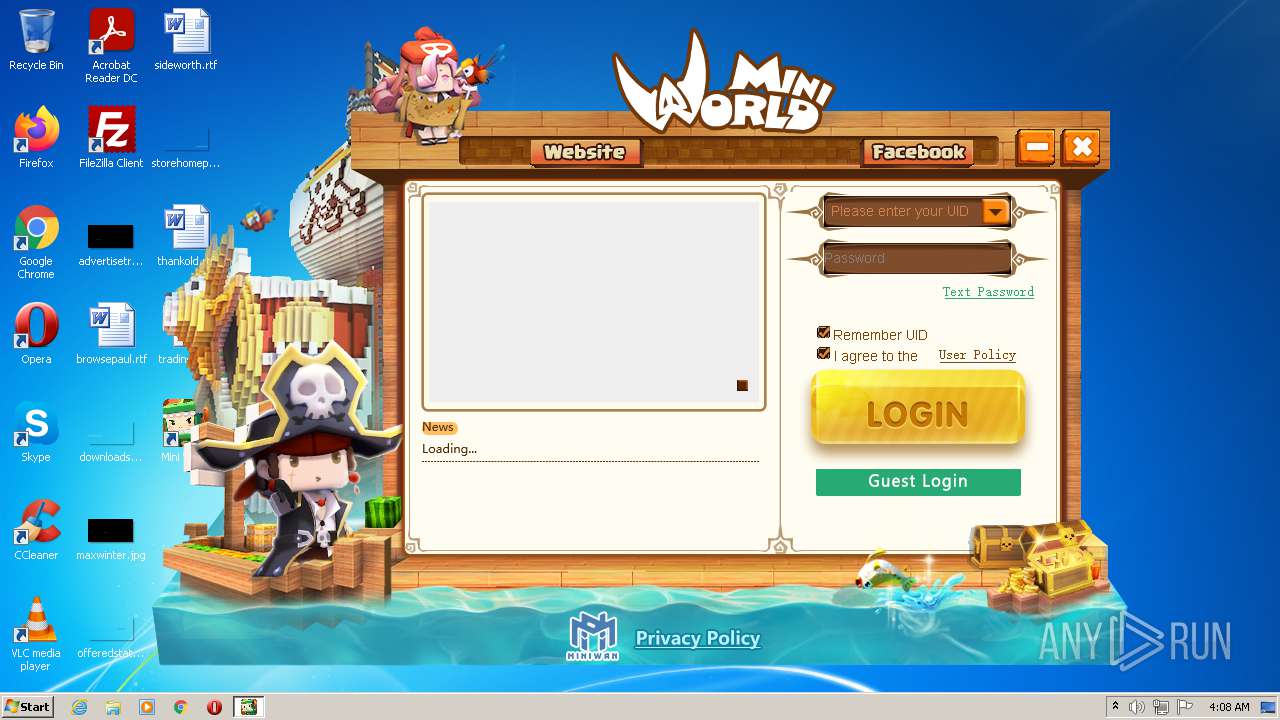
| File name: | mini_world_installation_package.exe |
| Full analysis: | https://app.any.run/tasks/f4a5d9cf-6ae9-4143-81f6-132563835502 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2021, 03:07:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 566689C2098F0DCDB756538668F7D2B0 |
| SHA1: | 57AAA26CA931E1346062A391D96174AA8946DF77 |
| SHA256: | 16138D638B231331060FE69914409BB9959AA92FCAEE48D4AC746D2F764BE89F |
| SSDEEP: | 196608:sn4KiVNWzpjvdzO9sh2Sjrq7jZsAuEaxFNe0:snL9zW2YSi/3u7xFNR |
MALICIOUS
Application was dropped or rewritten from another process
- MicroMiniNew.exe (PID: 2756)
Loads dropped or rewritten executable
- MicroMiniNew.exe (PID: 2756)
Changes settings of System certificates
- MicroMiniNew.exe (PID: 2756)
SUSPICIOUS
Checks supported languages
- mini_world_installation_package.exe (PID: 1560)
- MicroMiniNew.exe (PID: 2756)
Executable content was dropped or overwritten
- mini_world_installation_package.exe (PID: 1560)
Creates files in the user directory
- MicroMiniNew.exe (PID: 2756)
- mini_world_installation_package.exe (PID: 1560)
Drops a file with too old compile date
- mini_world_installation_package.exe (PID: 1560)
Reads the computer name
- mini_world_installation_package.exe (PID: 1560)
- MicroMiniNew.exe (PID: 2756)
Creates files in the program directory
- mini_world_installation_package.exe (PID: 1560)
Creates a software uninstall entry
- mini_world_installation_package.exe (PID: 1560)
Adds / modifies Windows certificates
- MicroMiniNew.exe (PID: 2756)
Reads internet explorer settings
- MicroMiniNew.exe (PID: 2756)
Reads Microsoft Outlook installation path
- MicroMiniNew.exe (PID: 2756)
Drops a file that was compiled in debug mode
- mini_world_installation_package.exe (PID: 1560)
INFO
Checks Windows Trust Settings
- MicroMiniNew.exe (PID: 2756)
Reads settings of System Certificates
- MicroMiniNew.exe (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00011420 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.39961 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
211 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Users\admin\AppData\Local\Temp\mini_world_installation_package.exe" | C:\Users\admin\AppData\Local\Temp\mini_world_installation_package.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2756 | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\MicroMiniNew.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\MicroMiniNew.exe | mini_world_installation_package.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ???? Microsoft ??????? Exit code: 0 Version: 1, 0, 1, 4 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\mini_world_installation_package.exe" | C:\Users\admin\AppData\Local\Temp\mini_world_installation_package.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
10 938
Read events
10 883
Write events
55
Delete events
0
Modification events
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | NSIS:StartMenuDir |
Value: Mini World Block Art | |||
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | DisplayName |
Value: Mini World Block Art 0.21.10 | |||
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Roaming\miniworldOverseasgame\uninst.exe | |||
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | DisplayVersion |
Value: 0.21.10 | |||
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | URLInfoAbout |
Value: http://en.mini1.cn | |||
| (PID) Process: | (1560) mini_world_installation_package.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mini World Block Art |
| Operation: | write | Name: | Publisher |
Value: MiniWan Technology CO.,LIMITED | |||
| (PID) Process: | (2756) MicroMiniNew.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2756) MicroMiniNew.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2756) MicroMiniNew.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2756) MicroMiniNew.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
9
Suspicious files
10
Text files
241
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\Microsoft.VC90.CRT.manifest | xml | |
MD5:6BB5D2AAD0AE1B4A82E7DDF7CF58802A | SHA256:9E0220511D4EBDB014CC17ECB8319D57E3B0FEA09681A80D8084AA8647196582 | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\GdiPlus.dll | executable | |
MD5:5017ECFB0B4C152DE6F848FABEBB69A8 | SHA256:2CC12B331F4E4CCEEE2CAEDEAE3595C89ED8863966737D9C14280773F5A3AB7C | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\iworld.cfg | xml | |
MD5:0B50D4E9EC3473CDEE9E4BCFE4B67EAC | SHA256:8950ACF6C344D62872A92B577F1AEB3F9E0C71AD689D3E6207E8EED3563C0BFF | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\start.mnw | executable | |
MD5:— | SHA256:— | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\configbase.ini | text | |
MD5:A1D32E7092CAFA0EB185FEA03490A187 | SHA256:AB628E1DE01C6B32A9FC531356F3B85D4D1EA6AC26D76292602F7B430CA49BAE | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\configload.ini | text | |
MD5:— | SHA256:— | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\msvcr90.dll | executable | |
MD5:7538050656FE5D63CB4B80349DD1CFE3 | SHA256:E16BC9B66642151DE612EE045C2810CA6146975015BD9679A354567F56DA2099 | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\miniworld.ico | image | |
MD5:— | SHA256:— | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\MicroMiniNew.exe | executable | |
MD5:— | SHA256:— | |||
| 1560 | mini_world_installation_package.exe | C:\Users\admin\AppData\Roaming\miniworldOverseasgame\msvcp100.dll | executable | |
MD5:BC83108B18756547013ED443B8CDB31B | SHA256:B2AD109C15EAA92079582787B7772BA0A2F034F7D075907FF87028DF0EAEA671 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
24
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2756 | MicroMiniNew.exe | GET | — | 163.171.132.19:80 | http://hwmdownload.mini1.cn/zhengshi5312-04-29/firstpatch-2.1.3.1.7z?version=2.1.3.1 | US | — | — | malicious |
2756 | MicroMiniNew.exe | GET | 301 | 151.101.1.229:80 | http://cdn.jsdelivr.net/npm/jquery@1.12.4/dist/jquery.min.js | US | — | — | whitelisted |
2756 | MicroMiniNew.exe | GET | — | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAkG%2FnjDvtjt4TrGKke%2FLjQ%3D | US | — | — | whitelisted |
2756 | MicroMiniNew.exe | GET | 301 | 151.101.1.229:80 | http://cdn.jsdelivr.net/npm/jquery.cookie@1.4.1/jquery.cookie.min.js | US | — | — | whitelisted |
2756 | MicroMiniNew.exe | GET | 200 | 49.51.39.29:8090 | http://hwoperate.mini1.cn:8090/loadset/loadresget.php?apiid=410 | CN | text | 98 b | unknown |
2756 | MicroMiniNew.exe | GET | 200 | 47.246.43.228:80 | http://mnweb.miniworldgame.com/web/game/version.json | US | text | 46 b | malicious |
2756 | MicroMiniNew.exe | GET | 200 | 47.254.25.186:80 | http://clogin.miniworldgame.com/newspage/ | US | html | 623 b | unknown |
2756 | MicroMiniNew.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.40 Kb | whitelisted |
2756 | MicroMiniNew.exe | GET | 200 | 47.246.43.228:80 | http://mnweb.miniworldgame.com/web/clogin/newspage/js/index.467f7bcc.js | US | text | 5.29 Kb | malicious |
2756 | MicroMiniNew.exe | GET | 200 | 47.246.43.228:80 | http://mnweb.miniworldgame.com/web/clogin/newspage/images/813ac9c3.png | US | image | 33.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | MicroMiniNew.exe | 49.51.39.29:8090 | hwoperate.mini1.cn | Tencent Building, Kejizhongyi Avenue | CN | unknown |
2756 | MicroMiniNew.exe | 151.101.1.229:80 | cdn.jsdelivr.net | Fastly | US | suspicious |
2756 | MicroMiniNew.exe | 47.246.43.228:80 | mnweb.miniworldgame.com | — | US | malicious |
2756 | MicroMiniNew.exe | 198.11.178.73:80 | tj_hk.mini1.cn | Alibaba (China) Technology Co., Ltd. | US | unknown |
2756 | MicroMiniNew.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2756 | MicroMiniNew.exe | 47.88.79.85:443 | www.miniworldgame.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2756 | MicroMiniNew.exe | 163.171.144.39:443 | cdn-mnweb.miniworldgame.com | — | US | malicious |
2756 | MicroMiniNew.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2756 | MicroMiniNew.exe | 198.11.178.73:443 | tj_hk.mini1.cn | Alibaba (China) Technology Co., Ltd. | US | unknown |
2756 | MicroMiniNew.exe | 18.184.146.246:14100 | hwacchm.miniworldgame.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hwoperate.mini1.cn |
| unknown |
mnweb.miniworldgame.com |
| malicious |
clogin.miniworldgame.com |
| unknown |
hwmdownload.mini1.cn |
| malicious |
cdn.jsdelivr.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
tj_hk.mini1.cn |
| unknown |
ocsp2.globalsign.com |
| whitelisted |
www.miniworldgame.com |
| unknown |
ocsp.digicert.com |
| whitelisted |