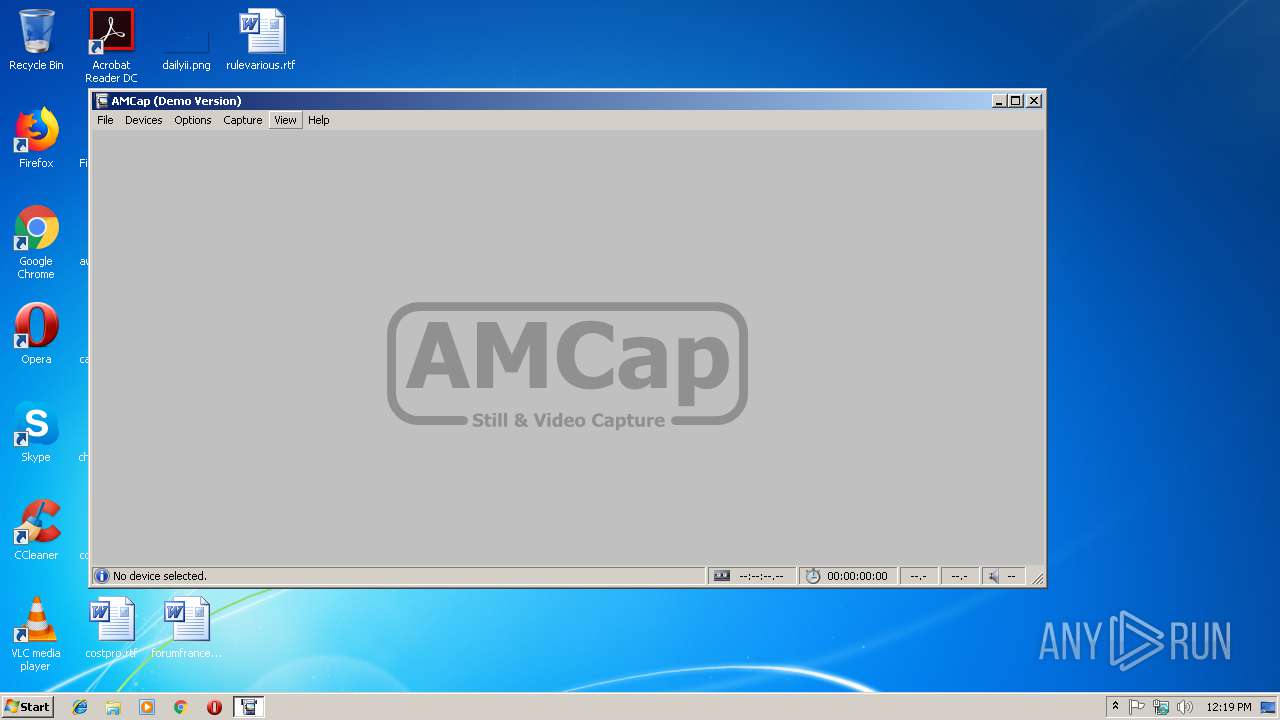
| File name: | amcap9-22-build-260-3.exe |
| Full analysis: | https://app.any.run/tasks/7e13e0f6-99bb-420c-b892-10737306fe91 |
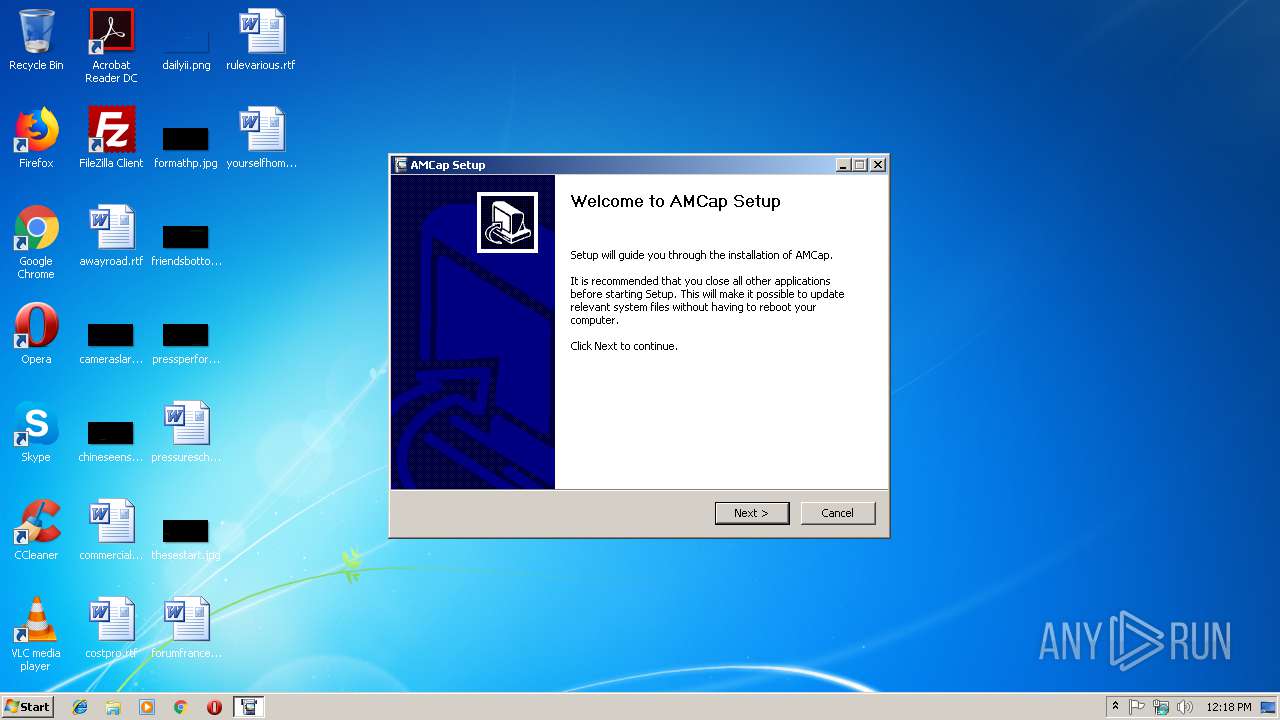
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2019, 12:18:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 421AC8F8BF9DCF2307A9BA2945B953E5 |
| SHA1: | 0BAD70BF4D568F2E7CC74C4B39A41BE0318A9AB7 |
| SHA256: | 15B3547774C9D6146EFBCDA7EDCE50E06940E3CF2C8A9A7C99A9420C3A9A5BA4 |
| SSDEEP: | 49152:5WQ4D0BydtPpbST+G631mO9OWnoMpIlMGTJRG:+tdSKGe13OcH5GT |
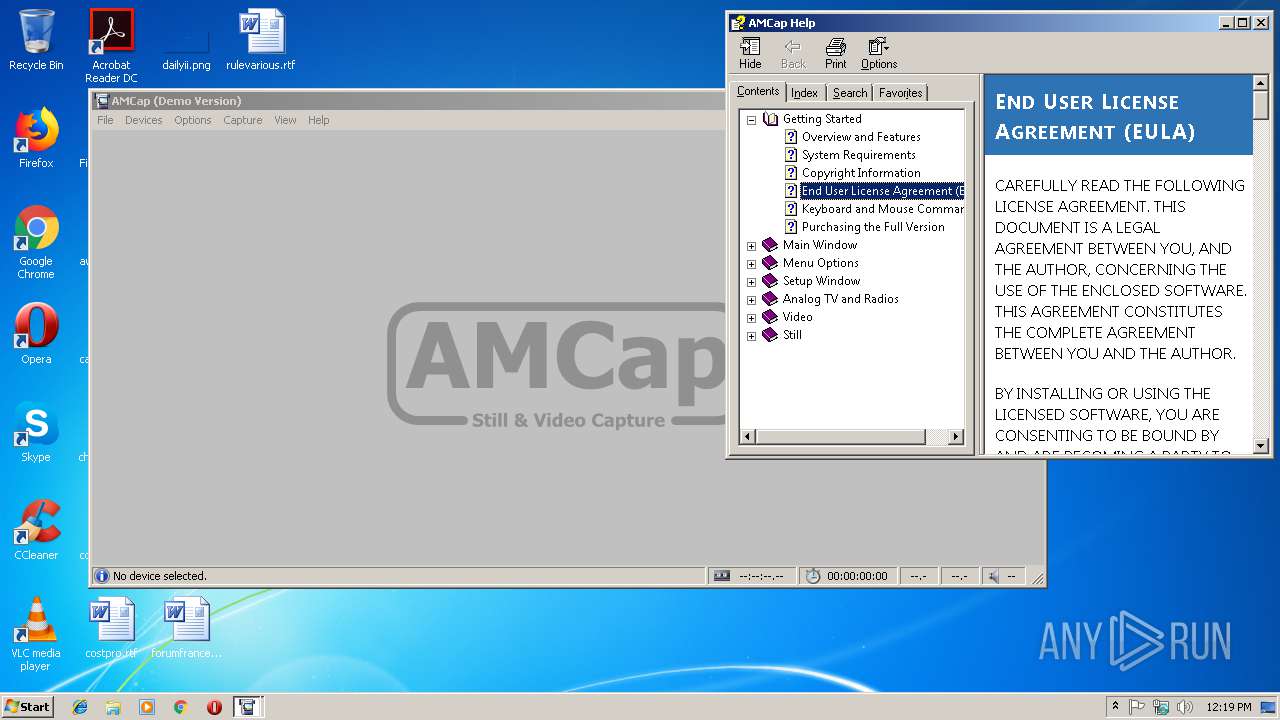
MALICIOUS
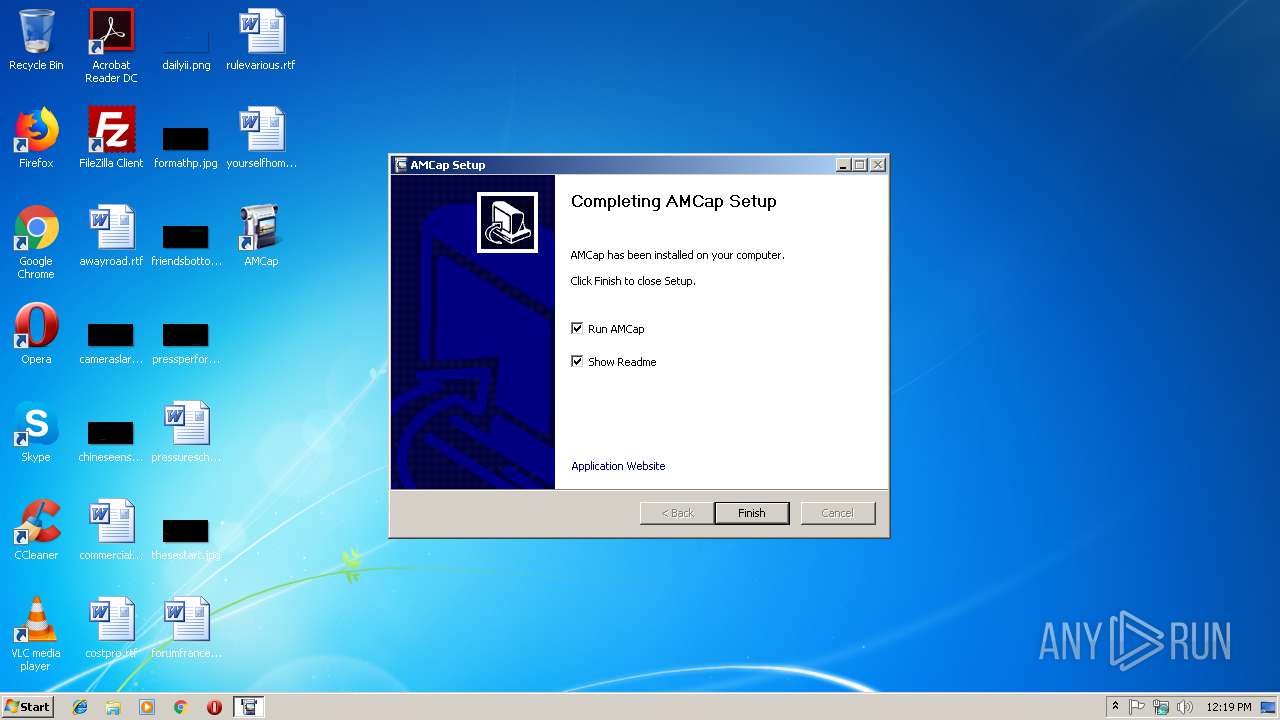
Loads dropped or rewritten executable
- amcap9-22-build-260-3.exe (PID: 3916)
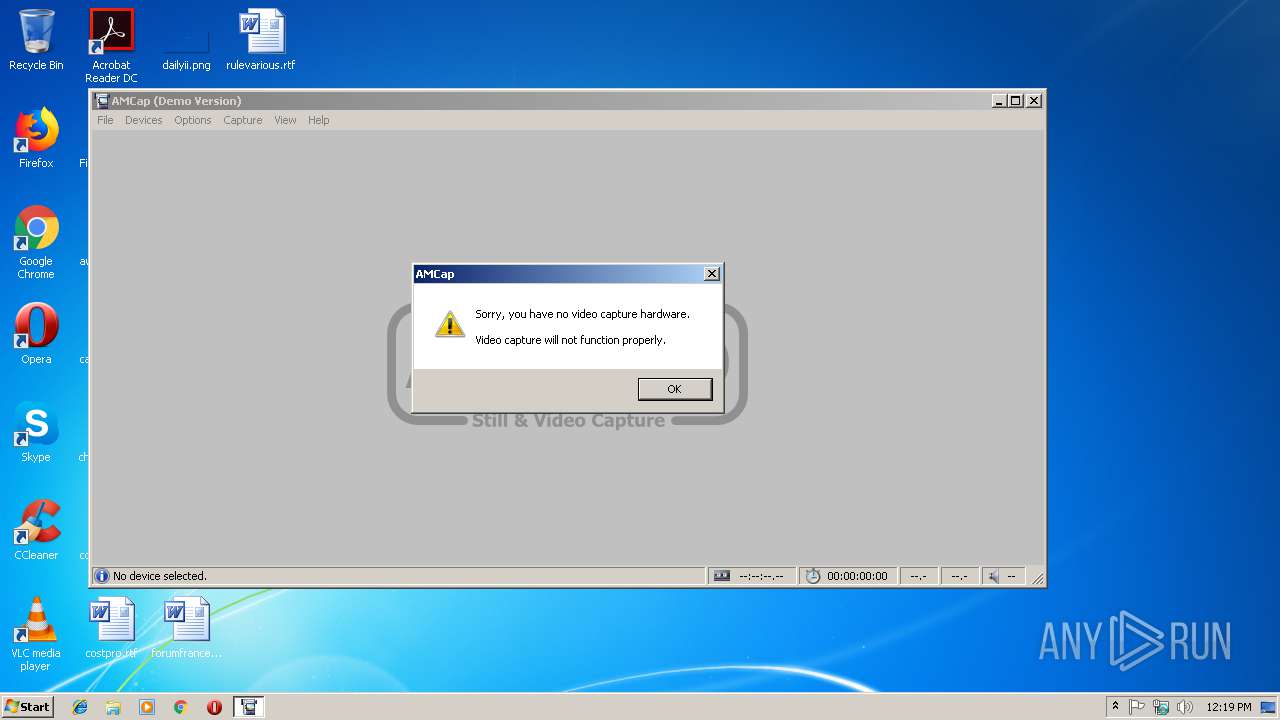
- AMCap.exe (PID: 3968)
Application was dropped or rewritten from another process
- AMCap.exe (PID: 3968)
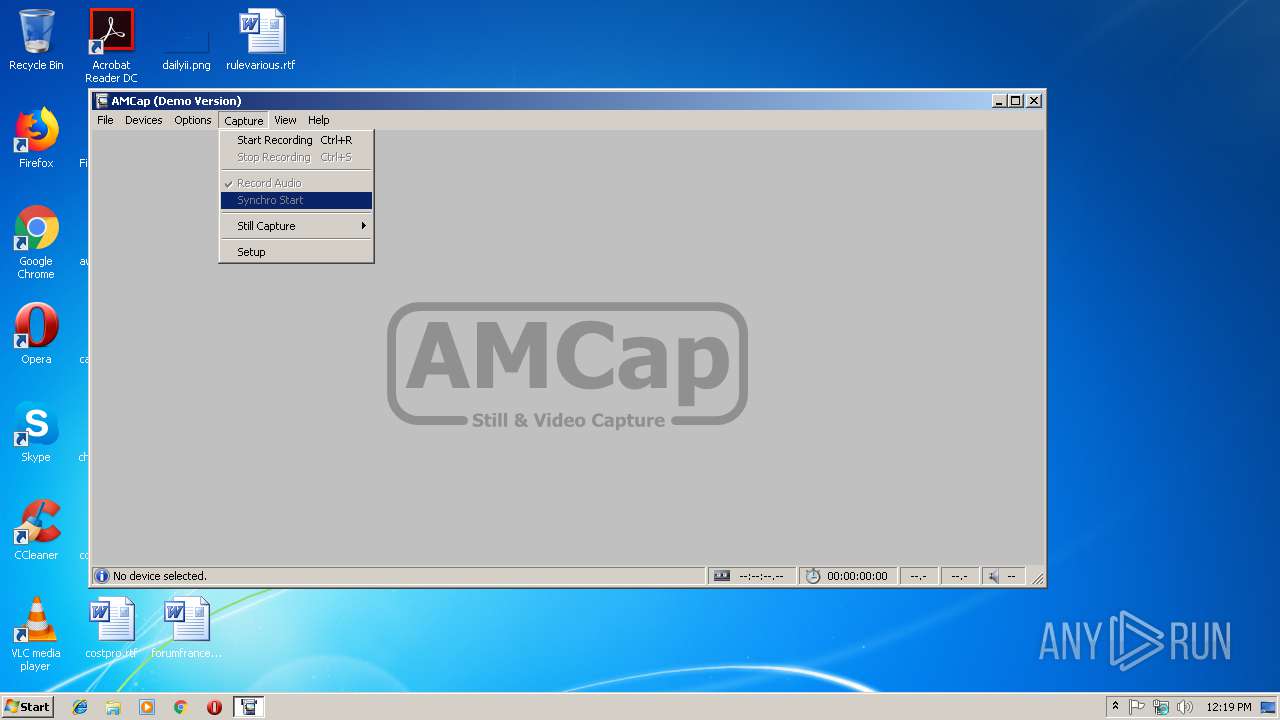
SUSPICIOUS
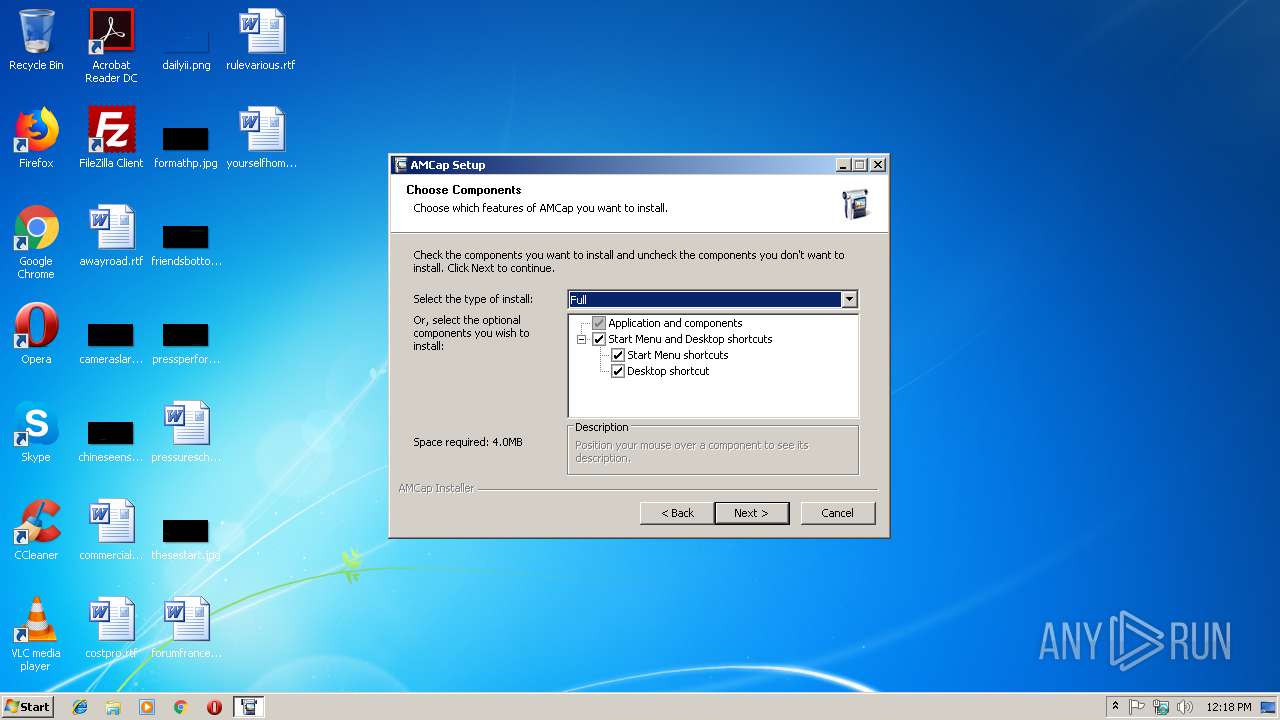
Executable content was dropped or overwritten
- amcap9-22-build-260-3.exe (PID: 3916)
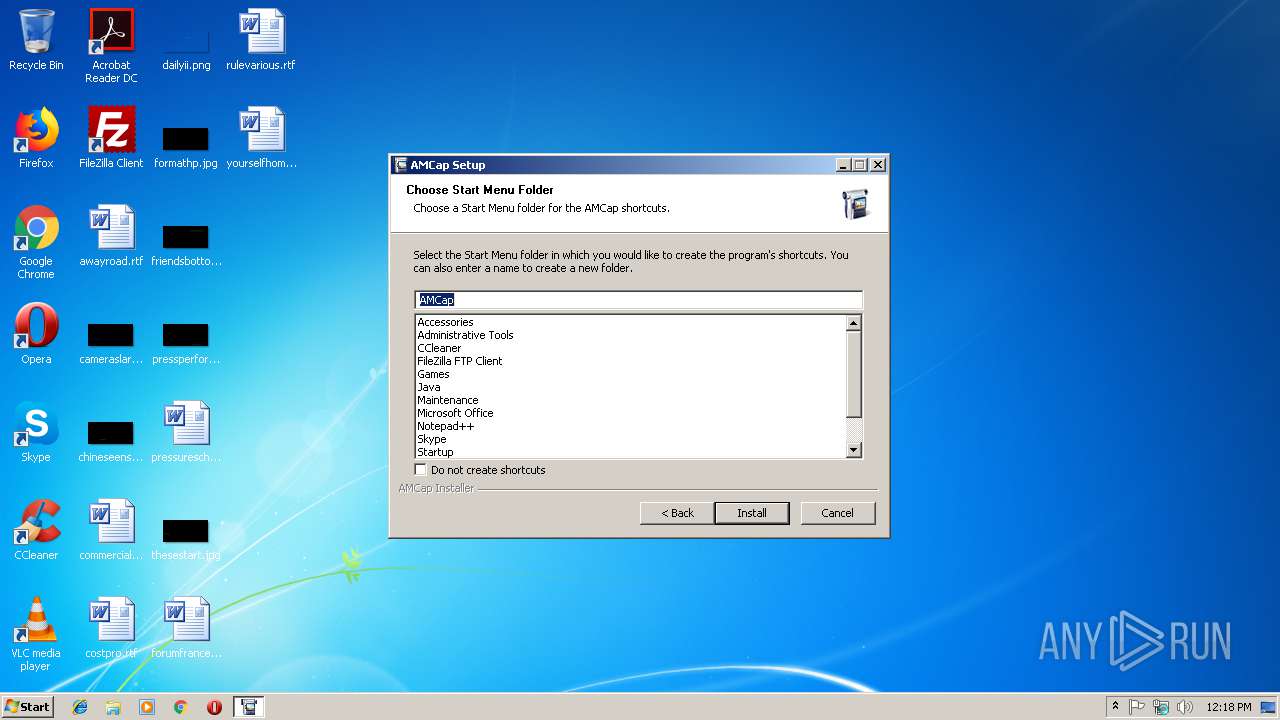
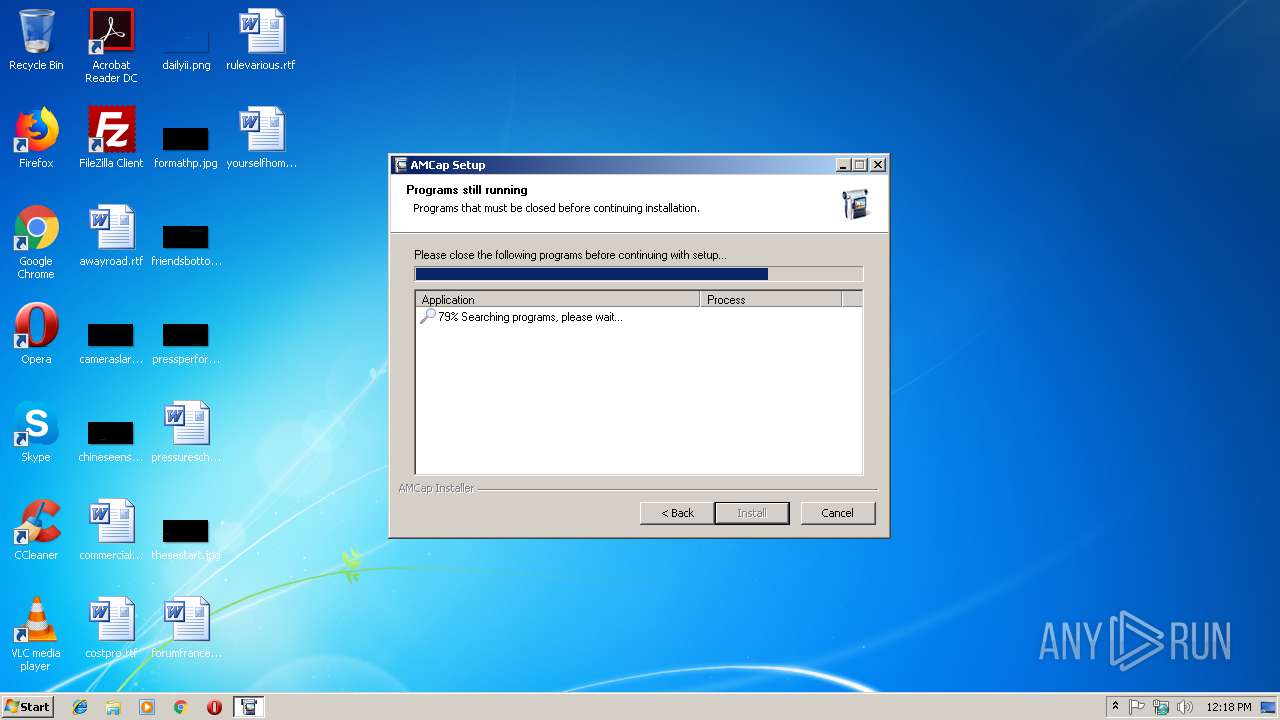
Searches for installed software
- amcap9-22-build-260-3.exe (PID: 3916)
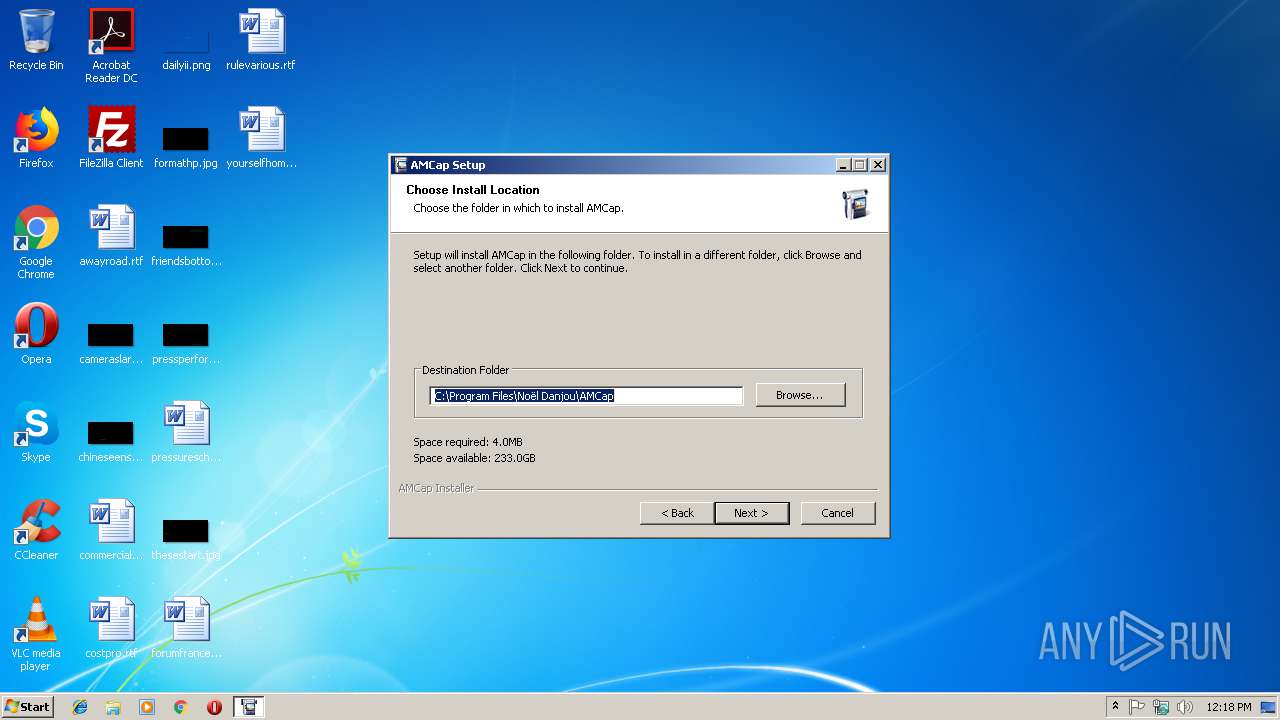
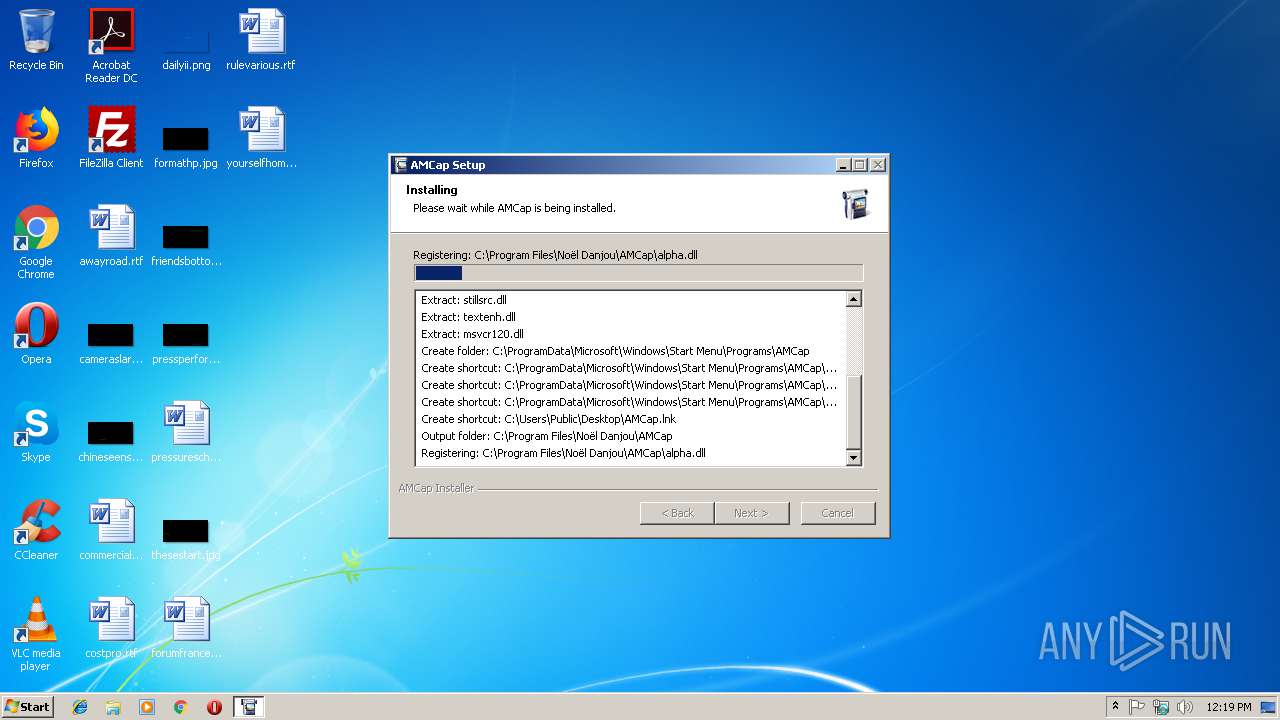
Creates files in the program directory
- amcap9-22-build-260-3.exe (PID: 3916)
Creates a software uninstall entry
- amcap9-22-build-260-3.exe (PID: 3916)
Creates COM task schedule object
- amcap9-22-build-260-3.exe (PID: 3916)
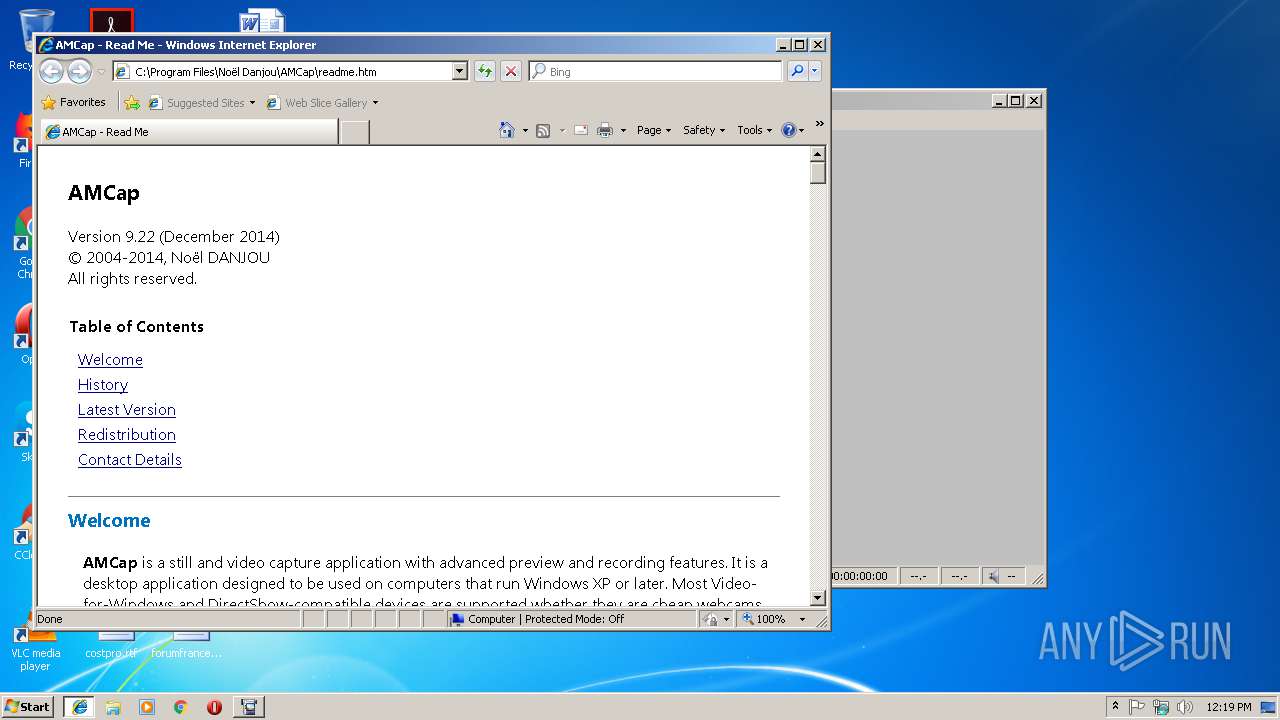
Starts Internet Explorer
- amcap9-22-build-260-3.exe (PID: 3916)
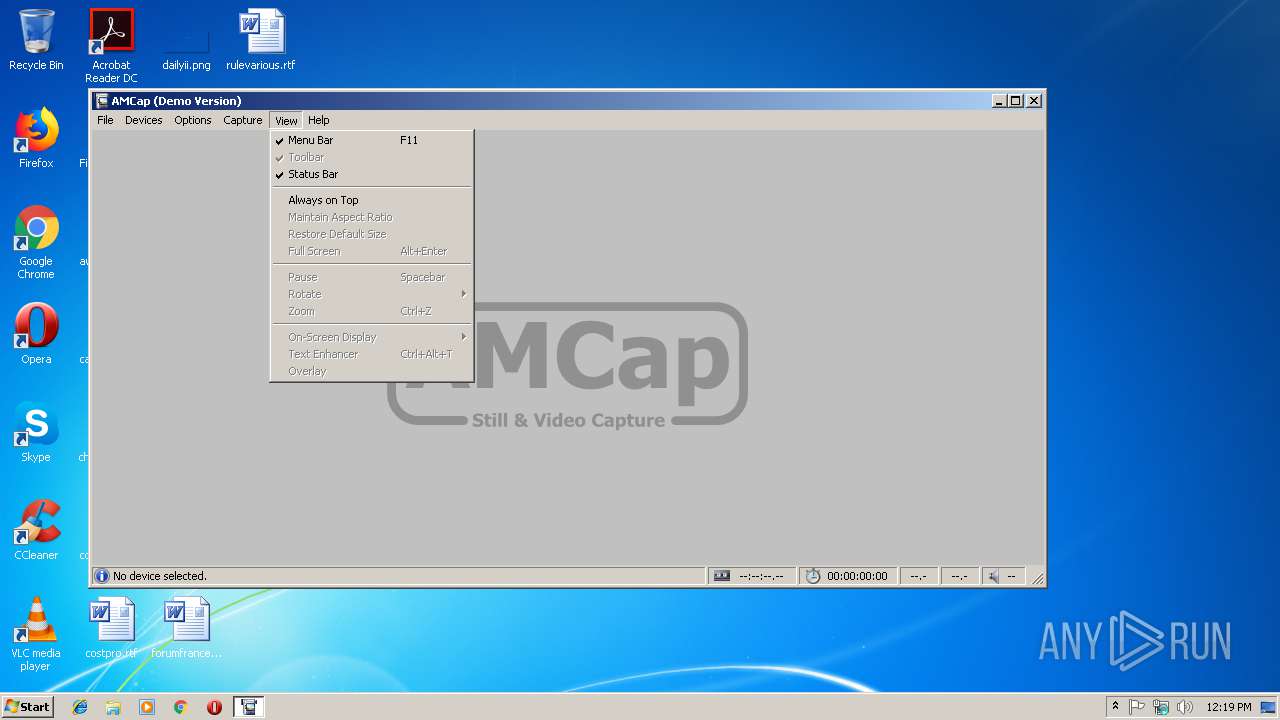
Reads internet explorer settings
- AMCap.exe (PID: 3968)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3476)
Changes internet zones settings
- iexplore.exe (PID: 2376)
Reads Internet Cache Settings
- iexplore.exe (PID: 2392)
Reads internet explorer settings
- iexplore.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:10:07 06:40:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x335a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.22.56.3 |
| ProductVersionNumber: | 9.22.56.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
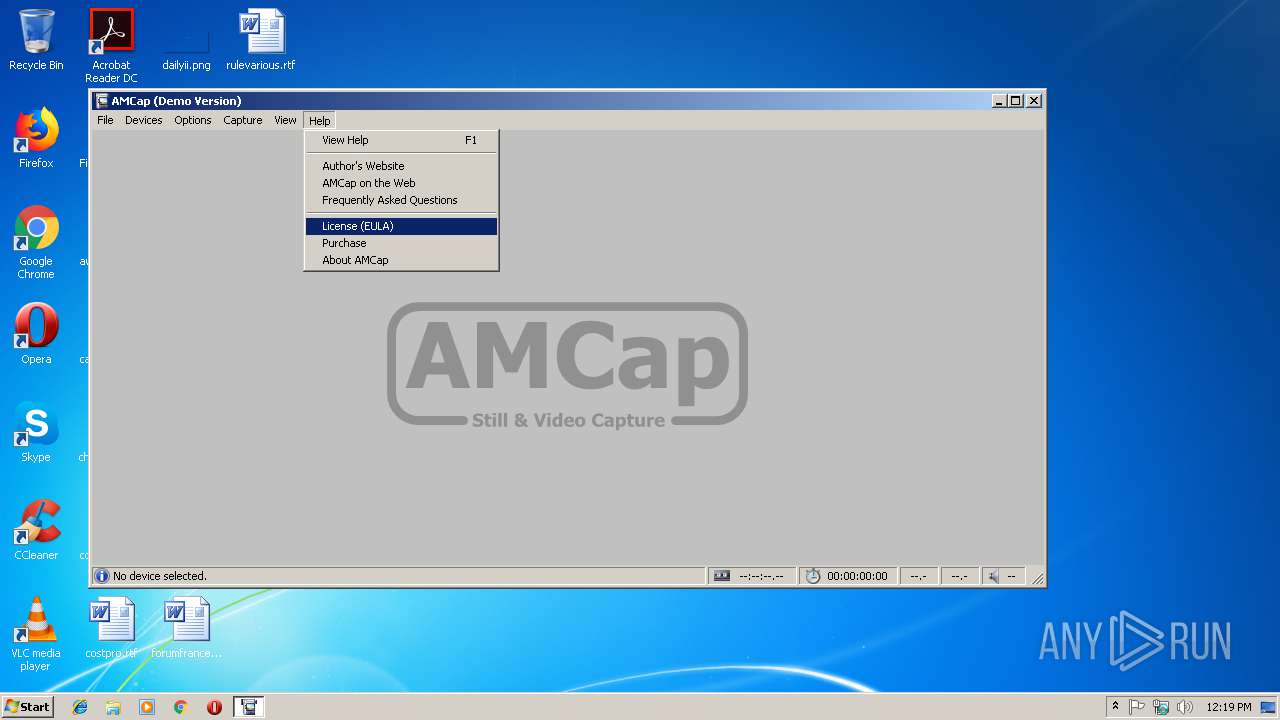
| CompanyName: | Noël Danjou |
| FileDescription: | AMCap Installer |
| FileVersion: | 9.22.56.3 |
| LegalCopyright: | © 2004-2014, Noël Danjou. All rights reserved. |
| OriginalFileName: | AMCapSetup.exe |
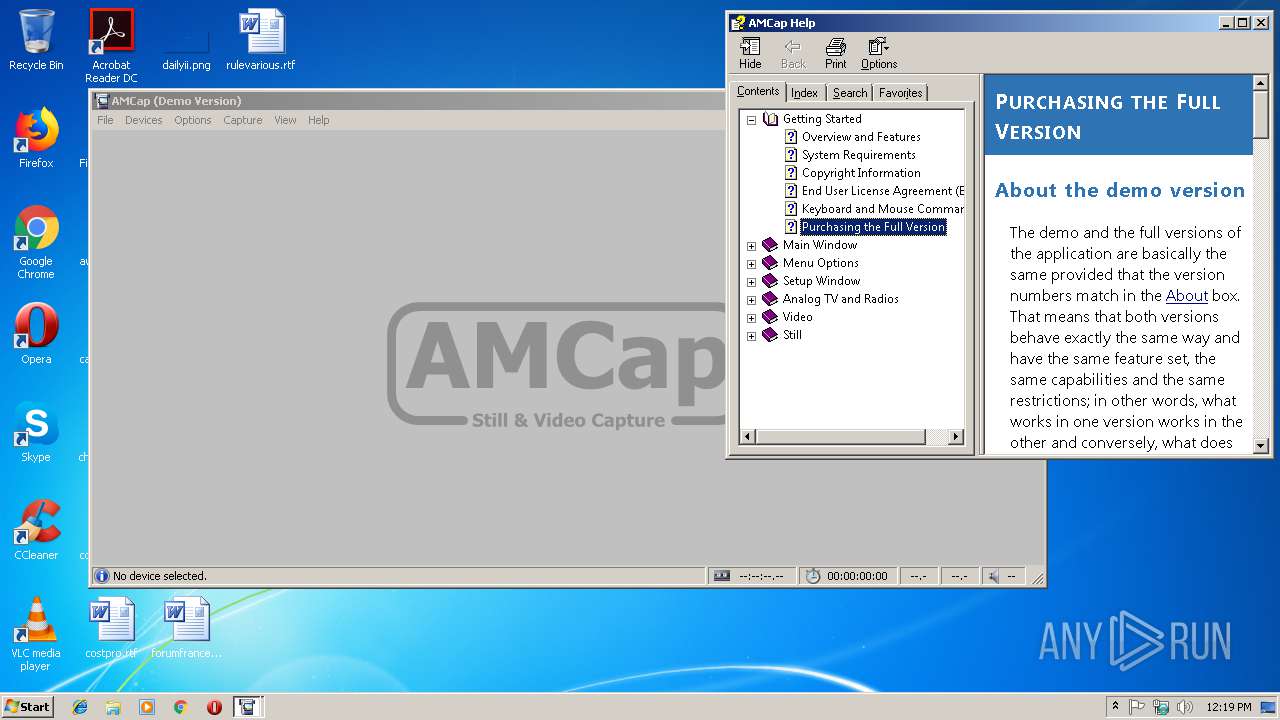
| ProductName: | AMCap (Demo Version) |
| ProductVersion: | 9.22 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Oct-2014 04:40:20 |
| Detected languages: |
|
| CompanyName: | Noël Danjou |
| FileDescription: | AMCap Installer |
| FileVersion: | 9.22.56.3 |
| LegalCopyright: | © 2004-2014, Noël Danjou. All rights reserved. |
| OriginalFilename: | AMCapSetup.exe |
| ProductName: | AMCap (Demo Version) |
| ProductVersion: | 9.22 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Oct-2014 04:40:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005EC6 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4389 |
.rdata | 0x00007000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03751 |
.data | 0x00009000 | 0x000202F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83403 |
.ndata | 0x0002A000 | 0x00030000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0005A000 | 0x0001AE60 | 0x0001B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.47426 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25141 | 1203 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.64465 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.82063 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.63516 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.3966 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 6.04006 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 6.0405 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 3.71308 | 1640 | UNKNOWN | English - United States | RT_ICON |
9 | 4.77341 | 1384 | UNKNOWN | English - United States | RT_ICON |
10 | 5.74706 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2376 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | amcap9-22-build-260-3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2376 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005C0" "00000538" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\amcap9-22-build-260-3.exe" | C:\Users\admin\AppData\Local\Temp\amcap9-22-build-260-3.exe | — | explorer.exe | |||||||||||
User: admin Company: Noël Danjou Integrity Level: MEDIUM Description: AMCap Installer Exit code: 3221226540 Version: 9.22.56.3 Modules
| |||||||||||||||
| 3476 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3916 | "C:\Users\admin\AppData\Local\Temp\amcap9-22-build-260-3.exe" | C:\Users\admin\AppData\Local\Temp\amcap9-22-build-260-3.exe | explorer.exe | ||||||||||||
User: admin Company: Noël Danjou Integrity Level: HIGH Description: AMCap Installer Exit code: 0 Version: 9.22.56.3 Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Noël Danjou\AMCap\AMCap.exe" | C:\Program Files\Noël Danjou\AMCap\AMCap.exe | — | amcap9-22-build-260-3.exe | |||||||||||
User: admin Company: Noël Danjou Integrity Level: HIGH Description: AMCap (Demo Version) Exit code: 0 Version: 9.22.260.3 Modules
| |||||||||||||||
Total events
1 126
Read events
815
Write events
308
Delete events
3
Modification events
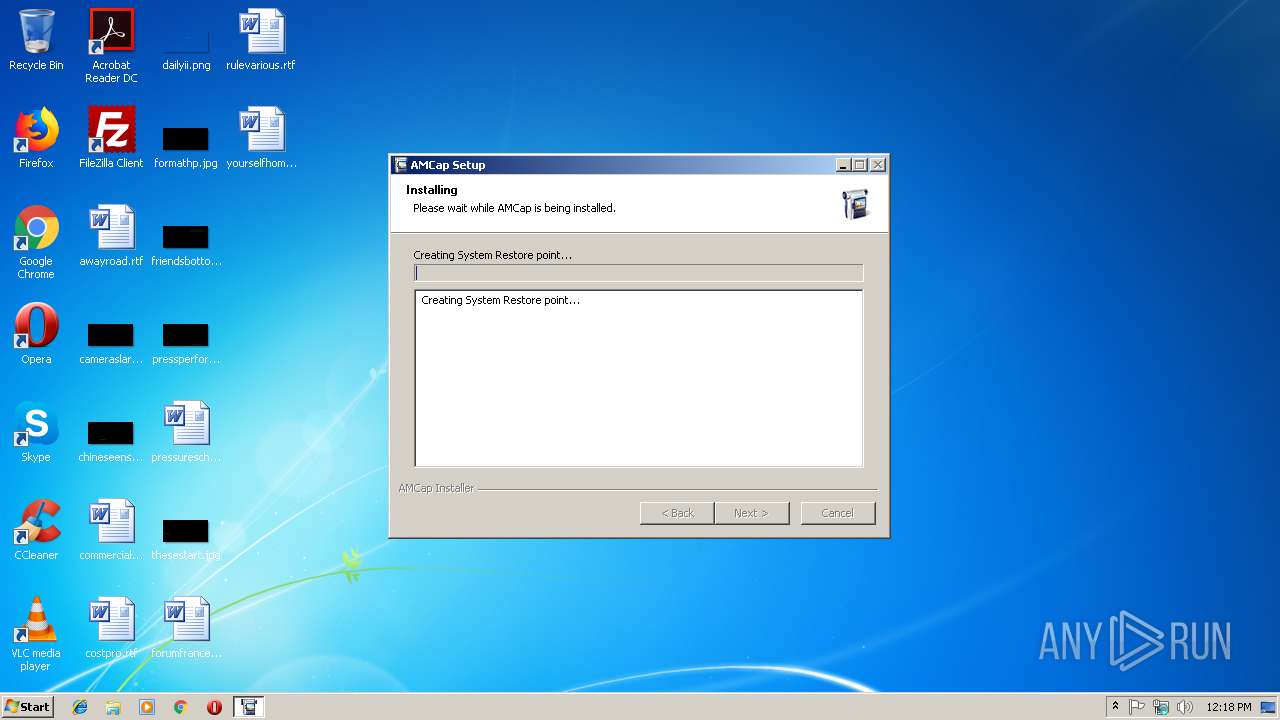
| (PID) Process: | (3916) amcap9-22-build-260-3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000000E4BFBA595ADD4014C0F0000AC0C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3916) amcap9-22-build-260-3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000000E4BFBA595ADD4014C0F0000AC0C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005CBD4EA695ADD401940D0000080C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005CBD4EA695ADD401940D0000A00F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005CBD4EA695ADD401940D0000FC0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005CBD4EA695ADD401940D00009C0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000108253A695ADD401940D0000A00F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000006AE455A695ADD401940D0000080C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000C44658A695ADD401940D00009C0F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000001EA95AA695ADD401940D0000FC0B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
15
Suspicious files
6
Text files
133
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3916 | amcap9-22-build-260-3.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3916 | amcap9-22-build-260-3.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\StartMenu.dll | executable | |
MD5:— | SHA256:— | |||
| 3916 | amcap9-22-build-260-3.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{e89c5a39-2f97-4739-b639-e9698f952bd9}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\nsDialogs.dll | executable | |
MD5:DBDBF4017FF91C9DE328697B5FD2E10A | SHA256:BE60A00F32924CCBE03F9914E33B8E1AD8C8A1CA442263A69896EFBA74925B36 | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\LangDLL.dll | executable | |
MD5:CD24BD16342D02D7665DDF304725046A | SHA256:7A296C111F54CA35369070B6776E787A4A588605F6F6D5ACF3420731AF7BCF23 | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2848 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\LockedList.dll | executable | |
MD5:DC2959D52AEC24DC5E7C8E5CEDA1B5F6 | SHA256:27A20E226FEE71E887D63469C6EF11506BECCB3826DF09B2E7559636841F84A9 | |||
| 3916 | amcap9-22-build-260-3.exe | C:\Users\admin\AppData\Local\Temp\nsqF090.tmp\System.dll | executable | |
MD5:3E6BF00B3AC976122F982AE2AADB1C51 | SHA256:4FF9B2678D698677C5D9732678F9CF53F17290E09D053691AAC4CC6E6F595CBE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2376 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2376 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |