| File name: | pro.smoc |
| Full analysis: | https://app.any.run/tasks/975f2dee-aed5-49f0-bfcd-49e8526f33dc |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2019, 18:05:19 |
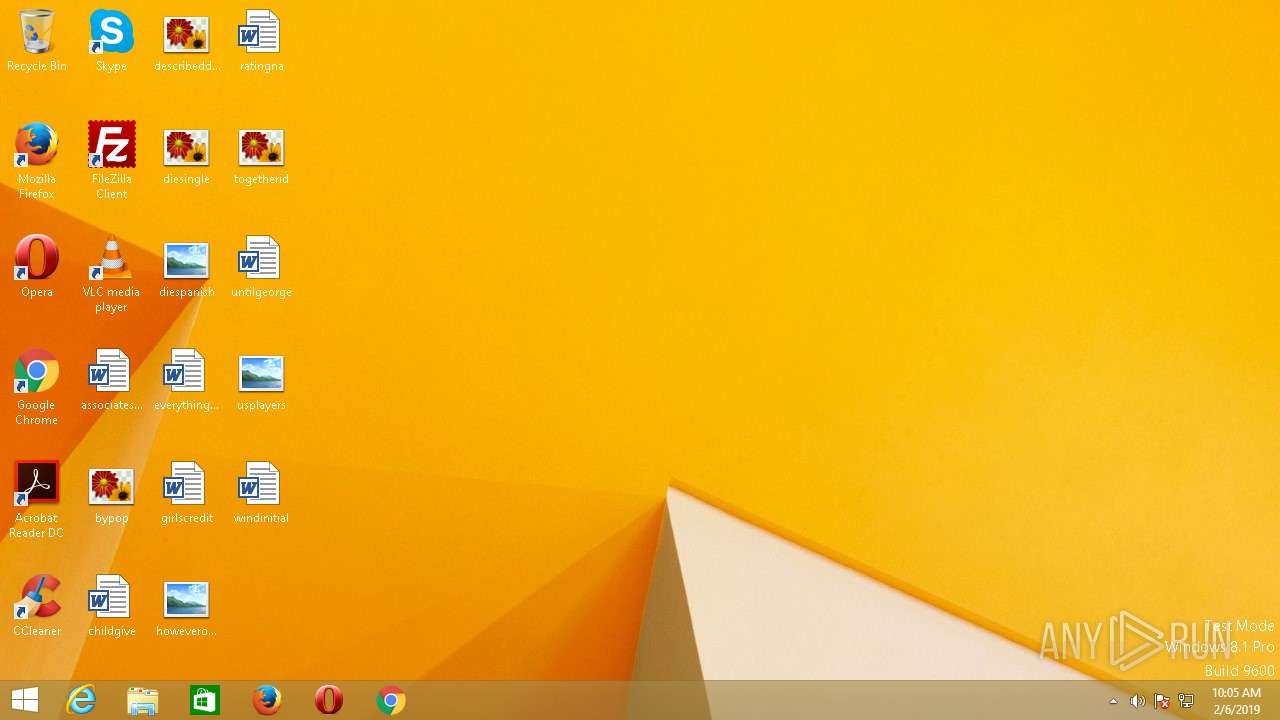
| OS: | Windows 8.1 Professional (build: 9600, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 99BF8EA085D667F7E28EF461D77AE77E |
| SHA1: | AA6E74C10BB065A0B5BE4768FCCD2BEEDD42C8E0 |
| SHA256: | 1595ECBC00303503B974747AFF928D2EACCE9B249E0DEF2EA29EE12191CC6F1A |
| SSDEEP: | 6144:Ac8gPyy0+QPDMvTcKNy0cBFH2R9MZNshcgyBVKmwrBJUgcRmOYBuBNmOdTSIpvVw:AhgPyy0+QPDMJypWqrr0 |
MALICIOUS
Stops/Deletes Windows Defender service
- cmd.exe (PID: 696)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 348)
- cmd.exe (PID: 2828)
Known privilege escalation attack
- DllHost.exe (PID: 1612)
Uses SVCHOST.EXE for hidden code execution
- qsp.smoc.exe (PID: 1076)
Loads the Task Scheduler COM API
- svchost.exe (PID: 2492)
SUSPICIOUS
Creates files in the user directory
- pro.smoc.exe (PID: 2204)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 1184)
Executable content was dropped or overwritten
- pro.smoc.exe (PID: 2204)
Starts CMD.EXE for commands execution
- pro.smoc.exe (PID: 2204)
- qsp.smoc.exe (PID: 1076)
Executes PowerShell scripts
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2468)
Checks supported languages
- powershell.exe (PID: 2344)
- powershell.exe (PID: 1184)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:06 15:55:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.21 |
| CodeSize: | 42496 |
| InitializedDataSize: | 224768 |
| UninitializedDataSize: | 19456 |
| EntryPoint: | 0x1284 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Feb-2019 14:55:14 |
| TLS Callbacks: | 2 callback(s) detected. |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 17 |
| Time date stamp: | 06-Feb-2019 14:55:14 |
| Pointer to Symbol Table: | 0x00044000 |
| Number of symbols: | 1686 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000A540 | 0x0000A600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.08677 |
.data | 0x0000C000 | 0x00029F30 | 0x0002A000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99783 |
.rdata | 0x00036000 | 0x00001B80 | 0x00001C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98608 |
.bss | 0x00038000 | 0x00004AD8 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0003D000 | 0x00000654 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.32565 |
.CRT | 0x0003E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.114463 |
.tls | 0x0003F000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.22482 |
/4 | 0x00040000 | 0x00000180 | 0x00000200 | IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.83448 |
/19 | 0x00041000 | 0x000003D1 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.57218 |
/35 | 0x00042000 | 0x00000485 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.20028 |
Imports
KERNEL32.dll |
msvcrt.dll |
Total processes
53
Monitored processes
22
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | /c sc stop WinDefend | C:\Windows\SysWOW64\cmd.exe | — | qsp.smoc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 5 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 696 | /c sc stop WinDefend | C:\Windows\SysWOW64\cmd.exe | — | pro.smoc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 908 | sc delete WinDefend | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 936 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Roaming\cleanmem\qsp.smoc.exe" | C:\Users\admin\AppData\Roaming\cleanmem\qsp.smoc.exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1184 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.3.9600.17396 (winblue_r4.141007-2030) Modules
| |||||||||||||||
| 1188 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1220 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1612 | C:\Windows\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.3.9600.17415 (winblue_r4.141028-1500) Modules
| |||||||||||||||
| 1744 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
Total events
516
Read events
498
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2204) pro.smoc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (1612) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1612) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1612) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1612) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1076) qsp.smoc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2344) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
5
Text files
1
Unknown types
99
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HQSIJCGD7OIHOS7K3Y27.temp | — | |
MD5:— | SHA256:— | |||
| 1184 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XLYKPX6JF5TUKU5GLW6B.temp | — | |
MD5:— | SHA256:— | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:2FED46CAAFE04BE9B8B1A2D72A2DC47A | SHA256:625A4AF307EACF83EF461A21E1B4994ECE0113469DEA82763274A01D53D01FA1 | |||
| 2204 | pro.smoc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-4080122336-2017344304-407619480-1001\0f5007522459c86e95ffcc62f32308f1_c5548495-682b-436b-b722-92c4f9c95ae9 | binary | |
MD5:B04550369967185055DD4CE10981A62F | SHA256:44808F61DC52DFA561B2219FD2D9BFC0C4DD4CDF5F602A46994F2C4D38262A20 | |||
| 1184 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:2FED46CAAFE04BE9B8B1A2D72A2DC47A | SHA256:625A4AF307EACF83EF461A21E1B4994ECE0113469DEA82763274A01D53D01FA1 | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\CommandAnalysis\PowerShell_AnalysisCacheIndex | pi2 | |
MD5:430BD5479EE485BD72CB59A3E144962B | SHA256:6C8482EE62C6997819E30E25997F23E183C594BF2F888C7422B07A824F82C4C2 | |||
| 1076 | qsp.smoc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-4080122336-2017344304-407619480-1001\0f5007522459c86e95ffcc62f32308f1_c5548495-682b-436b-b722-92c4f9c95ae9 | binary | |
MD5:6BBEB454B68D923249728BA1F6E9A257 | SHA256:34470426B18C9DAFC68DC6D865A98D6741BE0145A1E0EB7D81AD01588FB01C9B | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\CommandAnalysis\PowerShell_AnalysisCacheEntry_edce8eff-c273-4588-929e-6dff30710ab8 | pi2 | |
MD5:75A8DA7754349B38D64C87C938545B1B | SHA256:BF08151C174B5D00C9DBC7907B2C6A01B4BE76BFA3AFCE1E8BD98A04AD833C96 | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\CommandAnalysis\PowerShell_AnalysisCacheEntry_da66b6a9-c30d-4fc4-ae4e-673057367e27 | pi2 | |
MD5:E319F2B68F4F66EEAFB8AF0B4A0A8269 | SHA256:752D07B6533217BA3151127A91846A5847836D78A35F9CB2172C93E9CC034D88 | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\CommandAnalysis\PowerShell_AnalysisCacheEntry_05e27ee3-165b-407a-ab8f-be2a8e357ec1 | pi2 | |
MD5:9CA4D5F692D8687951CE3B708C66BE42 | SHA256:BD606E084EBF6E01E4AC166E566DE40FA3186F4FDEAE8C9292BA7B0AF31B31A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
pro.smoc.exe | SHIMVIEW: ShimInfo(Complete)
|
qsp.smoc.exe | SHIMVIEW: ShimInfo(Complete)
|