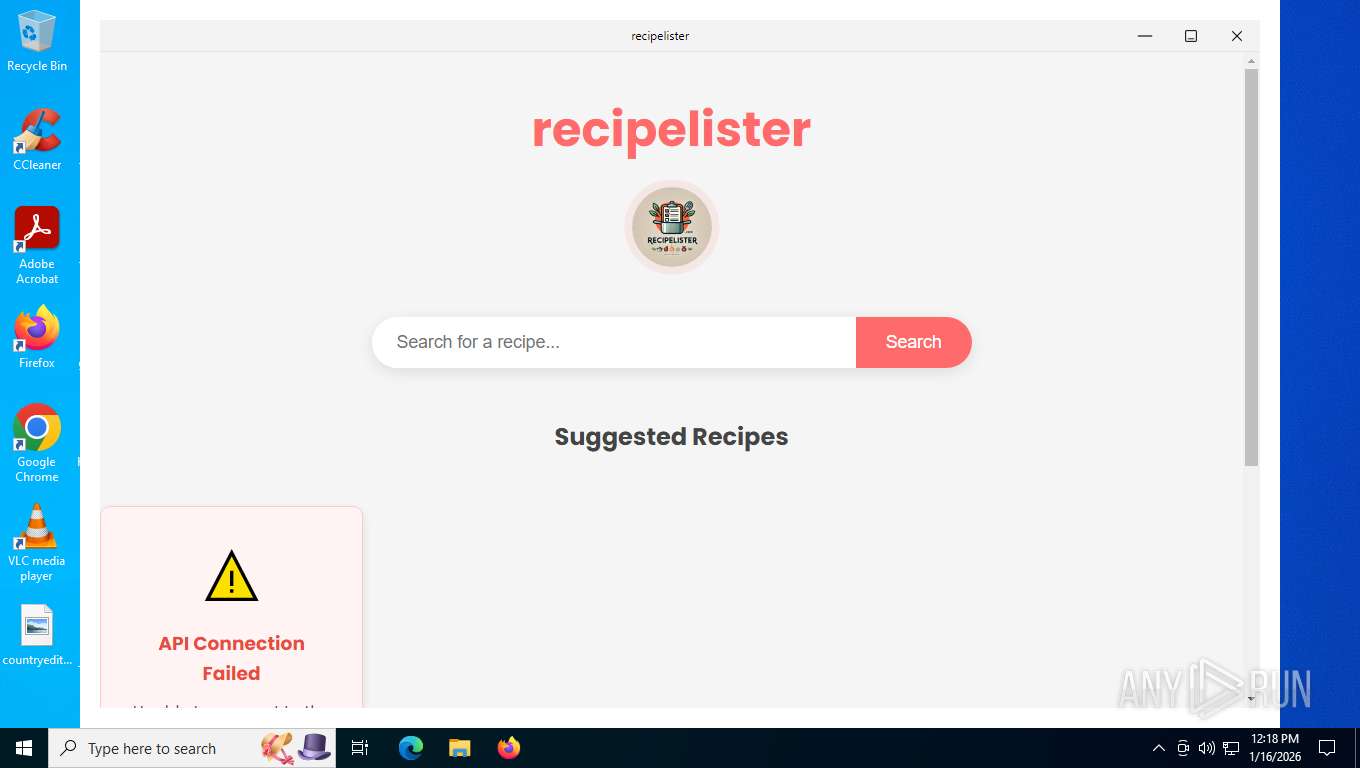
| File name: | RecipeLister.exe |
| Full analysis: | https://app.any.run/tasks/e693718d-56c0-4672-bd59-40927cc96fca |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2026, 17:17:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 8C21CEFCD6B32FACE145ED801F256589 |
| SHA1: | 53076D20B5F36FD8B69A0507D5CB08C0965DB4A2 |
| SHA256: | 1619BCAD3785BE31AC2FDEE0AB91392D08D9392032246E42673C3CB8964D4CB7 |
| SSDEEP: | 786432:ga7wj/+HAgZZspLEW45ADXsRSoRtOZWZ6NBcO2CNk9YdT:pbgEW4mDXsRSkOZK6NBcO2CNkET |
MALICIOUS
GENERIC has been found (auto)
- RecipeLister.exe (PID: 7748)
Executing a file with an untrusted certificate
- RecipeLister.exe (PID: 7748)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- RecipeLister.exe (PID: 7748)
The process creates files with name similar to system file names
- RecipeLister.exe (PID: 7748)
Process drops legitimate windows executable
- RecipeLister.exe (PID: 7748)
Malware-specific behavior (creating "System.dll" in Temp)
- RecipeLister.exe (PID: 7748)
Reads security settings of Internet Explorer
- RecipeLister.exe (PID: 7748)
Application launched itself
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Executable content was dropped or overwritten
- RecipeLister.exe (PID: 7748)
There is functionality for taking screenshot (YARA)
- RecipeLister.exe (PID: 7748)
INFO
Reads the computer name
- Recipe Finder - Recipe Lister.exe (PID: 8068)
- RecipeLister.exe (PID: 7748)
- Recipe Finder - Recipe Lister.exe (PID: 2624)
- Recipe Finder - Recipe Lister.exe (PID: 7496)
Create files in a temporary directory
- RecipeLister.exe (PID: 7748)
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Checks supported languages
- Recipe Finder - Recipe Lister.exe (PID: 8068)
- RecipeLister.exe (PID: 7748)
- Recipe Finder - Recipe Lister.exe (PID: 2624)
- Recipe Finder - Recipe Lister.exe (PID: 7496)
- Recipe Finder - Recipe Lister.exe (PID: 2164)
Checks proxy server information
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Reads Environment values
- Recipe Finder - Recipe Lister.exe (PID: 8068)
The sample compiled with english language support
- RecipeLister.exe (PID: 7748)
Reads product name
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Creates files or folders in the user directory
- Recipe Finder - Recipe Lister.exe (PID: 7496)
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Reads the machine GUID from the registry
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Process checks computer location settings
- Recipe Finder - Recipe Lister.exe (PID: 2164)
- Recipe Finder - Recipe Lister.exe (PID: 8068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:26:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 473088 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Recipe finder app powered by recipelister.com |
| FileVersion: | 1.0.0 |
| LegalCopyright: | Copyright © 2025 Recipe Finder - Recipe Lister |
| ProductName: | Recipe Finder - Recipe Lister |
| ProductVersion: | 1.0.0 |
Total processes
138
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2164 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --app-path="C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2908 --field-trial-handle=1720,i,786075692474534895,7672746713975210248,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:1 | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | Recipe Finder - Recipe Lister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1716 --field-trial-handle=1720,i,786075692474534895,7672746713975210248,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | Recipe Finder - Recipe Lister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 7184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7496 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --mojo-platform-channel-handle=2076 --field-trial-handle=1720,i,786075692474534895,7672746713975210248,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | Recipe Finder - Recipe Lister.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 7748 | "C:\Users\admin\Desktop\RecipeLister.exe" | C:\Users\admin\Desktop\RecipeLister.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Recipe finder app powered by recipelister.com Version: 1.0.0 Modules
| |||||||||||||||
| 8068 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | RecipeLister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
Total events
2 316
Read events
2 298
Write events
0
Delete events
18
Modification events
| (PID) Process: | (8068) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (8068) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (8068) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
Executable files
17
Suspicious files
139
Text files
15
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\LICENSE.electron.txt | text | |
MD5:4D42118D35941E0F664DDDBD83F633C5 | SHA256:5154E165BD6C2CC0CFBCD8916498C7ABAB0497923BAFCD5CB07673FE8480087D | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\nsis7z.dll | executable | |
MD5:80E44CE4895304C6A3A831310FBF8CD0 | SHA256:B393F05E8FF919EF071181050E1873C9A776E1A0AE8329AEFFF7007D0CADF592 | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\chrome_100_percent.pak | binary | |
MD5:4FC6564B727BAA5FECF6BF3F6116CC64 | SHA256:B7805392BFCE11118165E3A4E747AC0CA515E4E0CEADAB356D685575F6AA45FB | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\chrome_200_percent.pak | binary | |
MD5:47668AC5038E68A565E0A9243DF3C9E5 | SHA256:FAC820A98B746A04CE14EC40C7268D6A58819133972B538F9720A5363C862E32 | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\locales\af.pak | binary | |
MD5:862A2262D0E36414ABBAE1D9DF0C7335 | SHA256:57670EAE6D1871E648AD6148125EE82D08575BEC5B323459FC14C3831570774A | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 7748 | RecipeLister.exe | C:\Users\admin\AppData\Local\Temp\nskEB23.tmp\7z-out\locales\es-419.pak | binary | |
MD5:088DE6D12071EA5CF8D4A618ED45E7D5 | SHA256:D1019C780E836E0C30FE01928D23ECDD0CA04ED8EE886ADB3428E3683E4ED6EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
28
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7568 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7568 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.82:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5480 | svchost.exe | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
5480 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5480 | svchost.exe | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
5984 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 1.43 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.82:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 184.30.158.70:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 184.30.158.70:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5480 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5480 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
5984 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
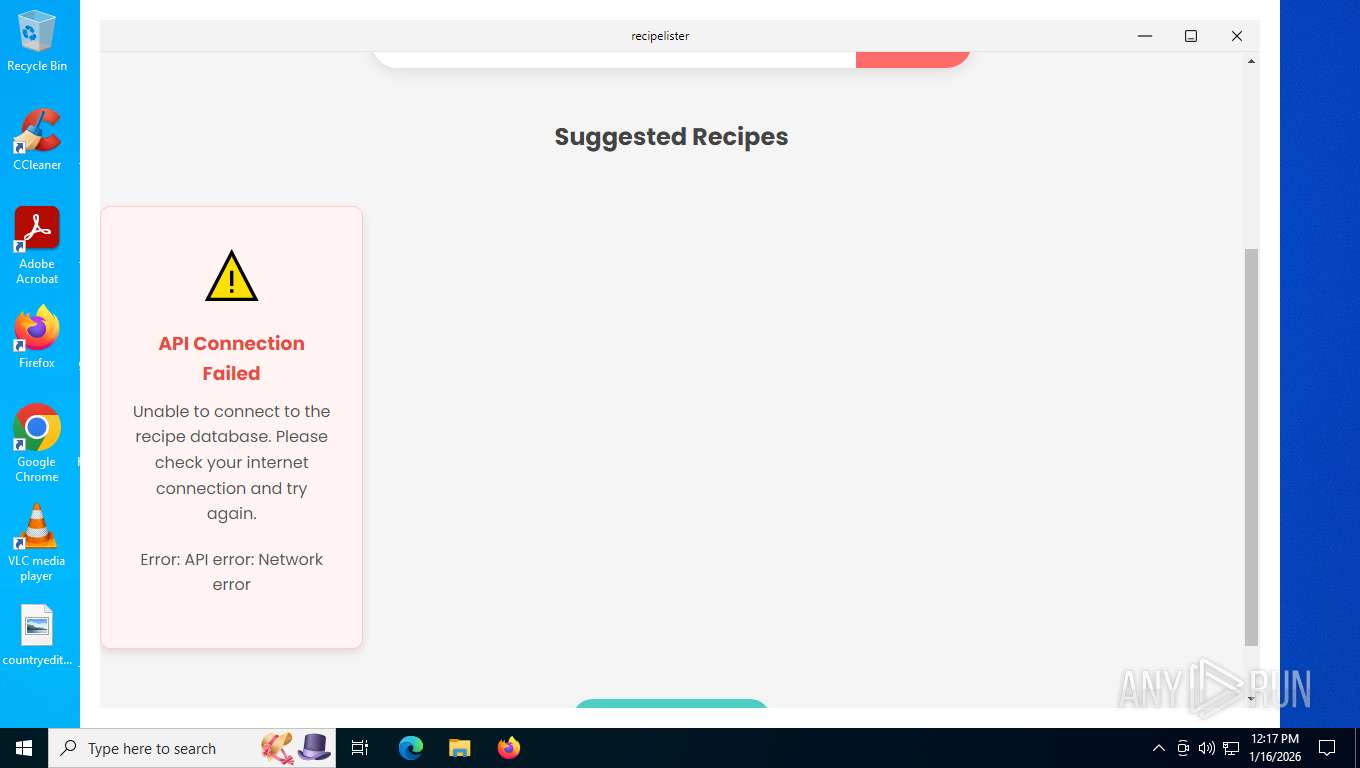
recipelister.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |