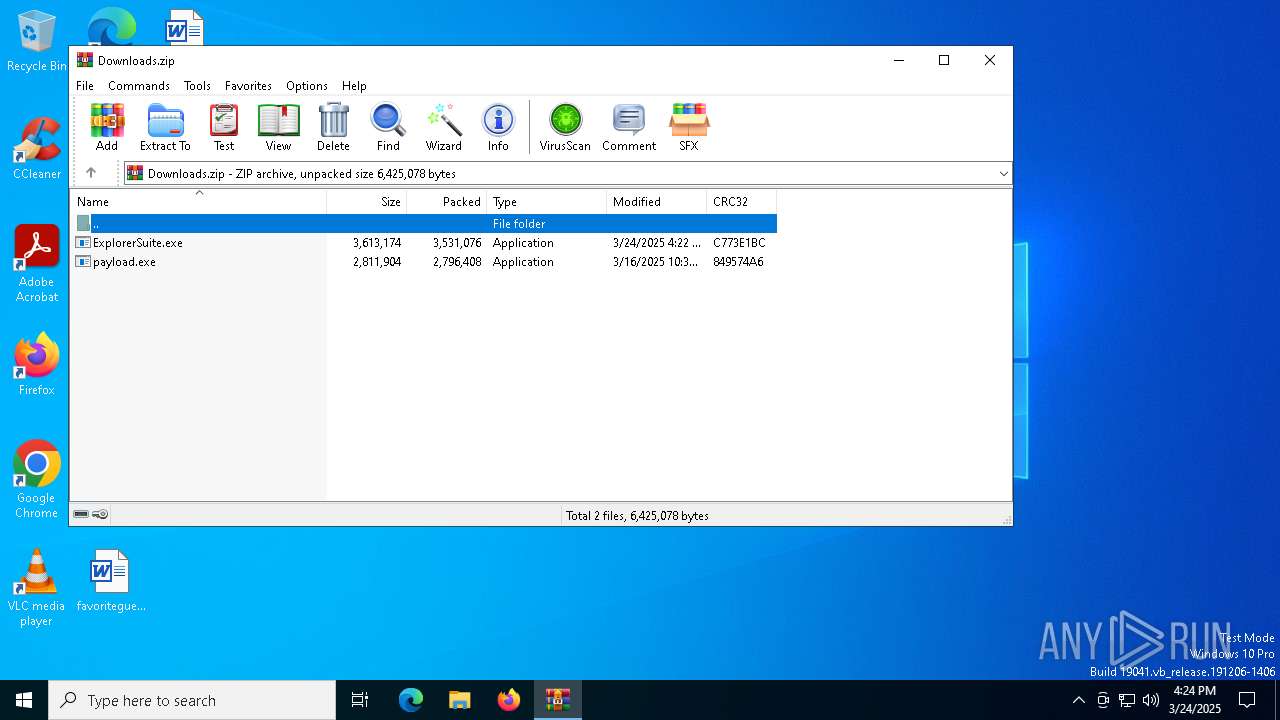
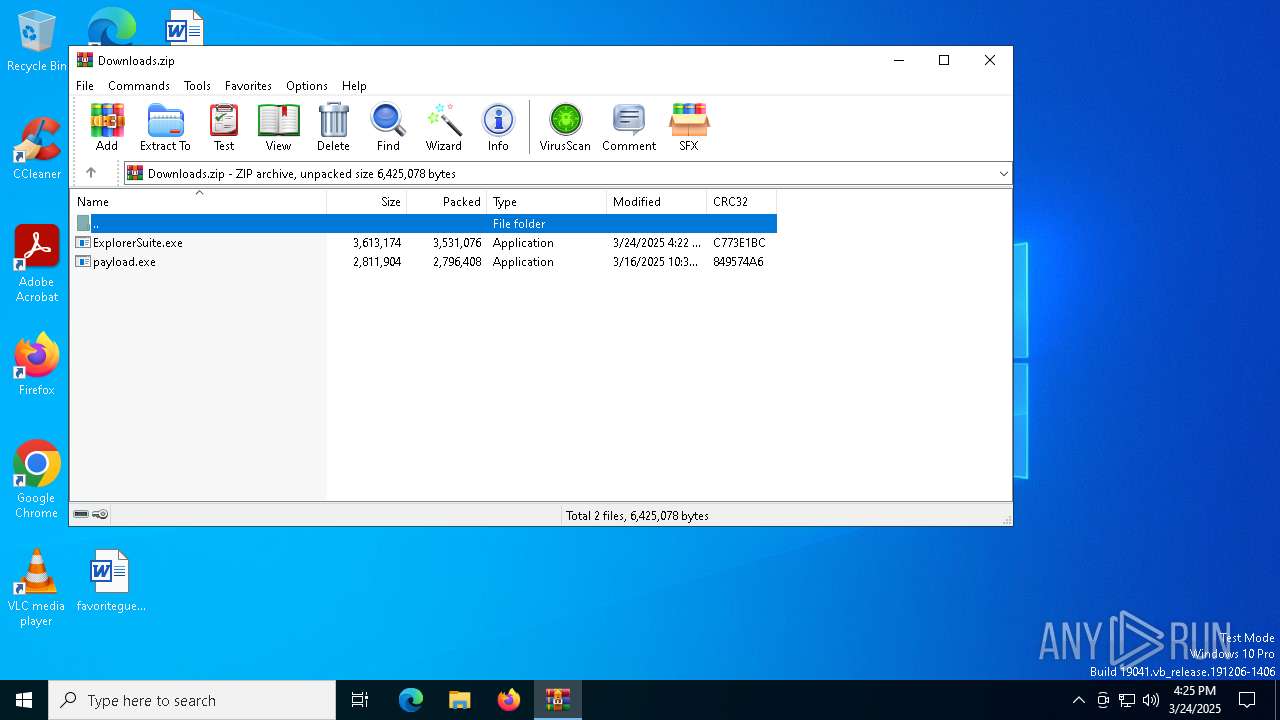
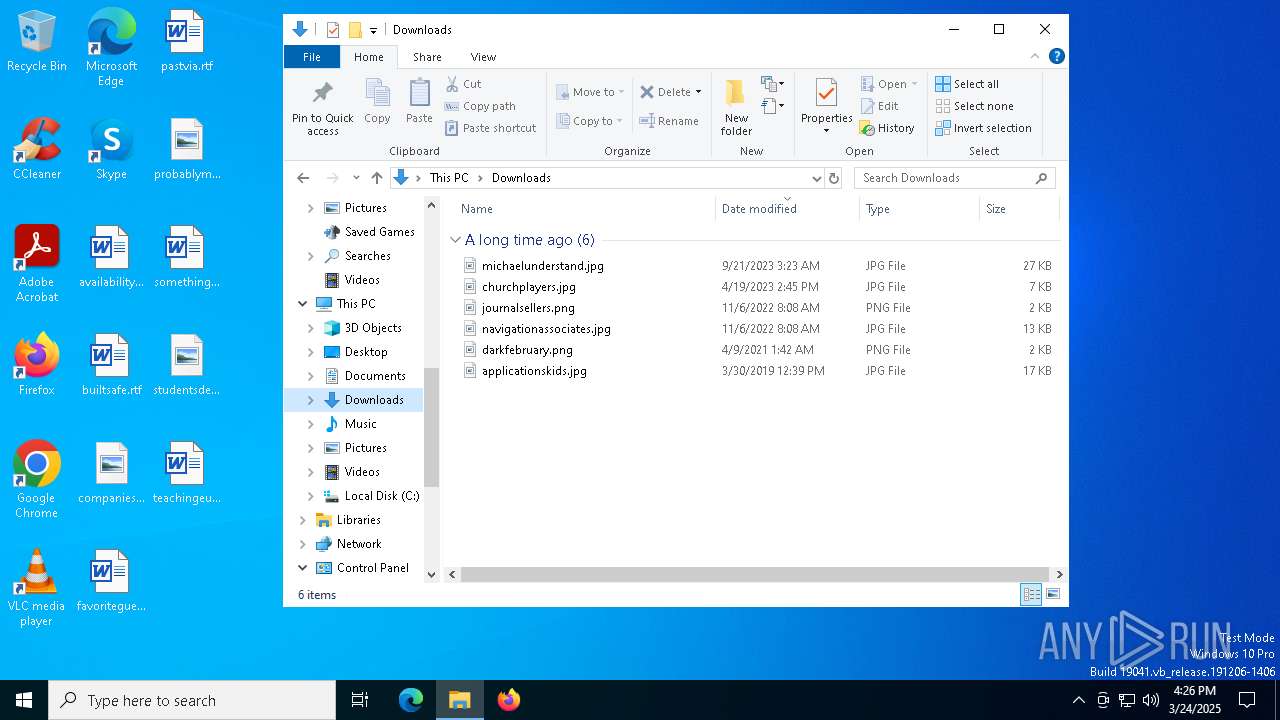
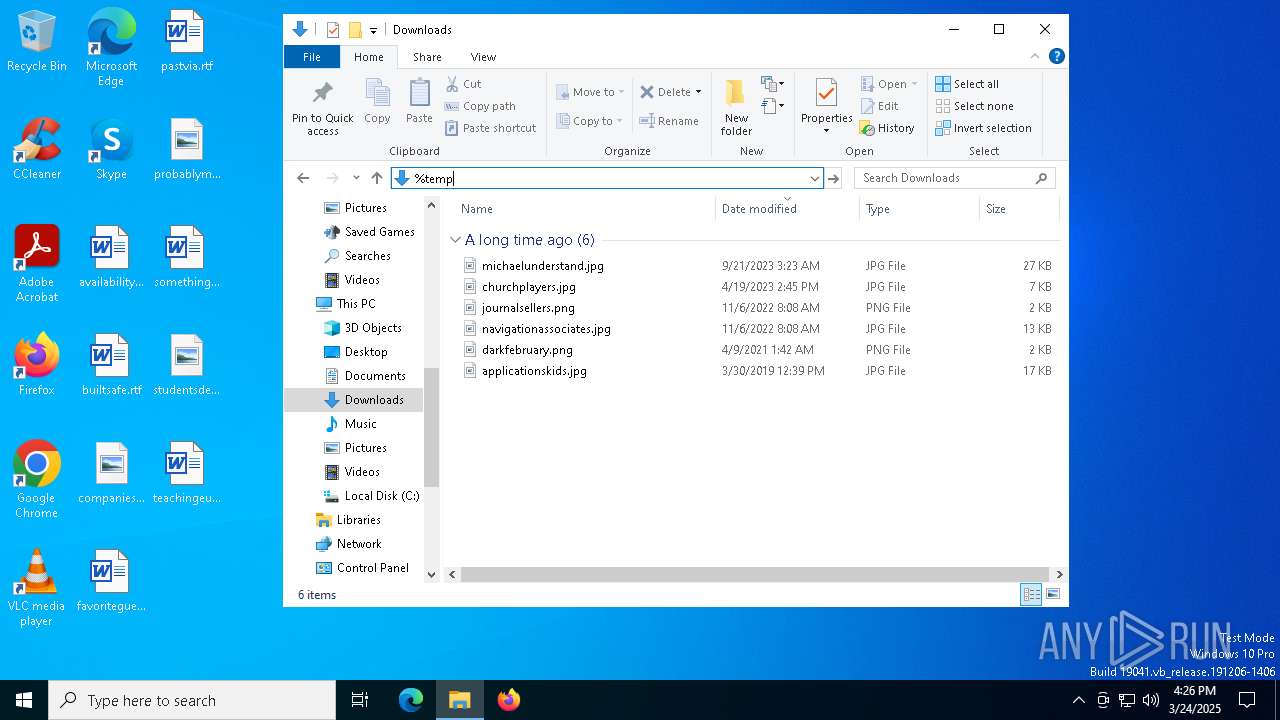
| File name: | Downloads.zip |
| Full analysis: | https://app.any.run/tasks/c7c8dc22-b2d0-49ca-b4dd-0fbf26168b64 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 16:24:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E036AC5E81A0B873E3A1C30CF8558077 |
| SHA1: | 842C62B9167EF14C106B10DE702FF11469ECE80E |
| SHA256: | 15C4A10D55248C6A6A83E80748F3B05846213E3E4673B0EAF8F76944319AAF2F |
| SSDEEP: | 98304:f3/5komYSpjBEbCbyoFbUctH7fVH4iwCQL63G3TQsCtj2KoYC+b426/fmywFpe7/:1EHQGFIL54rU/ObNM |
MALICIOUS
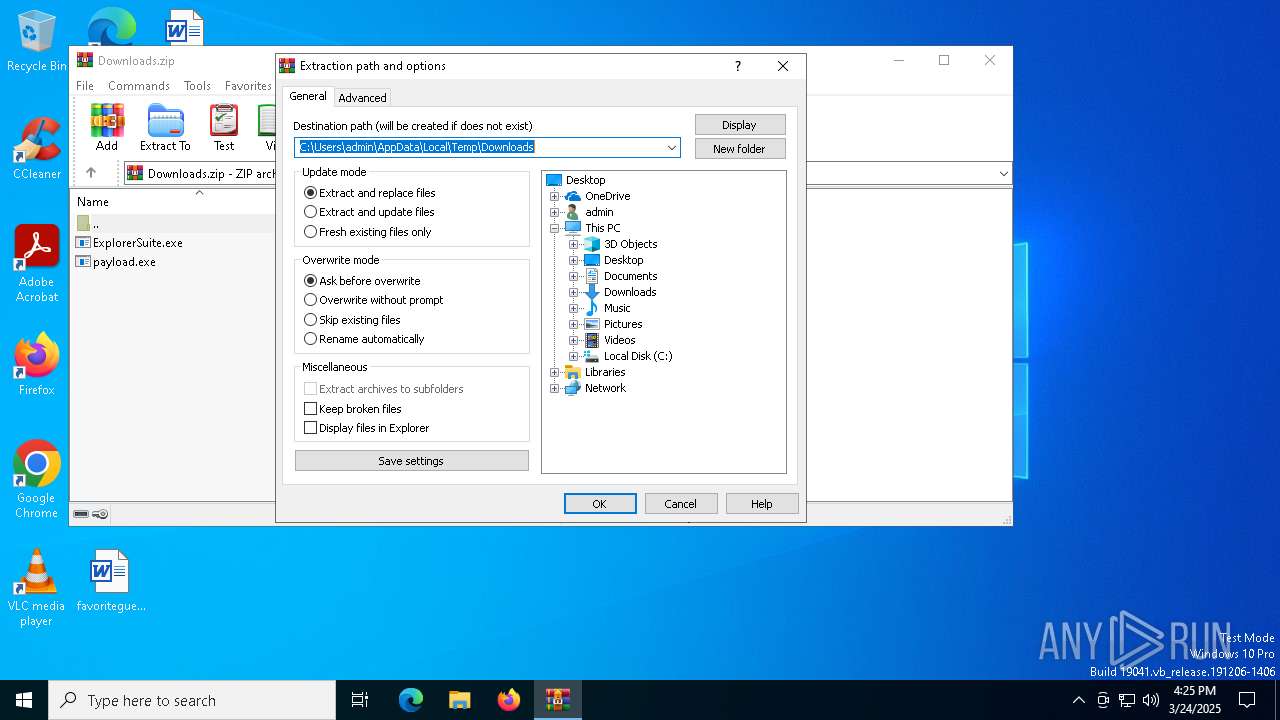
Generic archive extractor
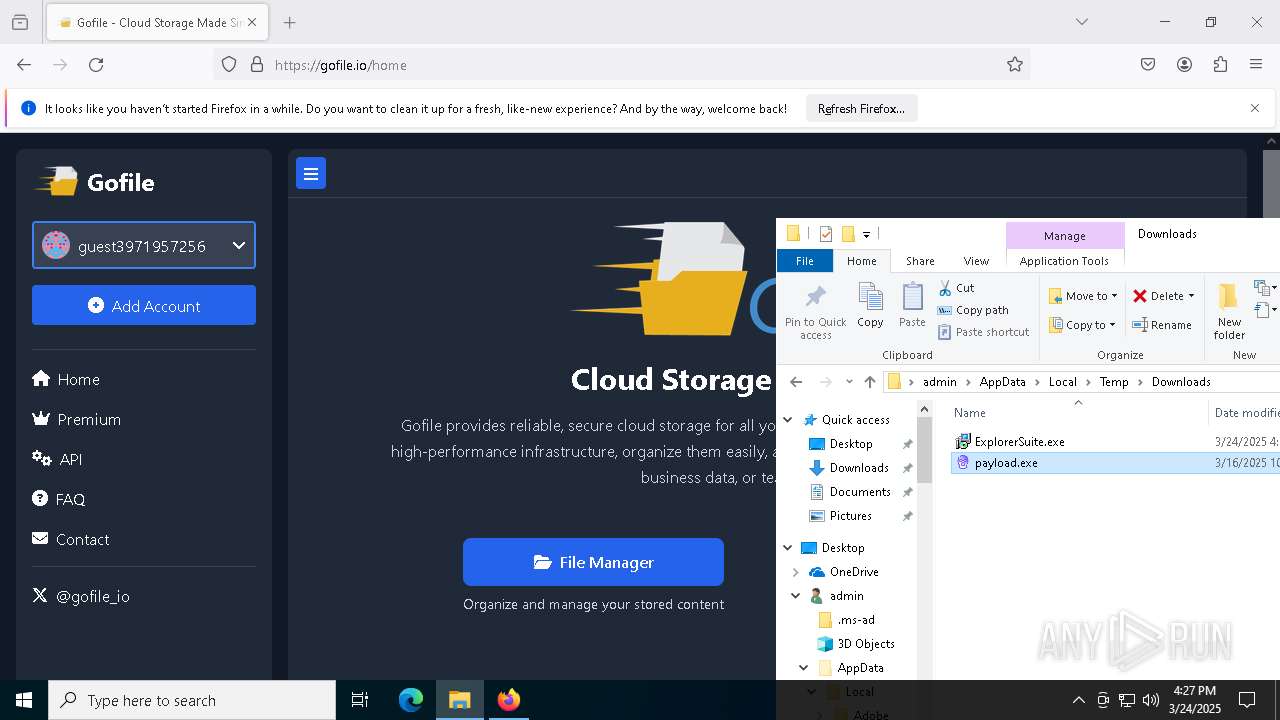
- WinRAR.exe (PID: 7352)
SUSPICIOUS
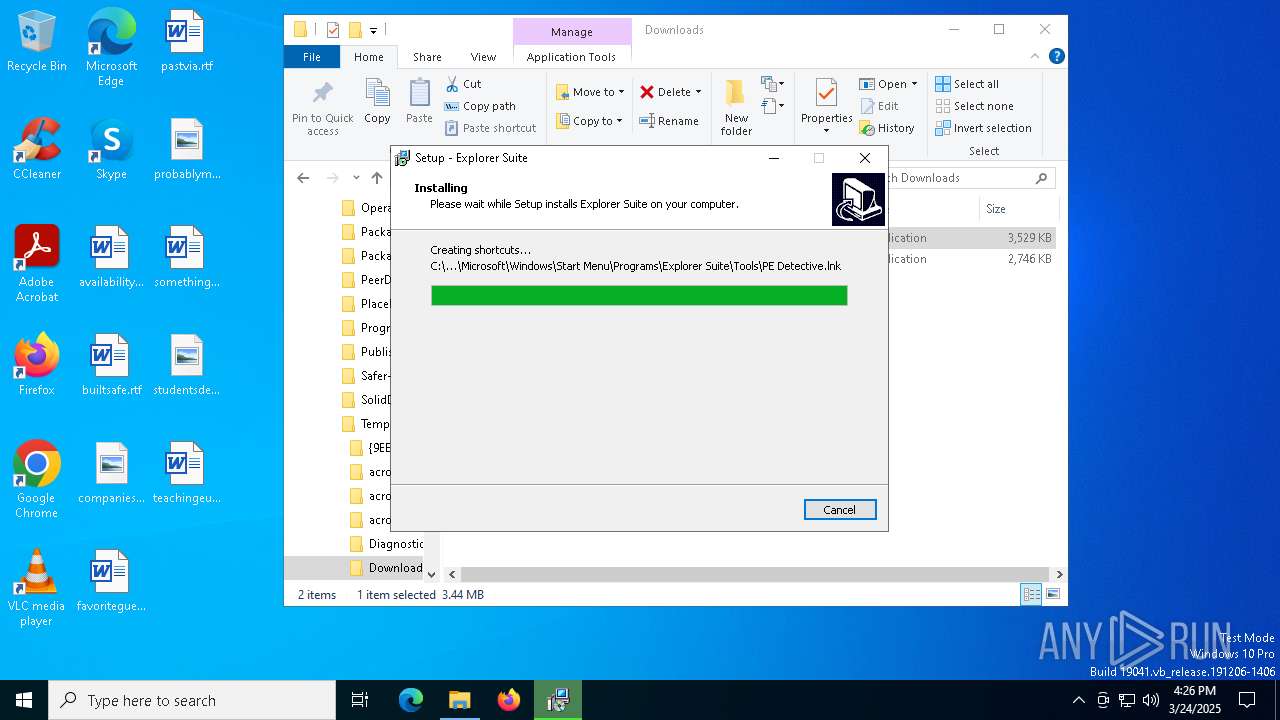
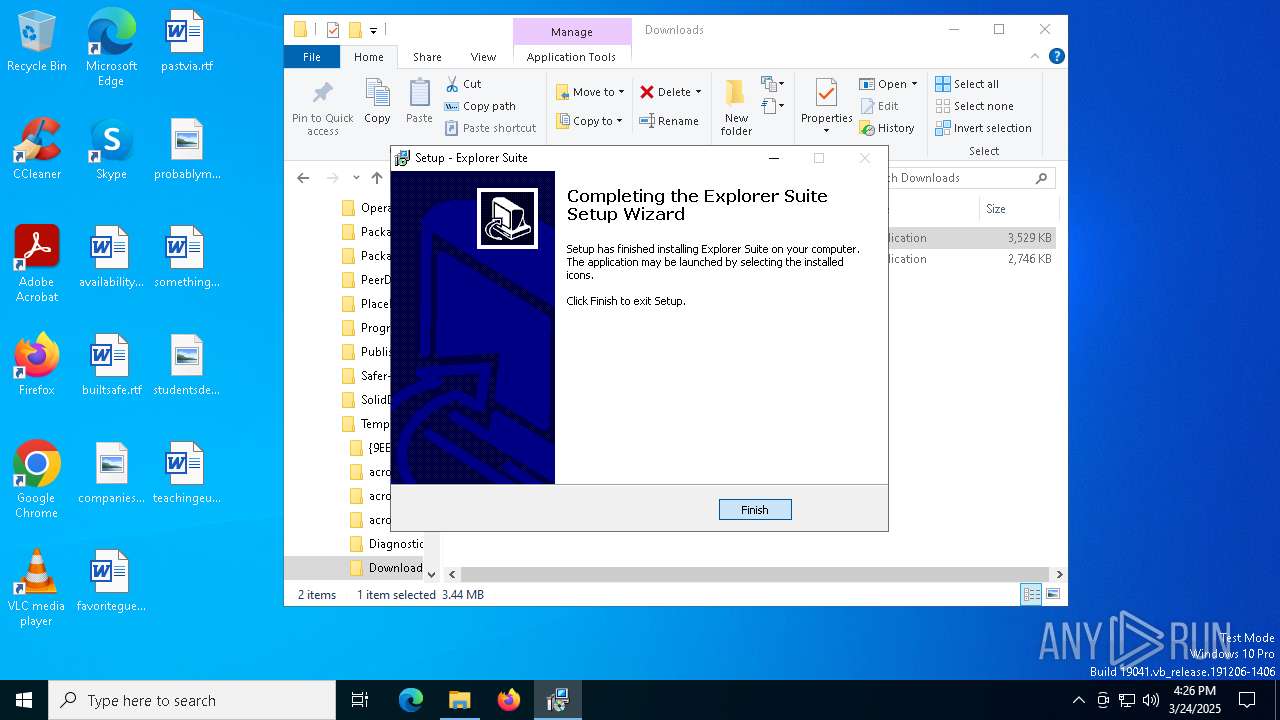
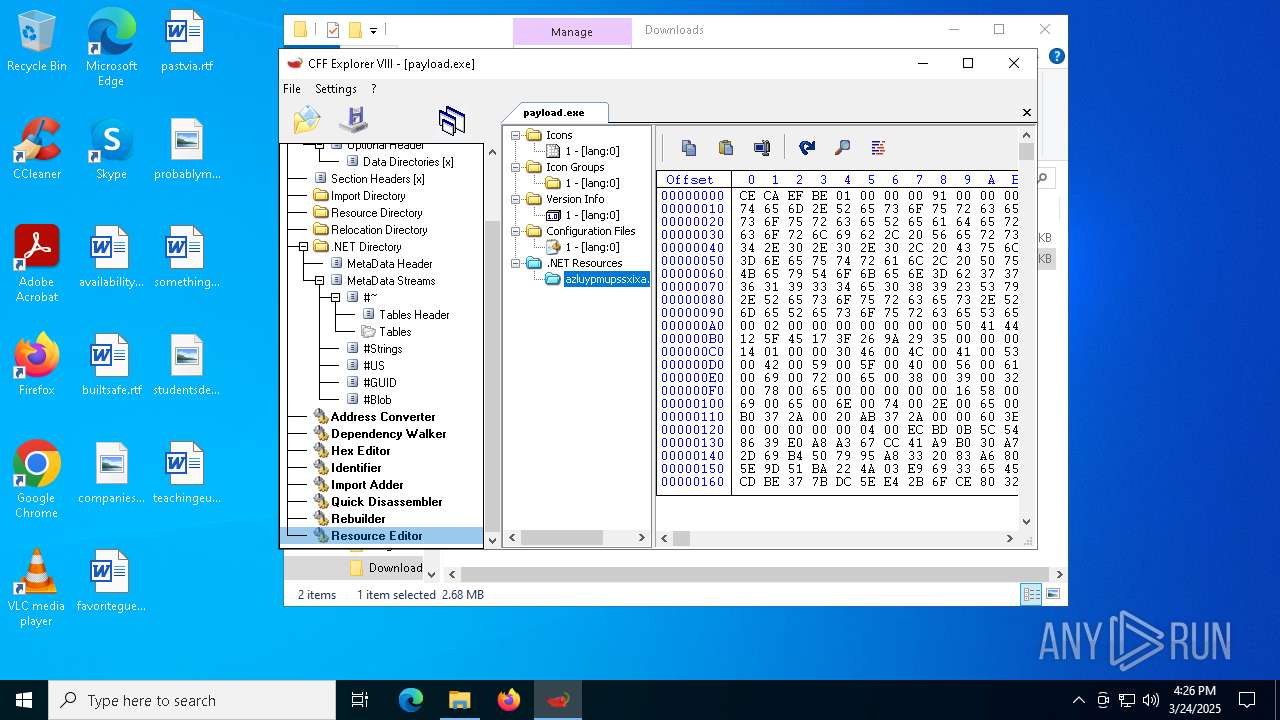
Executable content was dropped or overwritten
- ExplorerSuite.exe (PID: 4880)
- ExplorerSuite.exe (PID: 2096)
- ExplorerSuite.tmp (PID: 4448)
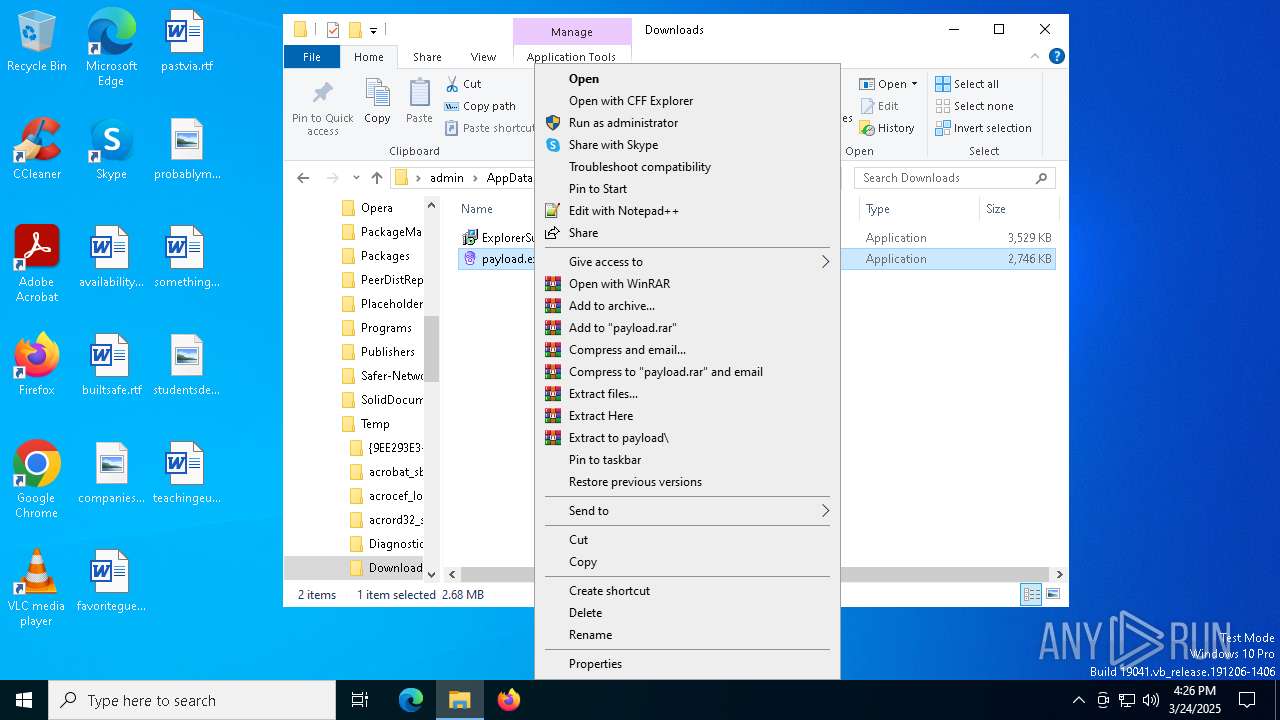
Reads security settings of Internet Explorer
- ExplorerSuite.tmp (PID: 2140)
- CFF Explorer.exe (PID: 4696)
Process drops legitimate windows executable
- ExplorerSuite.tmp (PID: 4448)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8092)
- BackgroundTransferHost.exe (PID: 7248)
- BackgroundTransferHost.exe (PID: 3884)
- BackgroundTransferHost.exe (PID: 7664)
- BackgroundTransferHost.exe (PID: 1164)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7248)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7248)
- slui.exe (PID: 7912)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7248)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7352)
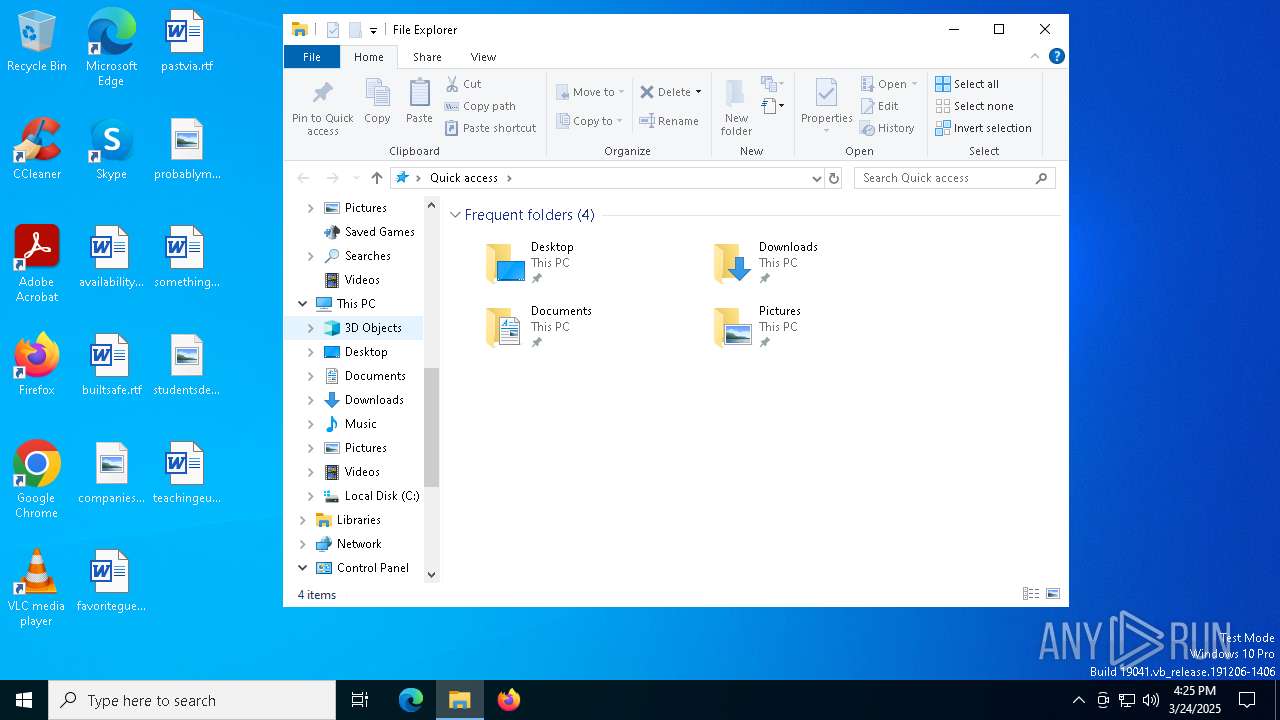
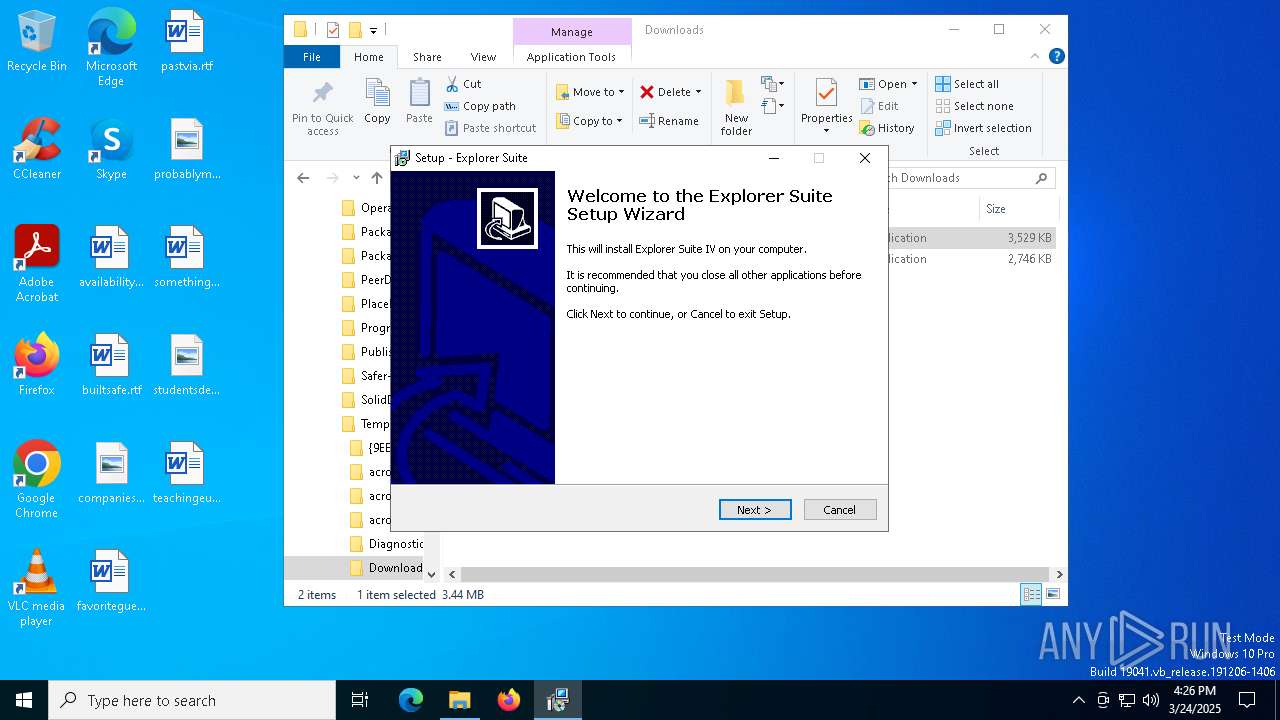
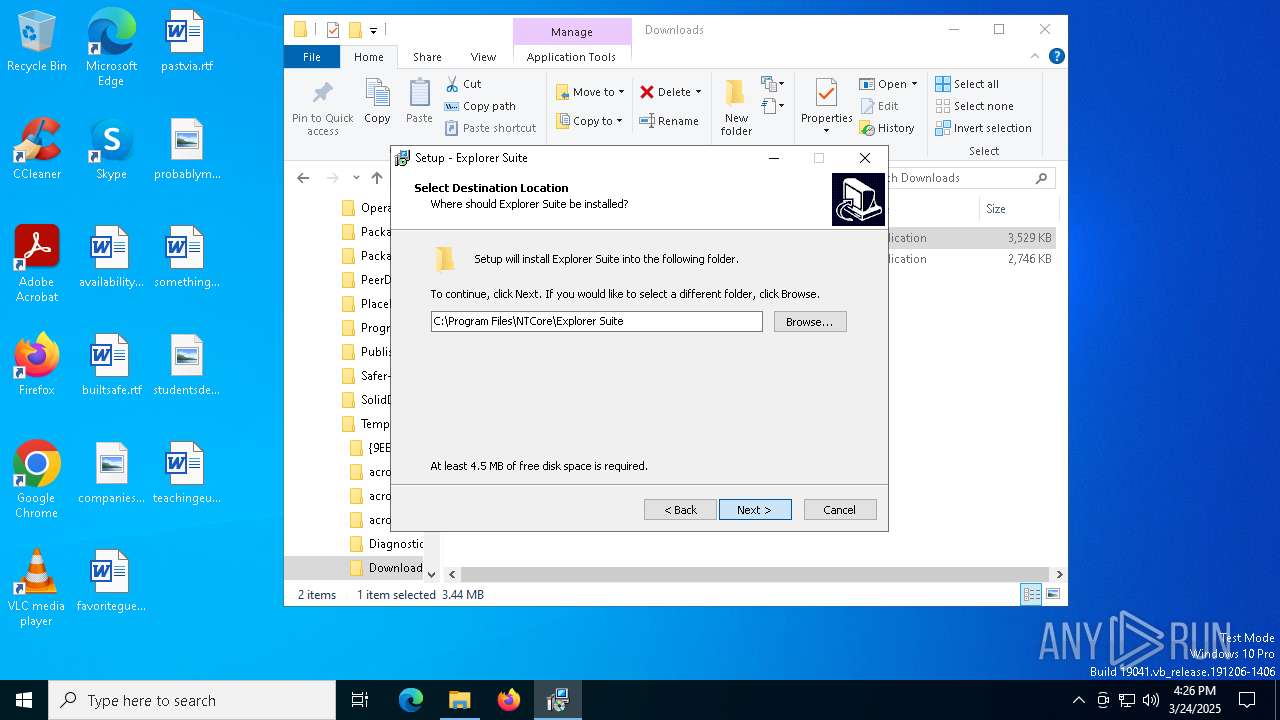
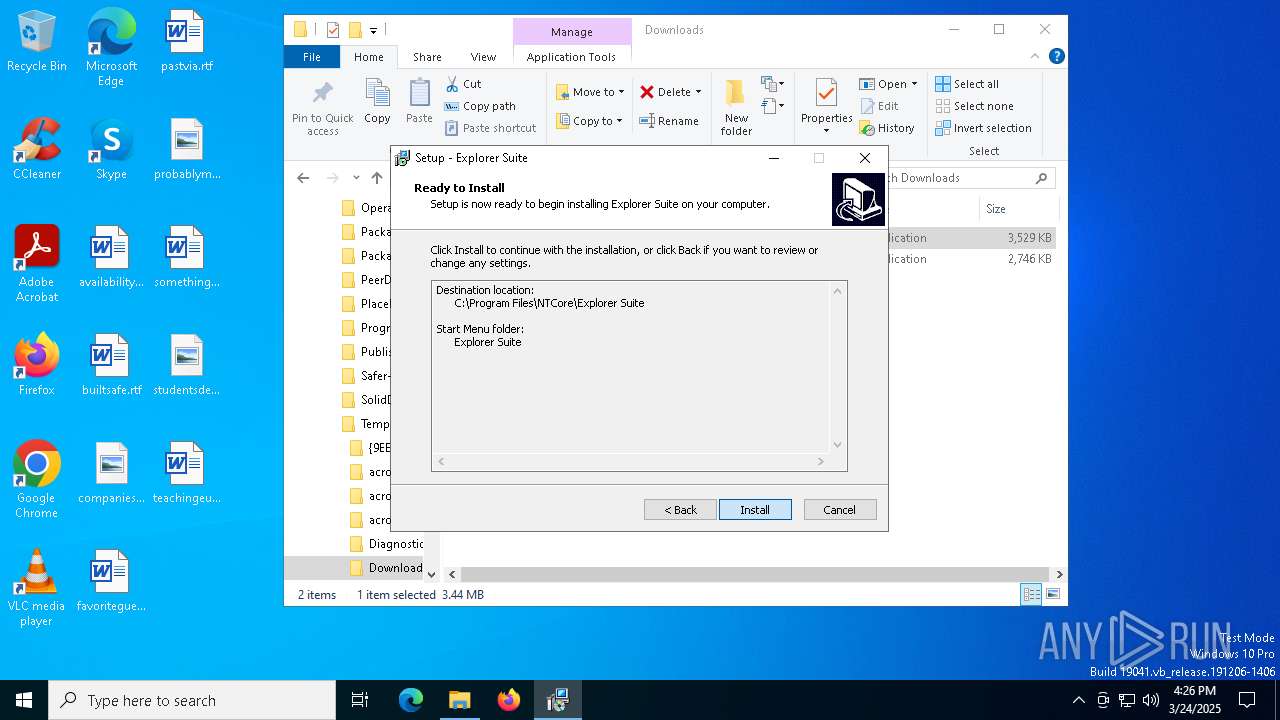
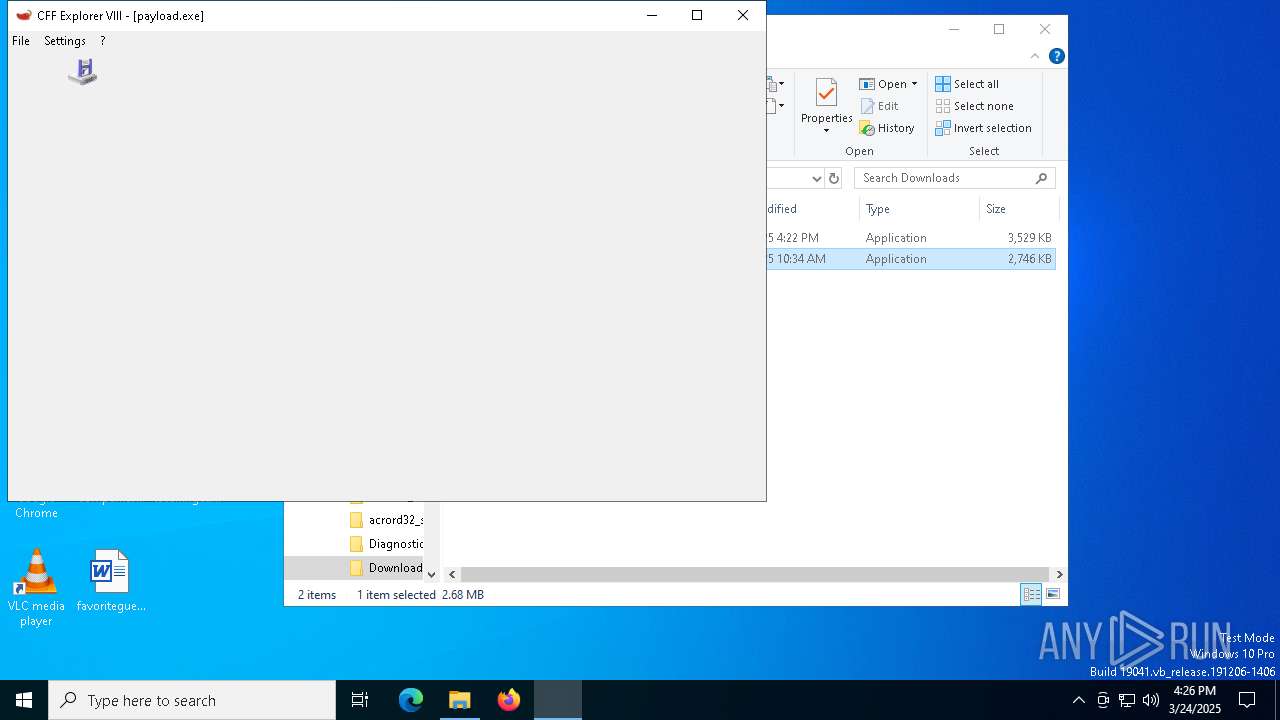
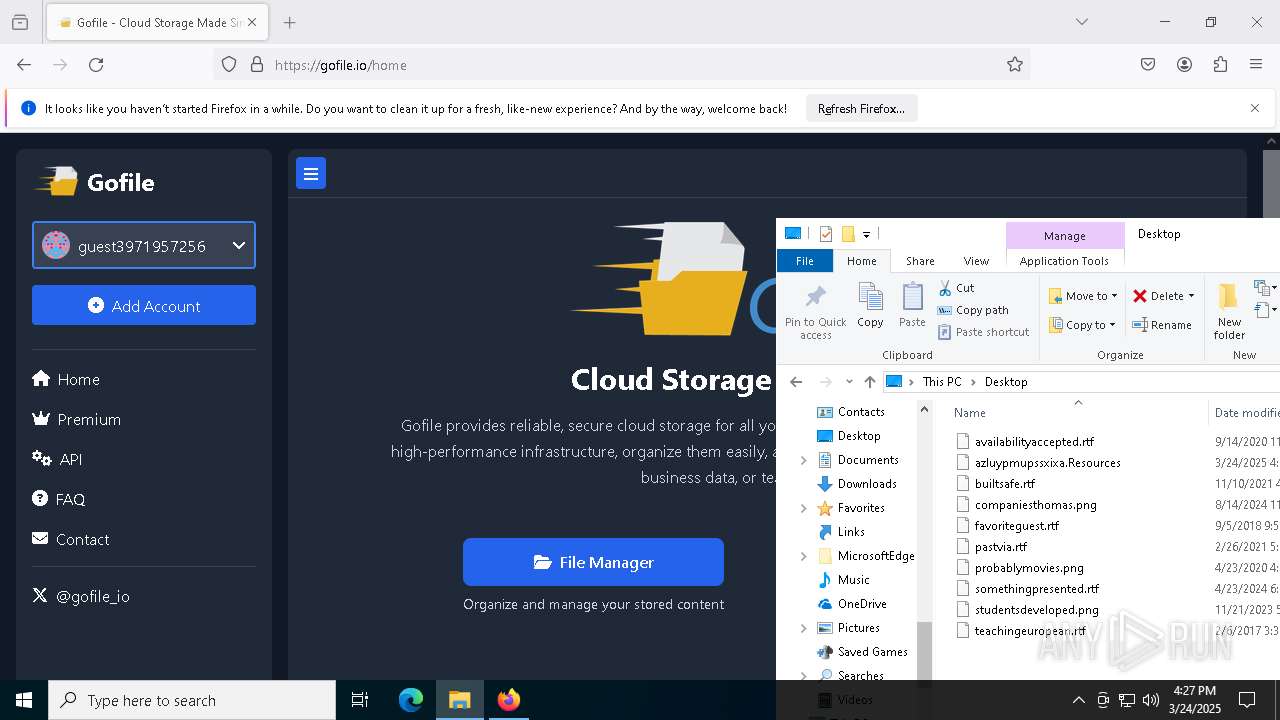
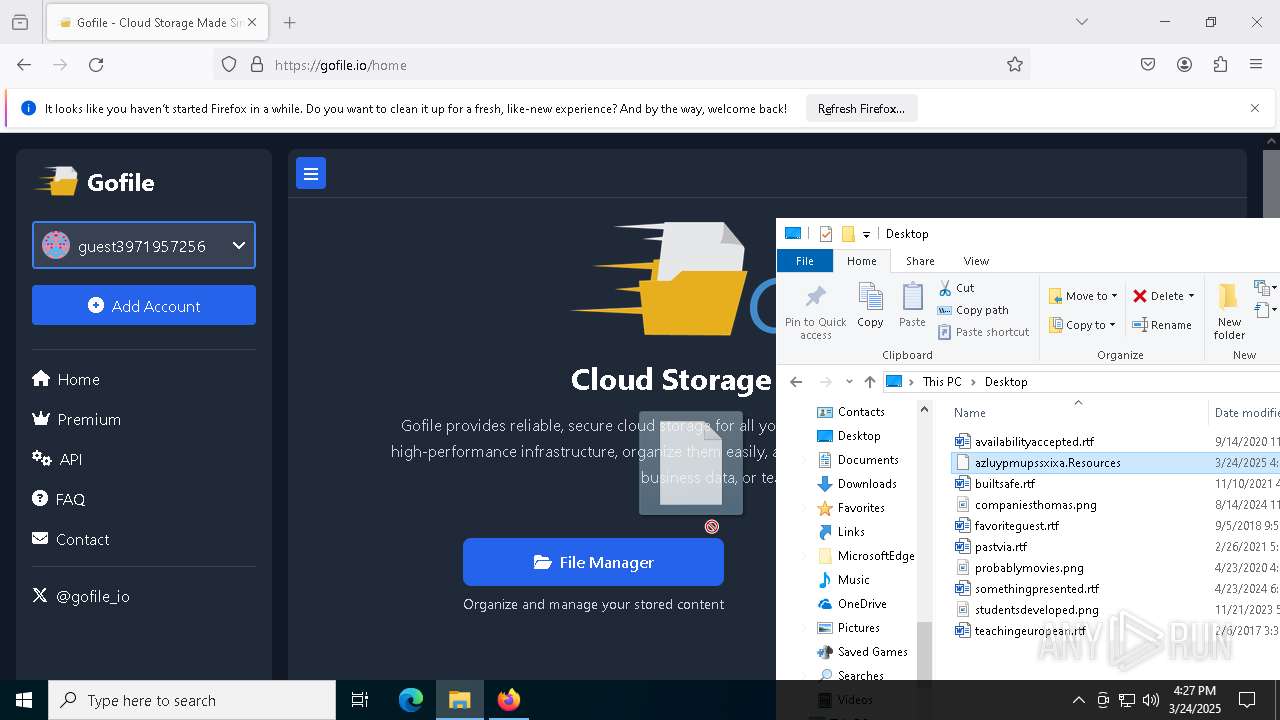
Manual execution by a user
- ExplorerSuite.exe (PID: 4880)
- CFF Explorer.exe (PID: 4696)
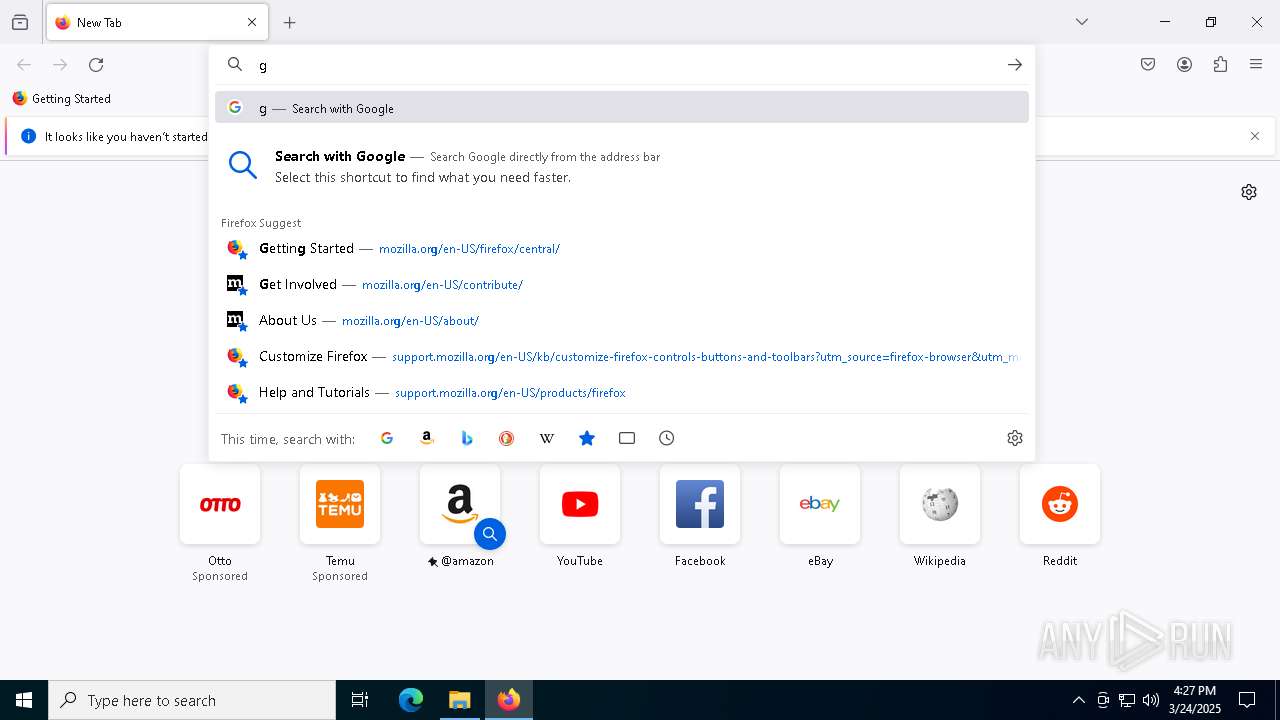
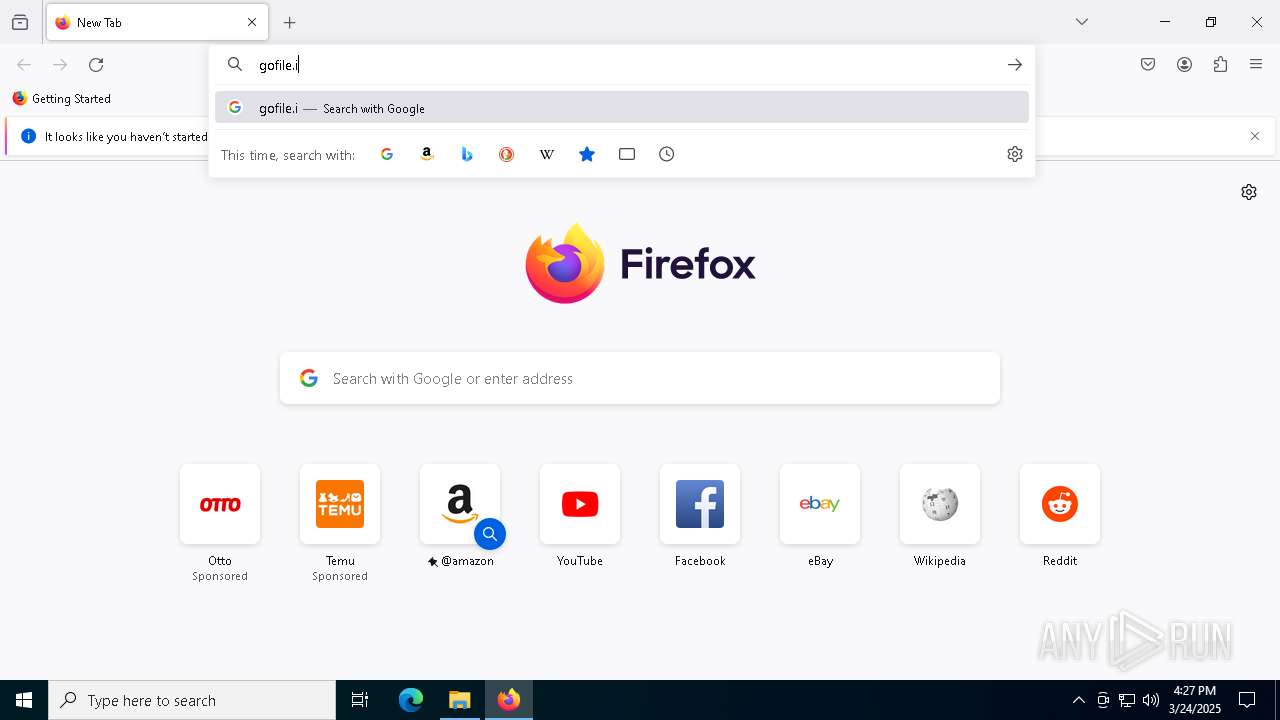
- firefox.exe (PID: 7724)
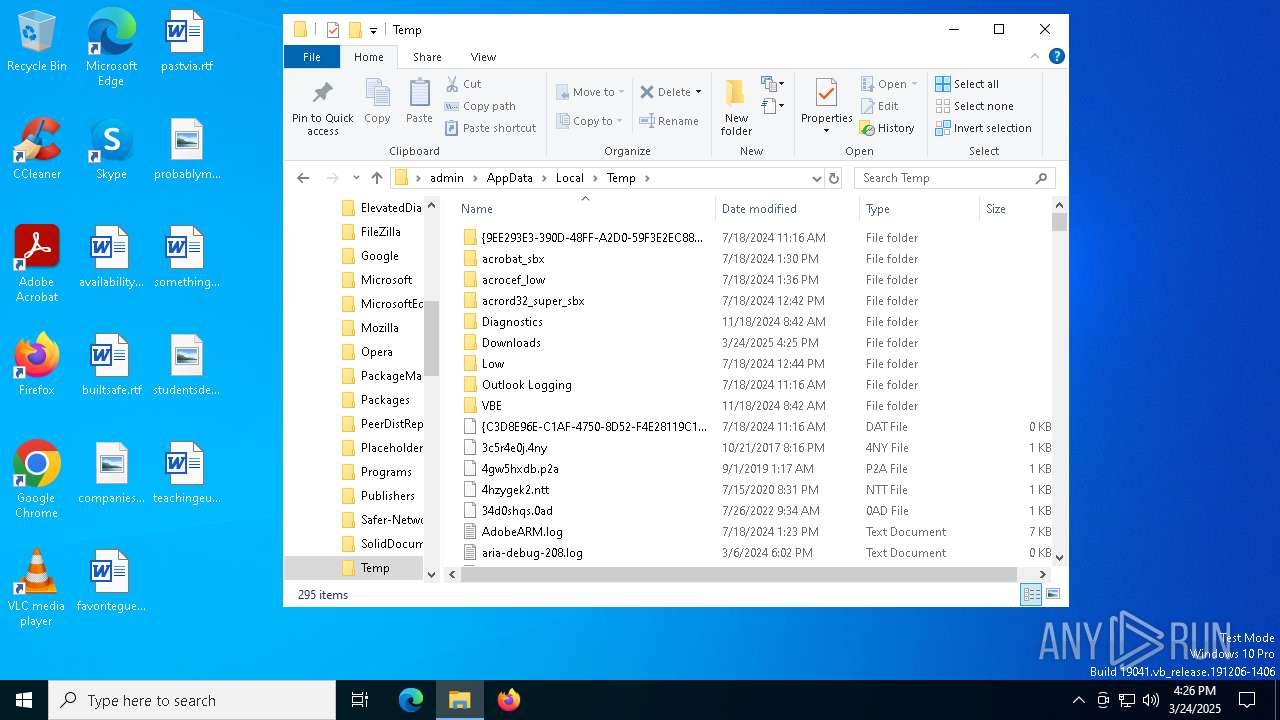
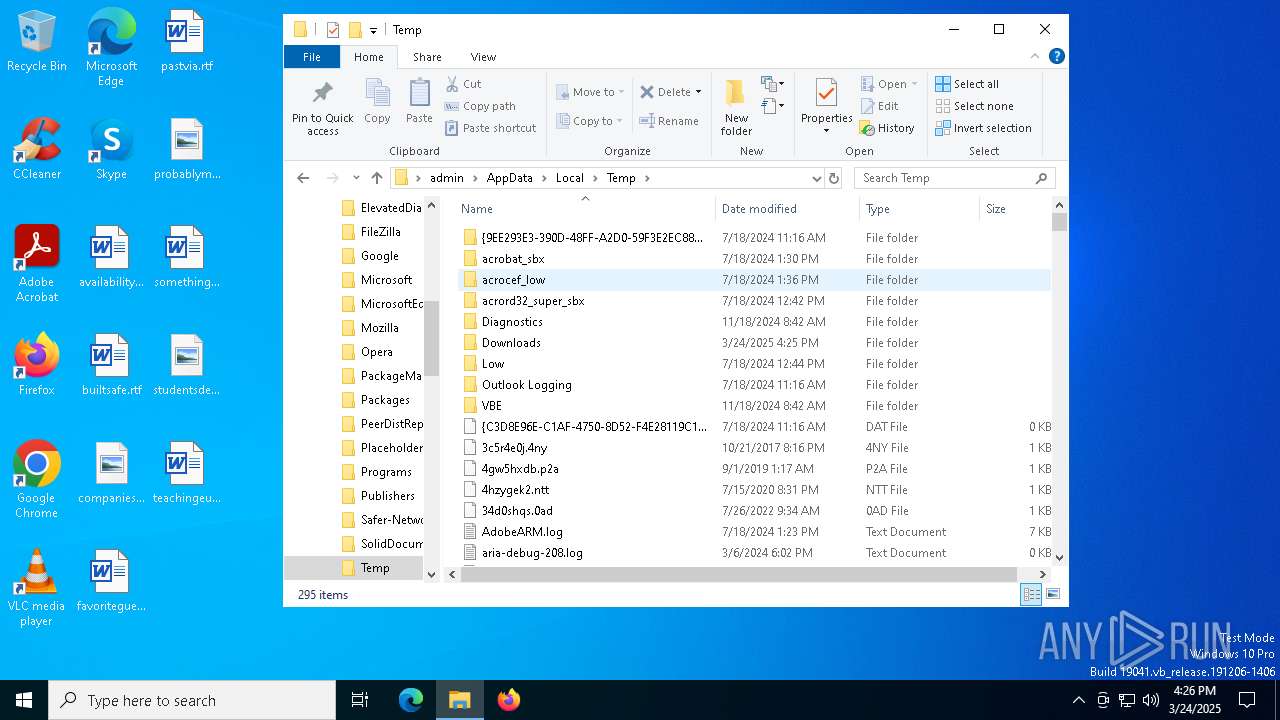
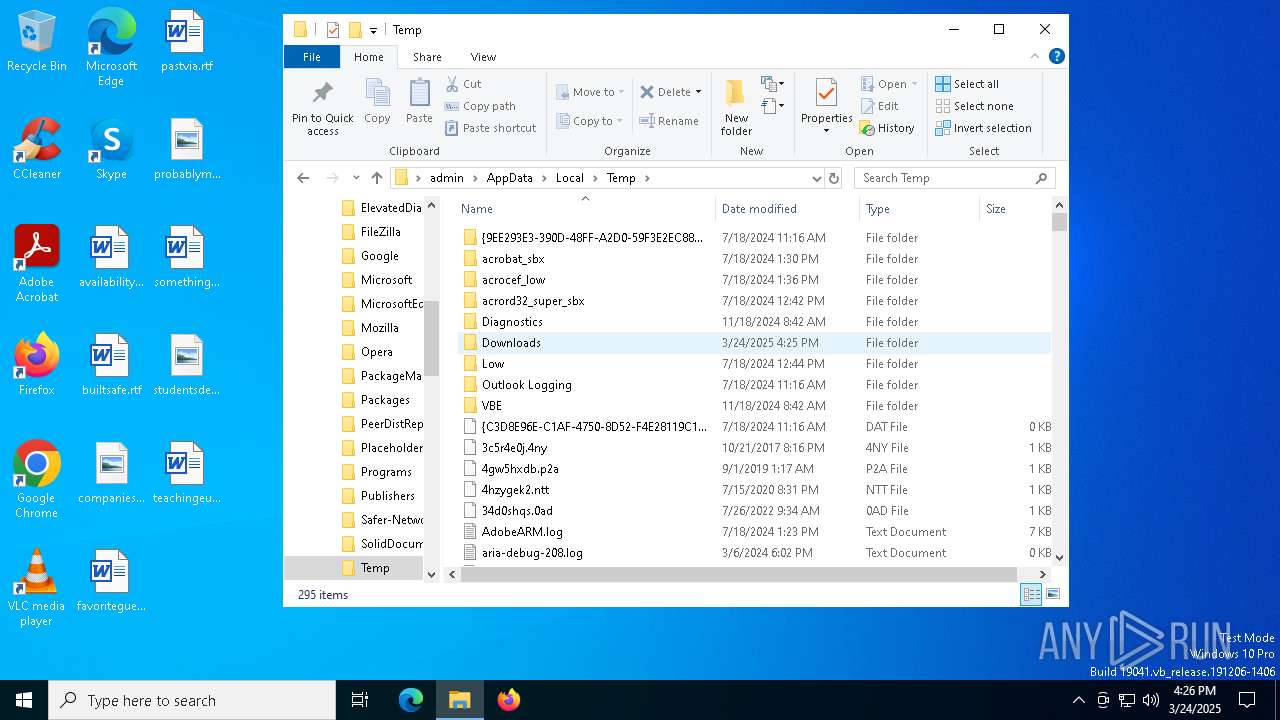
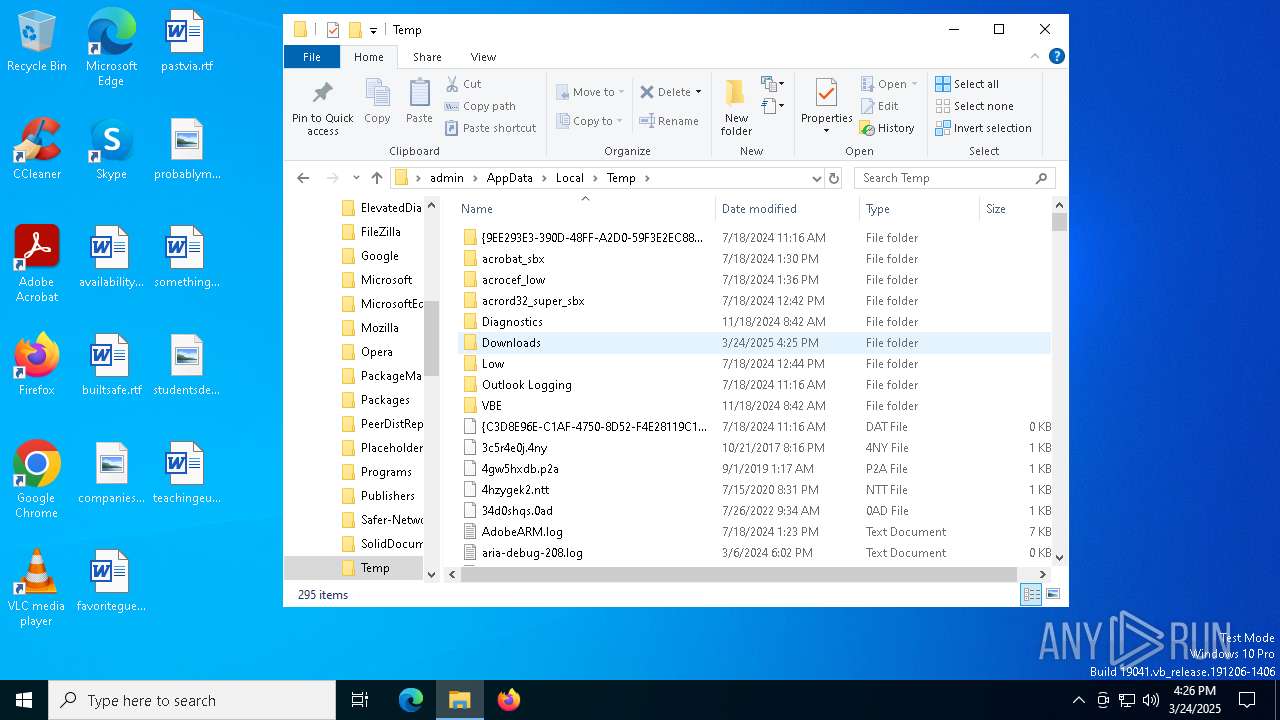
Create files in a temporary directory
- ExplorerSuite.exe (PID: 4880)
- ExplorerSuite.exe (PID: 2096)
- ExplorerSuite.tmp (PID: 4448)
Checks supported languages
- ExplorerSuite.exe (PID: 4880)
- ExplorerSuite.tmp (PID: 2140)
- CFF Explorer.exe (PID: 4696)
Reads the computer name
- ExplorerSuite.tmp (PID: 2140)
- ExplorerSuite.tmp (PID: 4448)
- CFF Explorer.exe (PID: 4696)
Process checks computer location settings
- ExplorerSuite.tmp (PID: 2140)
The sample compiled with english language support
- ExplorerSuite.tmp (PID: 4448)
Creates files in the program directory
- ExplorerSuite.tmp (PID: 4448)
The sample compiled with Italian language support
- ExplorerSuite.tmp (PID: 4448)
Application launched itself
- firefox.exe (PID: 7724)
- firefox.exe (PID: 1096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 16:22:34 |
| ZipCRC: | 0xc773e1bc |
| ZipCompressedSize: | 3531076 |
| ZipUncompressedSize: | 3613174 |
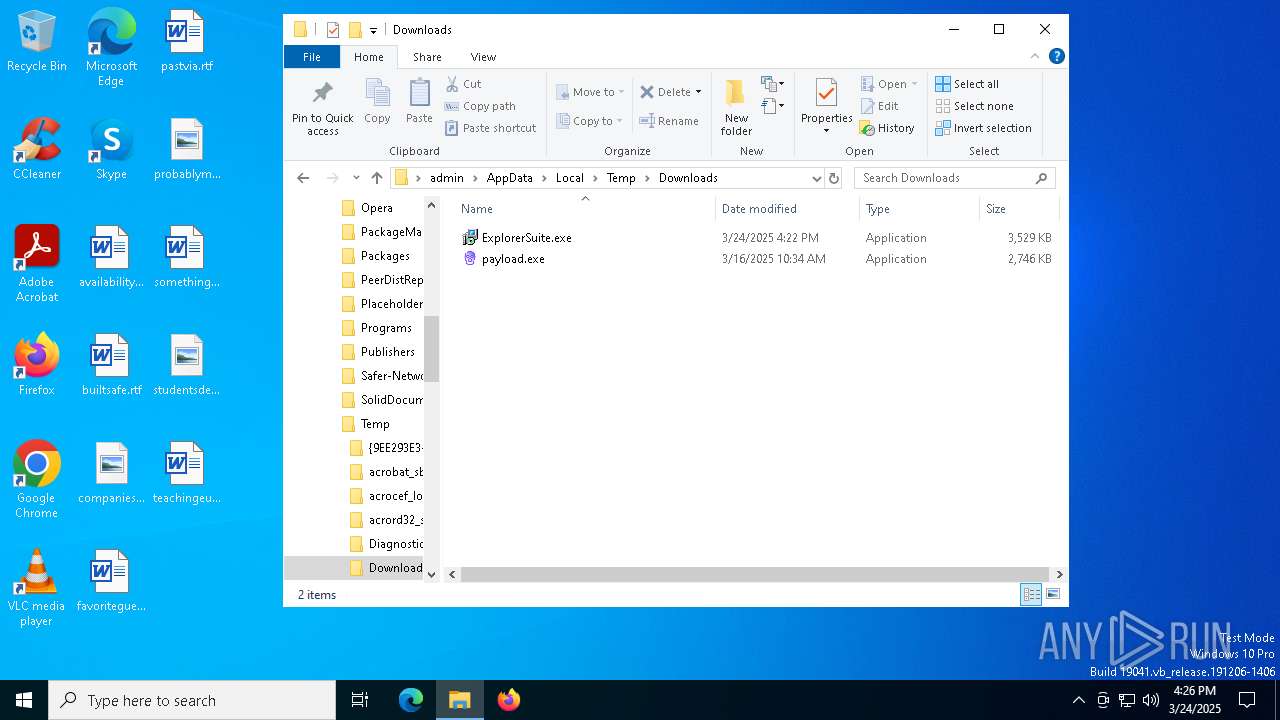
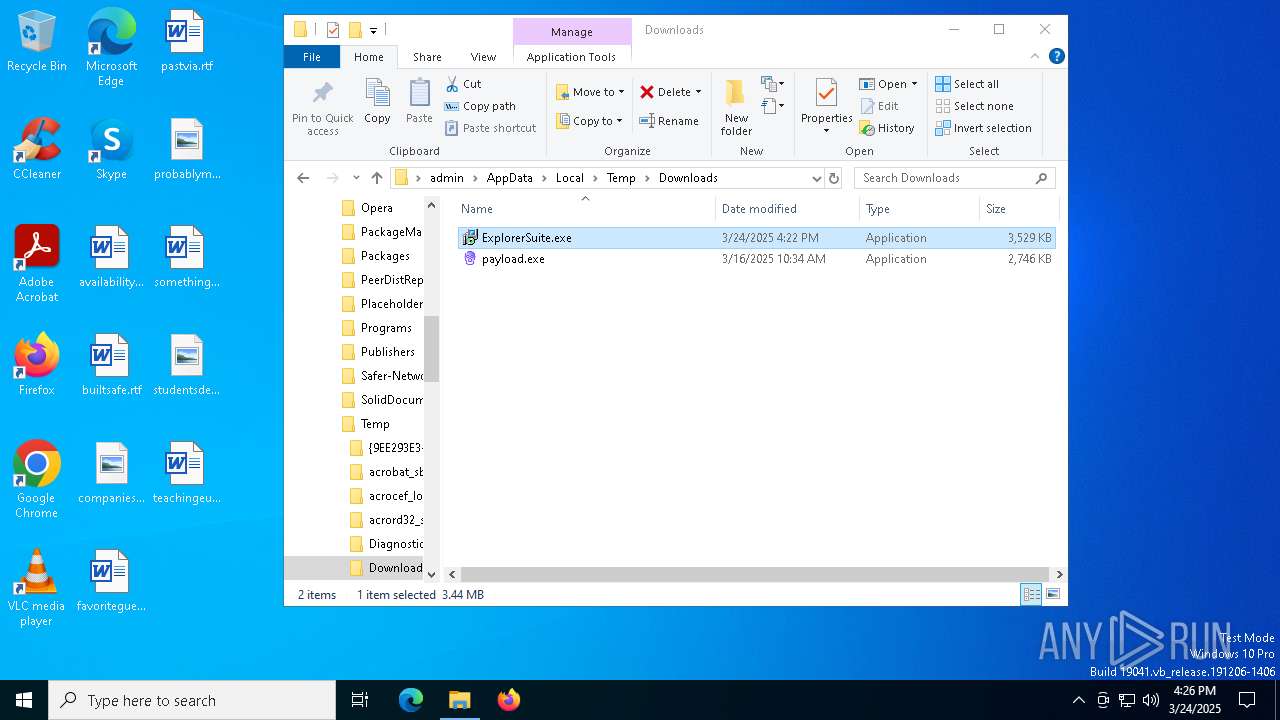
| ZipFileName: | ExplorerSuite.exe |
Total processes
167
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1096 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1164 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\Downloads\ExplorerSuite.exe" /SPAWNWND=$5014E /NOTIFYWND=$4020E | C:\Users\admin\AppData\Local\Temp\Downloads\ExplorerSuite.exe | ExplorerSuite.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Explorer Suite Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\is-9B6B6.tmp\ExplorerSuite.tmp" /SL5="$4020E,3231213,140800,C:\Users\admin\AppData\Local\Temp\Downloads\ExplorerSuite.exe" | C:\Users\admin\AppData\Local\Temp\is-9B6B6.tmp\ExplorerSuite.tmp | — | ExplorerSuite.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5076 -childID 4 -isForBrowser -prefsHandle 5108 -prefMapHandle 5056 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1452 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9a367093-bb42-4781-8bea-50b4079e837a} 1096 "\\.\pipe\gecko-crash-server-pipe.1096" 1dfa5ed74d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4228 -childID 2 -isForBrowser -prefsHandle 4292 -prefMapHandle 4288 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1452 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e11a9065-2b8e-4362-88d2-c72e01eabee1} 1096 "\\.\pipe\gecko-crash-server-pipe.1096" 1dfa1da8a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3884 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 763
Read events
23 573
Write events
172
Delete events
18
Modification events
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Downloads.zip | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8092) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8092) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
26
Suspicious files
199
Text files
44
Unknown types
0
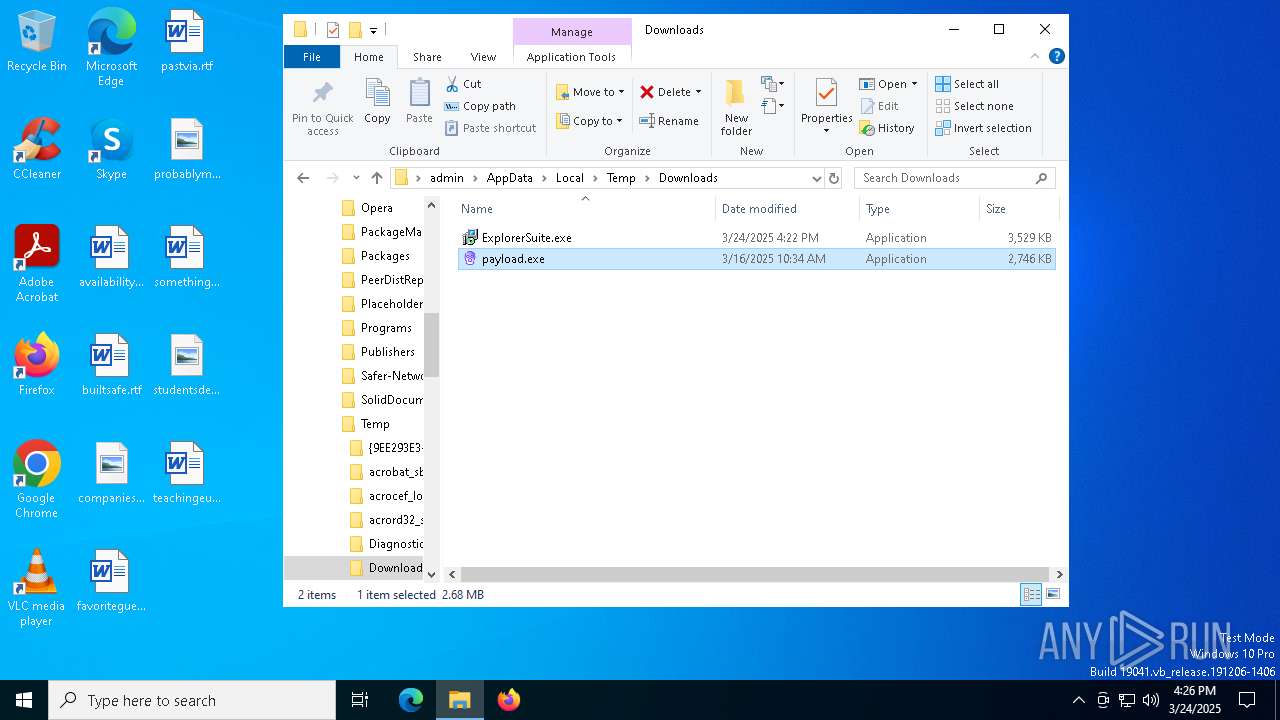
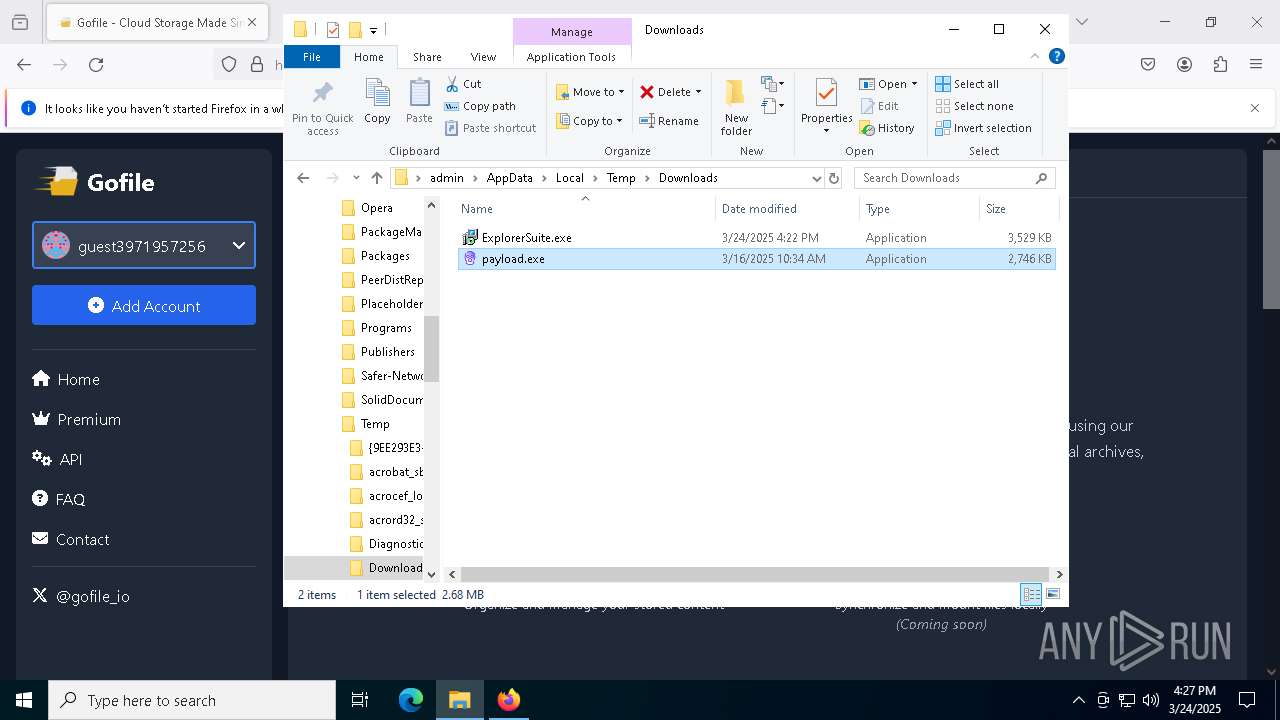
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7b622ca5-143c-4b16-9f8e-296faabeca82.down_data | — | |
MD5:— | SHA256:— | |||
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 4448 | ExplorerSuite.tmp | C:\Users\admin\AppData\Local\Temp\is-5SGFD.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c0d0c2c6-dc18-4e37-96aa-072074eeeea5.up_meta_secure | binary | |
MD5:A42C014774ABA5D5B56E104F7899A428 | SHA256:0548E55E299F4D1B50AD93F888FFE23C75A318BE00675DE4B5925711F80642B8 | |||
| 4448 | ExplorerSuite.tmp | C:\Users\admin\AppData\Local\Temp\is-5SGFD.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c0d0c2c6-dc18-4e37-96aa-072074eeeea5.cf8e60ea-7bd7-4cde-b93a-b58951757d56.down_meta | binary | |
MD5:193C072DCD72672019854AF28B05567D | SHA256:3084918607312078869E06082F3DD6EBBE78B86E98807BDCFB85B58795ABFF2A | |||
| 2096 | ExplorerSuite.exe | C:\Users\admin\AppData\Local\Temp\is-D6CR4.tmp\ExplorerSuite.tmp | executable | |
MD5:F0A190BC6334030BEB09F5CCC19D72F8 | SHA256:14278F7F7D5ED510F51D59D914ECA6FE2DDE6A51B86FA649D1661372680830BF | |||
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7b622ca5-143c-4b16-9f8e-296faabeca82.cf8e60ea-7bd7-4cde-b93a-b58951757d56.down_meta | binary | |
MD5:193C072DCD72672019854AF28B05567D | SHA256:3084918607312078869E06082F3DD6EBBE78B86E98807BDCFB85B58795ABFF2A | |||
| 7248 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7B94389F3FAA0A56E9870C574CA4E19F | SHA256:D29F9F3D177381AA608E214618096931FE463B75943FEB41BF771F4CCD67DEB8 | |||
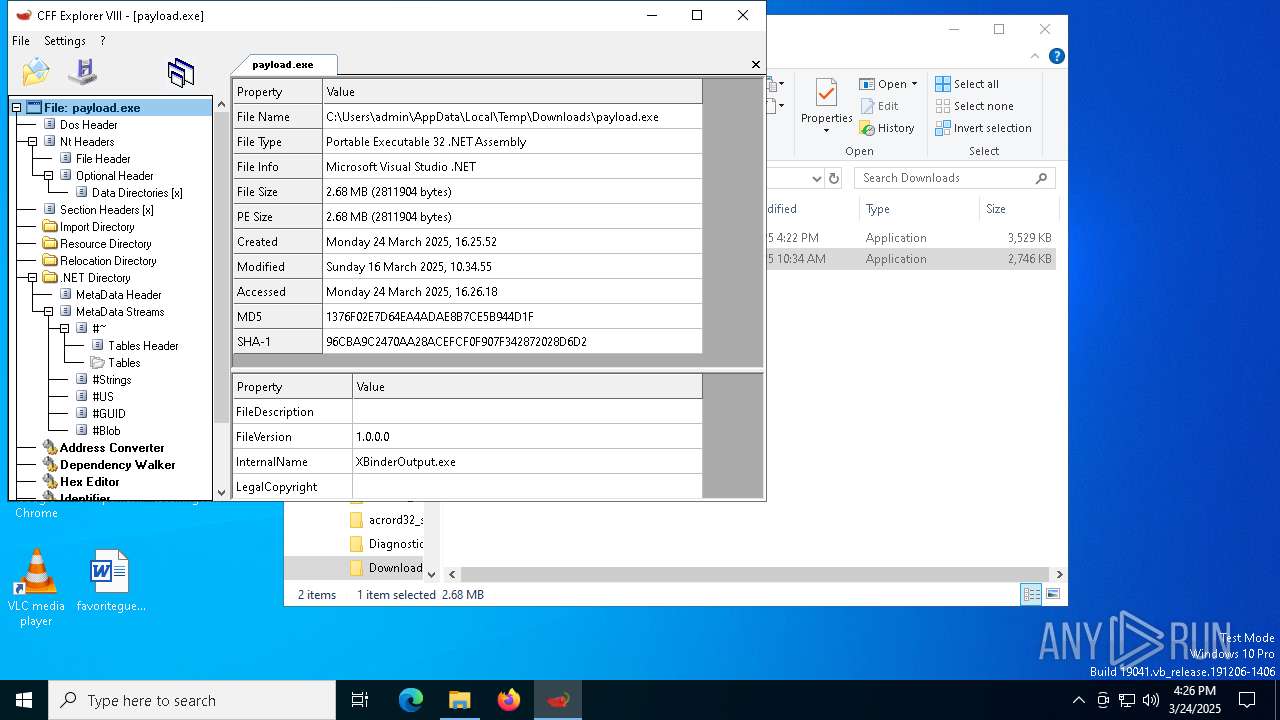
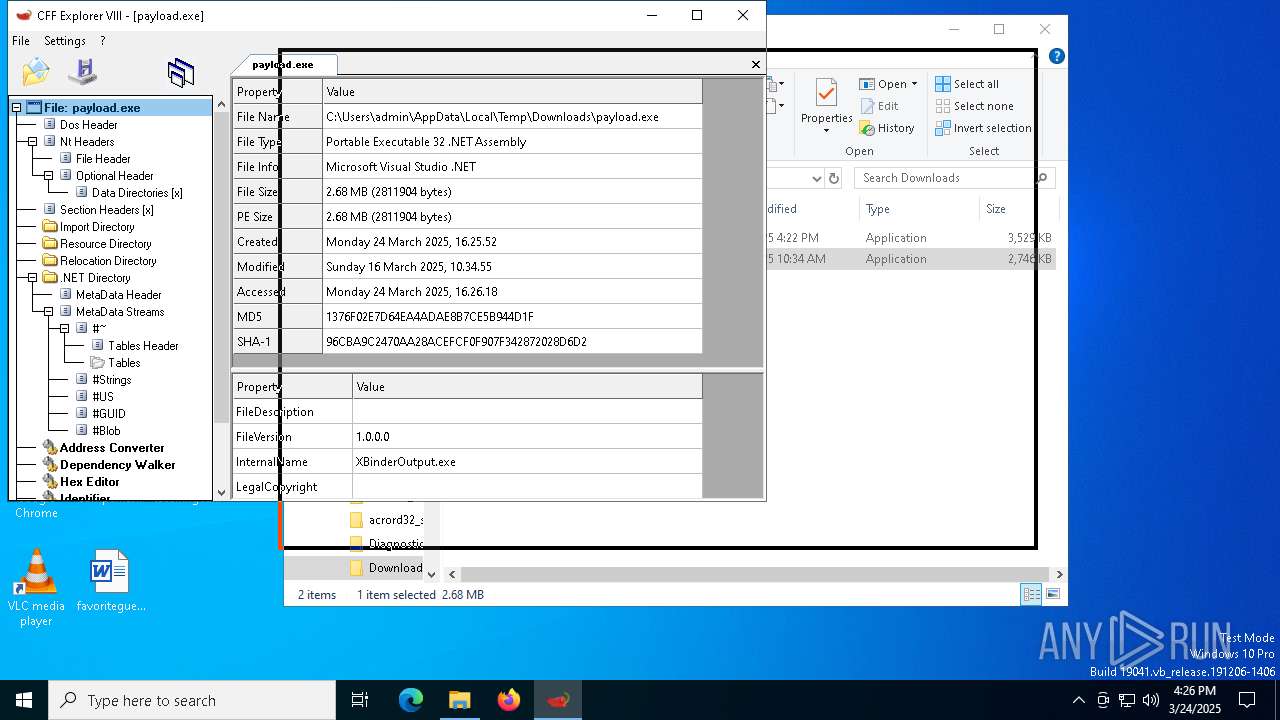
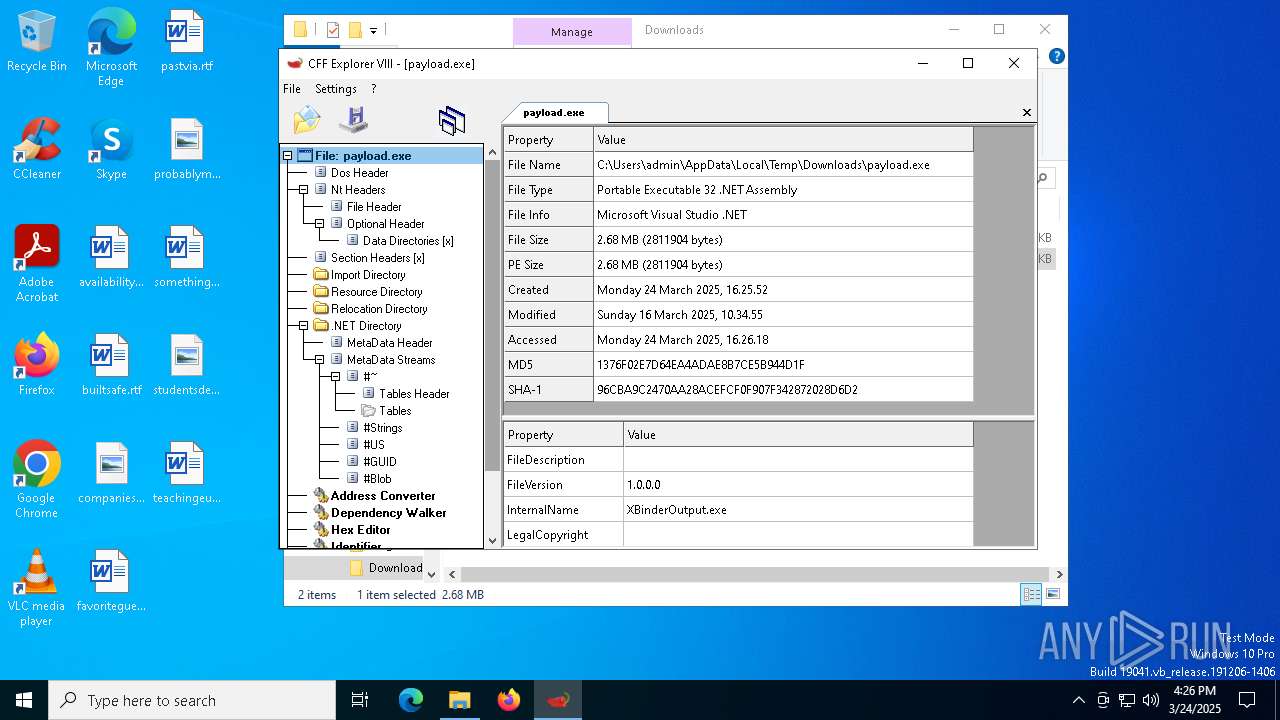
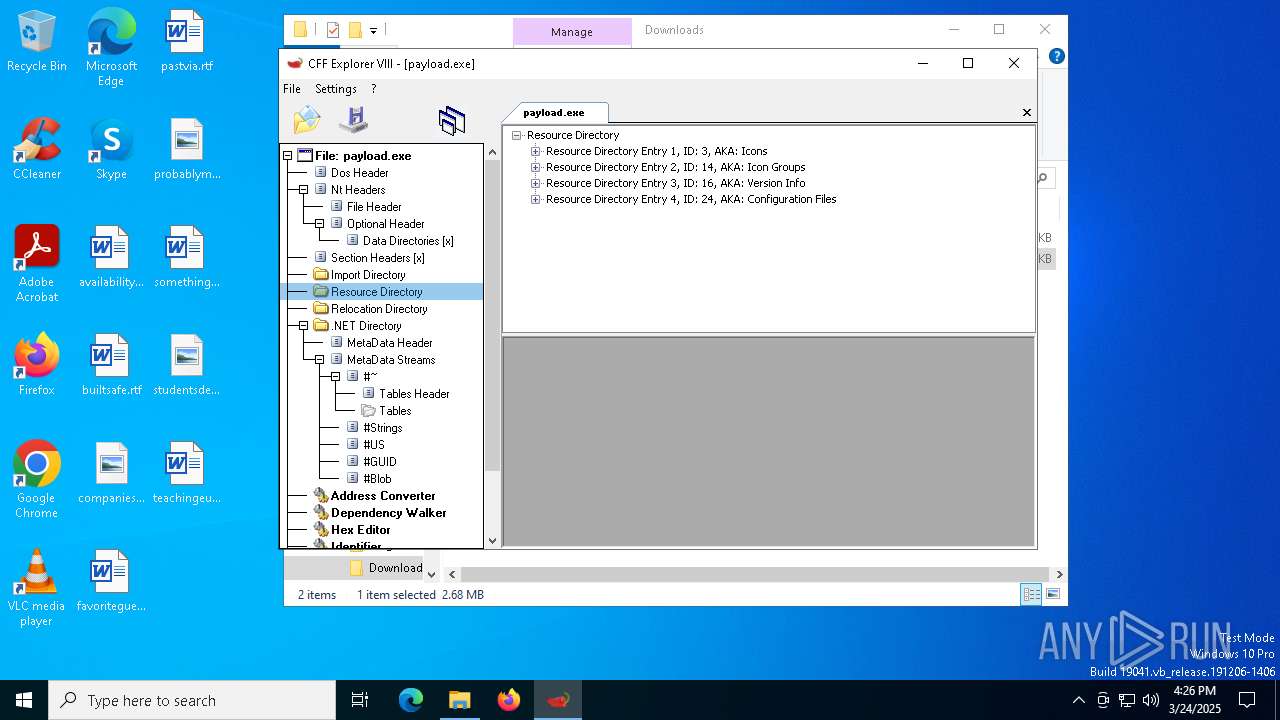
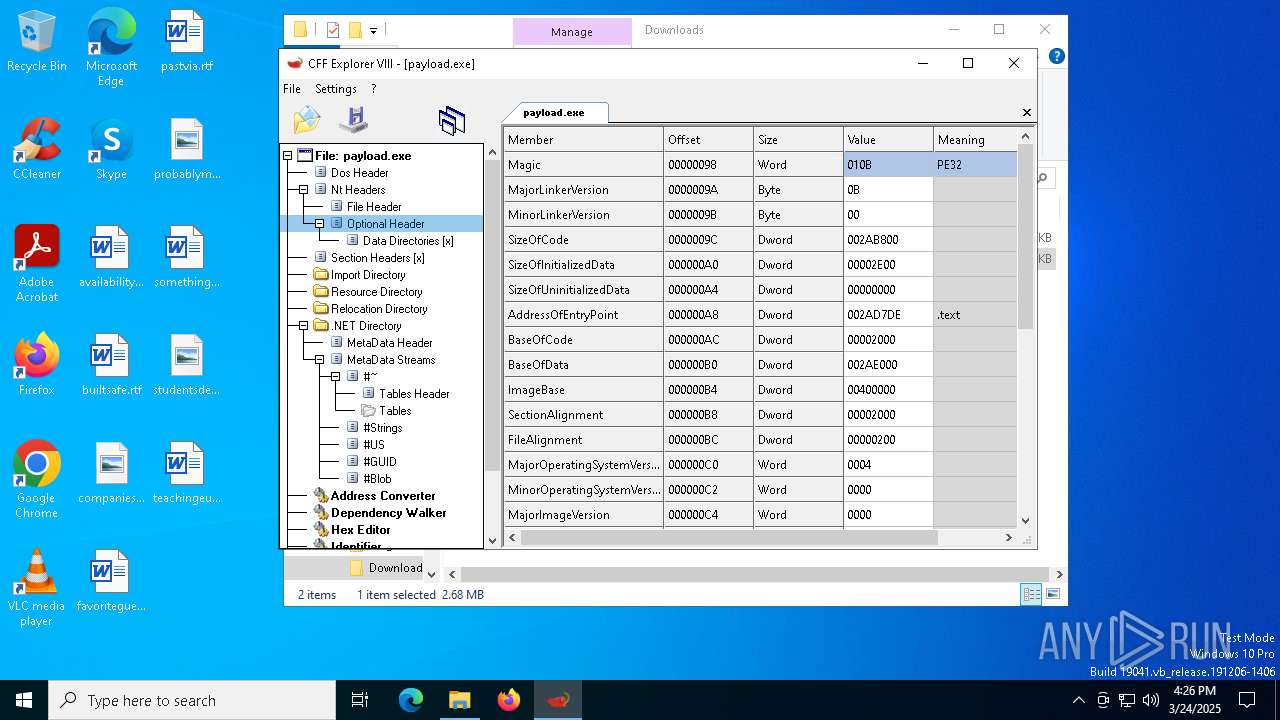
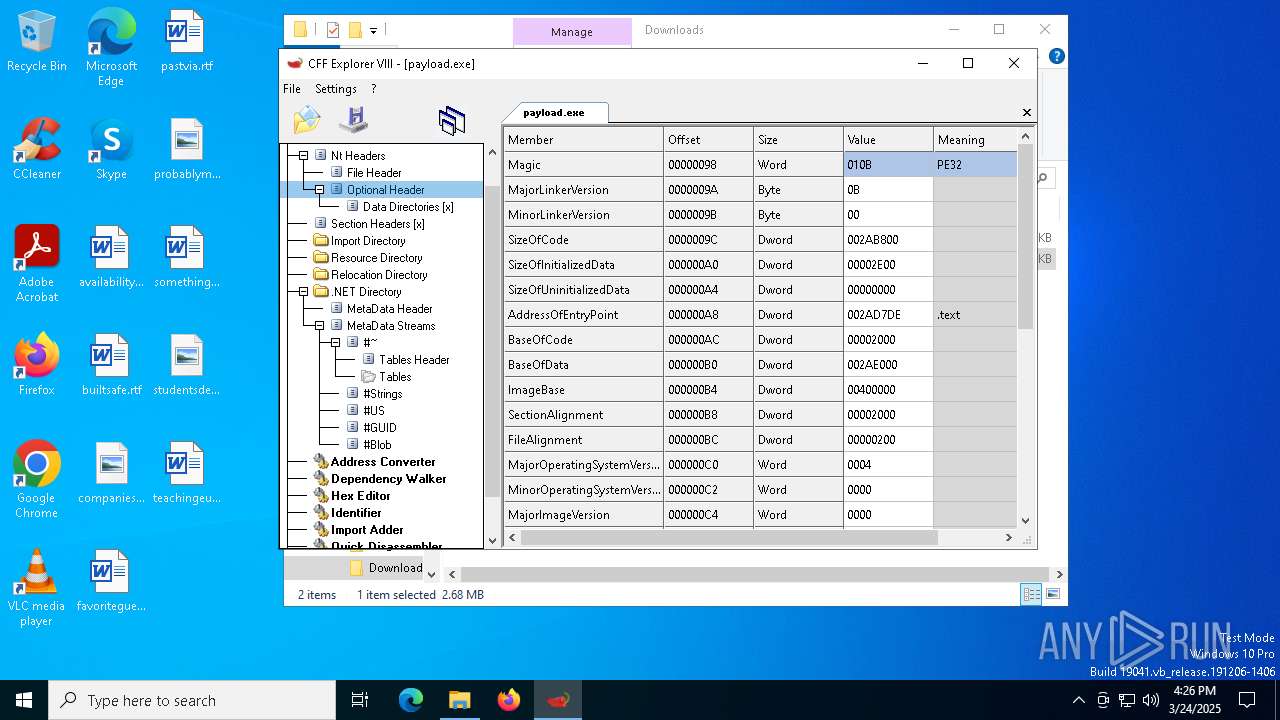
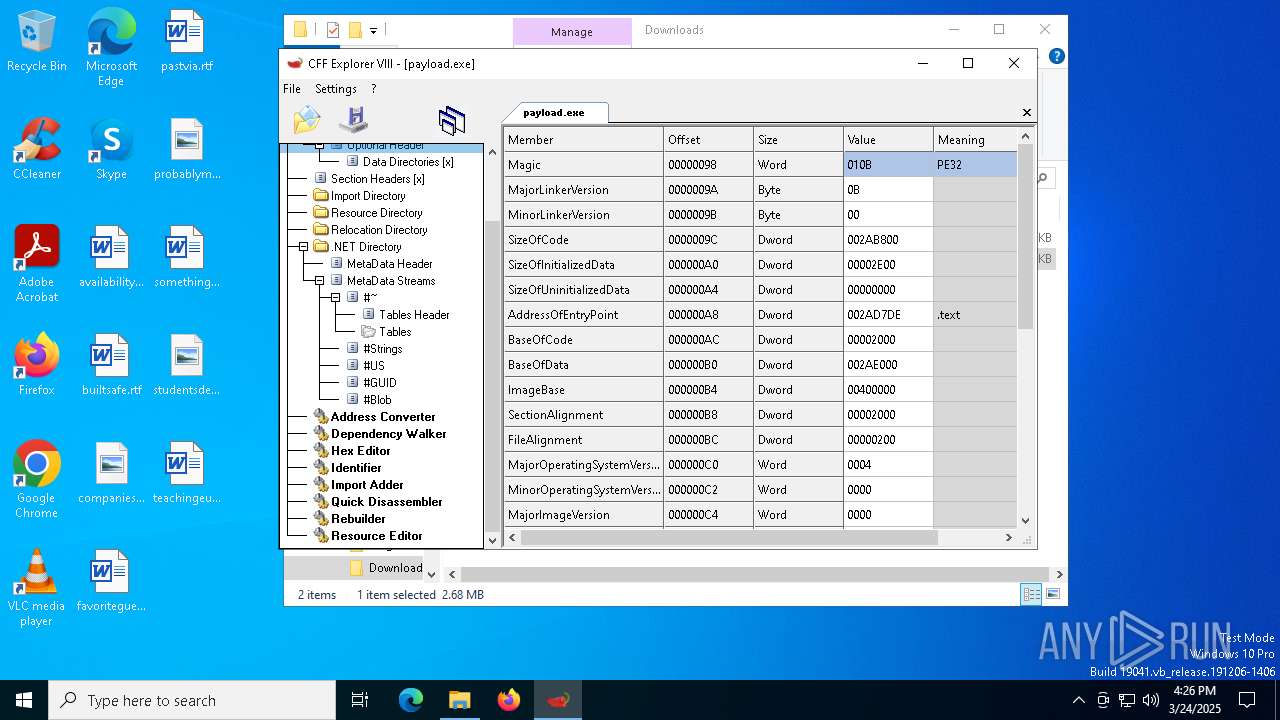
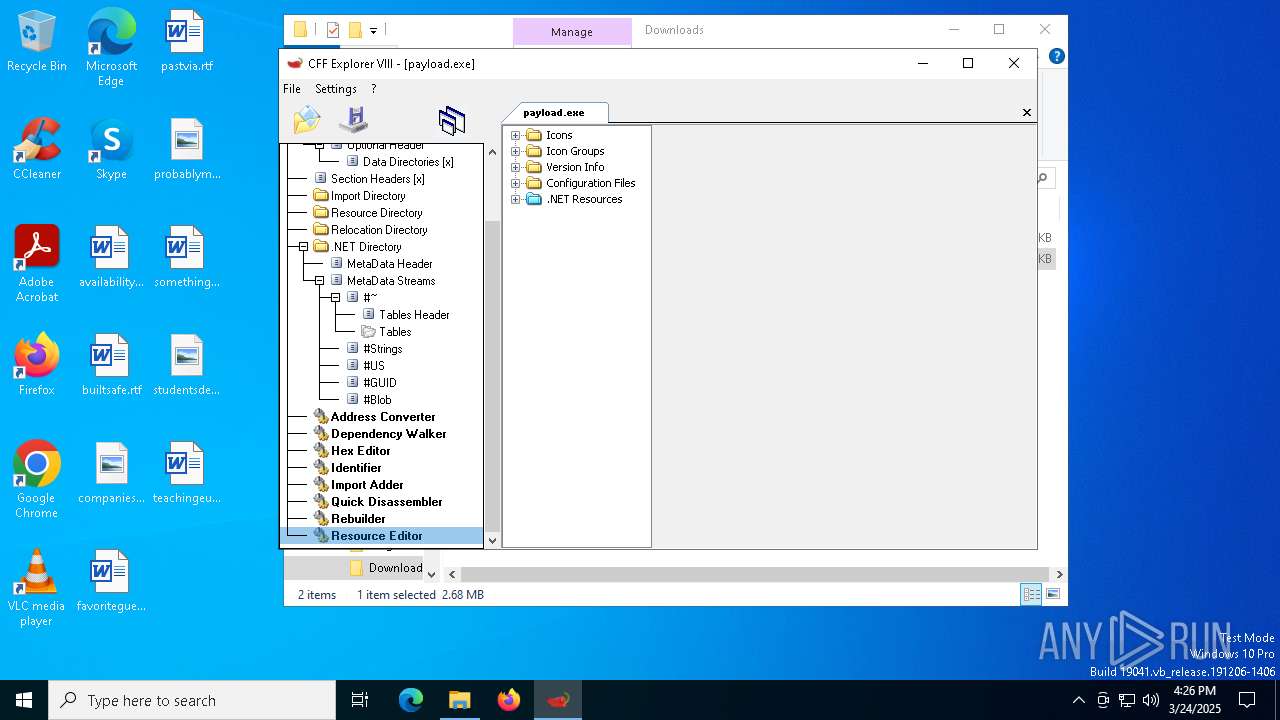
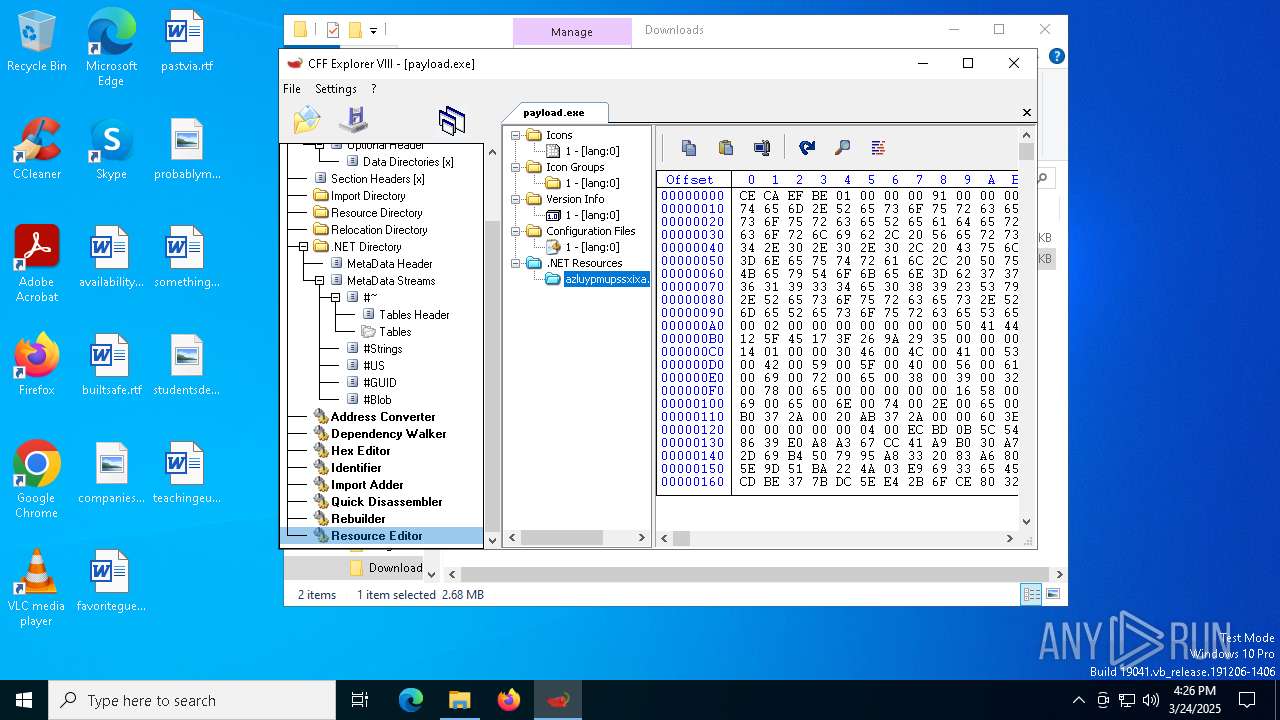
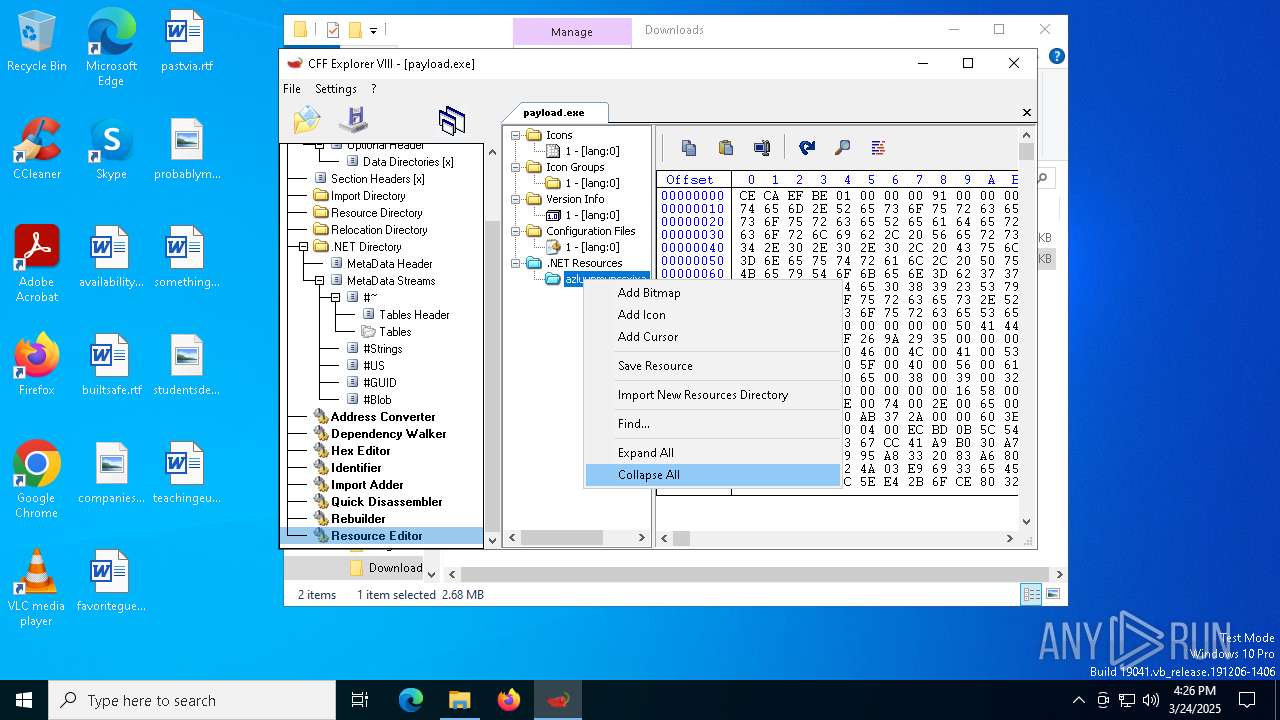
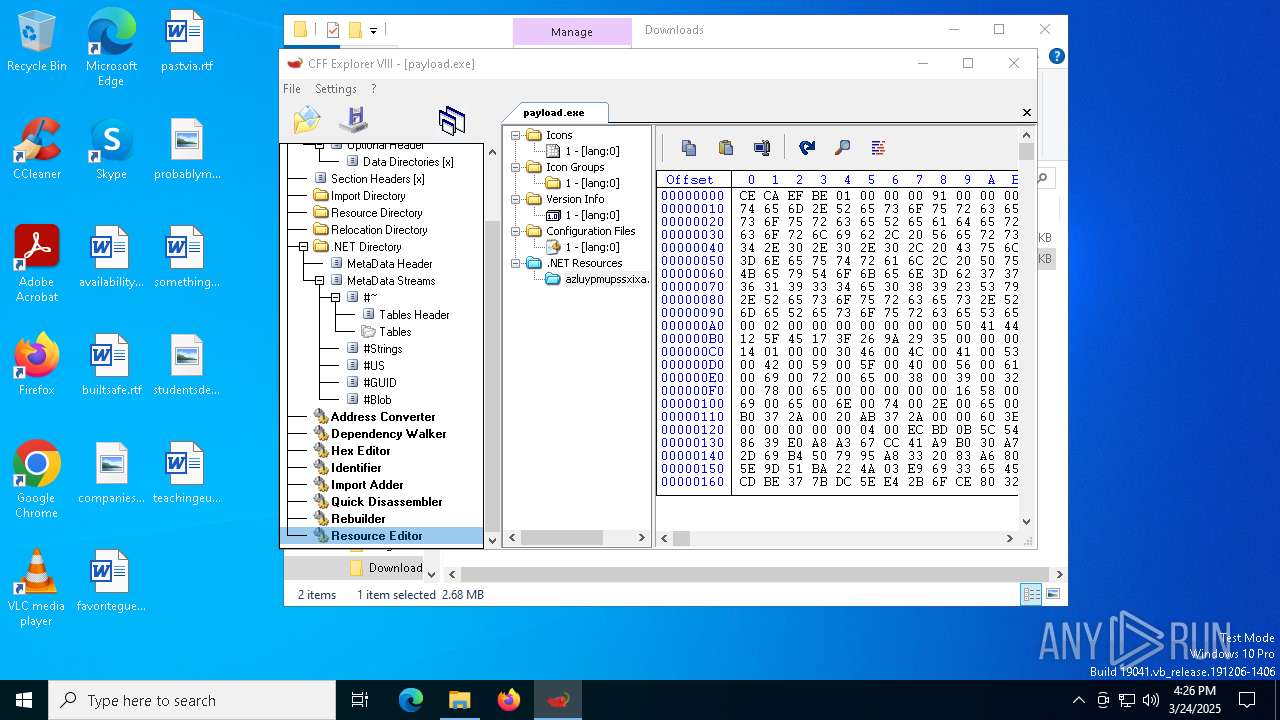
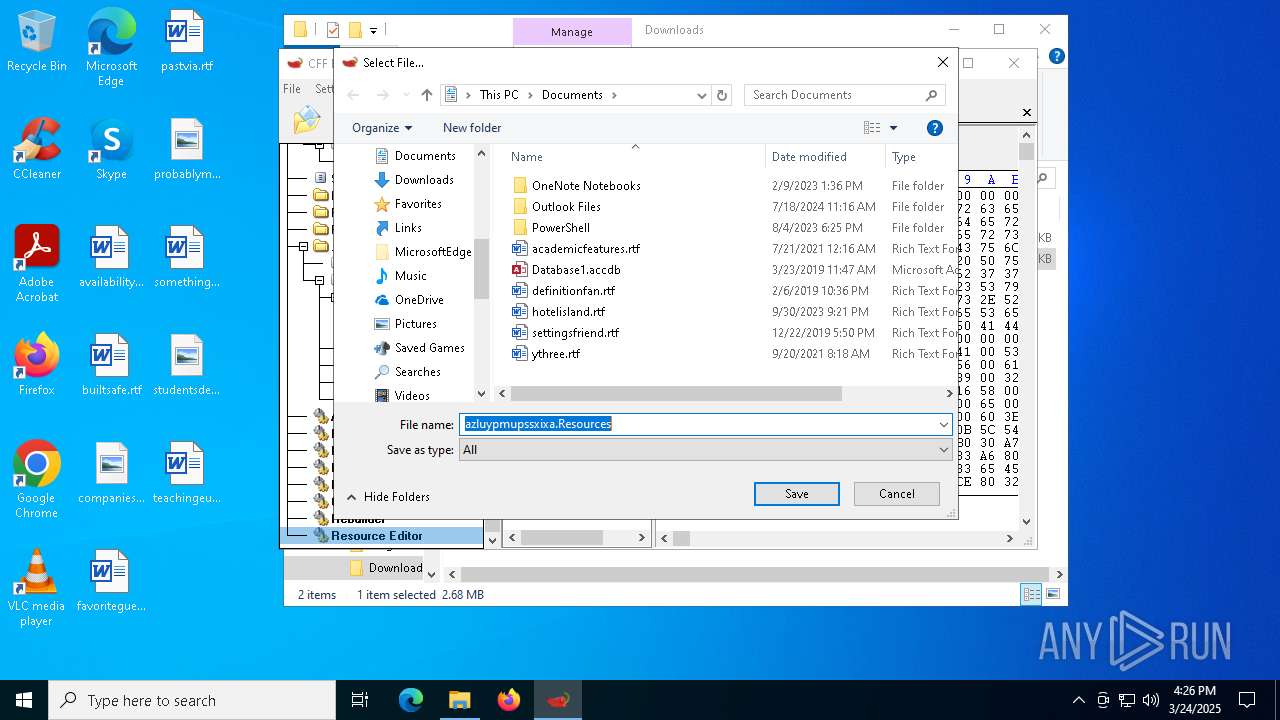
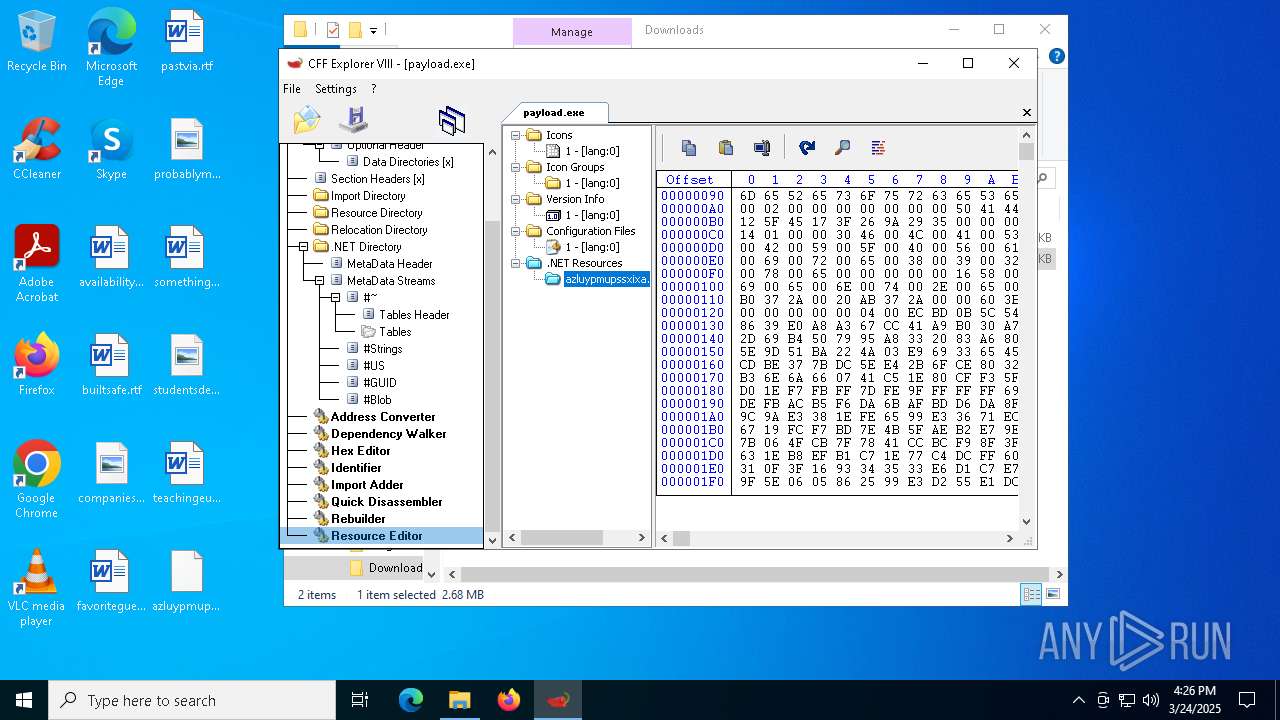
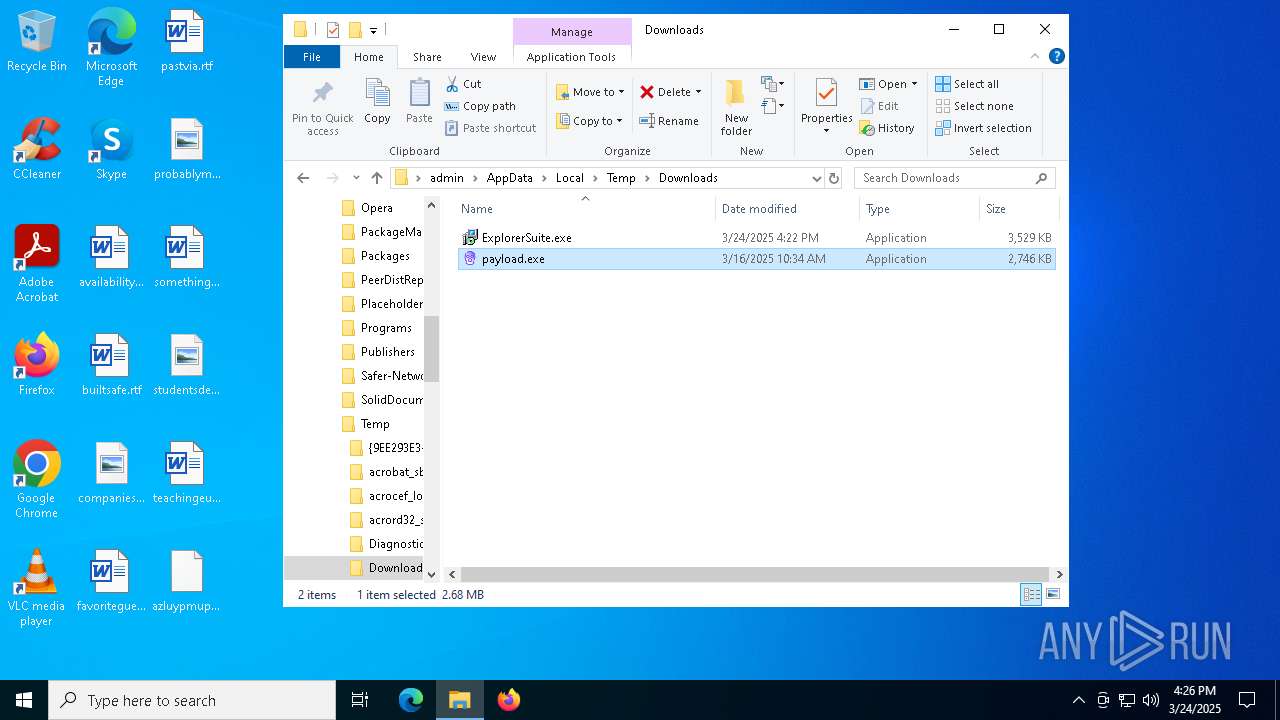
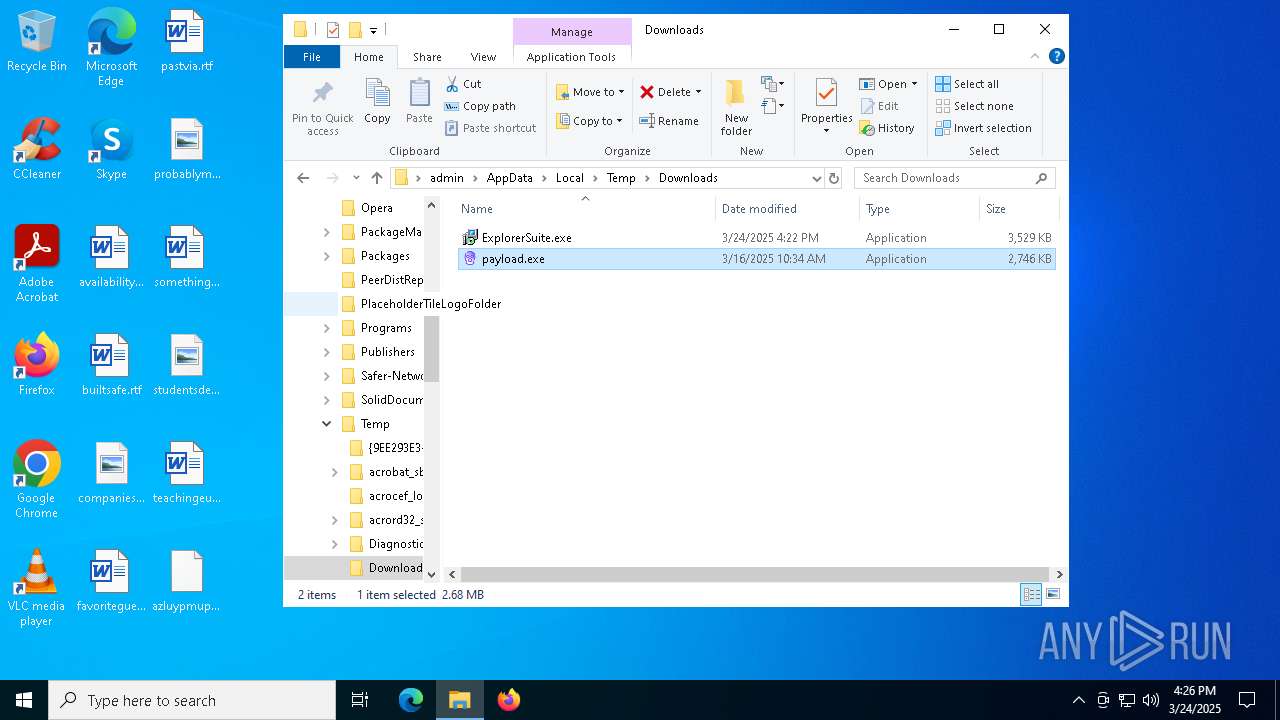
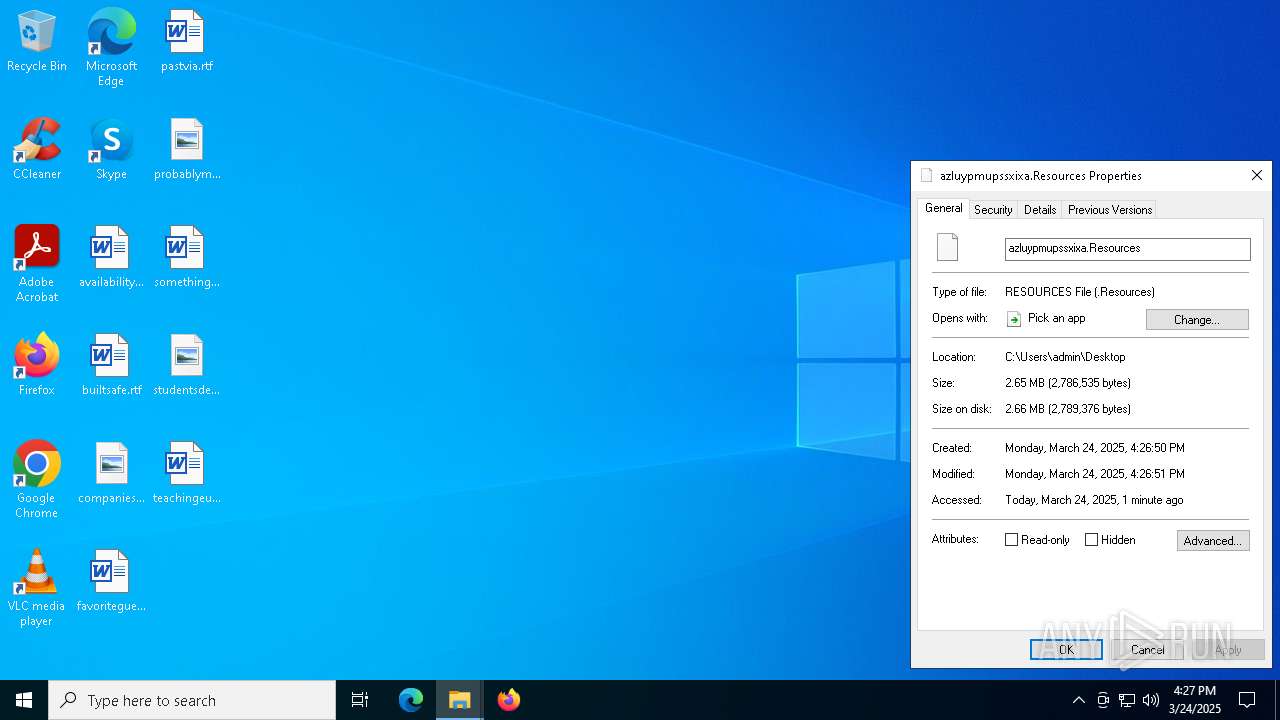
| 7352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Downloads\payload.exe | executable | |
MD5:1376F02E7D64EA4ADAE8B7CE5B944D1F | SHA256:5BB9816A0B5D0E0A692A065F66796E89F4EE4858456863B9A0B5BE9AC587375E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
101
DNS requests
129
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7628 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8020 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7248 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8020 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1096 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1096 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1096 | firefox.exe | POST | 200 | 2.22.242.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
6656 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.198.162.78:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
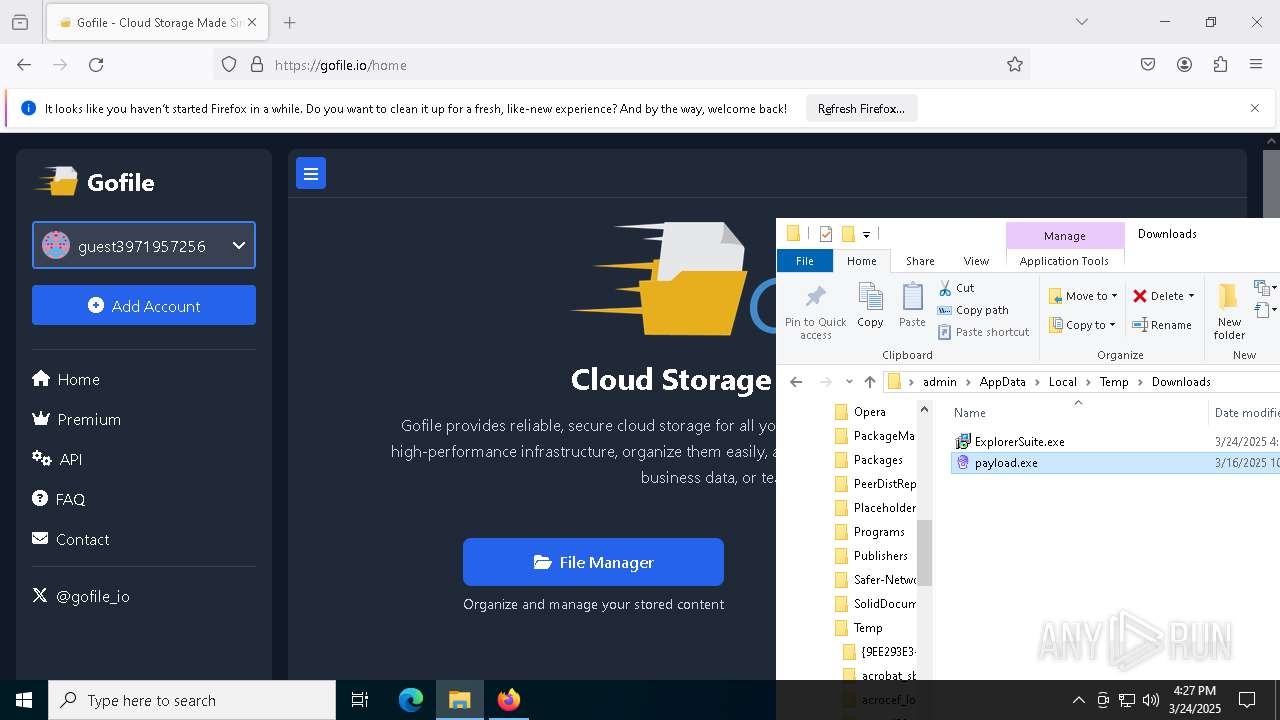
Threats
PID | Process | Class | Message |
|---|---|---|---|
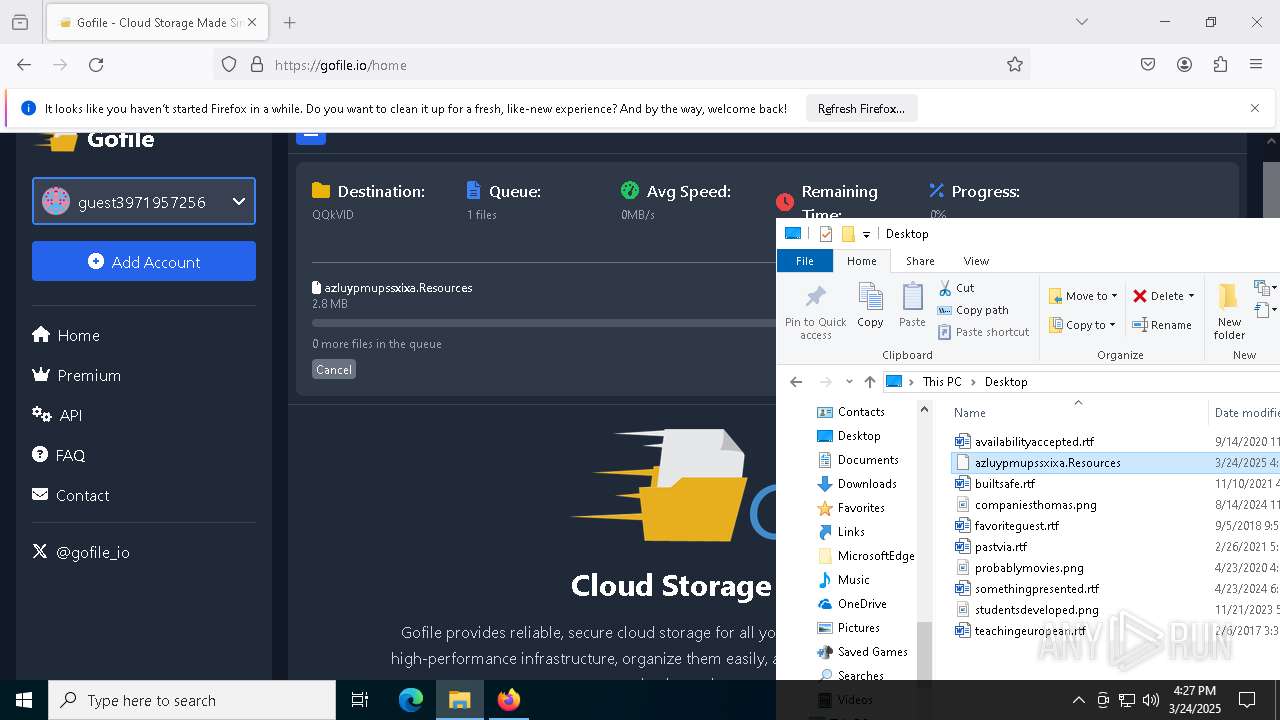
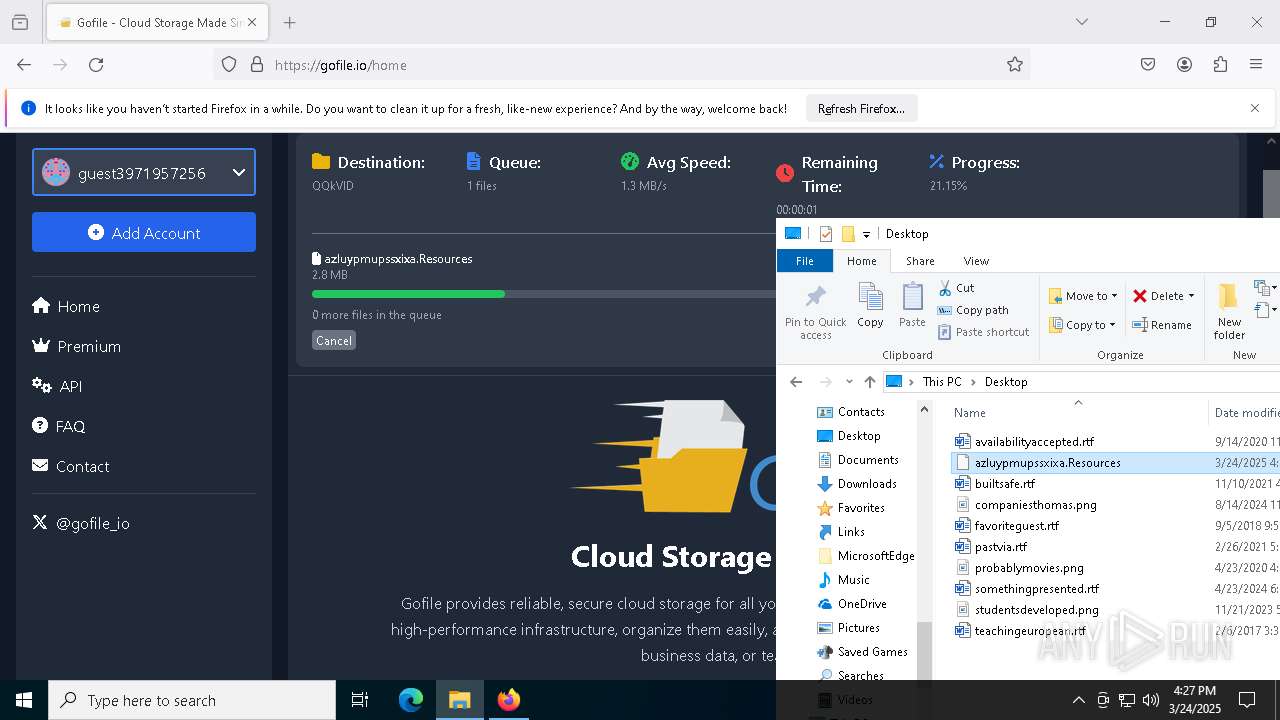
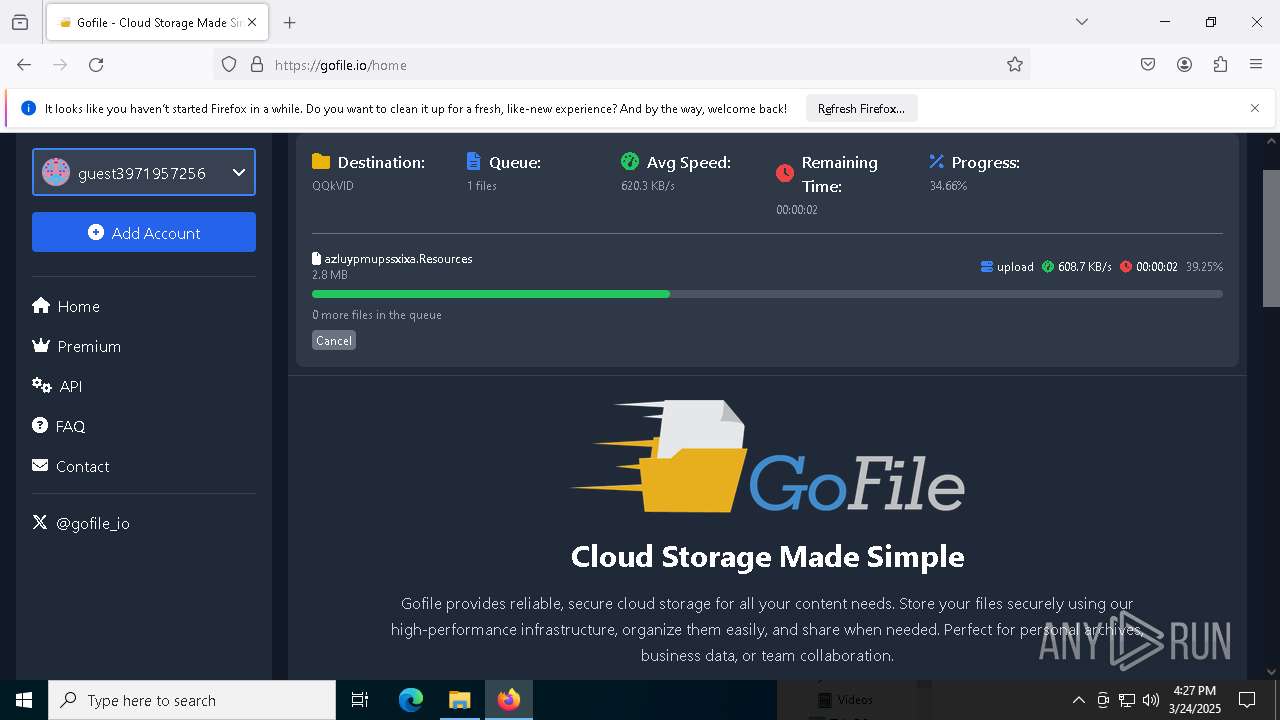
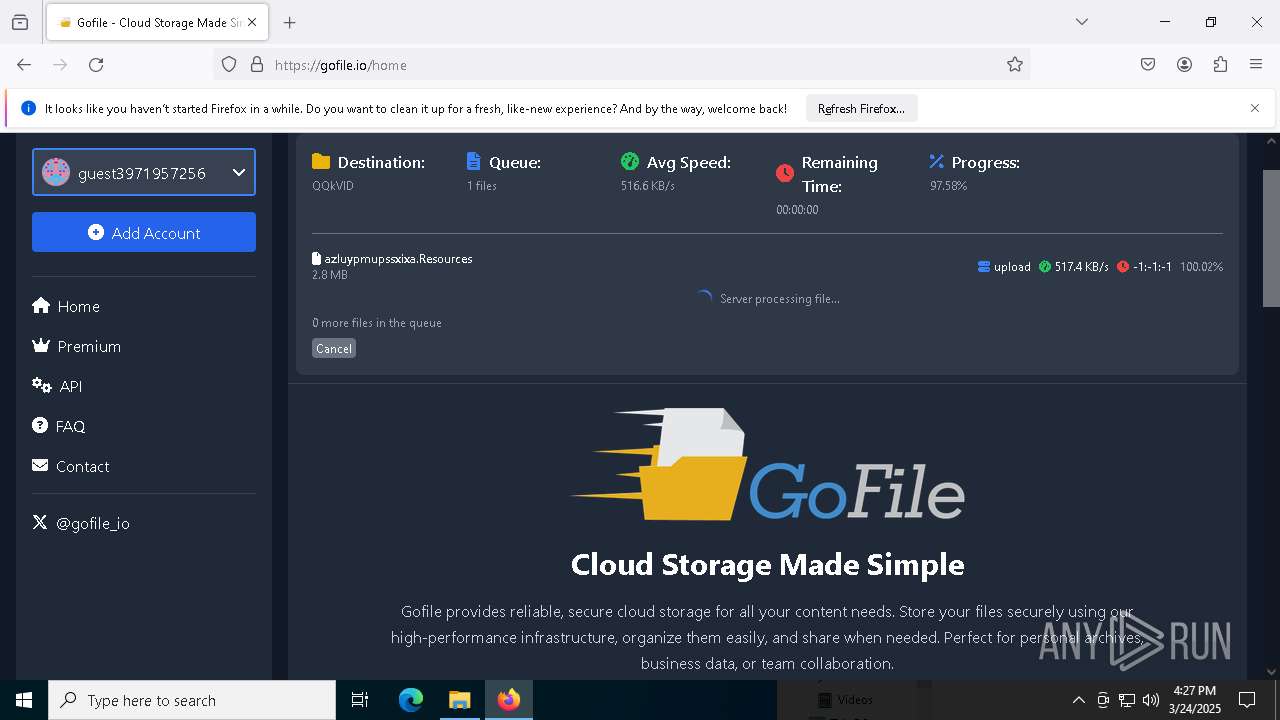
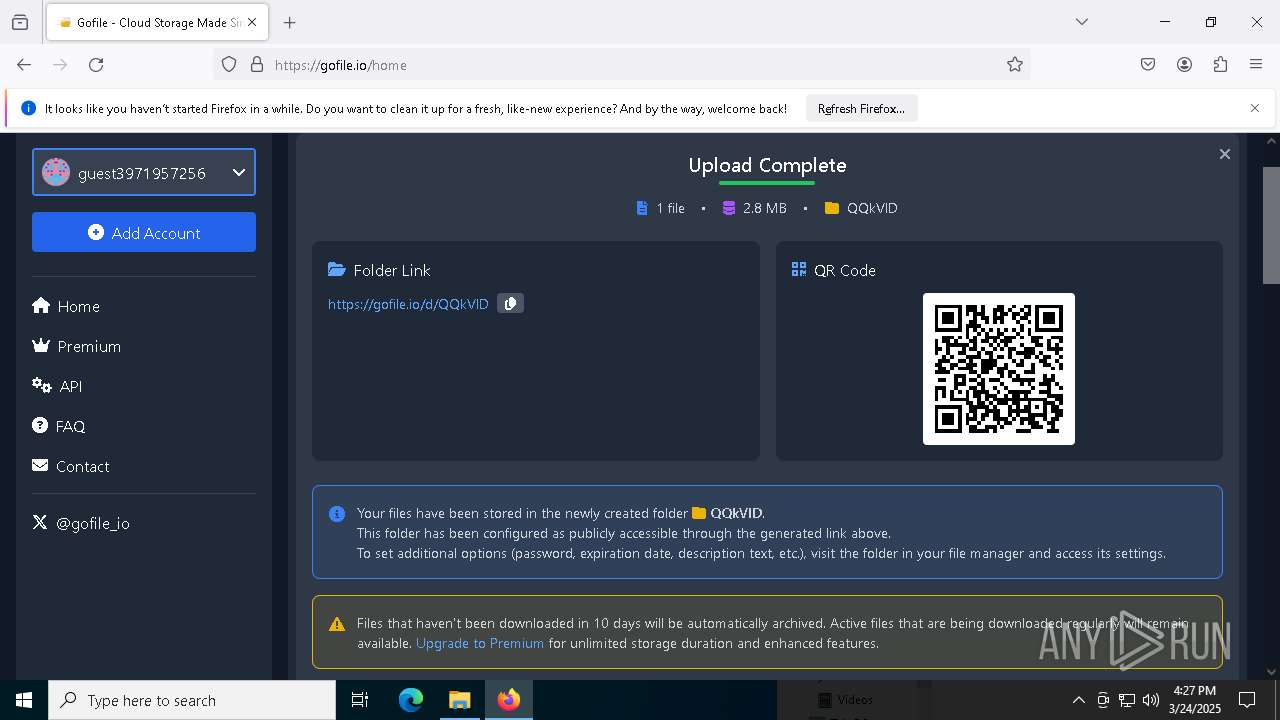
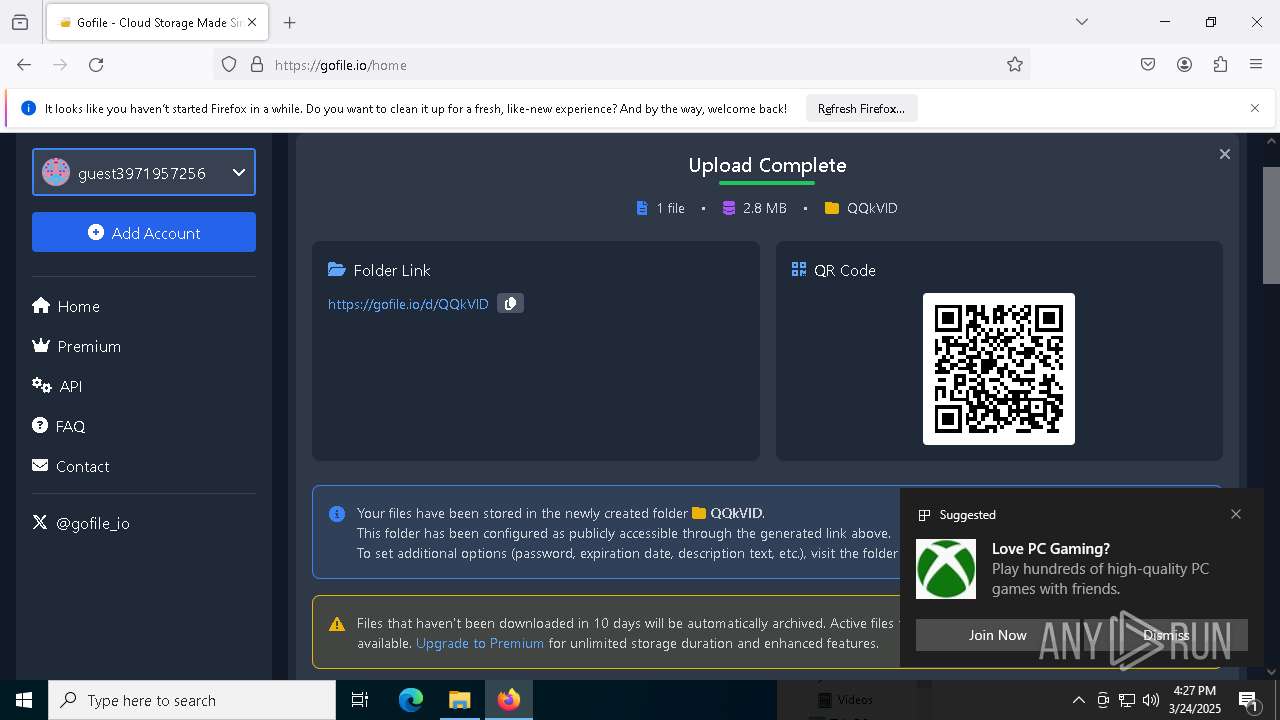
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
1096 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |