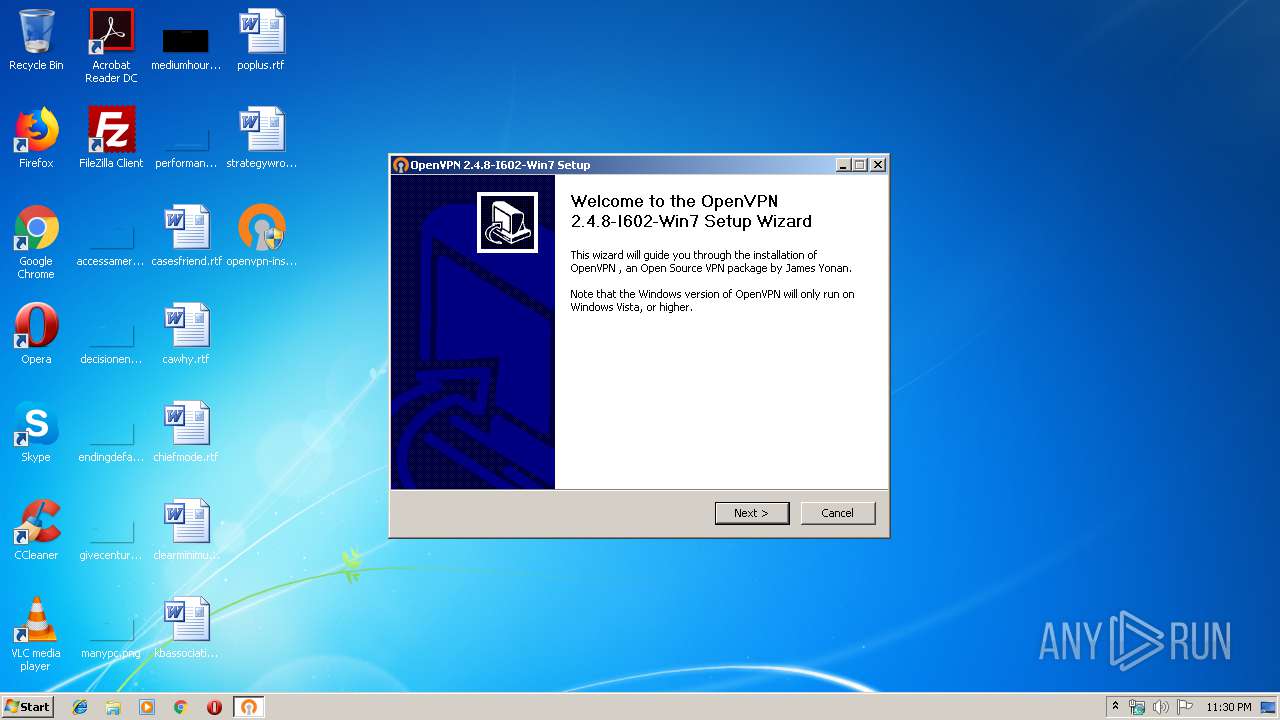
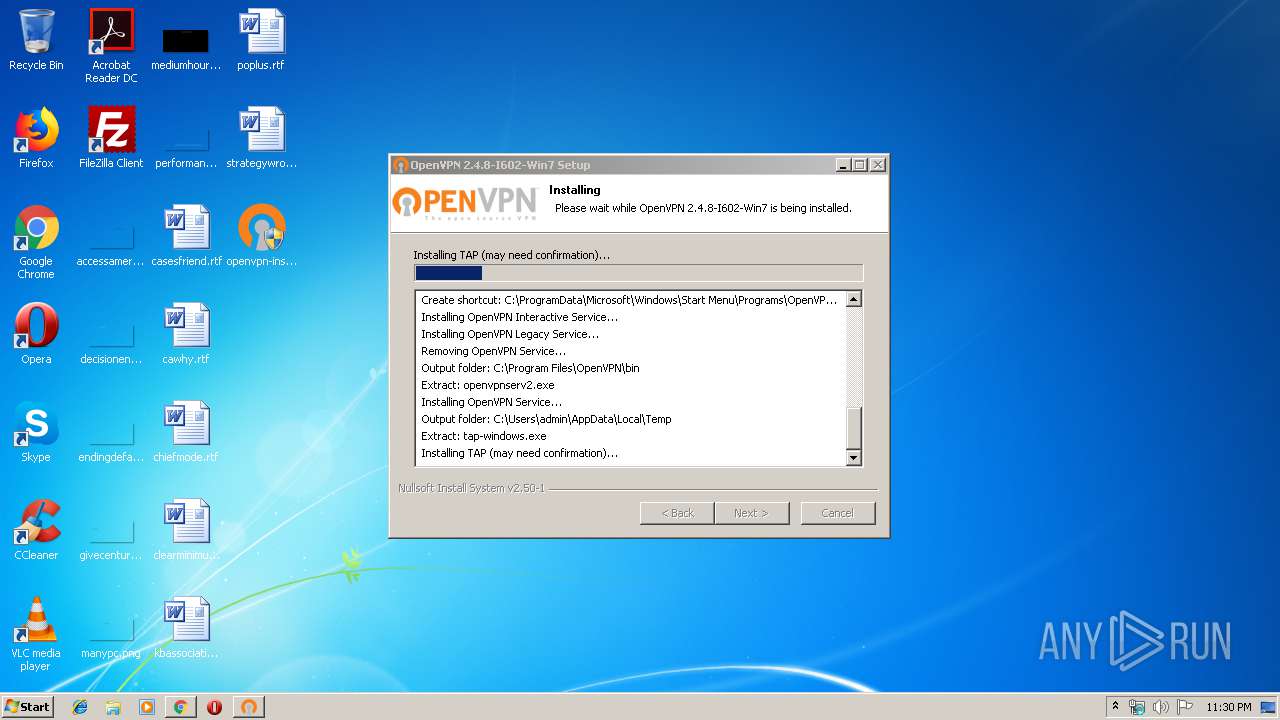
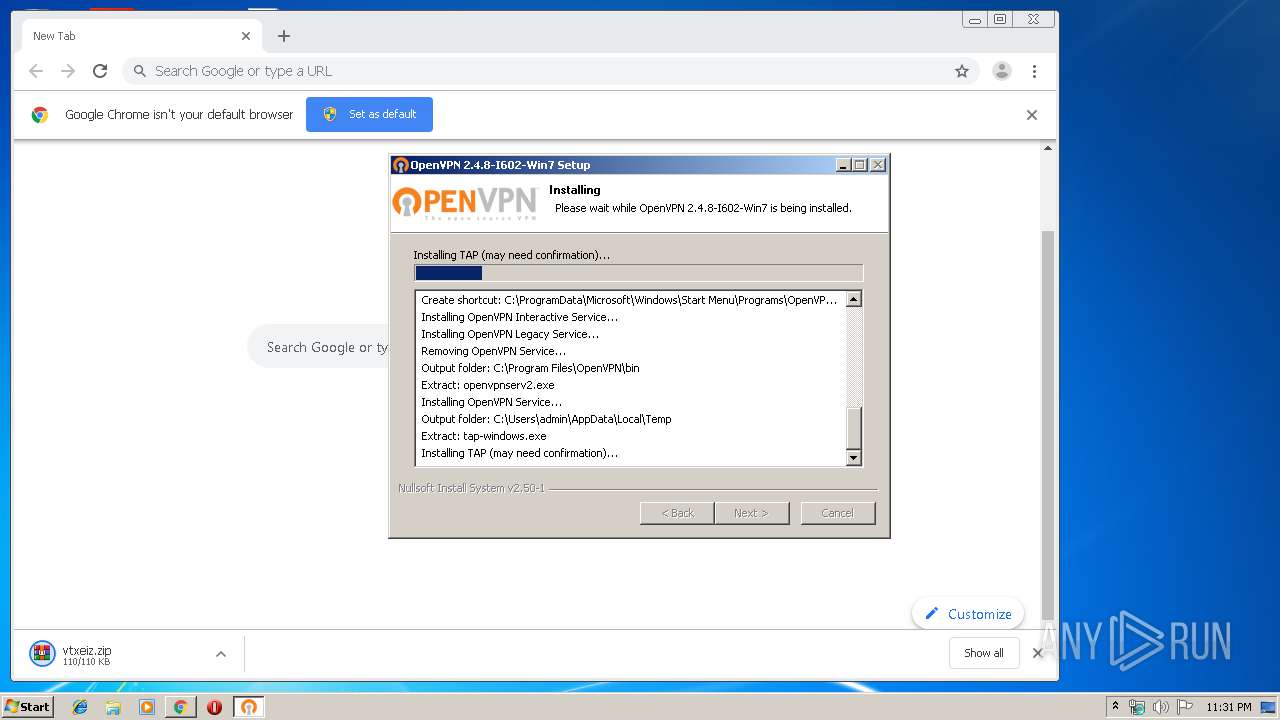
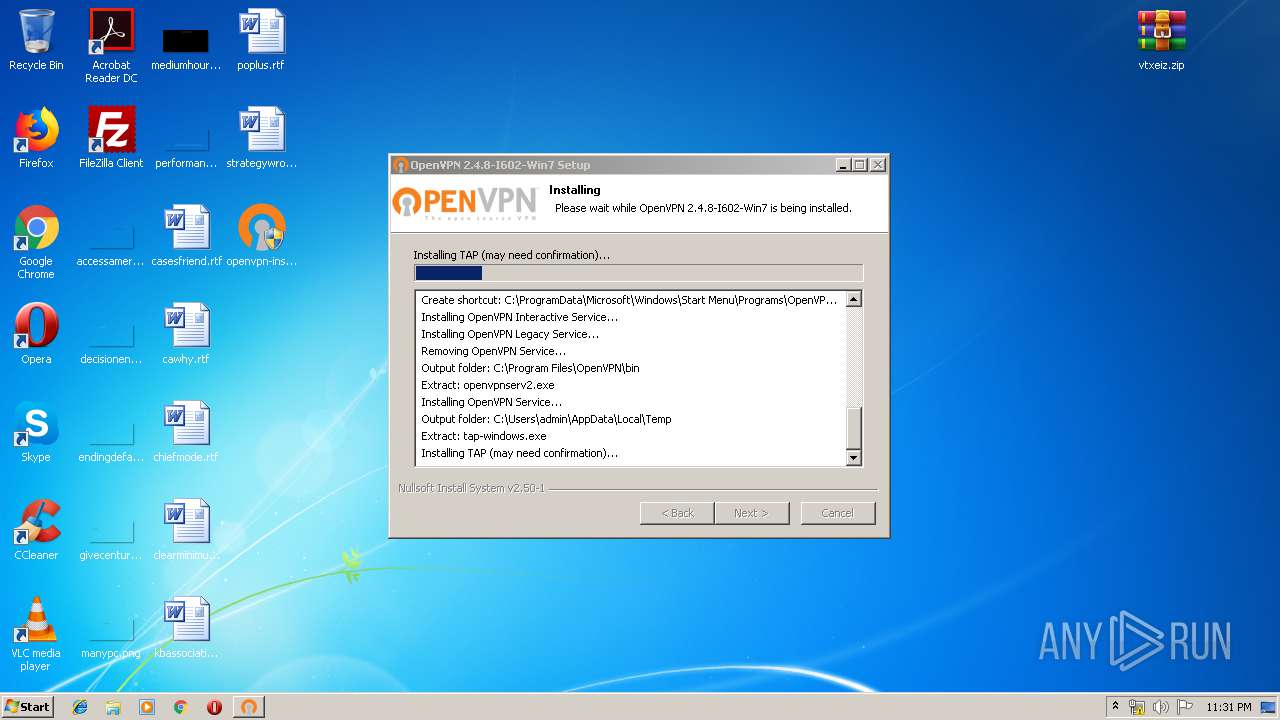
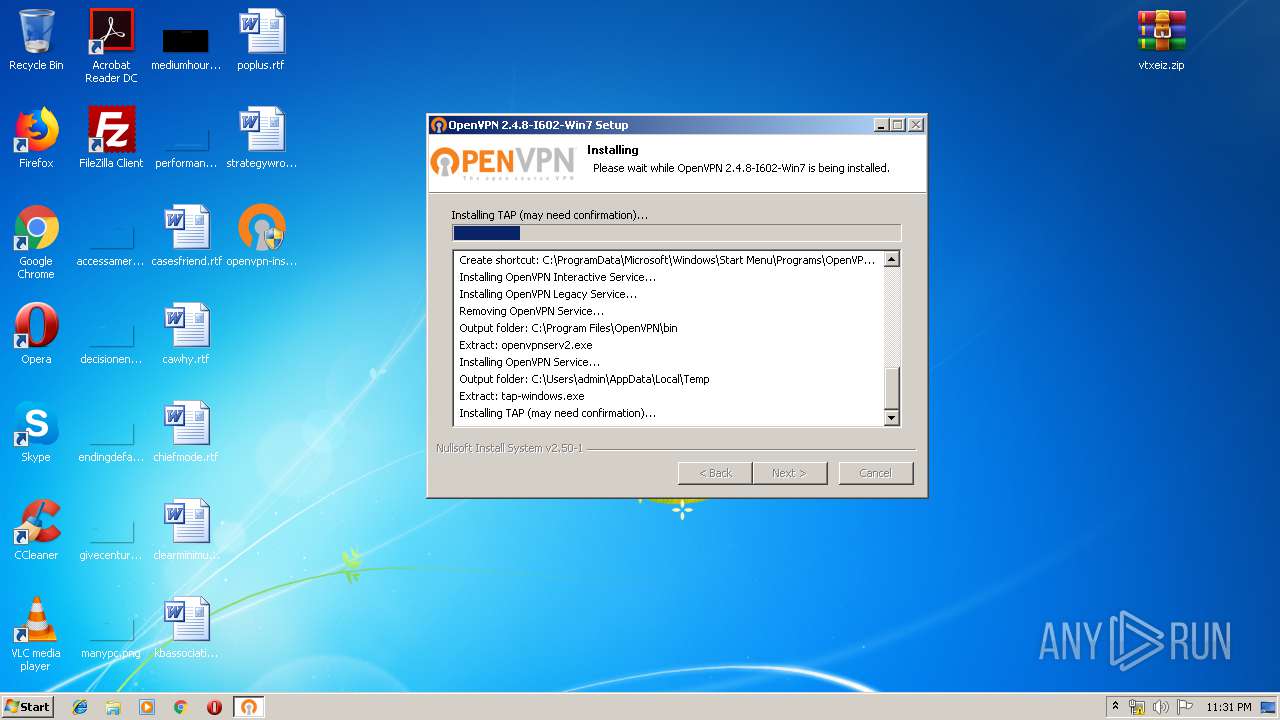
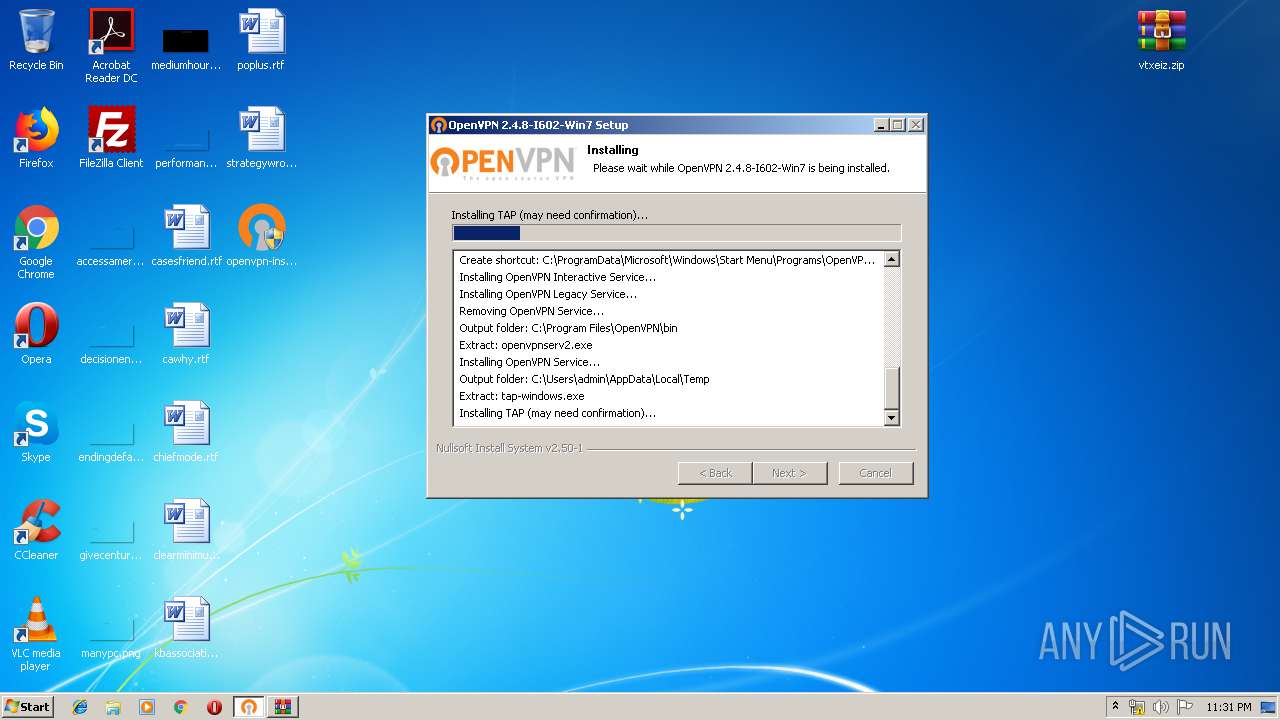
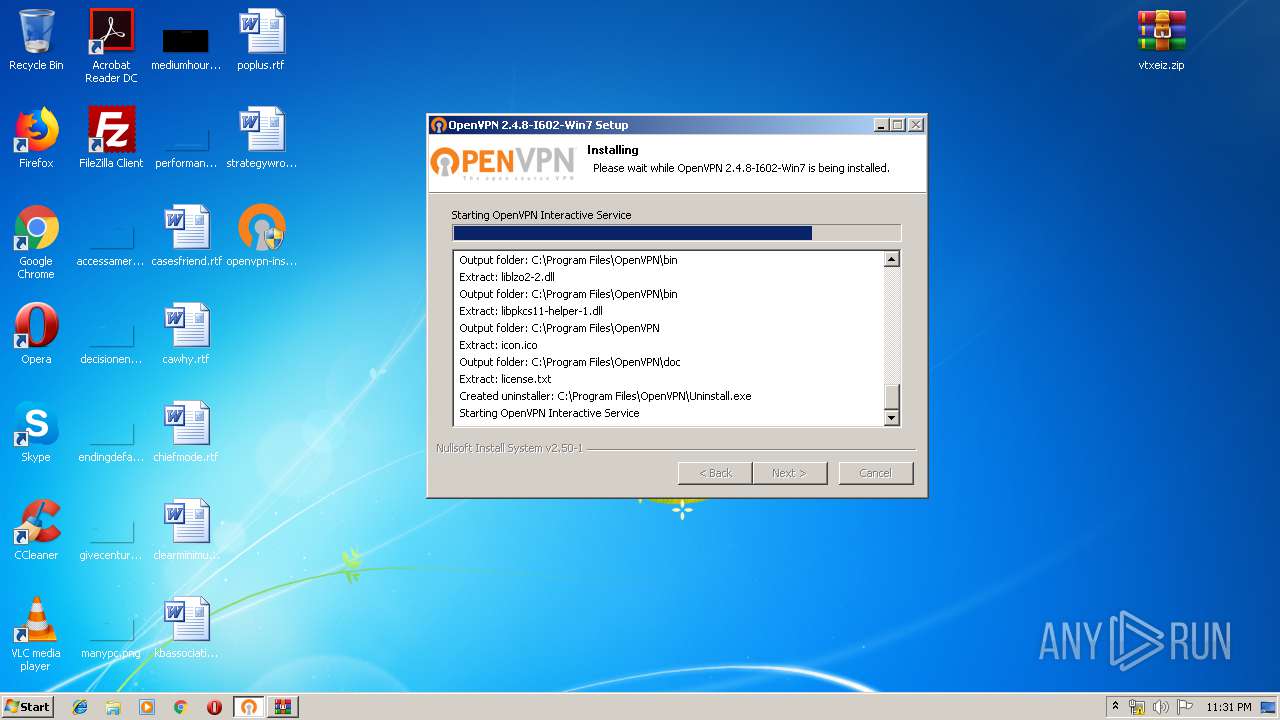
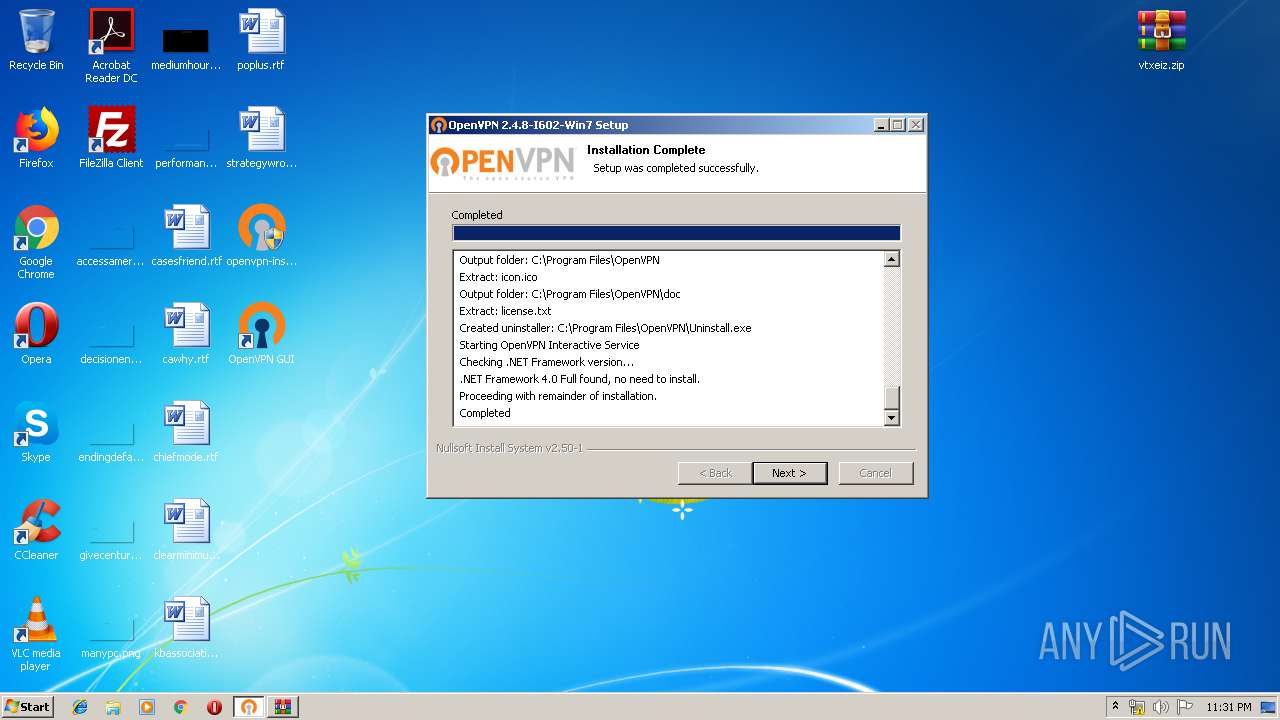
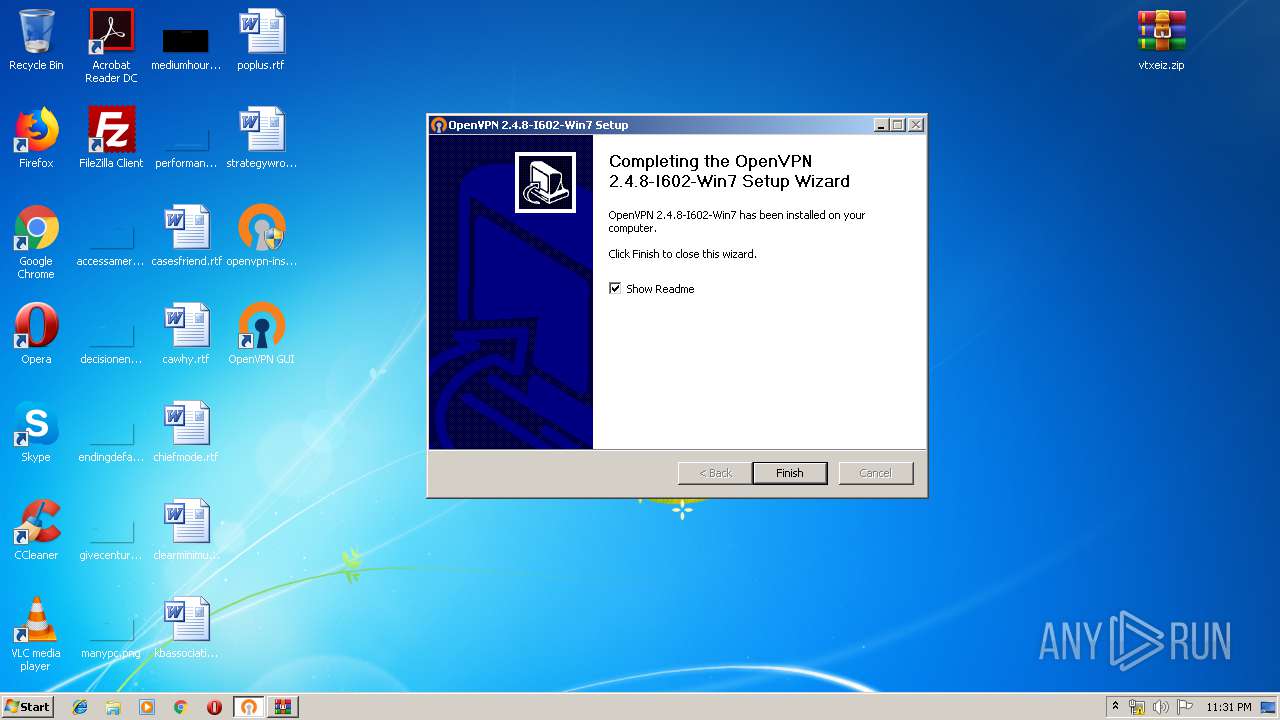
| File name: | openvpn-install-2.4.8-I602-Win7.exe |
| Full analysis: | https://app.any.run/tasks/fbbef183-64cf-4e2c-a405-aed909f89dc9 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 23:29:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 73BCD5B6A0208D953A38ED74FDEF5FF1 |
| SHA1: | 8C9F28D7BDBB4613777A9741809E34B91FD45A0F |
| SHA256: | 16165E4505874E71C9FE732041274C3CE10E0881DFEEECE529E8B54C5B558296 |
| SSDEEP: | 98304:VvSASt7w80xv6bfJh1Gxt9cbPqJH8eNzuJm6wH+bj:hSdNw80aJEtTJH1NzcUHu |
MALICIOUS
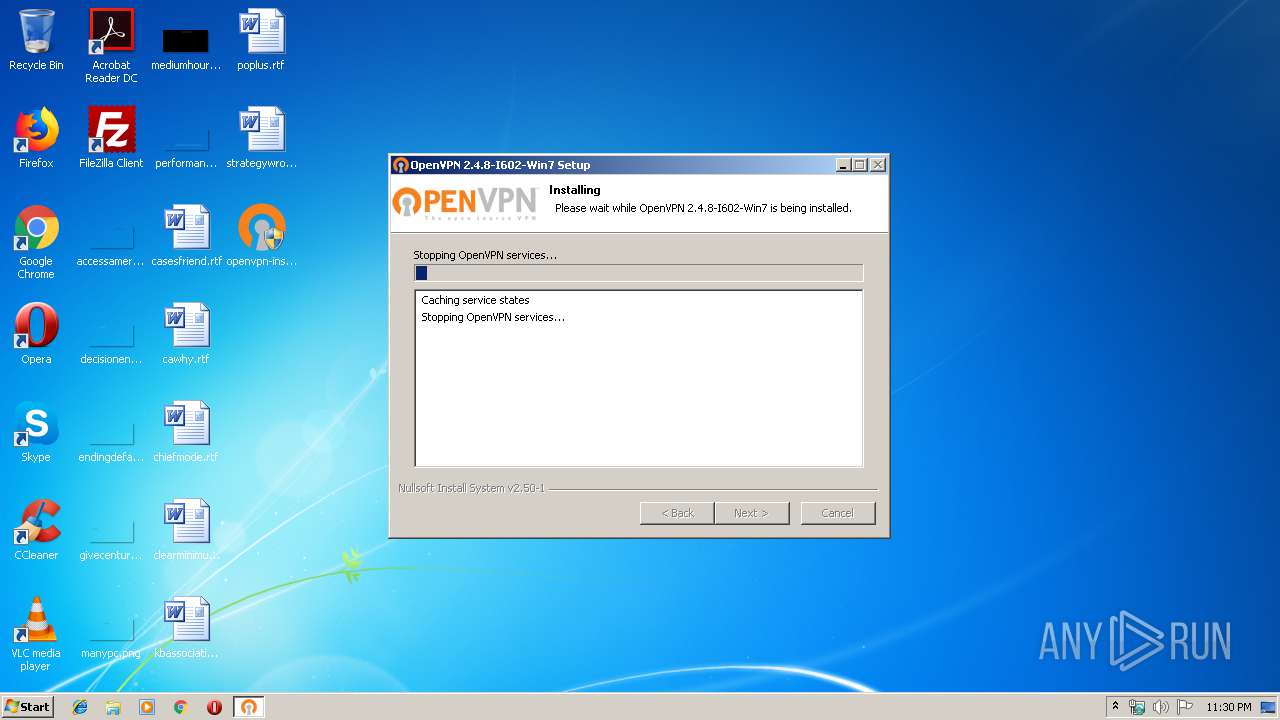
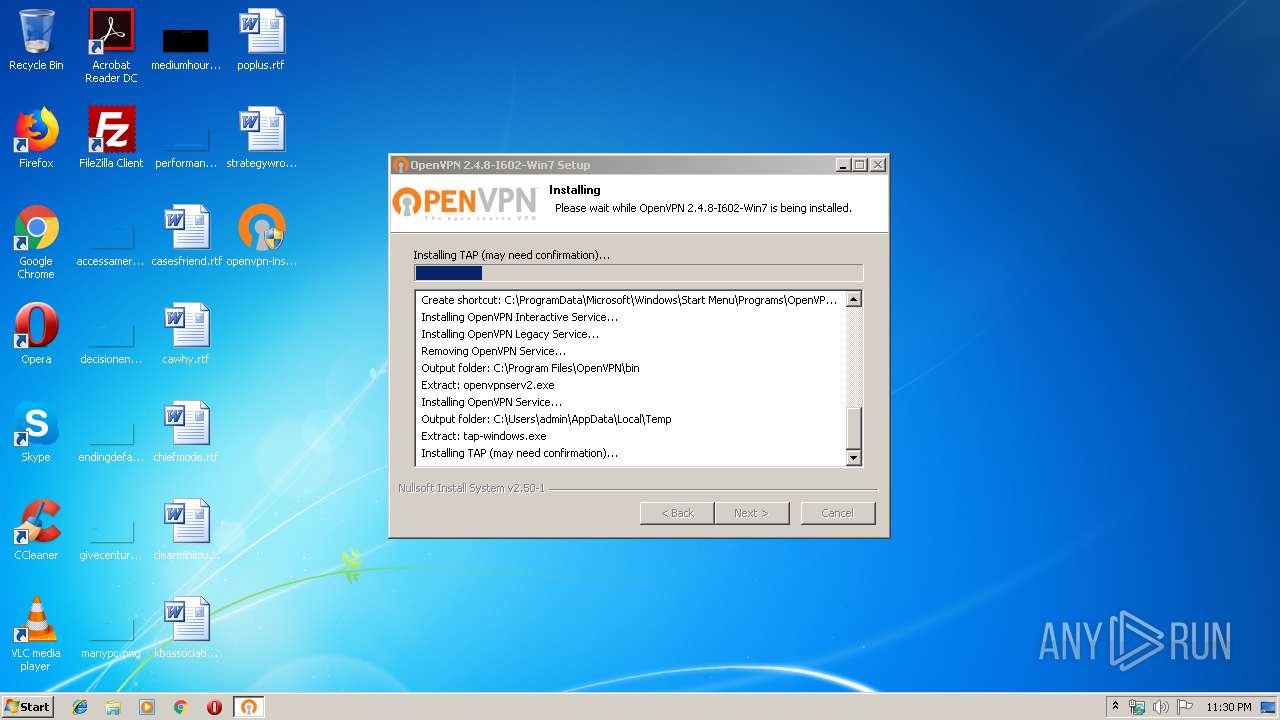
Loads dropped or rewritten executable
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
- tap-windows.exe (PID: 3696)
- openvpn.exe (PID: 952)
- openvpn-gui.exe (PID: 4048)
- openvpn.exe (PID: 3764)
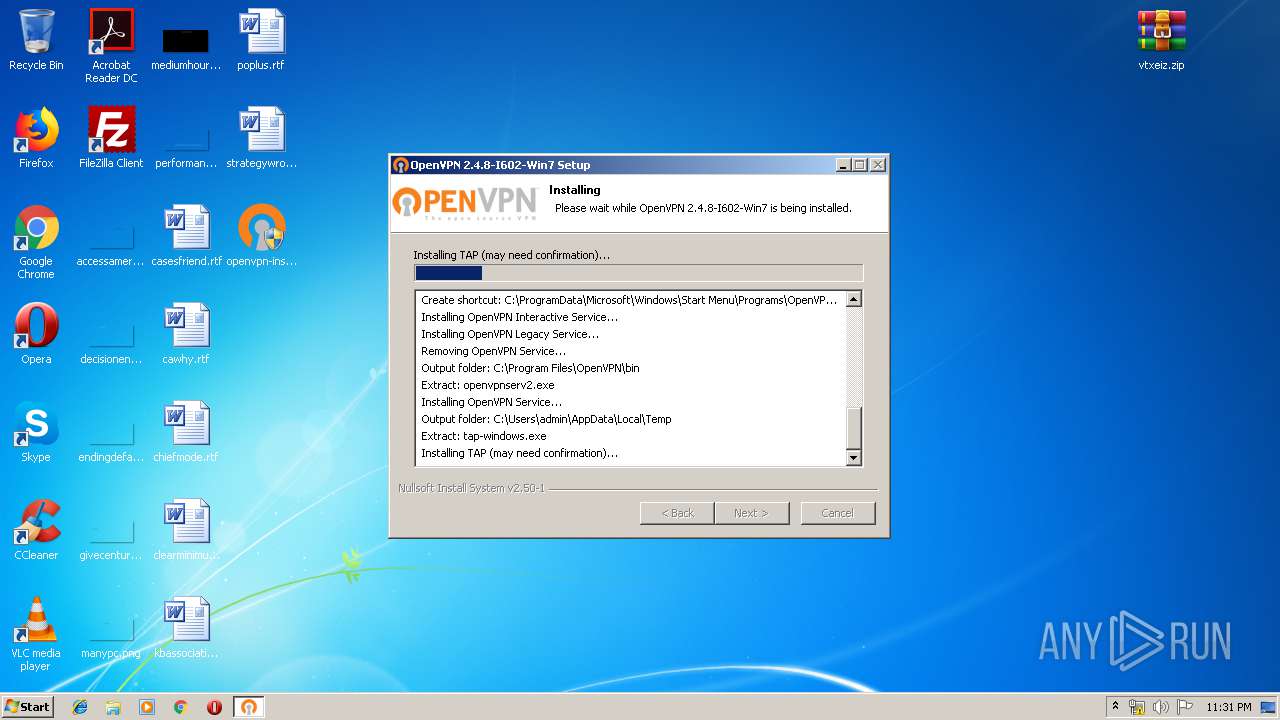
Application was dropped or rewritten from another process
- nsED3C.tmp (PID: 2040)
- tap-windows.exe (PID: 3696)
- nsF626.tmp (PID: 3956)
- tapinstall.exe (PID: 1728)
- nsF1C0.tmp (PID: 3900)
- tapinstall.exe (PID: 1972)
- openvpnserv.exe (PID: 1852)
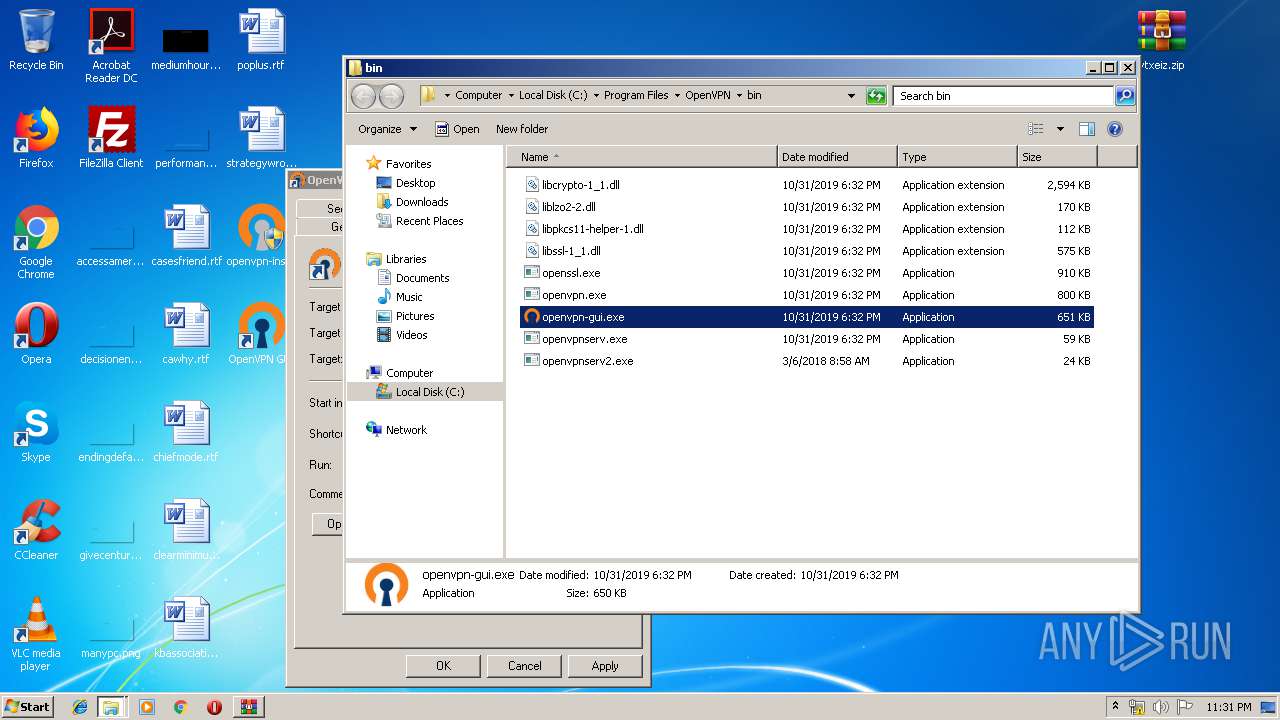
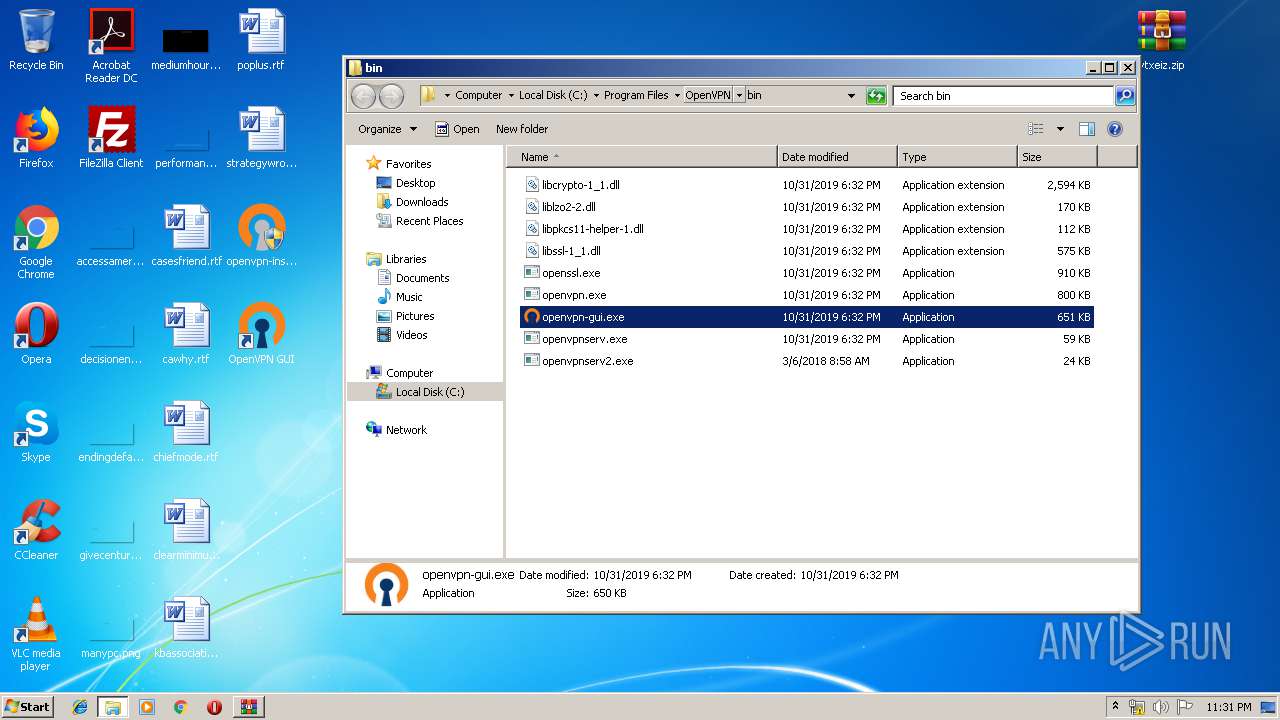
- openvpn-gui.exe (PID: 4048)
- openvpn.exe (PID: 952)
- openvpn.exe (PID: 3764)
Changes the autorun value in the registry
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
SUSPICIOUS
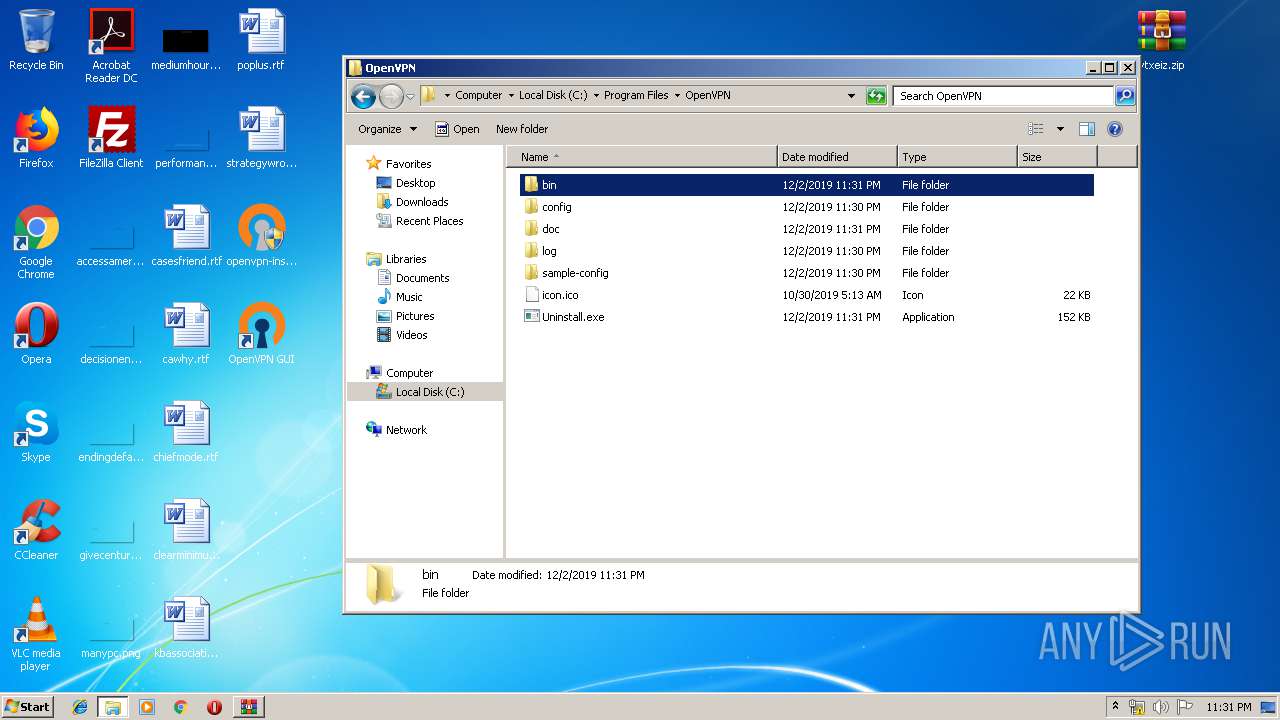
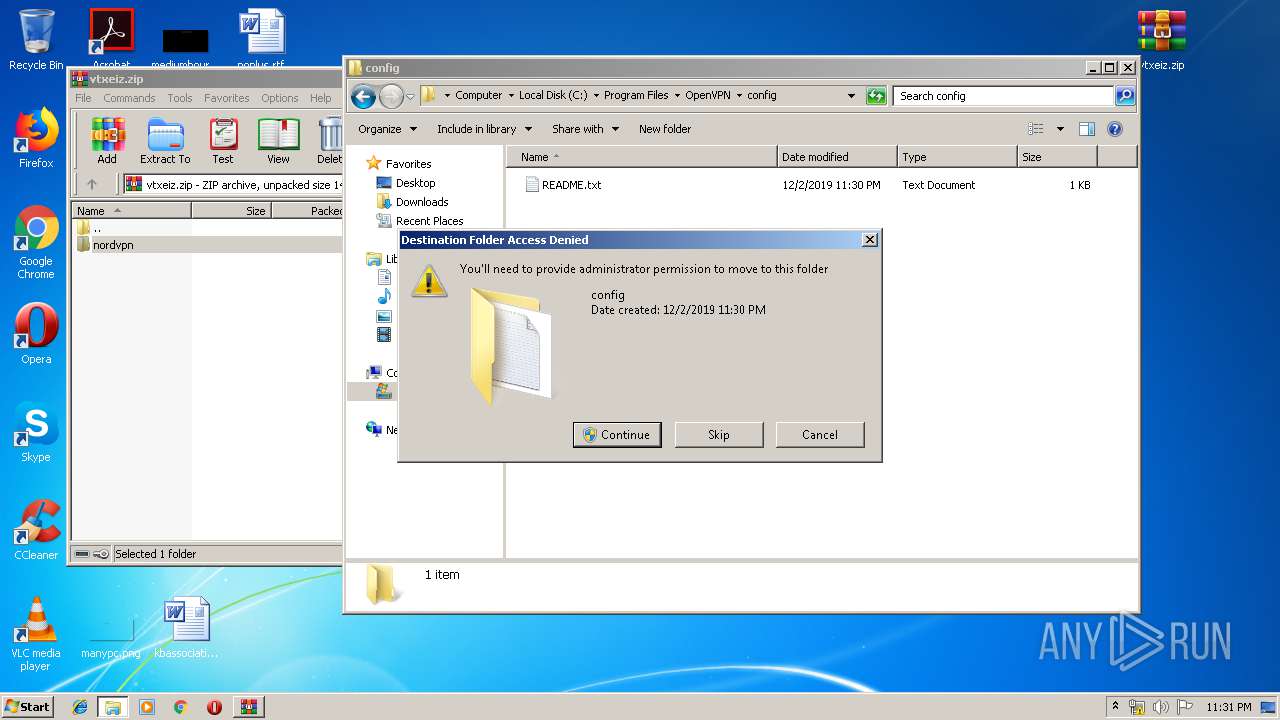
Creates files in the program directory
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
- tap-windows.exe (PID: 3696)
Executable content was dropped or overwritten
- tap-windows.exe (PID: 3696)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
- tapinstall.exe (PID: 1972)
- DrvInst.exe (PID: 1796)
- DrvInst.exe (PID: 2848)
Starts application with an unusual extension
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
- tap-windows.exe (PID: 3696)
Executed via COM
- DrvInst.exe (PID: 1796)
- DrvInst.exe (PID: 2848)
- DllHost.exe (PID: 2728)
Removes files from Windows directory
- DrvInst.exe (PID: 1796)
- DrvInst.exe (PID: 2848)
Creates files in the driver directory
- DrvInst.exe (PID: 1796)
- DrvInst.exe (PID: 2848)
Creates files in the Windows directory
- DrvInst.exe (PID: 1796)
- DrvInst.exe (PID: 2848)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 1796)
Executed as Windows Service
- vssvc.exe (PID: 688)
- openvpnserv.exe (PID: 1852)
Creates a software uninstall entry
- tap-windows.exe (PID: 3696)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
Modifies the open verb of a shell class
- openvpn-install-2.4.8-I602-Win7.exe (PID: 616)
INFO
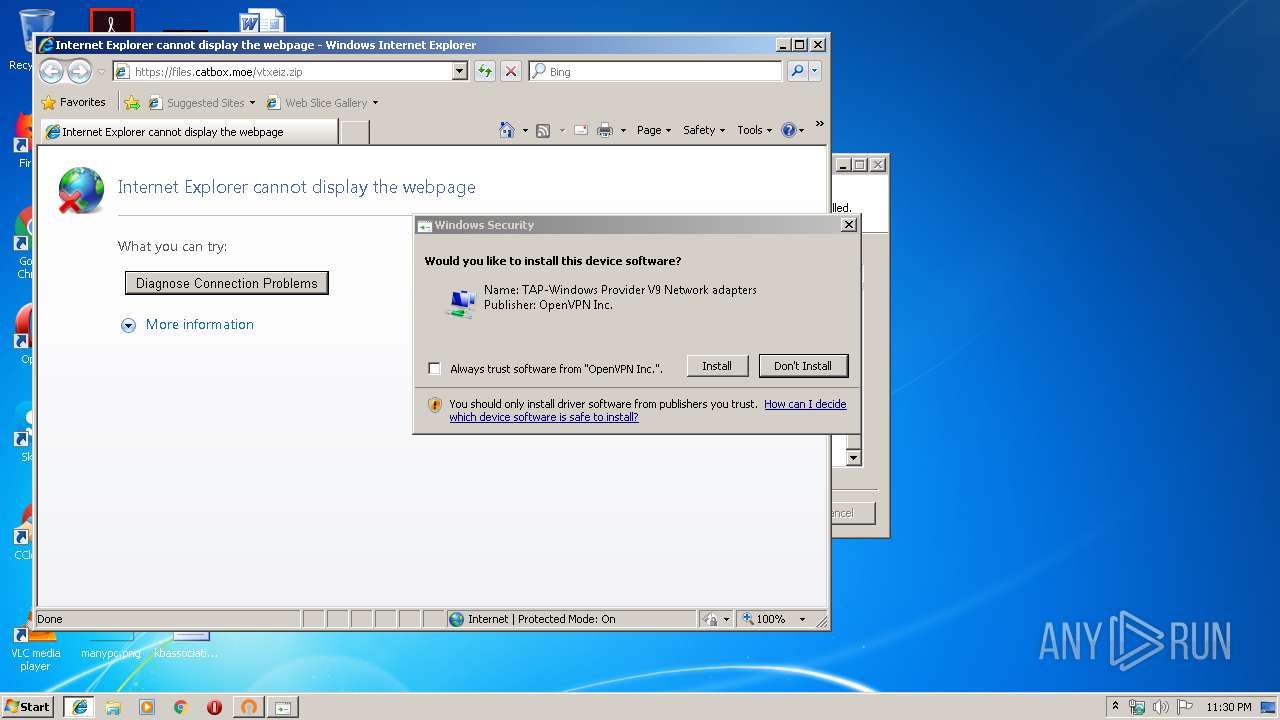
Changes internet zones settings
- iexplore.exe (PID: 4032)
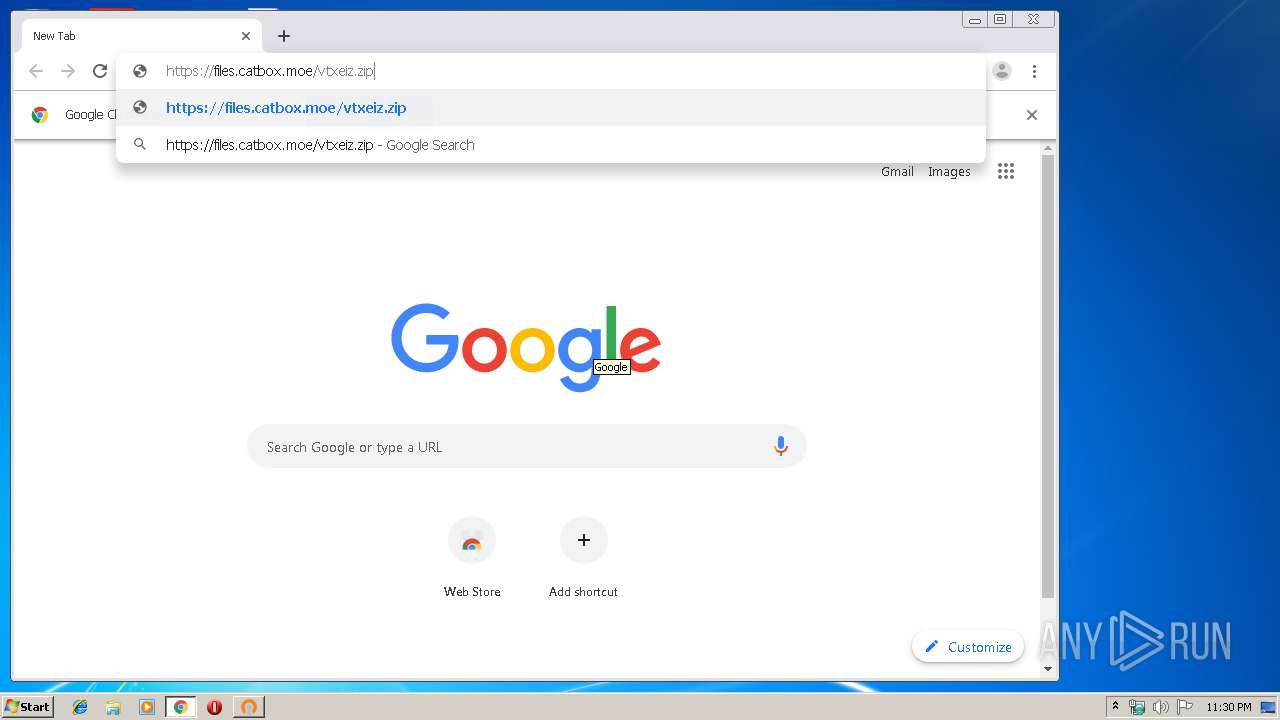
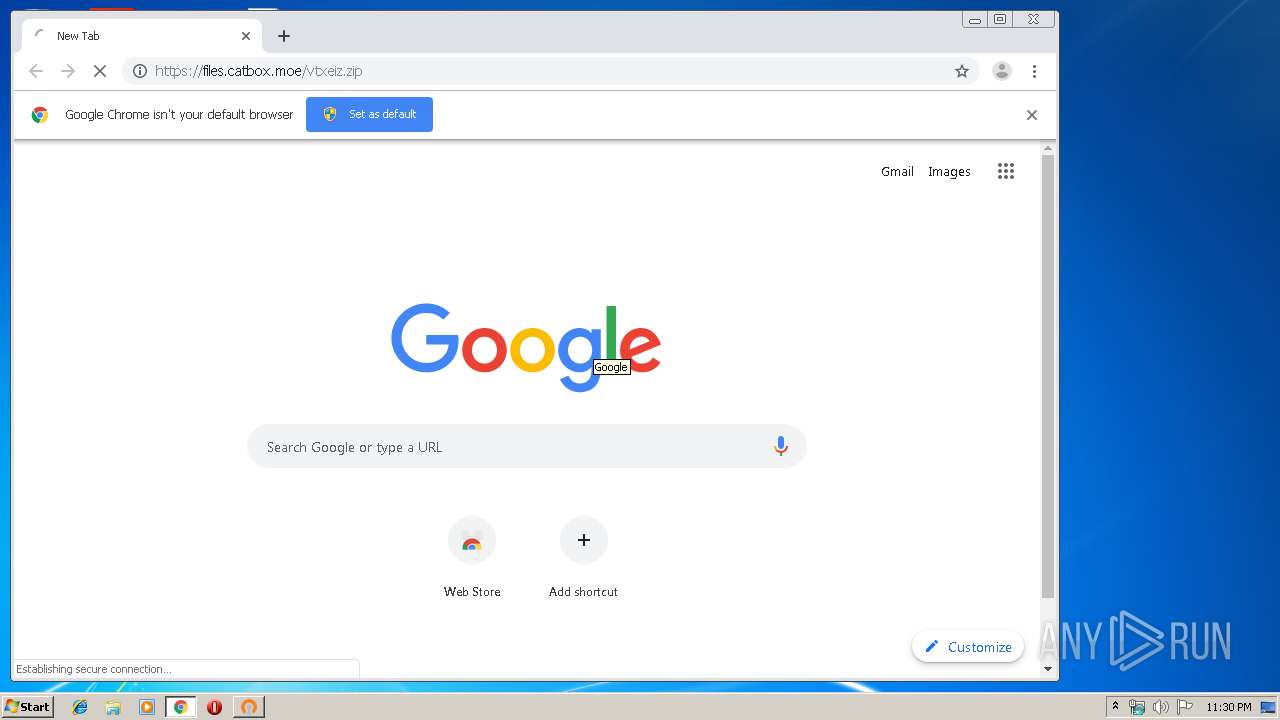
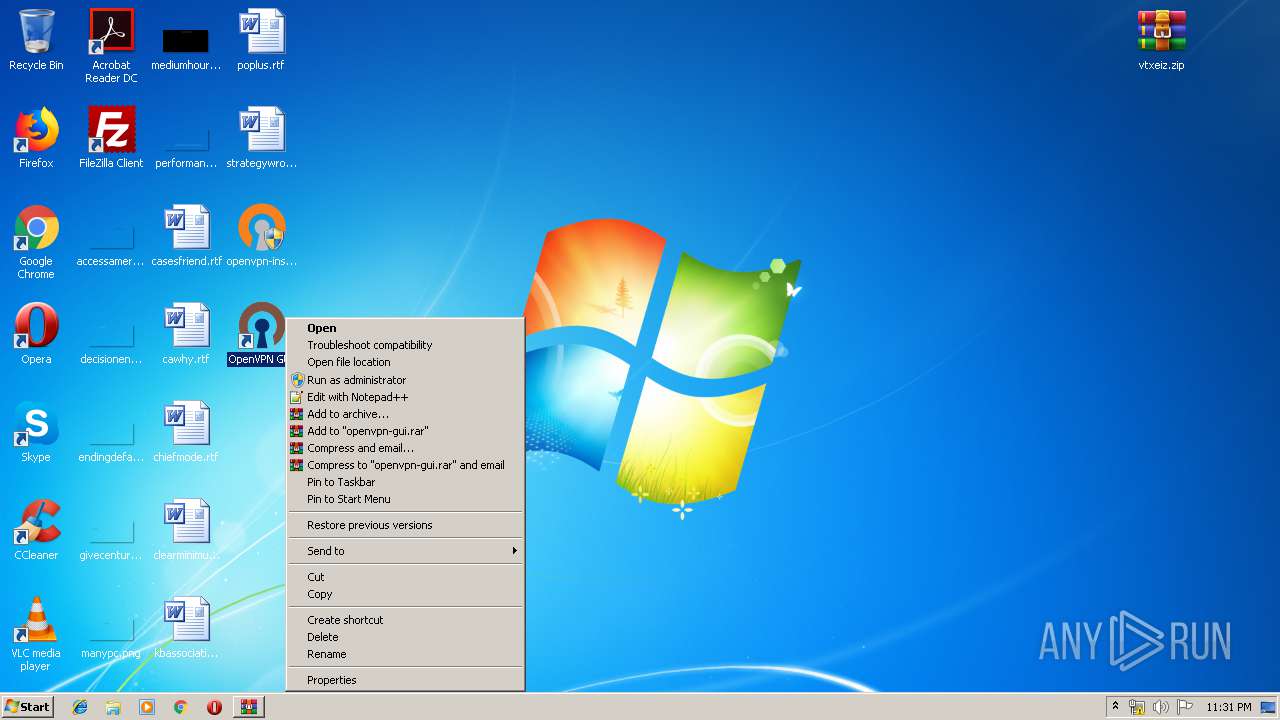
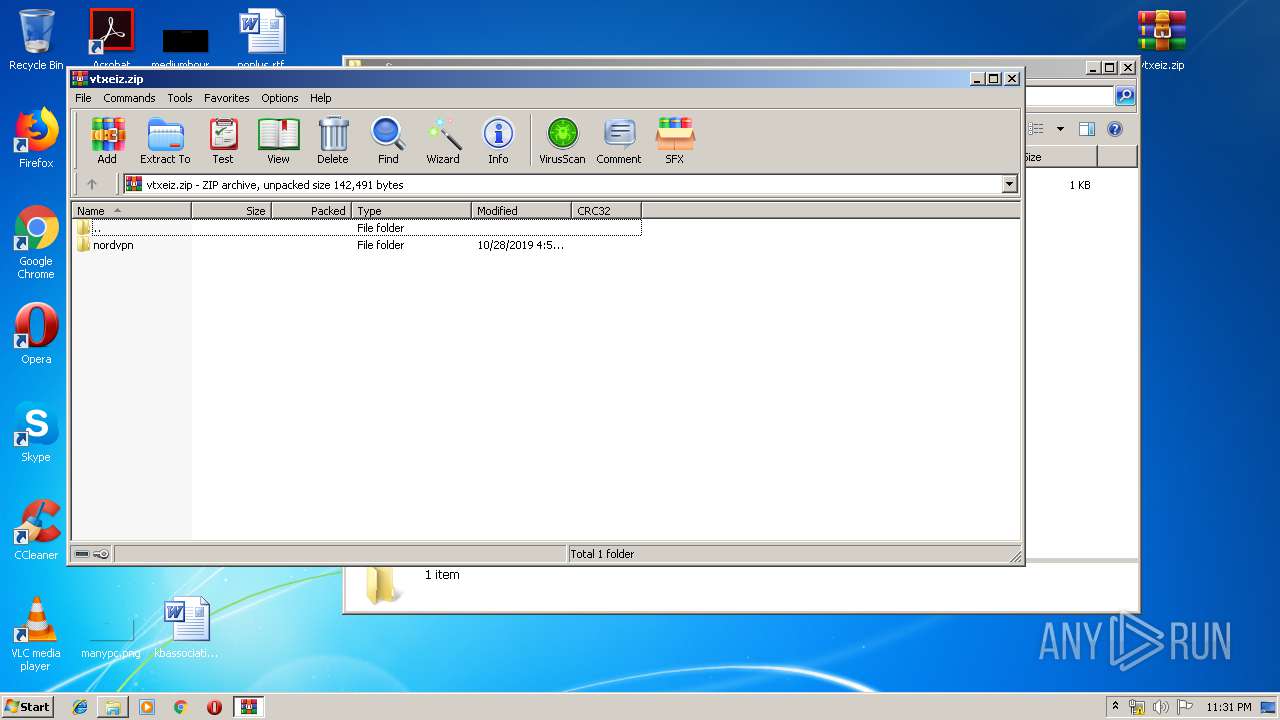
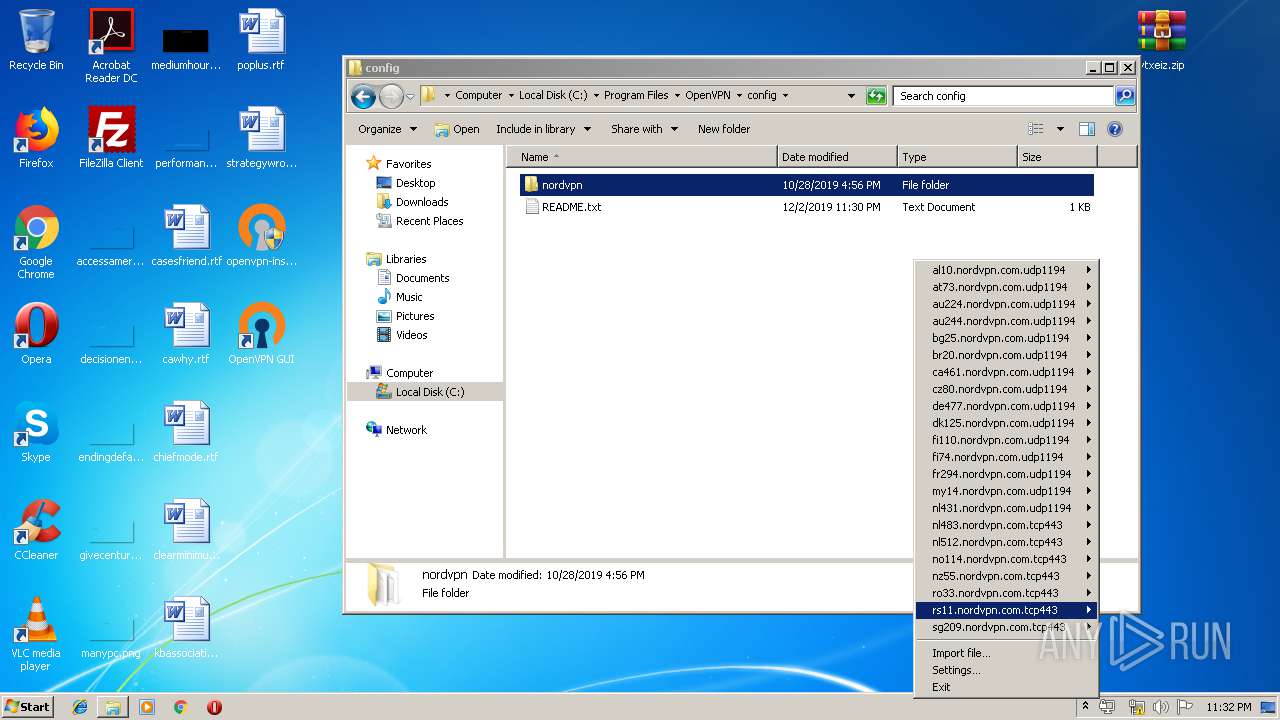
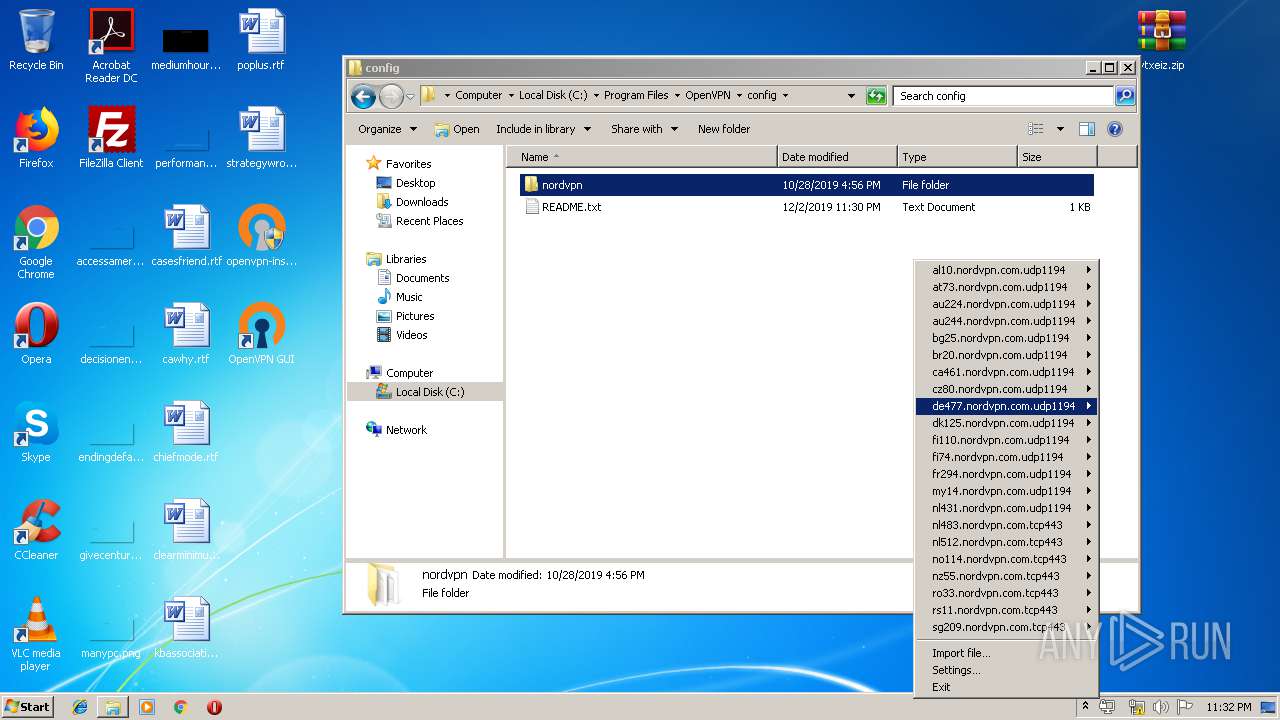
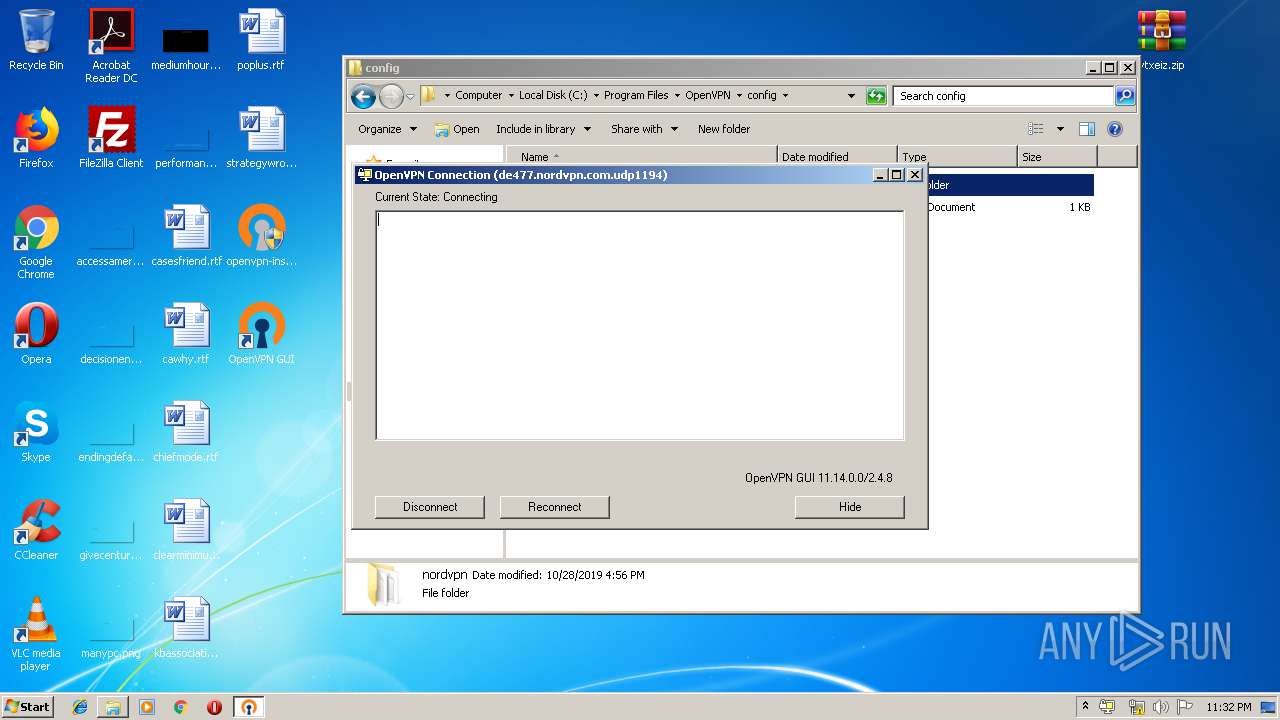
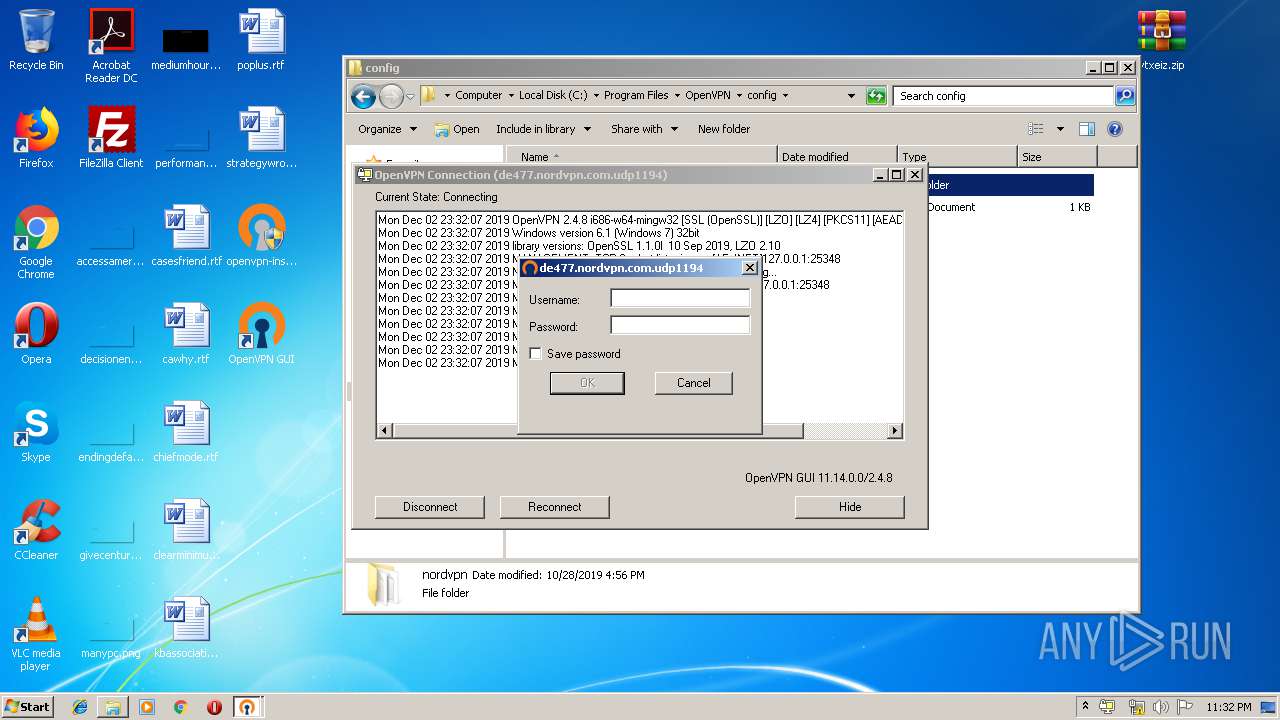
Manual execution by user
- iexplore.exe (PID: 4032)
- chrome.exe (PID: 1072)
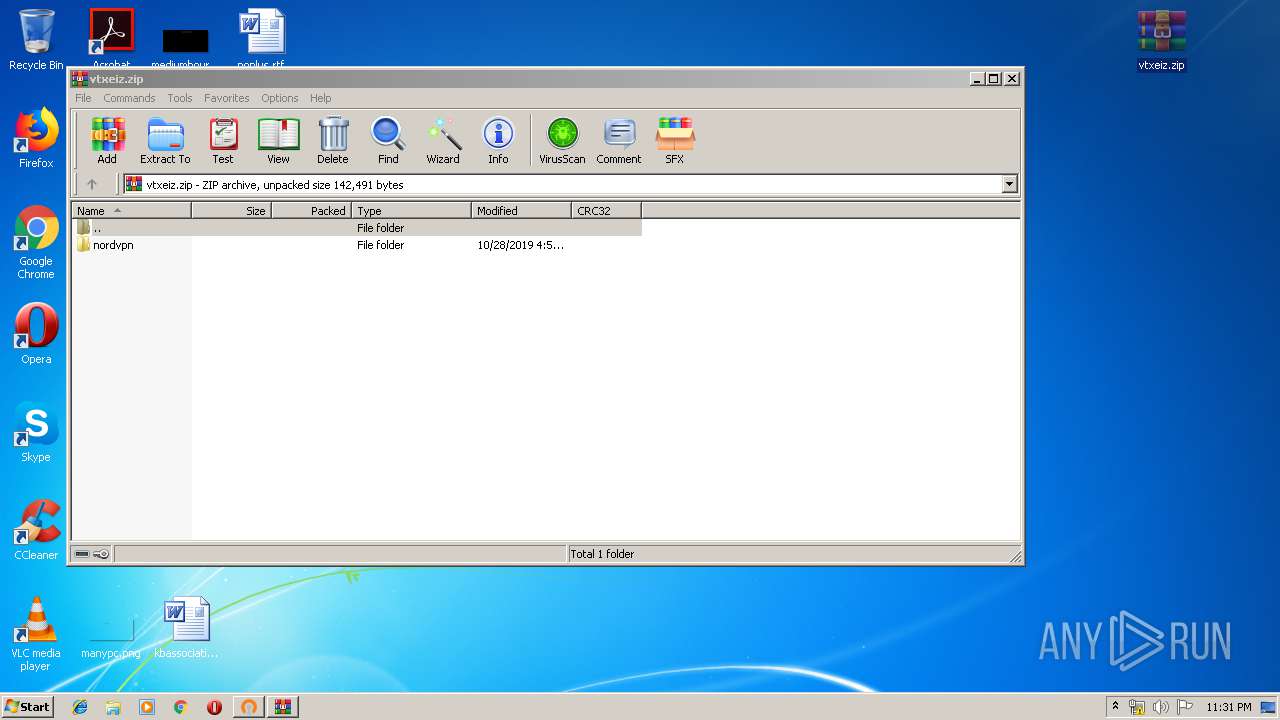
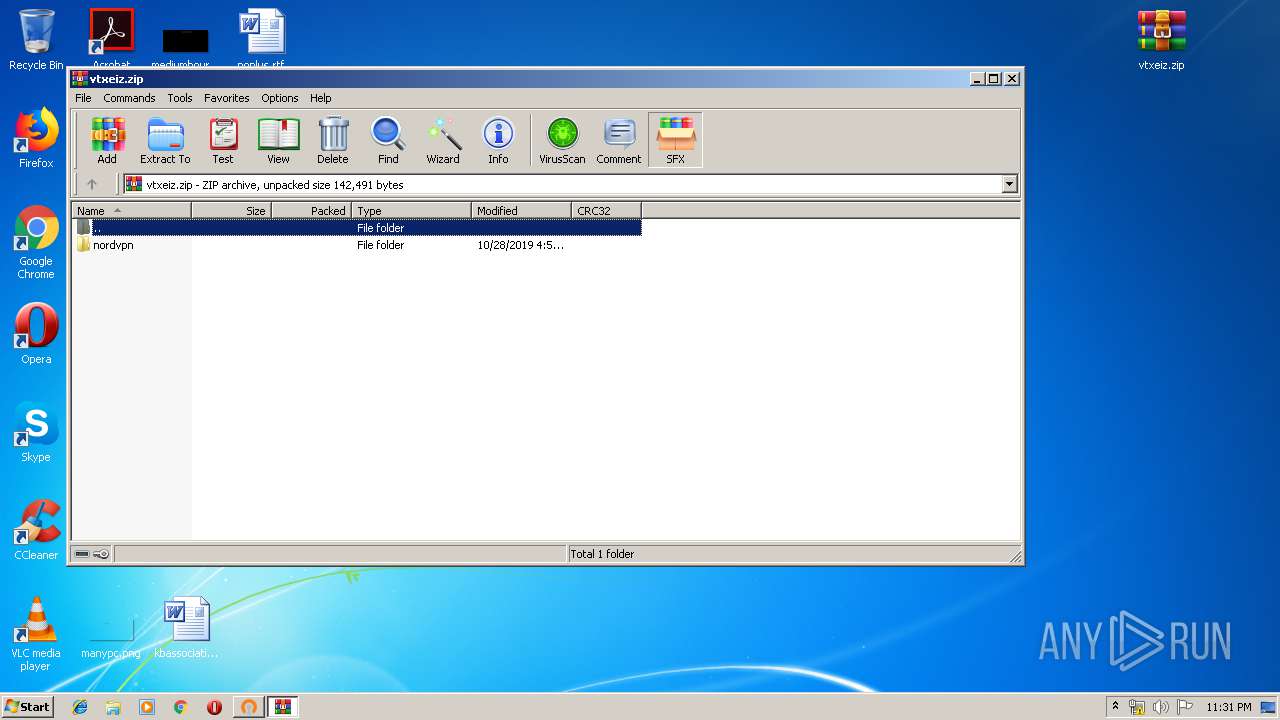
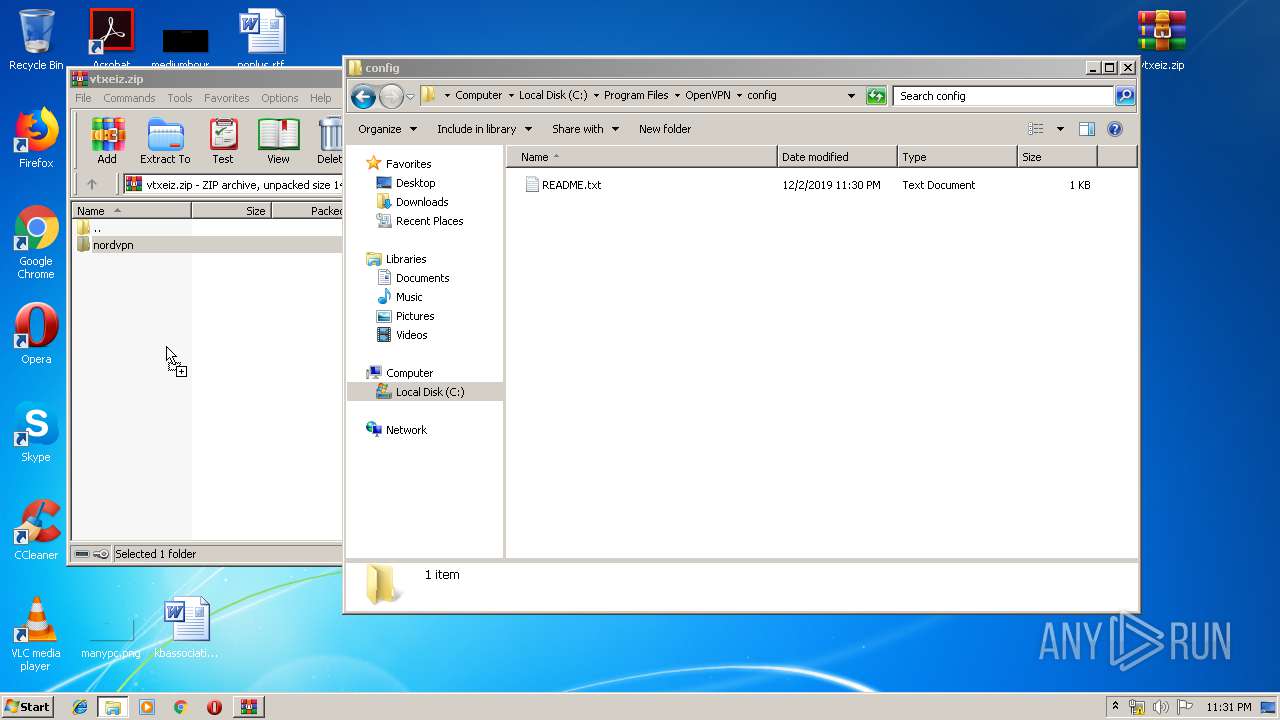
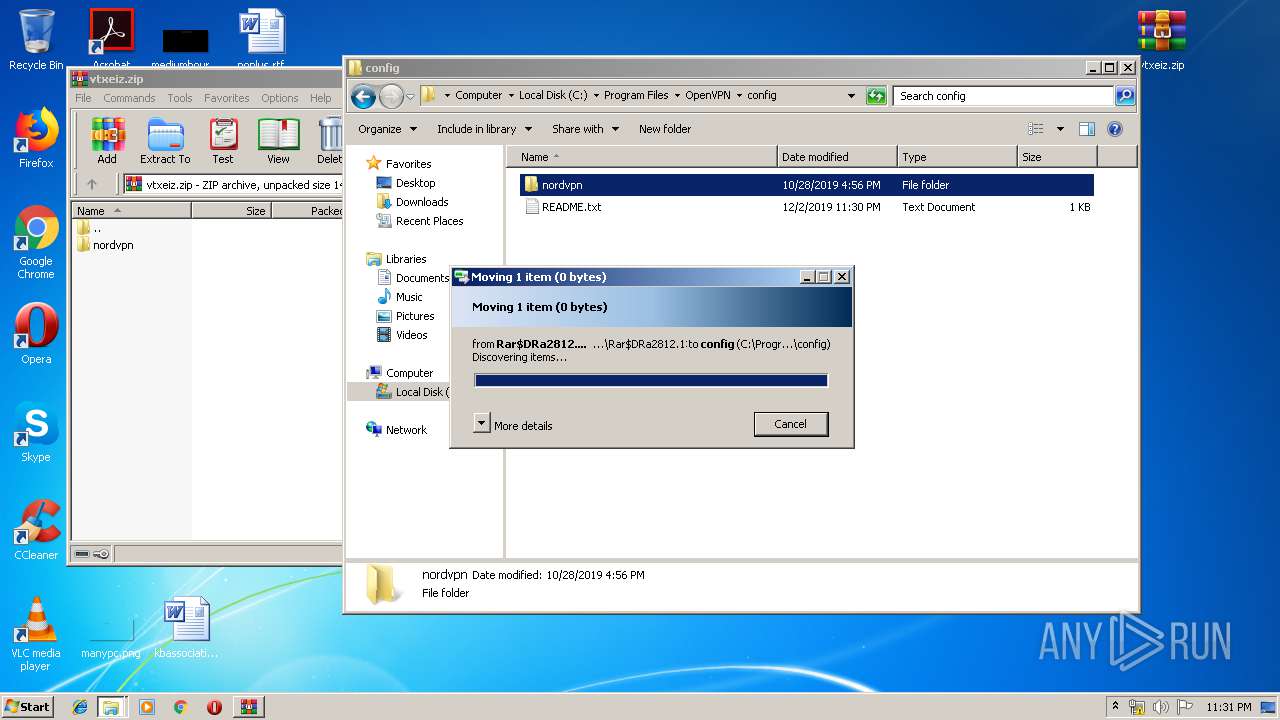
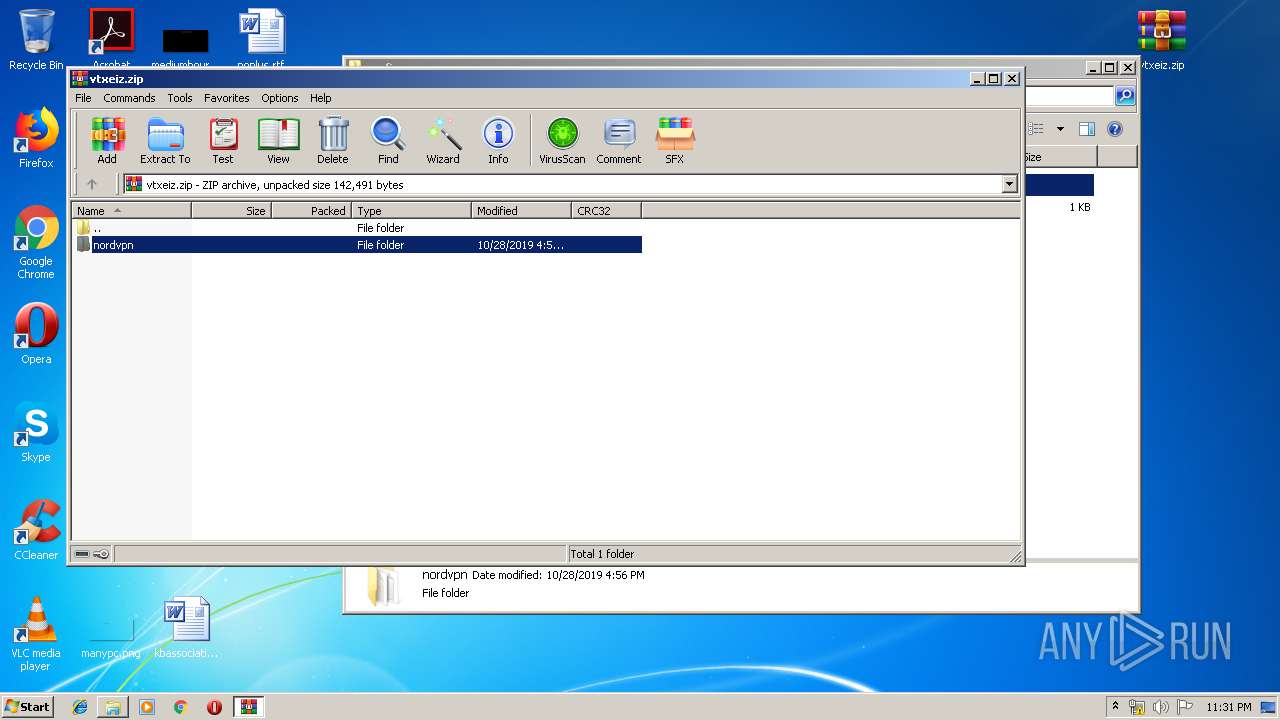
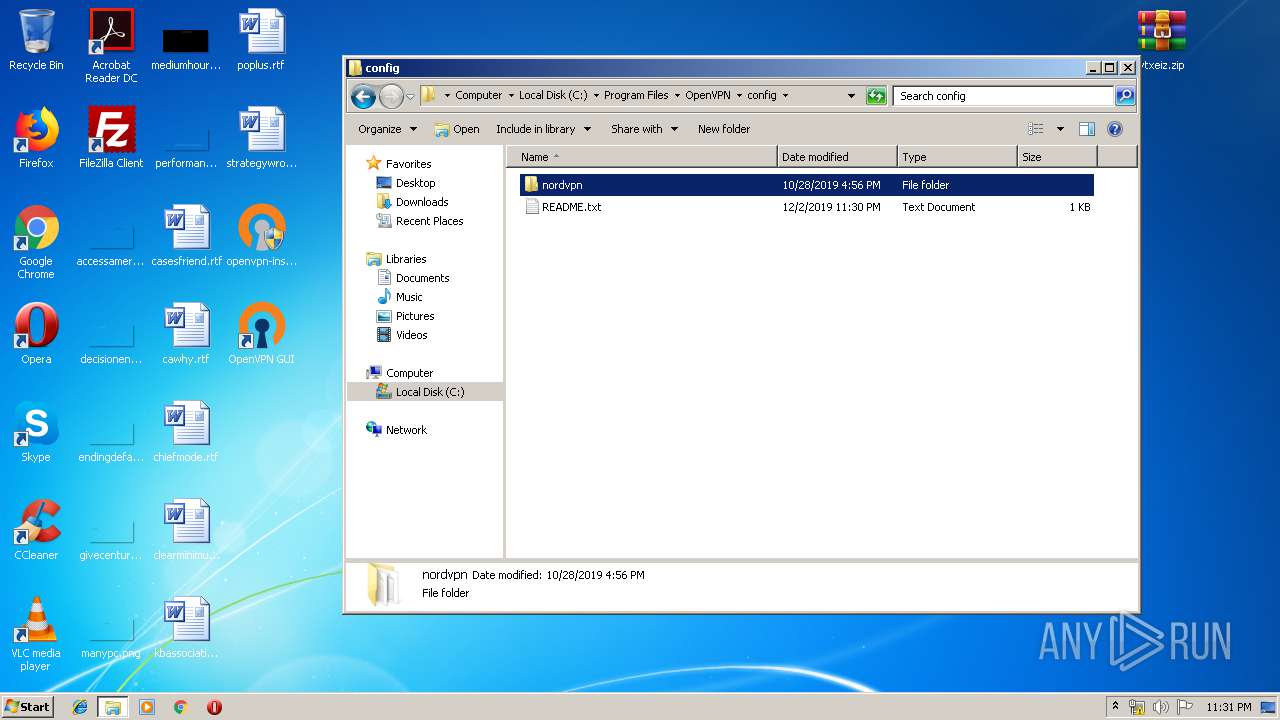
- WinRAR.exe (PID: 1188)
- WinRAR.exe (PID: 2812)
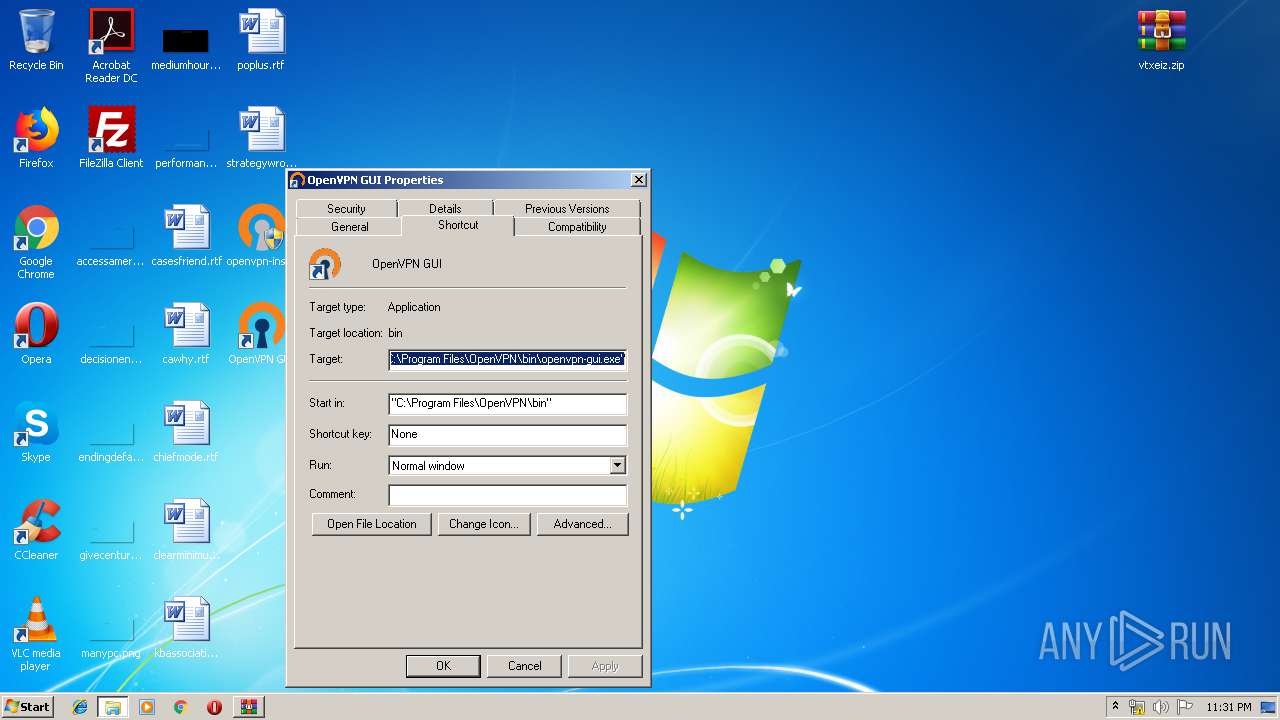
- openvpn-gui.exe (PID: 4048)
Reads Internet Cache Settings
- iexplore.exe (PID: 1800)
- chrome.exe (PID: 1072)
Reads internet explorer settings
- iexplore.exe (PID: 1800)
Application launched itself
- iexplore.exe (PID: 4032)
- chrome.exe (PID: 1072)
Low-level read access rights to disk partition
- vssvc.exe (PID: 688)
Searches for installed software
- DrvInst.exe (PID: 1796)
Reads the hosts file
- chrome.exe (PID: 1072)
- chrome.exe (PID: 3632)
Reads settings of System Certificates
- chrome.exe (PID: 3632)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:14 12:25:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 35840 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | 110080 |
| EntryPoint: | 0x435d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jan-2016 11:25:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Jan-2016 11:25:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008B00 | 0x00008C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.94115 |
.data | 0x0000A000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.62893 |
.rdata | 0x0000B000 | 0x000069D8 | 0x00006A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29941 |
.bss | 0x00012000 | 0x0001AD00 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002D000 | 0x00001298 | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.17963 |
.ndata | 0x0002F000 | 0x0001A000 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00049000 | 0x00006DC8 | 0x00006E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.84466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21582 | 960 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.15056 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 3.94986 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.50443 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.1424 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 4.74328 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.70702 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.47314 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70176 | 356 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68101 | 582 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
97
Monitored processes
47
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\Desktop\openvpn-install-2.4.8-I602-Win7.exe" | C:\Users\admin\Desktop\openvpn-install-2.4.8-I602-Win7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 688 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,12901661409061691577,5376071416096265081,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4657260838391090156 --mojo-platform-channel-handle=4192 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | openvpn --version | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpn-gui.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2768 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,12901661409061691577,5376071416096265081,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8375554051733747063 --mojo-platform-channel-handle=4260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\vtxeiz.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,12901661409061691577,5376071416096265081,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4552193330722948102 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\TAP-Windows\bin\tapinstall.exe" hwids tap0901 | C:\Program Files\TAP-Windows\bin\tapinstall.exe | — | nsF1C0.tmp | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
Total events
3 302
Read events
2 532
Write events
715
Delete events
55
Modification events
| (PID) Process: | (4032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
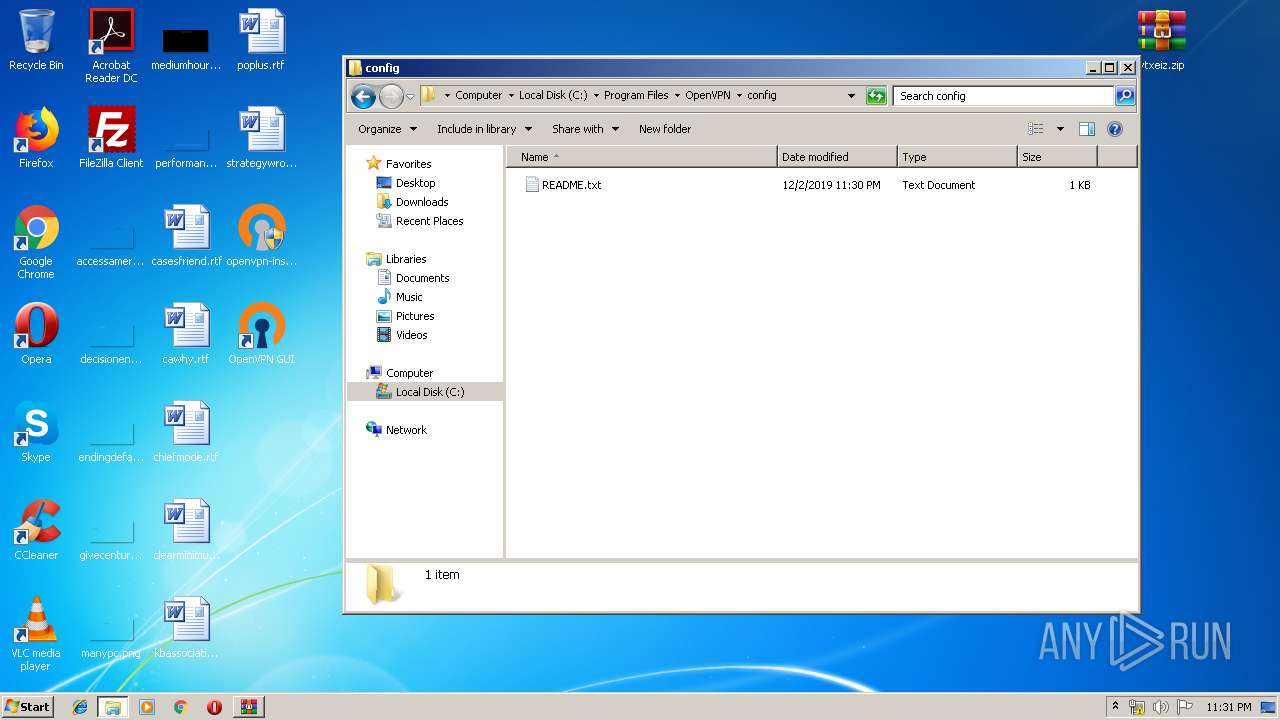
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | config_dir |
Value: C:\Program Files\OpenVPN\config | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | config_ext |
Value: ovpn | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | exe_path |
Value: C:\Program Files\OpenVPN\bin\openvpn.exe | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | log_dir |
Value: C:\Program Files\OpenVPN\log | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | priority |
Value: NORMAL_PRIORITY_CLASS | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | log_append |
Value: 0 | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | ovpn_admin_group |
Value: OpenVPN Administrators | |||
| (PID) Process: | (616) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | disable_save_passwords |
Value: 0 | |||
| (PID) Process: | (4032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
31
Suspicious files
57
Text files
632
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Program Files\OpenVPN\bin\openvpn.exe | executable | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Documentation\OpenVPN Windows Notes.lnk | lnk | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Documentation\OpenVPN Manual Page.lnk | lnk | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Shortcuts\OpenVPN Sample Configuration Files.lnk | lnk | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Program Files\OpenVPN\bin\openvpnserv.exe | executable | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Utilities\Generate a static OpenVPN key.lnk | lnk | |
MD5:— | SHA256:— | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsjC33D.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsjC33D.tmp\UserInfo.dll | executable | |
MD5:9F0CB655A832FDECB9433DD781004637 | SHA256:A94FD67DAF9137B26E2D98AA4CF46614439BD64263C5C211369A232C444862EA | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsjC33D.tmp\System.dll | executable | |
MD5:2E025E2CEE2953CCE0160C3CD2E1A64E | SHA256:D821A62802900B068DCF61DDC9FDFF2F7ADA04B706815AB6E5038B21543DA8A5 | |||
| 616 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsjC33D.tmp\modern-header.bmp | image | |
MD5:CD8BC7B987FA89E7FD5ACDED7148CF66 | SHA256:127FC8103D7D1DAACFB0ABB422C9B2AA8ED14FA095E06A997E43445D5D963352 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
32
DNS requests
20
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3632 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
3632 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
3632 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.94&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1575329420&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4032 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3632 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4032 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1800 | iexplore.exe | 104.149.191.66:443 | files.catbox.moe | Psychz Networks | US | suspicious |
3632 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.23.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 104.149.191.66:443 | files.catbox.moe | Psychz Networks | US | suspicious |
3632 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.22.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
files.catbox.moe |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report