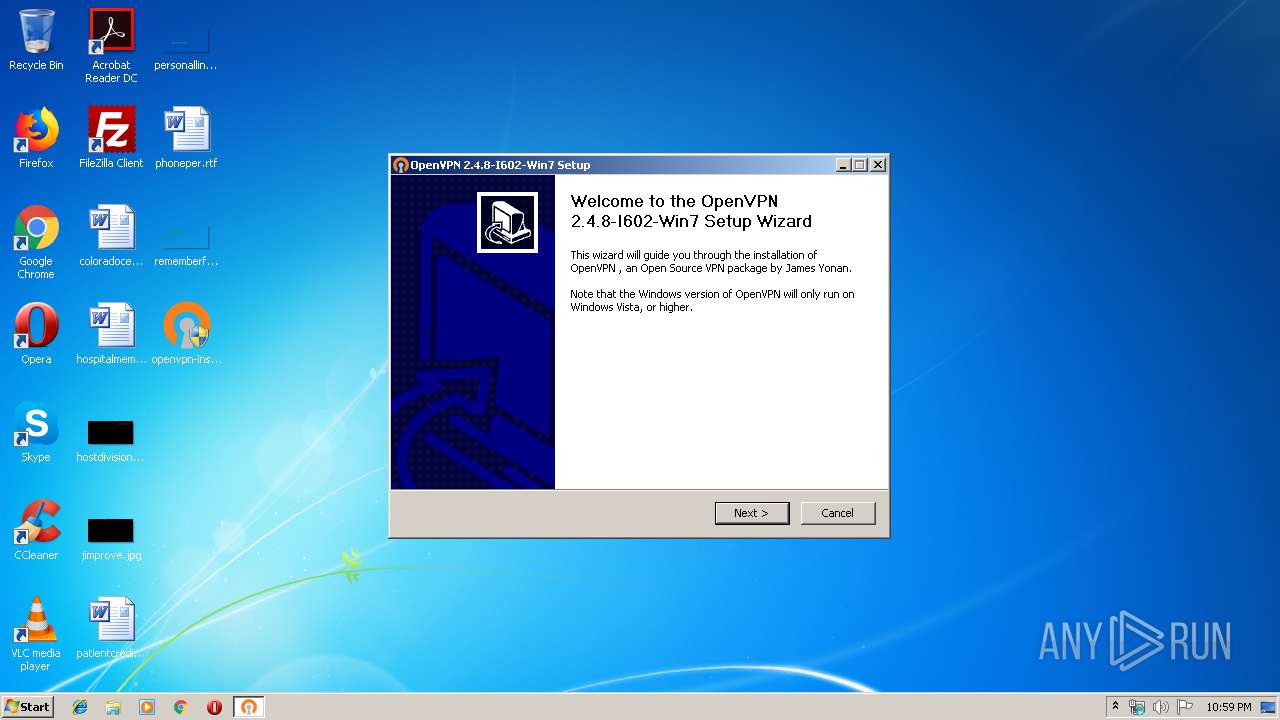
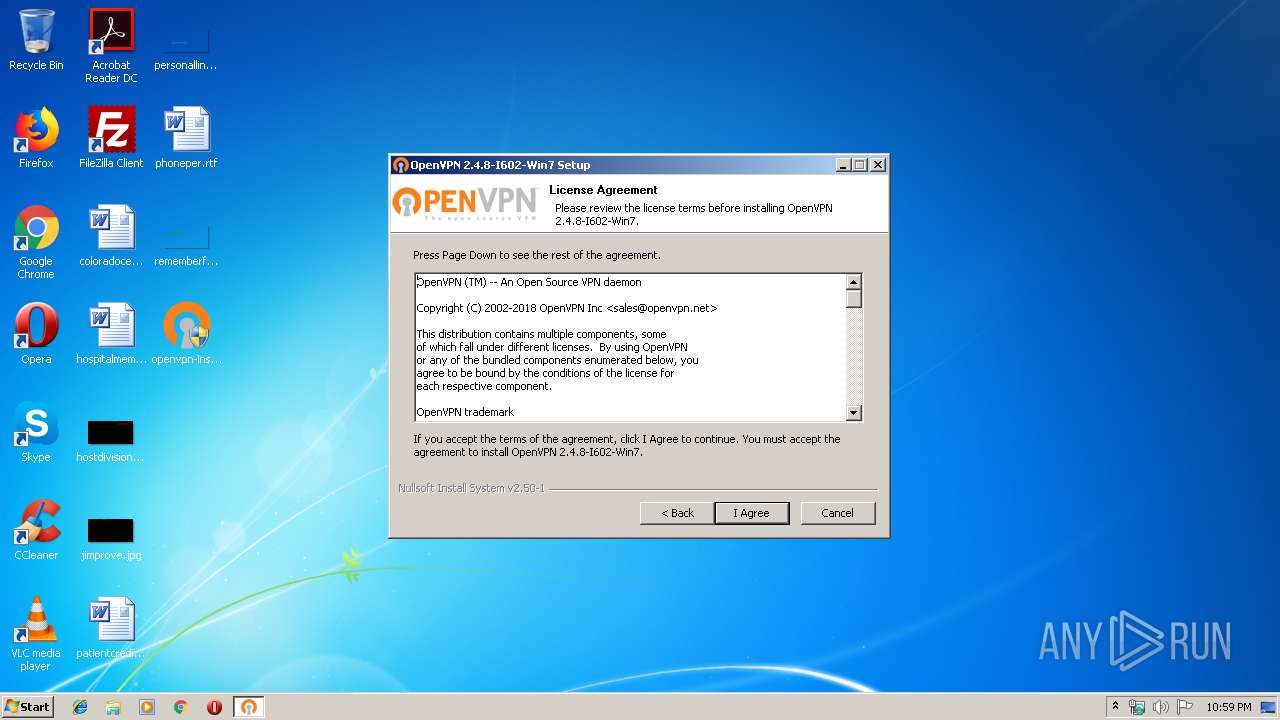
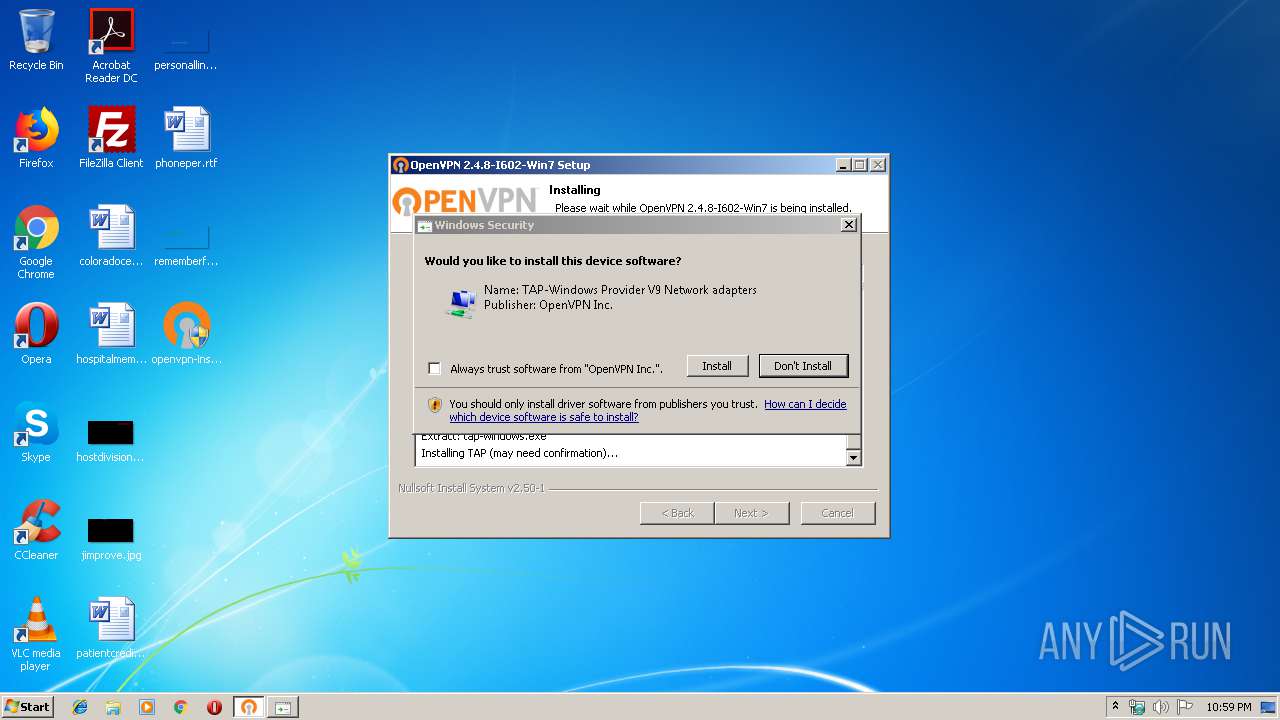
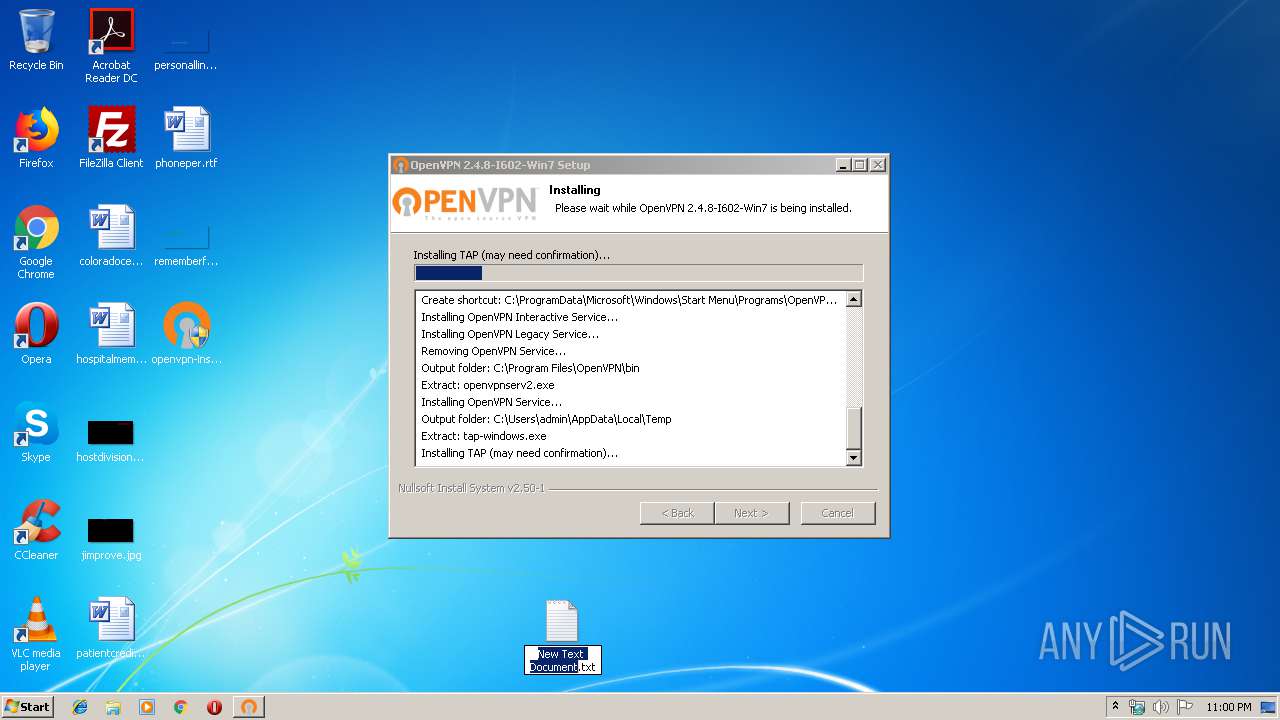
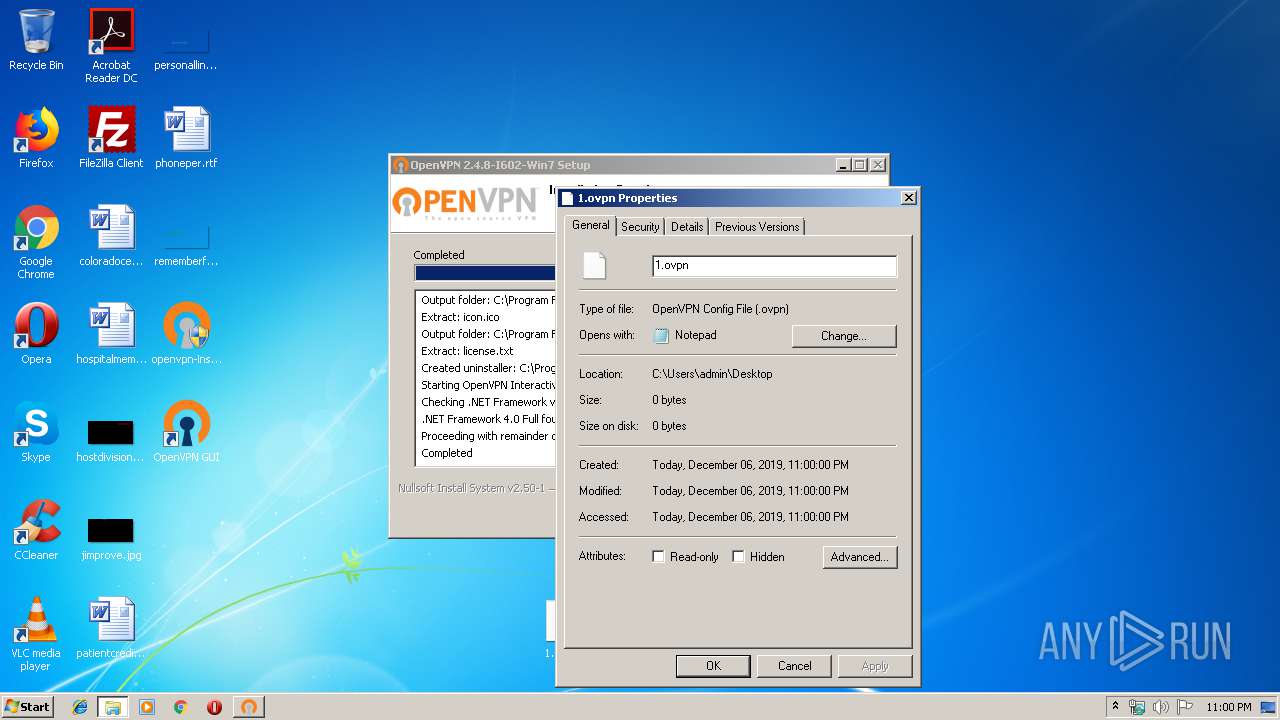
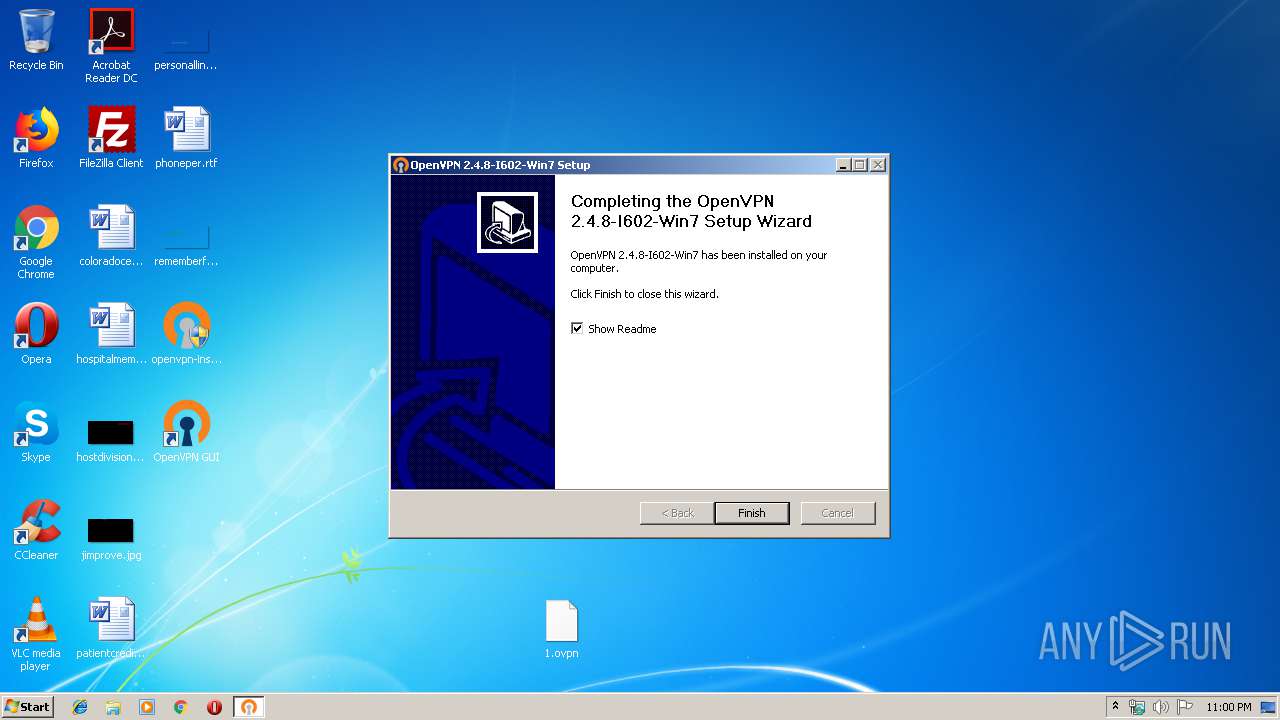
| File name: | openvpn-install-2.4.8-I602-Win7.exe |
| Full analysis: | https://app.any.run/tasks/3f49fb9f-c004-48ec-a0a5-d8d9035e3f8f |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 22:59:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 73BCD5B6A0208D953A38ED74FDEF5FF1 |
| SHA1: | 8C9F28D7BDBB4613777A9741809E34B91FD45A0F |
| SHA256: | 16165E4505874E71C9FE732041274C3CE10E0881DFEEECE529E8B54C5B558296 |
| SSDEEP: | 98304:VvSASt7w80xv6bfJh1Gxt9cbPqJH8eNzuJm6wH+bj:hSdNw80aJEtTJH1NzcUHu |
MALICIOUS
Application was dropped or rewritten from another process
- tap-windows.exe (PID: 600)
- nsD62B.tmp (PID: 856)
- nsD4D2.tmp (PID: 2668)
- tapinstall.exe (PID: 3820)
- tapinstall.exe (PID: 2604)
- nsD2FD.tmp (PID: 2992)
- openvpnserv.exe (PID: 3904)
- openvpn-gui.exe (PID: 3840)
- openvpn.exe (PID: 1268)
- openvpn.exe (PID: 4036)
- openvpn.exe (PID: 1048)
- openvpn.exe (PID: 4036)
- openvpn.exe (PID: 2836)
- openvpn.exe (PID: 2304)
- openvpn.exe (PID: 3680)
- openvpn.exe (PID: 2440)
- openvpn.exe (PID: 3312)
- openvpn.exe (PID: 1072)
Loads dropped or rewritten executable
- tap-windows.exe (PID: 600)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
- openvpn.exe (PID: 1268)
- openvpn-gui.exe (PID: 3840)
- openvpn.exe (PID: 4036)
- openvpn.exe (PID: 3680)
- openvpn.exe (PID: 4036)
- openvpn.exe (PID: 2304)
- openvpn.exe (PID: 1072)
- openvpn.exe (PID: 2440)
- openvpn.exe (PID: 3312)
- openvpn.exe (PID: 1048)
- openvpn.exe (PID: 2836)
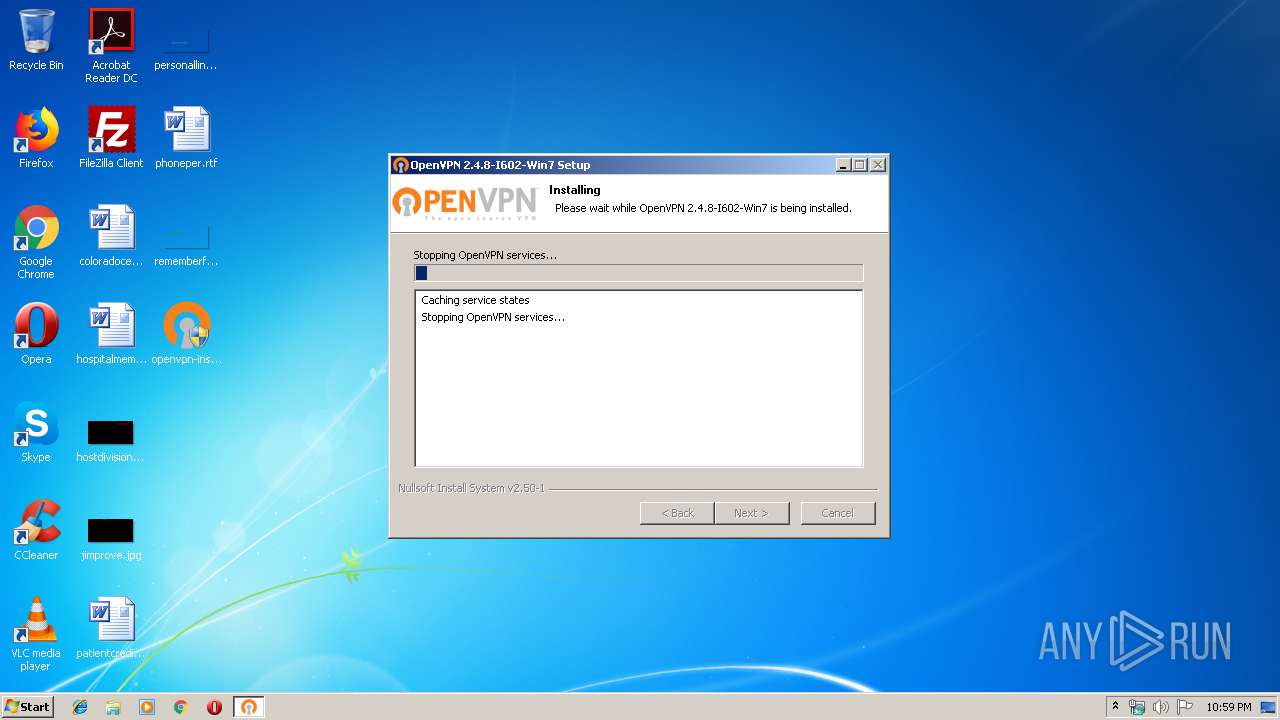
Changes the autorun value in the registry
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
SUSPICIOUS
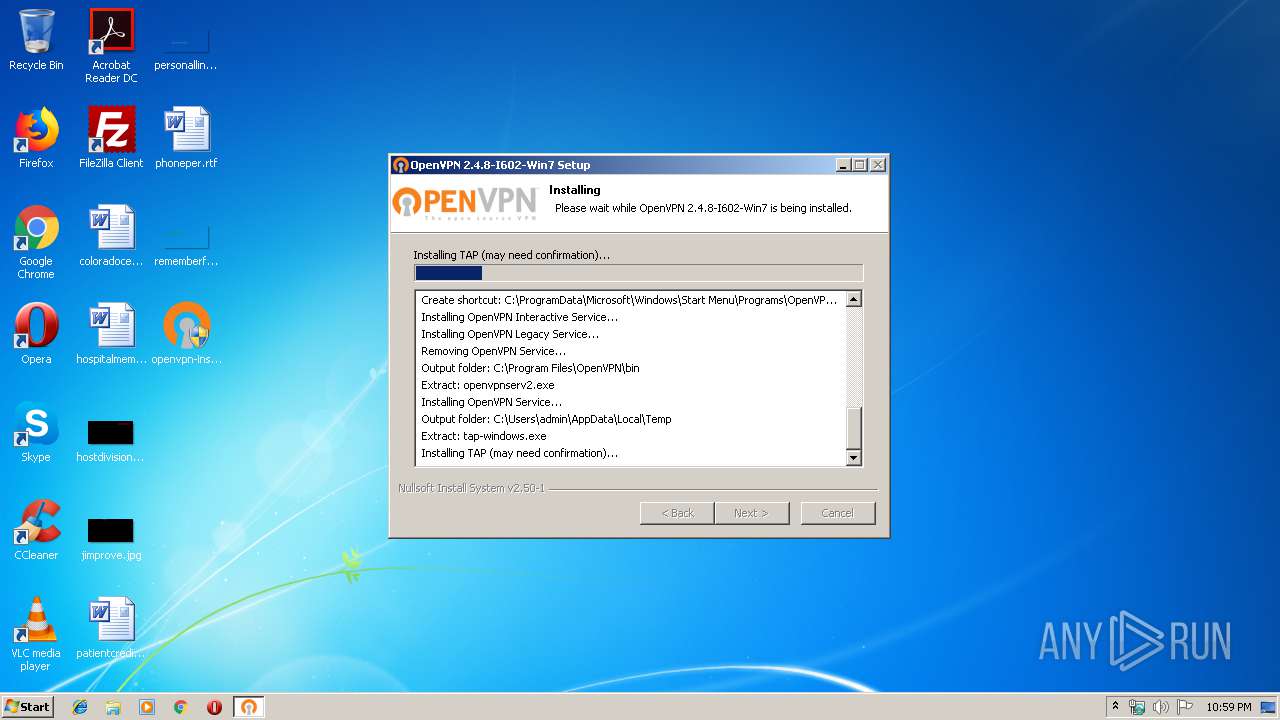
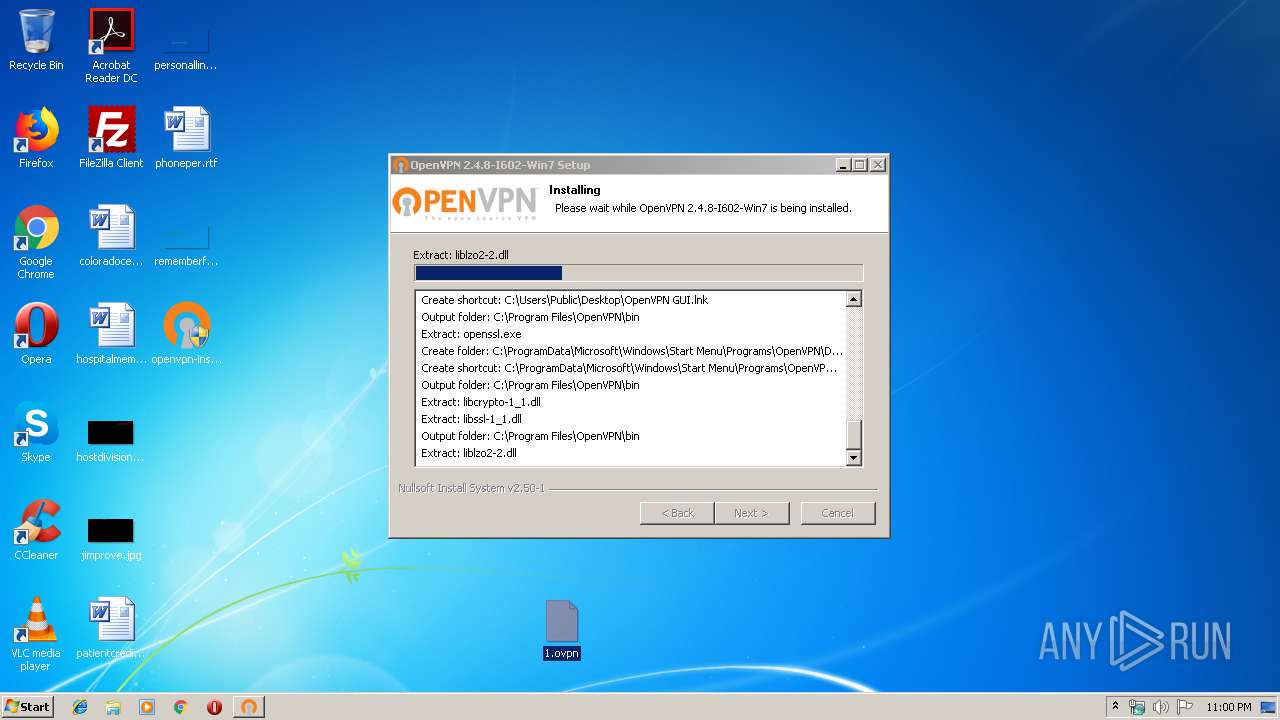
Executable content was dropped or overwritten
- tap-windows.exe (PID: 600)
- tapinstall.exe (PID: 2604)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
- DrvInst.exe (PID: 3780)
- DrvInst.exe (PID: 3460)
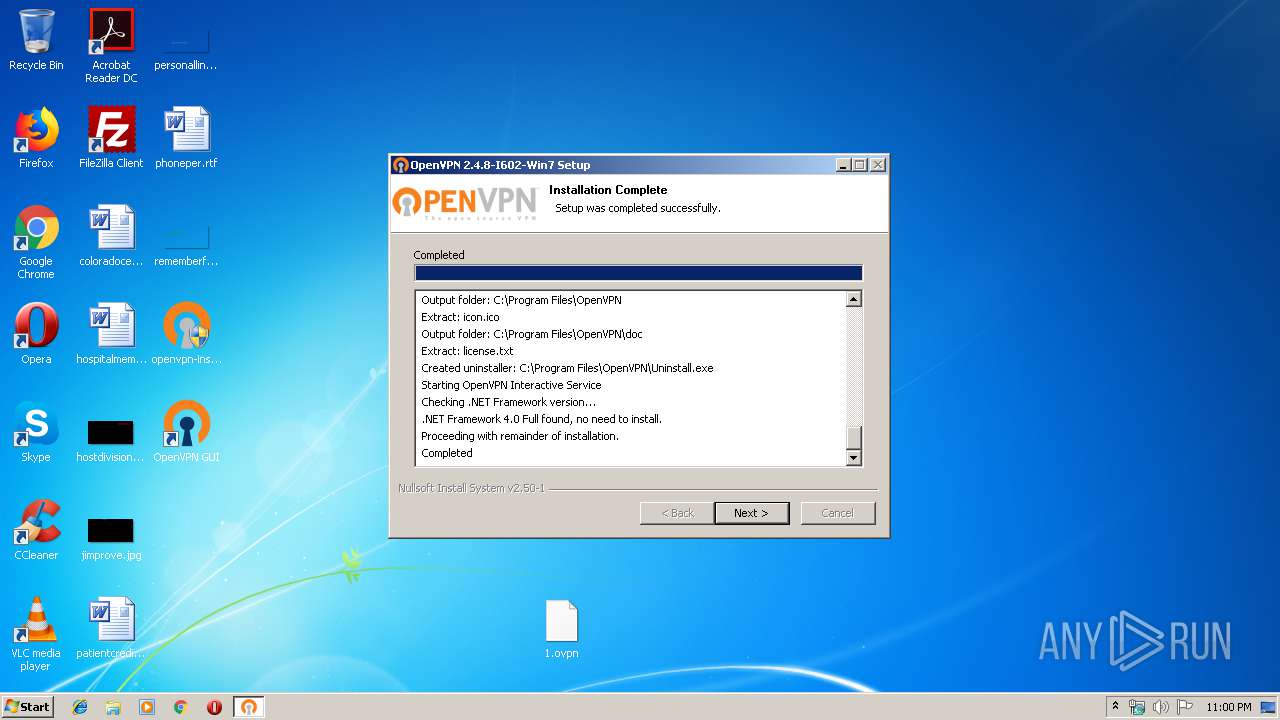
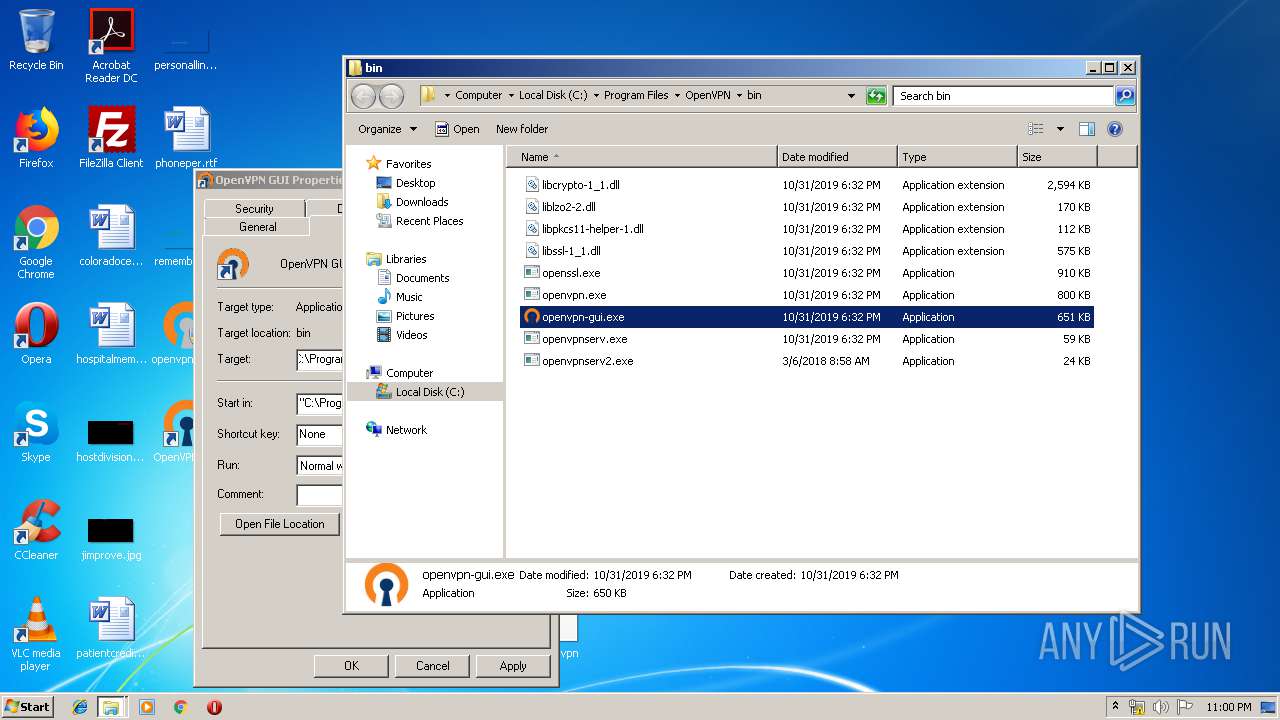
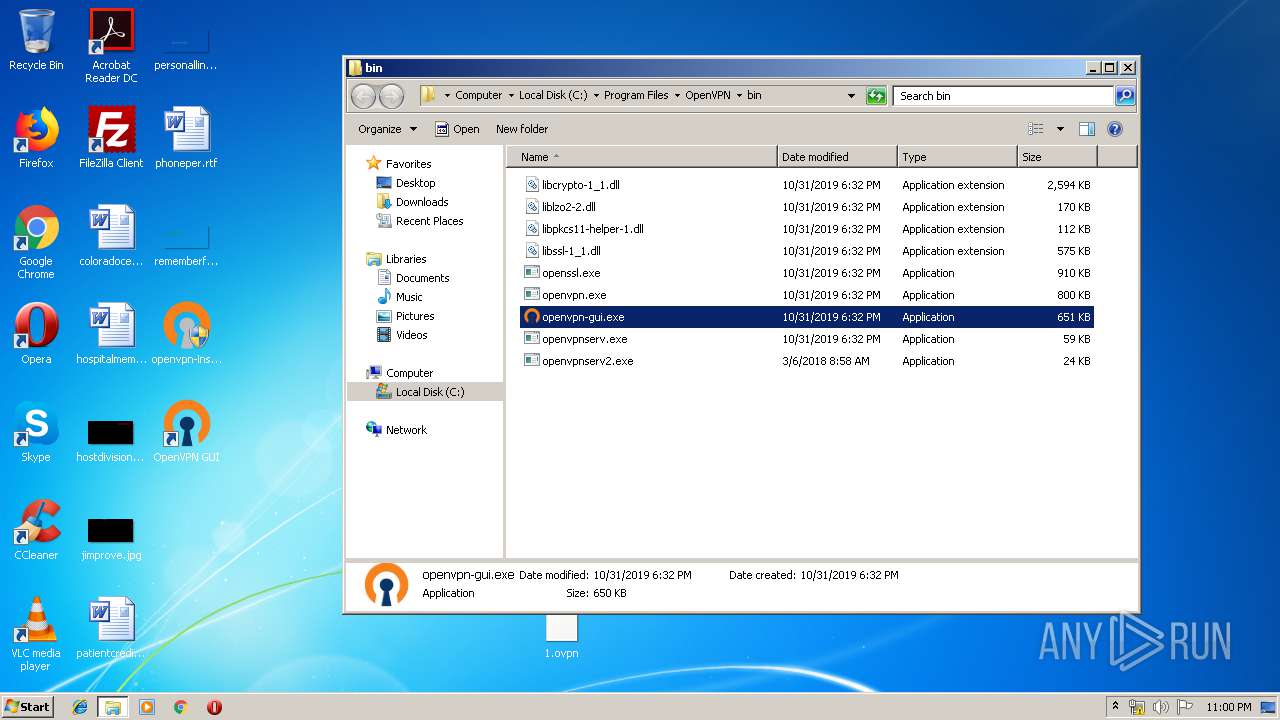
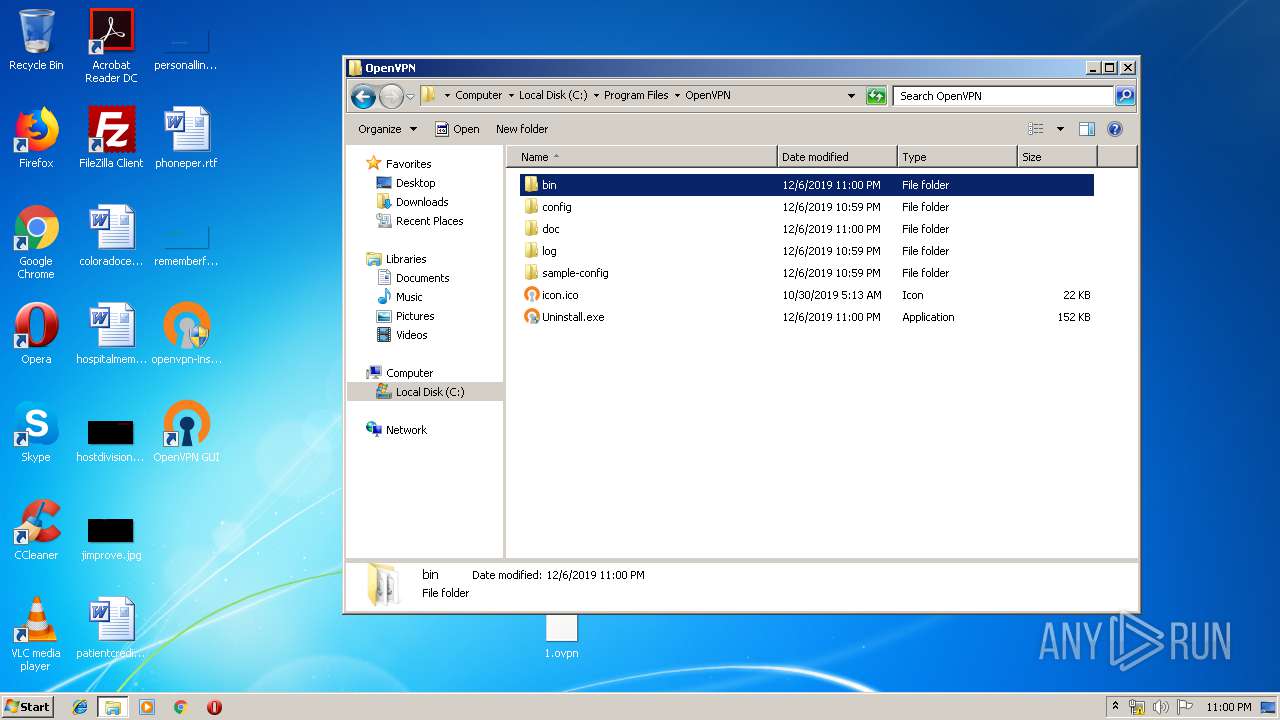
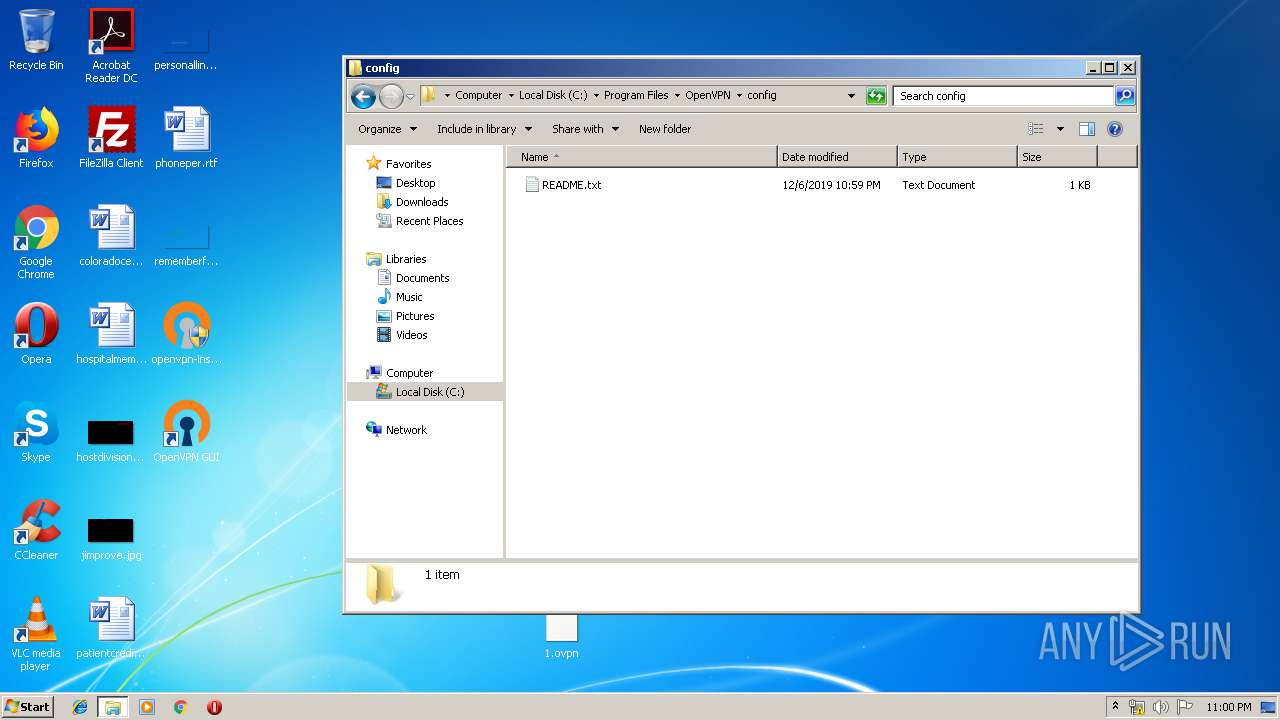
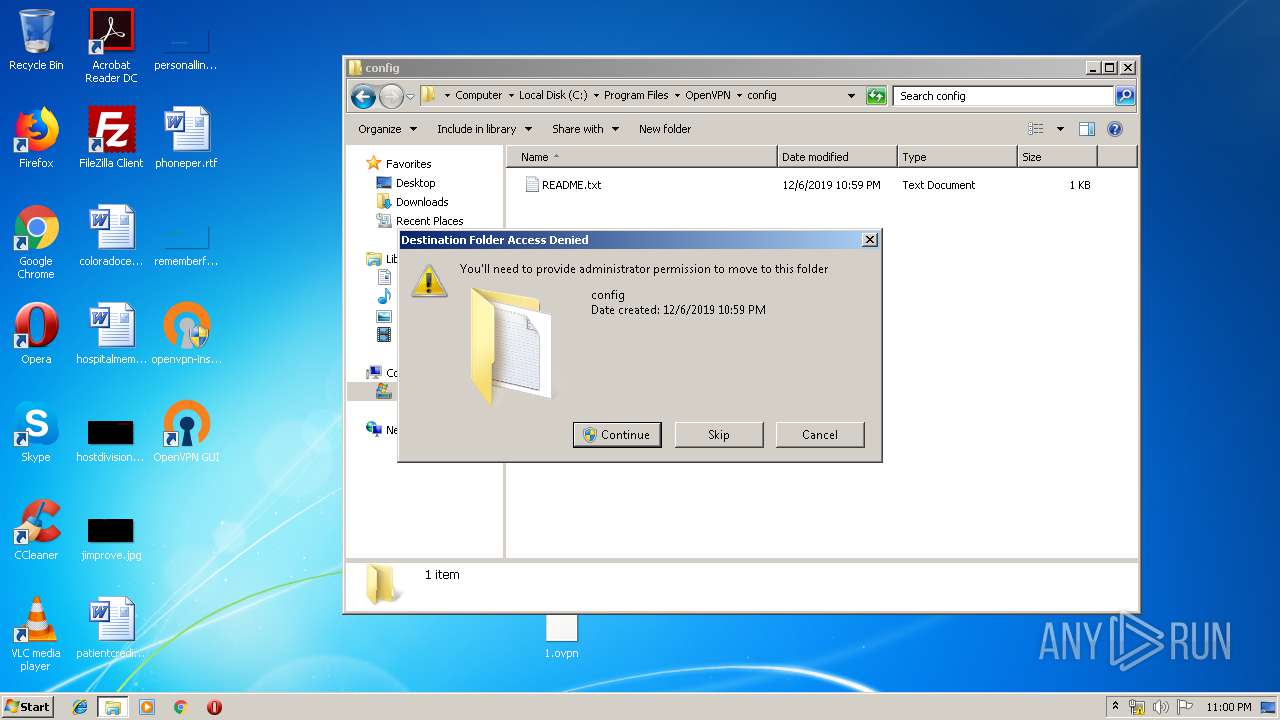
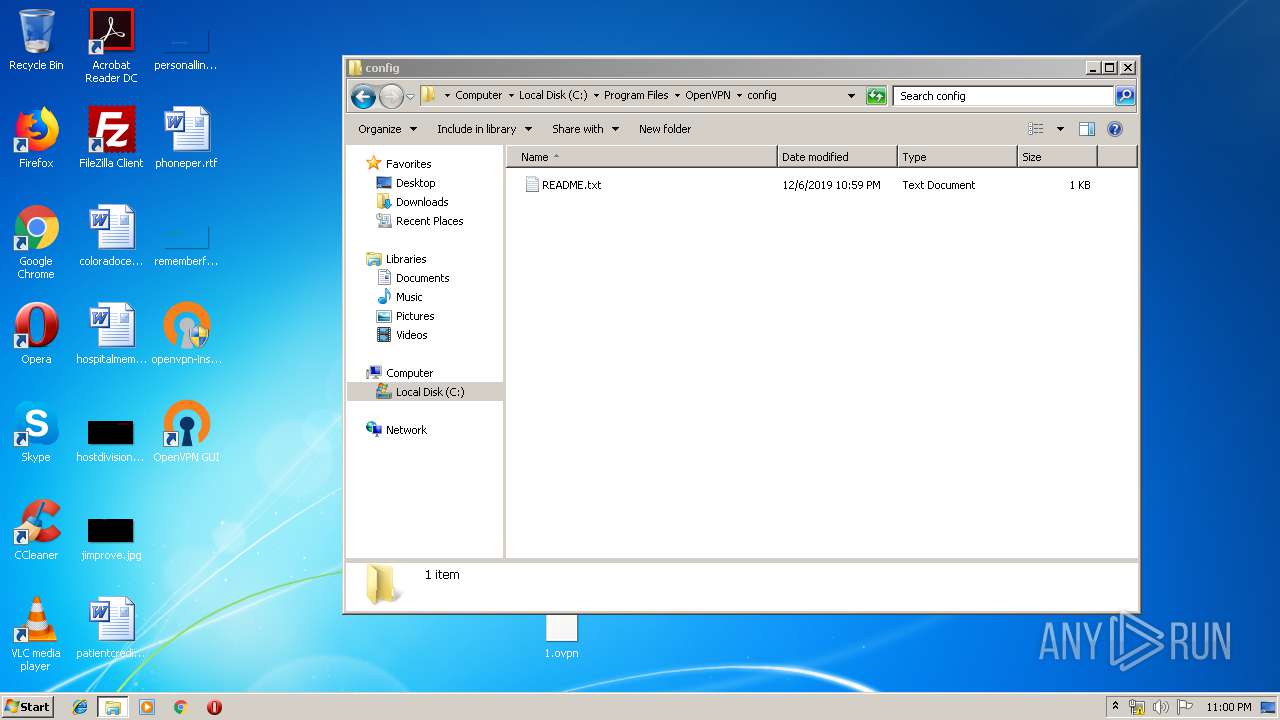
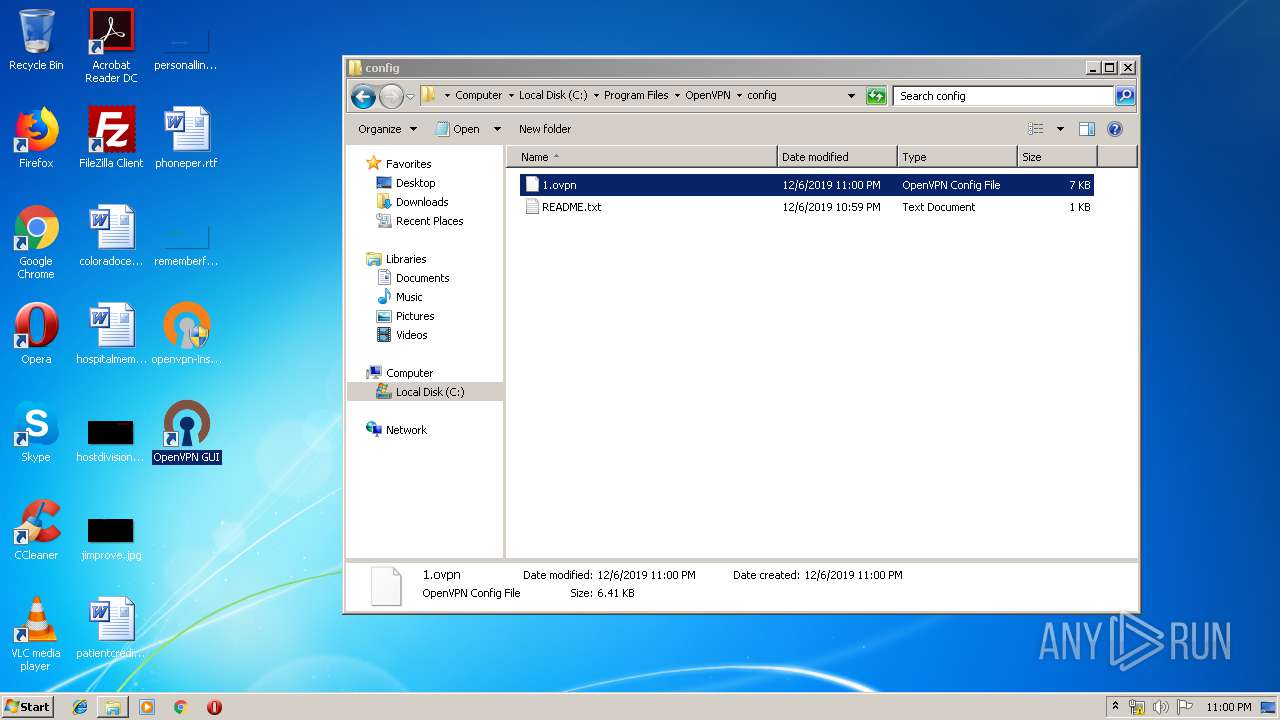
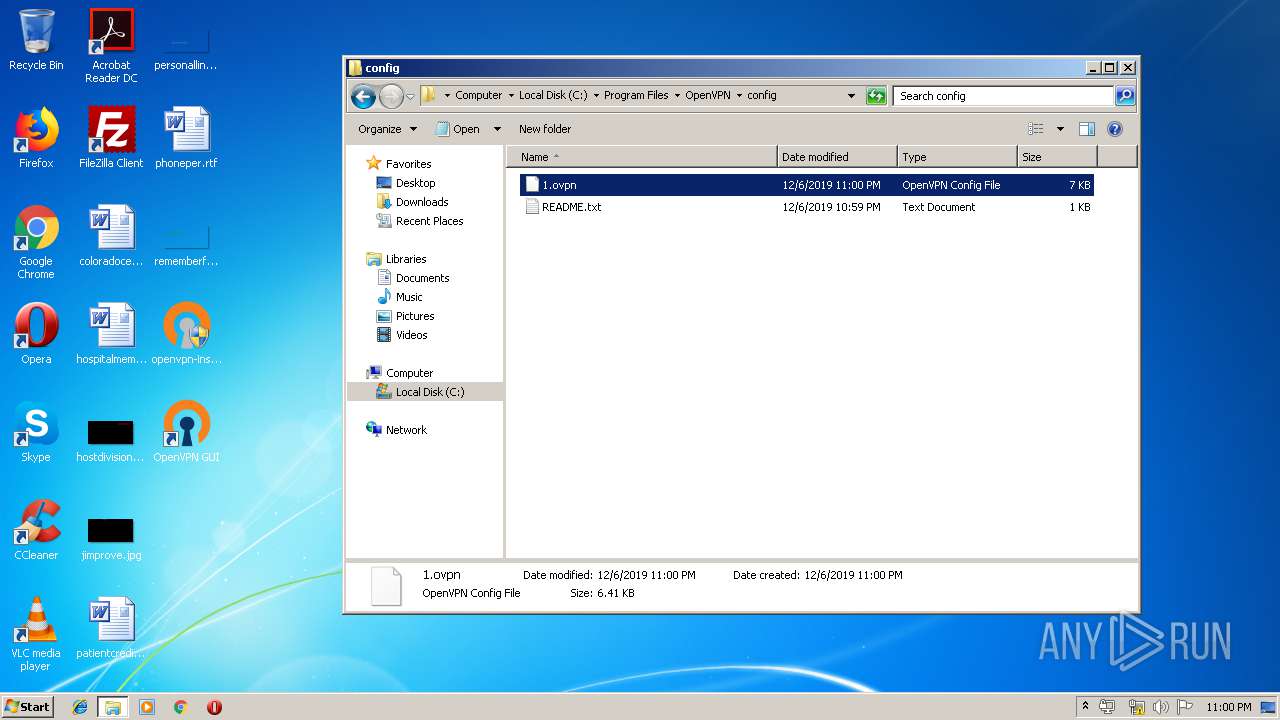
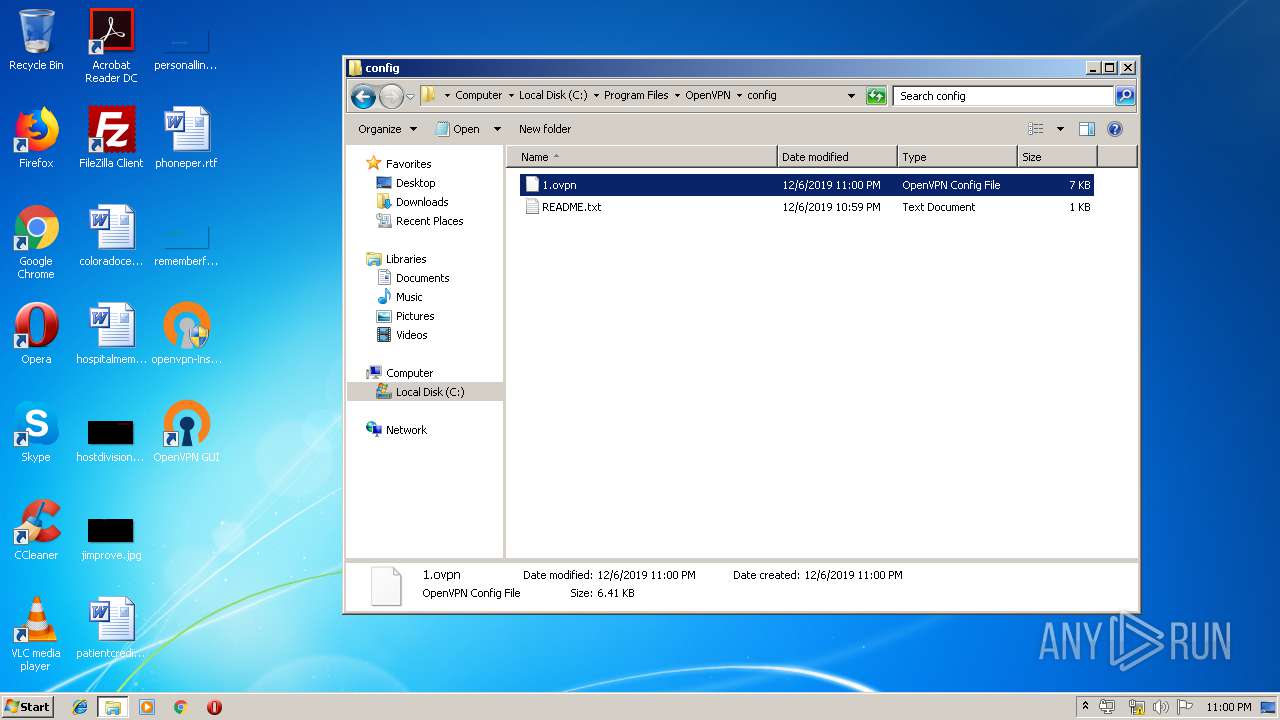
Creates files in the program directory
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
- tap-windows.exe (PID: 600)
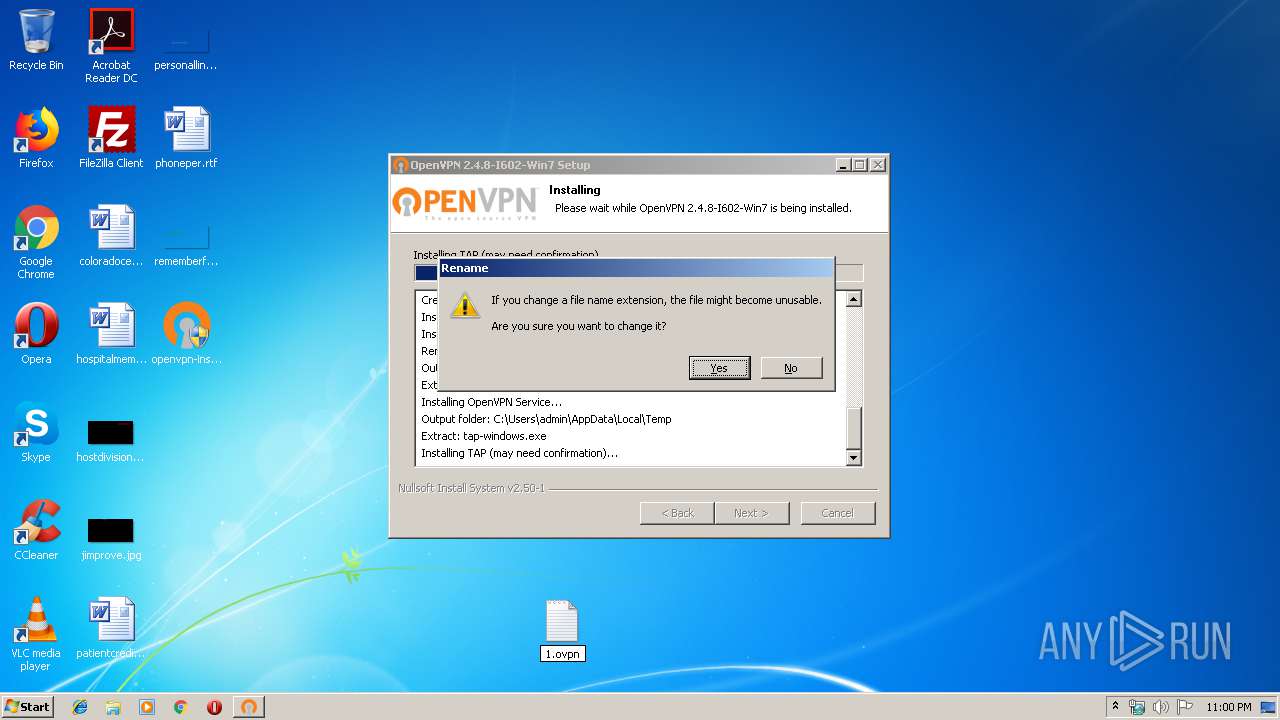
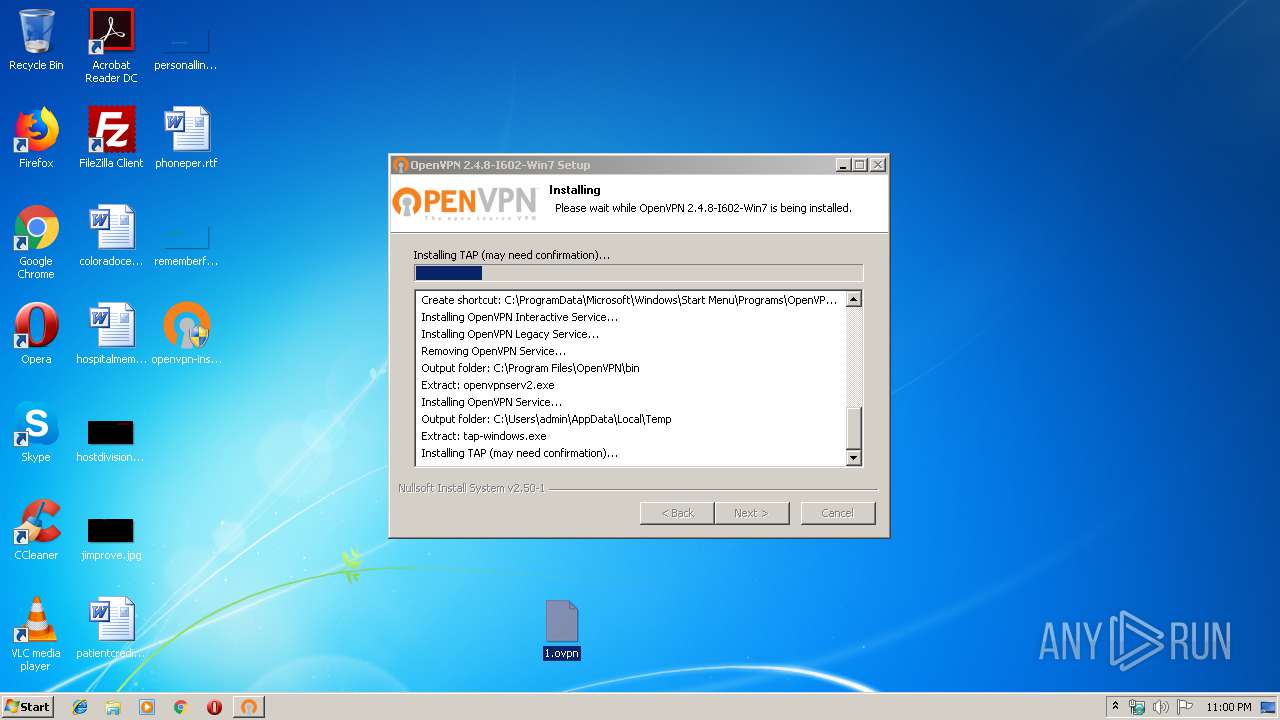
Starts application with an unusual extension
- tap-windows.exe (PID: 600)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
Creates files in the driver directory
- DrvInst.exe (PID: 3780)
- DrvInst.exe (PID: 3460)
Executed via COM
- DrvInst.exe (PID: 3780)
- DrvInst.exe (PID: 3460)
- DllHost.exe (PID: 2520)
Creates files in the Windows directory
- DrvInst.exe (PID: 3780)
- DrvInst.exe (PID: 3460)
Removes files from Windows directory
- DrvInst.exe (PID: 3780)
- DrvInst.exe (PID: 3460)
Executed as Windows Service
- vssvc.exe (PID: 3388)
- openvpnserv.exe (PID: 3904)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3780)
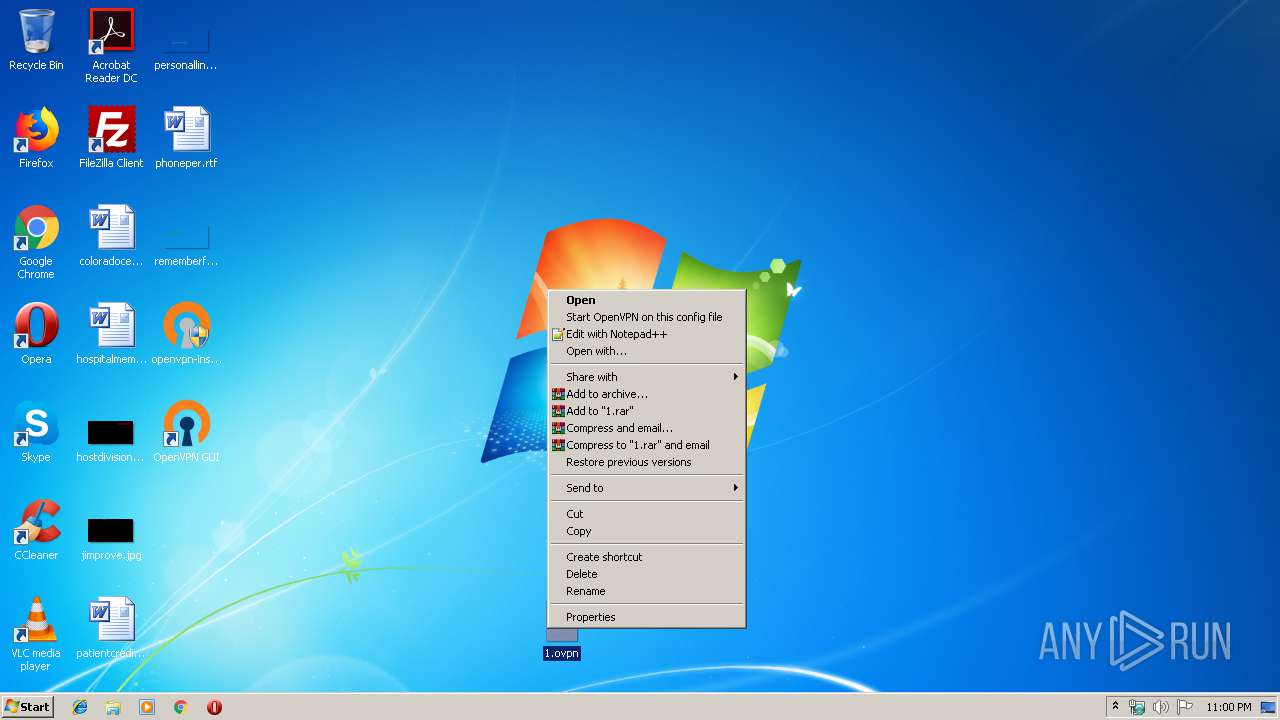
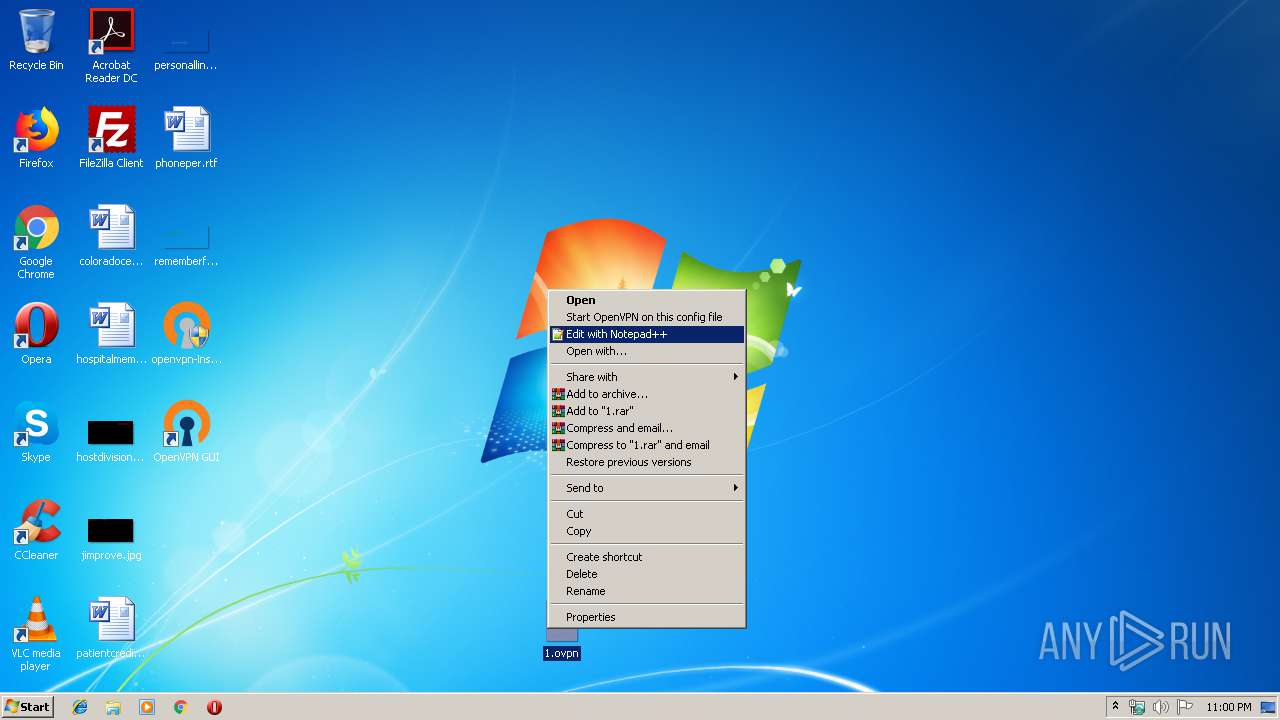
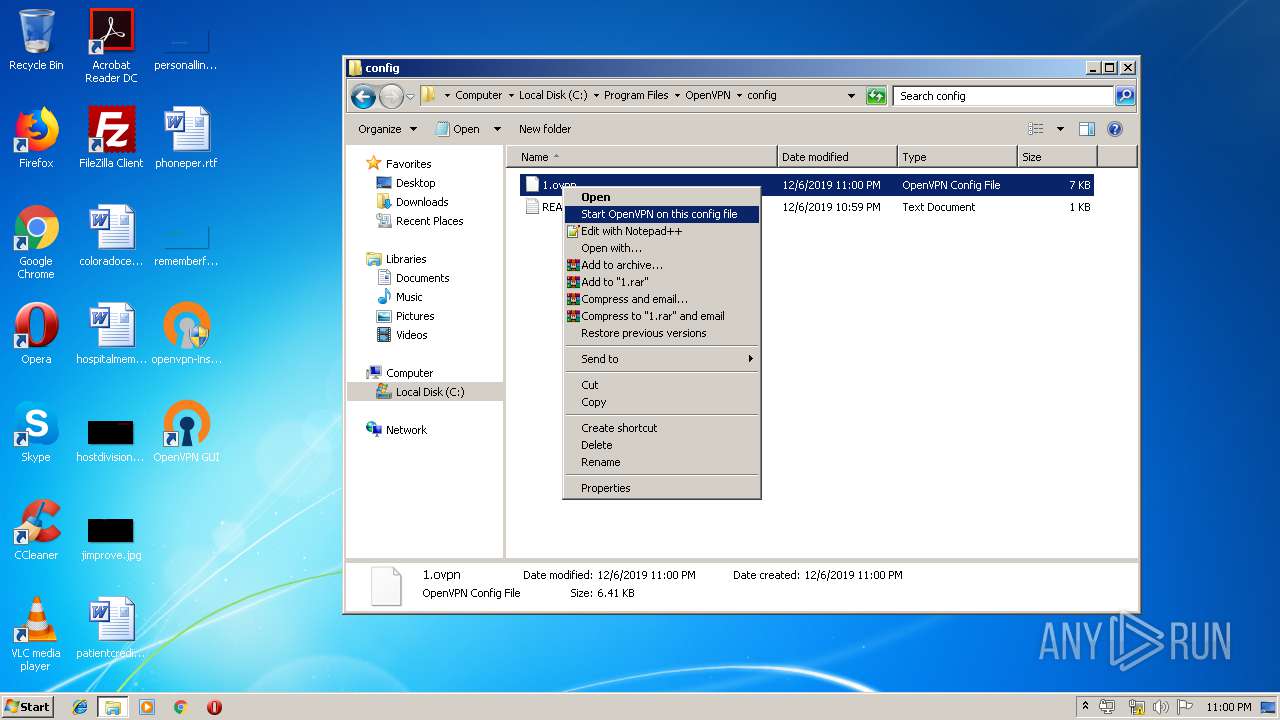
Modifies the open verb of a shell class
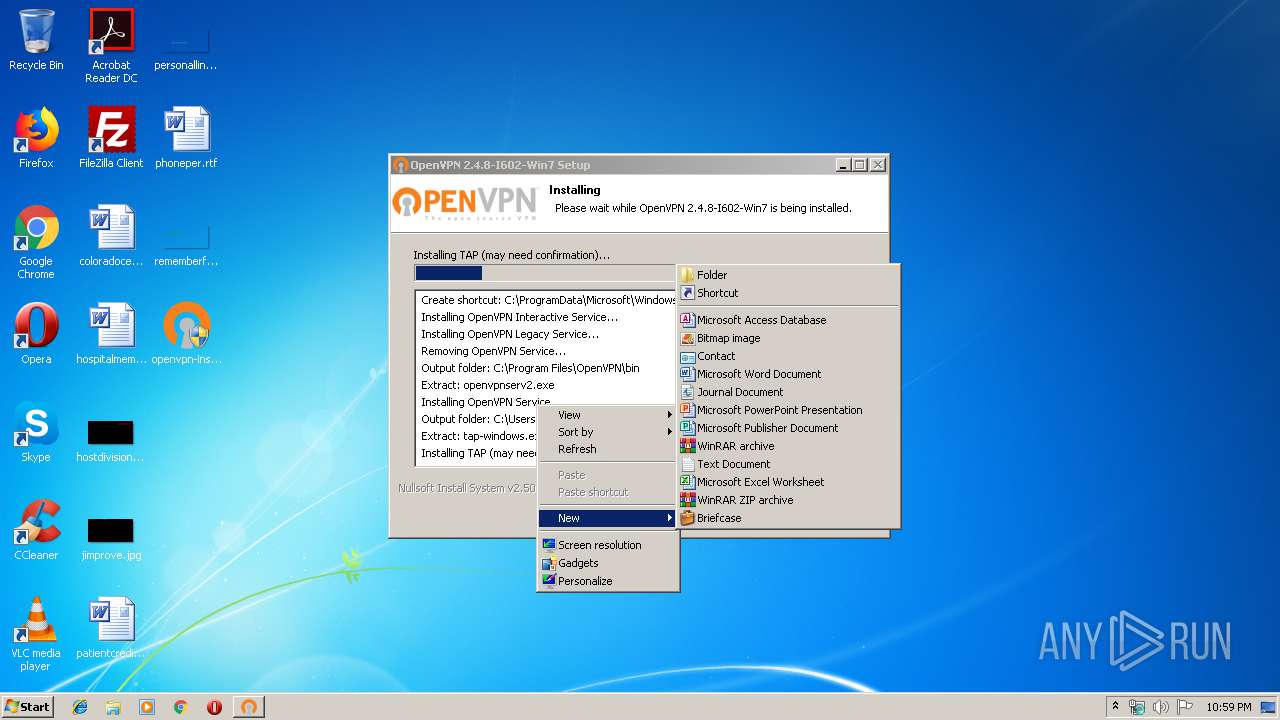
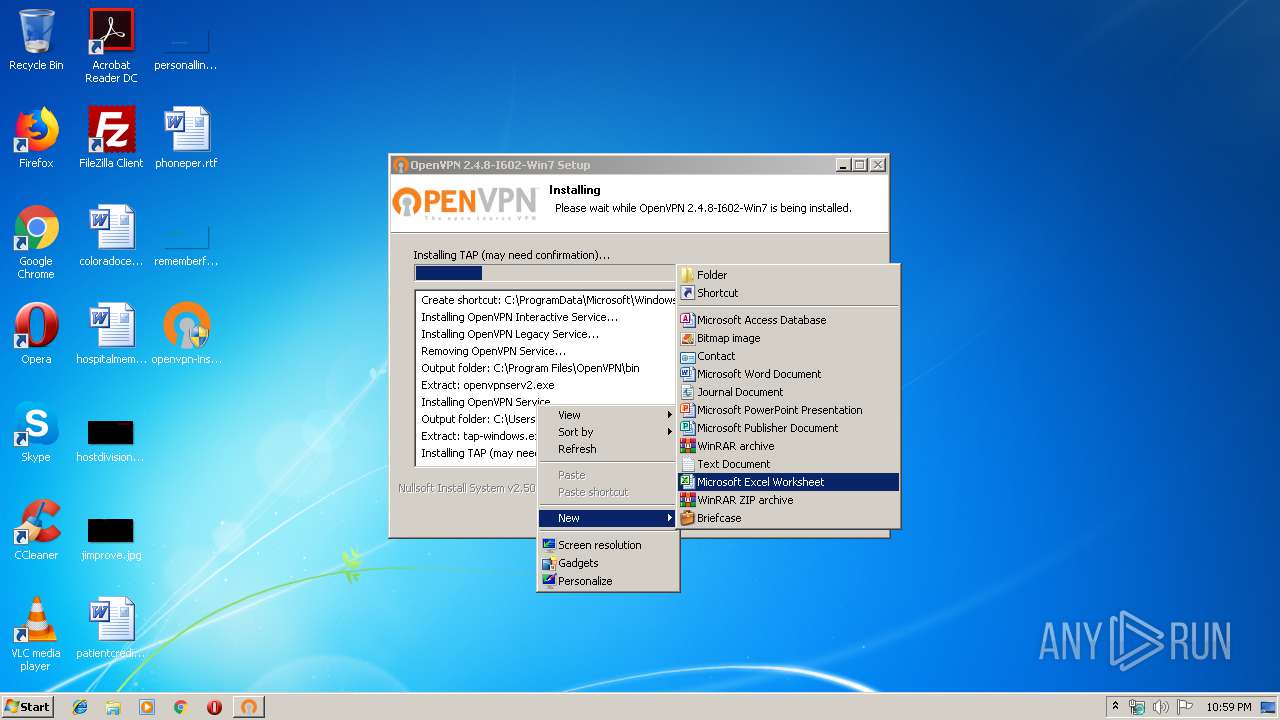
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
Creates a software uninstall entry
- tap-windows.exe (PID: 600)
- openvpn-install-2.4.8-I602-Win7.exe (PID: 2536)
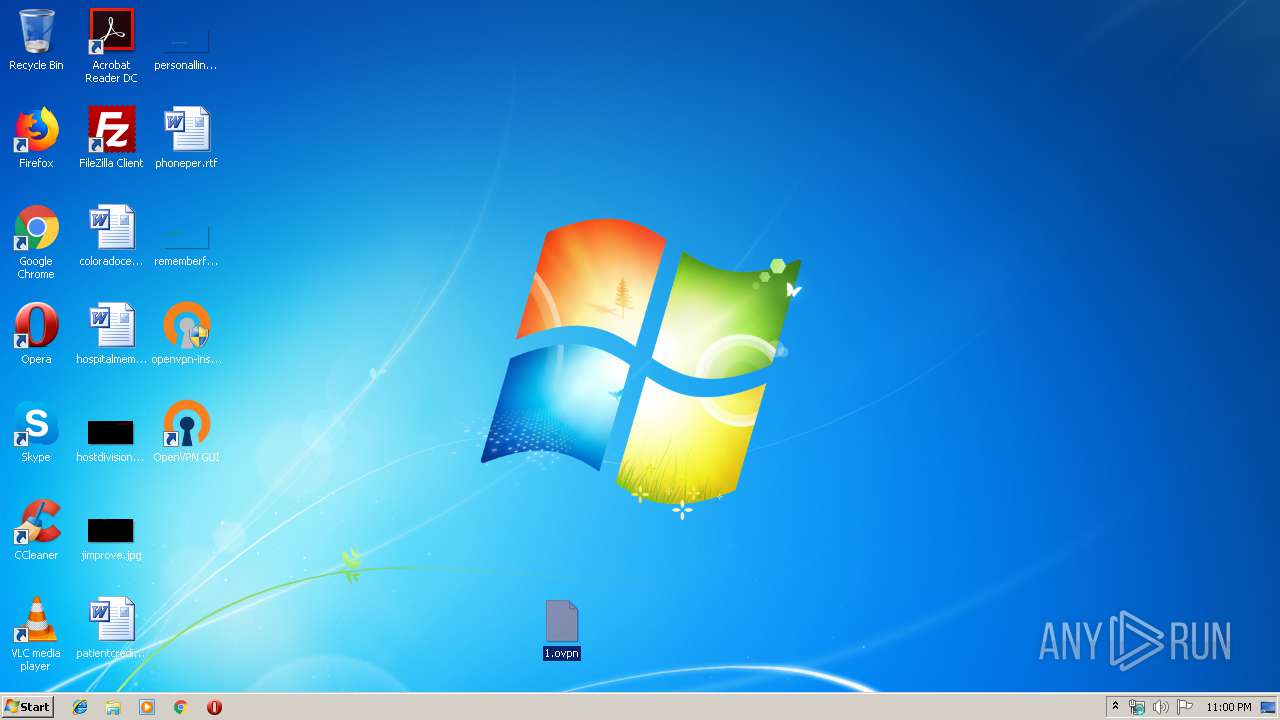
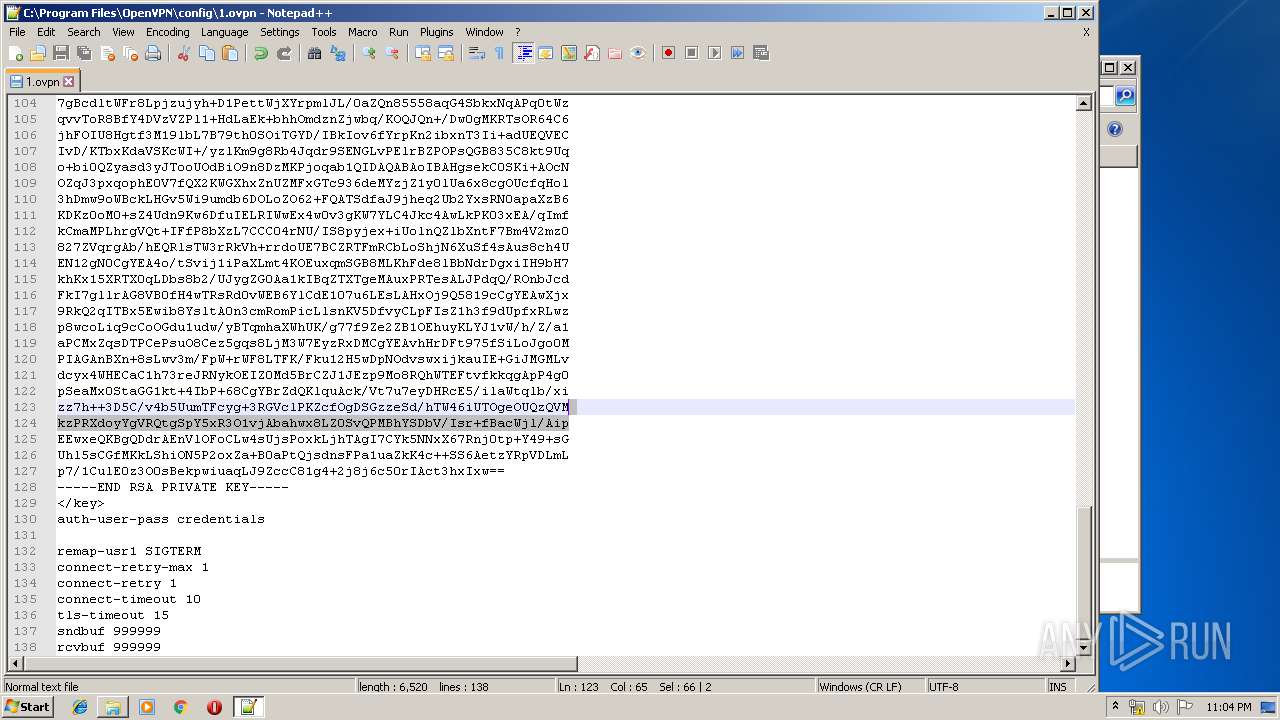
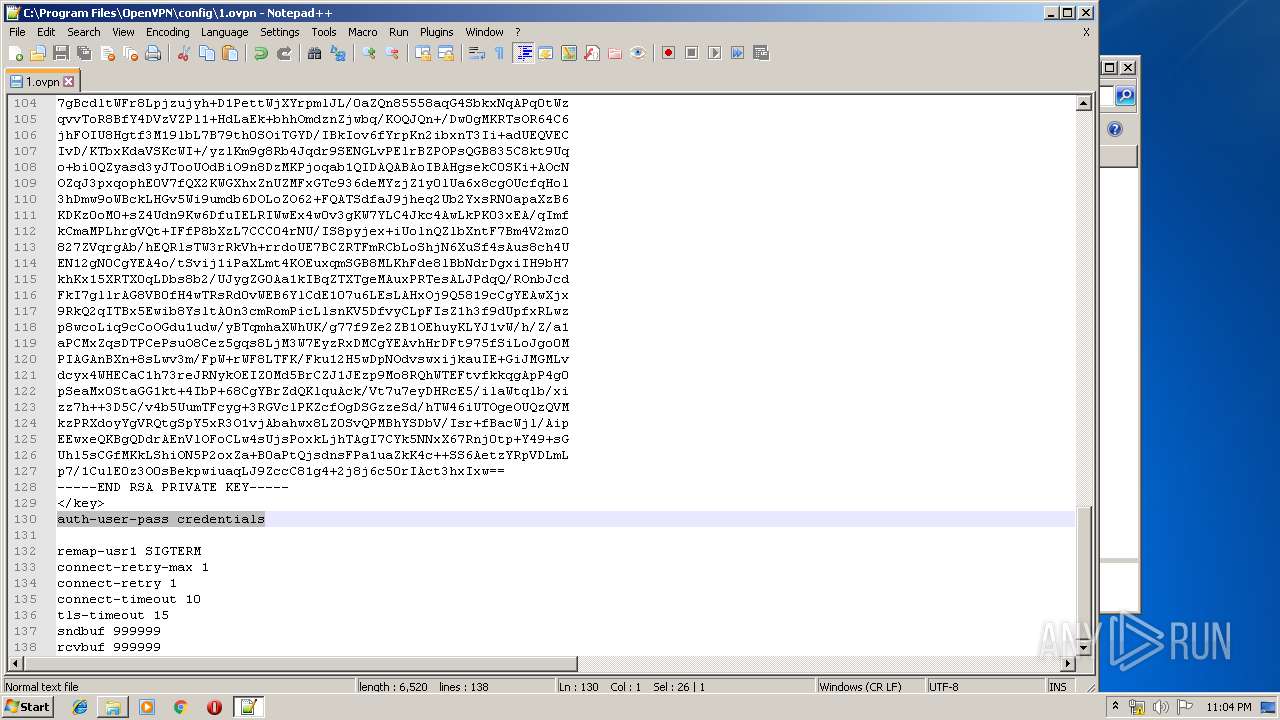
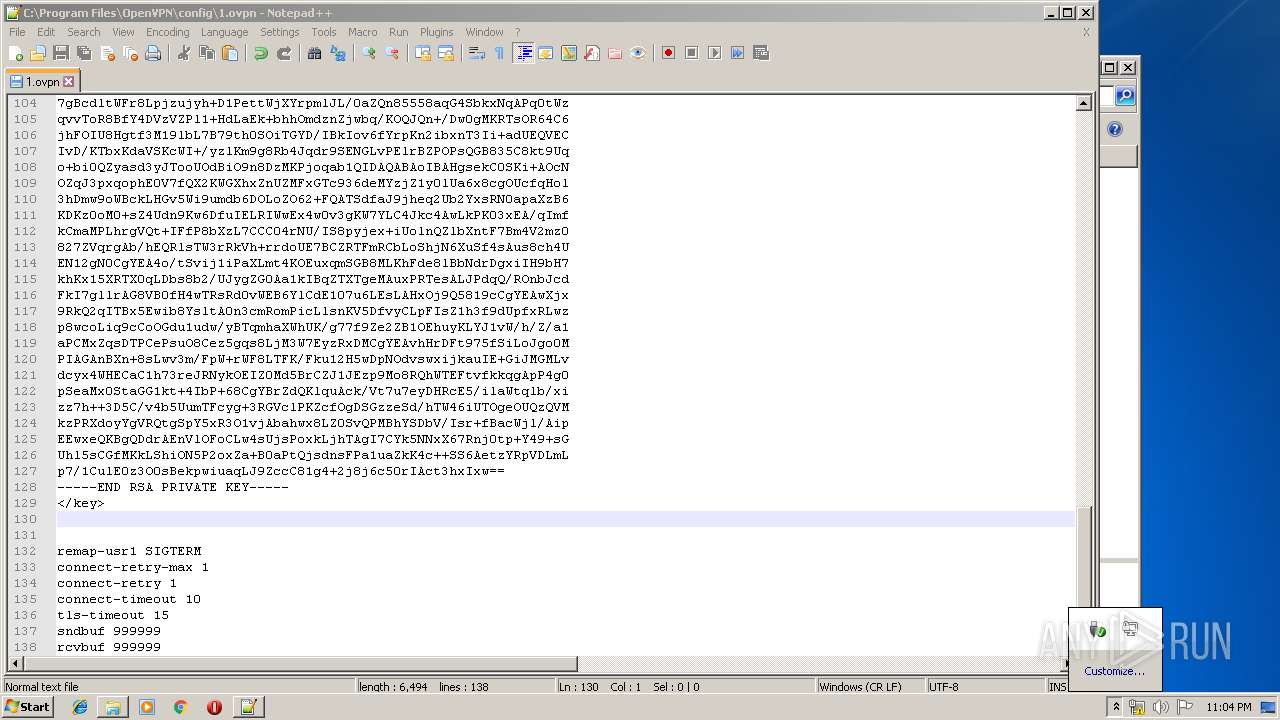
Creates files in the user directory
- notepad++.exe (PID: 1936)
- notepad++.exe (PID: 4064)
INFO
Searches for installed software
- DrvInst.exe (PID: 3780)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3388)
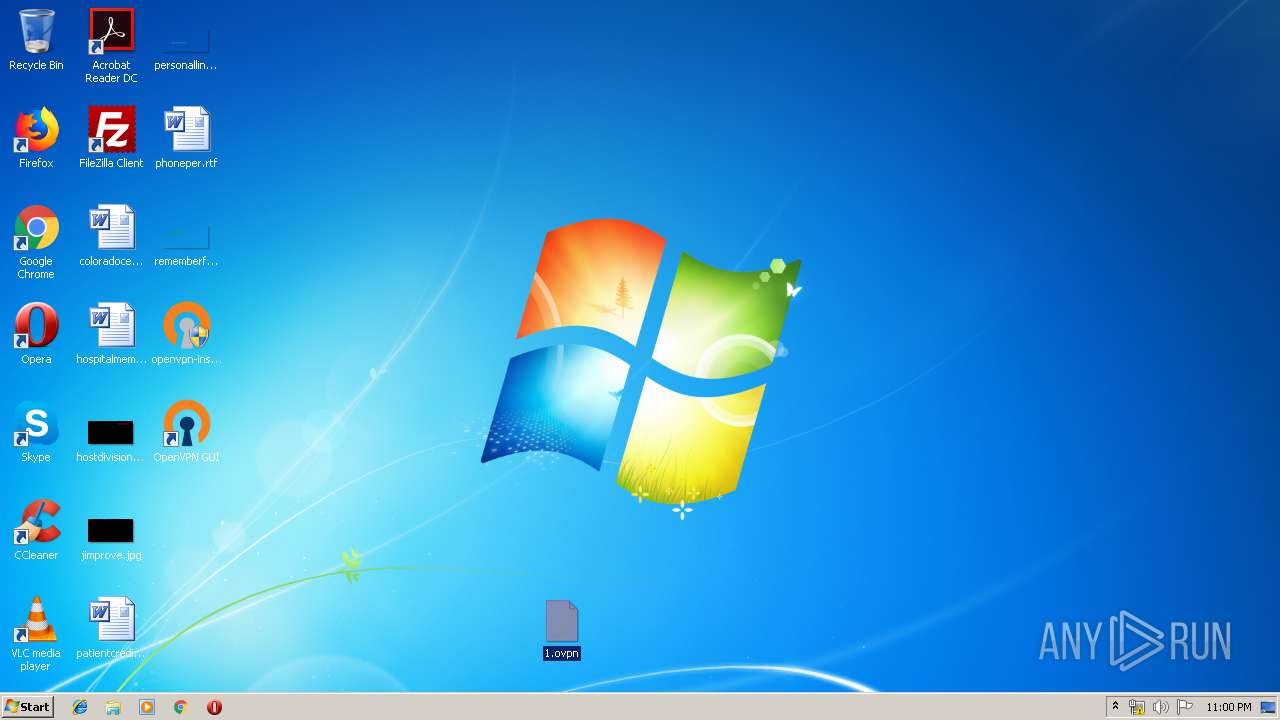
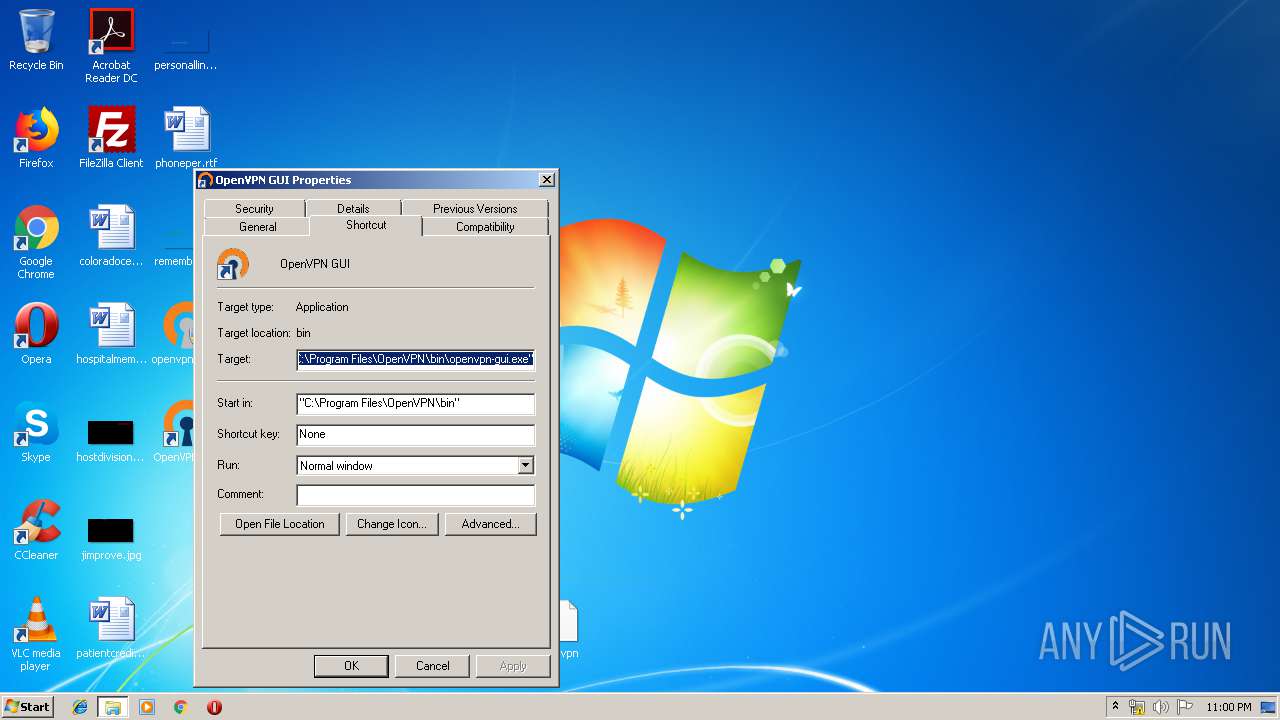
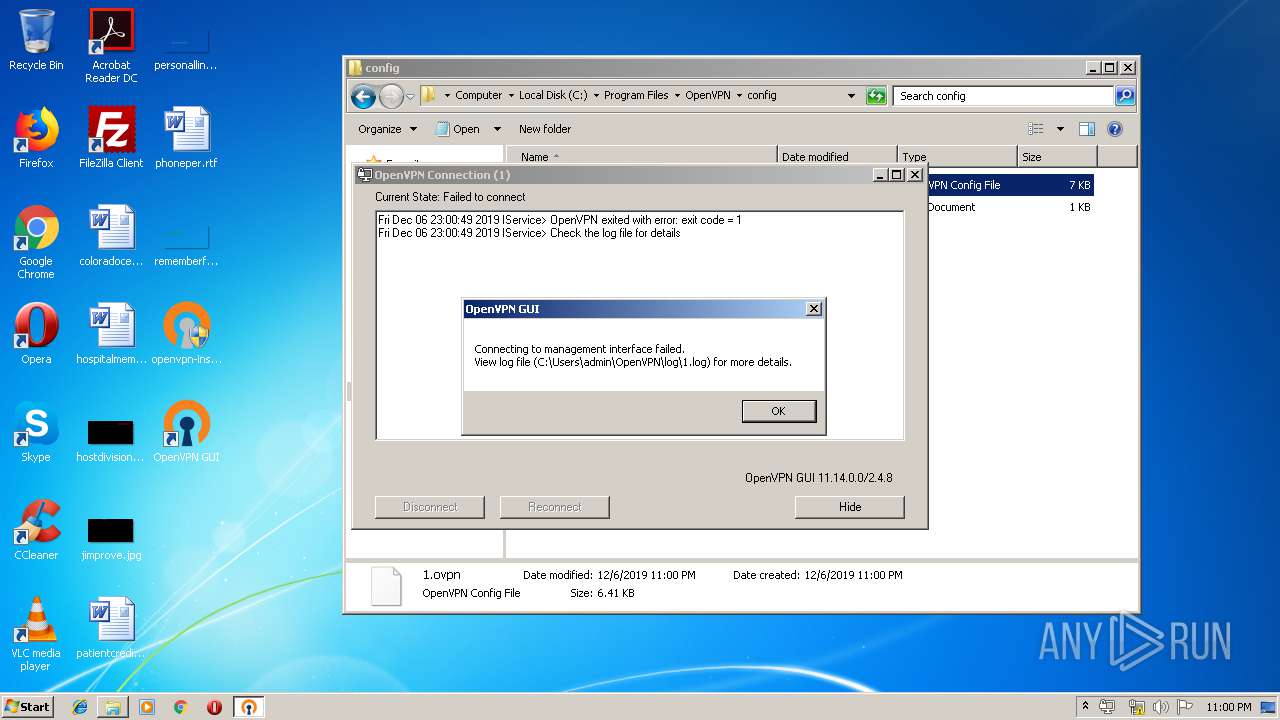
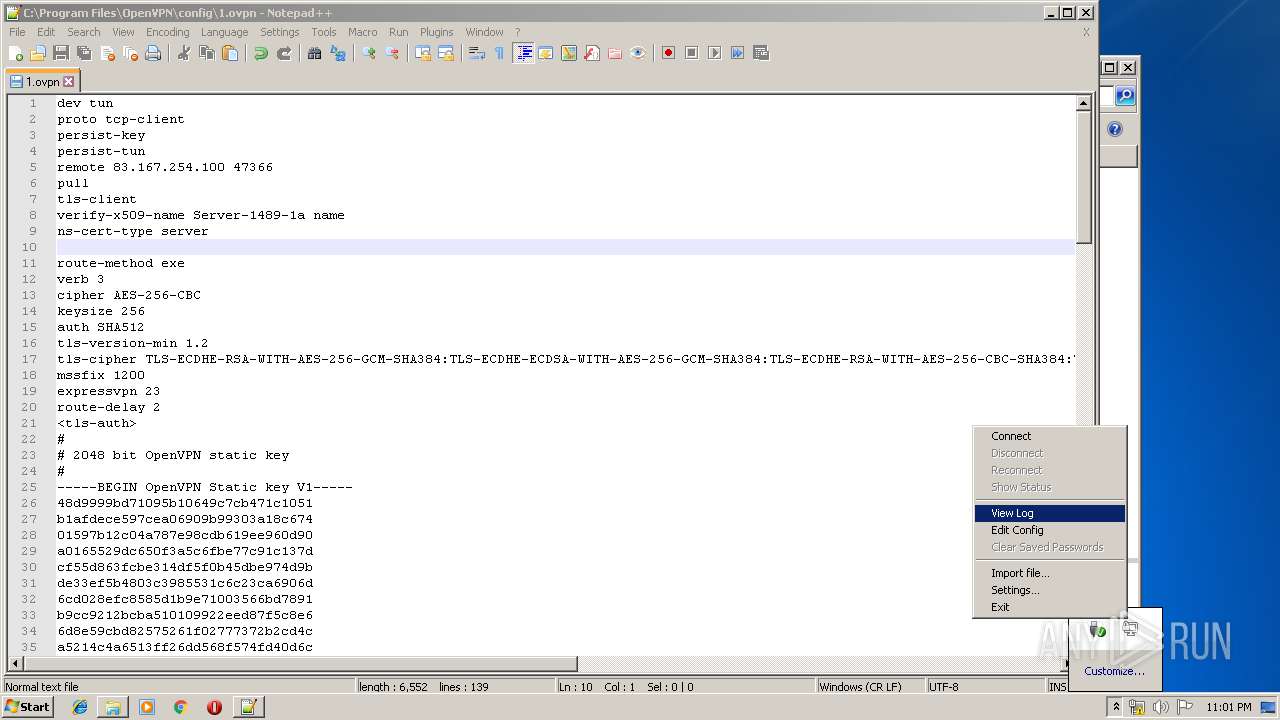
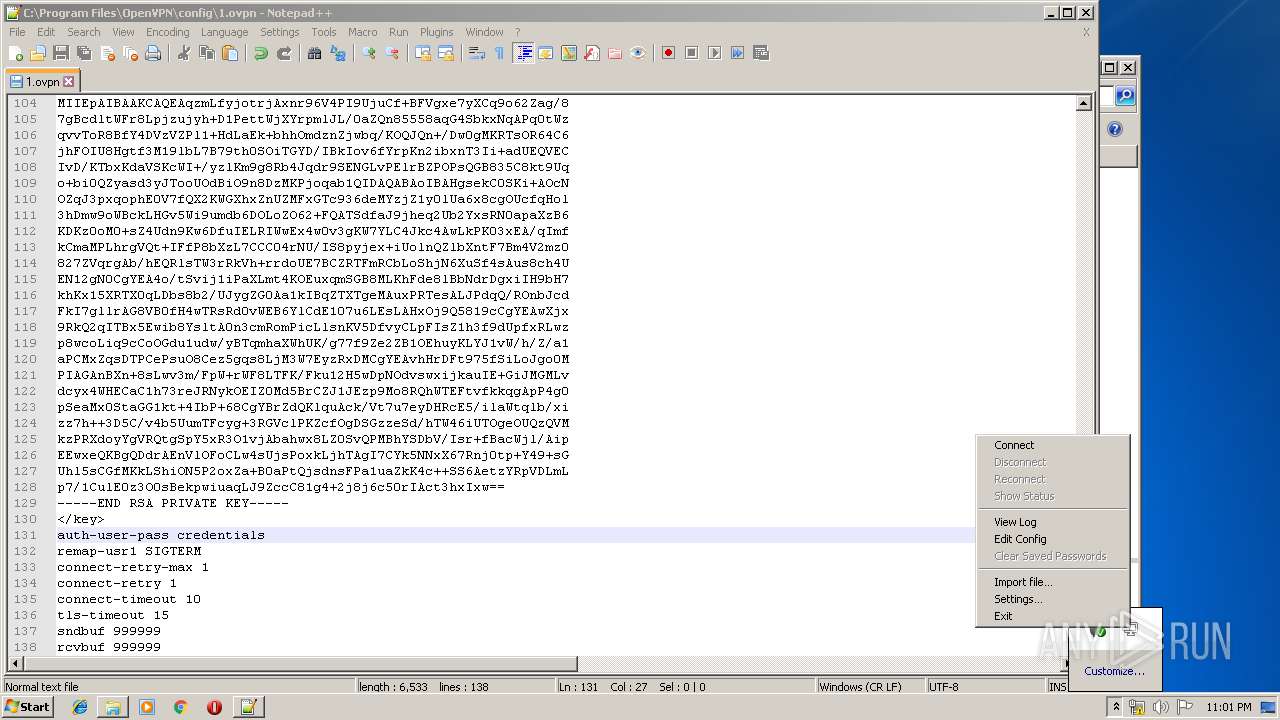
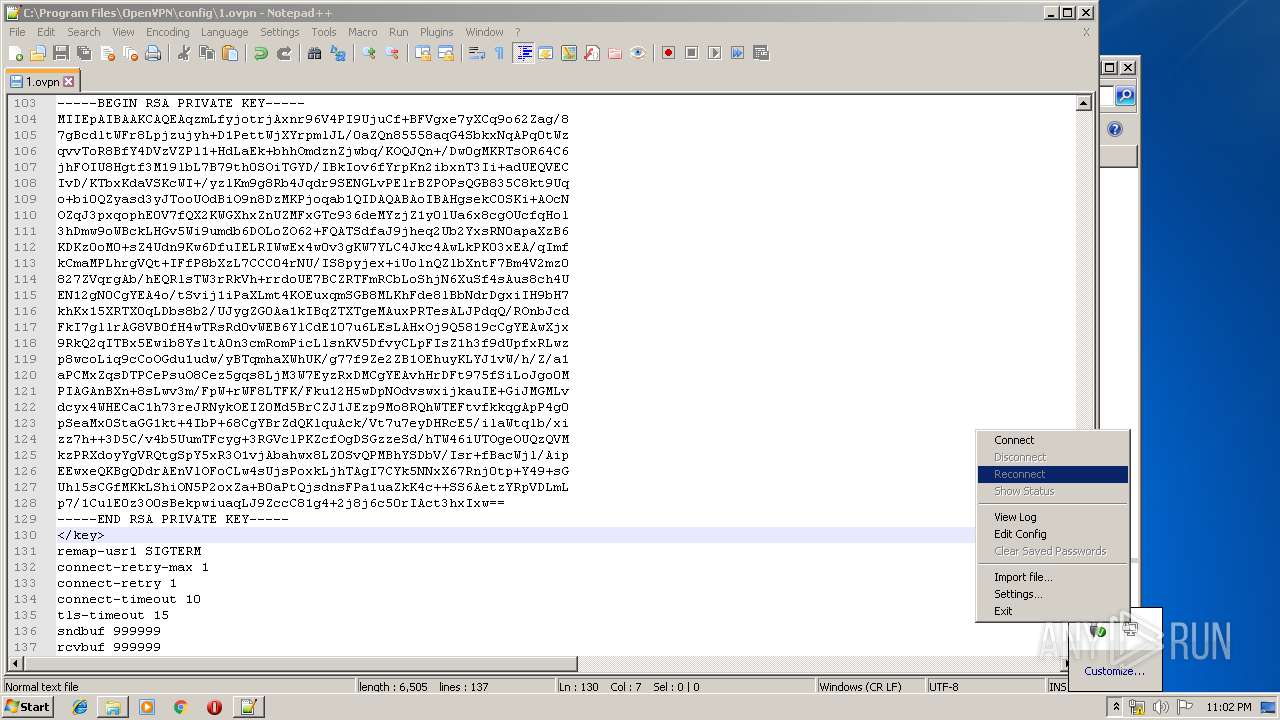
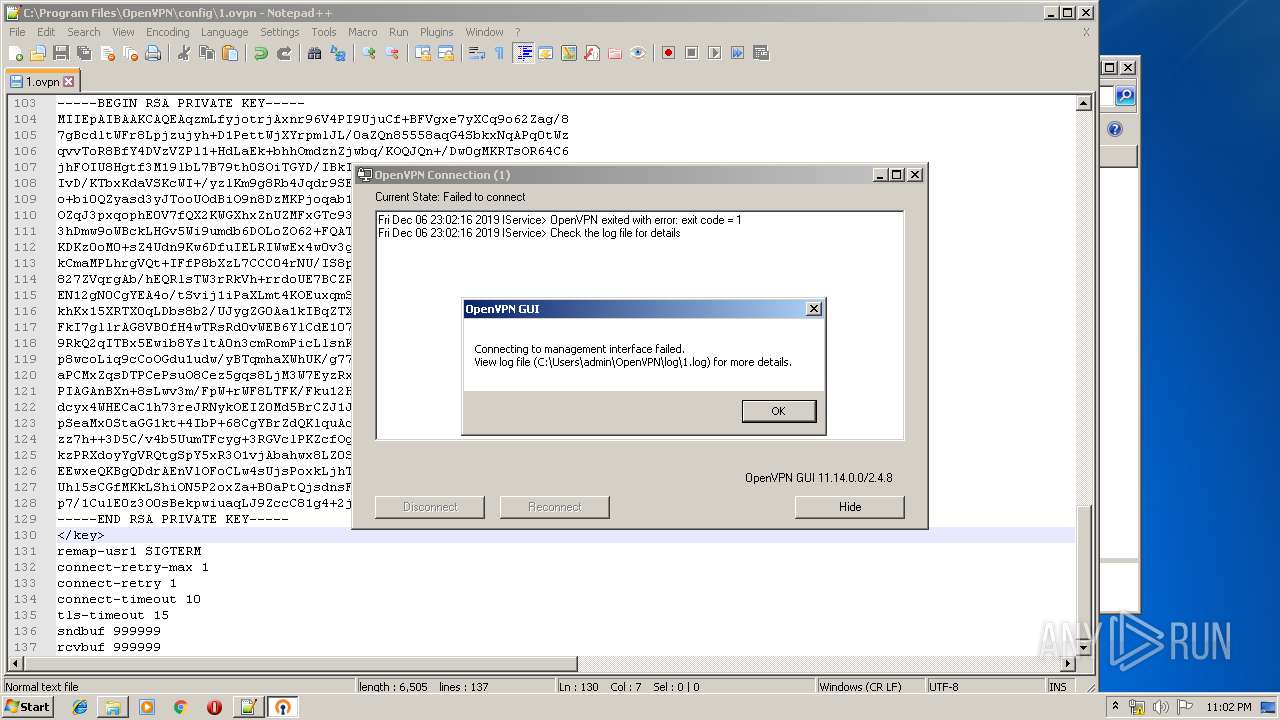
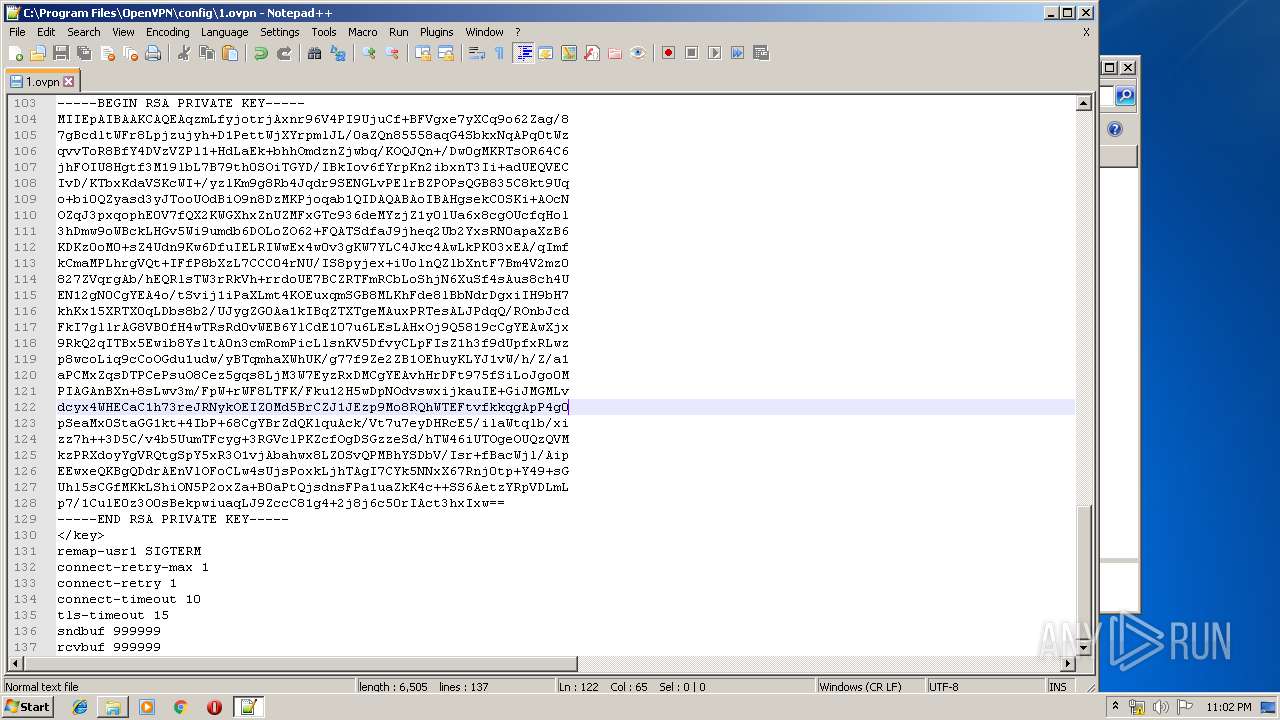
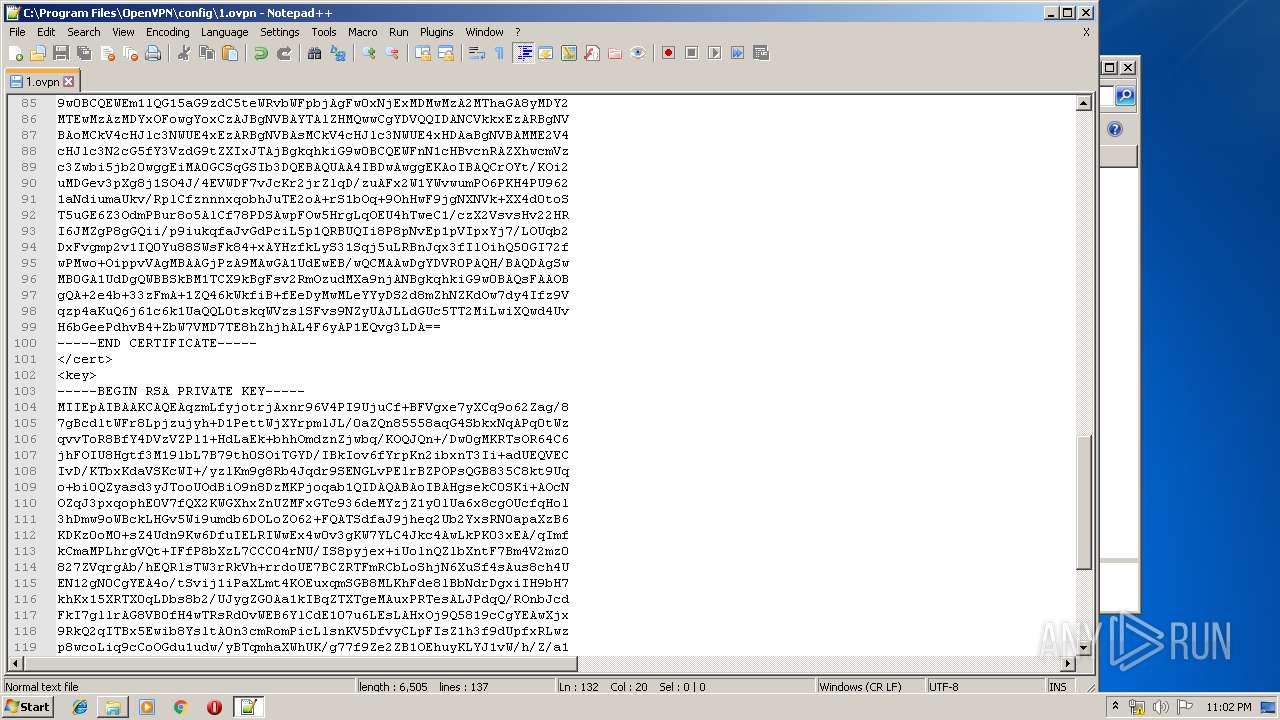
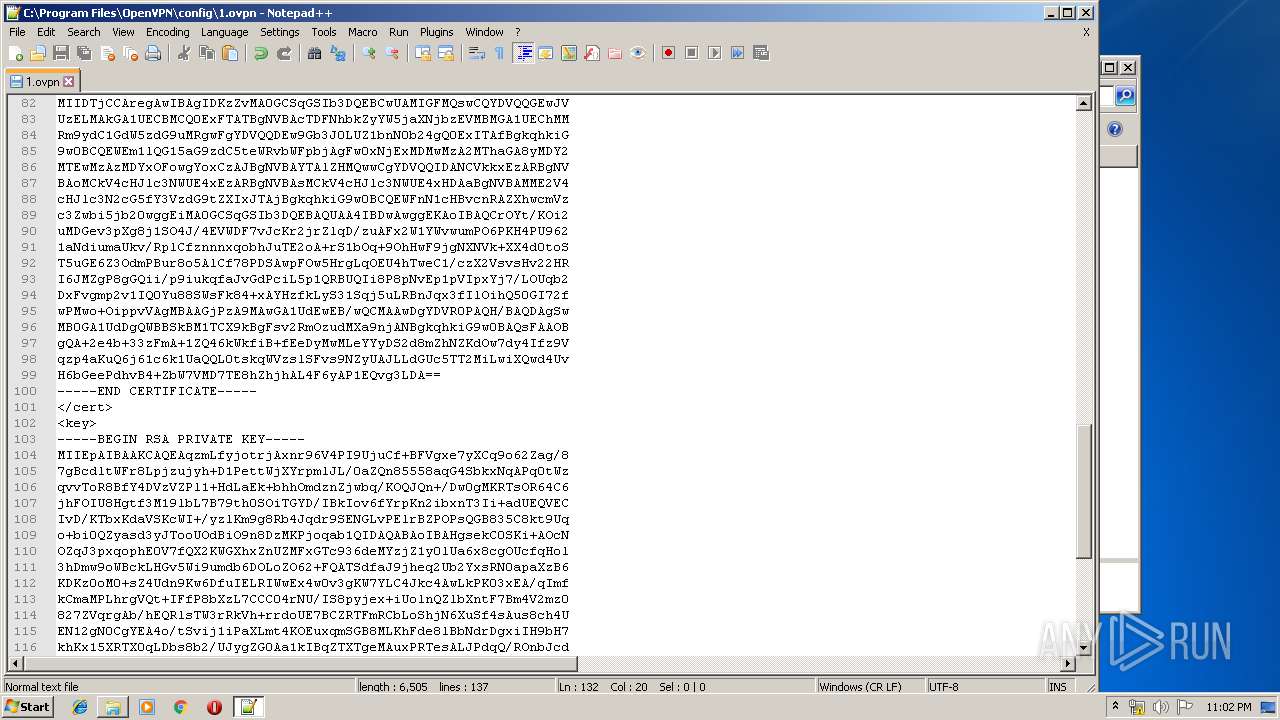
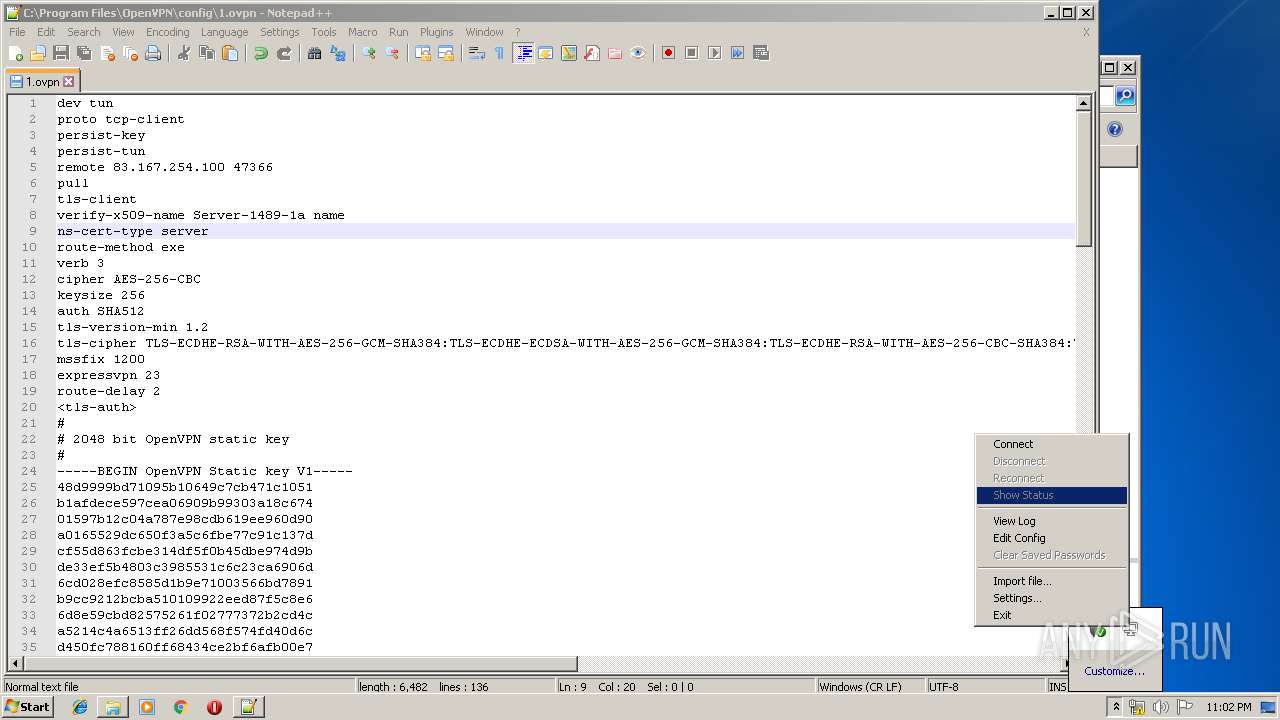
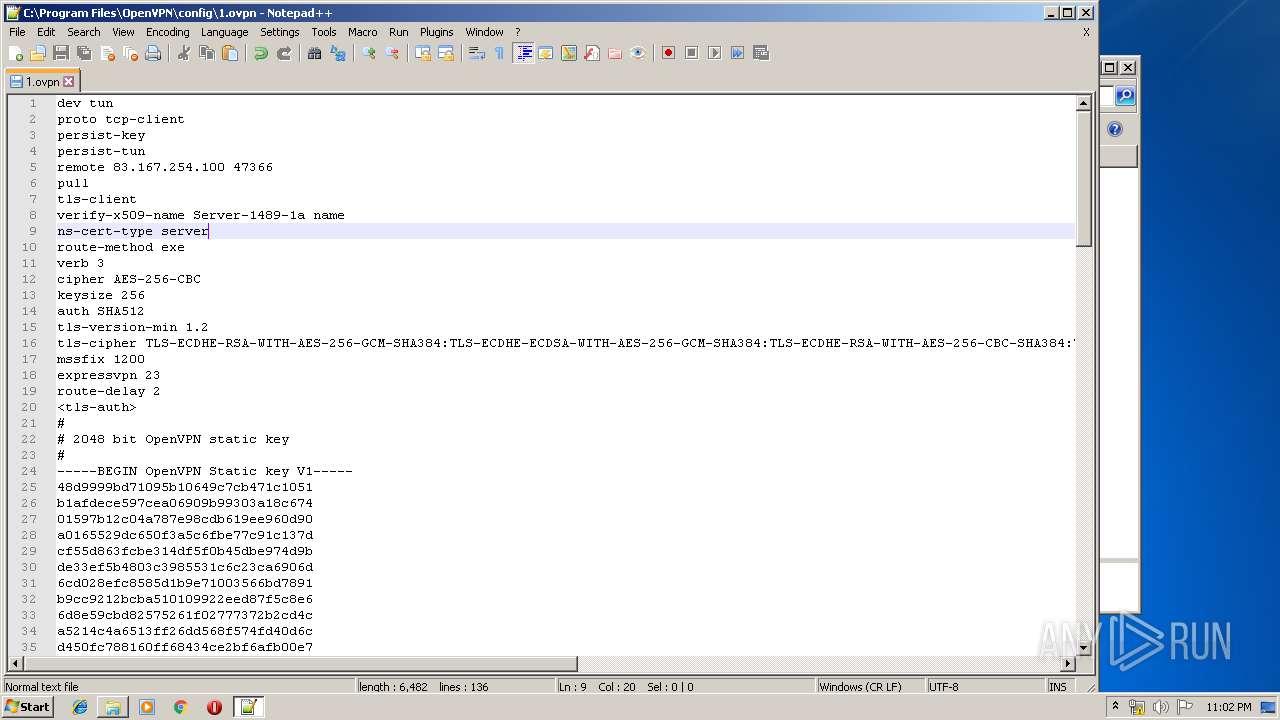
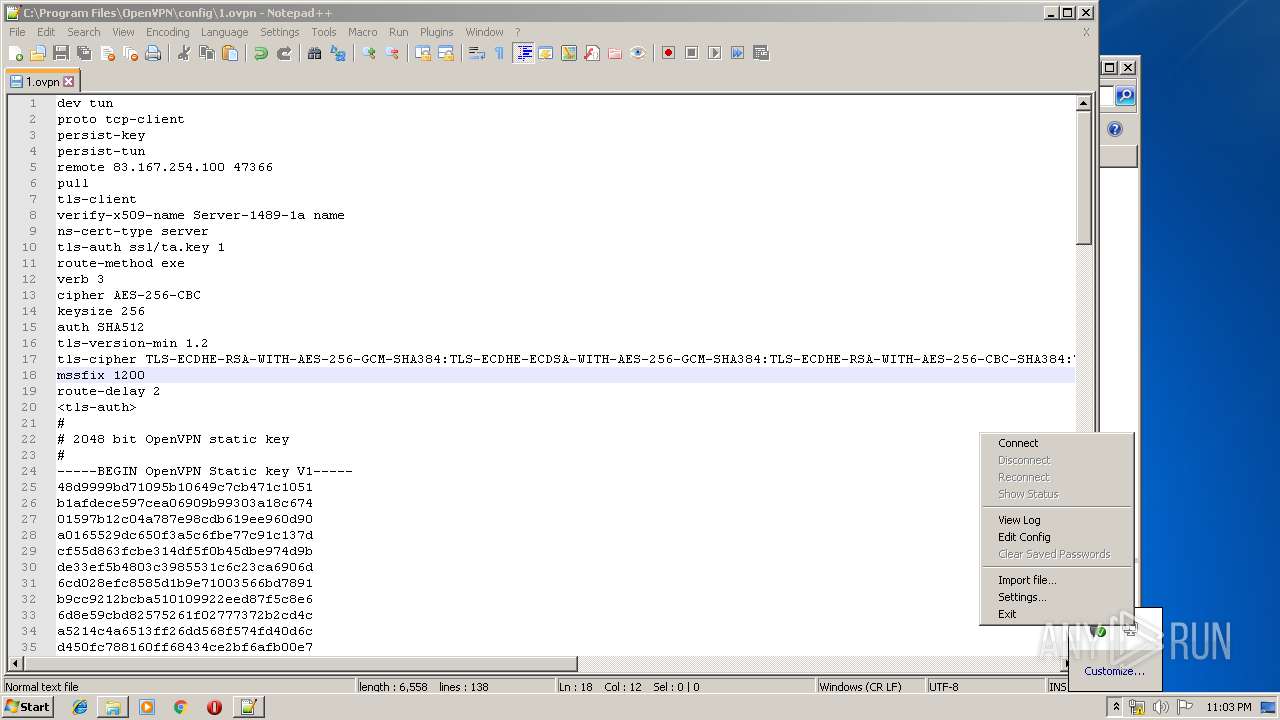
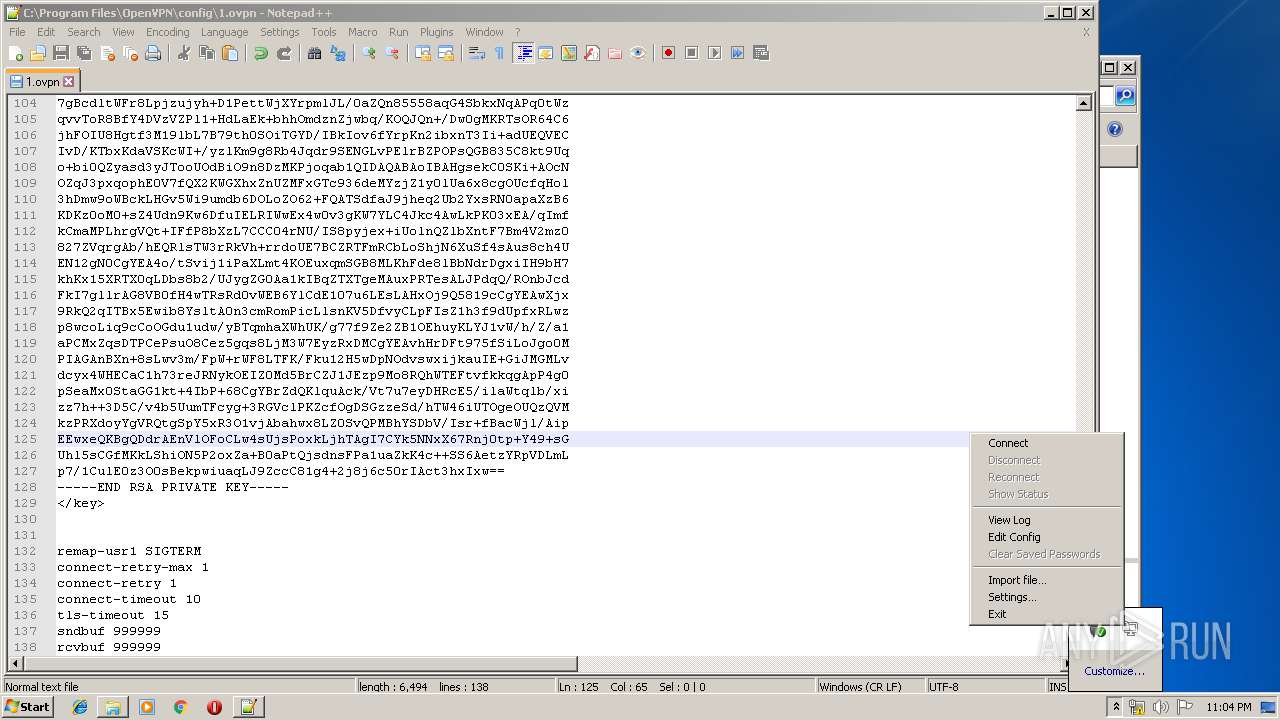
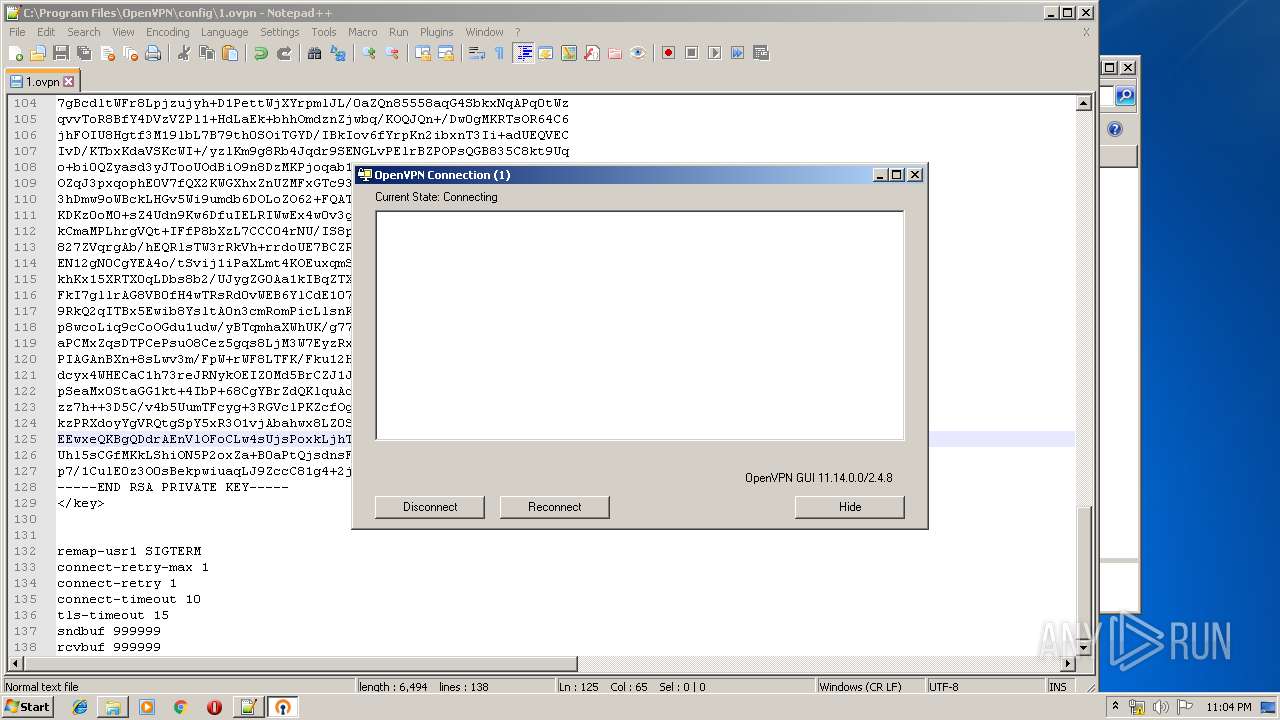
Manual execution by user
- notepad++.exe (PID: 1936)
- openvpn-gui.exe (PID: 3840)
- notepad++.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:14 12:25:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 35840 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | 110080 |
| EntryPoint: | 0x435d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jan-2016 11:25:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Jan-2016 11:25:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008B00 | 0x00008C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.94115 |
.data | 0x0000A000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.62893 |
.rdata | 0x0000B000 | 0x000069D8 | 0x00006A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29941 |
.bss | 0x00012000 | 0x0001AD00 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002D000 | 0x00001298 | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.17963 |
.ndata | 0x0002F000 | 0x0001A000 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00049000 | 0x00006DC8 | 0x00006E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.84466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21582 | 960 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.15056 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 3.94986 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.50443 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.1424 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 4.74328 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.70702 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.47314 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70176 | 356 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68101 | 582 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
94
Monitored processes
28
Malicious processes
8
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Users\admin\AppData\Local\Temp\tap-windows.exe" /S /SELECT_UTILITIES=1 | C:\Users\admin\AppData\Local\Temp\tap-windows.exe | nsD2FD.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\Temp\nsqD454.tmp\nsD62B.tmp" "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Users\admin\AppData\Local\Temp\nsqD454.tmp\nsD62B.tmp | — | tap-windows.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
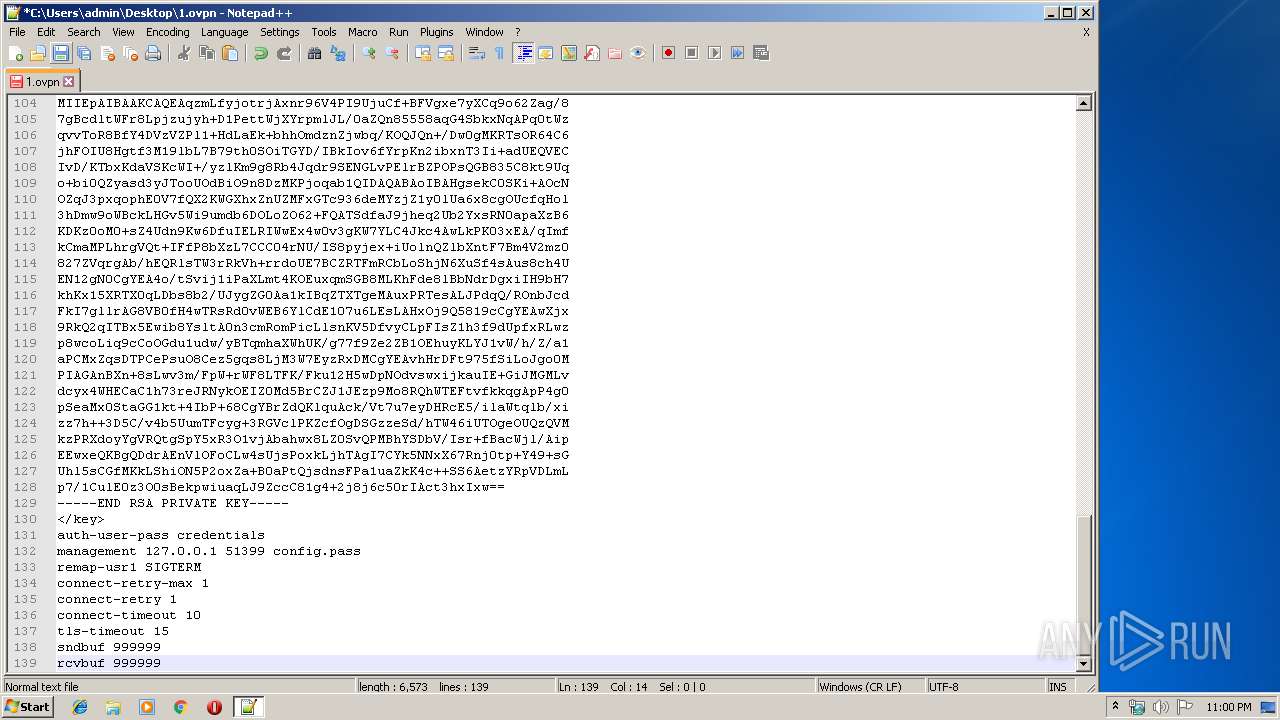
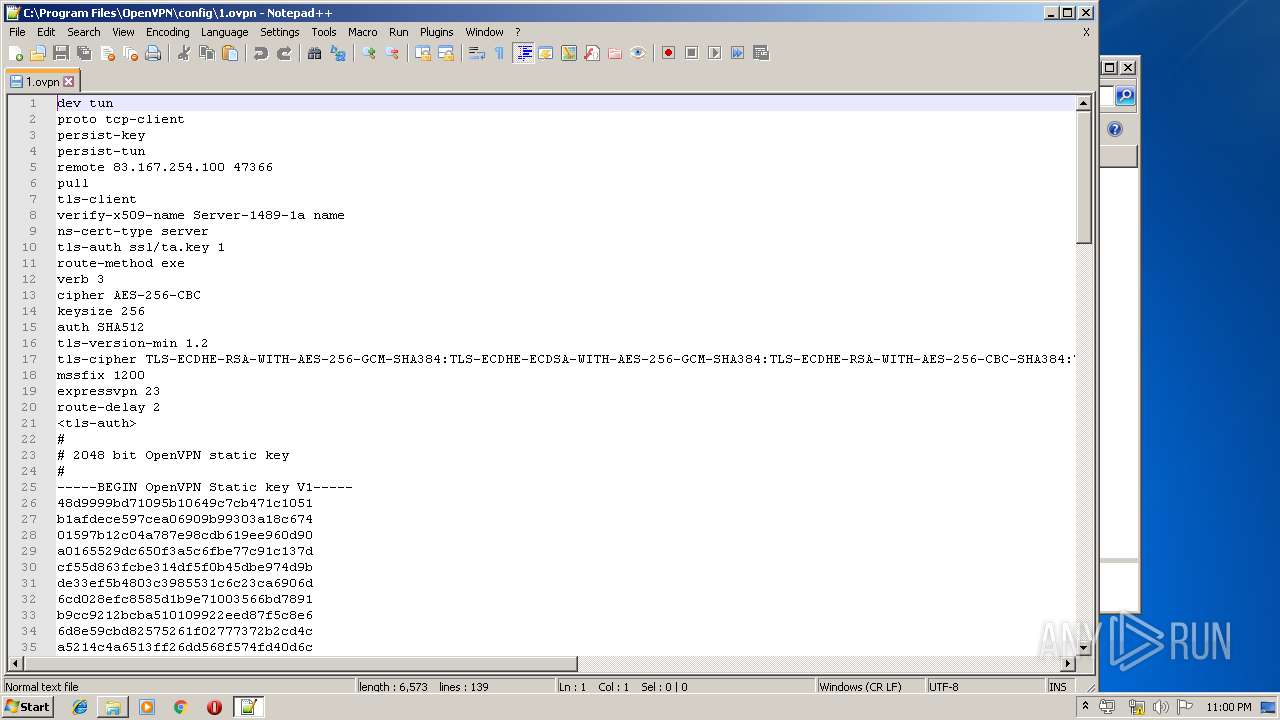
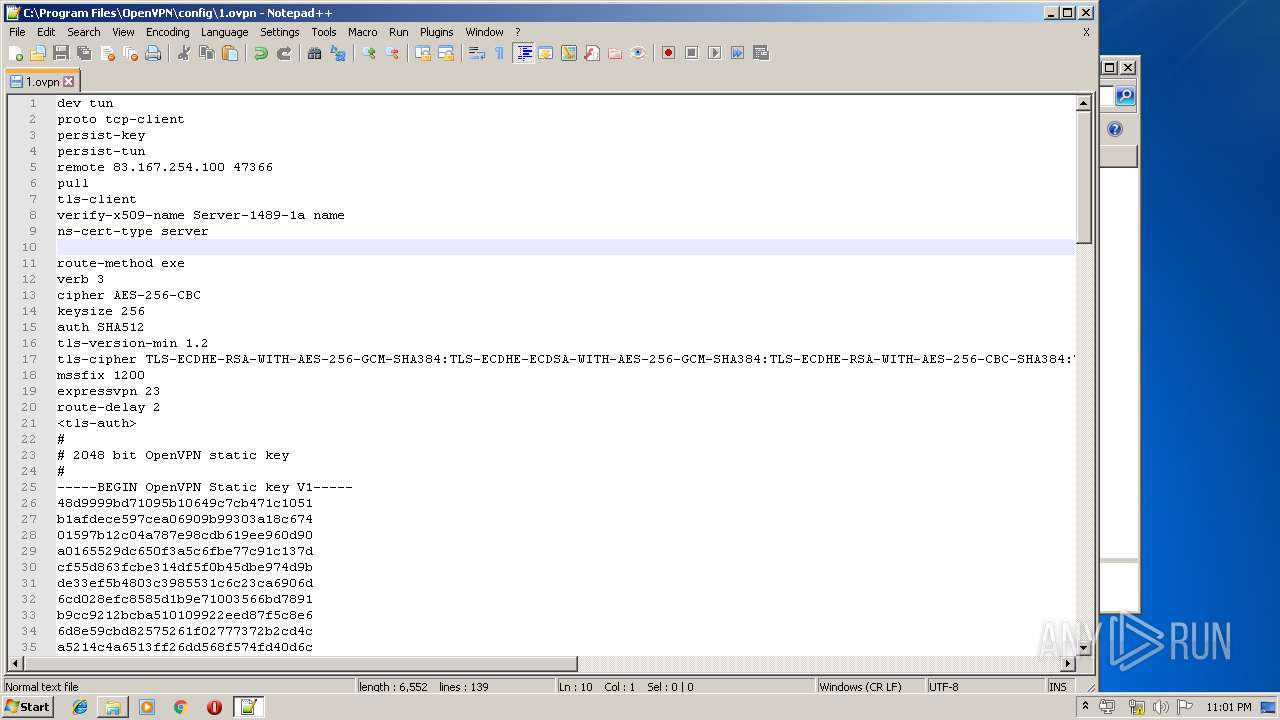
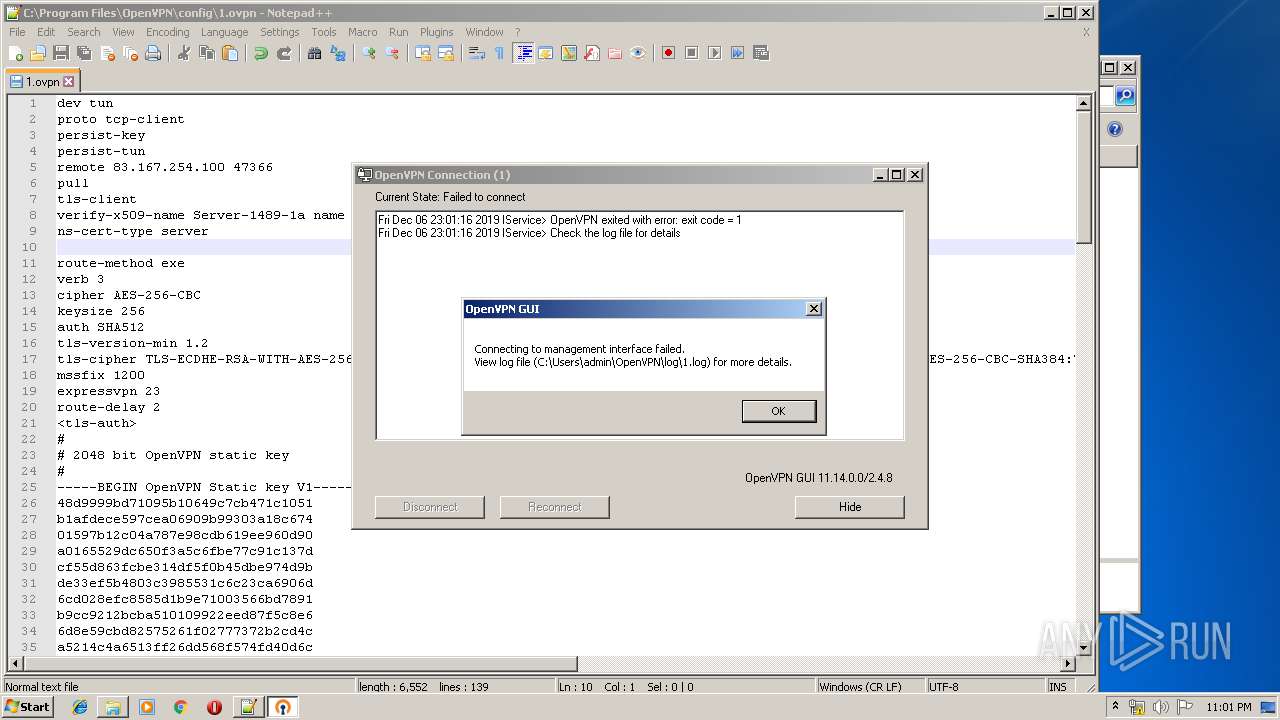
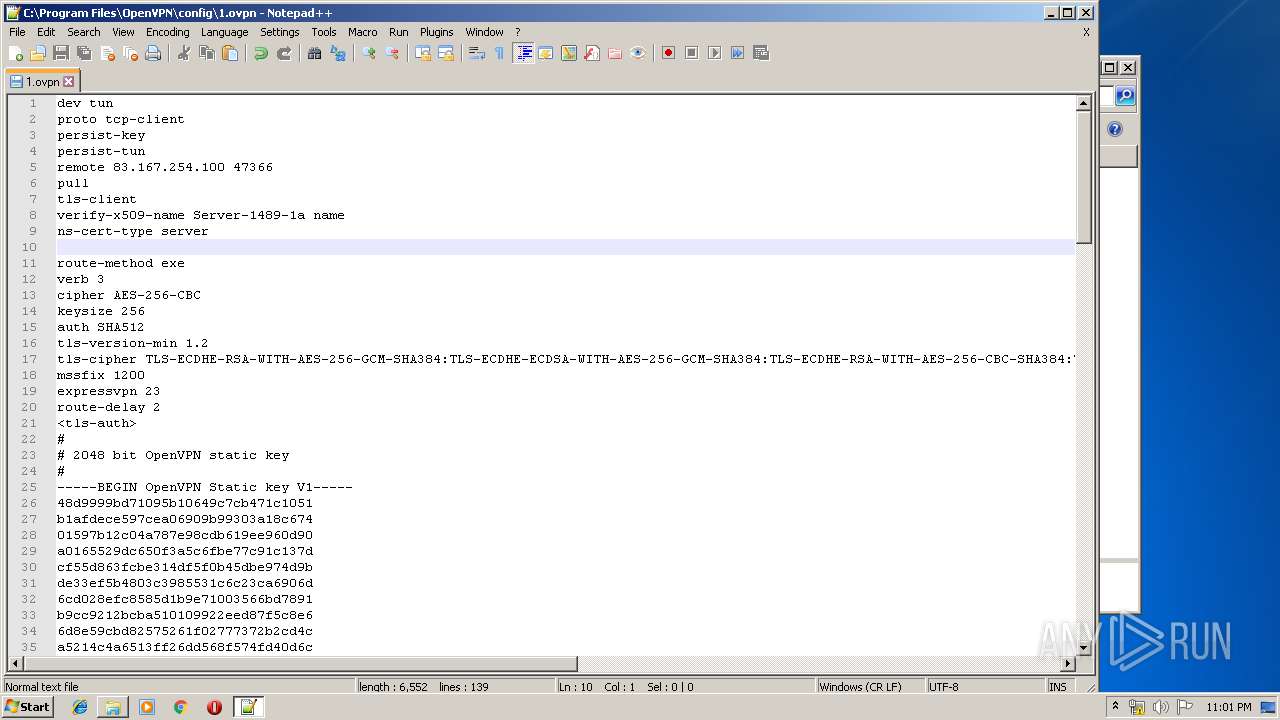
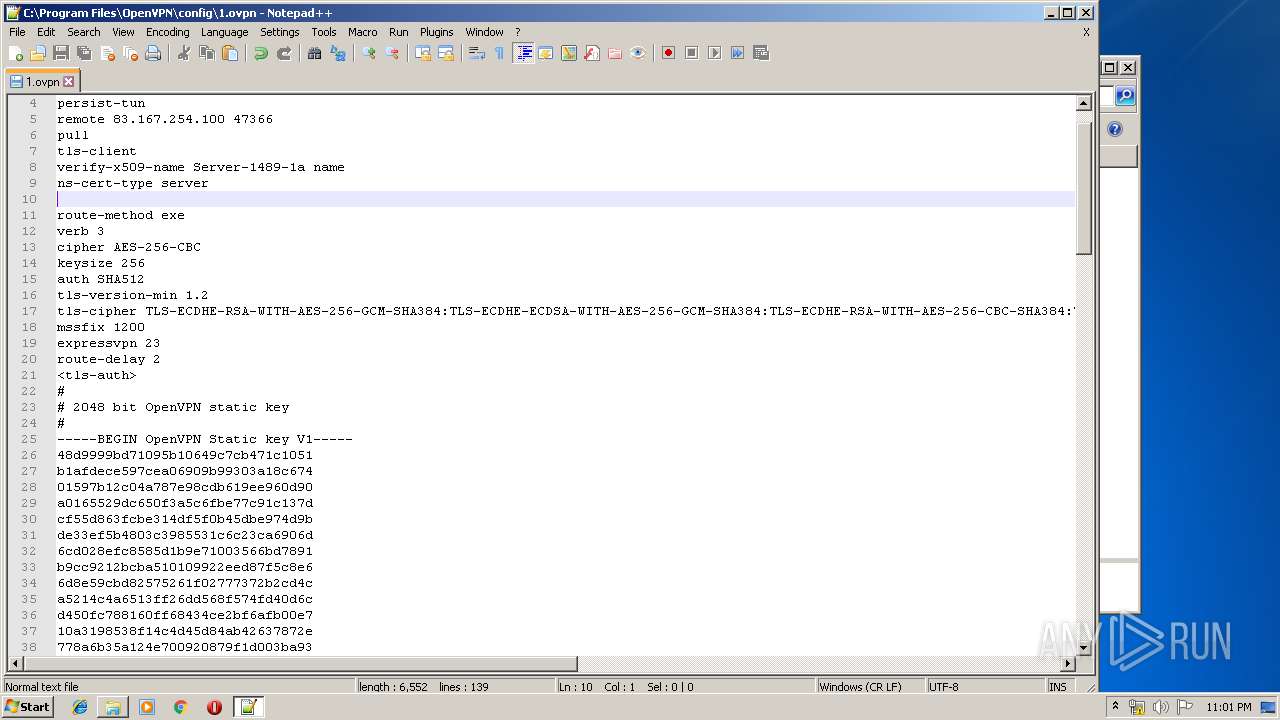
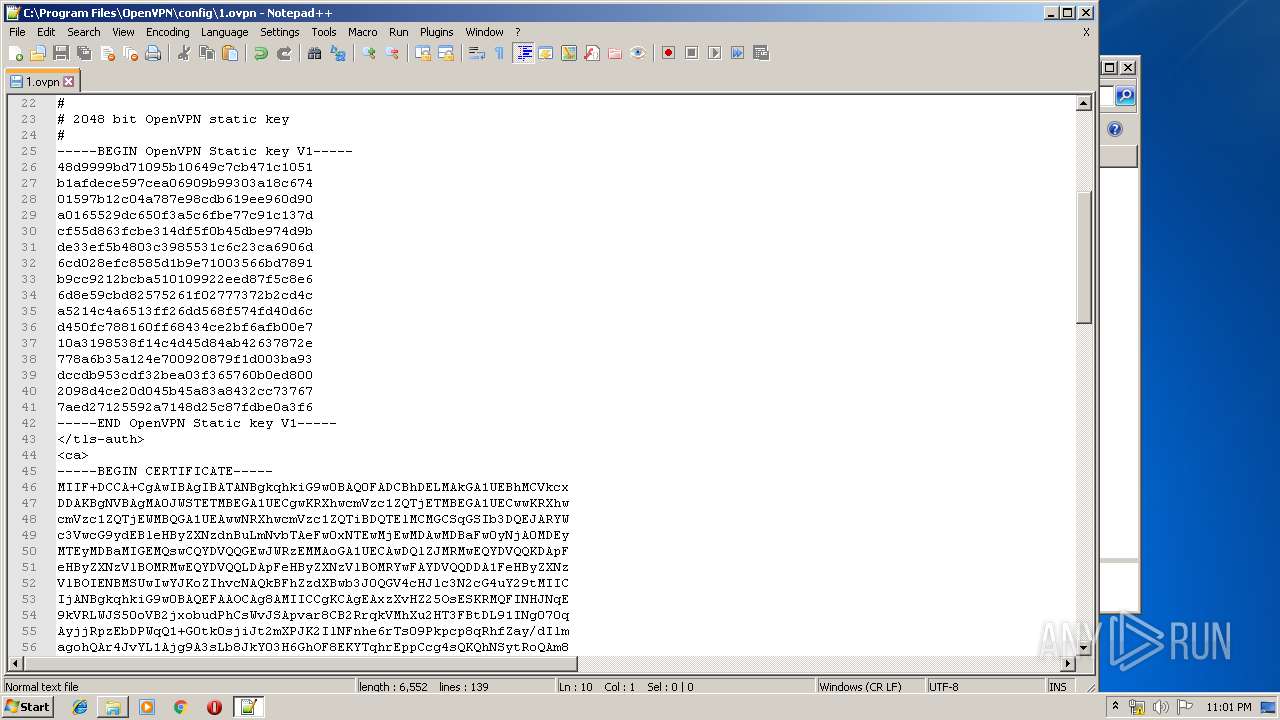
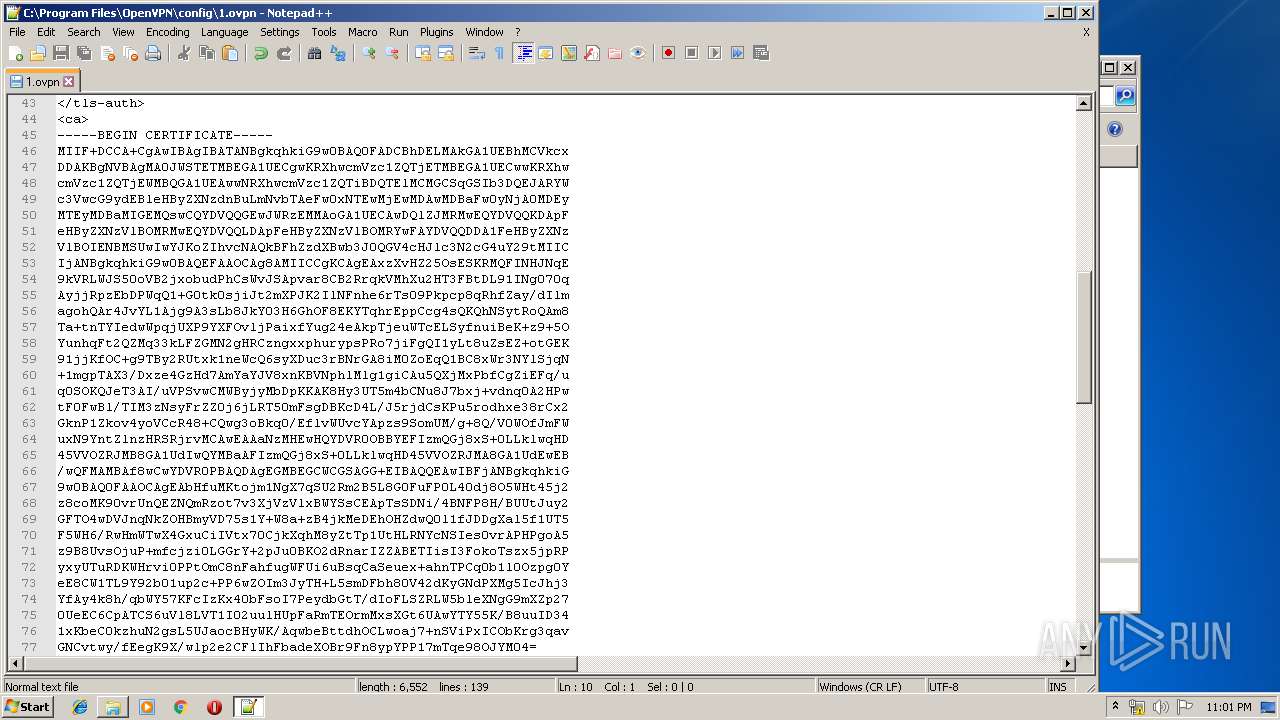
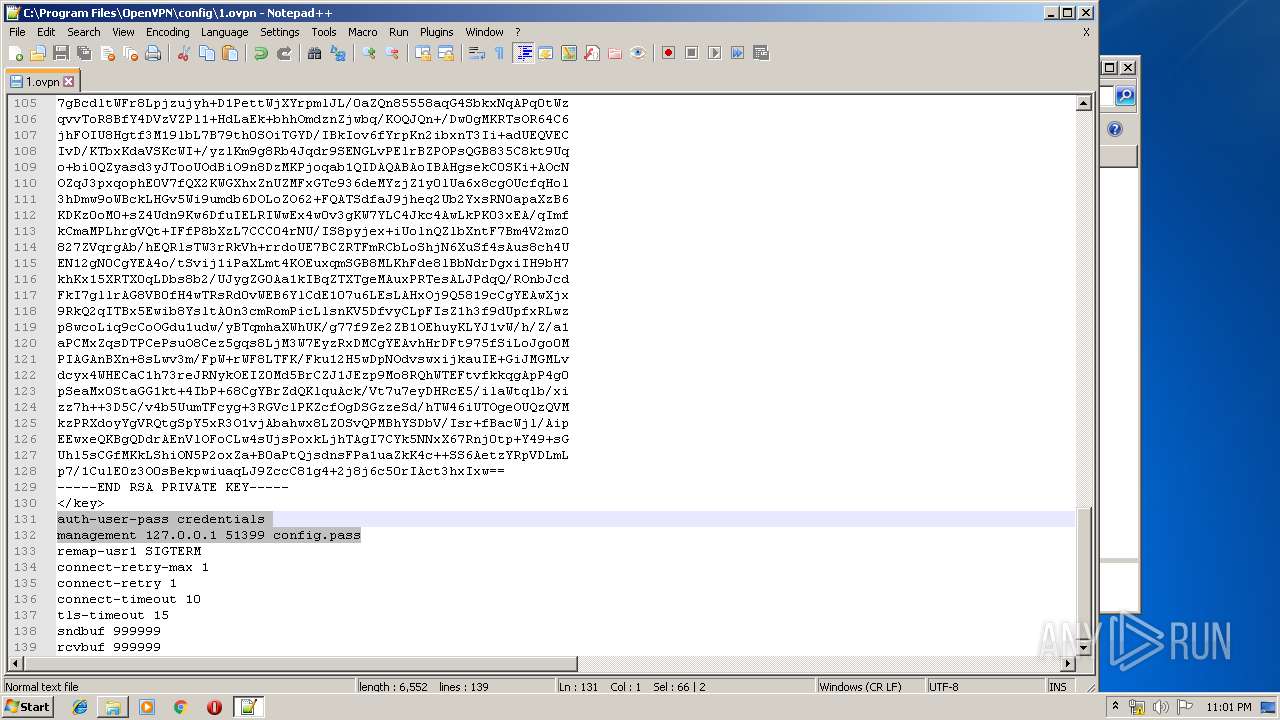
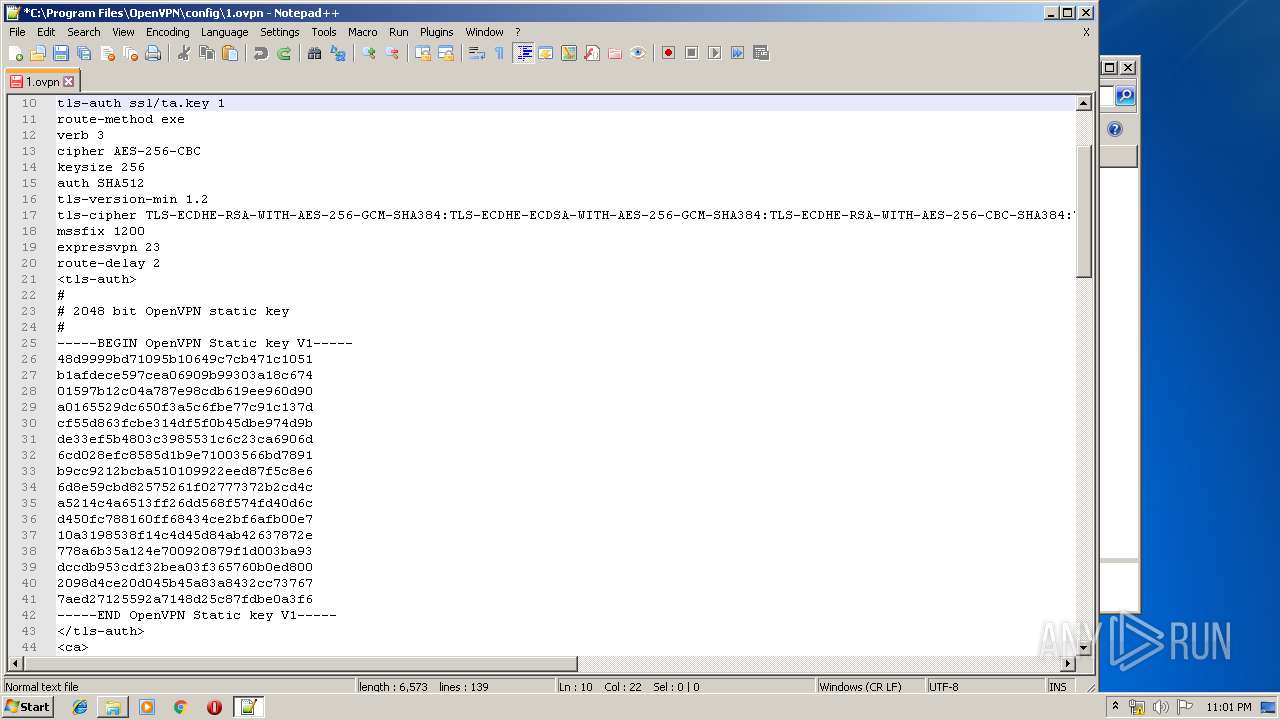
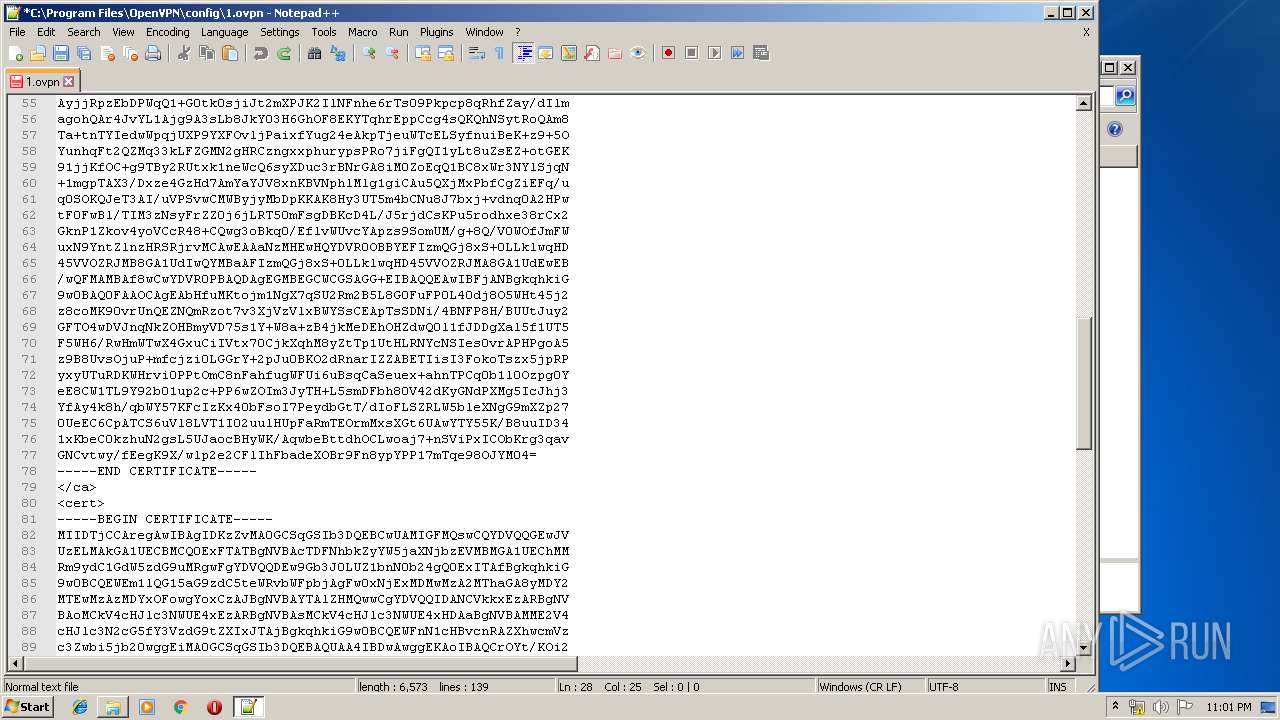
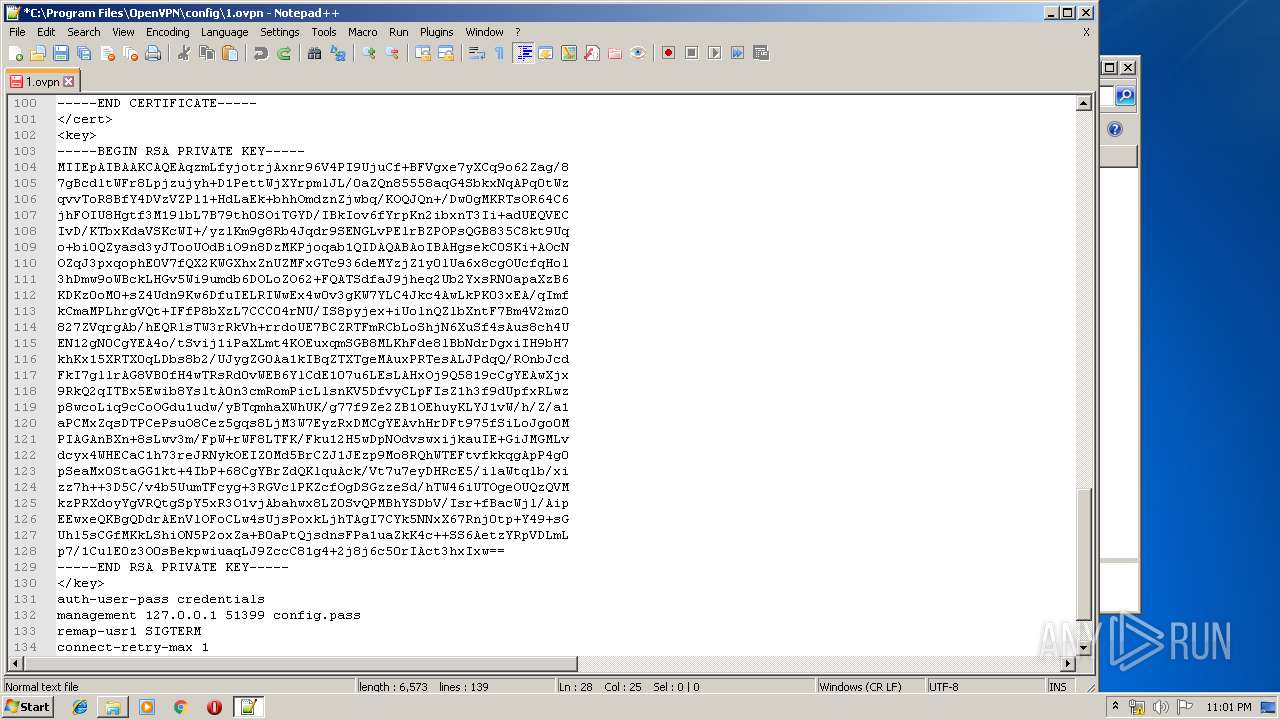
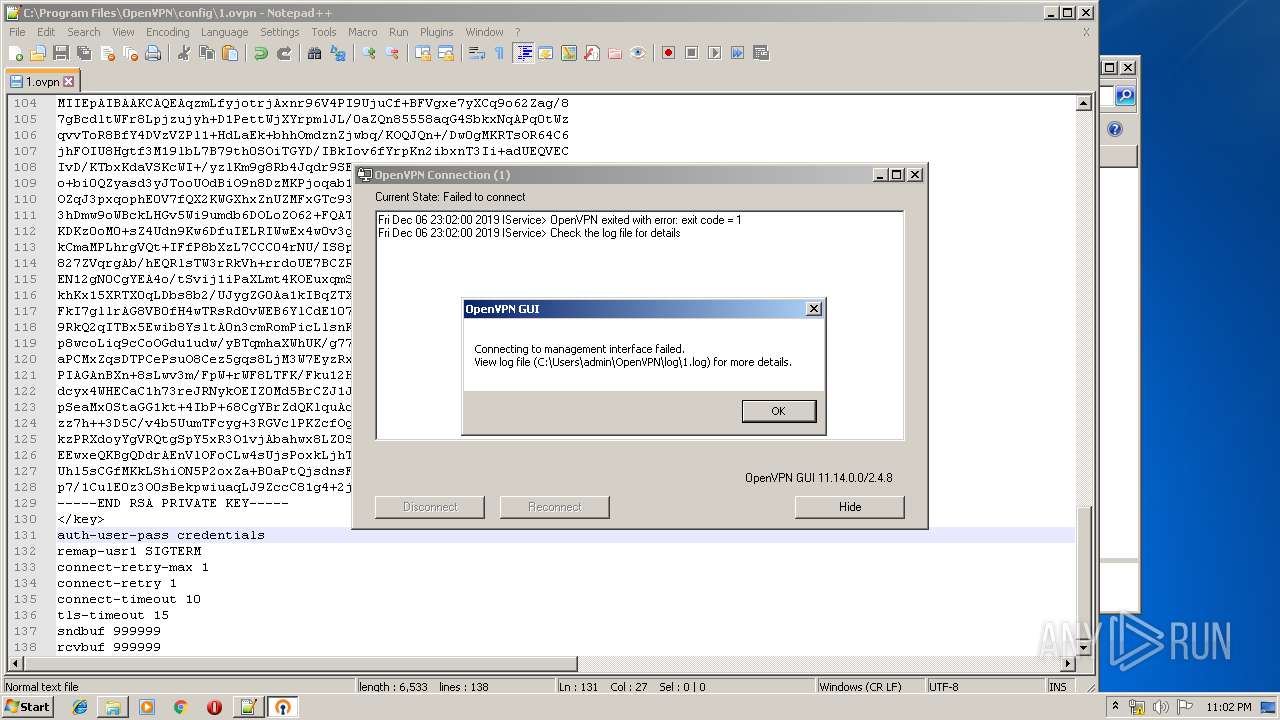
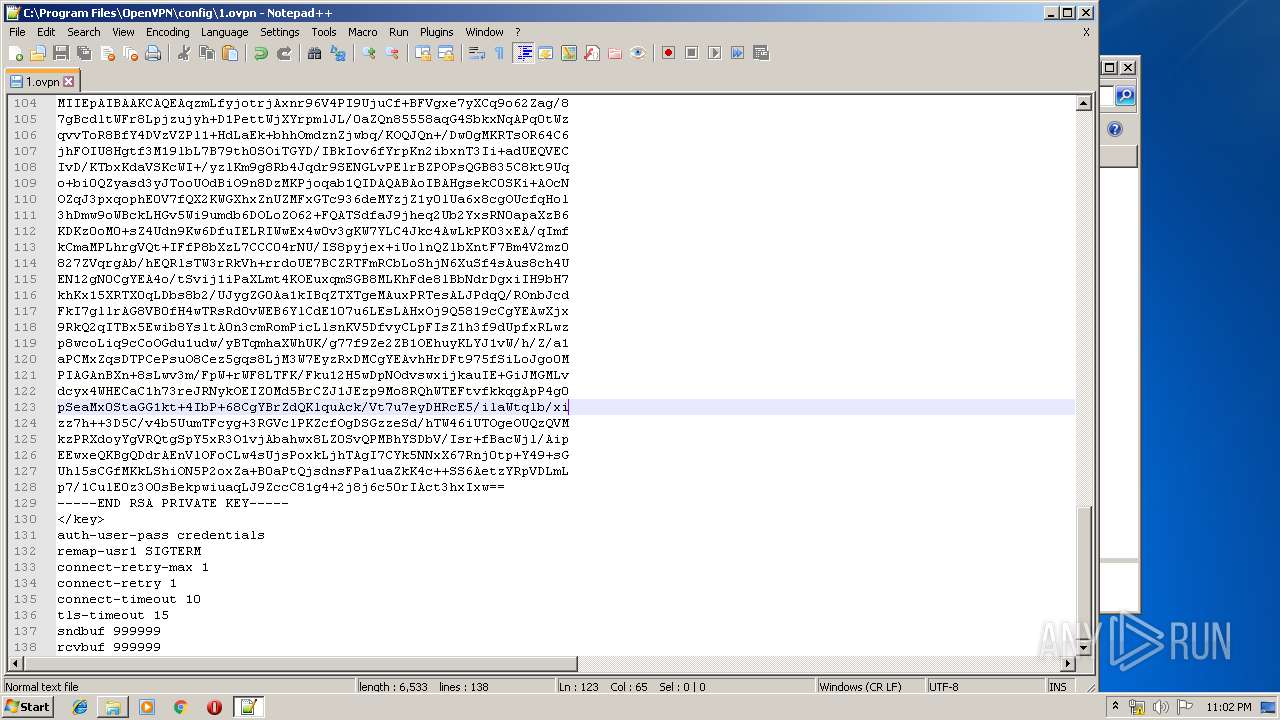
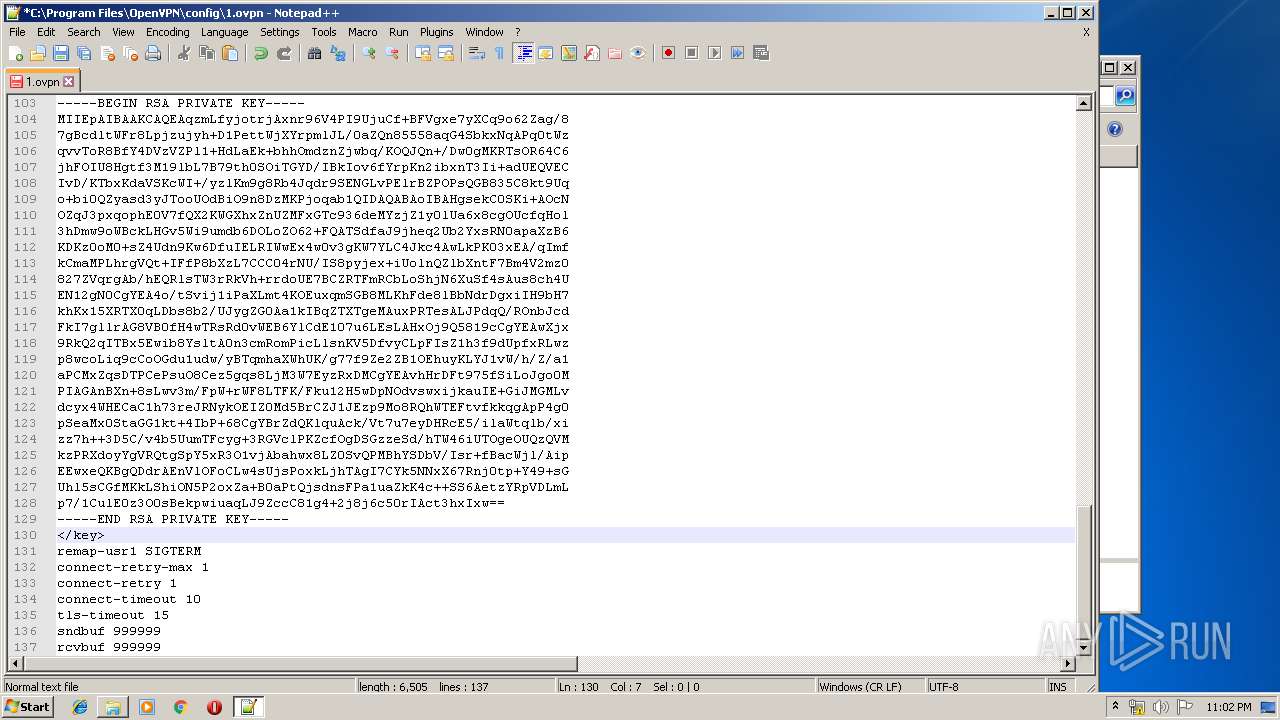
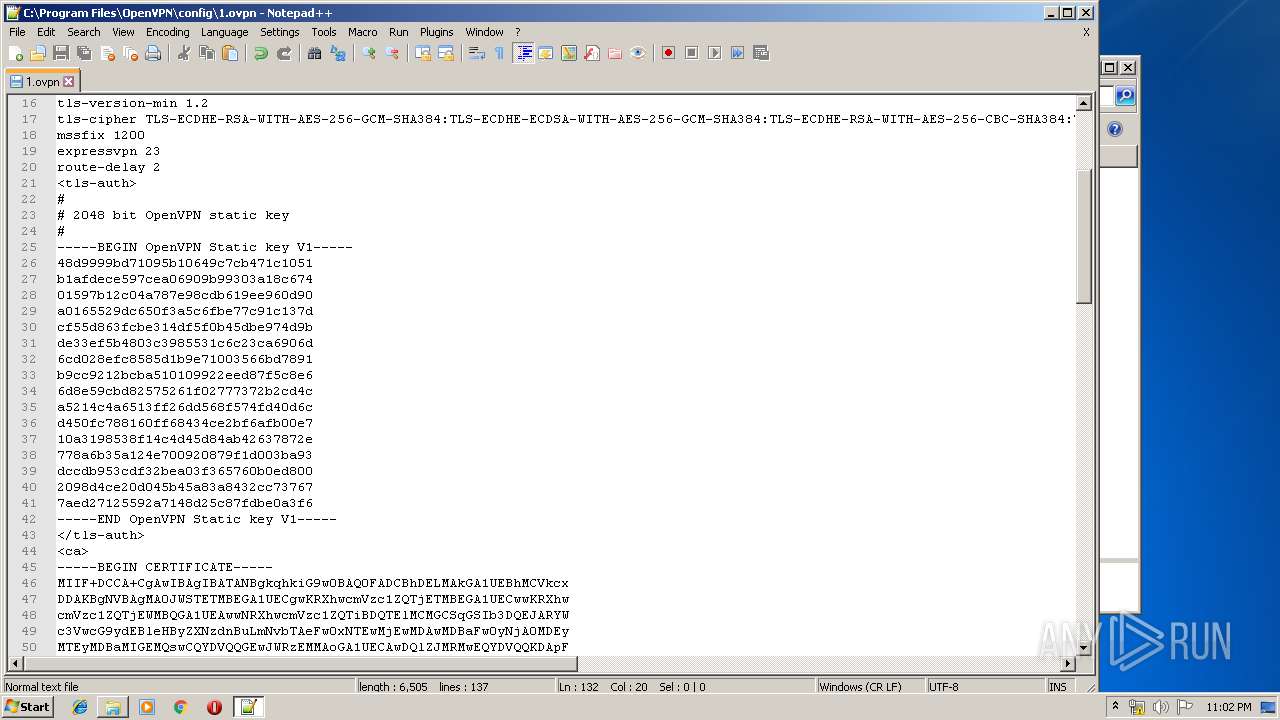
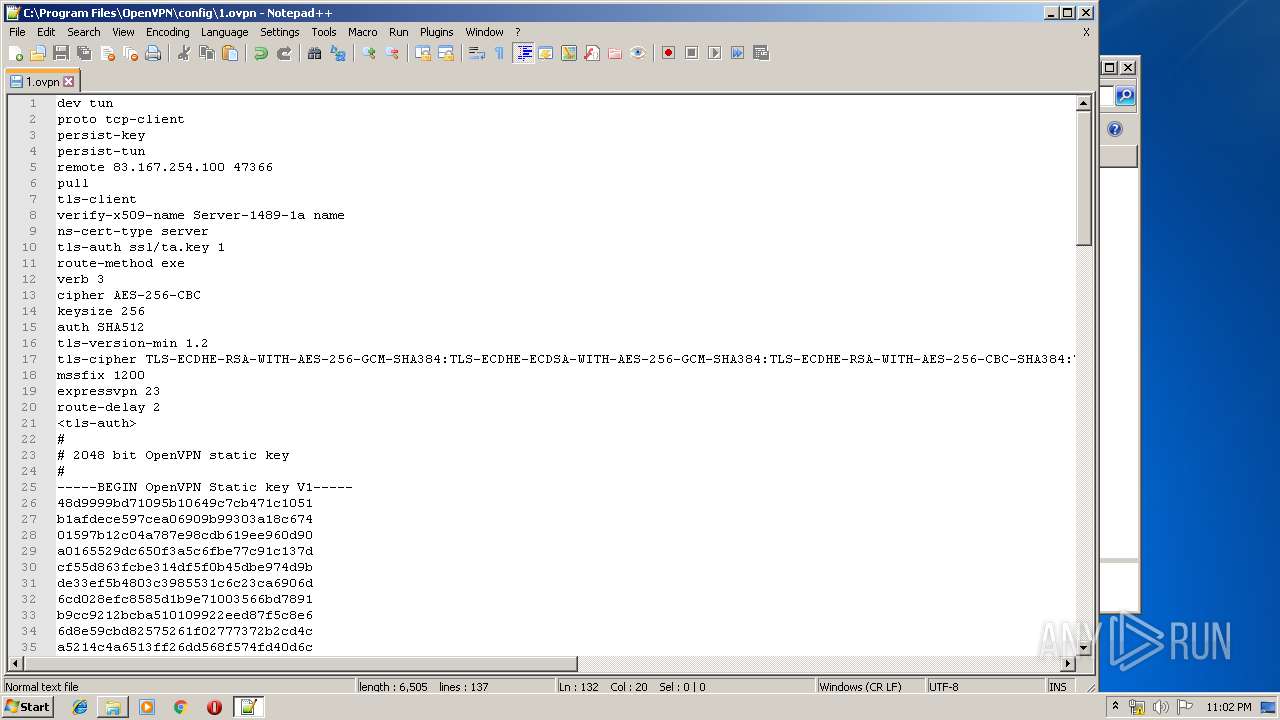
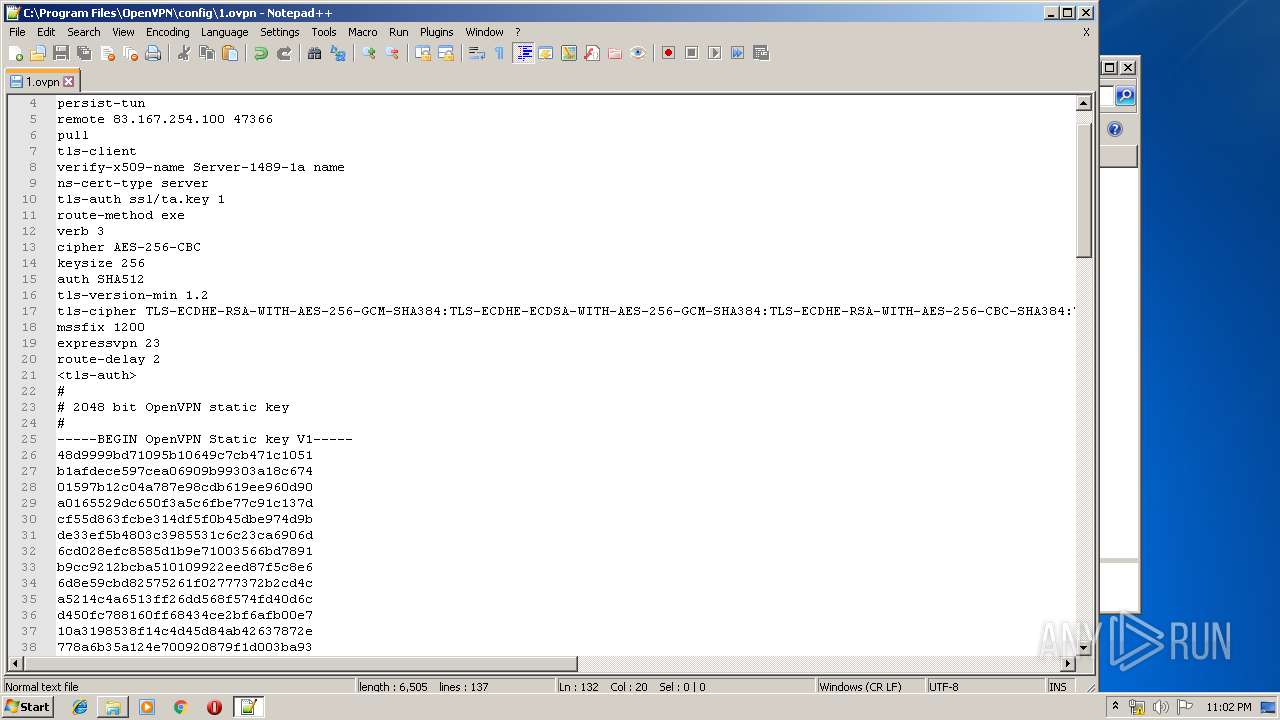
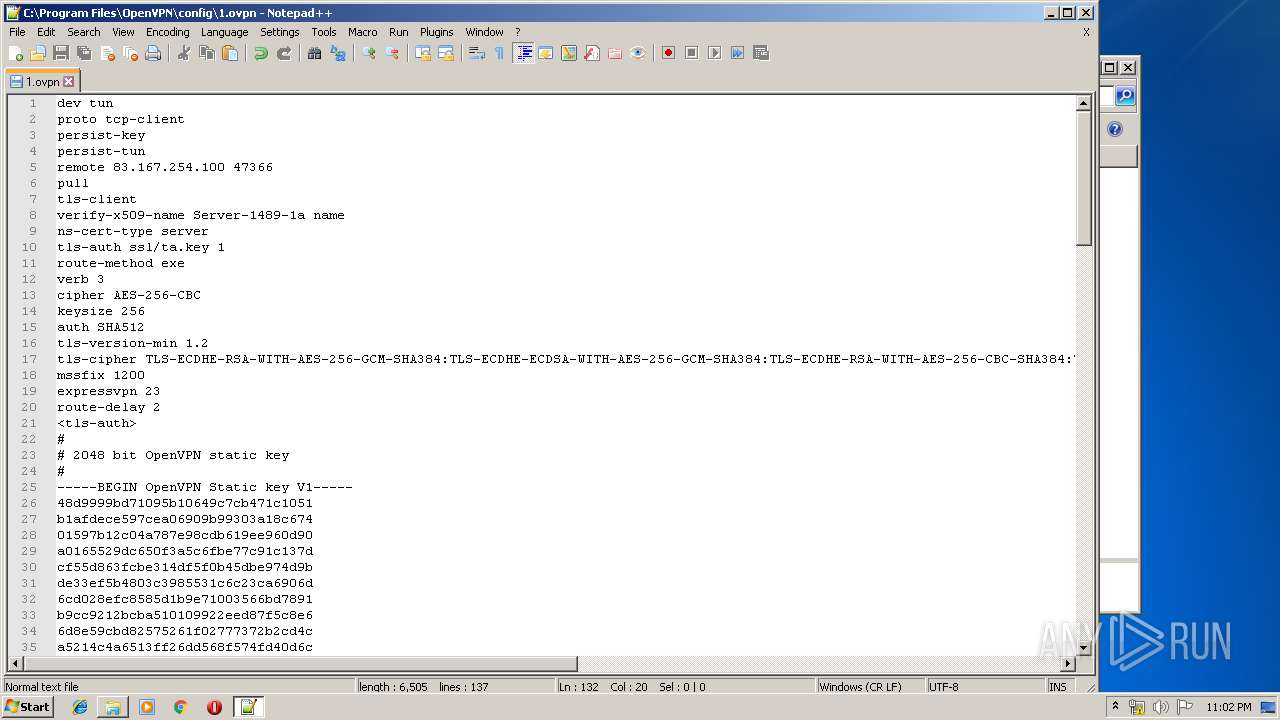
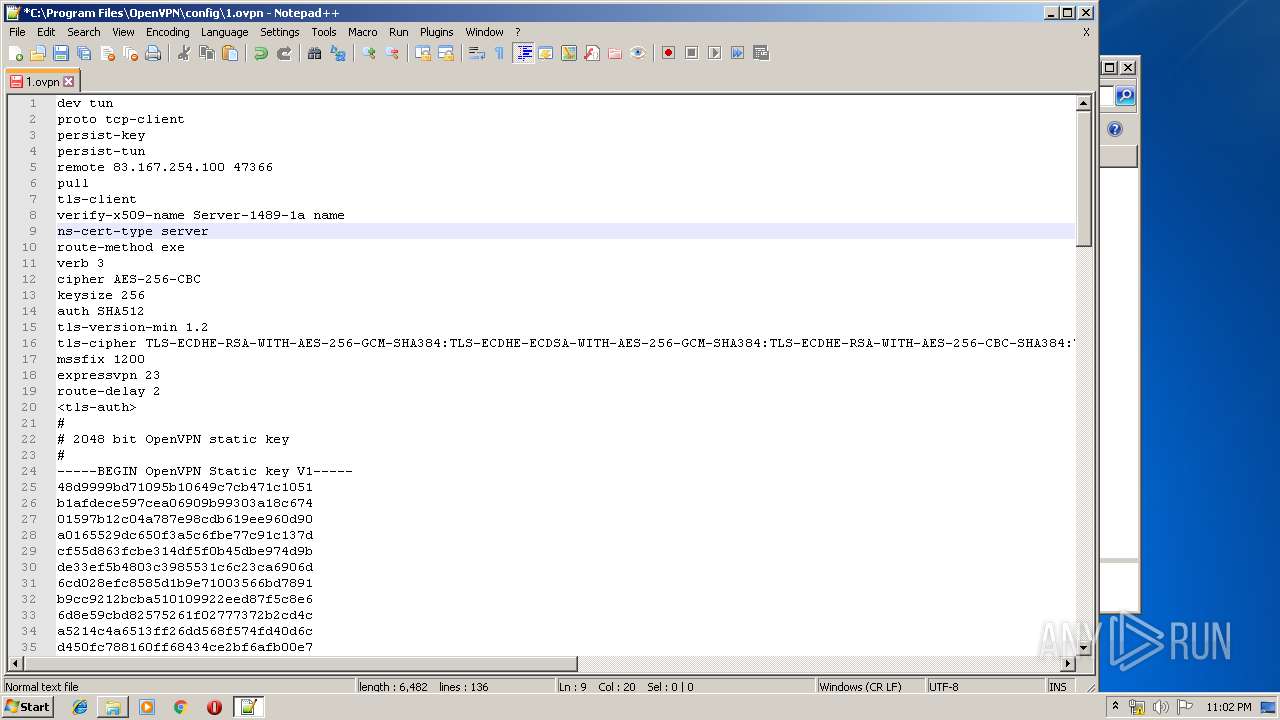
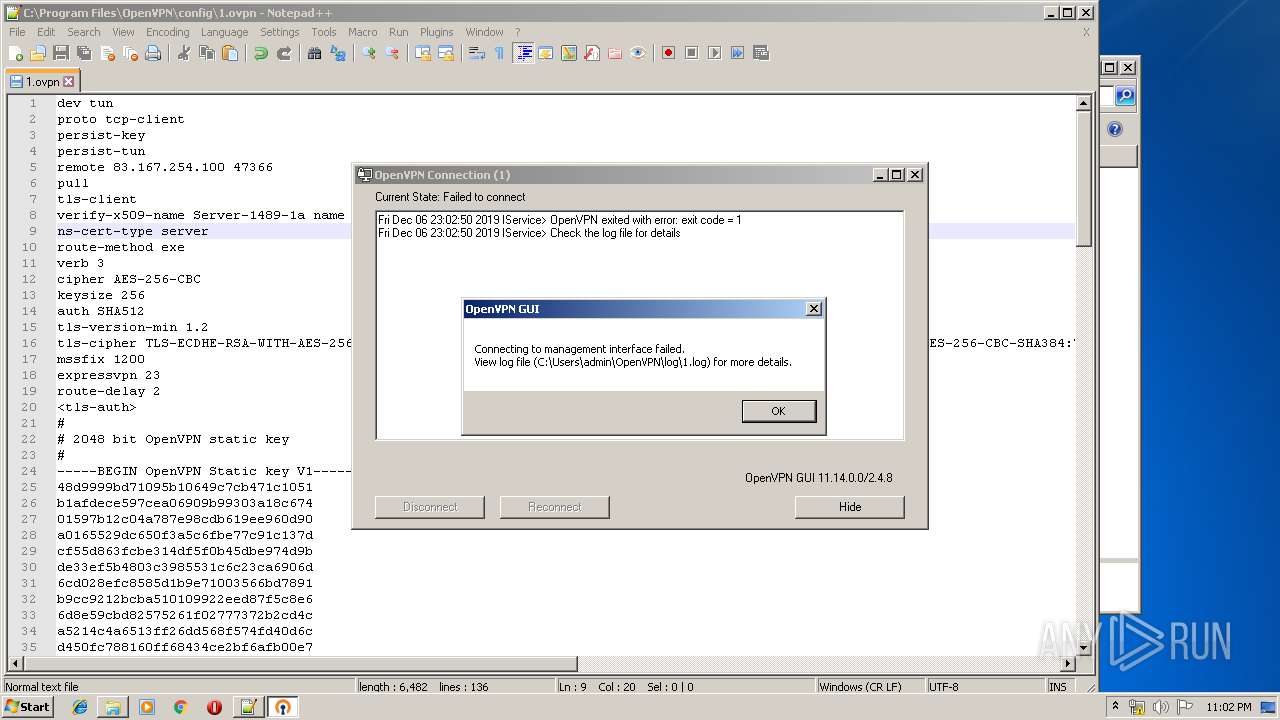
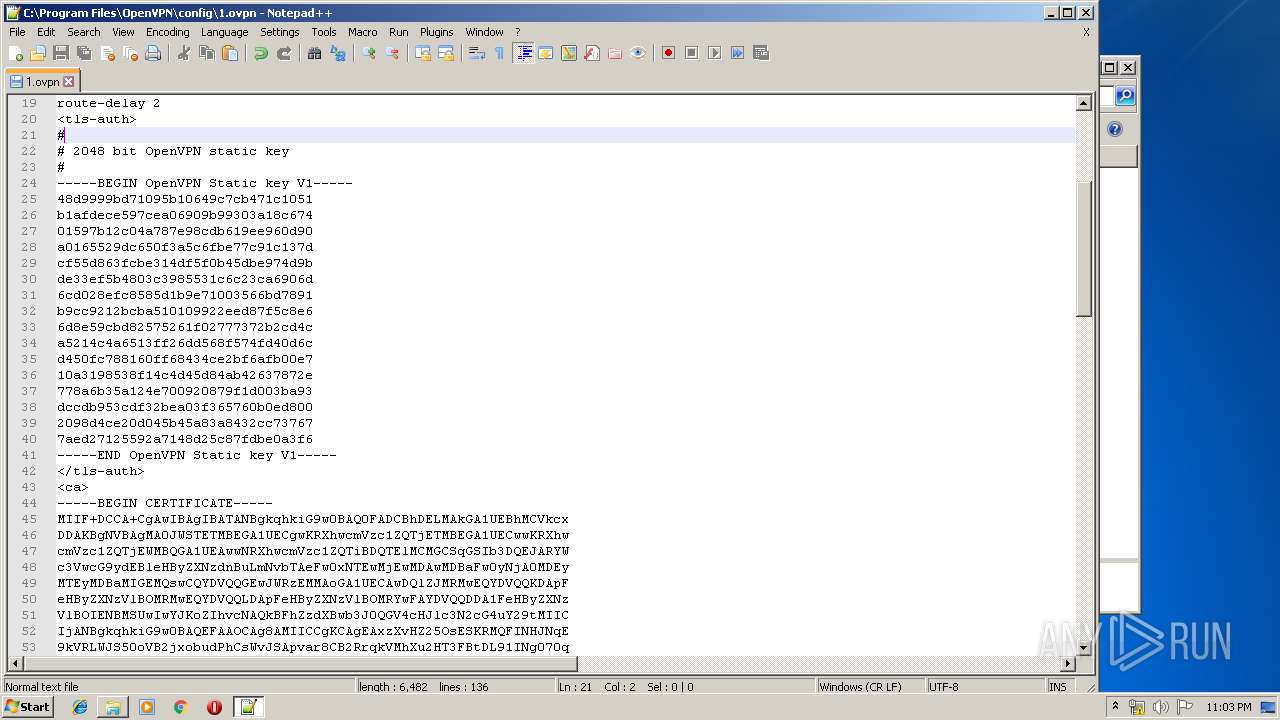
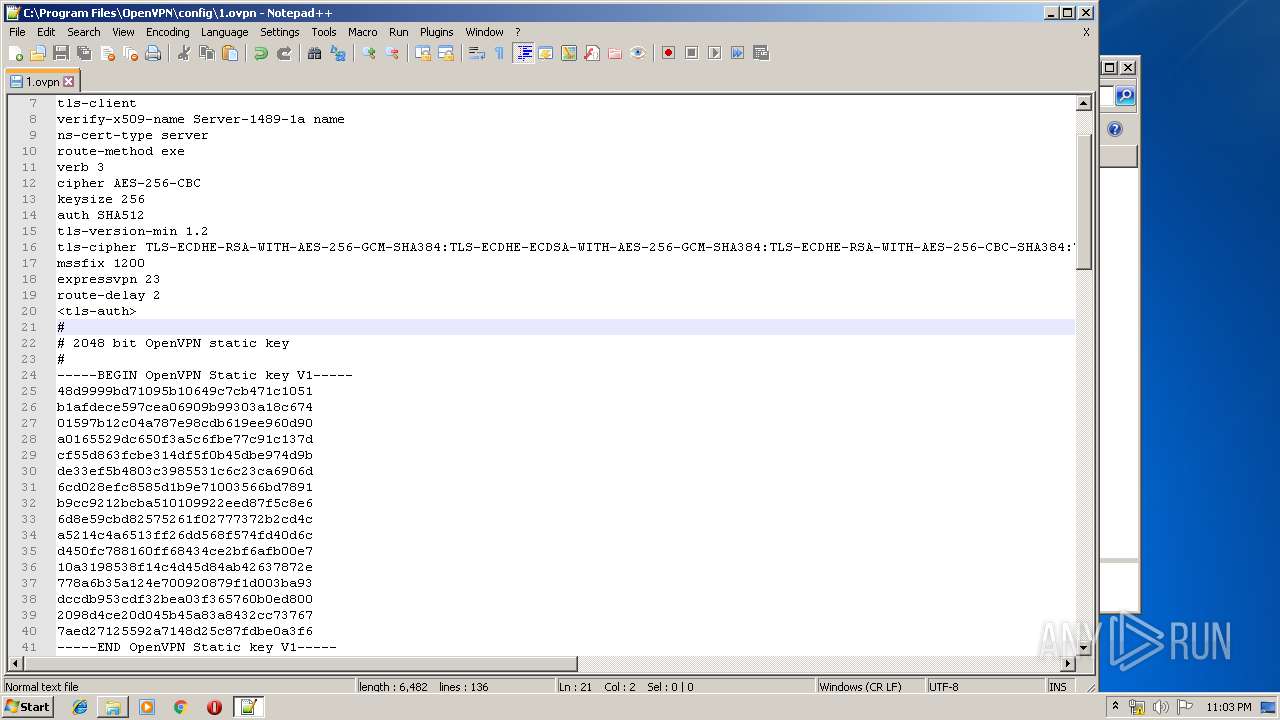
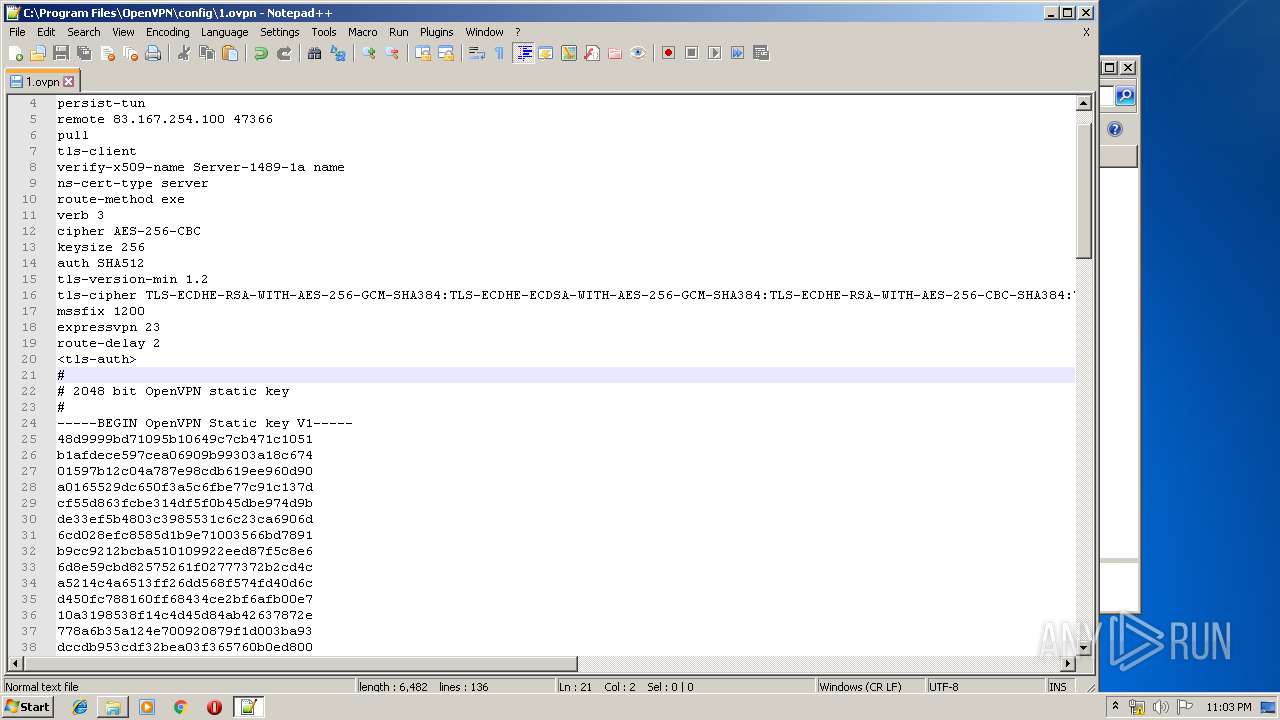
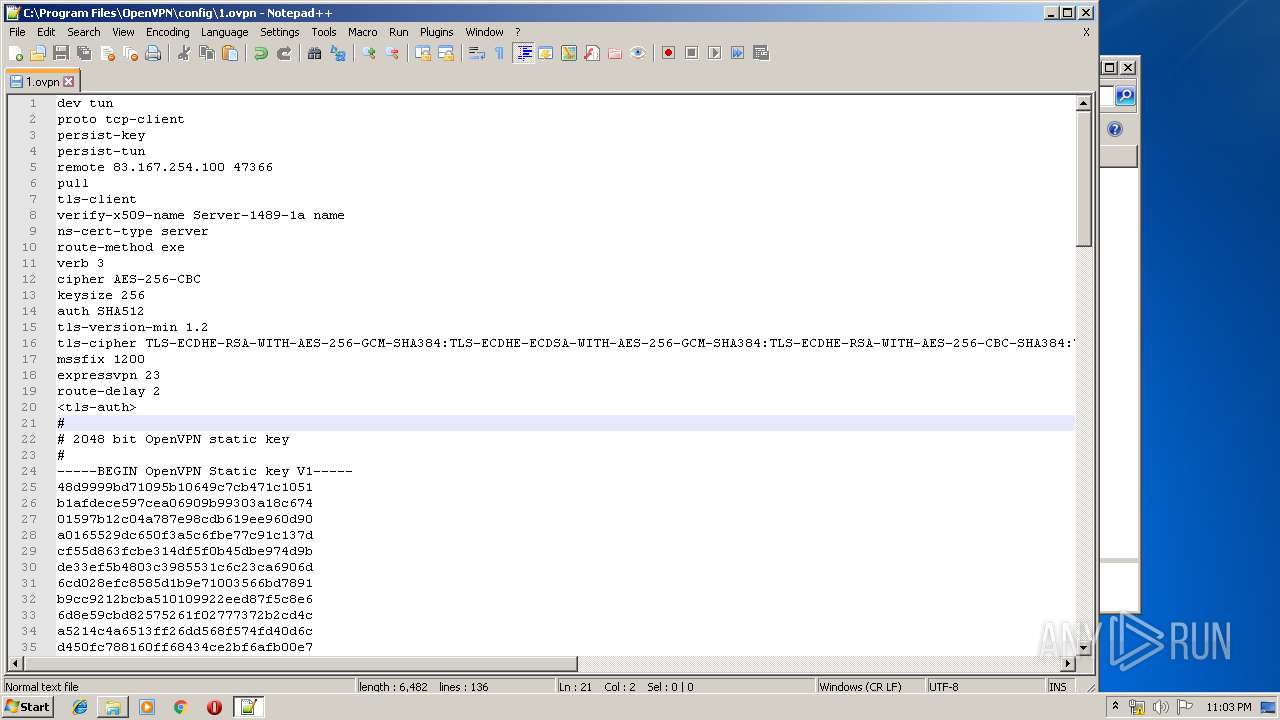
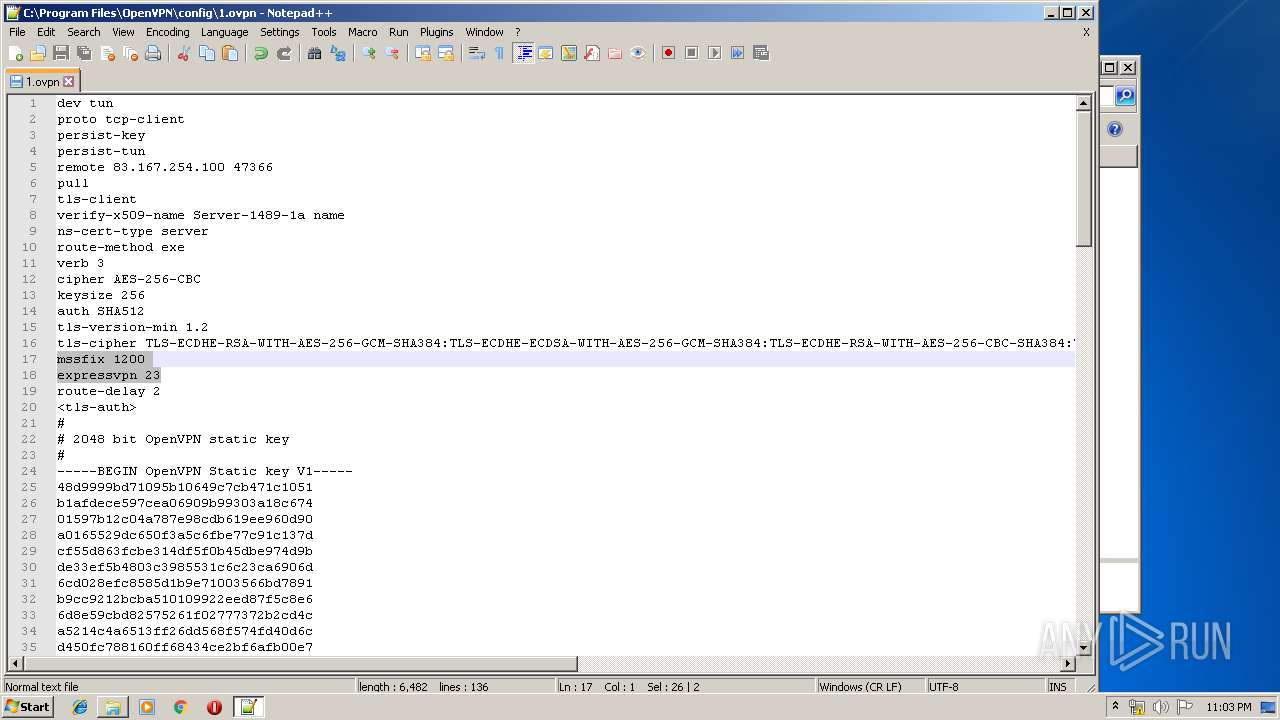
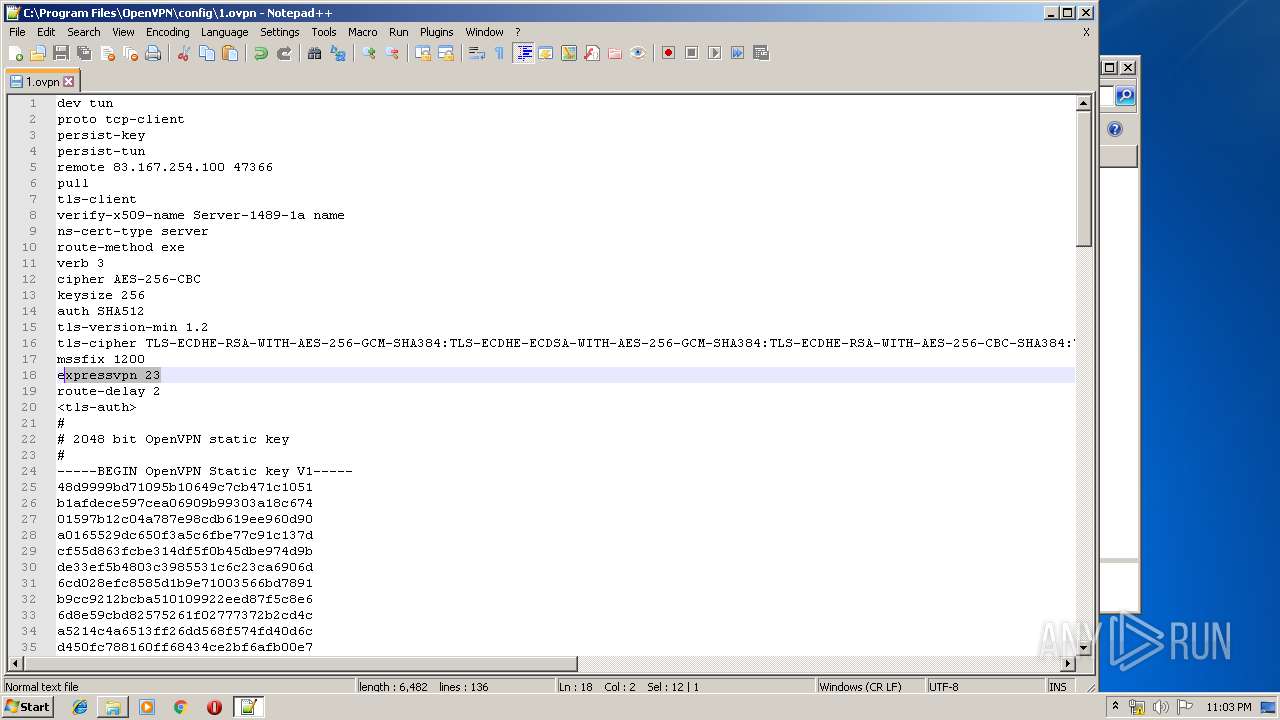
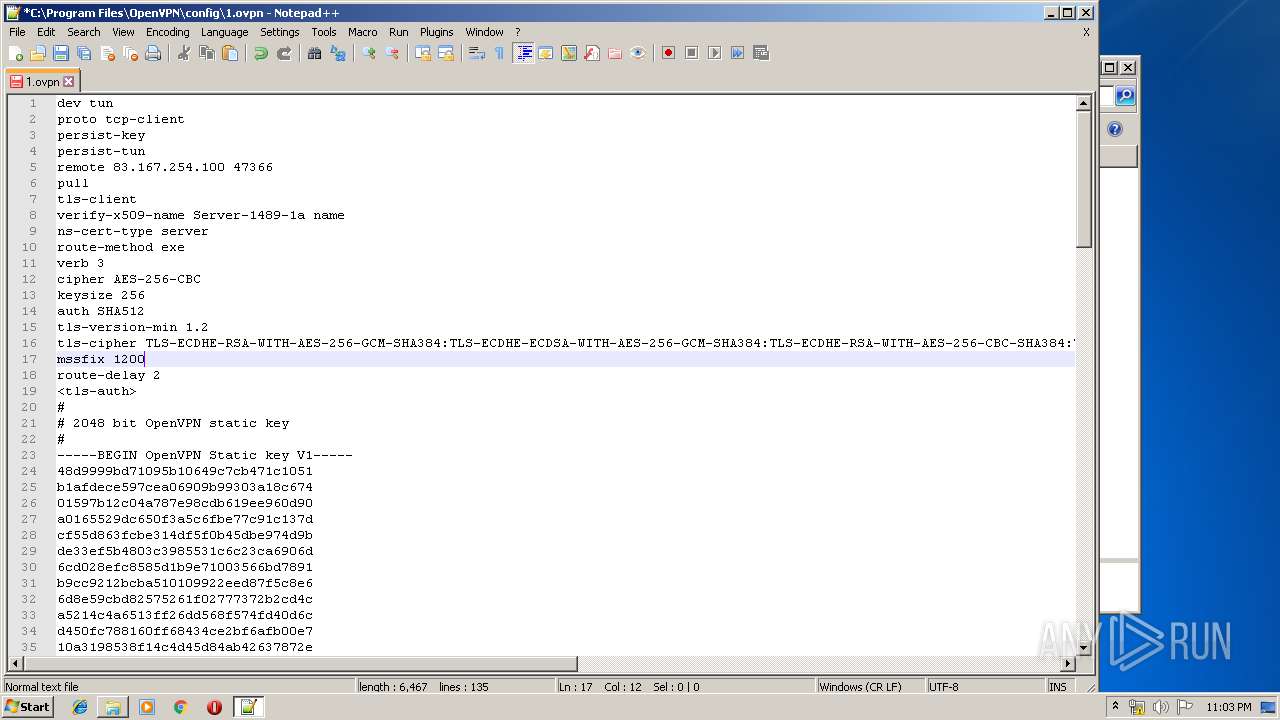
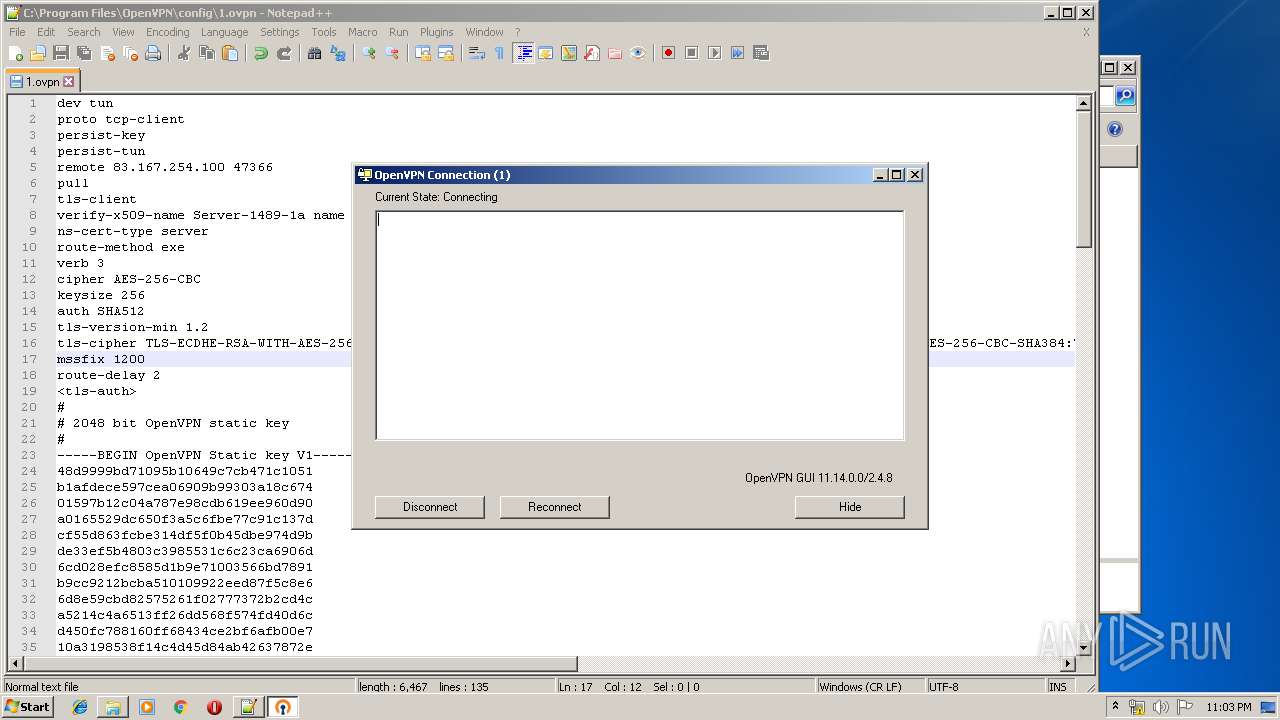
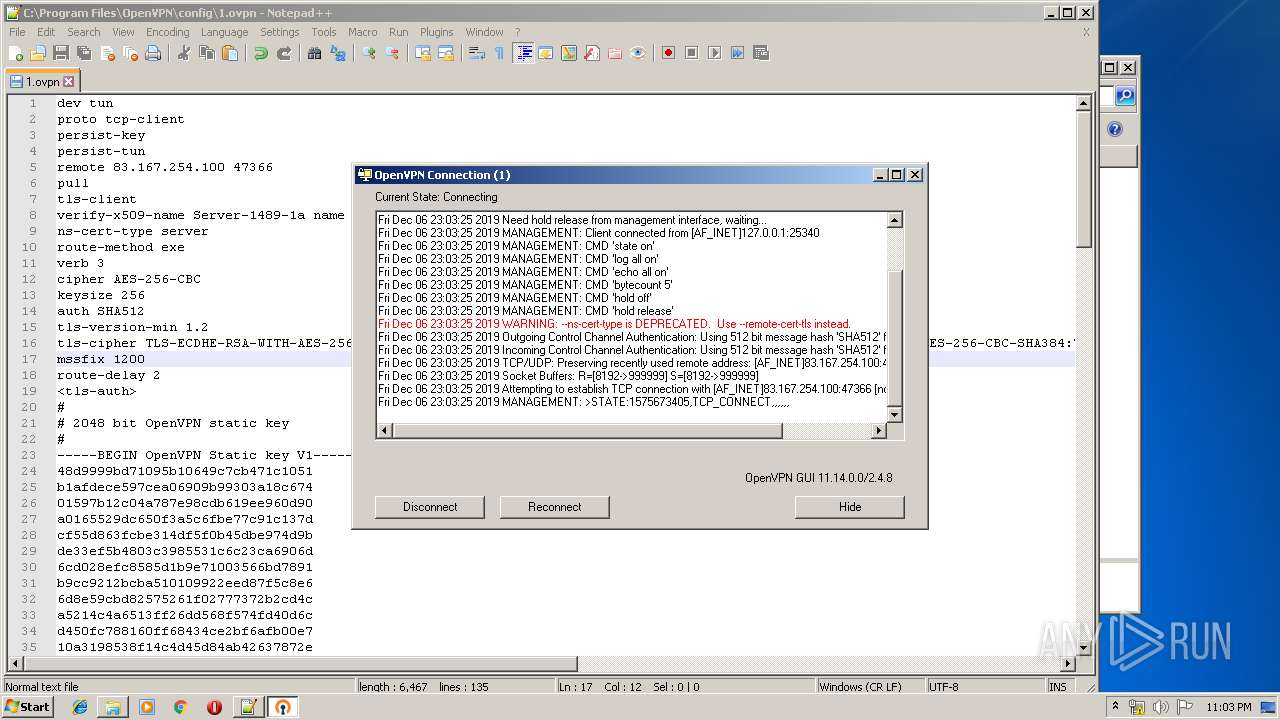
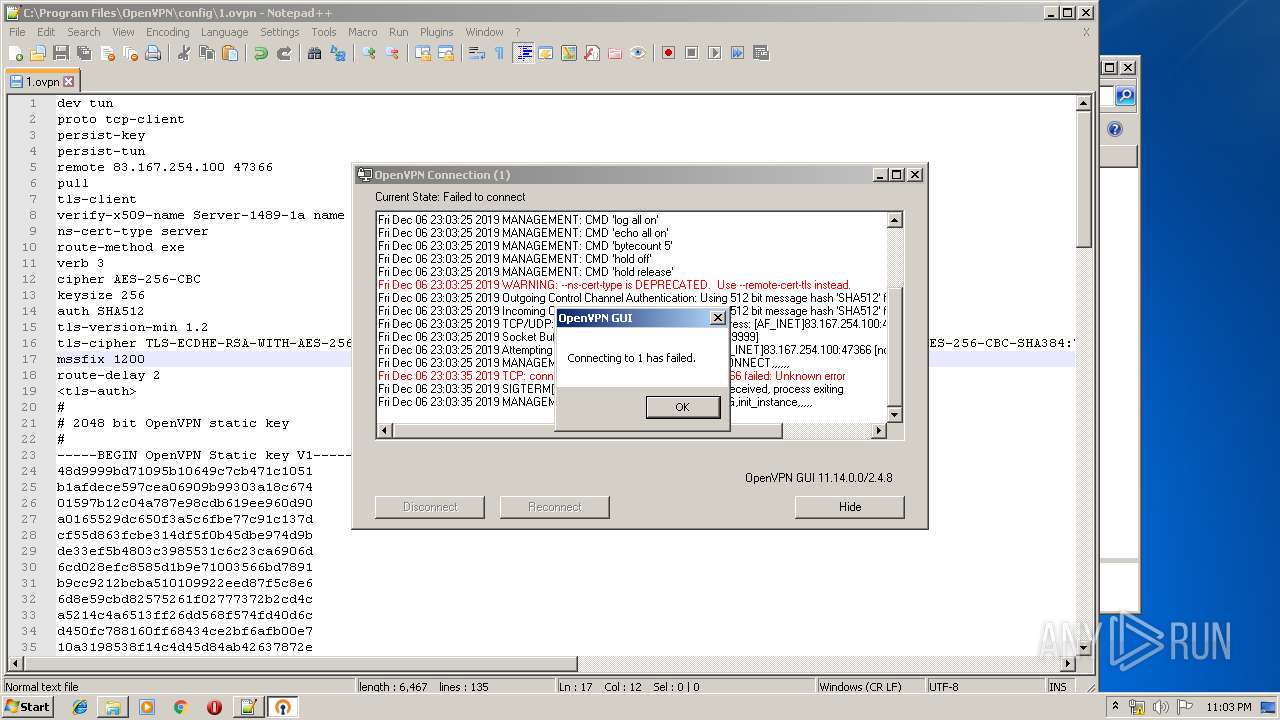
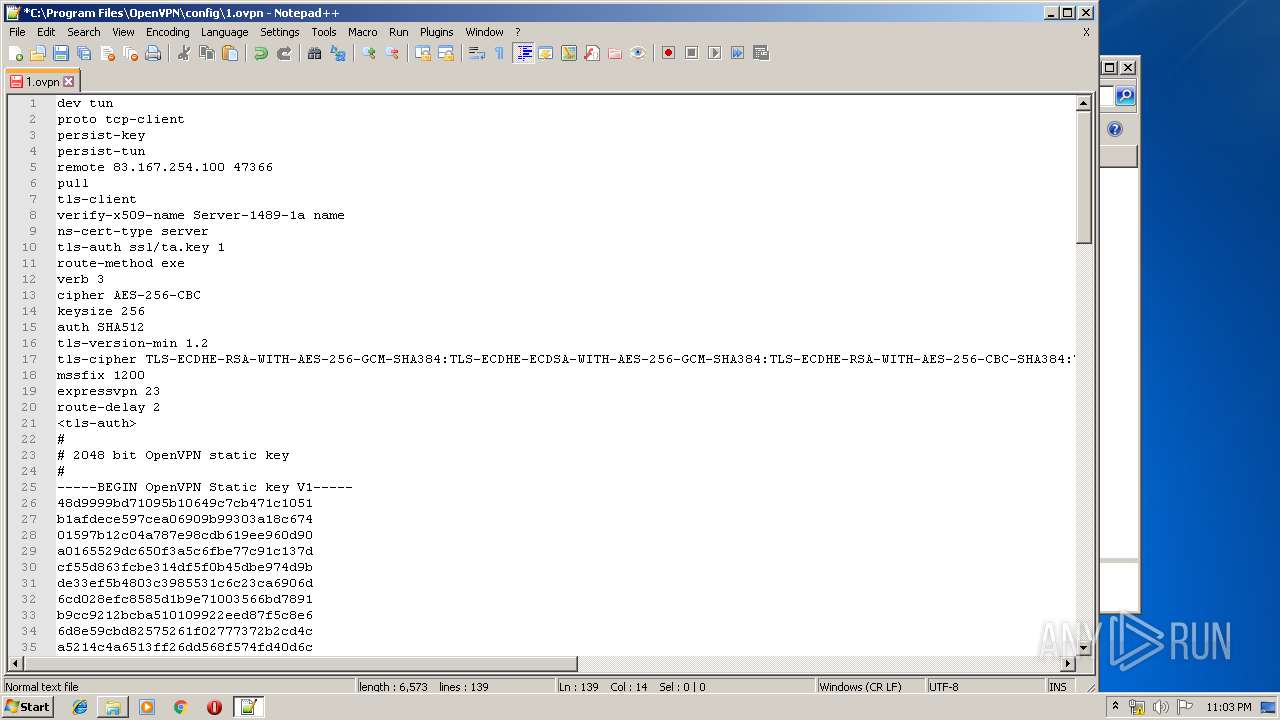
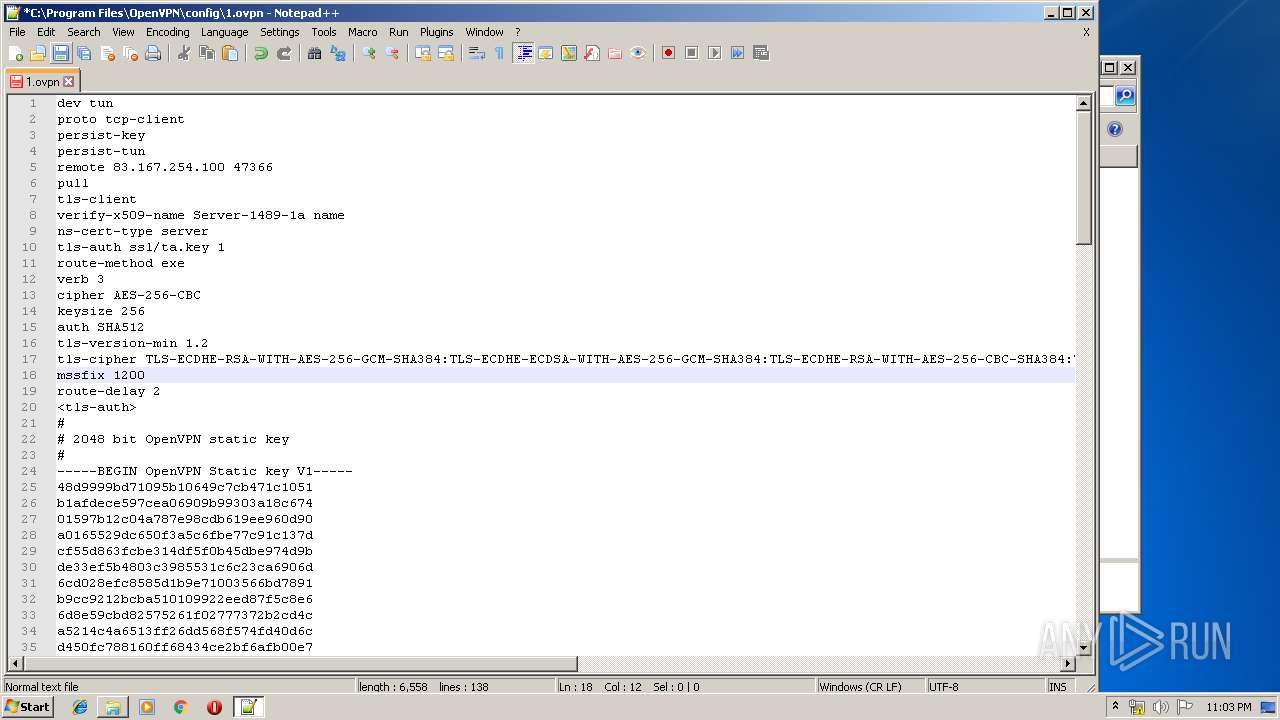
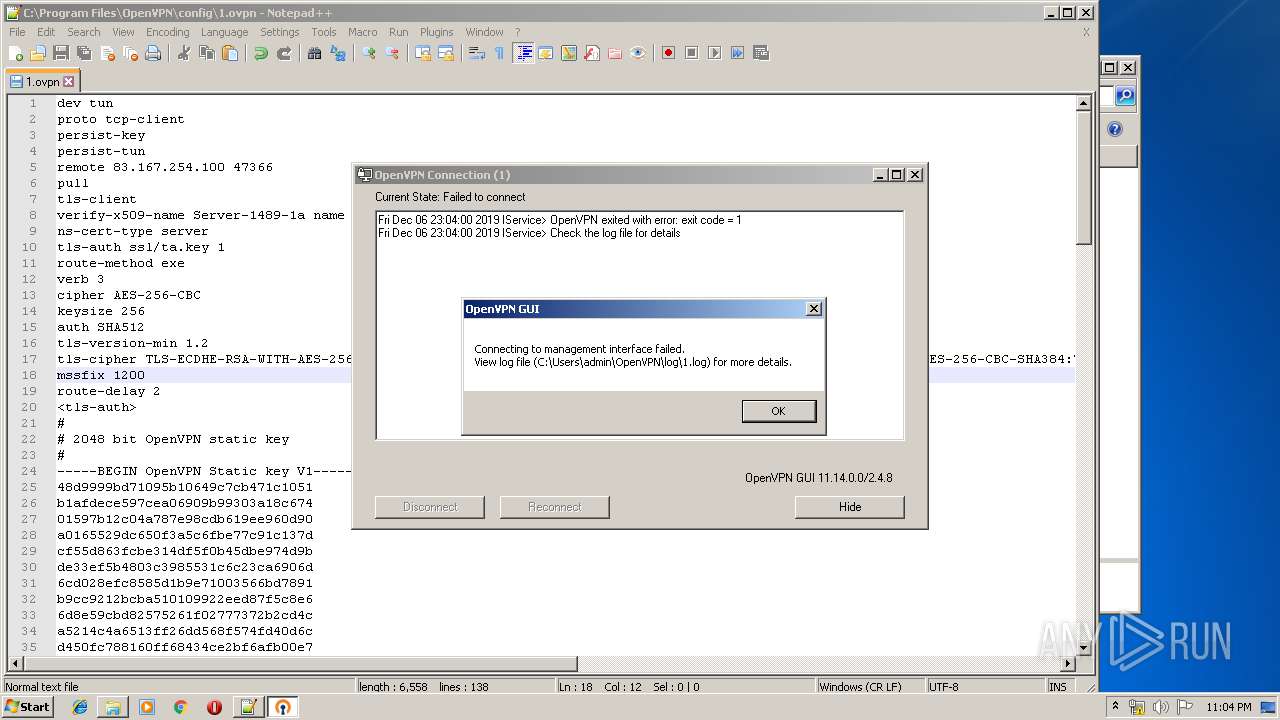
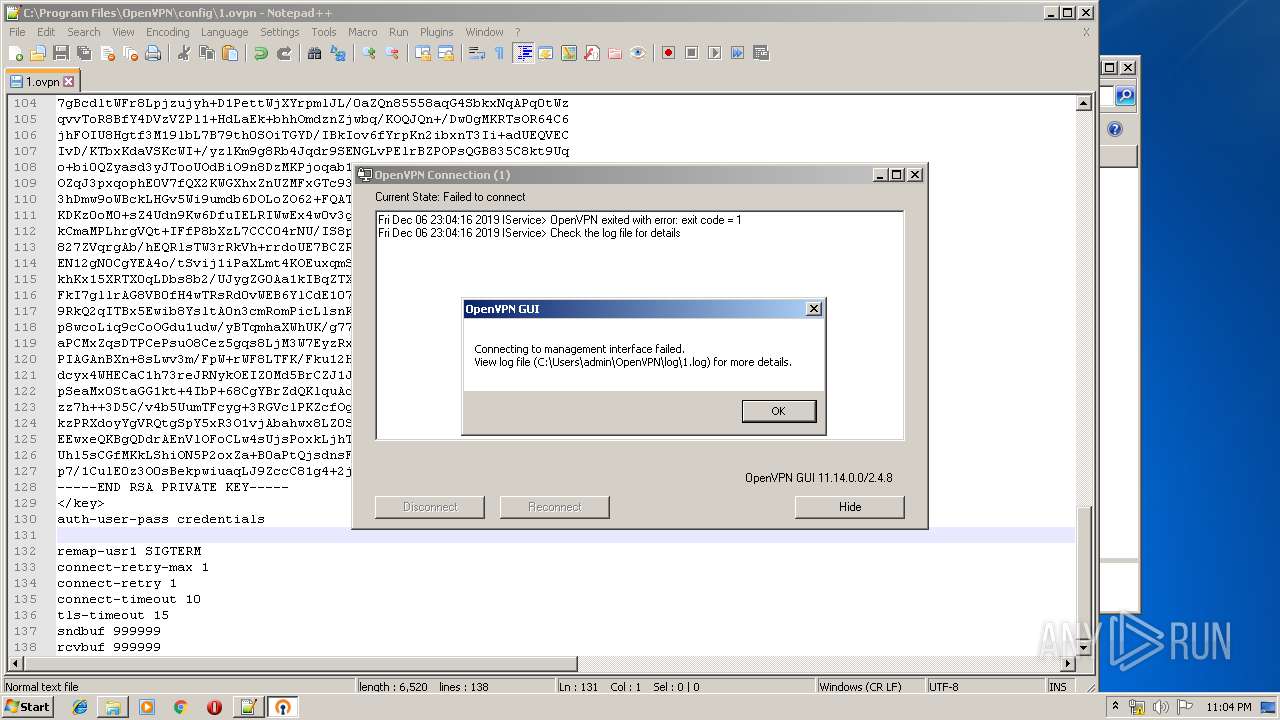
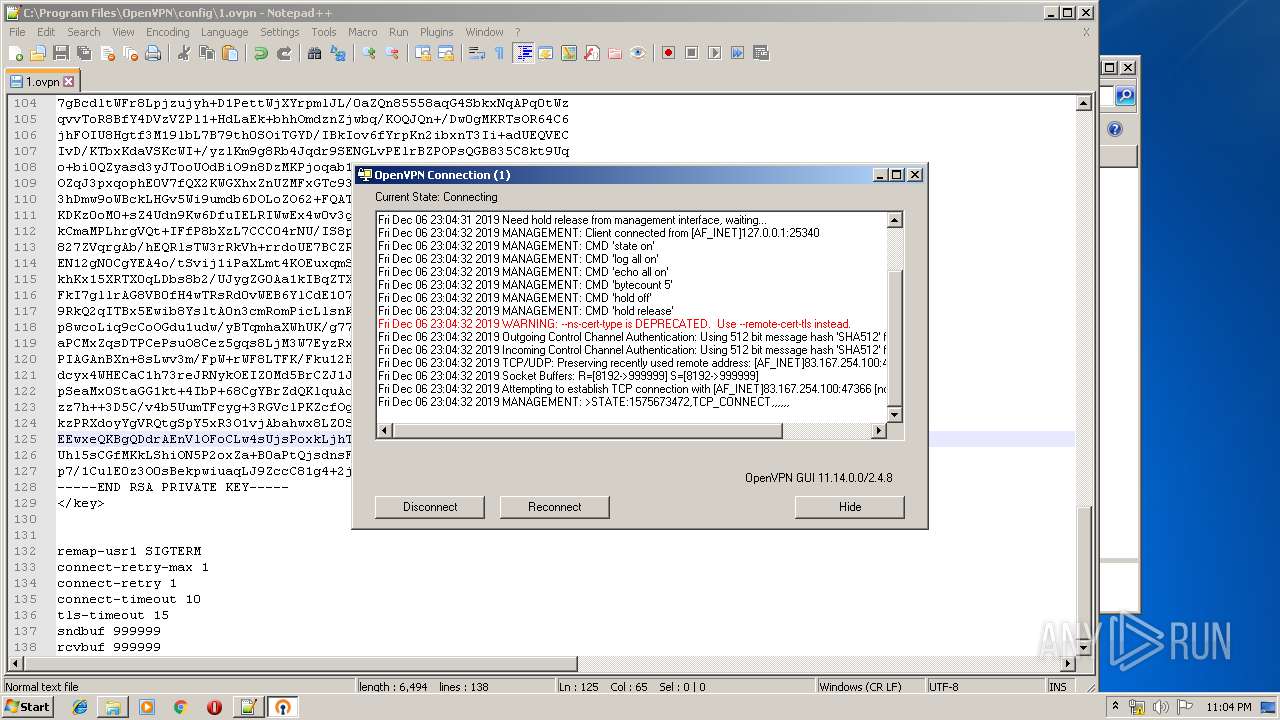
| 1048 | openvpn --log "C:\Users\admin\OpenVPN\log\1.log" --config "1.ovpn" --setenv IV_GUI_VER "OpenVPN GUI 11" --service f0000000204 0 --auth-retry interact --management 127.0.0.1 25340 stdin --management-query-passwords --management-hold --pull-filter ignore route-method --msg-channel 364 | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpnserv.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
| 1072 | openvpn --log "C:\Users\admin\OpenVPN\log\1.log" --config "1.ovpn" --setenv IV_GUI_VER "OpenVPN GUI 11" --service f0000000c6c 0 --auth-retry interact --management 127.0.0.1 25340 stdin --management-query-passwords --management-hold --pull-filter ignore route-method --msg-channel 372 | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpnserv.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
| 1268 | openvpn --version | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpn-gui.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
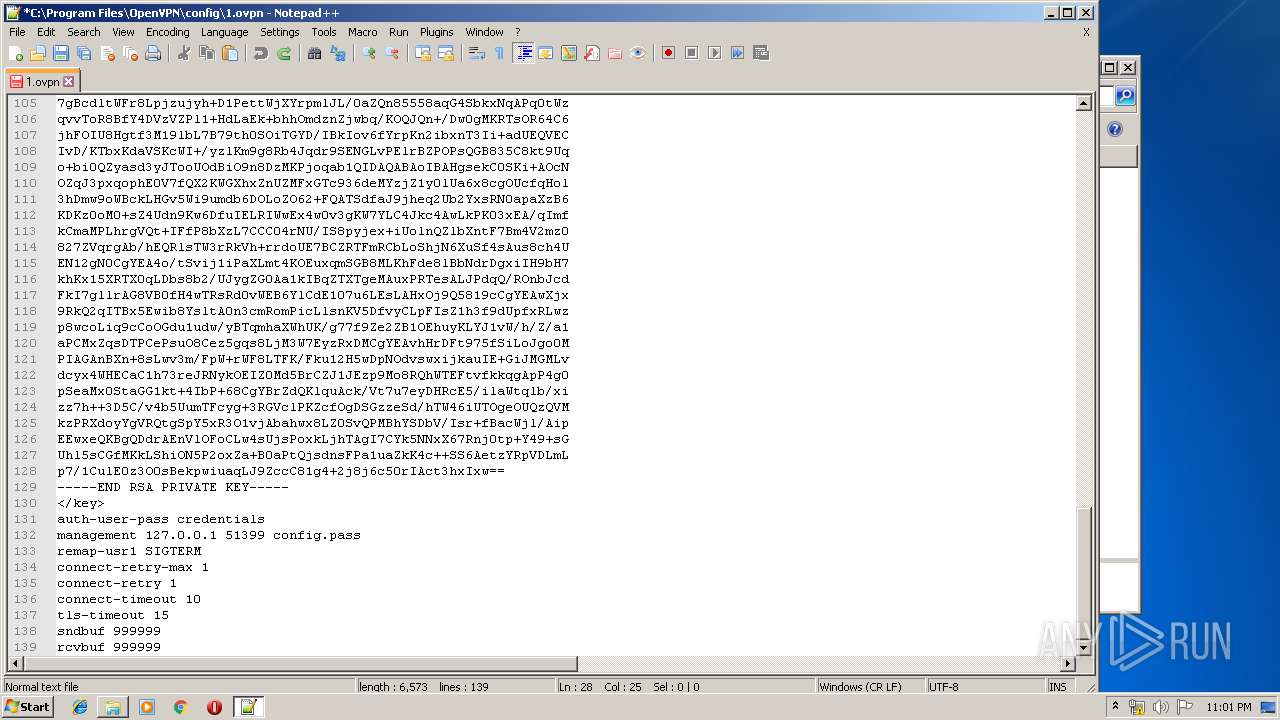
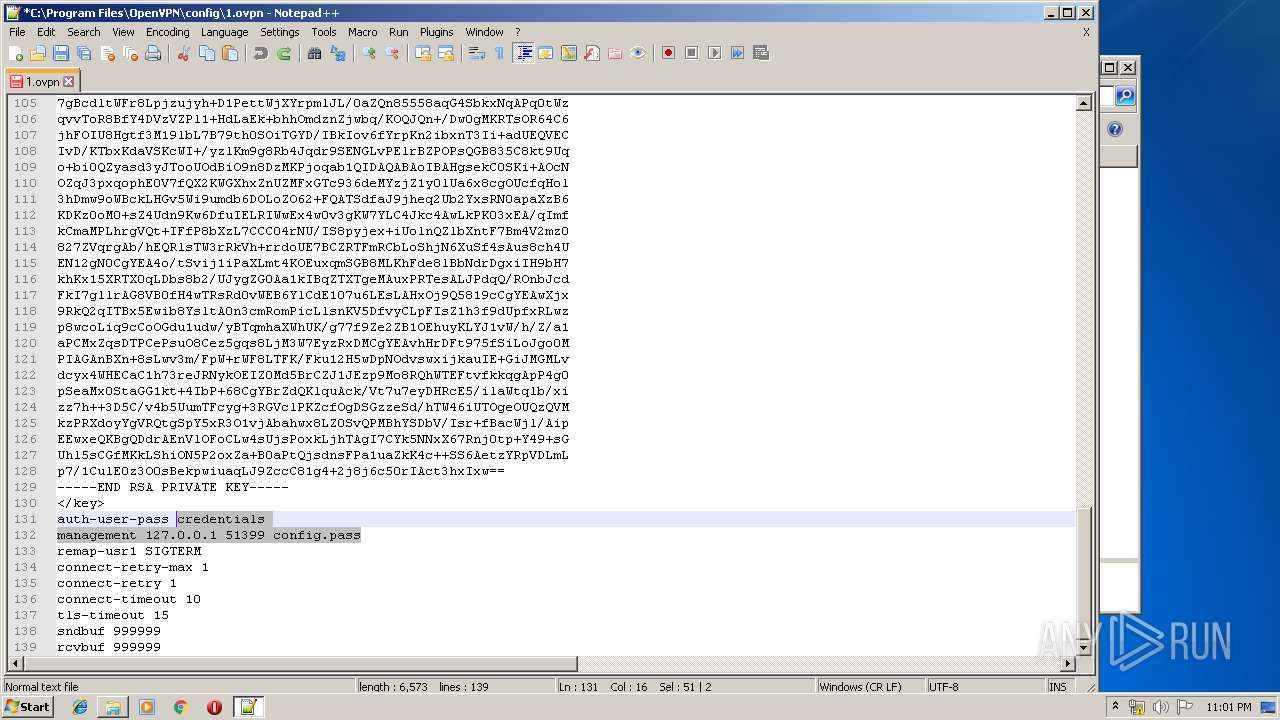
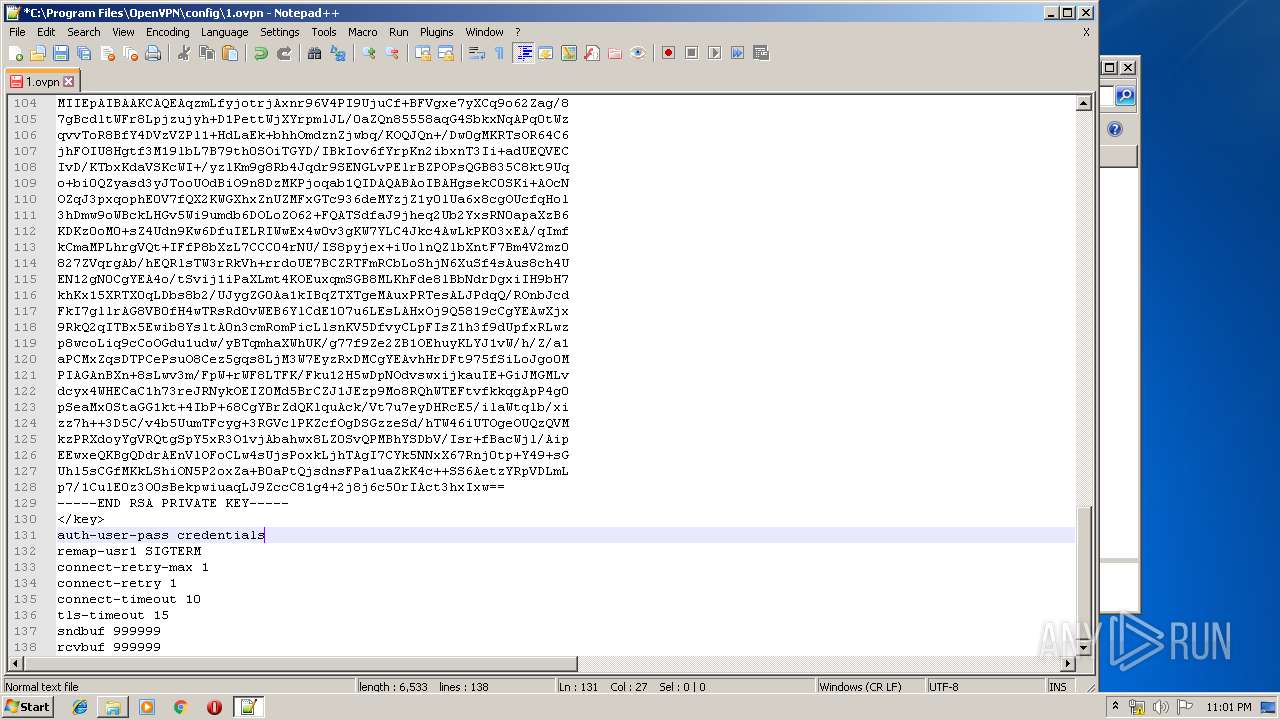
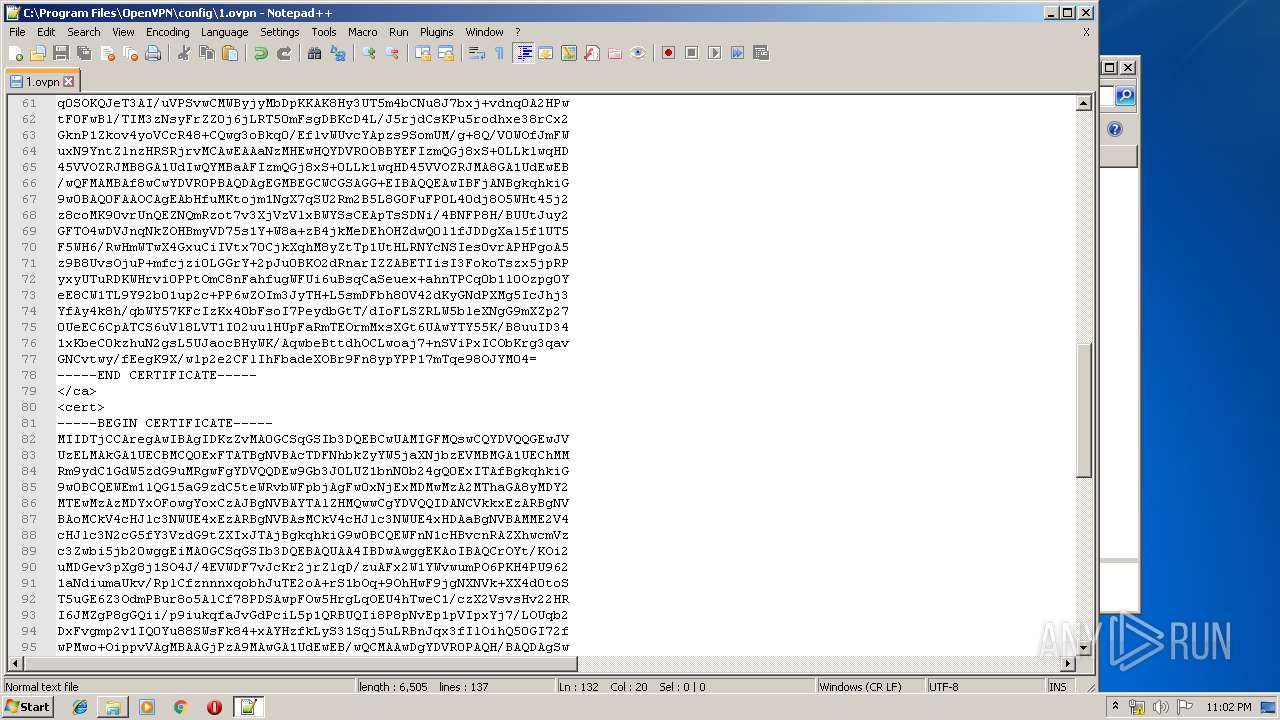
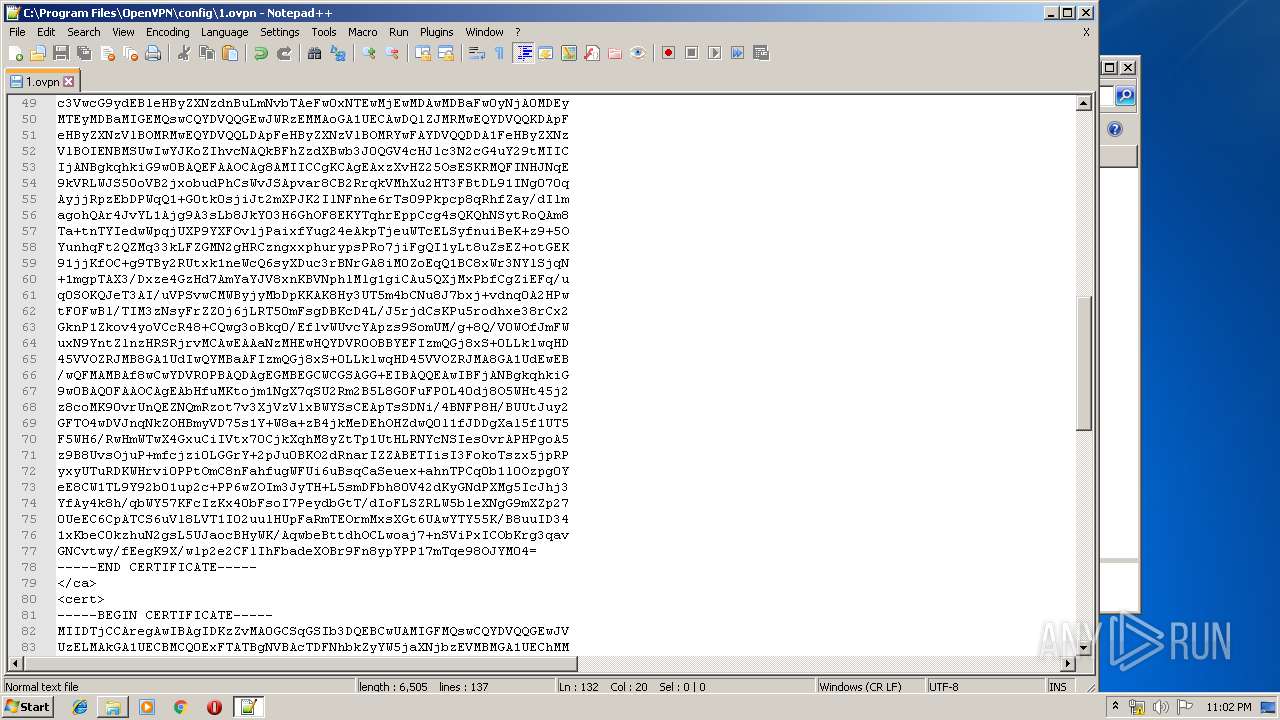
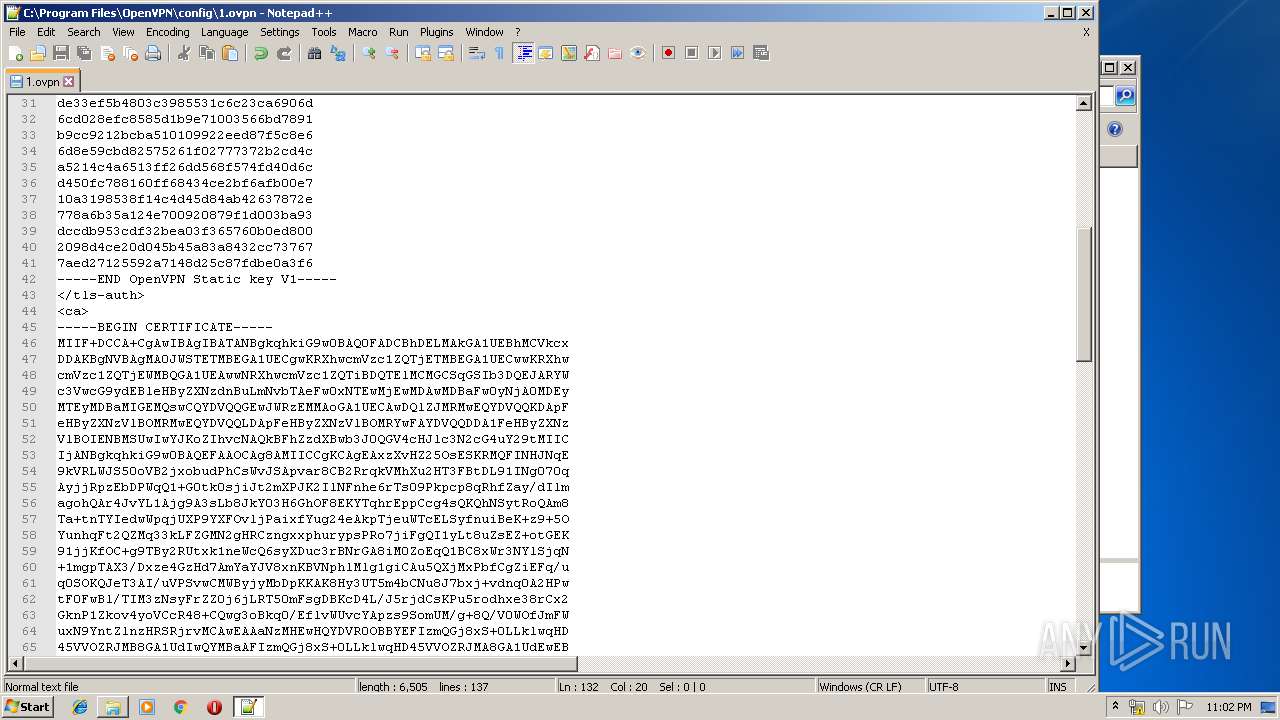
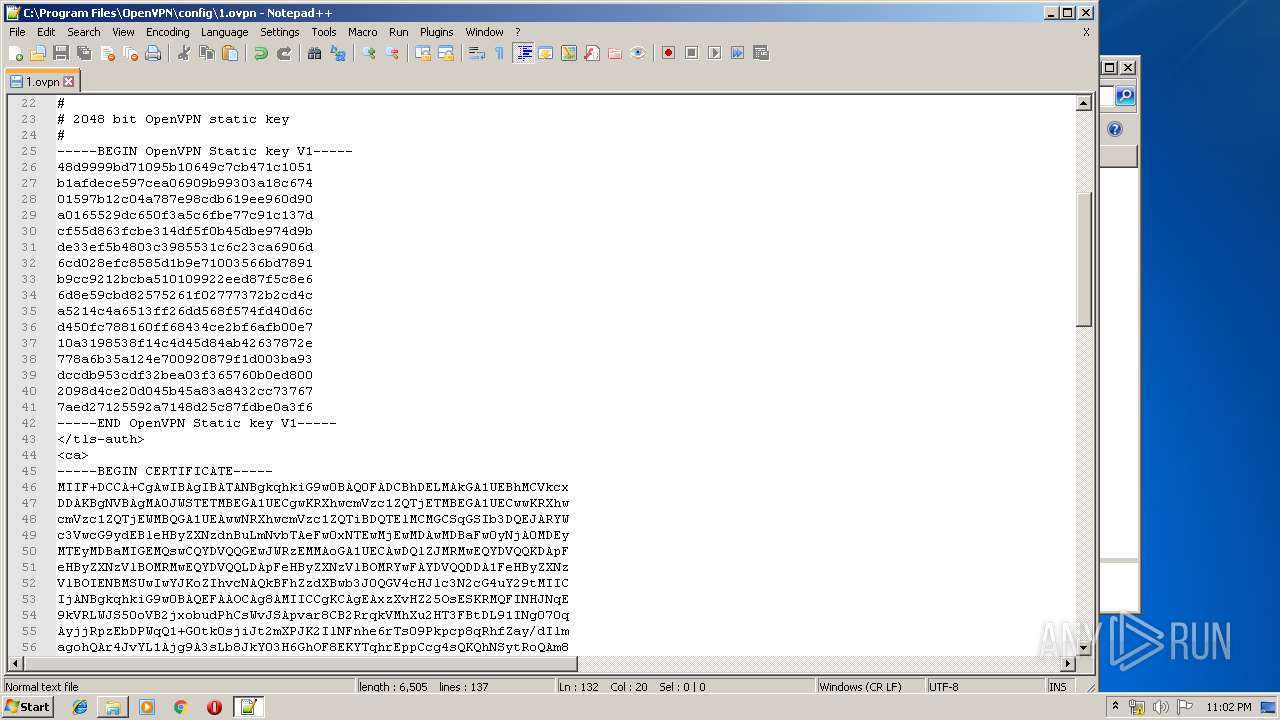
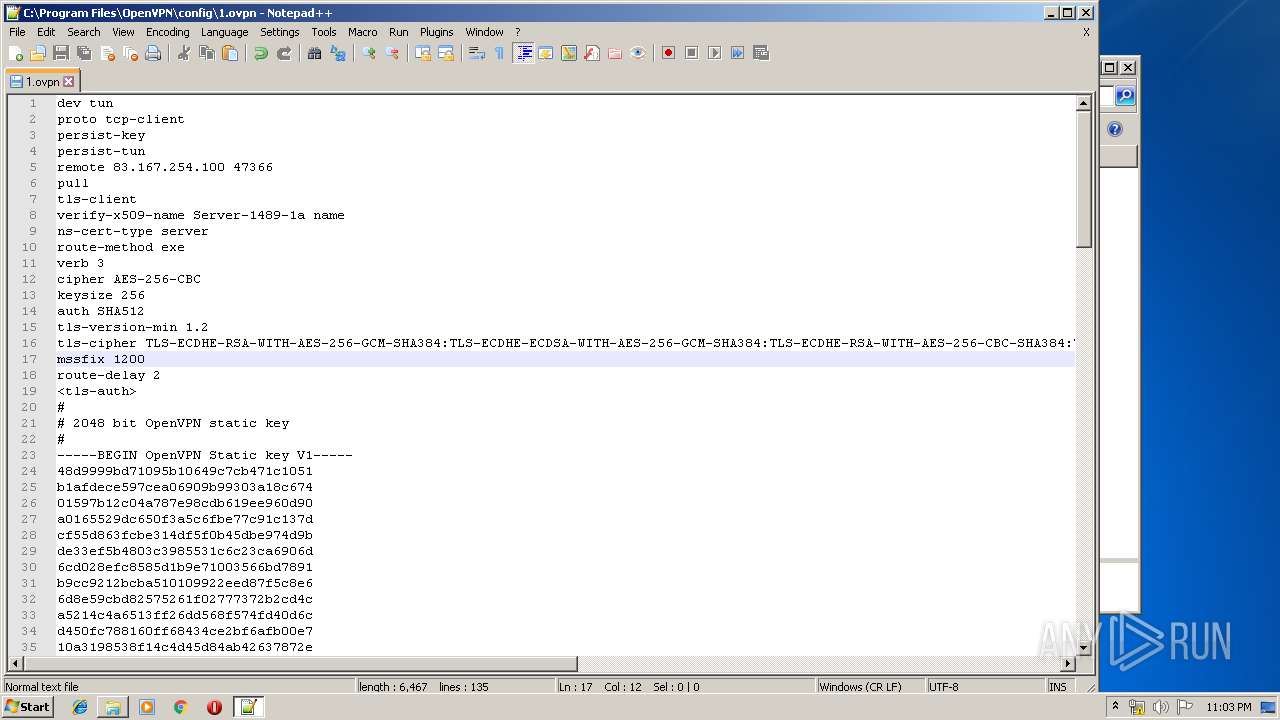
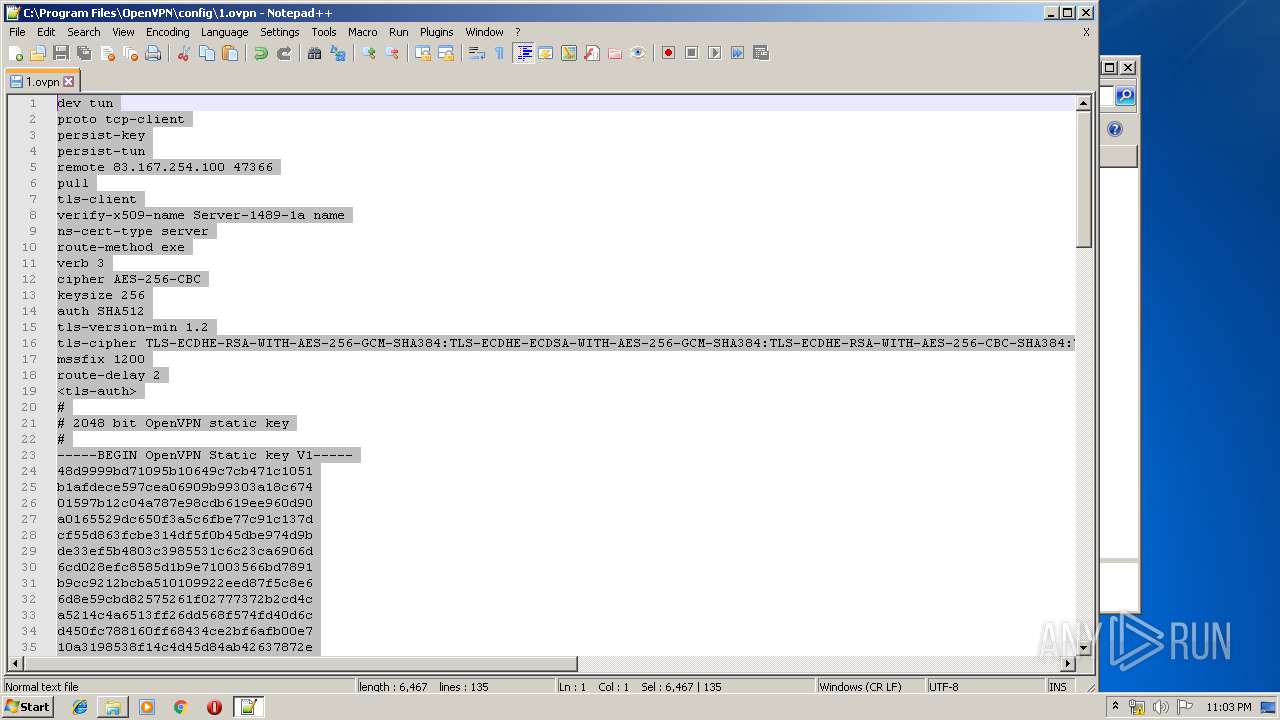
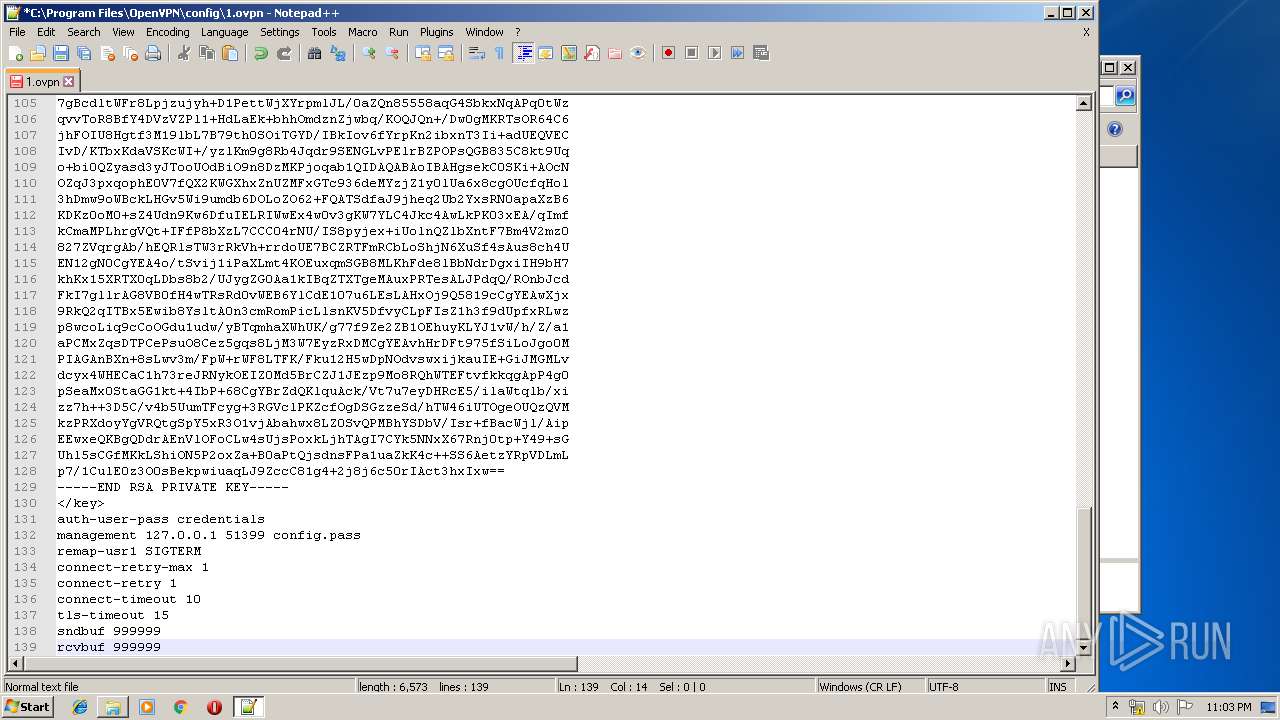
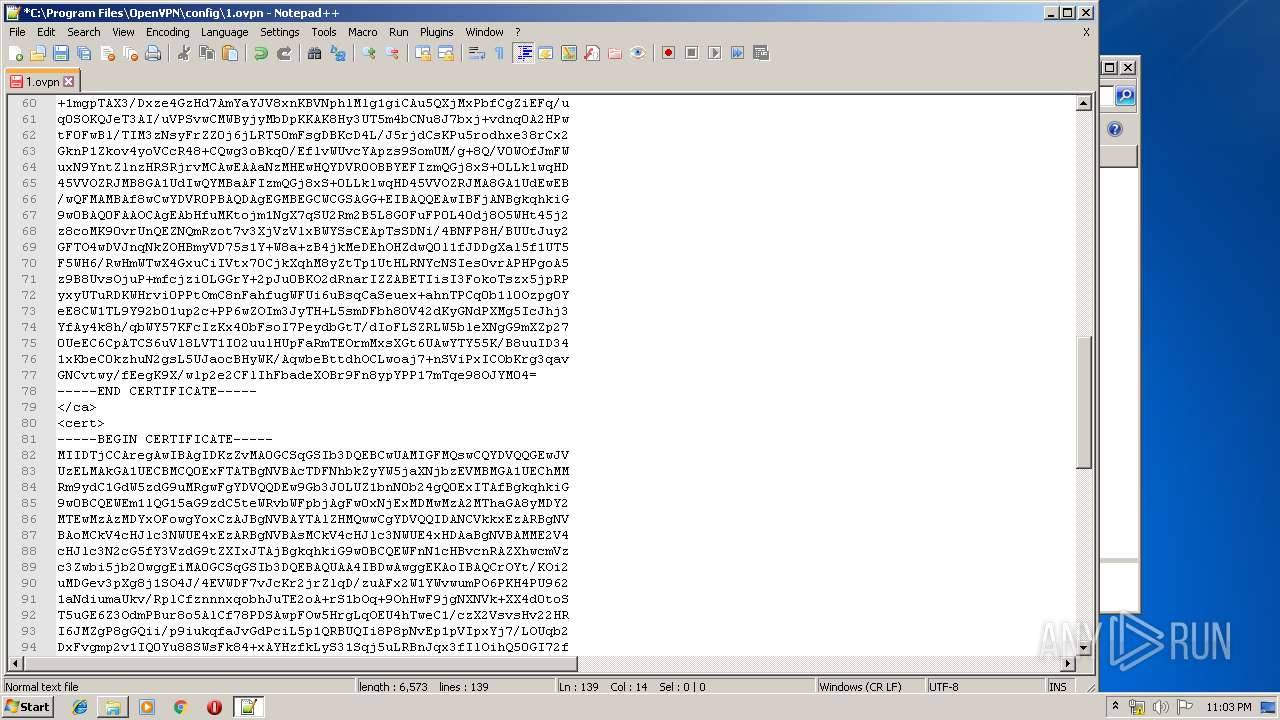
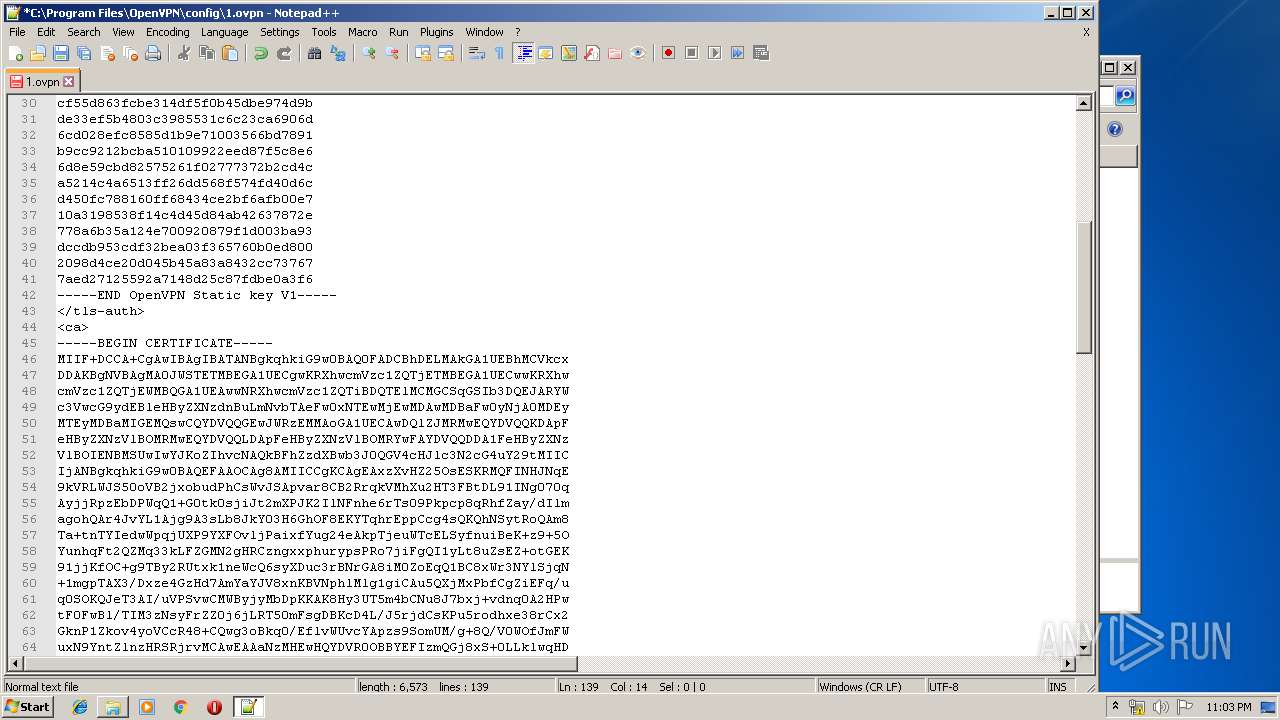
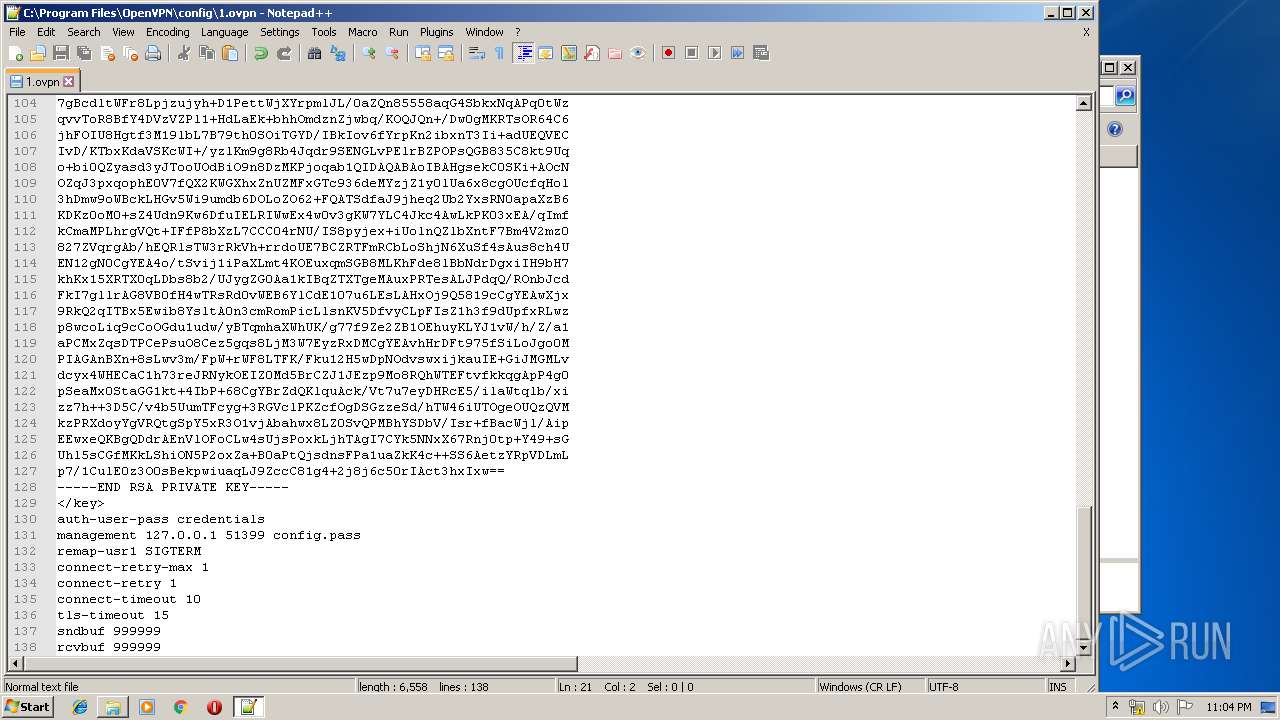
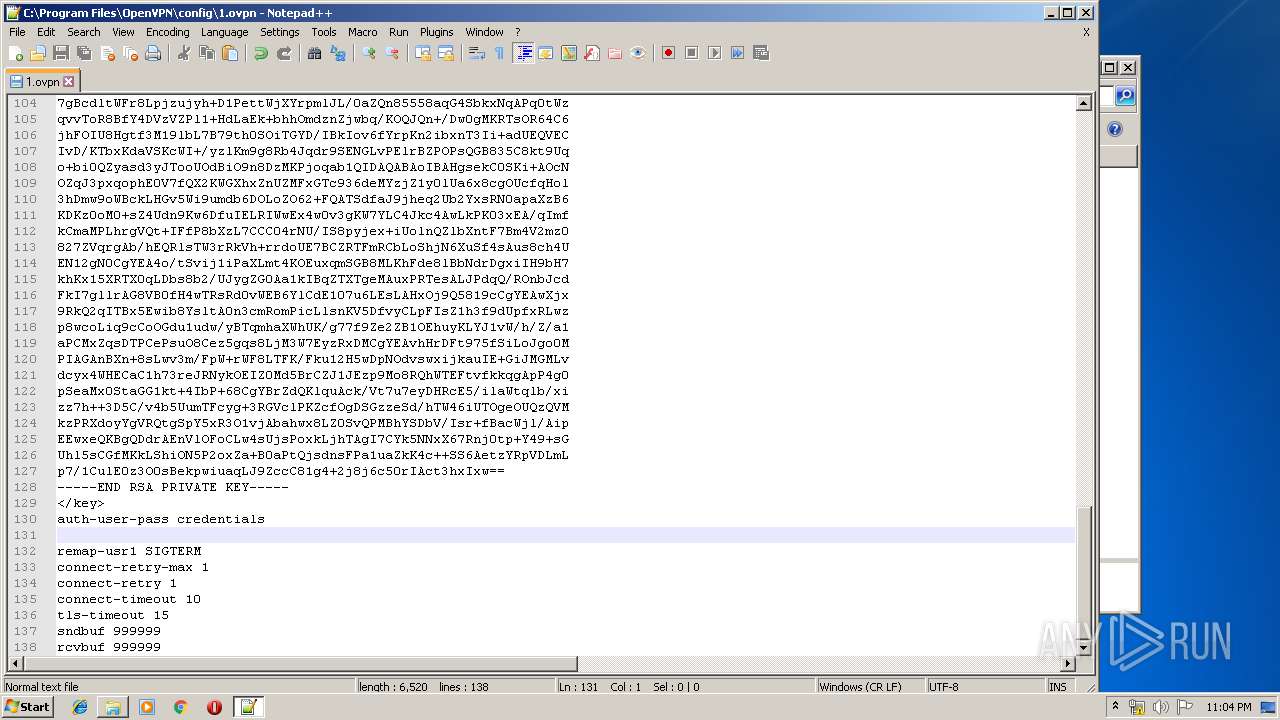
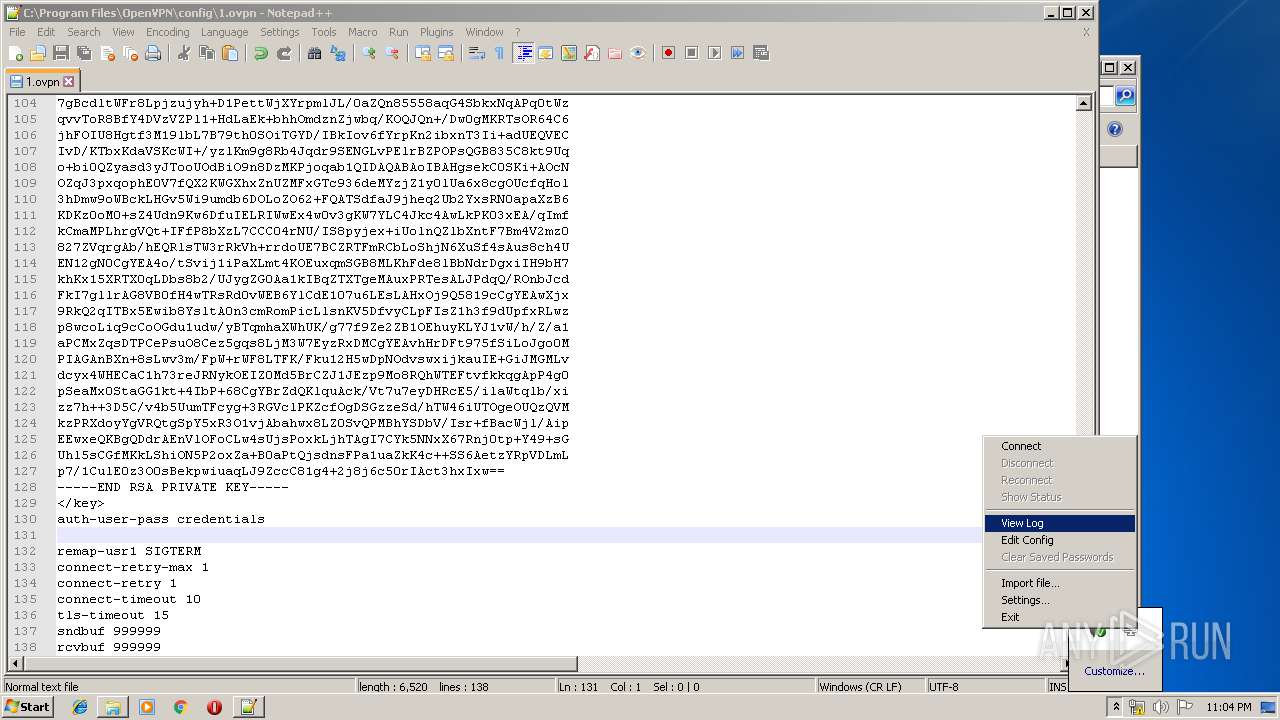
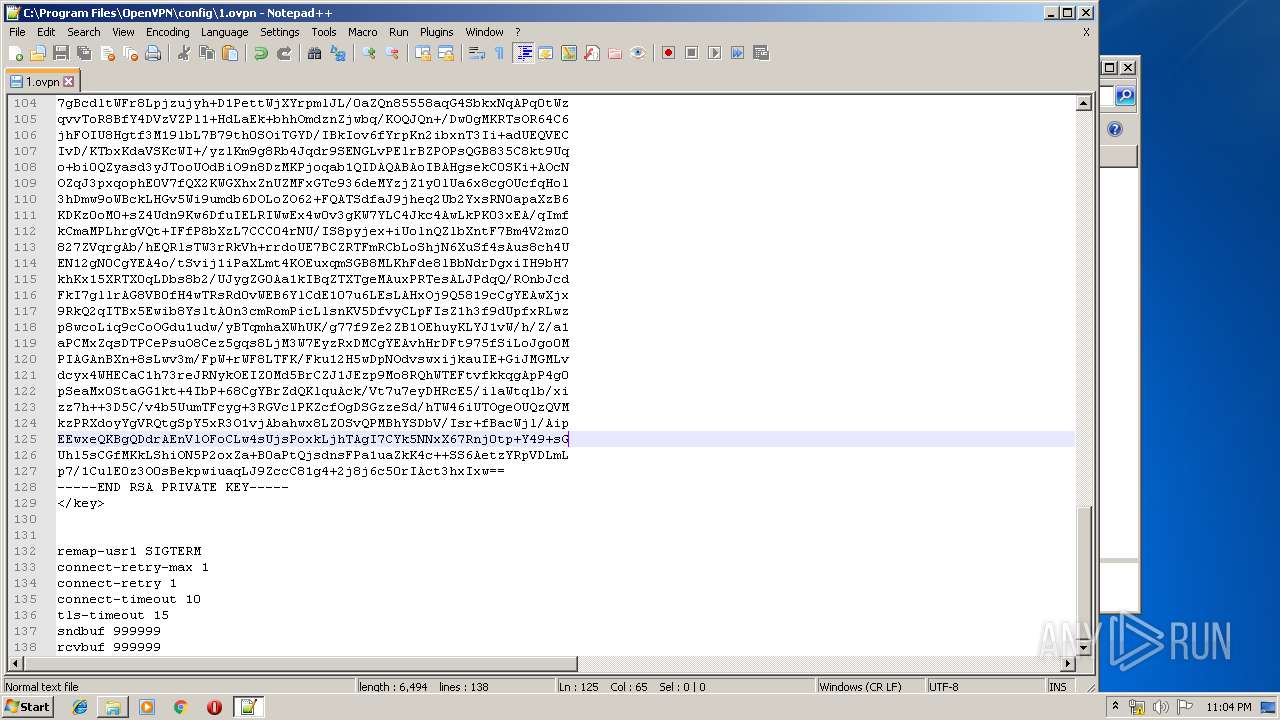
| 1936 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\1.ovpn" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1992 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{6f47c061-2274-2672-e3ed-9c03e9239323} Global\{709b490c-8734-640a-383d-3b49189ce853} C:\Windows\System32\DriverStore\Temp\{1febfac0-dd1d-0485-a18a-672e3b7b9409}\oemvista.inf C:\Windows\System32\DriverStore\Temp\{1febfac0-dd1d-0485-a18a-672e3b7b9409}\tap0901.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | openvpn --log "C:\Users\admin\OpenVPN\log\1.log" --config "1.ovpn" --setenv IV_GUI_VER "OpenVPN GUI 11" --service f000000077c 0 --auth-retry interact --management 127.0.0.1 25340 stdin --management-query-passwords --management-hold --pull-filter ignore route-method --msg-channel 196 | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpnserv.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
| 2440 | openvpn --log "C:\Users\admin\OpenVPN\log\1.log" --config "1.ovpn" --setenv IV_GUI_VER "OpenVPN GUI 11" --service f00000005a8 0 --auth-retry interact --management 127.0.0.1 25340 stdin --management-query-passwords --management-hold --pull-filter ignore route-method --msg-channel 392 | C:\Program Files\OpenVPN\bin\openvpn.exe | — | openvpnserv.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 1 Version: 2.4.8.0 Modules
| |||||||||||||||
| 2520 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 793
Read events
1 174
Write events
569
Delete events
50
Modification events
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | config_dir |
Value: C:\Program Files\OpenVPN\config | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | config_ext |
Value: ovpn | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | exe_path |
Value: C:\Program Files\OpenVPN\bin\openvpn.exe | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | log_dir |
Value: C:\Program Files\OpenVPN\log | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | priority |
Value: NORMAL_PRIORITY_CLASS | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | log_append |
Value: 0 | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | ovpn_admin_group |
Value: OpenVPN Administrators | |||
| (PID) Process: | (2536) openvpn-install-2.4.8-I602-Win7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\OpenVPN |
| Operation: | write | Name: | disable_save_passwords |
Value: 0 | |||
| (PID) Process: | (2604) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2604) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
Executable files
31
Suspicious files
18
Text files
247
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Program Files\OpenVPN\bin\openvpn.exe | executable | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Documentation\OpenVPN Windows Notes.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Documentation\OpenVPN Manual Page.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Program Files\OpenVPN\bin\openvpnserv.exe | executable | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsyB478.tmp\System.dll | executable | |
MD5:2E025E2CEE2953CCE0160C3CD2E1A64E | SHA256:D821A62802900B068DCF61DDC9FDFF2F7ADA04B706815AB6E5038B21543DA8A5 | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsyB478.tmp\modern-header.bmp | image | |
MD5:CD8BC7B987FA89E7FD5ACDED7148CF66 | SHA256:127FC8103D7D1DAACFB0ABB422C9B2AA8ED14FA095E06A997E43445D5D963352 | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Utilities\Generate a static OpenVPN key.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsyB478.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\OpenVPN\Shortcuts\OpenVPN Sample Configuration Files.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2536 | openvpn-install-2.4.8-I602-Win7.exe | C:\Users\admin\AppData\Local\Temp\nsyB478.tmp\nsProcess.dll | executable | |
MD5:05450FACE243B3A7472407B999B03A72 | SHA256:95FE9D92512FF2318CC2520311EF9145B2CEE01209AB0E1B6E45C7CE1D4D0E89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | openvpn.exe | 83.167.254.100:47366 | — | Master Internet s.r.o. | CZ | unknown |
3680 | openvpn.exe | 83.167.254.100:47366 | — | Master Internet s.r.o. | CZ | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2764 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|