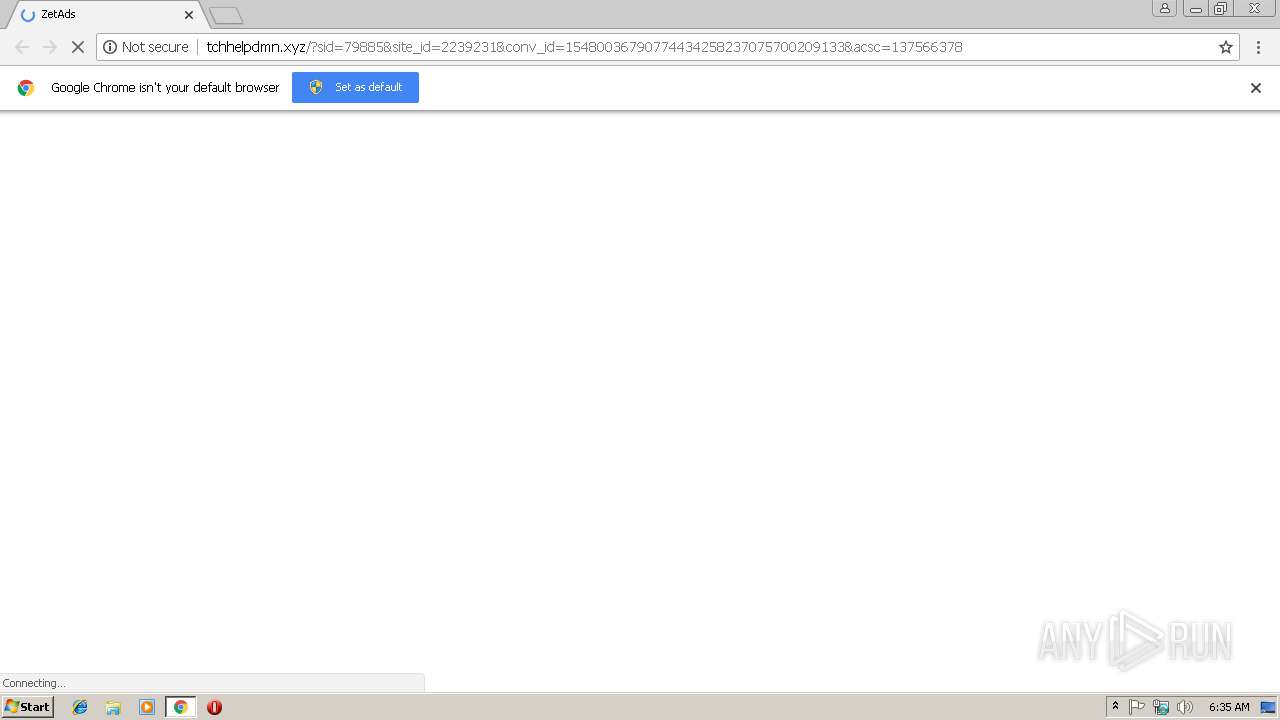
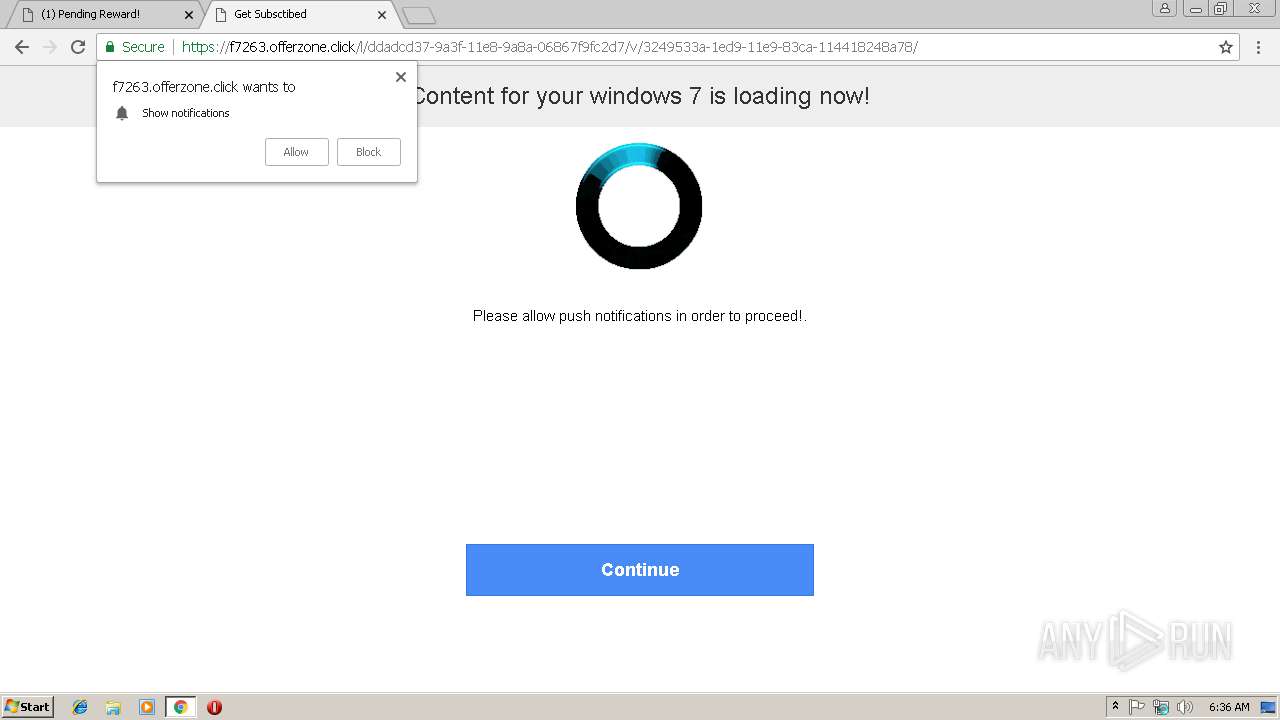
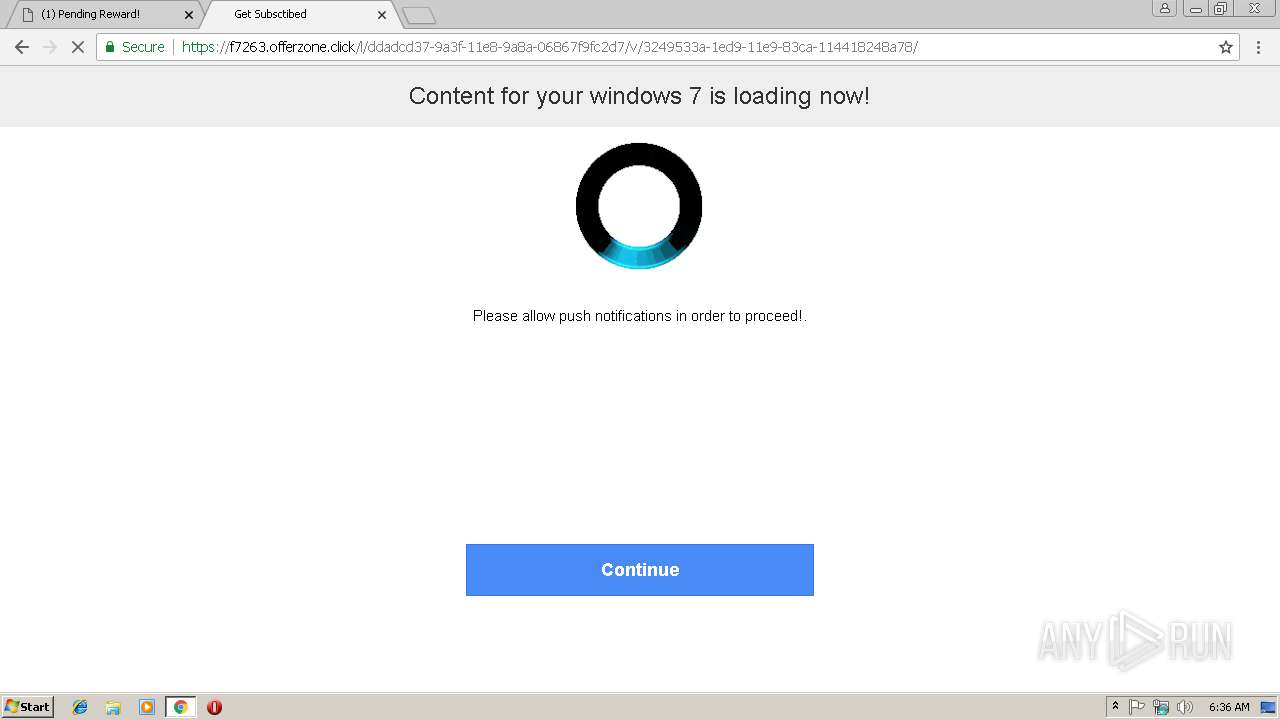
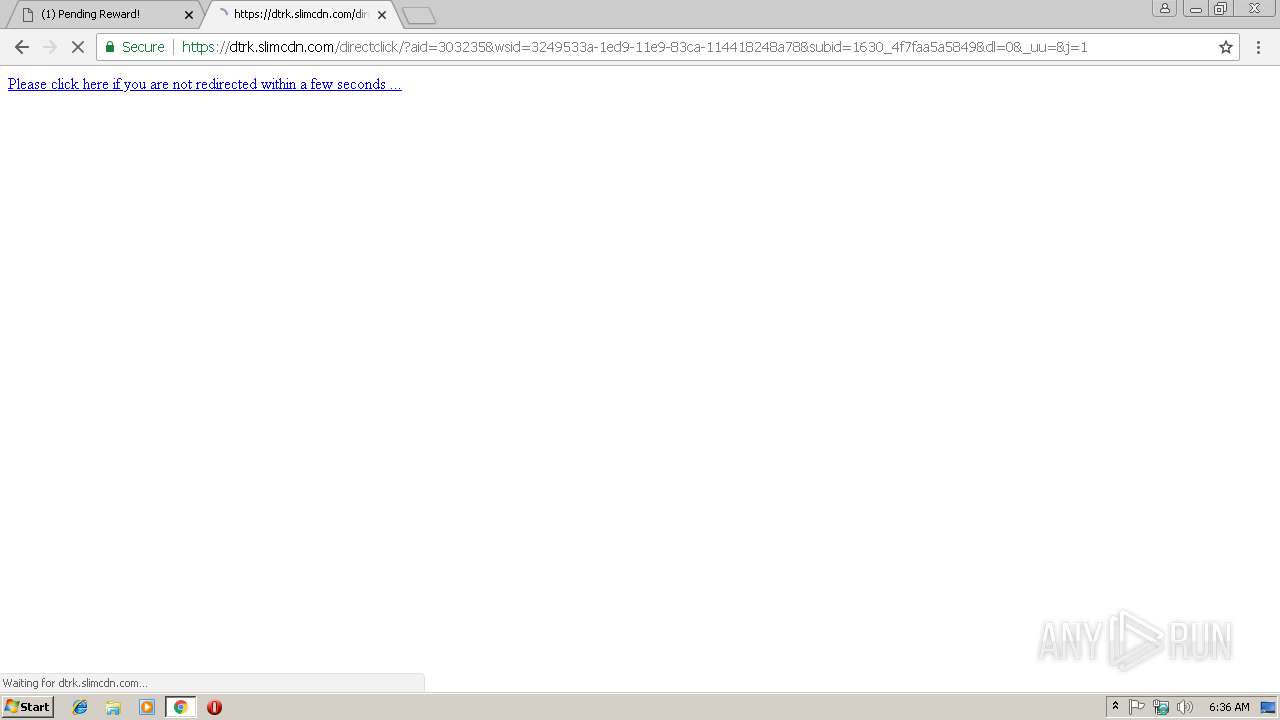
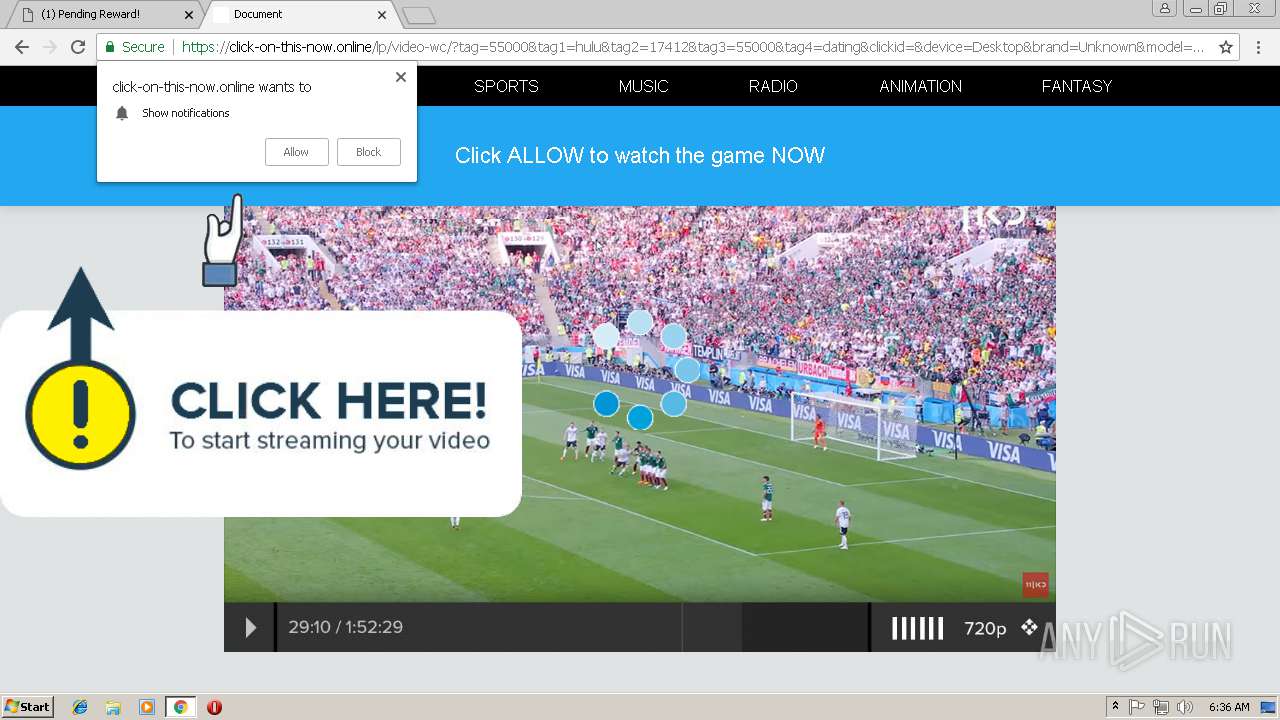
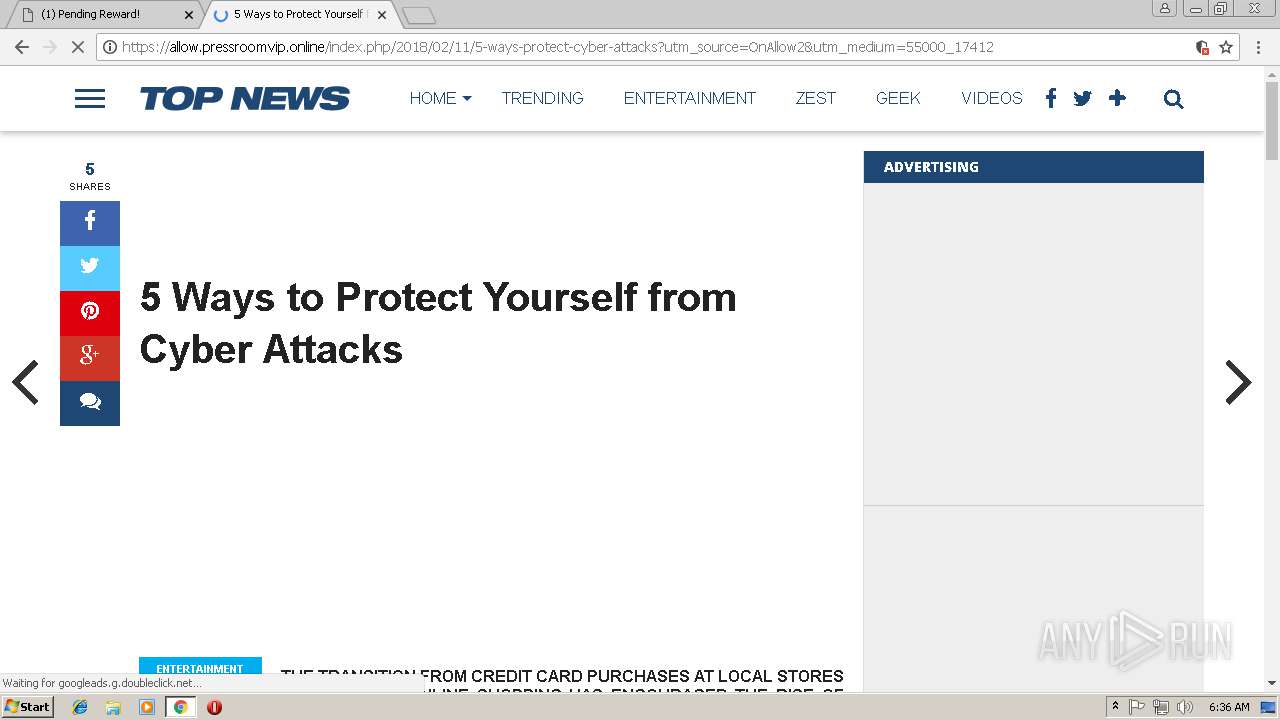
| URL: | http://tchhelpdmn.xyz/?sid=79885&site_id=2239231&conv_id=15480036790774434258237075700209133&acsc=137566378 |
| Full analysis: | https://app.any.run/tasks/0763a5a1-663a-44de-ab97-6fcd1049c8dd |
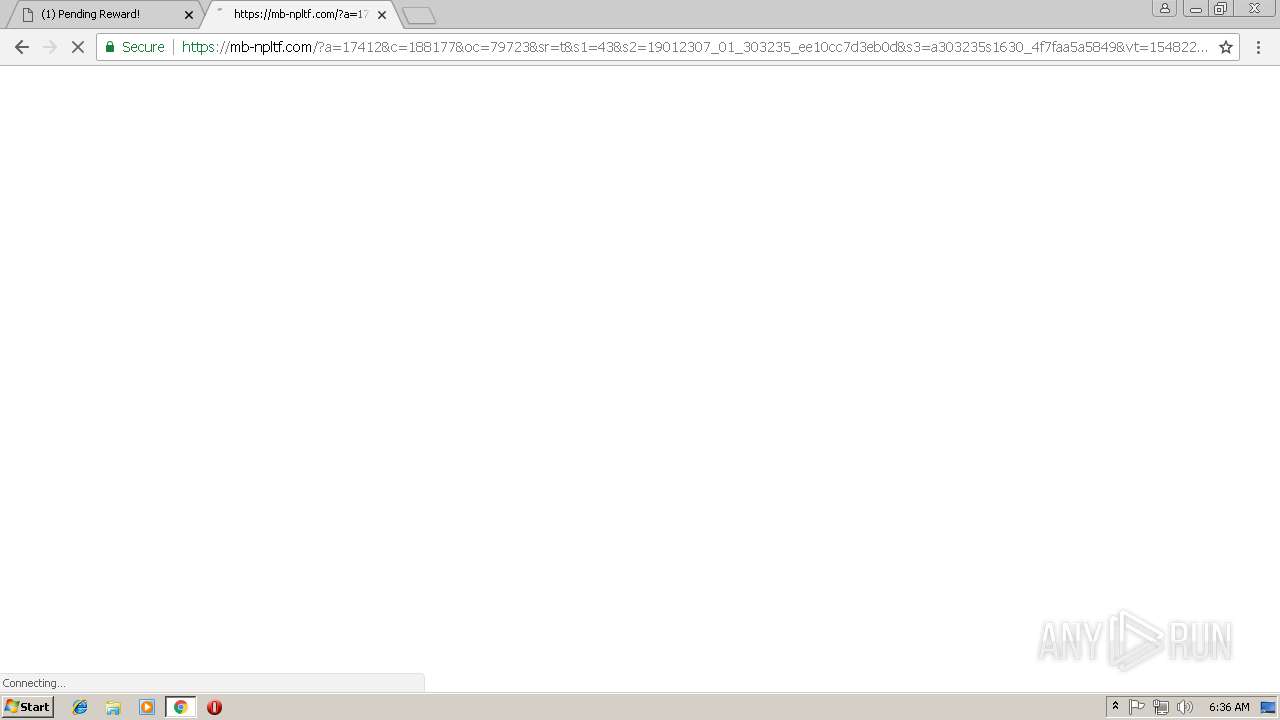
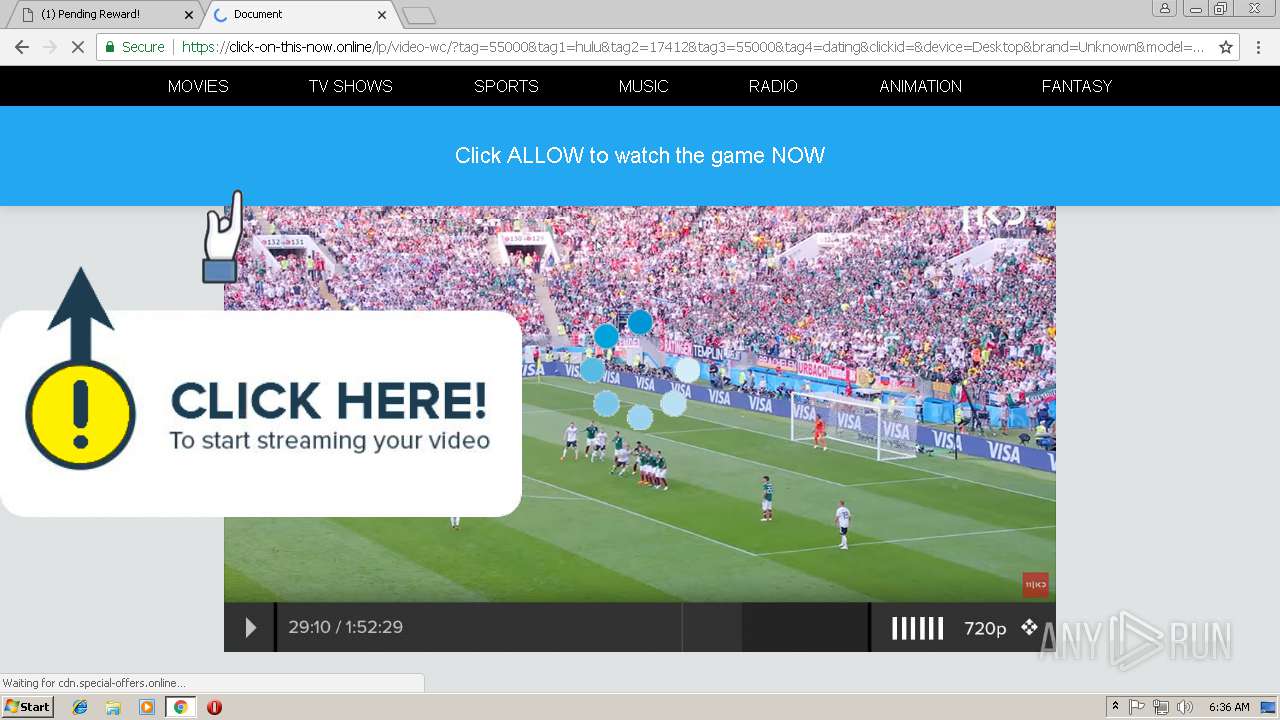
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2019, 06:35:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23C5A03CDF0DE47520589F10B04F9240 |
| SHA1: | 8E1A7462CAC08CC89094079AEBAFF016F9ACA74D |
| SHA256: | 15B02310C45A59D4AAC78CCAD21CAB68C468C06B7F66A975CE199173696C212B |
| SSDEEP: | 3:N1KKGUcLLAKd9vf+A6vDdL2Mbs8TvVhRkXqVdhj:CKZcHXvf+A6vBnbLvVhgqbhj |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 3364)
Application launched itself
- chrome.exe (PID: 3364)
Connects to unusual port
- chrome.exe (PID: 3364)
Changes settings of System certificates
- chrome.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,15897119828604457581,10932583172939042683,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=A7EA0A446DD1B99A8D4D51BB8EA39CF4 --mojo-platform-channel-handle=1656 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,15897119828604457581,10932583172939042683,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=7A2F67EFBE847F298F8A761BC417899A --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,15897119828604457581,10932583172939042683,131072 --enable-features=PasswordImport --service-pipe-token=51ED6FA61BDC52E740339FBF3FD5FF58 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51ED6FA61BDC52E740339FBF3FD5FF58 --renderer-client-id=4 --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://tchhelpdmn.xyz/?sid=79885&site_id=2239231&conv_id=15480036790774434258237075700209133&acsc=137566378 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3368 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,15897119828604457581,10932583172939042683,131072 --enable-features=PasswordImport --service-pipe-token=490C0A1AAACE95E8BD91CFEA6986B0A1 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=490C0A1AAACE95E8BD91CFEA6986B0A1 --renderer-client-id=3 --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,15897119828604457581,10932583172939042683,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=CB26ECEEA3738065D5AE51DD4A2B2B55 --mojo-platform-channel-handle=3640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
520
Read events
473
Write events
44
Delete events
3
Modification events
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3364-13192698943598750 |
Value: 259 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3364-13192698943598750 |
Value: 259 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
38
Text files
75
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\af315013-3a99-47bb-9c68-f28a7f916bfa.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\070d8e05-c664-4faf-ba62-410090aa8f8a.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1992ff.TMP | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19933d.TMP | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF19933d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
86
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3364 | chrome.exe | GET | 302 | 18.153.1.93:80 | http://2crg1.voluumtrk.com/b228d82f-5b30-40ed-ac2e-434830bd5a51?tag=55000&tag1=hulu&tag2=17412&tag3=55000&tag4=dating&clickid=&device=Desktop&brand=Unknown&model=Unknown&country=LT&affid=55000&subid=17412&ln=en&cid=%7Btransaction_id%7D&useragent=%7Bvar:useragent%7D&ip=85.206.166.82&bv=Chrome%2068&as=pc | US | — | — | suspicious |
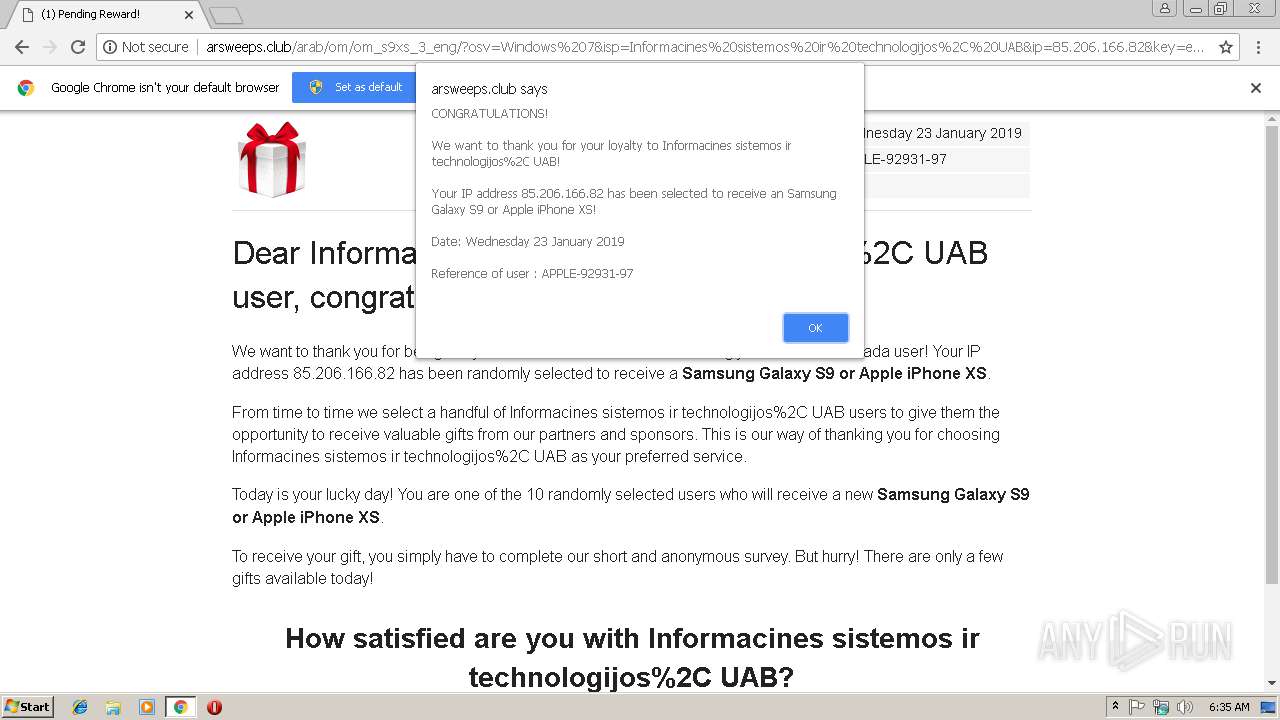
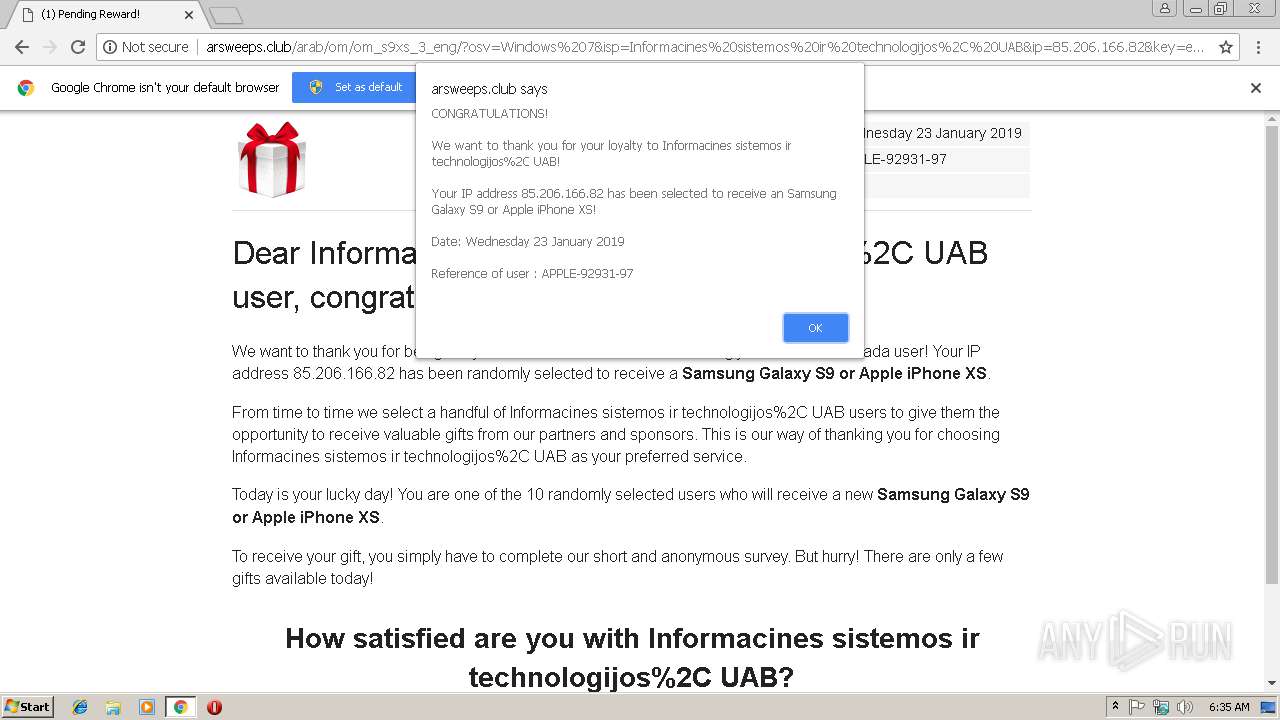
3364 | chrome.exe | GET | 404 | 159.89.14.246:80 | http://arsweeps.club/favicon.ico | US | html | 290 b | suspicious |
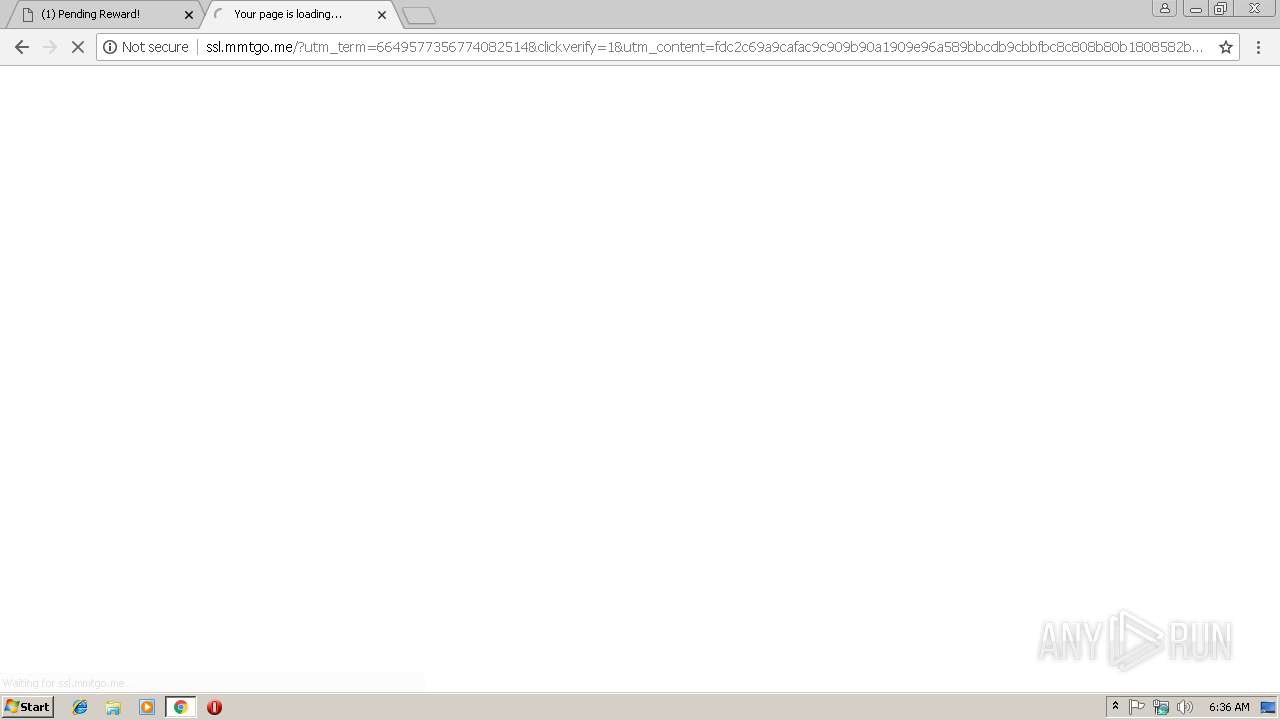
3364 | chrome.exe | GET | 200 | 198.143.165.219:80 | http://ssl.mmtgo.me/?utm_medium=ac76a9c1ea8f539604b03991d9b0c55b26ddcfa2&utm_campaign=rmt&1=10365875&2=49564fc3204b4f12837d86ab12ea337afd11 | US | html | 2.25 Kb | suspicious |
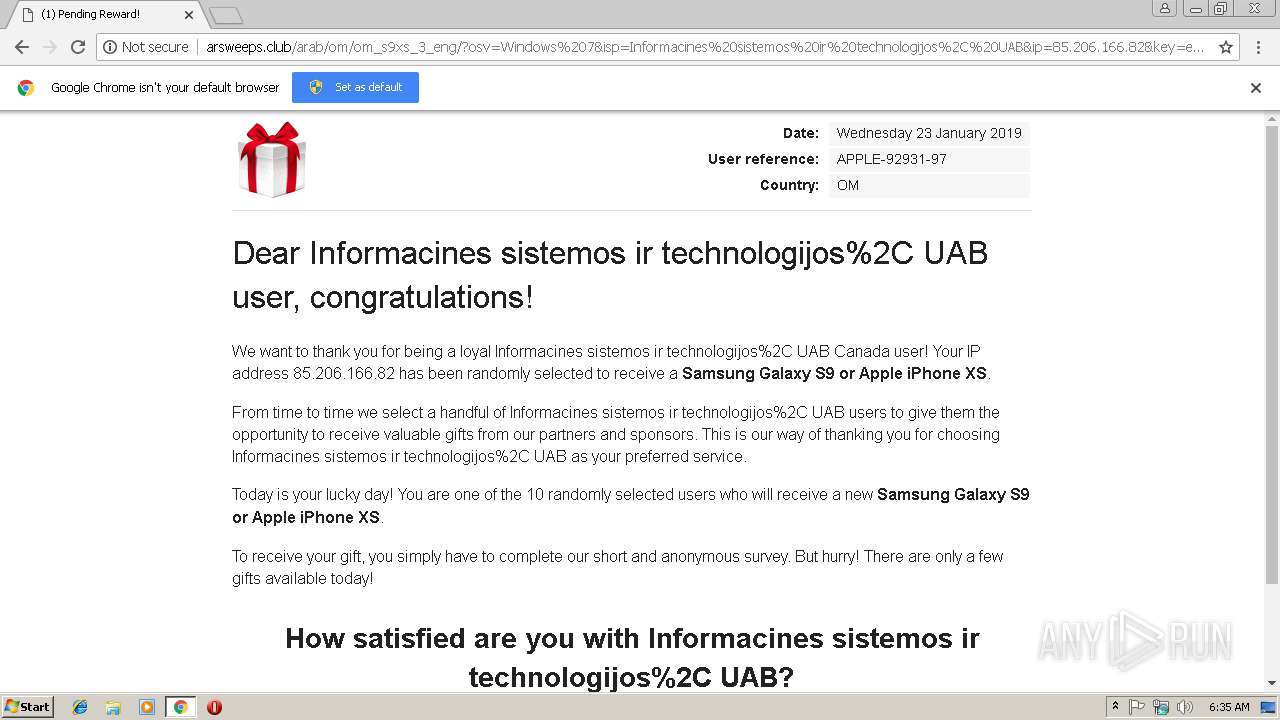
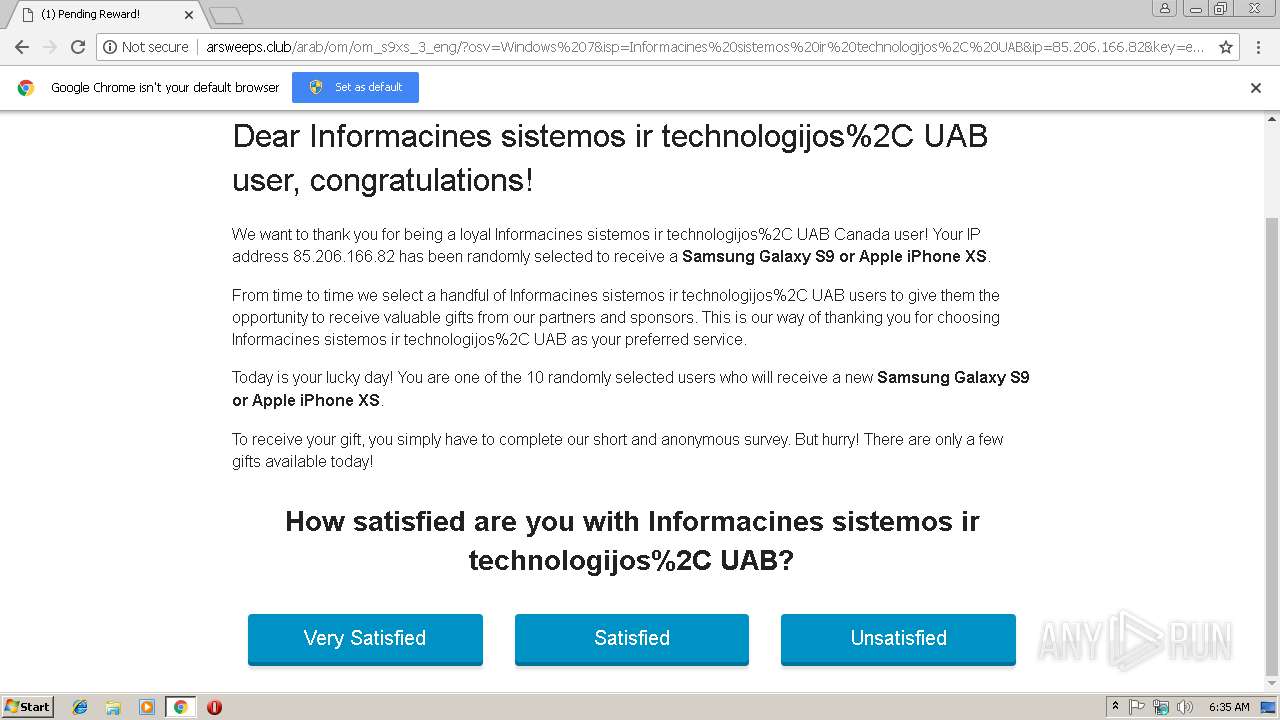
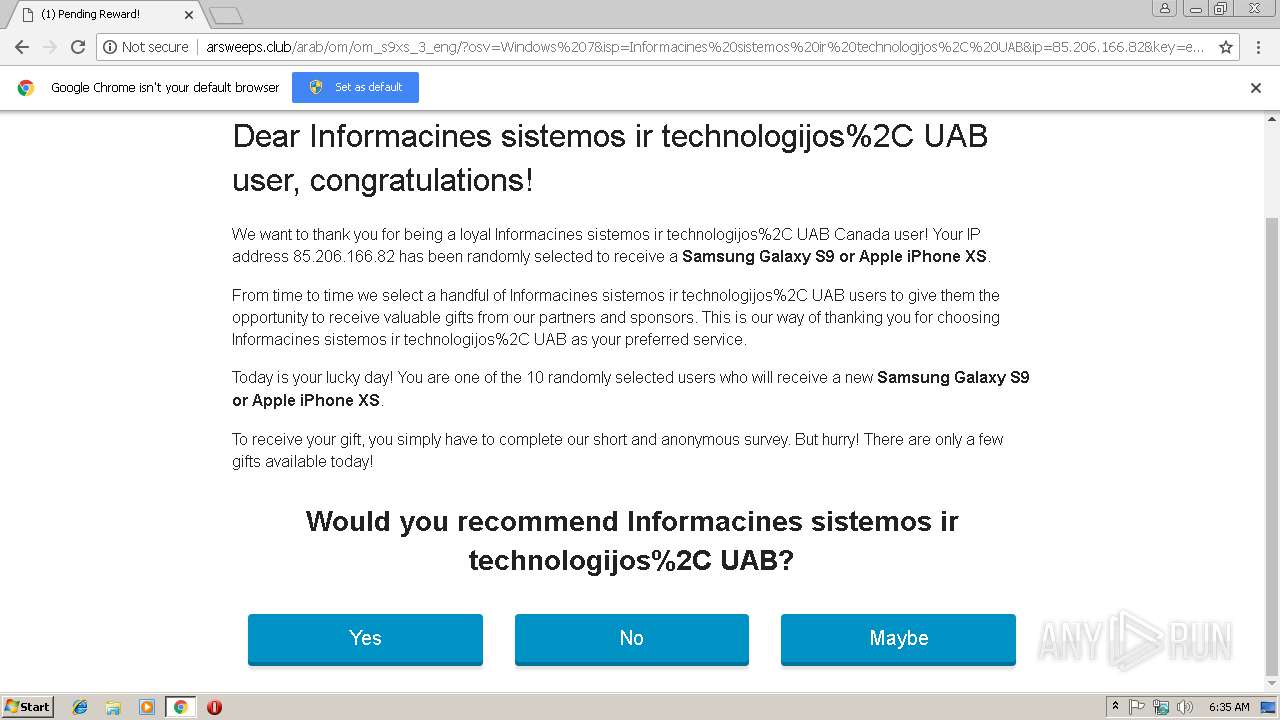
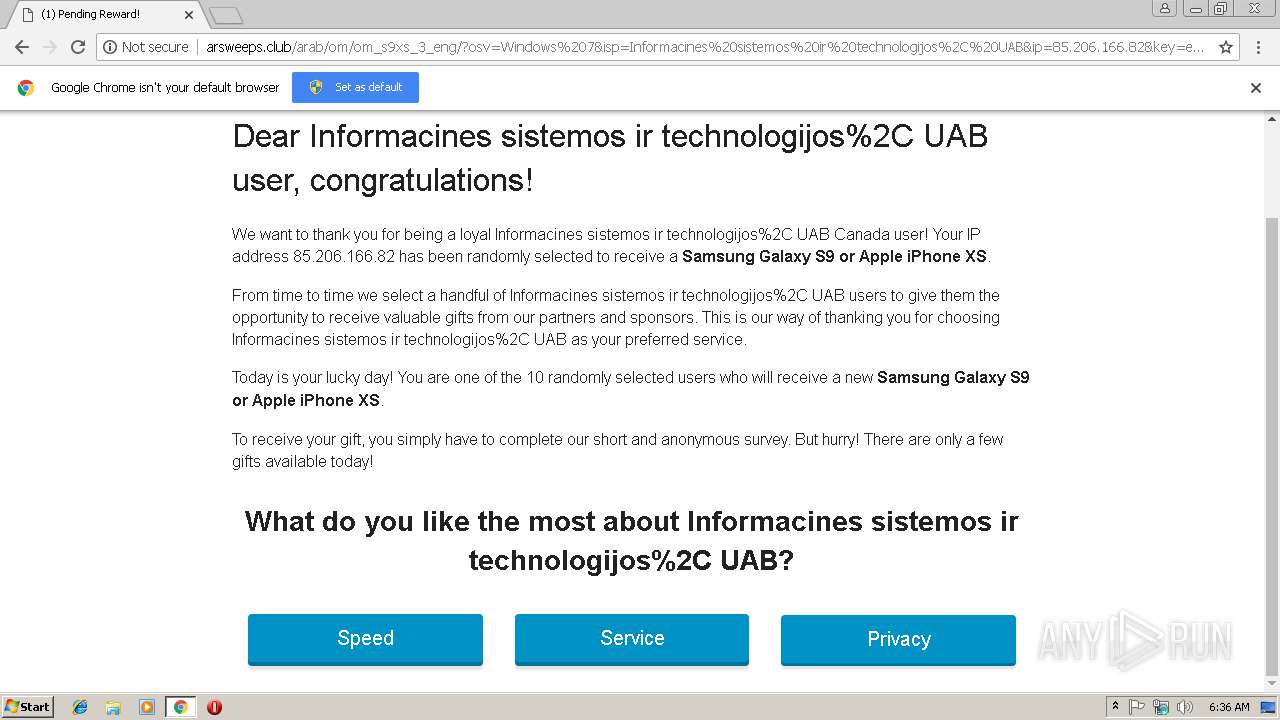
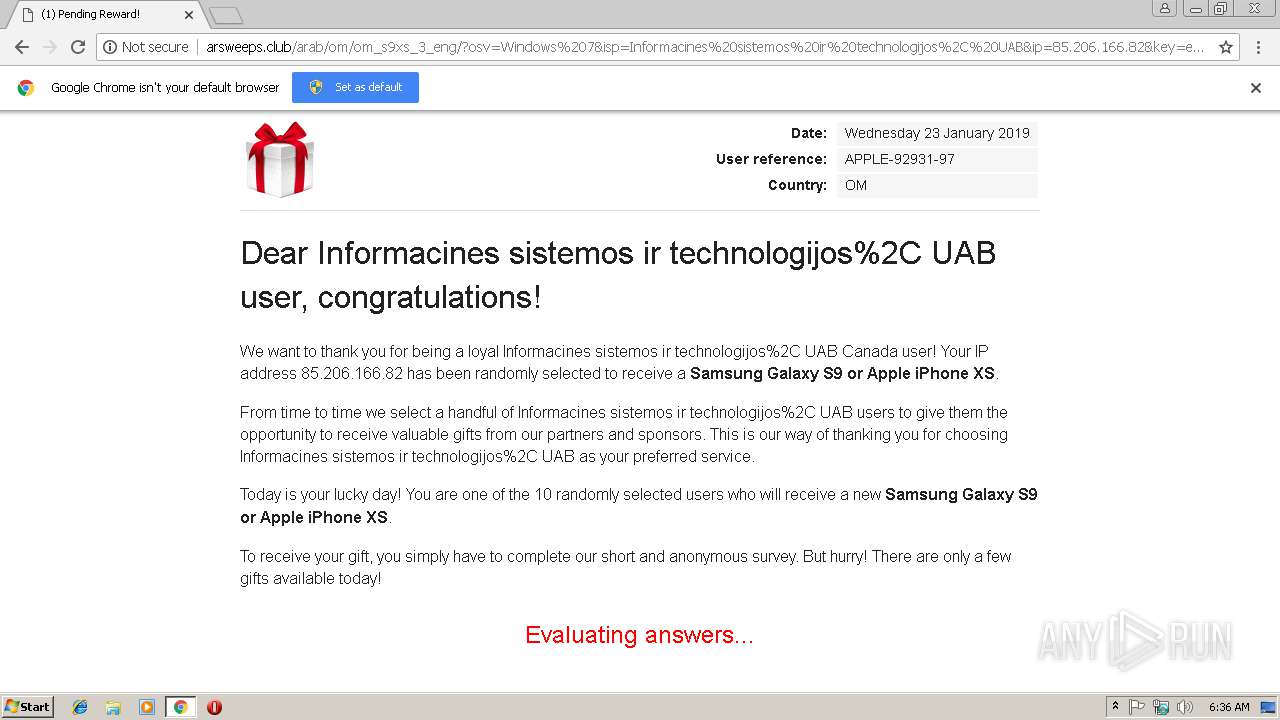
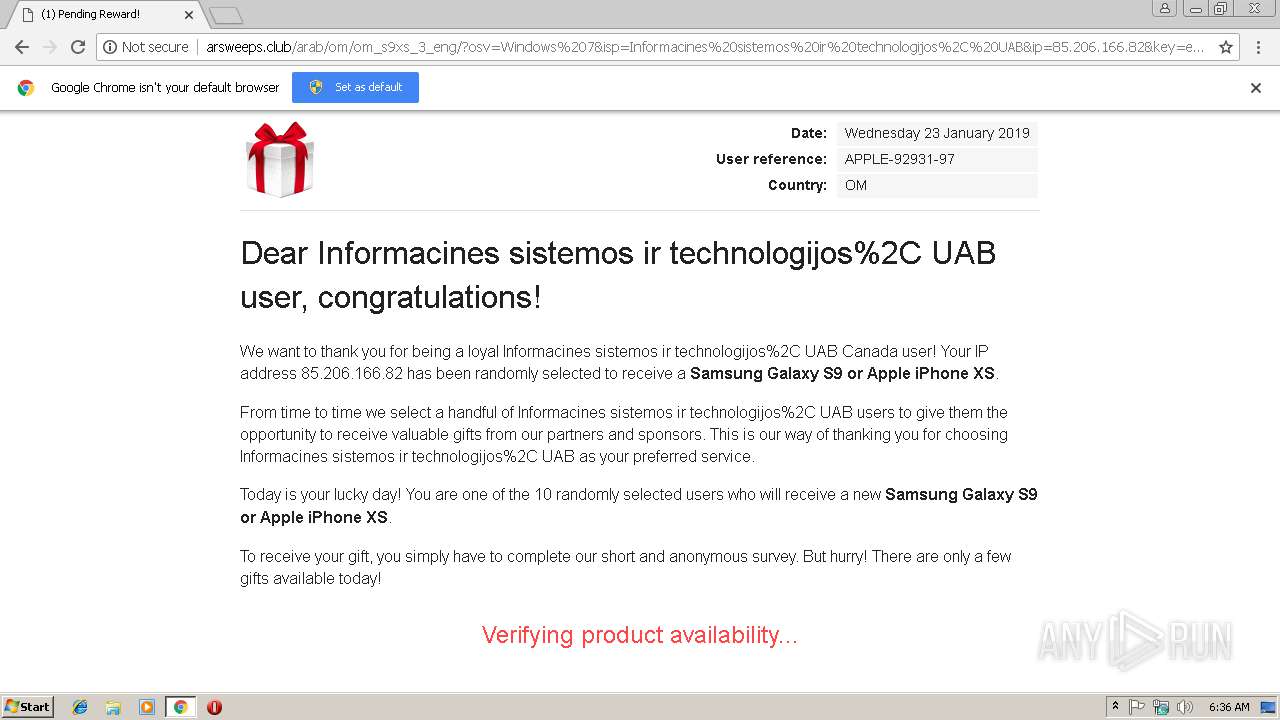
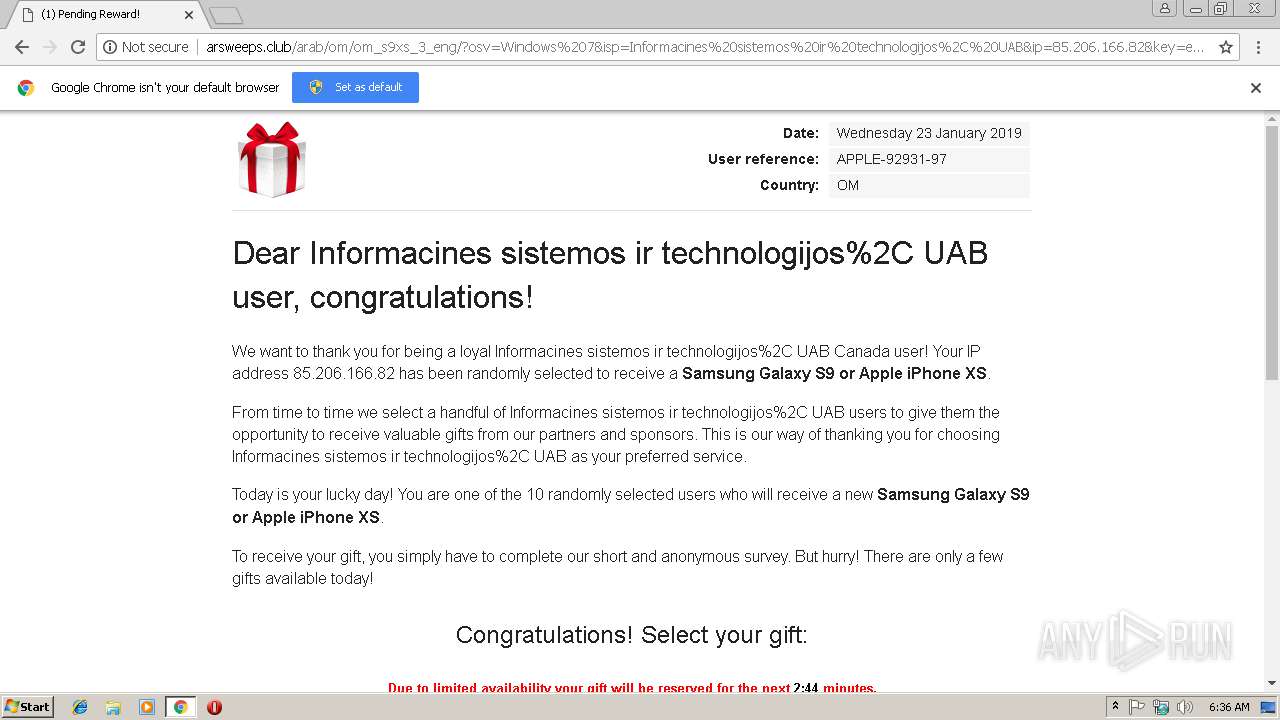
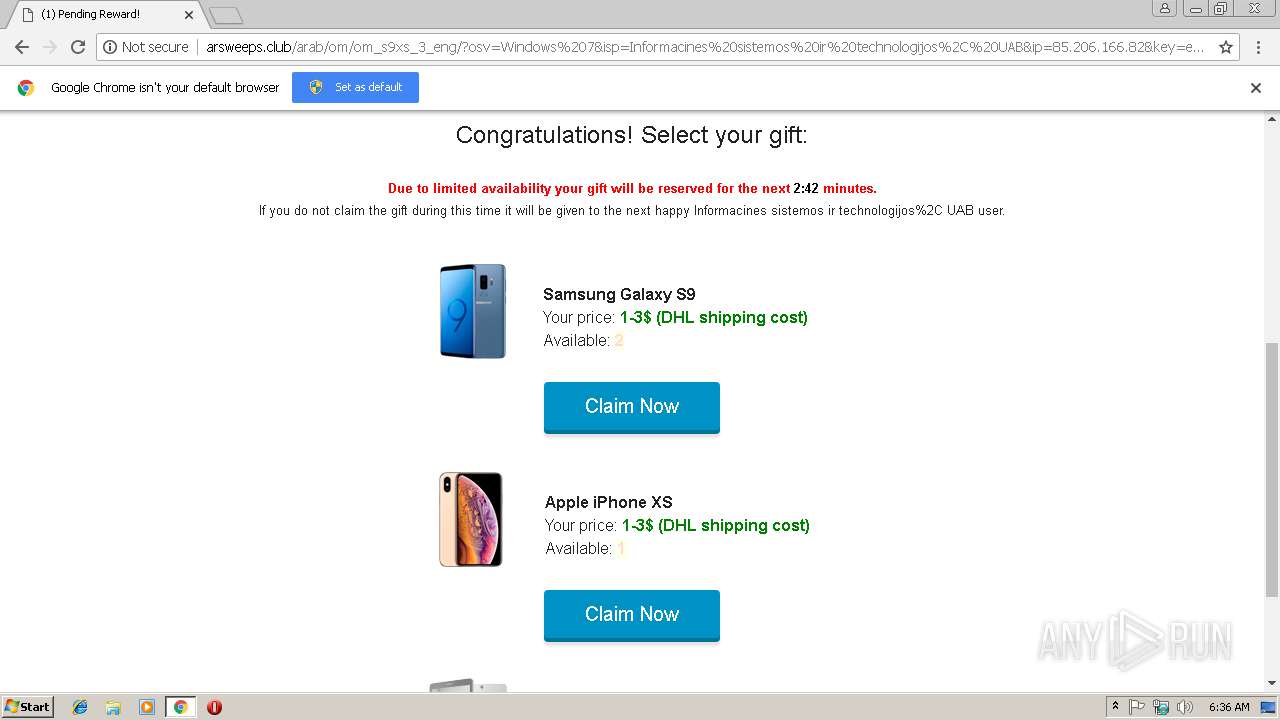
3364 | chrome.exe | GET | 200 | 159.89.14.246:80 | http://arsweeps.club/arab/om/om_s9xs_3_eng/?osv=Windows%207&isp=Informacines%20sistemos%20ir%20technologijos%2C%20UAB&ip=85.206.166.82&key=eyJ0aW1lc3RhbXAiOiIxNTQ4MjI1MzQ2IiwiaGFzaCI6IjRhMzlhNjdjNWYxMTcxMzlmY2QyZjNlZThlNTZiZjUwZWQ4MzgzZWUifQ%3D%3D&bemobdata=c%3Dacf4b19d-6691-4b4b-b420-a4903760d994..a%3D0..b%3D0..e%3D6011377735123860460..c1%3D23603963..c2%3D8534..r%3Dhttp%253A%252F%252Ftchhelpdmn.xyz%252F%253Fsid%253D79885%2526site_id%253D2239231%2526conv_id%253D15480036790774434258237075700209133%2526acsc%253D137566378 | US | html | 5.30 Kb | suspicious |
3364 | chrome.exe | GET | 200 | 159.89.14.246:80 | http://arsweeps.club/arab/om/om_s9xs_3_eng/amp-viewer.js | US | text | 23.9 Kb | suspicious |
3364 | chrome.exe | GET | 200 | 172.104.240.77:80 | http://tchhelpdmn.xyz/?sid=79885&site_id=2239231&conv_id=15480036790774434258237075700209133&acsc=137566378 | US | html | 277 b | whitelisted |
3364 | chrome.exe | GET | 200 | 159.89.14.246:80 | http://arsweeps.club/arab/om/om_s9xs_3_eng/cadeau.png | US | image | 4.11 Kb | suspicious |
3364 | chrome.exe | GET | 200 | 159.89.14.246:80 | http://arsweeps.club/arab/om/om_s9xs_3_eng/amp-viewer.css | US | text | 1.86 Kb | suspicious |
3364 | chrome.exe | GET | 200 | 198.143.165.219:80 | http://ssl.mmtgo.me/?utm_term=6649577356774082514&clickverify=1&utm_content=fdc2c69a9cafac9c909b90a1909e96a589bbcdb9cbbfbc8c808b80b1808582b5ba8bba898ebe8c8d8283b181c1e8ebe2f6feb8d0f0fcb29da0a790a3a29794959e999d8ceeefddedd3d1d8d1e6d0d6d5facbc8ccc6cfc9cecbf3c0c1c2c7c4c7f8fdf8f9aff6fcf5f2f32f | US | html | 1.71 Kb | suspicious |
3364 | chrome.exe | GET | 302 | 198.143.165.219:80 | http://ssl.mmtgo.me/proc.php?389fa03d3ab355d173b09c7a43b9e44b7bd2702a | US | compressed | 1.71 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 172.104.240.77:80 | tchhelpdmn.xyz | — | US | unknown |
3364 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
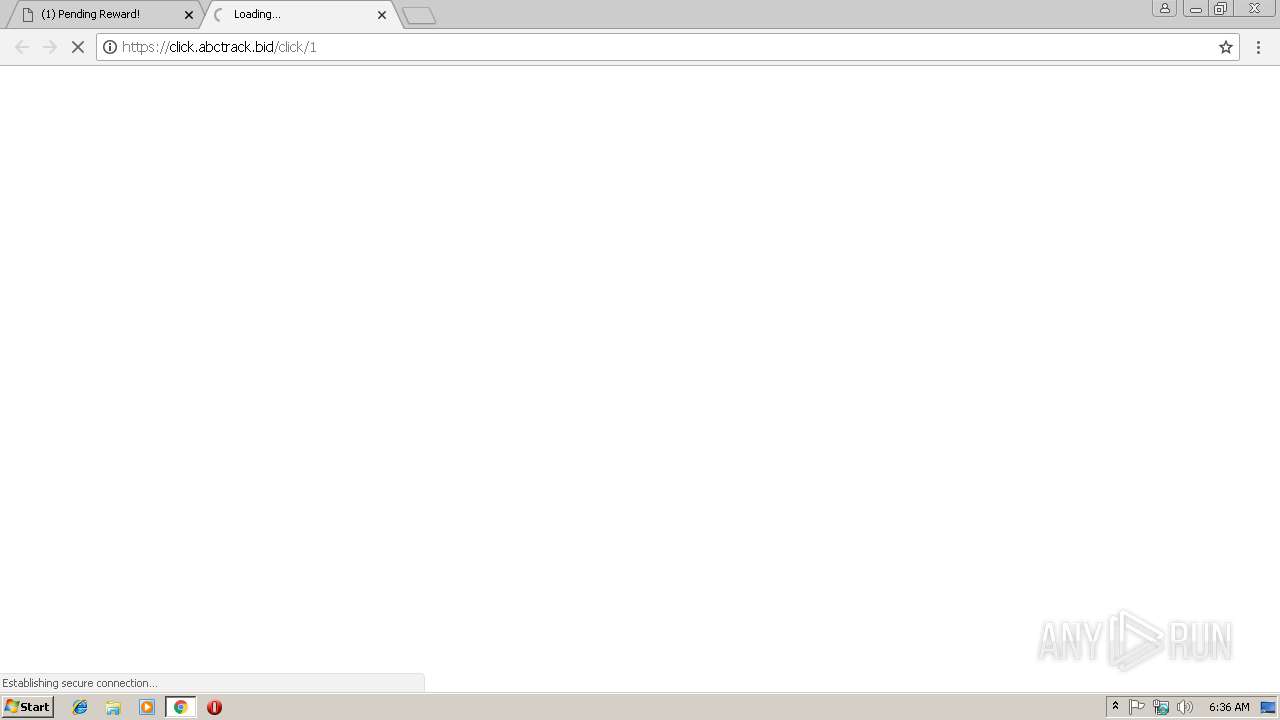
3364 | chrome.exe | 18.195.232.208:443 | click.abctrack.bid | Amazon.com, Inc. | DE | unknown |
3364 | chrome.exe | 159.89.14.246:80 | arsweeps.club | — | US | suspicious |
3364 | chrome.exe | 104.19.205.29:443 | amp.cloudflare.com | Cloudflare Inc | US | shared |
3364 | chrome.exe | 54.230.199.208:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
3364 | chrome.exe | 107.6.174.196:443 | up.trkgenius.com | SingleHop, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
tchhelpdmn.xyz |
| whitelisted |
accounts.google.com |
| shared |
click.abctrack.bid |
| suspicious |
arsweeps.club |
| suspicious |
amp.cloudflare.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
cd-down.com |
| unknown |
x.ss2.us |
| whitelisted |