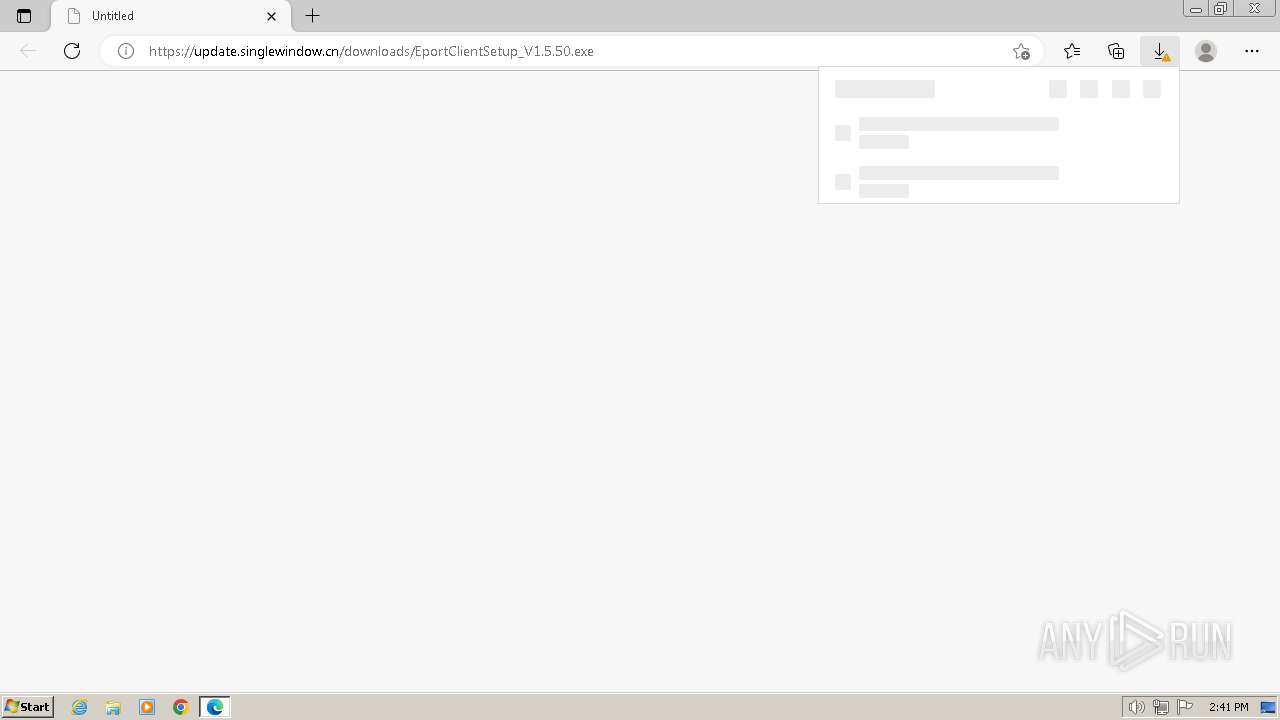
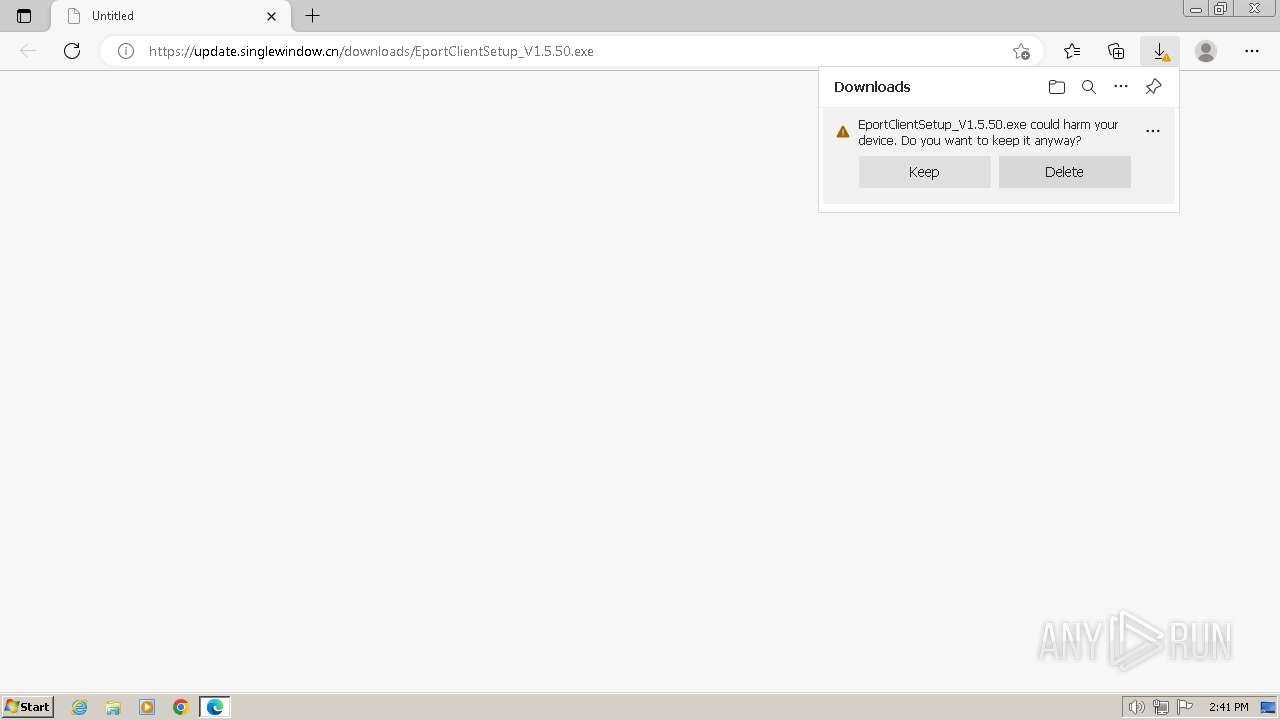
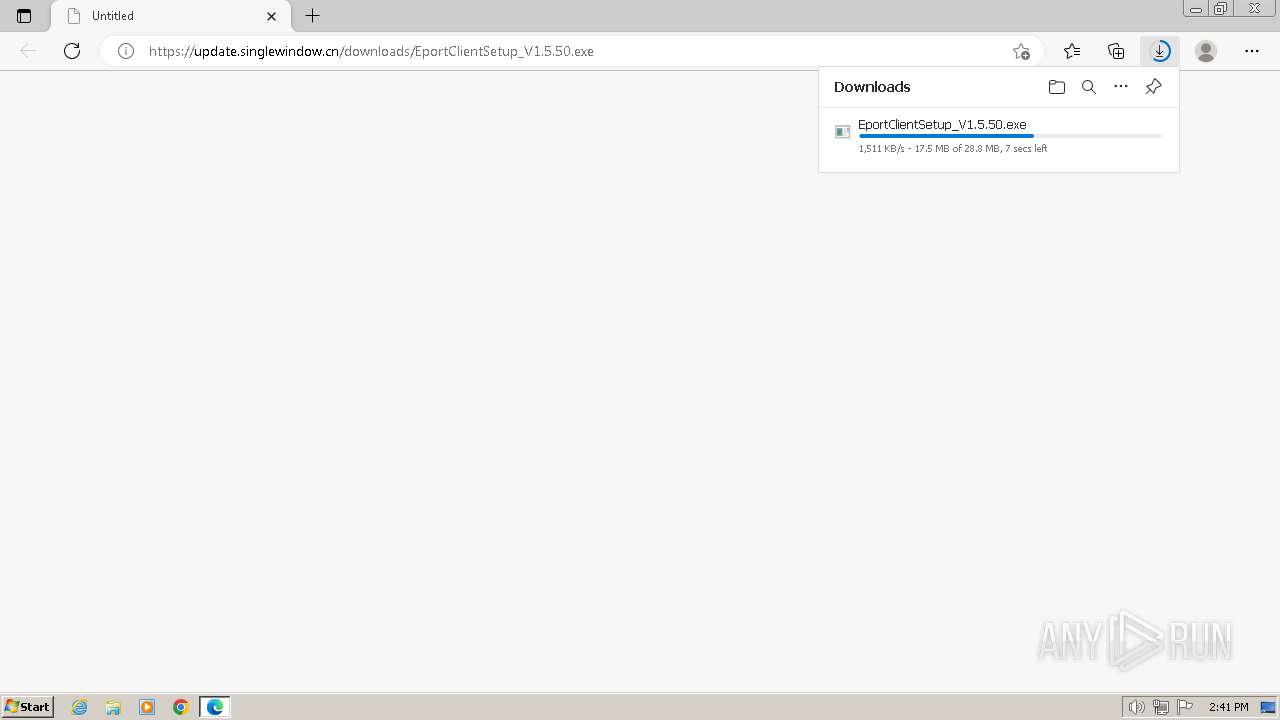
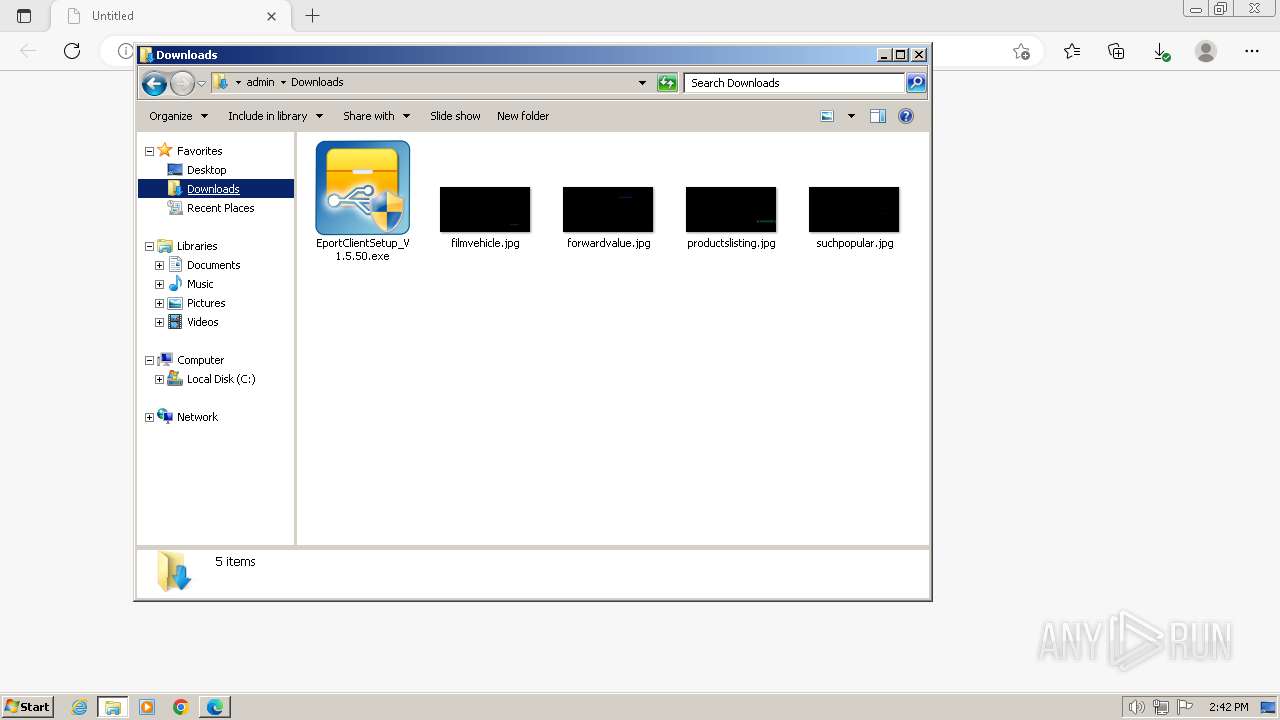
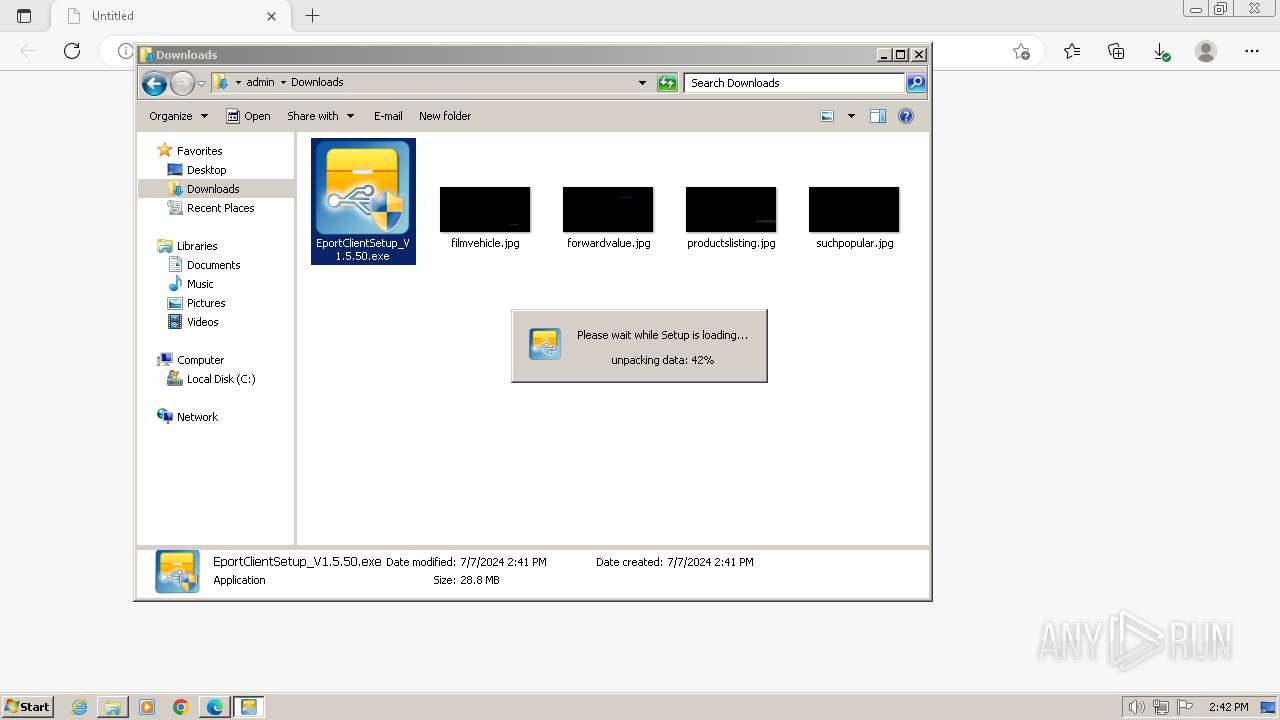
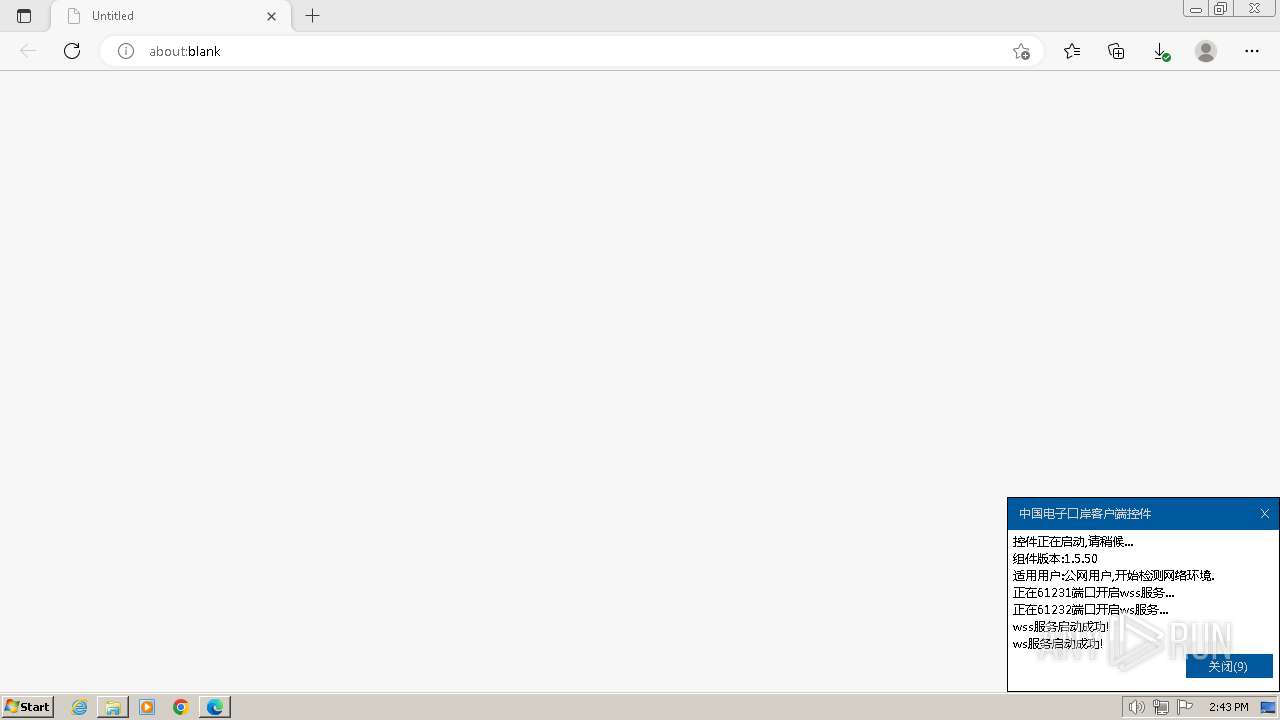
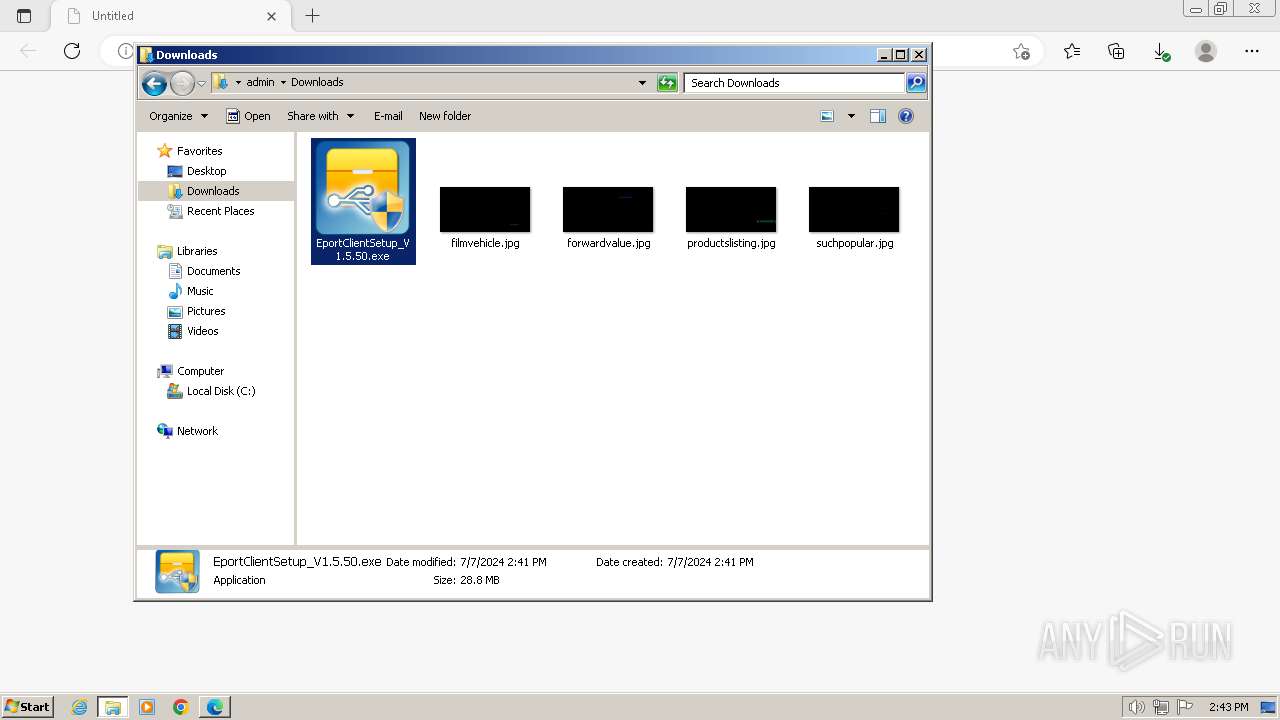
| URL: | https://update.singlewindow.cn/downloads/EportClientSetup_V1.5.50.exe |
| Full analysis: | https://app.any.run/tasks/0b48144a-5c16-4e51-a522-eccb9e0c1e62 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2024, 13:41:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 94F22E3B9DC45AA7E9B4FB41449FBBF4 |
| SHA1: | F1CA92F602F084716C10707AD62CAB4DB6FC905D |
| SHA256: | 15F0510EB2DE763284951524BC530775B5085E95E2EA7911C996C138CE1FC1FB |
| SSDEEP: | 3:N8vRAv2JKa1KZss0QgLQWC:2v5ozZsPLQWC |
MALICIOUS
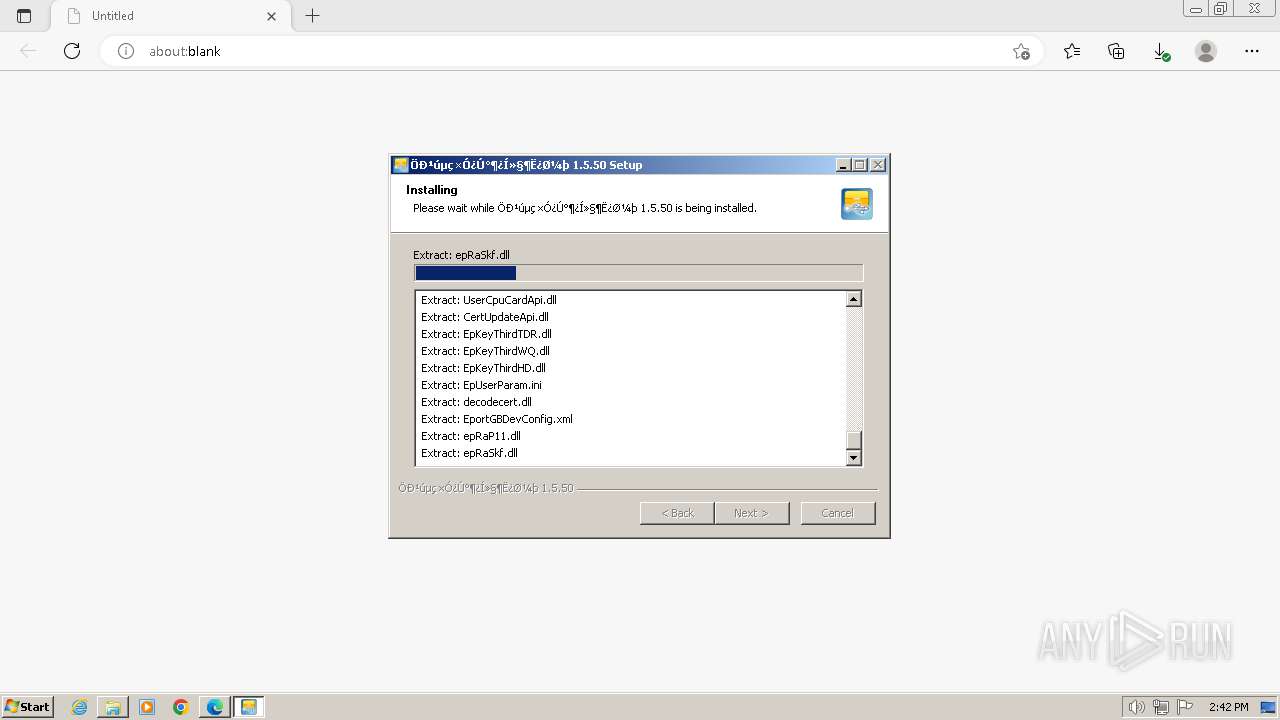
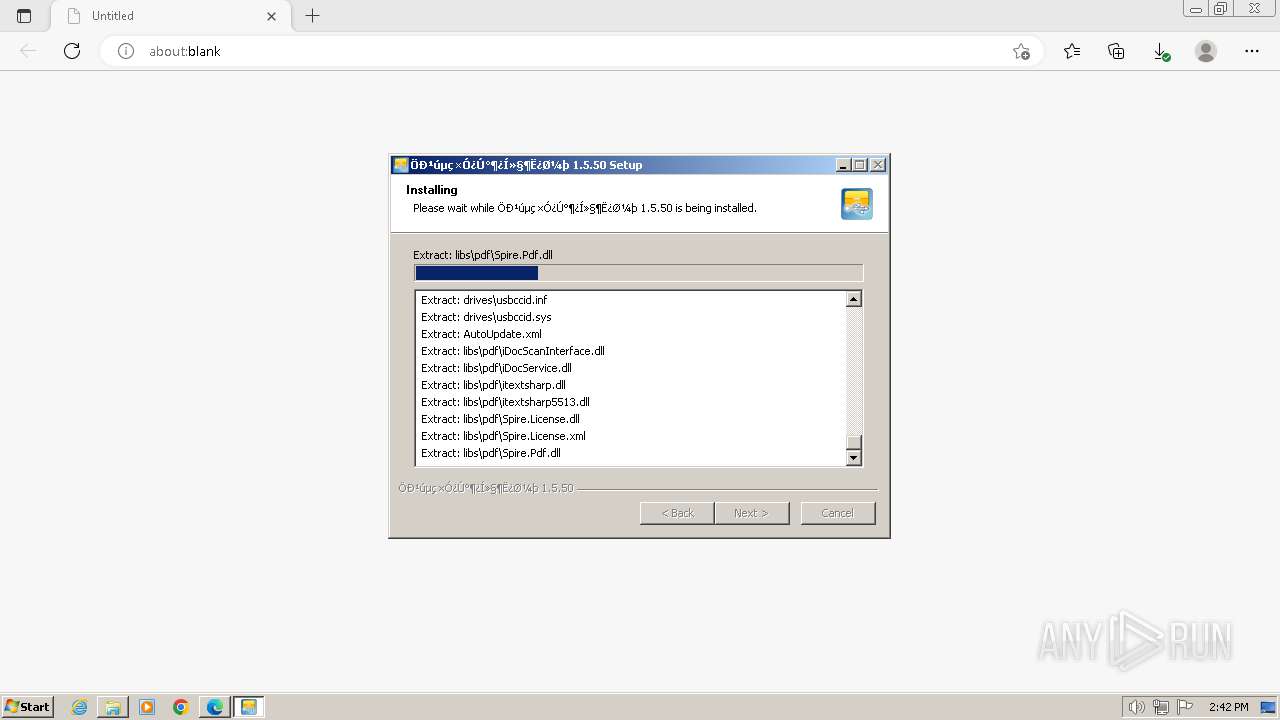
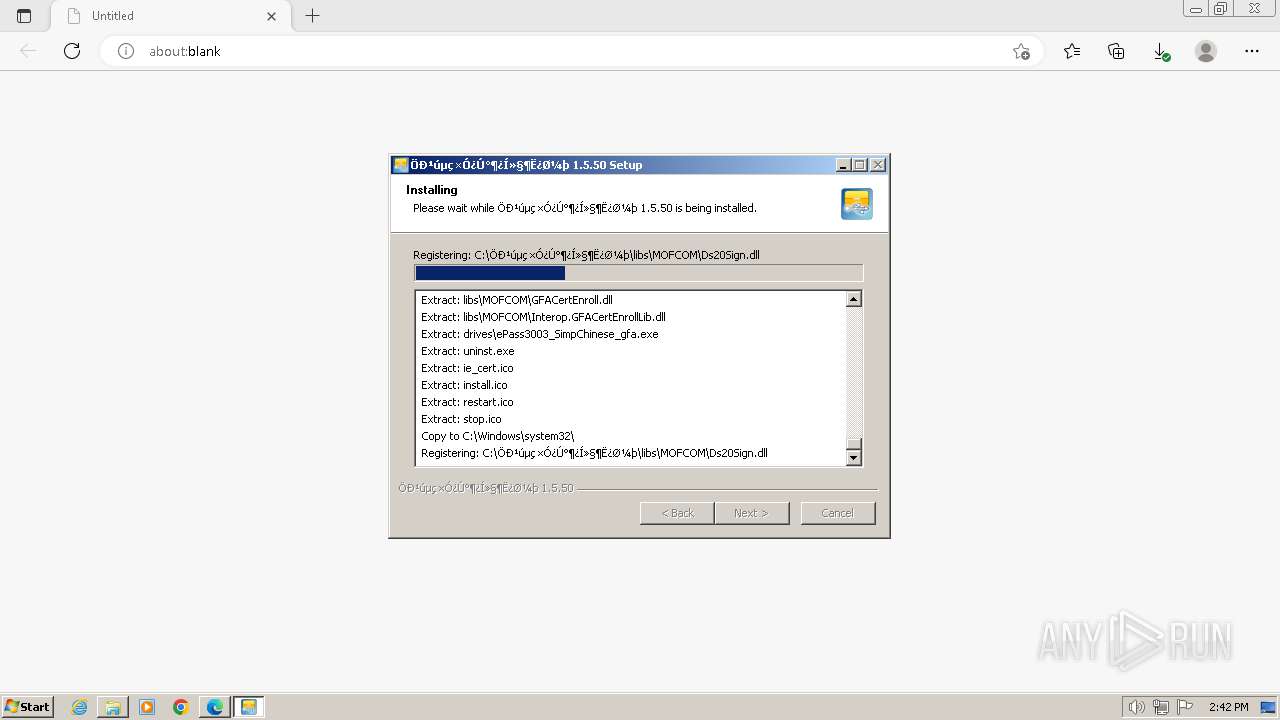
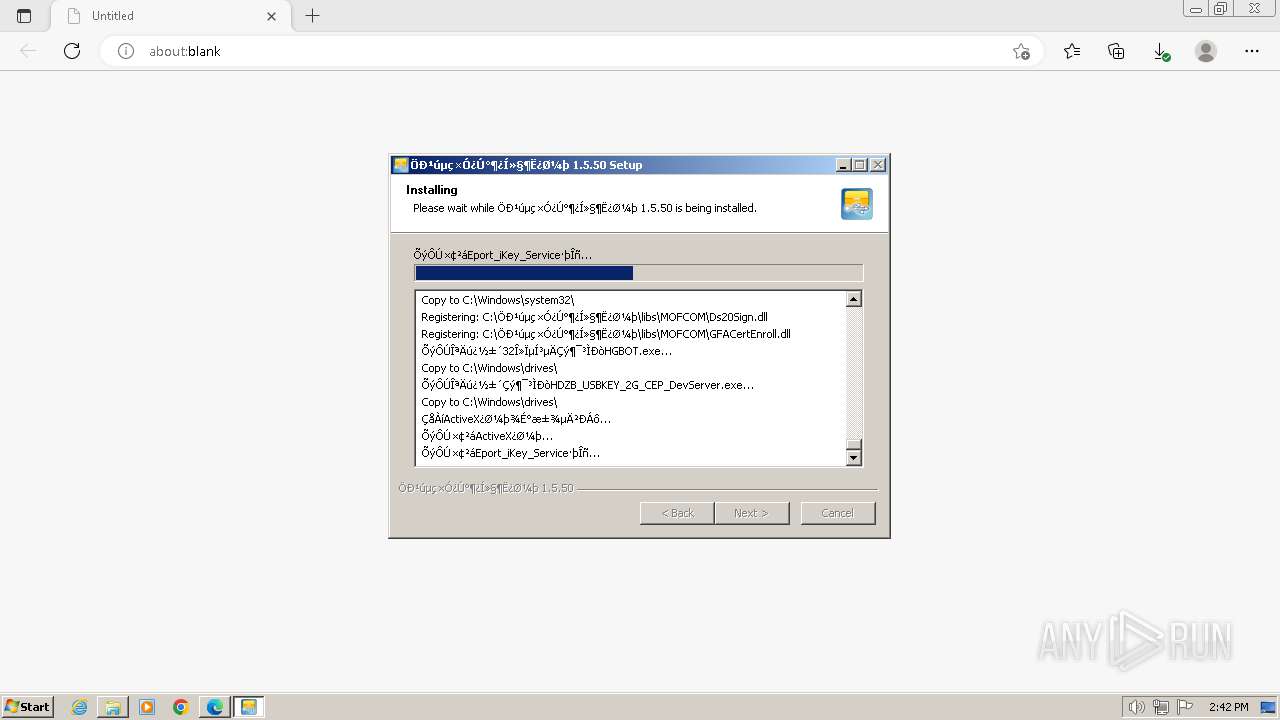
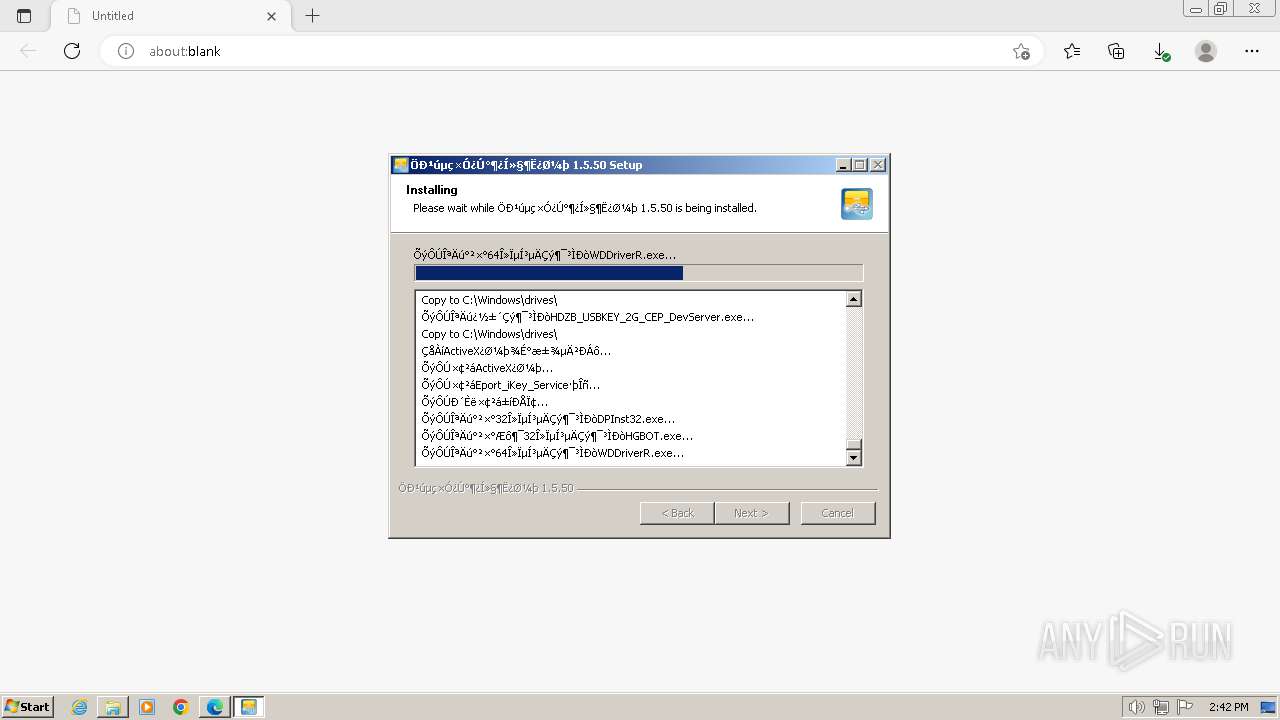
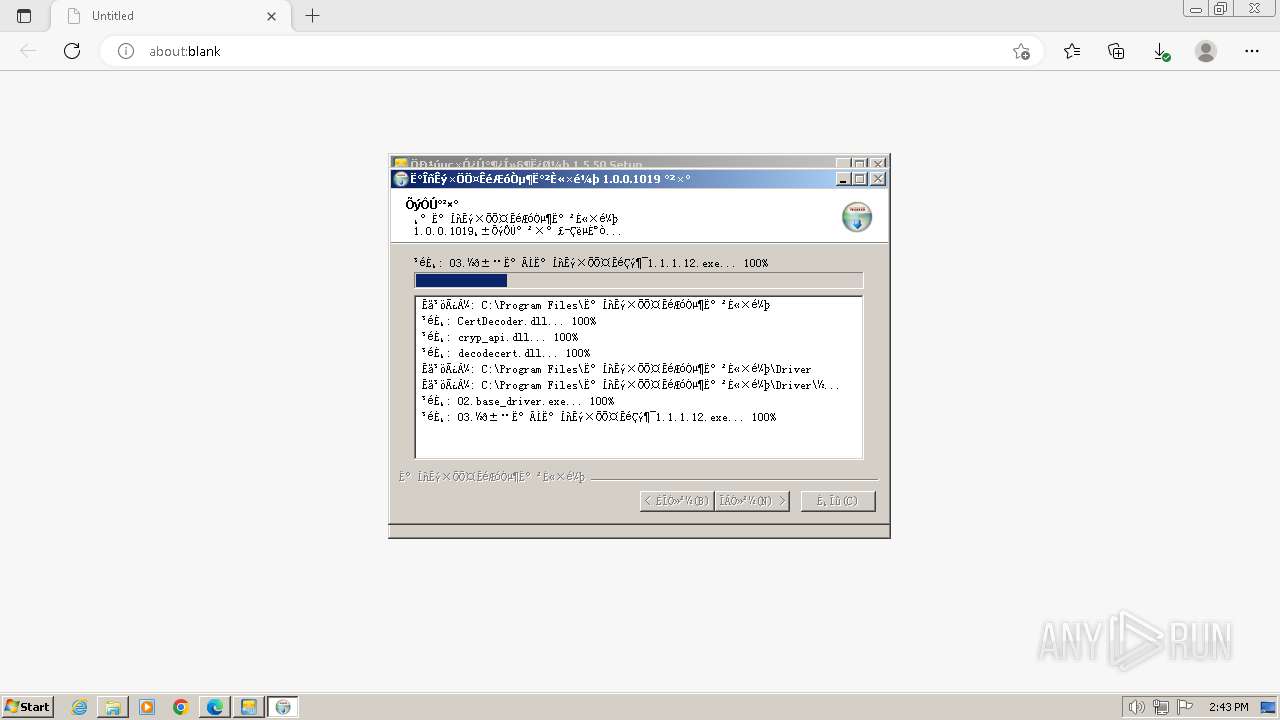
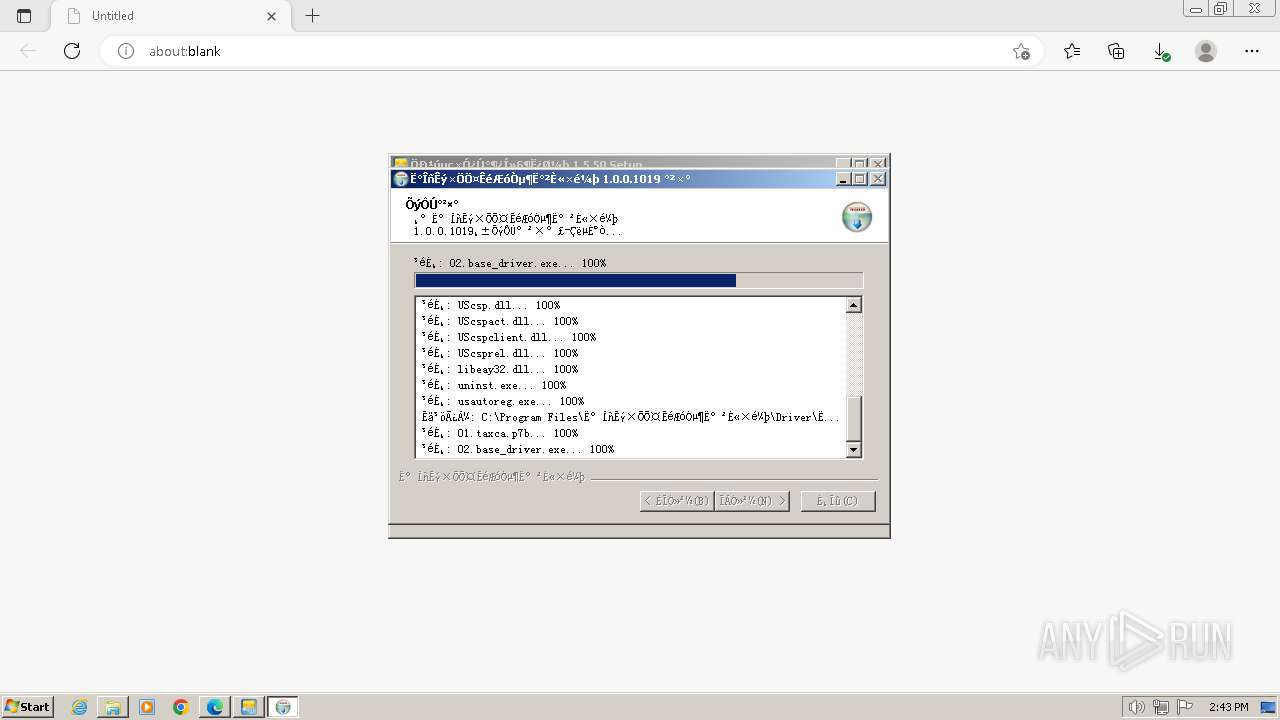
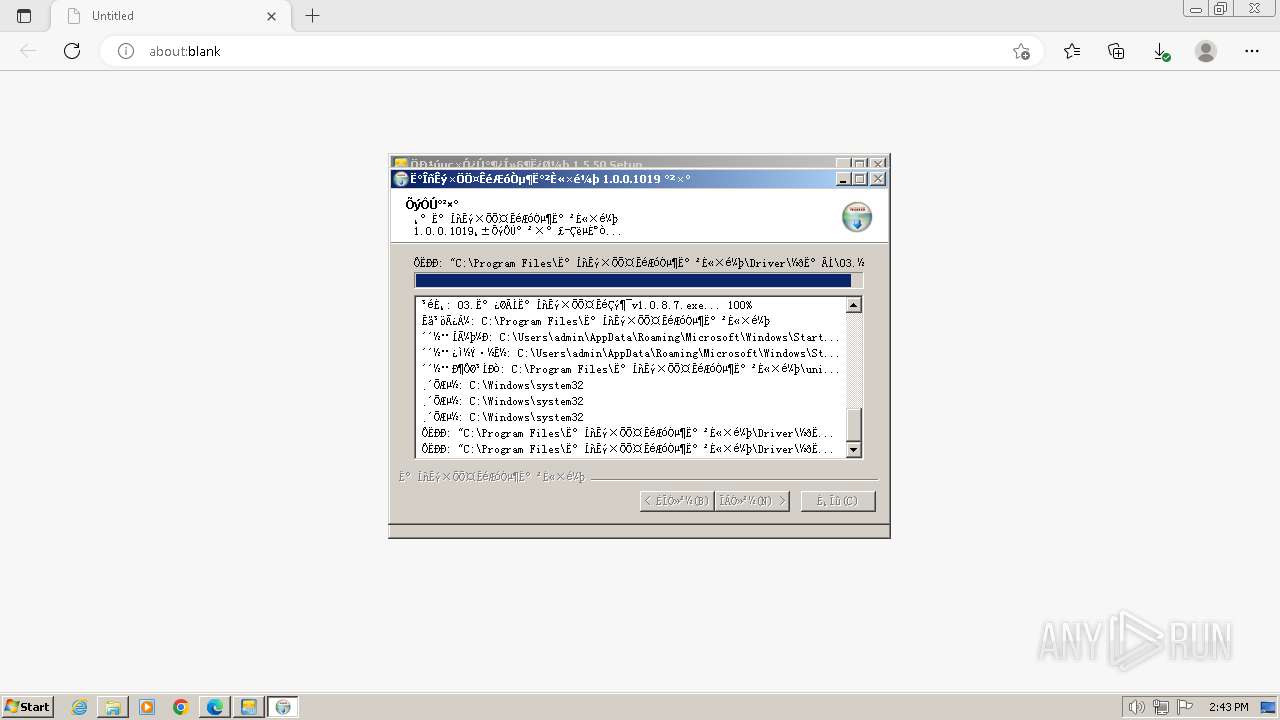
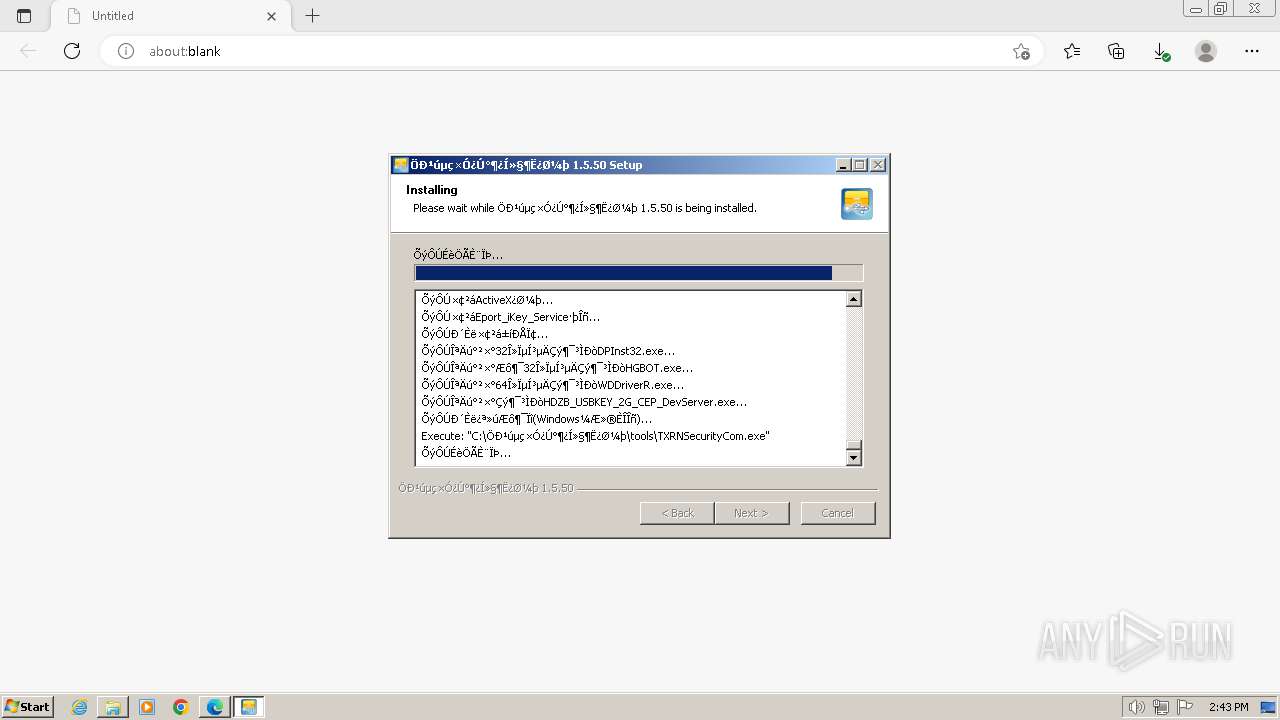
Drops the executable file immediately after the start
- EportClientSetup_V1.5.50.exe (PID: 2704)
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
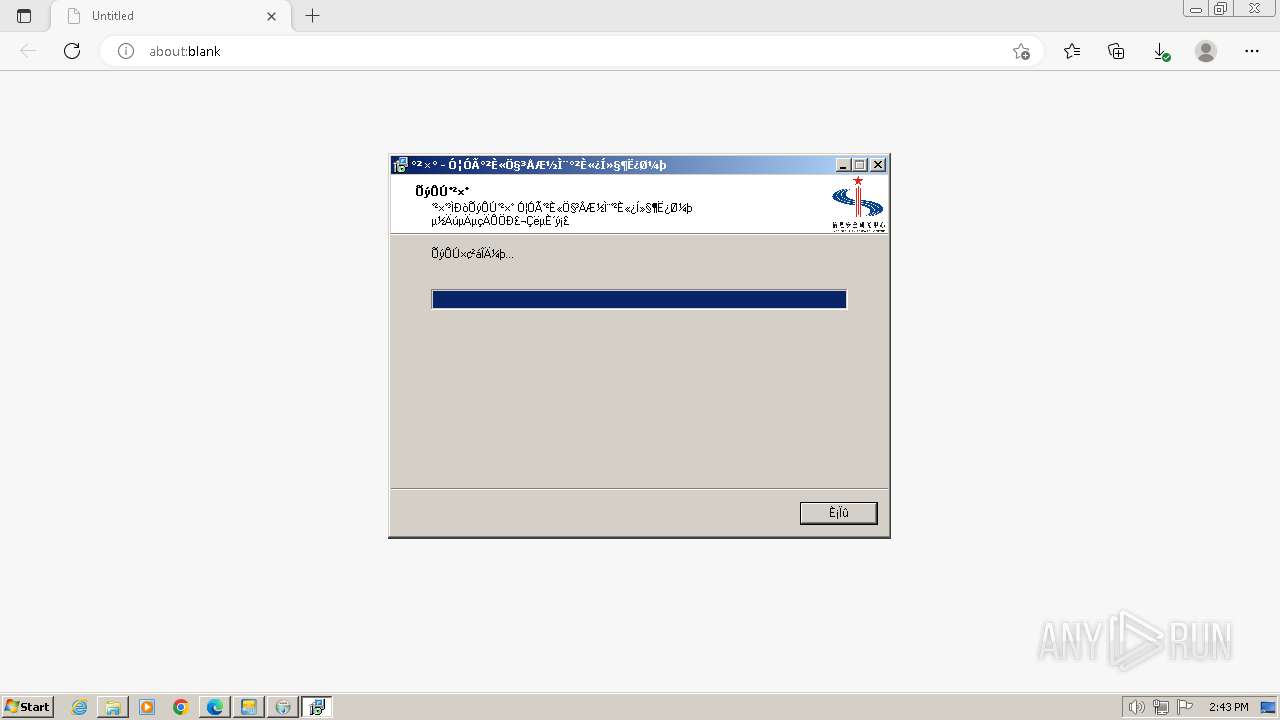
- WDTokenServerSetup.exe (PID: 4008)
- TXRNSecurityCom.exe (PID: 3016)
- 02.base_driver.exe (PID: 3136)
- 02.base_driver.tmp (PID: 3976)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
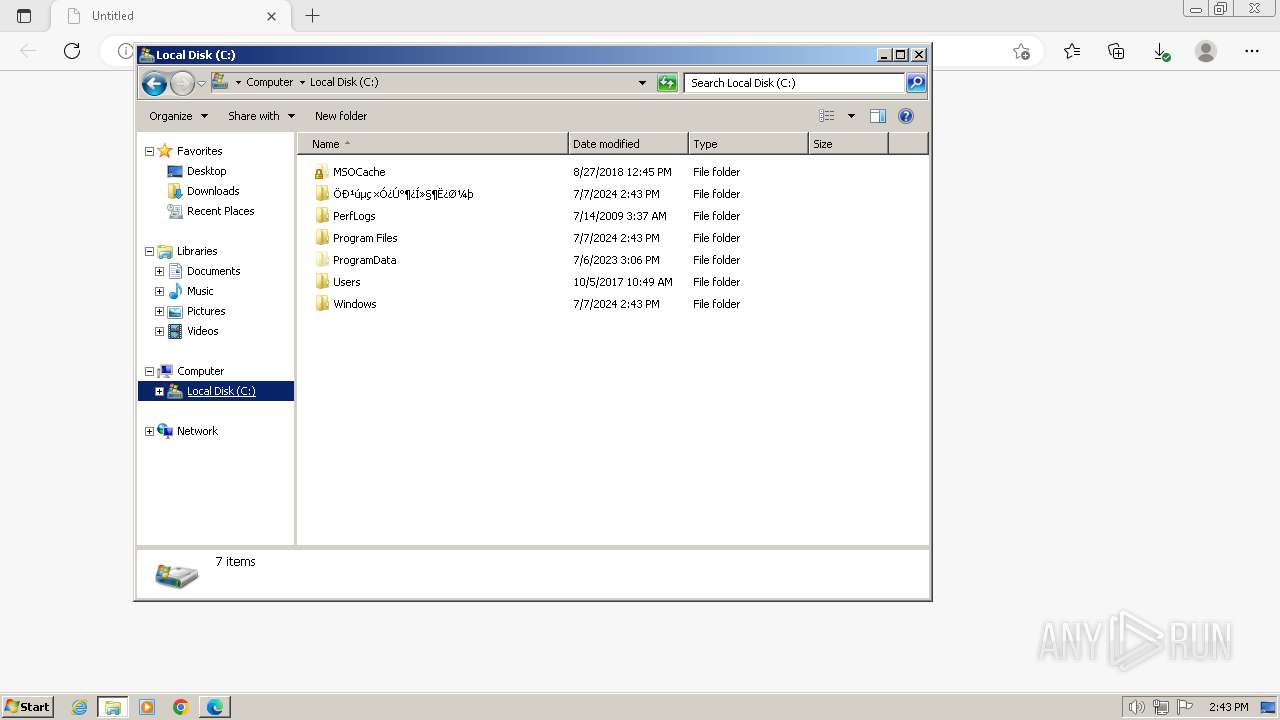
Creates a writable file in the system directory
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- WDTokenServerSetup.exe (PID: 4008)
- TXRNSecurityCom.exe (PID: 3016)
- ActiveXRegGs.exe (PID: 2492)
- 02.base_driver.tmp (PID: 3976)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- CnEport.Pub.WinService.exe (PID: 748)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Uses Task Scheduler to autorun other applications
- ns4E5C.tmp (PID: 1388)
Starts NET.EXE for service management
- net.exe (PID: 3728)
- ns5095.tmp (PID: 1944)
- ns8F15.tmp (PID: 3708)
- ns9205.tmp (PID: 3328)
- net.exe (PID: 880)
- net.exe (PID: 4056)
Registers / Runs the DLL via REGSVR32.EXE
- 02.base_driver.tmp (PID: 3976)
Changes the autorun value in the registry
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
SUSPICIOUS
Executable content was dropped or overwritten
- EportClientSetup_V1.5.50.exe (PID: 2704)
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- TXRNSecurityCom.exe (PID: 3016)
- 02.base_driver.exe (PID: 3136)
- 02.base_driver.tmp (PID: 3976)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Drops a system driver (possible attempt to evade defenses)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
Creates/Modifies COM task schedule object
- EportClientSetup_V1.5.50.exe (PID: 2704)
- RegAsm.exe (PID: 3768)
- regsvr32.exe (PID: 2900)
- ActiveXRegGs.exe (PID: 2492)
Adds/modifies Windows certificates
- RegAsm.exe (PID: 3768)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Starts application with an unusual extension
- EportClientSetup_V1.5.50.exe (PID: 2704)
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- TXRNSecurityCom.exe (PID: 3016)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
Reads settings of System Certificates
- RegAsm.exe (PID: 3768)
- InstallUtil.exe (PID: 1840)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Checks Windows Trust Settings
- RegAsm.exe (PID: 3768)
- InstallUtil.exe (PID: 1840)
- drvinst.exe (PID: 3176)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Reads security settings of Internet Explorer
- InstallUtil.exe (PID: 1840)
- RegAsm.exe (PID: 3768)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
- SetAccessControl.exe (PID: 1280)
Process drops legitimate windows executable
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- 02.base_driver.tmp (PID: 3976)
Creates files in the driver directory
- drvinst.exe (PID: 3176)
Executes as Windows Service
- HGBOT.exe (PID: 4064)
- WDTokenServerHaiGuan.exe (PID: 3364)
- WDDrvRpr_Share.exe (PID: 3496)
- ServiceIoApi.exe (PID: 2700)
- CnEport.Pub.WinService.exe (PID: 748)
Malware-specific behavior (creating "System.dll" in Temp)
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- TXRNSecurityCom.exe (PID: 3016)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
The process creates files with name similar to system file names
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- TXRNSecurityCom.exe (PID: 3016)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Starts CMD.EXE for commands execution
- ns4125.tmp (PID: 3852)
- ns41A3.tmp (PID: 2000)
- ns42CB.tmp (PID: 4032)
- ns4349.tmp (PID: 2276)
- ns4464.tmp (PID: 2016)
- ns4994.tmp (PID: 680)
- ns4A71.tmp (PID: 2816)
- ns4AEF.tmp (PID: 3812)
- ns4BDC.tmp (PID: 2352)
- ns4A03.tmp (PID: 2324)
Starts SC.EXE for service management
- cmd.exe (PID: 3936)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 2444)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3628)
- ns4D70.tmp (PID: 2604)
- ns5113.tmp (PID: 3896)
- ns8F93.tmp (PID: 936)
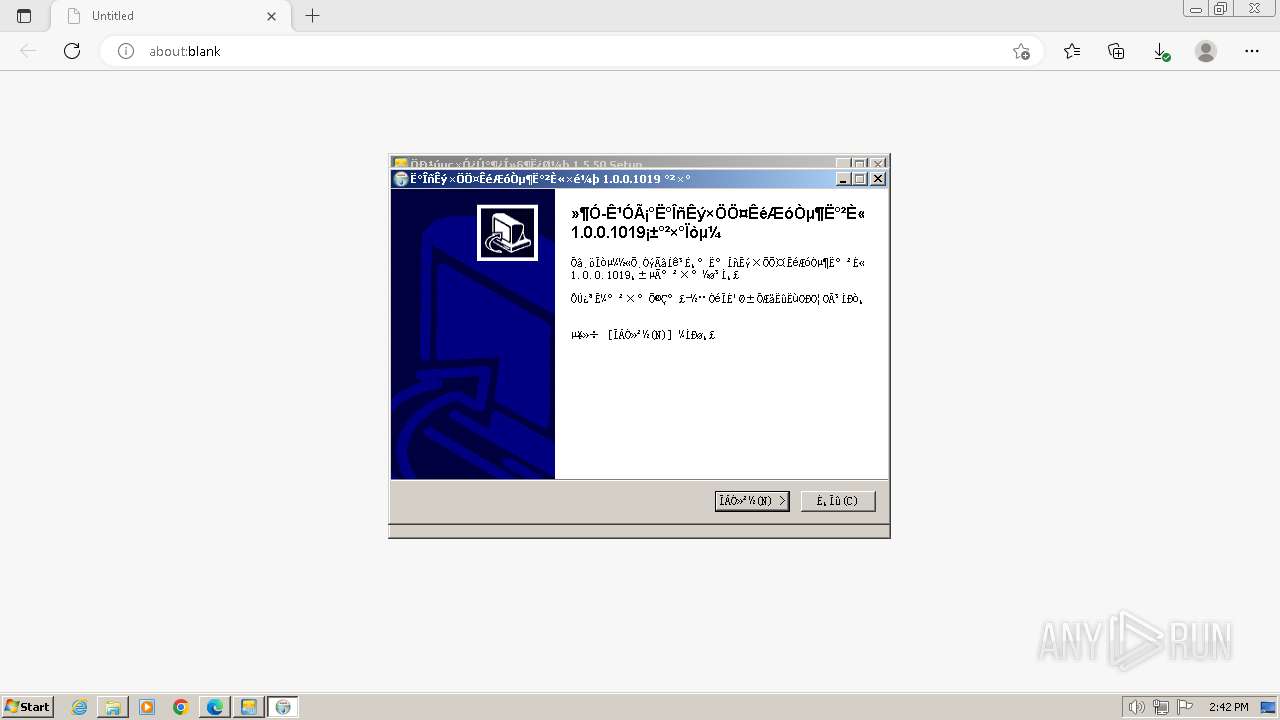
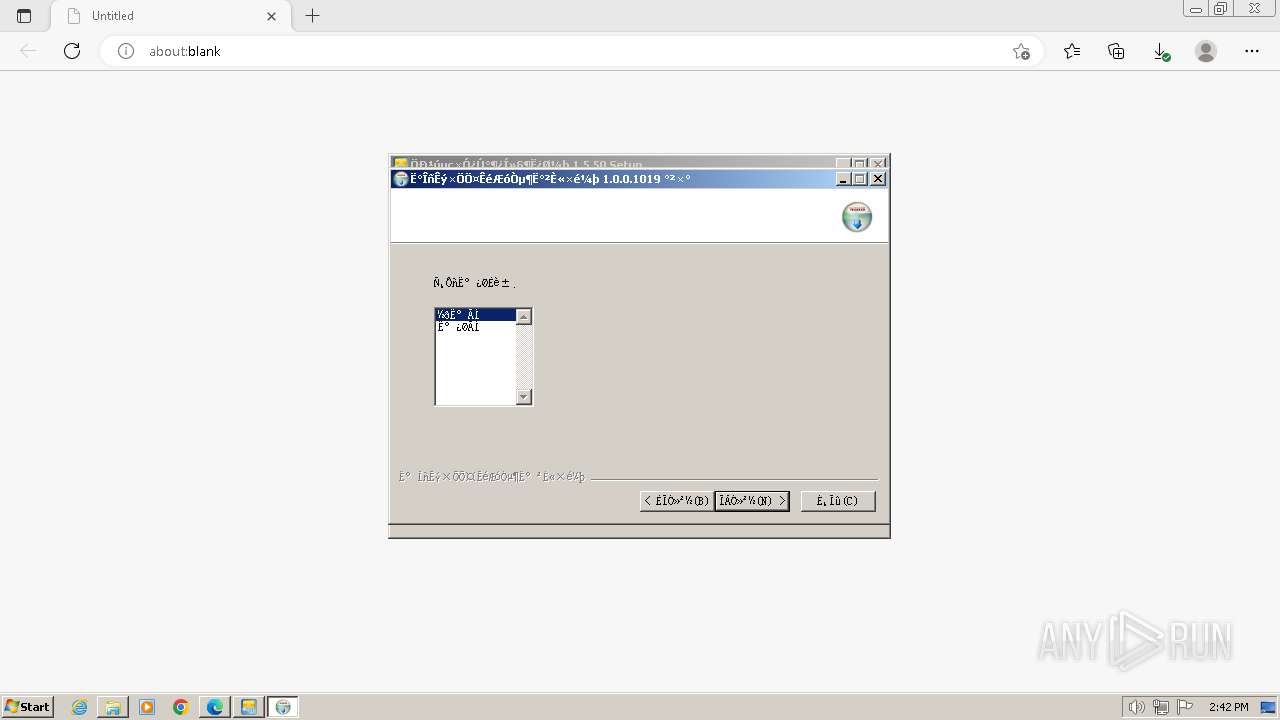
Creates a software uninstall entry
- WDDriverR.exe (PID: 3132)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
- EportClientSetup_V1.5.50.exe (PID: 2704)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 624)
Uses powercfg.exe to modify the power settings
- ns4FB5.tmp (PID: 2264)
Reads the Windows owner or organization settings
- 02.base_driver.tmp (PID: 3976)
Mutex name with non-standard characters
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
Reads the Internet Settings
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Uses REG/REGEDIT.EXE to modify registry
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
There is functionality for taking screenshot (YARA)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Uses RUNDLL32.EXE to load library
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
INFO
Drops the executable file immediately after the start
- msedge.exe (PID: 3344)
- msedge.exe (PID: 2944)
Reads the computer name
- wmpnscfg.exe (PID: 2900)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- RegAsm.exe (PID: 3768)
- InstallUtil.exe (PID: 1840)
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- HGBOT.exe (PID: 1828)
- HGBOT.exe (PID: 4064)
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- WDTokenServerHaiGuan.exe (PID: 2068)
- WDTokenServerHaiGuan.exe (PID: 3364)
- WDDrvRpr_Share.exe (PID: 2708)
- WDDrvRpr_Share.exe (PID: 3496)
- HDZB_USBKEY_2G_CEP_DevServer.exe (PID: 1836)
- TXRNSecurityCom.exe (PID: 3016)
- 02.base_driver.tmp (PID: 3976)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ServiceIoApi.exe (PID: 2120)
- ServiceIoApi.exe (PID: 2700)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
- GFA_certd3003.exe (PID: 2412)
Application launched itself
- msedge.exe (PID: 3344)
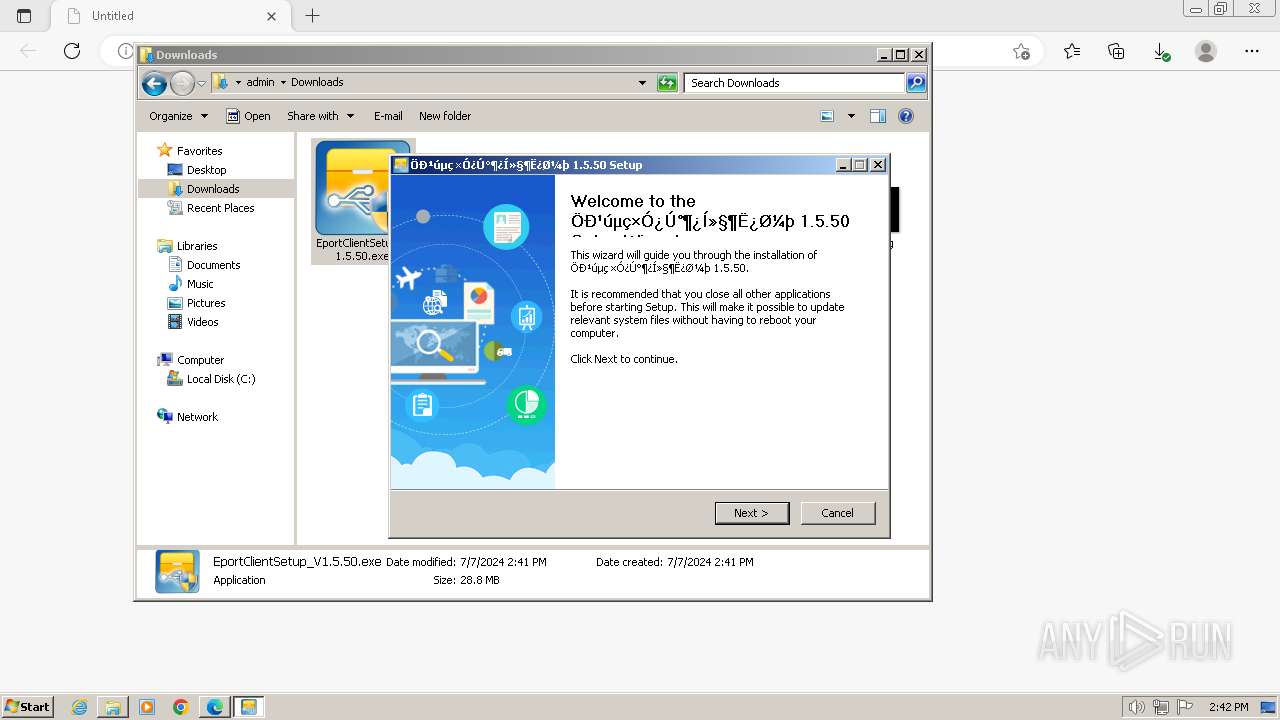
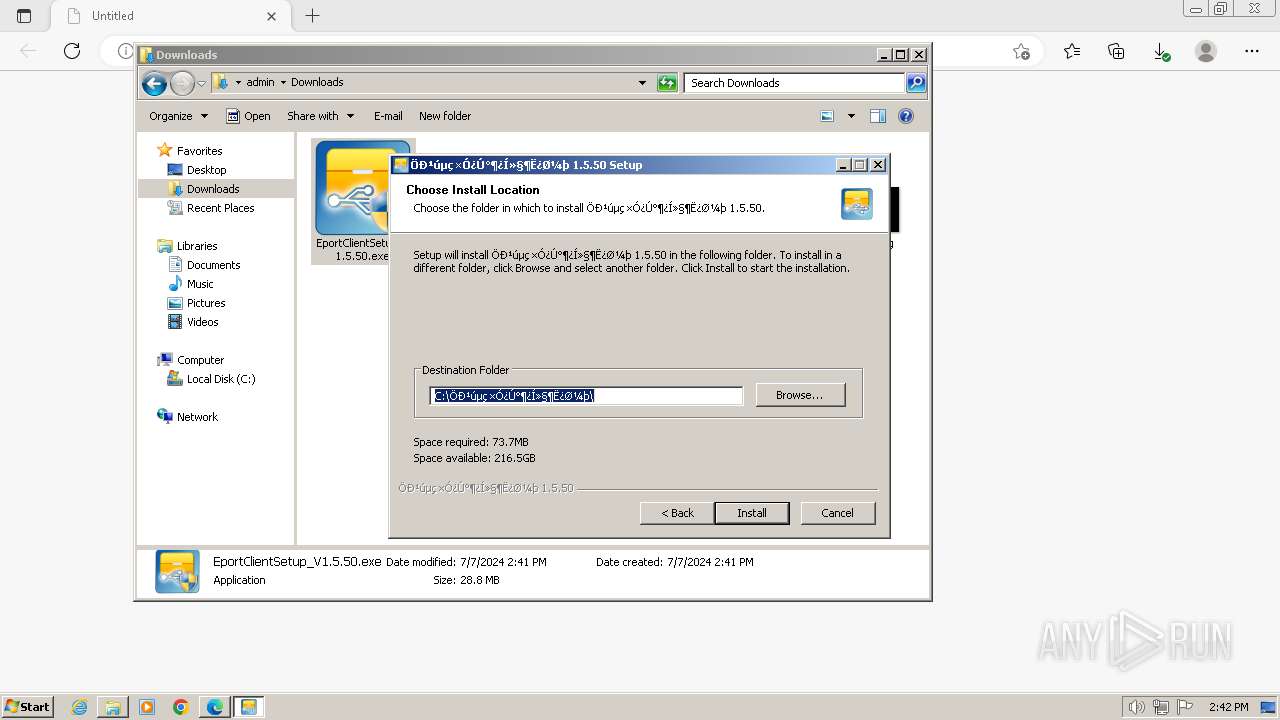
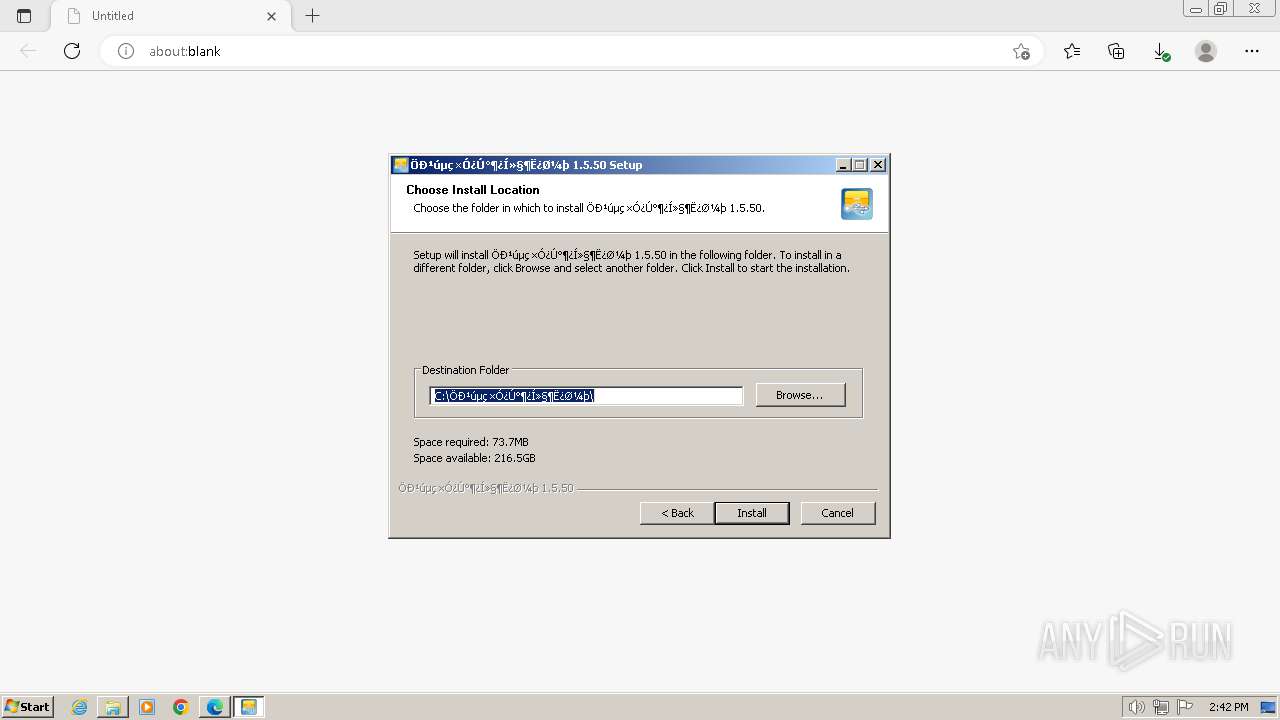
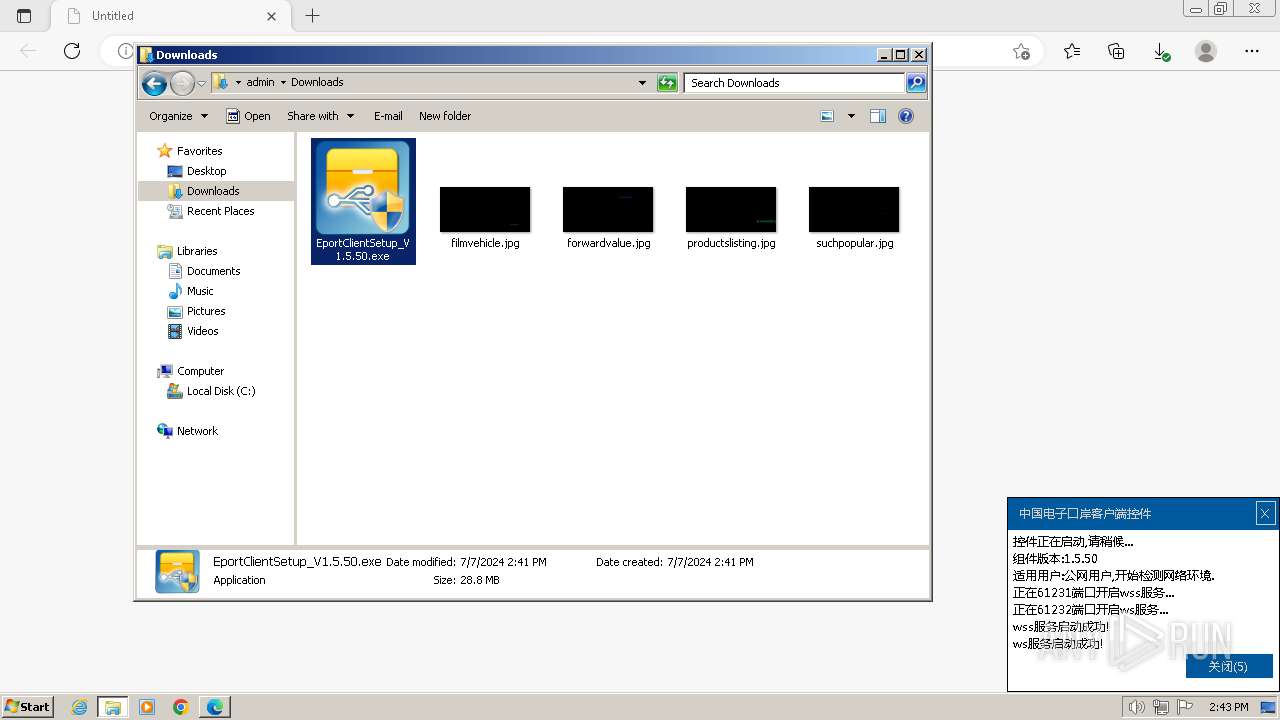
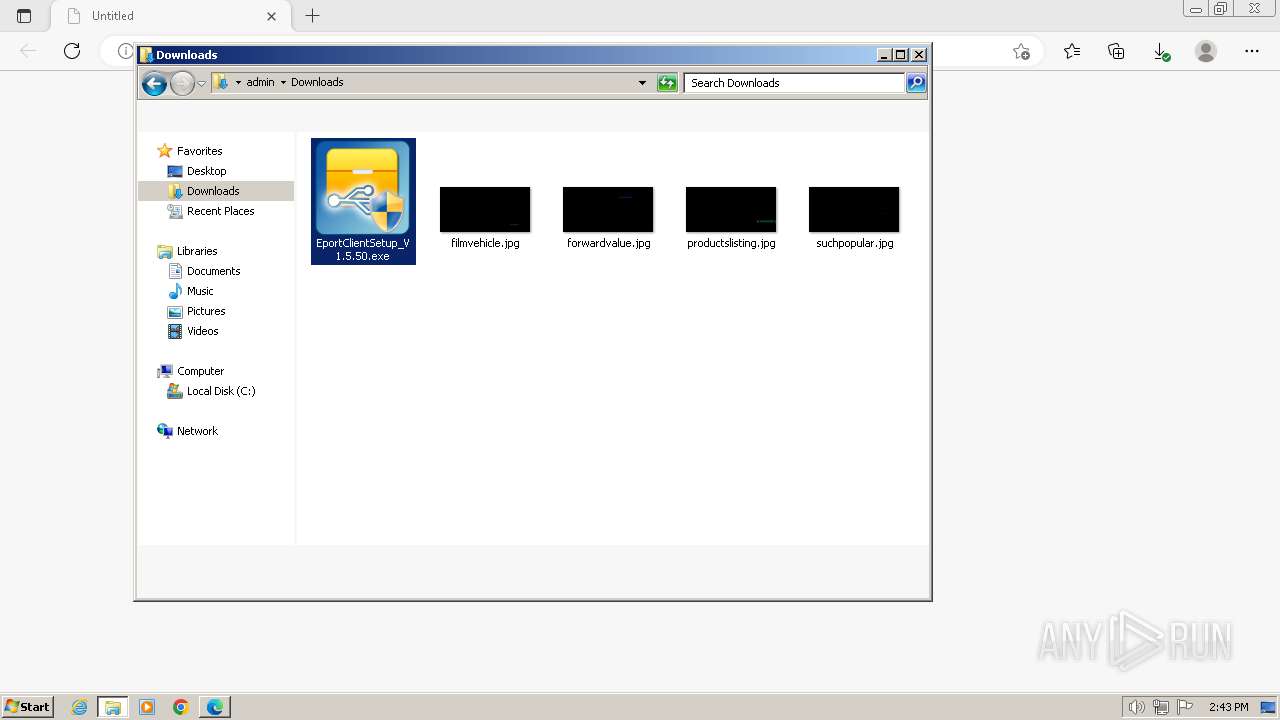
Manual execution by a user
- wmpnscfg.exe (PID: 2900)
- explorer.exe (PID: 3140)
- EportClientSetup_V1.5.50.exe (PID: 832)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- GFA_certd3003.exe (PID: 2412)
Checks supported languages
- wmpnscfg.exe (PID: 2900)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- ns3406.tmp (PID: 2988)
- RegAsm.exe (PID: 3768)
- InstallUtil.exe (PID: 1840)
- ns3772.tmp (PID: 3752)
- DPInst32.exe (PID: 3352)
- ns3A70.tmp (PID: 3708)
- drvinst.exe (PID: 3176)
- HGBOT.exe (PID: 1828)
- ns3FA2.tmp (PID: 2500)
- HGBOT.exe (PID: 4064)
- WDDriverR.exe (PID: 3132)
- ns4020.tmp (PID: 2740)
- ns4125.tmp (PID: 3852)
- ns41A3.tmp (PID: 2000)
- WDTokenServerSetup.exe (PID: 4008)
- ns43F6.tmp (PID: 3616)
- WDTokenServerHaiGuan.exe (PID: 2068)
- ns4464.tmp (PID: 2016)
- WDTokenServerHaiGuan.exe (PID: 3364)
- ns4916.tmp (PID: 2540)
- registCCID.exe (PID: 3684)
- ns4994.tmp (PID: 680)
- ns4A03.tmp (PID: 2324)
- ns4AEF.tmp (PID: 3812)
- ns4A71.tmp (PID: 2816)
- WDDrvRpr_Share.exe (PID: 2708)
- ns4B5E.tmp (PID: 1132)
- ns4BDC.tmp (PID: 2352)
- WDDrvRpr_Share.exe (PID: 3496)
- HDZB_USBKEY_2G_CEP_DevServer.exe (PID: 1836)
- ns4D70.tmp (PID: 2604)
- ns4DDE.tmp (PID: 148)
- TXRNSecurityCom.exe (PID: 3016)
- ns4E5C.tmp (PID: 1388)
- ns4FB5.tmp (PID: 2264)
- ns5095.tmp (PID: 1944)
- ns4349.tmp (PID: 2276)
- ns42CB.tmp (PID: 4032)
- ns4D01.tmp (PID: 2368)
- ns5113.tmp (PID: 3896)
- 02.base_driver.exe (PID: 3136)
- 02.base_driver.tmp (PID: 3976)
- ActiveXRegGs.exe (PID: 2492)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ns8F15.tmp (PID: 3708)
- ns8F93.tmp (PID: 936)
- ServiceIoApi.exe (PID: 2120)
- ns9205.tmp (PID: 3328)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- ServiceIoApi.exe (PID: 2700)
- nsAB24.tmp (PID: 3608)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
- nsB0C3.tmp (PID: 1036)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
- GFA_certd3003.exe (PID: 2412)
Executable content was dropped or overwritten
- msedge.exe (PID: 3344)
- msedge.exe (PID: 2944)
The process uses the downloaded file
- msedge.exe (PID: 2308)
Create files in a temporary directory
- EportClientSetup_V1.5.50.exe (PID: 2704)
- DPInst32.exe (PID: 3352)
- WDDriverR.exe (PID: 3132)
- WDTokenServerSetup.exe (PID: 4008)
- TXRNSecurityCom.exe (PID: 3016)
- 02.base_driver.exe (PID: 3136)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- 02.base_driver.tmp (PID: 3976)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 3768)
- EportClientSetup_V1.5.50.exe (PID: 2704)
- InstallUtil.exe (PID: 1840)
- DPInst32.exe (PID: 3352)
- drvinst.exe (PID: 3176)
- WDDriverR.exe (PID: 3132)
- TXRNSecurityCom.exe (PID: 3016)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- ServiceIoApi.exe (PID: 2700)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Reads the software policy settings
- RegAsm.exe (PID: 3768)
- InstallUtil.exe (PID: 1840)
- drvinst.exe (PID: 3176)
- SetAccessControl.exe (PID: 1280)
- CnEport.Pub.WinService.exe (PID: 748)
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Creates files or folders in the user directory
- TXRNSecurityCom.exe (PID: 3016)
- EportClientSetup_V1.5.50.exe (PID: 2704)
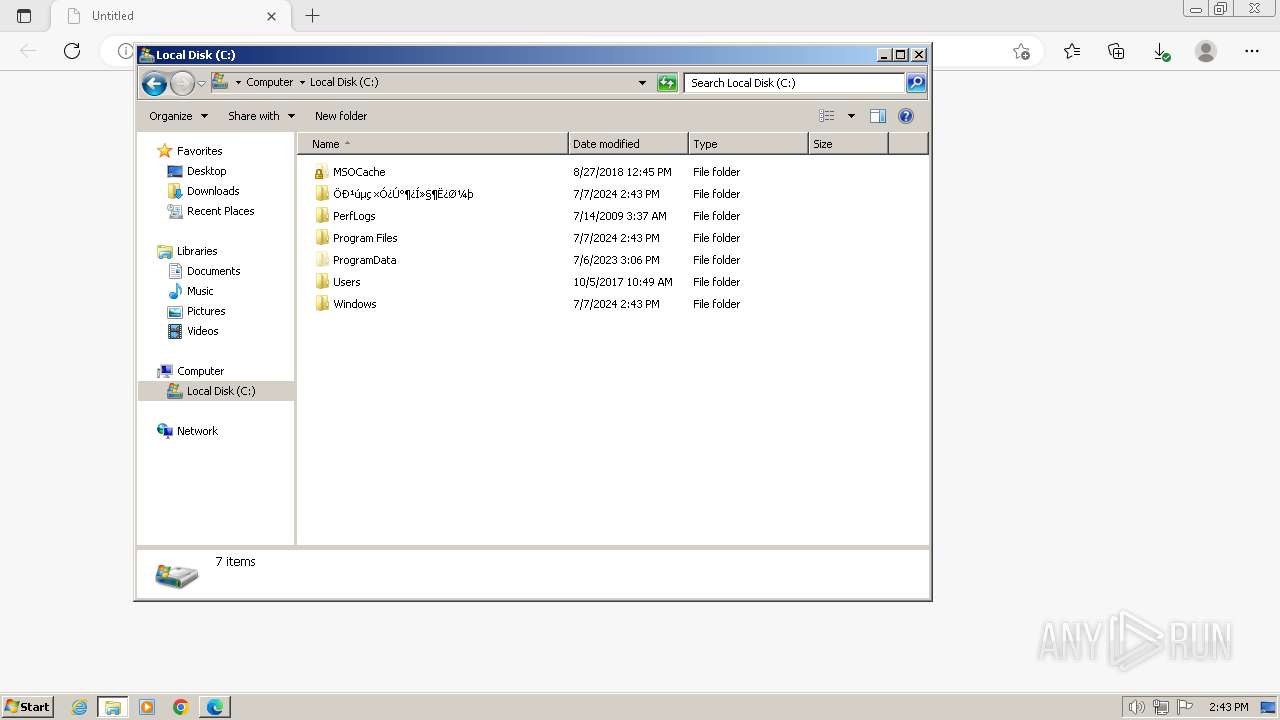
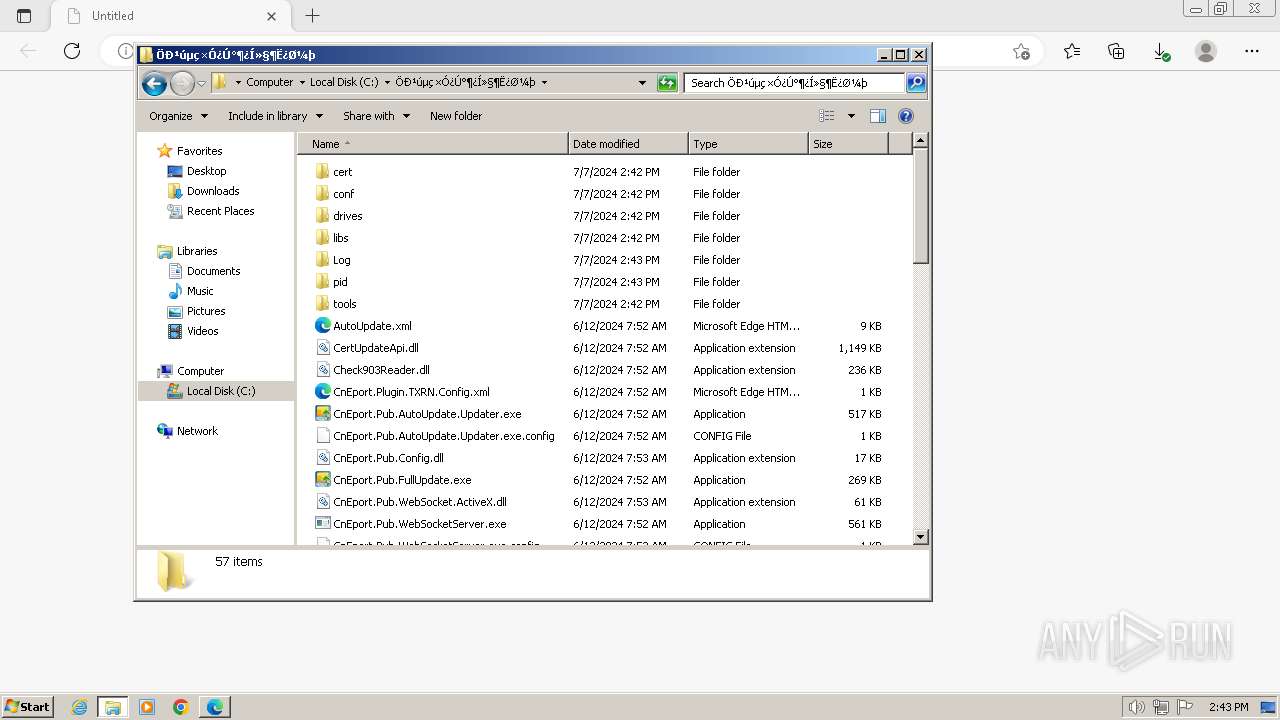
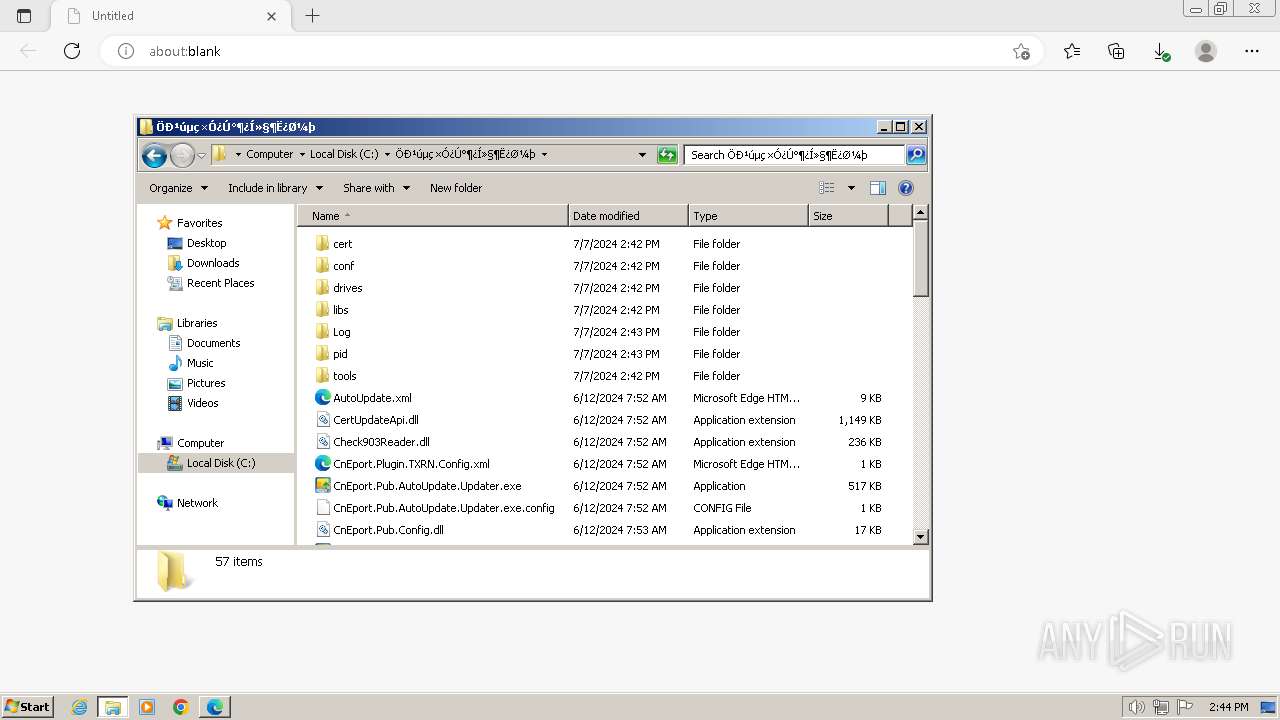
Creates files in the program directory
- TXRNSecurityCom.exe (PID: 3016)
- 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe (PID: 3388)
- ePass3003_SimpChinese_gfa.exe (PID: 1820)
Creates a software uninstall entry
- 02.base_driver.tmp (PID: 3976)
Reads Environment values
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Disables trace logs
- CnEport.Pub.WebSocketServer.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
189
Monitored processes
111
Malicious processes
18
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Users\admin\AppData\Local\Temp\nss9544.tmp\ns4DDE.tmp" schtasks.exe /Delete /tn CnEportClientComponent /F | C:\Users\admin\AppData\Local\Temp\nss9544.tmp\ns4DDE.tmp | — | EportClientSetup_V1.5.50.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 624 | schtasks.exe /Delete /tn CnEportClientComponent /F | C:\Windows\System32\schtasks.exe | — | ns4DDE.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\nsv4069.tmp\ns4994.tmp" cmd.exe /c sc config SCardSvr start= auto | C:\Users\admin\AppData\Local\Temp\nsv4069.tmp\ns4994.tmp | — | WDDriverR.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2236 --field-trial-handle=1300,i,6948227265991936742,8421750198859435237,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 748 | "C:\Öйúµç×Ó¿Ú°¶¿Í»§¶Ë¿Ø¼þ\CnEport.Pub.WinService.exe" | C:\Öйúµç×Ó¿Ú°¶¿Í»§¶Ë¿Ø¼þ\CnEport.Pub.WinService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Eport Soft Integrity Level: SYSTEM Description: CnEport.Pub.WinService assembly Version: 2.0.17179.1607 Modules
| |||||||||||||||
| 832 | "C:\Users\admin\Downloads\EportClientSetup_V1.5.50.exe" | C:\Users\admin\Downloads\EportClientSetup_V1.5.50.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 880 | net start "ServiceIoApi" | C:\Windows\System32\net.exe | — | ns9205.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | "C:\Users\admin\AppData\Local\Temp\nsg8EF5.tmp\ns8F93.tmp" sc delete ServiceIoApi | C:\Users\admin\AppData\Local\Temp\nsg8EF5.tmp\ns8F93.tmp | — | 03.½ð±¨Ë°ÅÌË°ÎñÊý×ÖÖ¤ÊéÇý¶¯1.1.1.12.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1060 Modules
| |||||||||||||||
| 1000 | C:\Windows\system32\rundll32.exe "C:\Windows\system32\GFACSP11.dll",eb_RunNoElevated "C:\Program Files\EnterSafe\ePass3003_GFA\GFA_certd3003.exe" | C:\Windows\System32\rundll32.exe | — | ePass3003_SimpChinese_gfa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Local\Temp\nss9544.tmp\nsB0C3.tmp" "C:\Öйúµç×Ó¿Ú°¶¿Í»§¶Ë¿Ø¼þ\drives\ePass3003_SimpChinese_gfa.exe" /S | C:\Users\admin\AppData\Local\Temp\nss9544.tmp\nsB0C3.tmp | — | EportClientSetup_V1.5.50.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
63 463
Read events
62 109
Write events
1 314
Delete events
40
Modification events
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 9B9D08BC3E7B2F00 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
234
Suspicious files
132
Text files
83
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4e2da.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e2fa.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e309.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4e338.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
| 3416 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
748 | CnEport.Pub.WinService.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAj0a%2FGVPO1IO7x66TQNez8%3D | unknown | — | — | unknown |
748 | CnEport.Pub.WinService.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3344 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2944 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2944 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2944 | msedge.exe | 14.29.101.169:443 | update.singlewindow.cn | Chinanet | CN | unknown |
3344 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.singlewindow.cn |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |