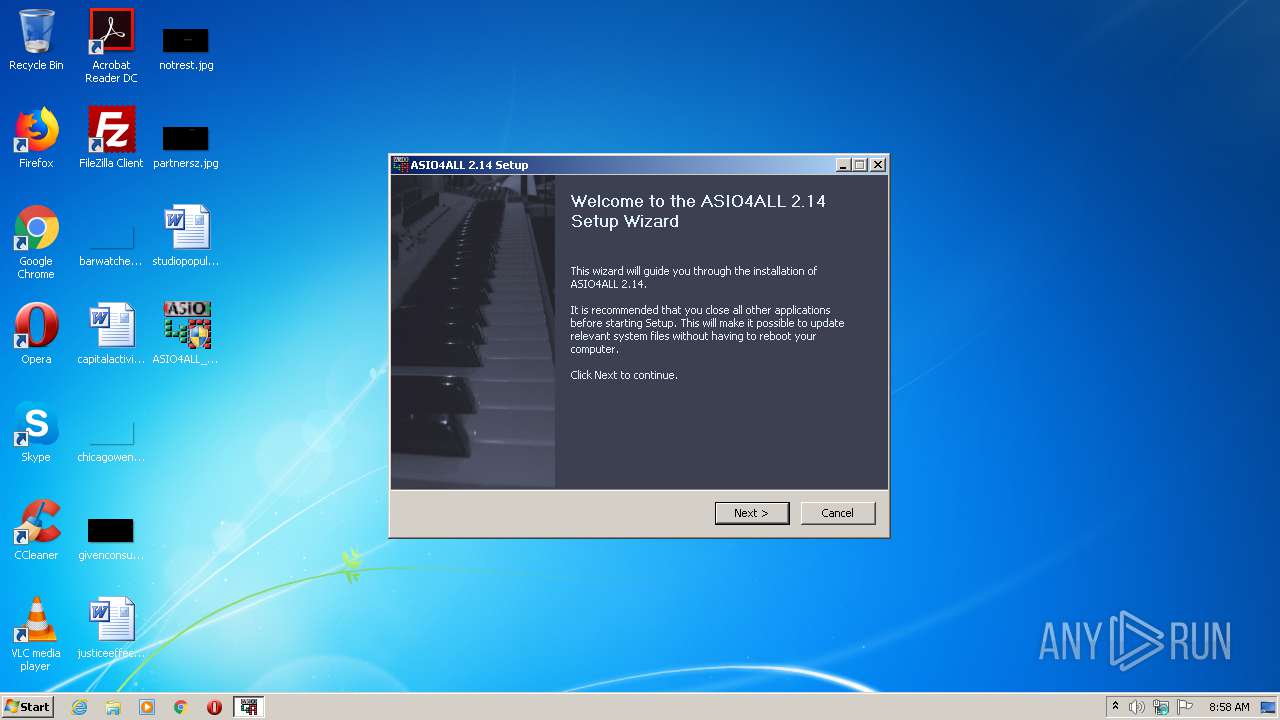
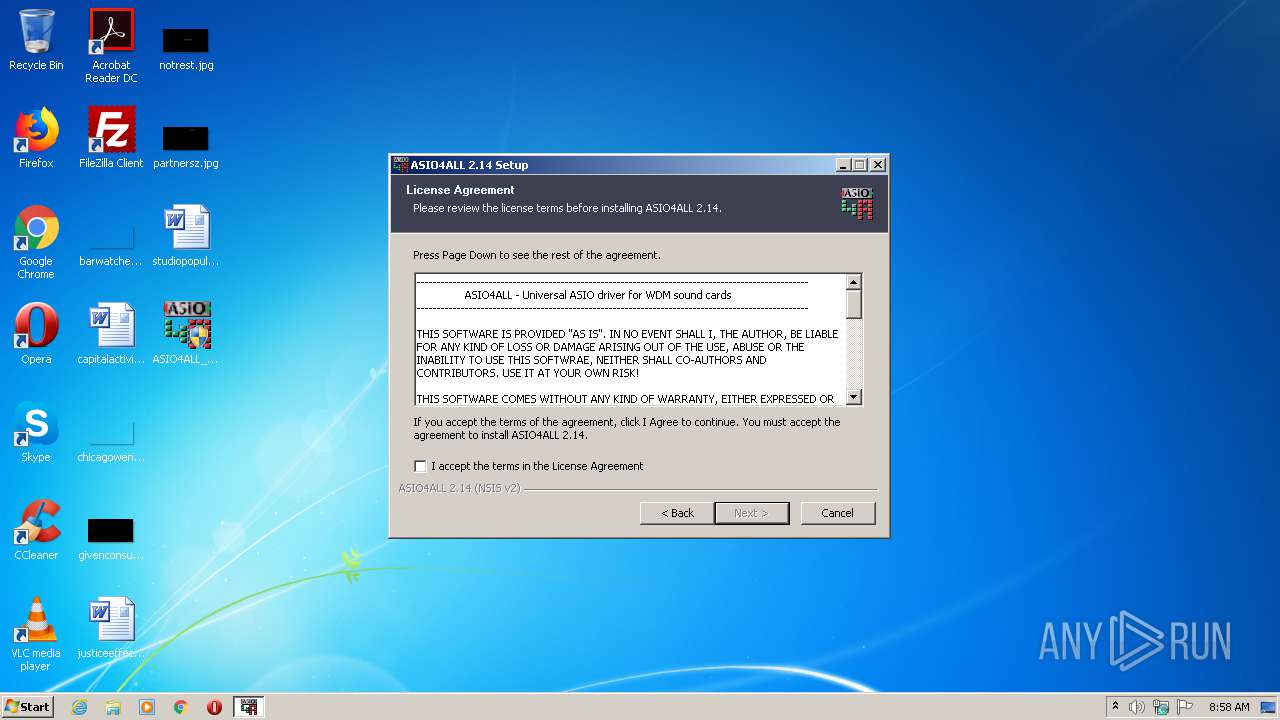
| File name: | ASIO4ALL_2_14_English.exe |
| Full analysis: | https://app.any.run/tasks/3a90e943-5734-4b51-9662-a41848efdc51 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2020, 07:57:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | ACEF732136F28D0DE0B241253C5D197B |
| SHA1: | 7ED17BC8155686D61E2EBFBB44BA92AEED8AA39F |
| SHA256: | 15A3A1FF103F583F9E5493349C85B98799BAADEE44CB3F25A0611141A4A6D8FA |
| SSDEEP: | 12288:pFJjUsUf1t1aLwHFUh6YEN9kW1jADqEf4NrGZW:/NUNraLwKQNSEZ |
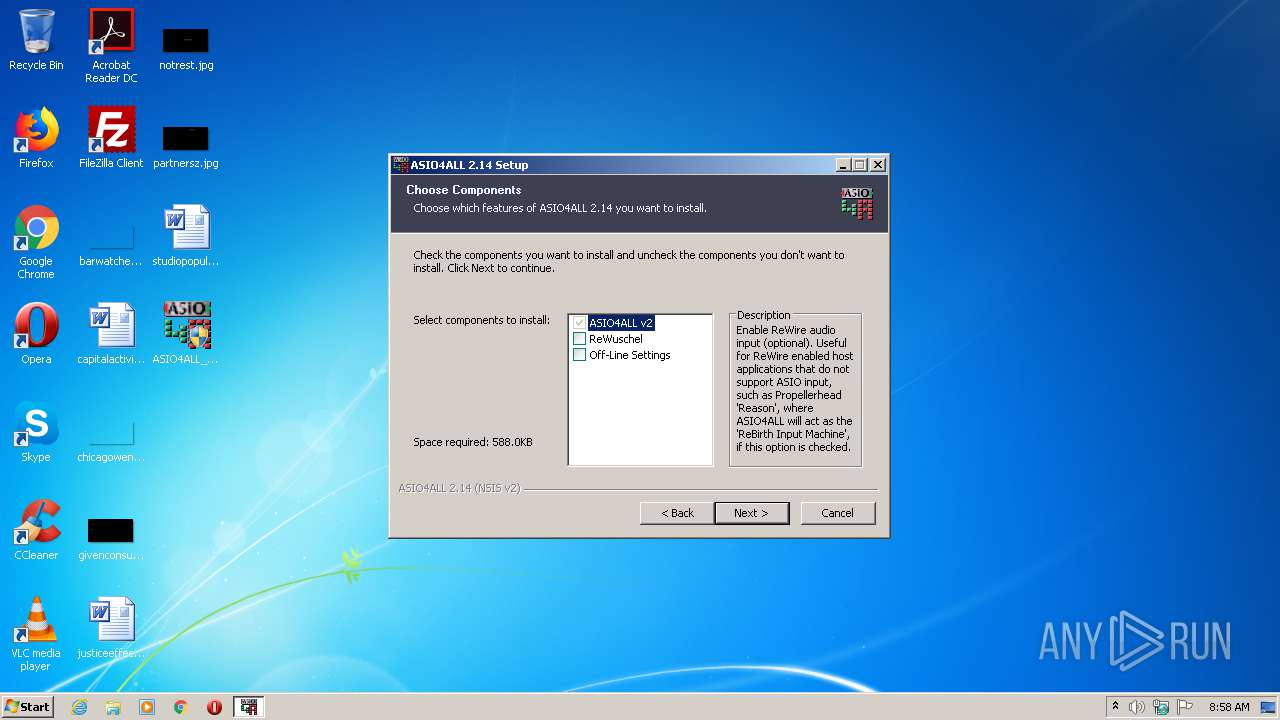
MALICIOUS
Loads dropped or rewritten executable
- ASIO4ALL_2_14_English.exe (PID: 3548)
- a4apanel.exe (PID: 1264)
Registers / Runs the DLL via REGSVR32.EXE
- ASIO4ALL_2_14_English.exe (PID: 3548)
Application was dropped or rewritten from another process
- a4apanel.exe (PID: 1264)
SUSPICIOUS
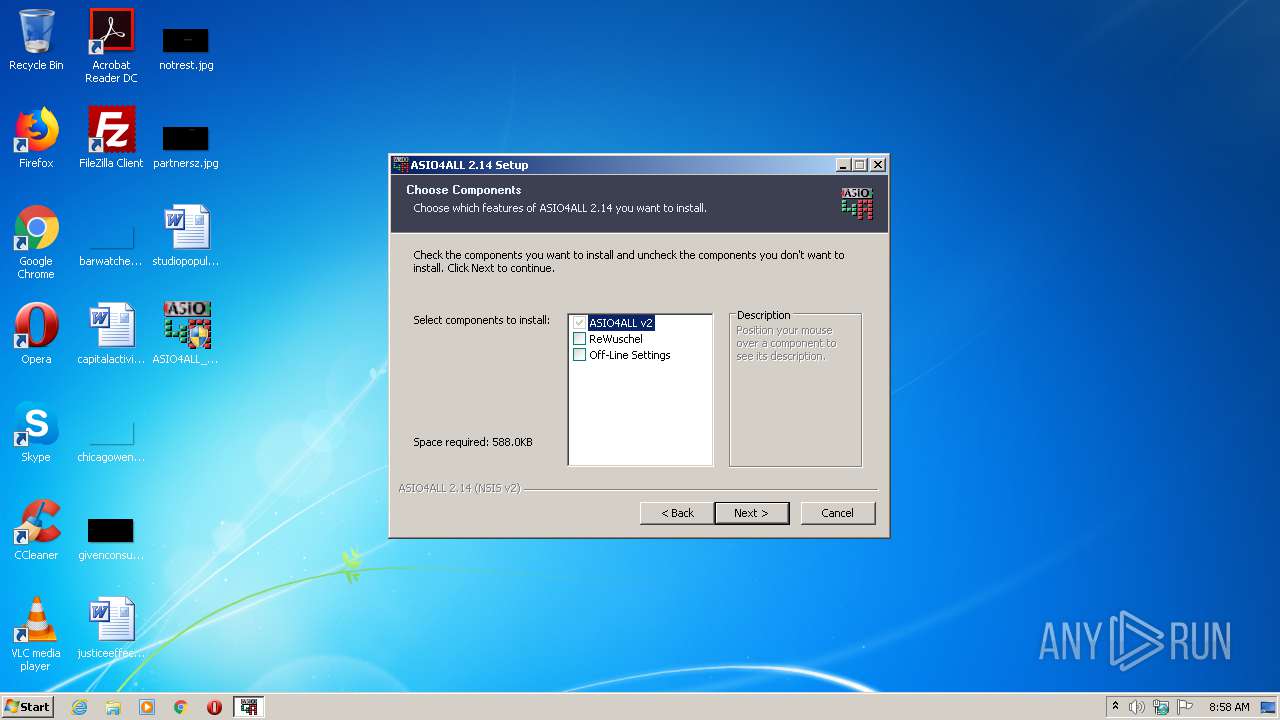
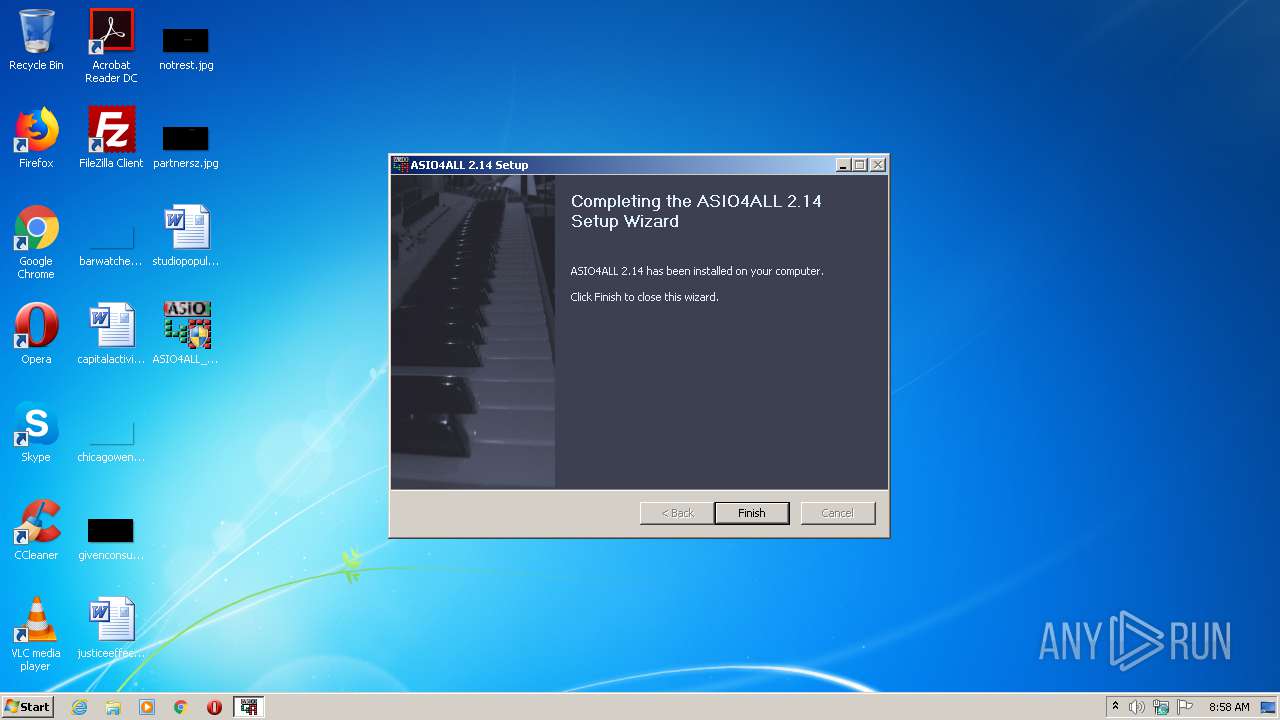
Executable content was dropped or overwritten
- ASIO4ALL_2_14_English.exe (PID: 3548)
Creates files in the program directory
- ASIO4ALL_2_14_English.exe (PID: 3548)
Creates files in the user directory
- ASIO4ALL_2_14_English.exe (PID: 3548)
Creates COM task schedule object
- ASIO4ALL_2_14_English.exe (PID: 3548)
Creates a software uninstall entry
- ASIO4ALL_2_14_English.exe (PID: 3548)
INFO
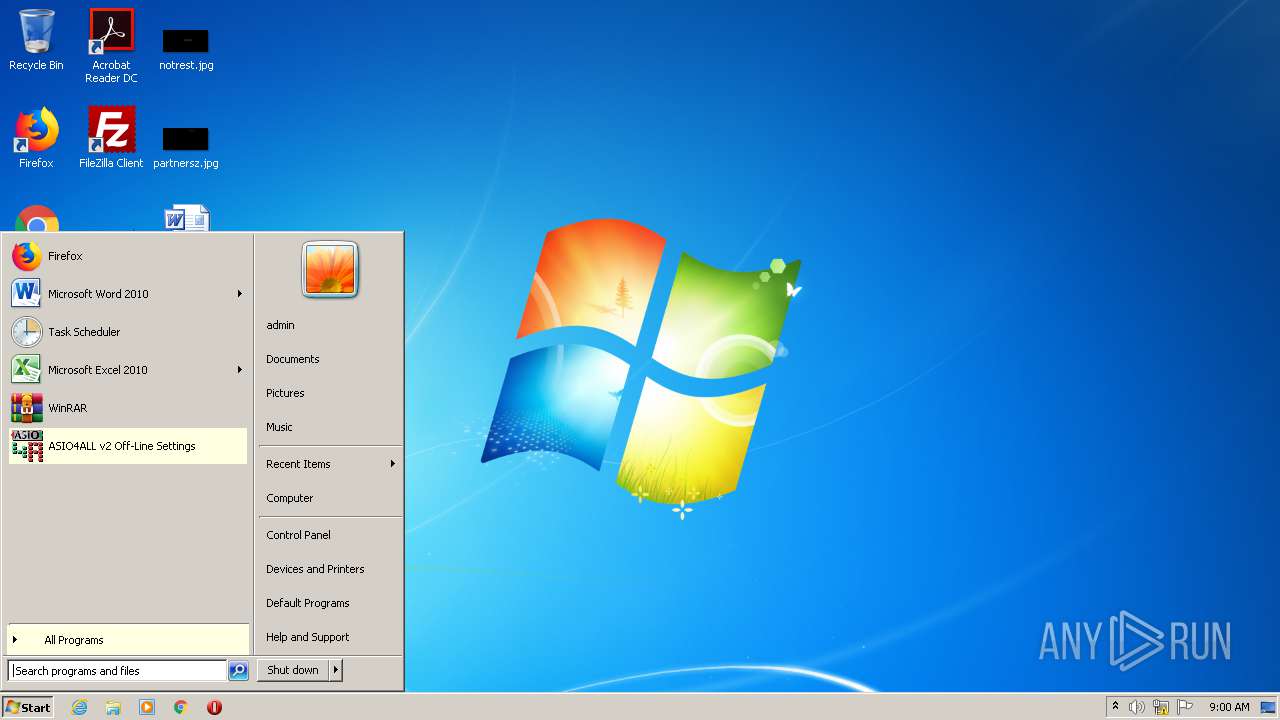
Manual execution by user
- a4apanel.exe (PID: 1264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:05:03 16:08:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30e3 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-May-2008 14:08:47 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-May-2008 14:08:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B26 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47552 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04904 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77023 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x000016C0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.97375 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08937 | 733 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.83321 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
109 | 2.70146 | 212 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1264 | "C:\Program Files\ASIO4ALL v2\a4apanel.exe" | C:\Program Files\ASIO4ALL v2\a4apanel.exe | — | explorer.exe | |||||||||||
User: admin Company: Michael Tippach Integrity Level: MEDIUM Description: ASIO4ALL Panel Launcher Exit code: 0 Version: 2.14.0000 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\Desktop\ASIO4ALL_2_14_English.exe" | C:\Users\admin\Desktop\ASIO4ALL_2_14_English.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2780 | "C:\Windows\system32\regsvr32.exe" -s "C:\Program Files\ASIO4ALL v2\asio4all64.dll" | C:\Windows\system32\regsvr32.exe | — | ASIO4ALL_2_14_English.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\Users\admin\Desktop\ASIO4ALL_2_14_English.exe" | C:\Users\admin\Desktop\ASIO4ALL_2_14_English.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
251
Read events
163
Write events
88
Delete events
0
Modification events
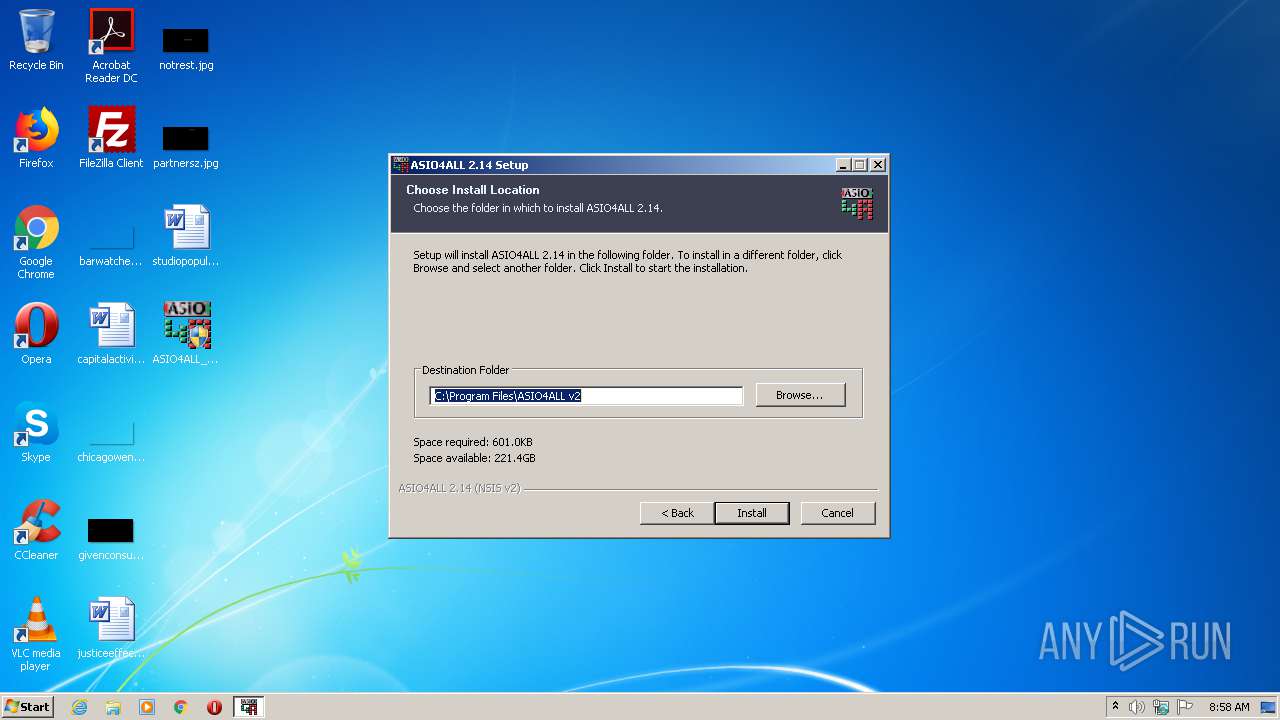
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Propellerhead Software\ReWire\ASIO4ALL ReWireIn |
| Operation: | write | Name: | Device Path |
Value: C:\Program Files\ASIO4ALL v2\asio4all.dll | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ASIO4ALL |
| Operation: | write | Name: | |
Value: C:\Program Files\ASIO4ALL v2 | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | DisplayName |
Value: ASIO4ALL | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\ASIO4ALL v2\uninstall.exe | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | DisplayVersion |
Value: 2.14 | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\ASIO4ALL v2\uninstall.exe | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | HelpLink |
Value: http://mtippach.proboards.com/ | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | Publisher |
Value: Michael Tippach | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.asio4all.com/intro.html | |||
| (PID) Process: | (3548) ASIO4ALL_2_14_English.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ASIO4ALL |
| Operation: | write | Name: | URLUpdateInfo |
Value: http://www.asio4all.com/index.html | |||
Executable files
8
Suspicious files
1
Text files
27
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
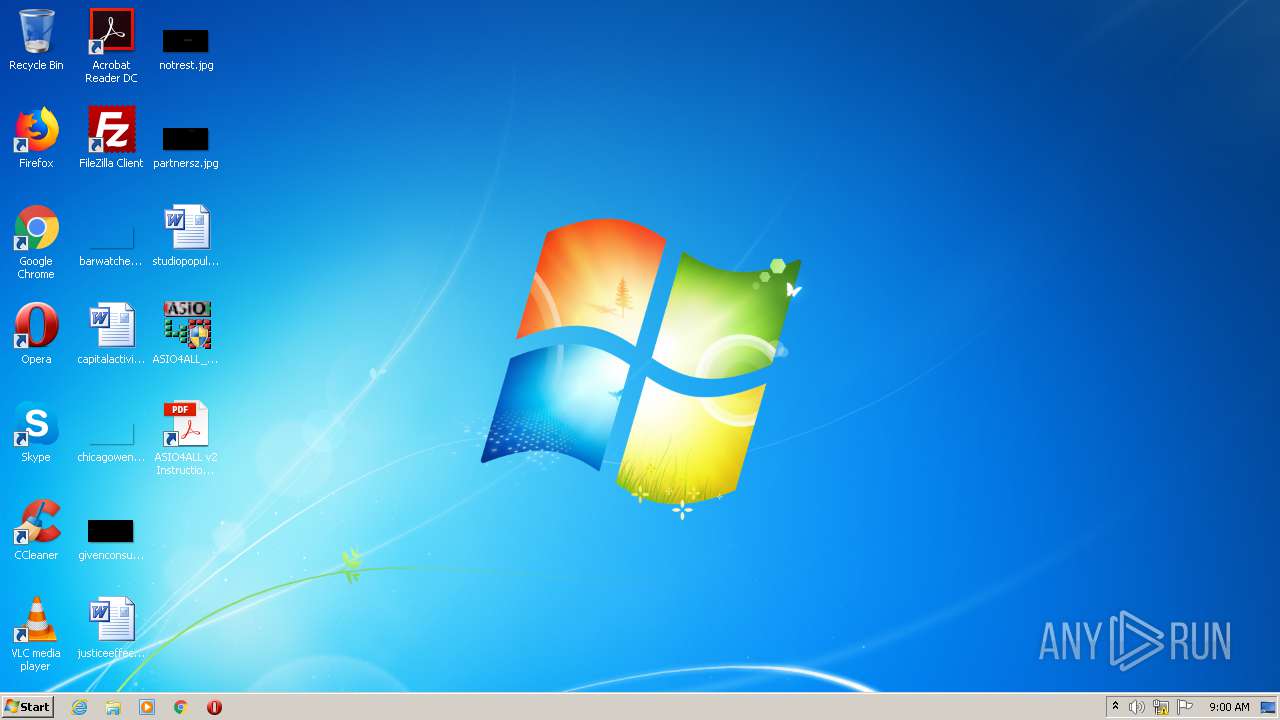
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\Desktop\ASIO4ALL v2 Instruction Manual.lnk | lnk | |
MD5:38108D68BEB2D3C57583C7C231FF4505 | SHA256:6AFC0006CFA56EBB78B84570EE7B64666D9C2BC9C0CD6F09C7397229C92A48A1 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ASIO4ALL v2\ASIO4ALL v2 Off-Line Settings.lnk | lnk | |
MD5:645F9AFF0BD39FDB36066C5DEAE6167A | SHA256:A1BB0BED6EC3A4236D19C9D7E10A7092AFF83E0BE49738A03F9470AEDFA47424 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ASIO4ALL v2\ASIO4ALL v2 Instruction Manual.lnk | lnk | |
MD5:24D5D89ED87DD81EB59031D5B6724EFB | SHA256:FA247EBBE8272214F53056D6DA0135C5BE01766153A59DE68D08E55CD418147D | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ASIO4ALL v2\ASIO4ALL Web Site.lnk | lnk | |
MD5:72490EDC73A8BDB2A11F0FF03A42B41E | SHA256:F2FB7E9F1C87489E37873CC6B713D8636A466CB9FC79A9C878185FB94DEB2578 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\AppData\Local\Temp\nstCF60.tmp\ioSpecial.ini | text | |
MD5:4A1F9DD1501E9E57C9CCD15CEDBD7930 | SHA256:8A0BBFDD0A9CE2A80241AC68E66644D904F66DE171CA6BF7719327AE519EF849 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Program Files\ASIO4ALL v2\a4apanel64.exe | executable | |
MD5:861265483C1D6BCAACCE89EA743C1976 | SHA256:2933BEB43CAF5D8FB3BA422630F99516ABEBB7CA8B8BA6371CCA51D6CB6D67B2 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Program Files\ASIO4ALL v2\ASIO4ALL Web Site.url | text | |
MD5:15A5D95ED493BF090F5A9633943B775A | SHA256:007DF5B56AD9FFB83061019E3FBF9F7A8AF84A4EA8C65C38B0F02AB27C4E2546 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ASIO4ALL v2\Uninstall.lnk | lnk | |
MD5:50D020EEA1FF98B4E52531134BF8B397 | SHA256:6CE225F8118217AE1F5F72036112476C1242CF156B7119E5DEA2A9F2D1DA1378 | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Program Files\ASIO4ALL v2\uninstall.exe | executable | |
MD5:1BC7413137D38A0A5F8A2C8A0A63BB23 | SHA256:E43AFE8128C9FC6AC3D455987964A5D90E6E2ED422EACD7437B6D50903E7796C | |||
| 3548 | ASIO4ALL_2_14_English.exe | C:\Program Files\ASIO4ALL v2\ASIO4ALL v2 Instruction Manual.pdf | ||
MD5:882F5C35FE9BD596CEF83B7582A6B47B | SHA256:94CE78F6B9B6D42C2C1A149E074E7F3AA2394DC5BE002996A16D0B425A7A3F55 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report