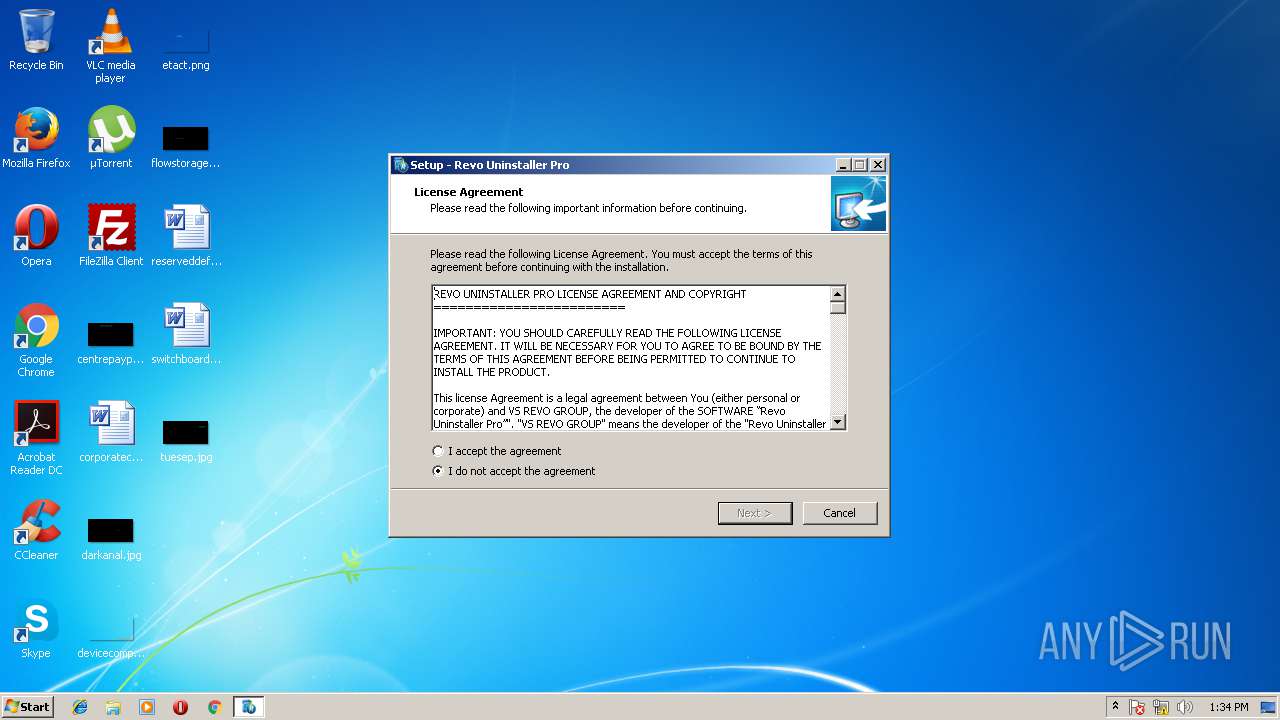
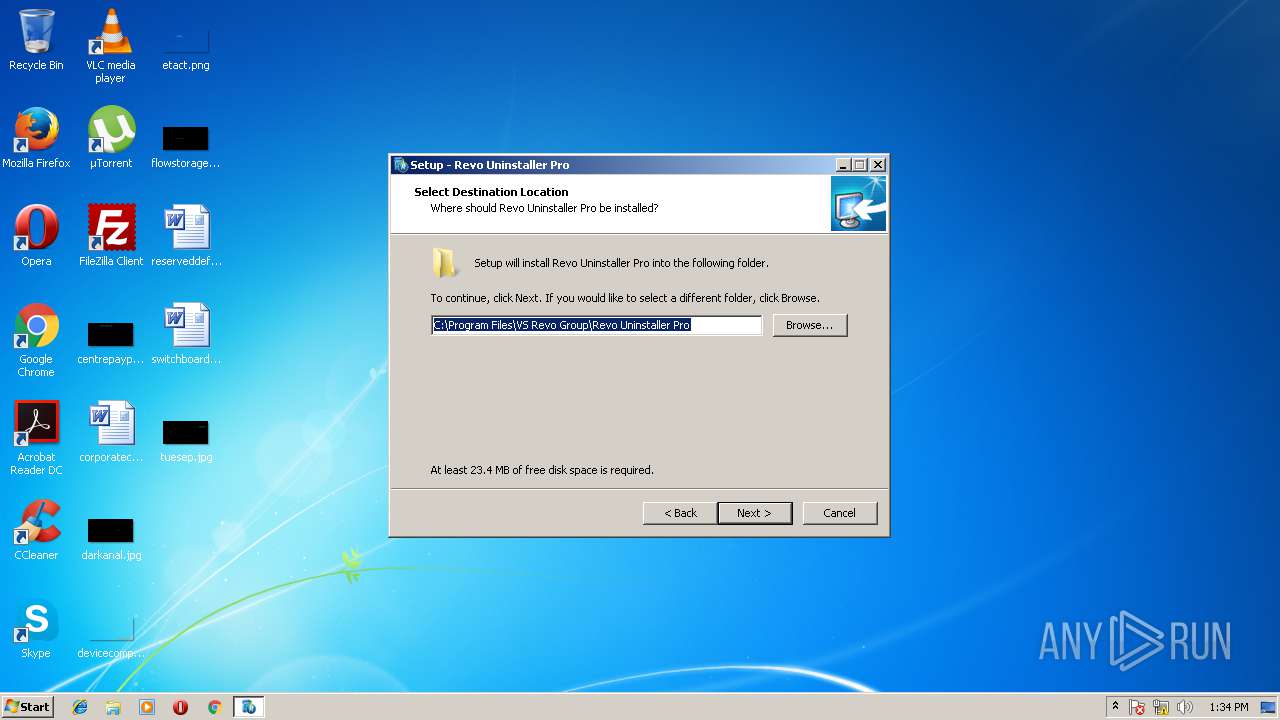
| File name: | RevoUninProSetup.exe |
| Full analysis: | https://app.any.run/tasks/e418f959-b0a4-4dbf-b595-236435523016 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2018, 12:33:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FAB2A75449E886F76B7FF69C43144CA4 |
| SHA1: | 87F4306960BFEA82947684574A891DF3A0D611B2 |
| SHA256: | 157675A479B21CB8034DC273DA906F13A62703703135E34175D41C7941A67BB1 |
| SSDEEP: | 196608:IezJA6Wv+CLAwr8fp0r6ZDvDTj5eeHiADpyGNOkjXz2VrcfjVtdv/yQc+FR7mXB+:IuA3v+CLzrqrTFeeHzyGzXaVrc5tdv/p |
MALICIOUS
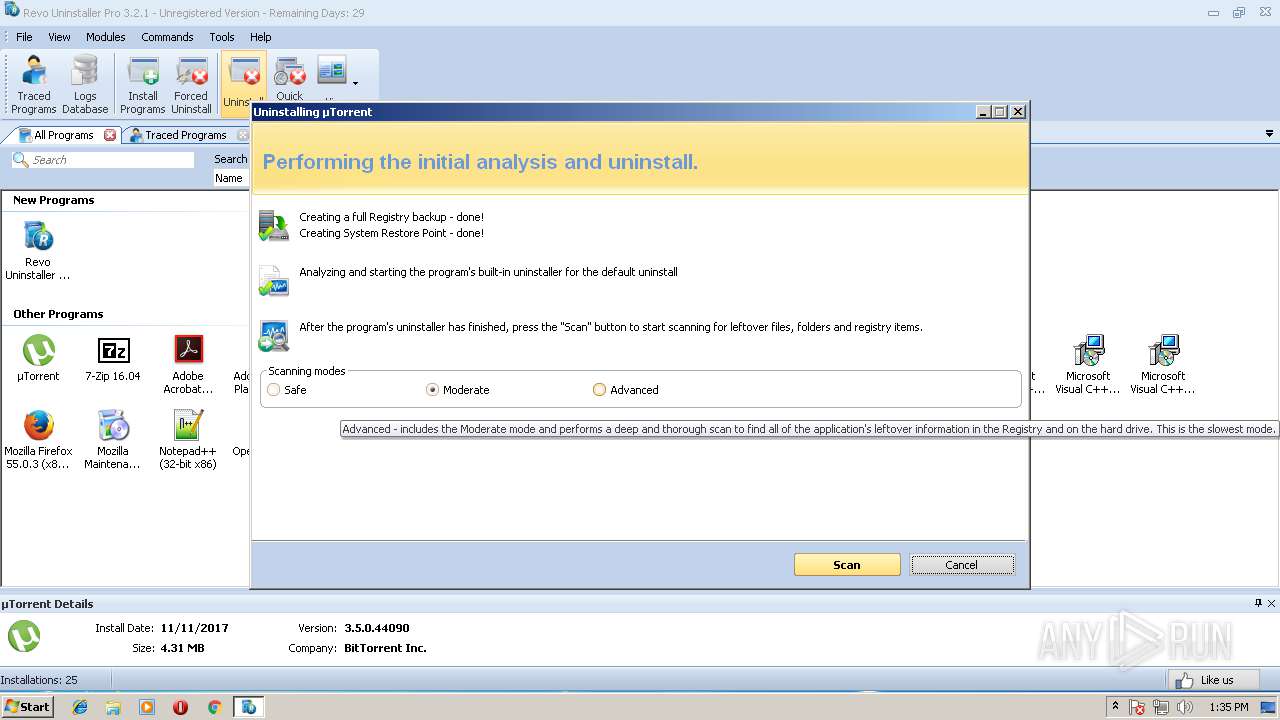
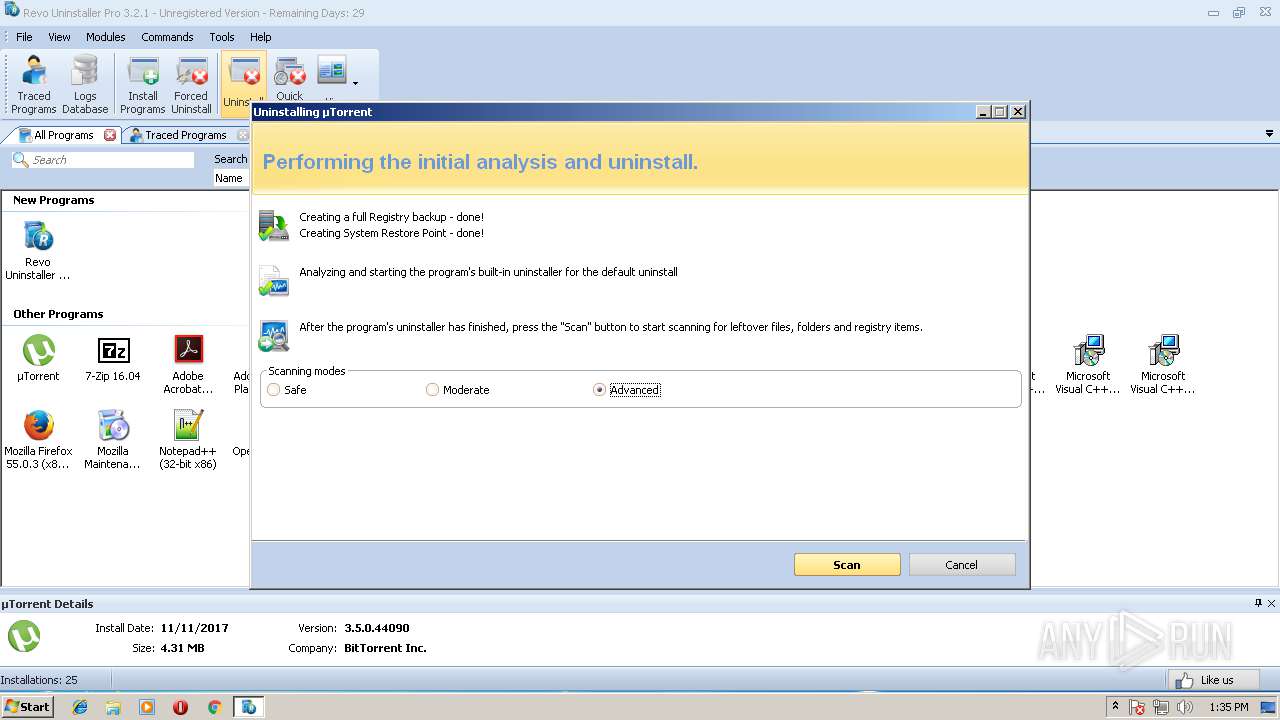
Registers / Runs the DLL via REGSVR32.EXE
- RevoUninProSetup.tmp (PID: 3572)
Changes the autorun value in the registry
- rundll32.exe (PID: 3436)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2032)
- mshta.exe (PID: 3548)
- svchost.exe (PID: 868)
- RevoUninPro.exe (PID: 2948)
- setup.exe (PID: 3312)
Application was dropped or rewritten from another process
- ruplp.exe (PID: 1576)
- RevoUninPro.exe (PID: 2184)
- ruplp.exe (PID: 2180)
- RevoUninPro.exe (PID: 2948)
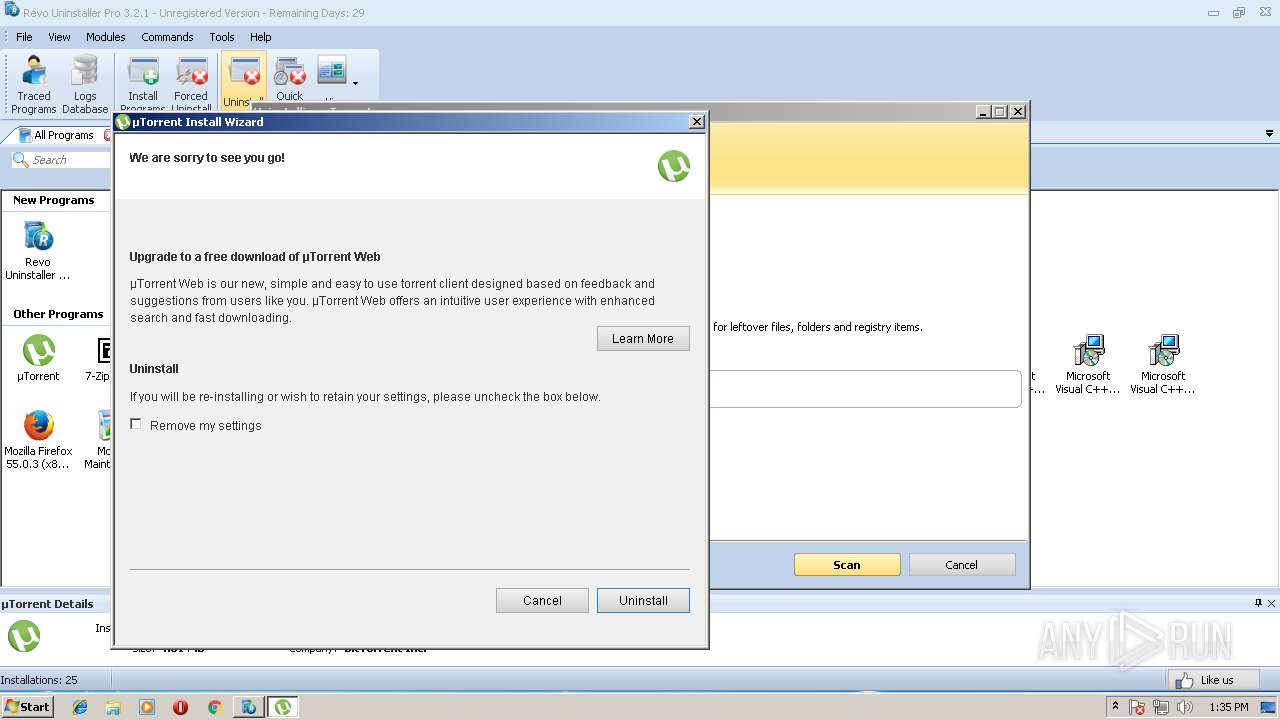
- uTorrent.exe (PID: 384)
- uTorrent.exe (PID: 3108)
- ose.exe (PID: 3828)
- ose00000.exe (PID: 664)
- OSPPSVC.EXE (PID: 2492)
- setup.exe (PID: 3312)
- MSOHTMED.EXE (PID: 2984)
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 2492)
SUSPICIOUS
Modifies the open verb of a shell class
- RevoUninProSetup.tmp (PID: 3572)
- MsiExec.exe (PID: 2824)
Creates files in the Windows directory
- rundll32.exe (PID: 3436)
- mscorsvw.exe (PID: 3768)
- ngen.exe (PID: 1844)
- ngen.exe (PID: 1992)
- ngen.exe (PID: 2116)
- mscorsvw.exe (PID: 2224)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3624)
- mscorsvw.exe (PID: 1532)
- ngen.exe (PID: 2032)
- msiexec.exe (PID: 1348)
- ngen.exe (PID: 3740)
- mscorsvw.exe (PID: 1248)
- ngen.exe (PID: 3516)
- ngen.exe (PID: 3848)
- mscorsvw.exe (PID: 1492)
- ngen.exe (PID: 1248)
- ngen.exe (PID: 1900)
- mscorsvw.exe (PID: 3248)
- ngen.exe (PID: 3992)
- mscorsvw.exe (PID: 3276)
- ngen.exe (PID: 708)
- ngen.exe (PID: 1744)
- mscorsvw.exe (PID: 3180)
- ngen.exe (PID: 676)
- ngen.exe (PID: 3900)
- mscorsvw.exe (PID: 2728)
- mscorsvw.exe (PID: 2888)
- mscorsvw.exe (PID: 3960)
- ngen.exe (PID: 2620)
- mscorsvw.exe (PID: 3180)
- ngen.exe (PID: 1464)
- mscorsvw.exe (PID: 3084)
- ngen.exe (PID: 3048)
- ngen.exe (PID: 2004)
- mscorsvw.exe (PID: 3456)
- ngen.exe (PID: 1424)
- mscorsvw.exe (PID: 3148)
- ngen.exe (PID: 2604)
- ngen.exe (PID: 2892)
- mscorsvw.exe (PID: 1284)
- mscorsvw.exe (PID: 2912)
- mscorsvw.exe (PID: 840)
- ngen.exe (PID: 2996)
- ngen.exe (PID: 2468)
- ngen.exe (PID: 1616)
- ngen.exe (PID: 2024)
- ngen.exe (PID: 2396)
- ngen.exe (PID: 3932)
- mscorsvw.exe (PID: 2104)
- ngen.exe (PID: 3588)
- mscorsvw.exe (PID: 3144)
- ngen.exe (PID: 3316)
- ngen.exe (PID: 4060)
- ngen.exe (PID: 1980)
Creates files in the driver directory
- rundll32.exe (PID: 3436)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3436)
- RevoUninProSetup.exe (PID: 3352)
- RevoUninProSetup.tmp (PID: 3572)
- RevoUninProSetup.exe (PID: 2040)
- uTorrent.exe (PID: 384)
- MsiExec.exe (PID: 3988)
- MsiExec.exe (PID: 3752)
- MsiExec.exe (PID: 1264)
- ose.exe (PID: 3828)
- msiexec.exe (PID: 1348)
- MsiExec.exe (PID: 3528)
- MsiExec.exe (PID: 1132)
- setup.exe (PID: 3312)
- MsiExec.exe (PID: 3980)
- MsiExec.exe (PID: 2164)
- MsiExec.exe (PID: 2824)
- MsiExec.exe (PID: 2972)
Creates or modifies windows services
- rundll32.exe (PID: 3436)
- RevoUninPro.exe (PID: 2948)
- DllHost.exe (PID: 2268)
- svchost.exe (PID: 868)
- DllHost.exe (PID: 1800)
- setup.exe (PID: 3312)
Reads Windows owner settings
- RevoUninProSetup.tmp (PID: 3572)
Removes files from Windows directory
- rundll32.exe (PID: 3436)
- mscorsvw.exe (PID: 3768)
- mscorsvw.exe (PID: 2224)
- msiexec.exe (PID: 1348)
- mscorsvw.exe (PID: 1248)
- mscorsvw.exe (PID: 3248)
- mscorsvw.exe (PID: 1492)
- mscorsvw.exe (PID: 1532)
- mscorsvw.exe (PID: 3180)
- mscorsvw.exe (PID: 2888)
- mscorsvw.exe (PID: 2728)
- mscorsvw.exe (PID: 3960)
- mscorsvw.exe (PID: 3180)
- mscorsvw.exe (PID: 3084)
- mscorsvw.exe (PID: 3148)
- mscorsvw.exe (PID: 3456)
- mscorsvw.exe (PID: 2912)
- mscorsvw.exe (PID: 840)
- mscorsvw.exe (PID: 1284)
- mscorsvw.exe (PID: 3144)
- mscorsvw.exe (PID: 3276)
- mscorsvw.exe (PID: 2104)
Reads the Windows organization settings
- RevoUninProSetup.tmp (PID: 3572)
Creates COM task schedule object
- regsvr32.exe (PID: 2032)
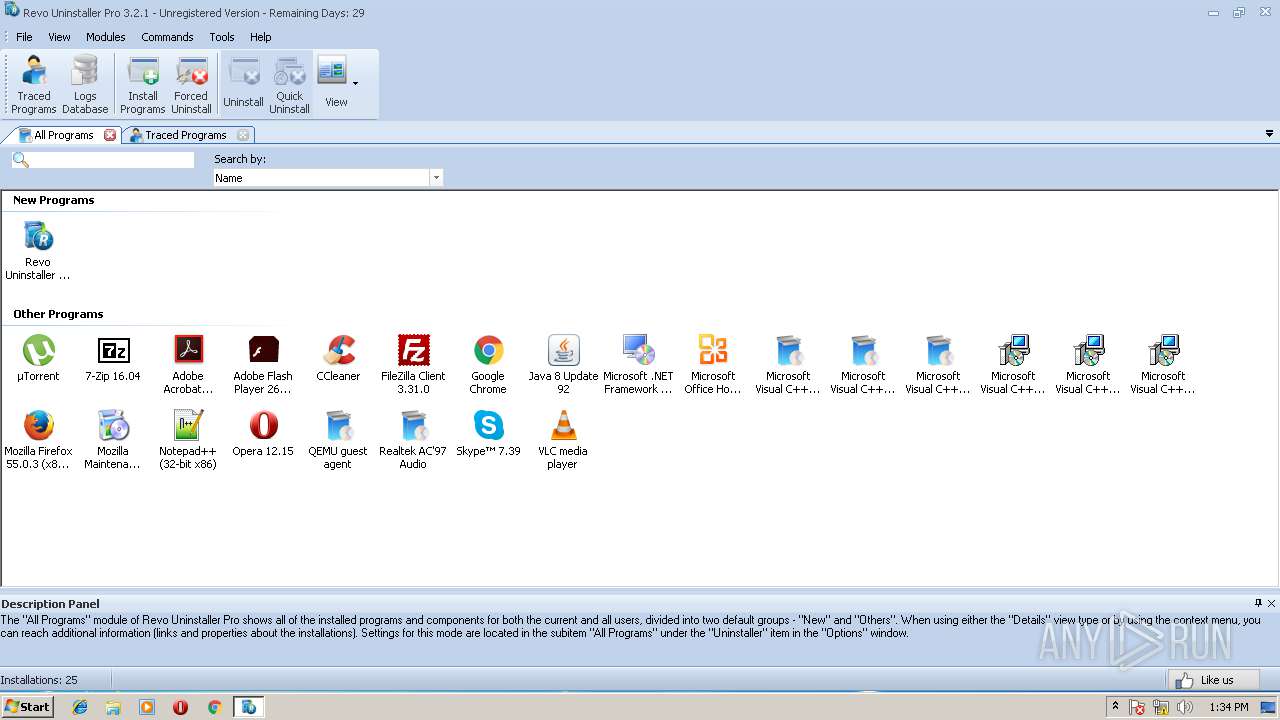
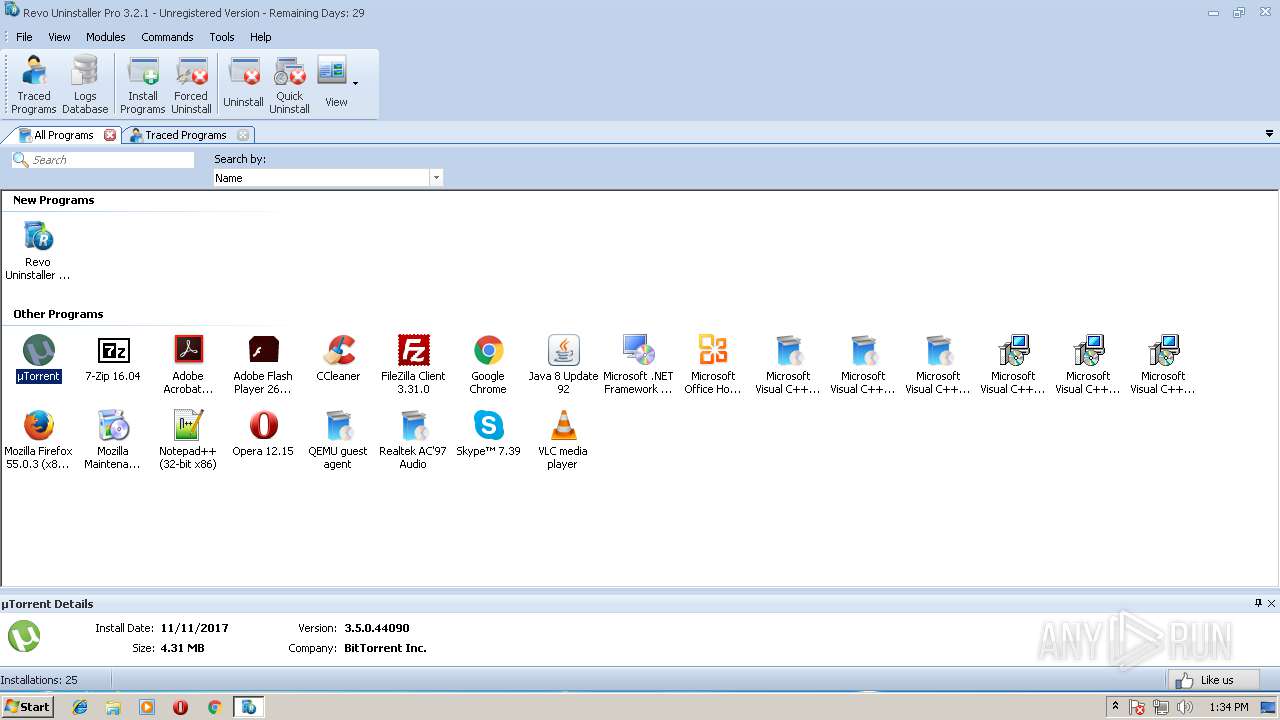
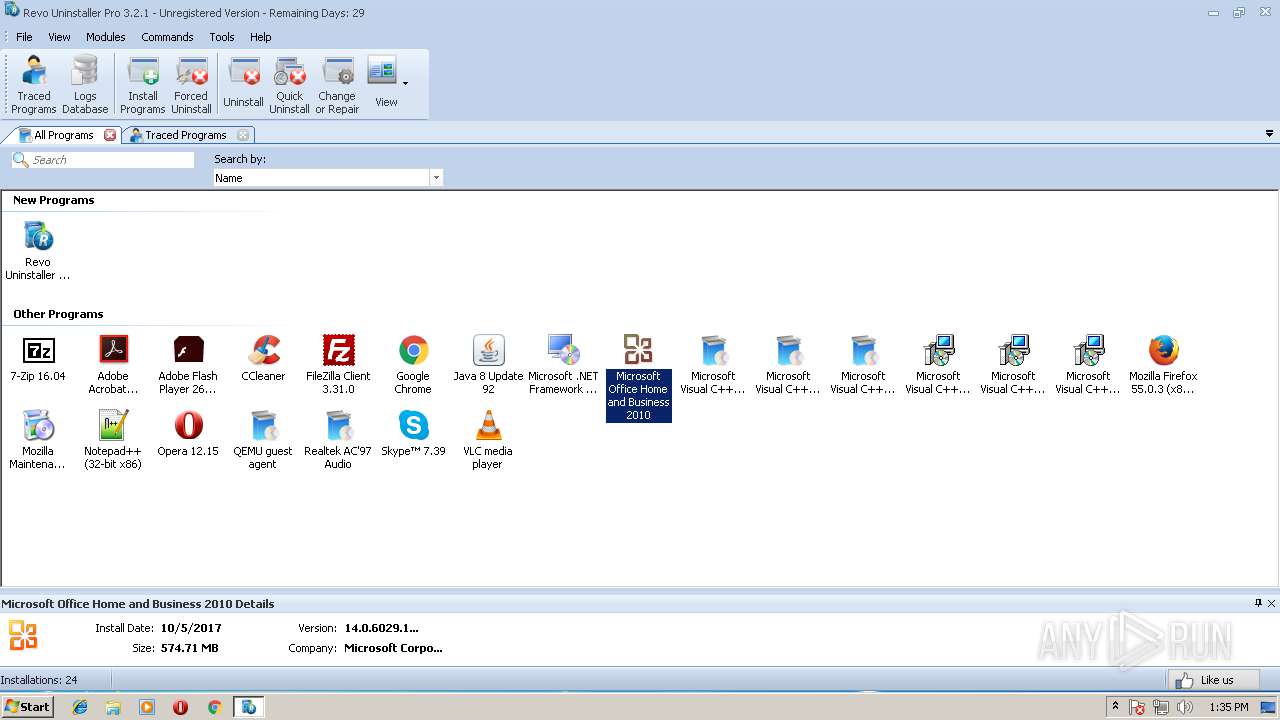
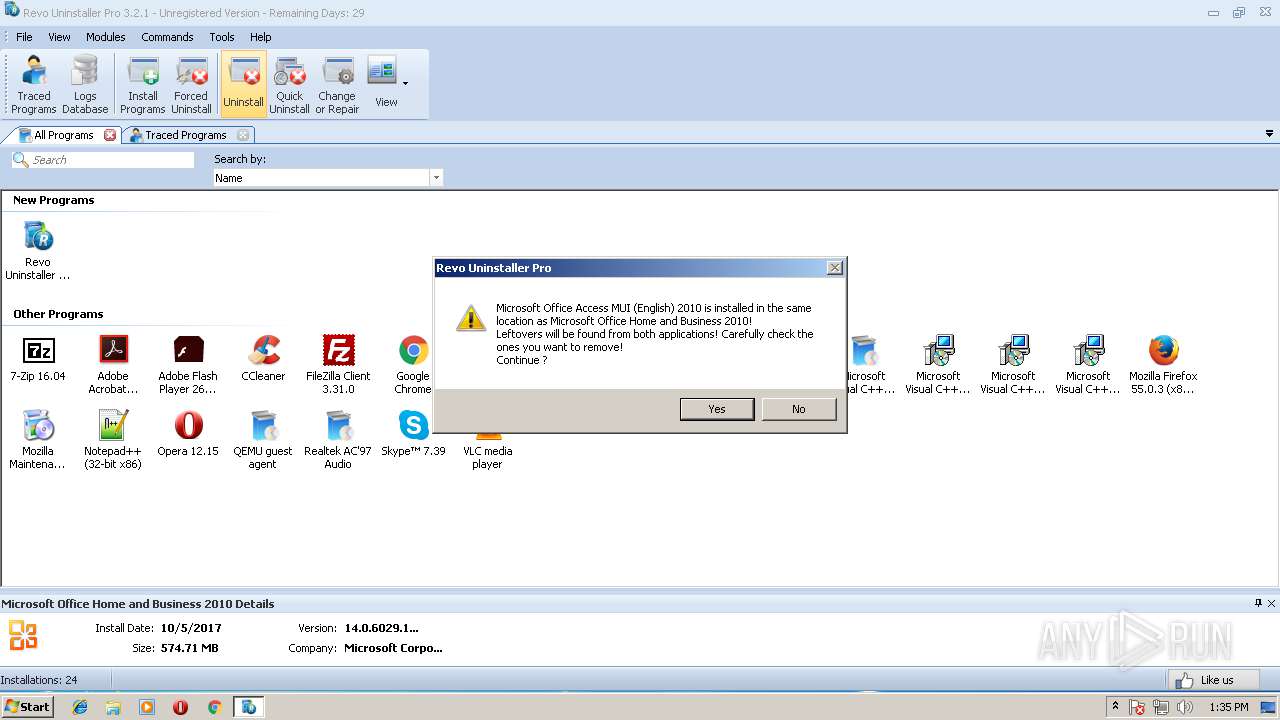
Searches for installed software
- RevoUninPro.exe (PID: 2184)
- setup.exe (PID: 3312)
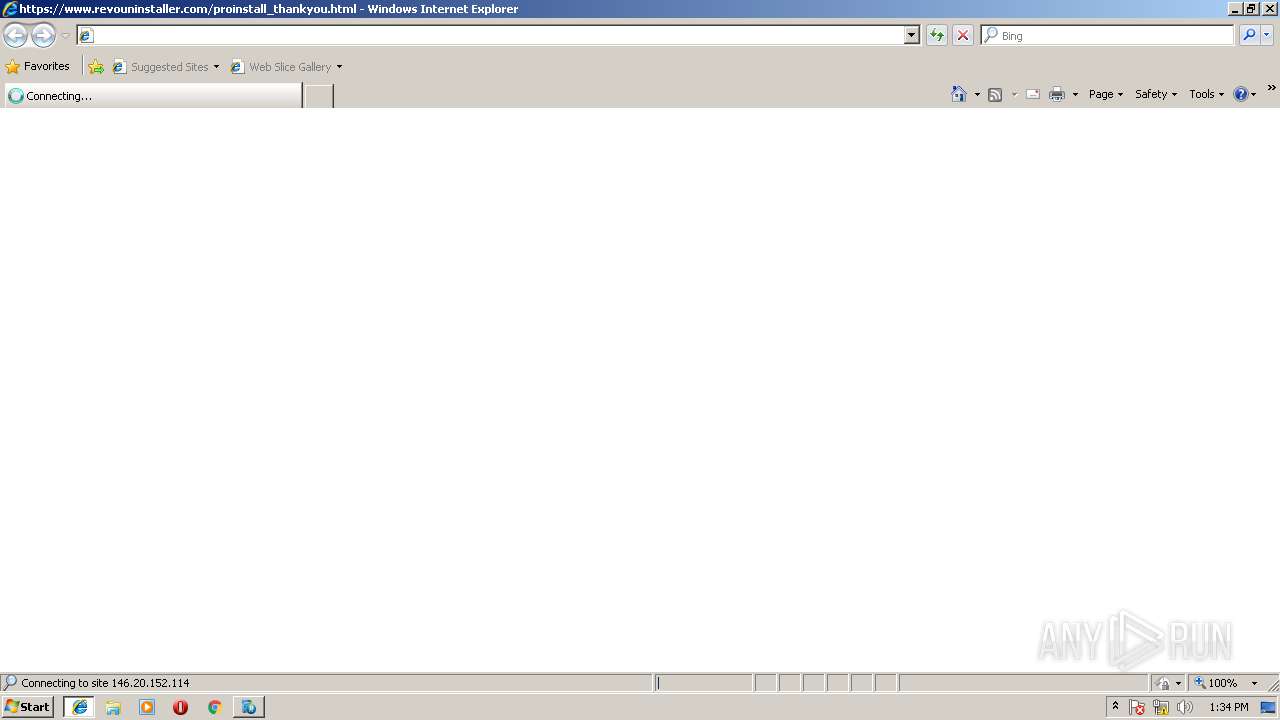
Starts Internet Explorer
- RevoUninProSetup.tmp (PID: 3572)
Creates files in the user directory
- RevoUninProSetup.tmp (PID: 3572)
- uTorrent.exe (PID: 384)
- uTorrent.exe (PID: 3108)
Starts MSHTA.EXE for opening HTA or HTMLS files
- uTorrent.exe (PID: 3108)
Executes scripts
- mshta.exe (PID: 3548)
Checks for external IP
- mshta.exe (PID: 3548)
Creates files in the program directory
- OSPPSVC.EXE (PID: 2492)
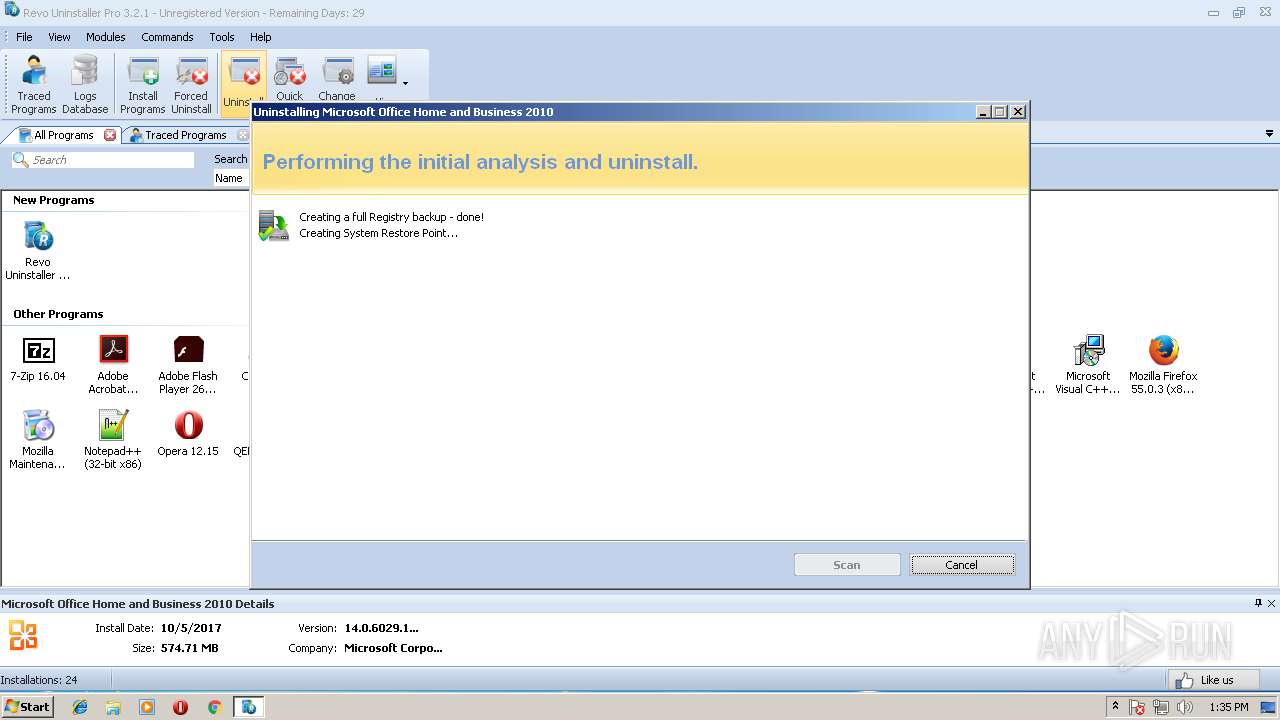
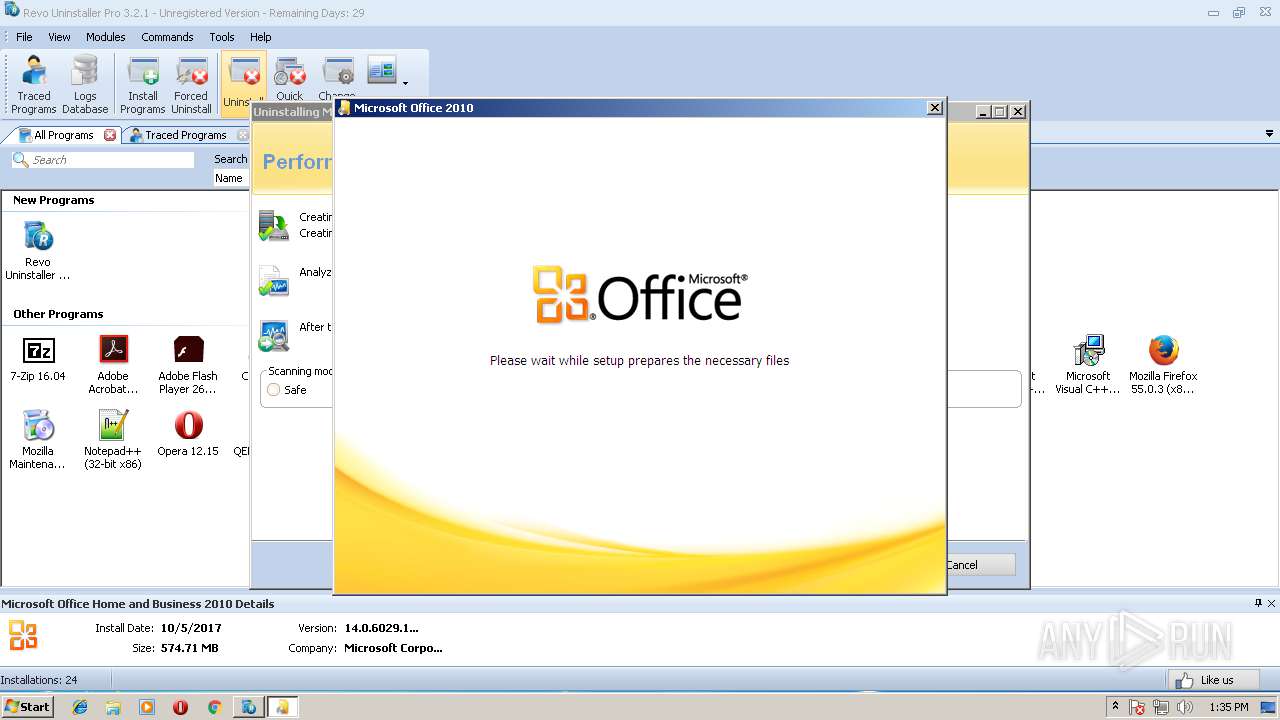
Starts Microsoft Office Application
- msiexec.exe (PID: 1348)
INFO
Application was dropped or rewritten from another process
- RevoUninProSetup.tmp (PID: 976)
- RevoUninProSetup.tmp (PID: 3572)
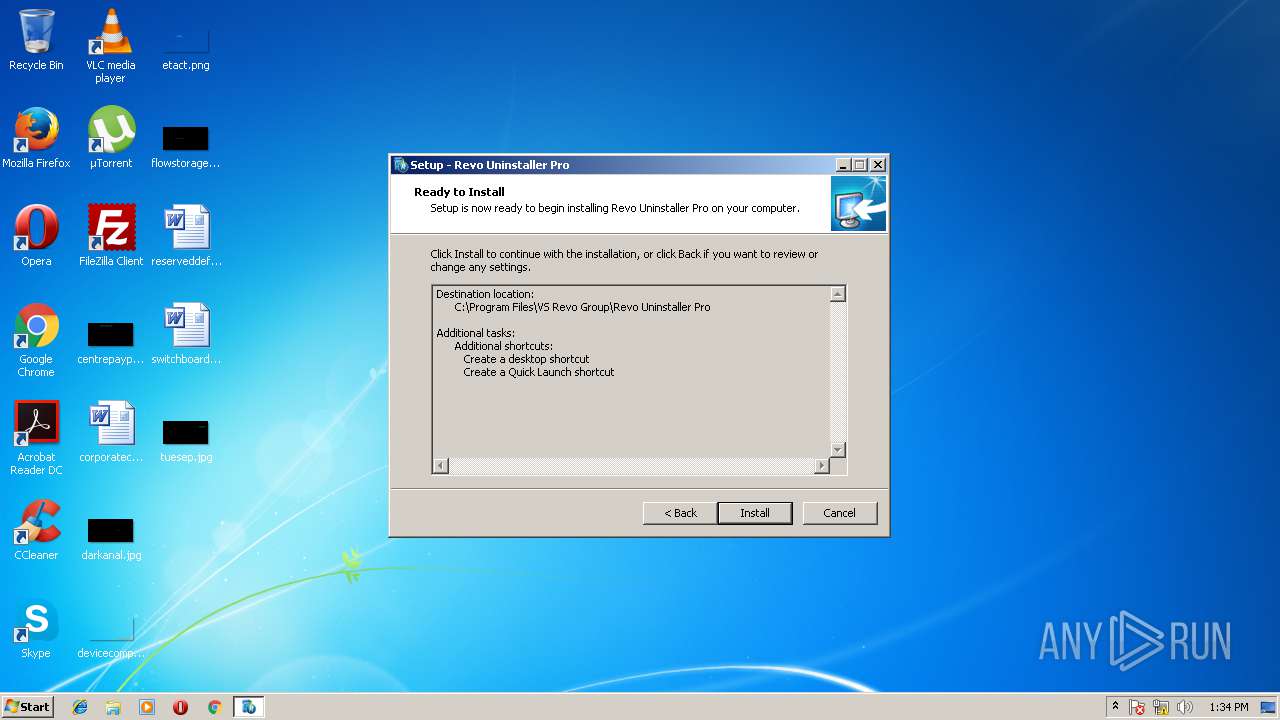
Creates a software uninstall entry
- RevoUninProSetup.tmp (PID: 3572)
Creates files in the program directory
- RevoUninProSetup.tmp (PID: 3572)
- MsiExec.exe (PID: 2520)
- MsiExec.exe (PID: 2668)
- MsiExec.exe (PID: 2508)
- MsiExec.exe (PID: 3620)
- MsiExec.exe (PID: 1628)
- MsiExec.exe (PID: 3368)
- MsiExec.exe (PID: 3380)
- MsiExec.exe (PID: 4084)
- msiexec.exe (PID: 1348)
- MsiExec.exe (PID: 2368)
Dropped object may contain URL's
- rundll32.exe (PID: 3436)
- RevoUninPro.exe (PID: 2184)
- iexplore.exe (PID: 3036)
- RevoUninPro.exe (PID: 2948)
- iexplore.exe (PID: 1544)
- setup.exe (PID: 3312)
- uTorrent.exe (PID: 3108)
- ose.exe (PID: 3828)
- MsiExec.exe (PID: 1264)
- uTorrent.exe (PID: 384)
- MsiExec.exe (PID: 3988)
- RevoUninProSetup.tmp (PID: 3572)
- MsiExec.exe (PID: 1132)
- MsiExec.exe (PID: 3752)
- msiexec.exe (PID: 1348)
- MsiExec.exe (PID: 3528)
- MsiExec.exe (PID: 3980)
- MsiExec.exe (PID: 2164)
- MsiExec.exe (PID: 2824)
- MsiExec.exe (PID: 2972)
Changes settings of System certificates
- iexplore.exe (PID: 3036)
Reads internet explorer settings
- iexplore.exe (PID: 3036)
- mshta.exe (PID: 3548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3036)
Changes internet zones settings
- iexplore.exe (PID: 1544)
Creates or modifies windows services
- vssvc.exe (PID: 2812)
Creates files in the user directory
- iexplore.exe (PID: 3036)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2812)
Reads settings of System Certificates
- DrvInst.exe (PID: 3564)
Reads Microsoft Office registry keys
- setup.exe (PID: 3312)
- MsiExec.exe (PID: 2824)
- MSOHTMED.EXE (PID: 2984)
Application launched itself
- msiexec.exe (PID: 1348)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2508)
- MsiExec.exe (PID: 3752)
- MsiExec.exe (PID: 1264)
- MsiExec.exe (PID: 2520)
- MsiExec.exe (PID: 2668)
- MsiExec.exe (PID: 3528)
- MsiExec.exe (PID: 3620)
- msiexec.exe (PID: 1348)
- MsiExec.exe (PID: 1132)
- MsiExec.exe (PID: 2420)
- MsiExec.exe (PID: 2968)
- MsiExec.exe (PID: 1628)
- MsiExec.exe (PID: 1824)
- MsiExec.exe (PID: 2148)
- MsiExec.exe (PID: 2736)
- MsiExec.exe (PID: 2972)
- MsiExec.exe (PID: 3260)
- MsiExec.exe (PID: 2848)
- MsiExec.exe (PID: 2368)
- MsiExec.exe (PID: 4044)
- MsiExec.exe (PID: 3480)
- MsiExec.exe (PID: 2164)
- MsiExec.exe (PID: 3980)
- MsiExec.exe (PID: 3368)
- MsiExec.exe (PID: 3380)
- MsiExec.exe (PID: 1612)
- MsiExec.exe (PID: 4084)
- MsiExec.exe (PID: 3988)
- MsiExec.exe (PID: 2824)
- MsiExec.exe (PID: 3504)
- MsiExec.exe (PID: 3828)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 133120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.1.0 |
| ProductVersionNumber: | 3.2.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | VS Revo Group |
| FileDescription: | Revo Uninstaller Pro |
| FileVersion: | 3.2.1.0 |
| LegalCopyright: | VS Revo Group, Ltd. |
| ProductName: | Revo Uninstaller Pro |
| ProductVersion: | 3.2.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | VS Revo Group |
| FileDescription: | Revo Uninstaller Pro |
| FileVersion: | 3.2.1.0 |
| LegalCopyright: | VS Revo Group, Ltd. |
| ProductName: | Revo Uninstaller Pro |
| ProductVersion: | 3.2.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0001E7F8 | 0x0001E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.55543 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.31163 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.40198 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.54703 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.66897 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.51052 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
191
Monitored processes
114
Malicious processes
16
Suspicious processes
54
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
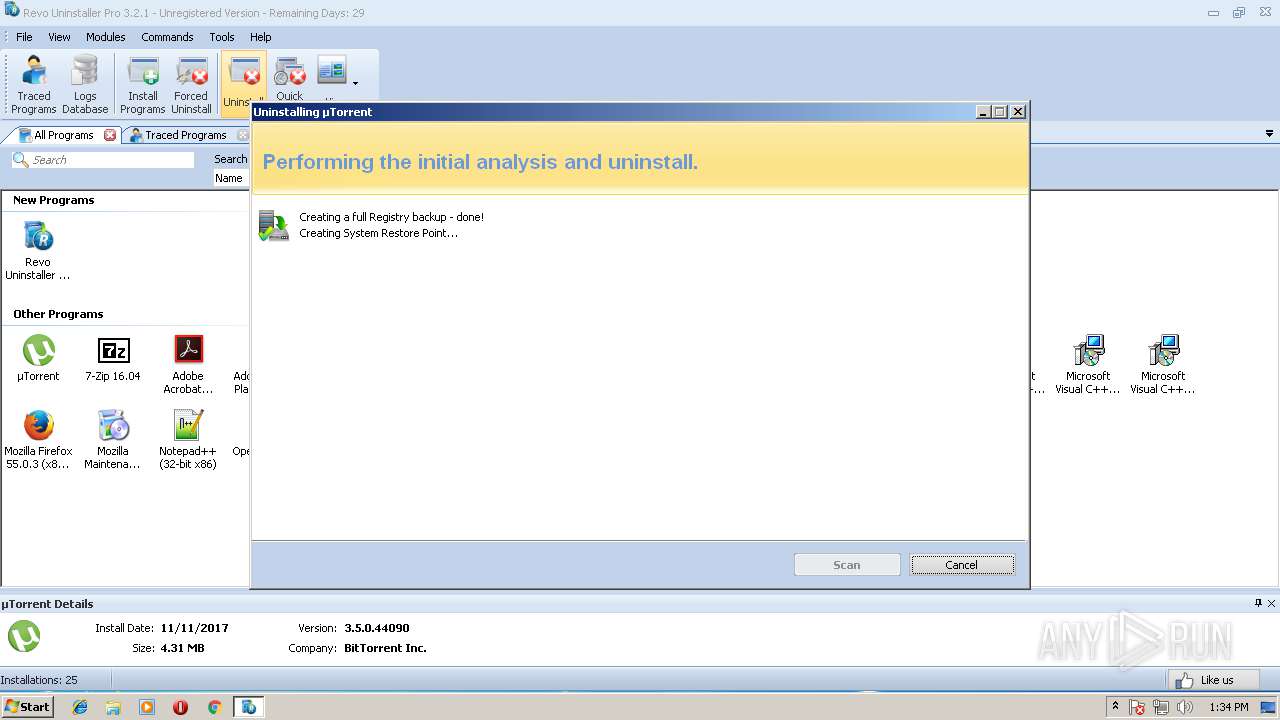
| 384 | "C:\Users\admin\AppData\Roaming\uTorrent\uTorrent.exe" /UNINSTALL | C:\Users\admin\AppData\Roaming\uTorrent\uTorrent.exe | RevoUninPro.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: HIGH Description: µTorrent Exit code: 0 Version: 3.5.0.44090 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\ose00000.exe" -standalone | C:\Users\admin\AppData\Local\Temp\ose00000.exe | — | ose.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Office Source Engine Exit code: 0 Version: 14.0.4730.1010 Modules
| |||||||||||||||
| 676 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe uninstall "Microsoft.VisualStudio.Tools.Applications.ServerDocument.v9.0, Version=9.0.0.00000000, Culture=neutral, PublicKeyToken=B03F5F7F11D50A3A" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 708 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe uninstall "Microsoft.VisualStudio.Tools.Applications.Contract.v10.0, Version=10.0.0.00000, Culture=neutral, PublicKeyToken=B03F5F7F11D50A3A" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 840 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 108 -InterruptEvent 0 -NGENProcess fc -Pipe 104 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | "C:\Users\admin\AppData\Local\Temp\is-08J4C.tmp\RevoUninProSetup.tmp" /SL5="$90146,11643902,200704,C:\Users\admin\AppData\Local\Temp\RevoUninProSetup.exe" | C:\Users\admin\AppData\Local\Temp\is-08J4C.tmp\RevoUninProSetup.tmp | — | RevoUninProSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1132 | C:\Windows\system32\MsiExec.exe -Embedding 7970C83B38BBA8FDA8315B6F275DD054 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe uninstall "Microsoft.VisualStudio.Tools.Applications.Contract.v9.0, Version=9.0.0.00000000, Culture=neutral, PublicKeyToken=B03F5F7F11D50A3A" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1248 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 108 -InterruptEvent 0 -NGENProcess fc -Pipe 104 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
57 647
Read events
22 945
Write events
2 358
Delete events
32 344
Modification events
| (PID) Process: | (868) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 5 | |||
| (PID) Process: | (868) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 4 | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {2C5515DC-2A7E-4BFD-B813-CACC2B685EB7} |
Value: Revo Uninstaller Pro Extension | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{1D928D64-60D3-4FAC-B810-C4D9D8A680CF} |
| Operation: | write | Name: | |
Value: RUExt | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\RUExt.DLL |
| Operation: | write | Name: | AppID |
Value: {1D928D64-60D3-4FAC-B810-C4D9D8A680CF} | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{2C5515DC-2A7E-4BFD-B813-CACC2B685EB7} |
| Operation: | write | Name: | |
Value: RUShellExt Class | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{2C5515DC-2A7E-4BFD-B813-CACC2B685EB7}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RUExt.dll | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{2C5515DC-2A7E-4BFD-B813-CACC2B685EB7}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shellex\ContextMenuHandlers\RUShellExt |
| Operation: | write | Name: | |
Value: {2C5515DC-2A7E-4BFD-B813-CACC2B685EB7} | |||
| (PID) Process: | (2032) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Msi.Package\shellex\ContextMenuHandlers\RUShellExt |
| Operation: | write | Name: | |
Value: {2C5515DC-2A7E-4BFD-B813-CACC2B685EB7} | |||
Executable files
490
Suspicious files
175
Text files
639
Unknown types
131
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\is-GE28E.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-0SCHE.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-BBH3M.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-3A5P4.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-94A7H.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-0MPVR.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-8QGAN.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-PADN8.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-RBD56.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | RevoUninProSetup.tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-2UGN5.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
40
DNS requests
17
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
384 | uTorrent.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
384 | uTorrent.exe | GET | 200 | 67.215.238.66:80 | http://download-lb.utorrent.com/endpoint/hydra-ut/os/win7/track/stable/cc-tag/290/browser/ie/os-region/US/os-lang/en/os-ver/6.1/enc-ver/111258682/ | US | compressed | 761 Kb | whitelisted |
3548 | mshta.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json?callback=jQuery191021957326772279573_1527338101879&_=1527338101880 | DE | text | 427 b | malicious |
3108 | uTorrent.exe | GET | 200 | 67.215.238.66:80 | http://download-lb.utorrent.com/endpoint/hydra-ut/os/win7/track/stable/cc-tag/290/browser/ie/os-region/US/os-lang/en/os-ver/6.1/enc-ver/111258682/ | US | compressed | 761 Kb | whitelisted |
384 | uTorrent.exe | POST | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3252 | cscript.exe | GET | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjMxMDgiLCJoIjoiMzVGbVZyYjRwLTdTUUZTdCIsInYiOiIxMTEyNTg2ODIiLCJiIjo0NDA5MCwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJXaW5kb3dzIEludGVybmV0IEV4cGxvcmVyIiwiZGJ2IjoiOC4wIiwiaWJyIjpbeyJuYW1lIjoiRmlyZWZveCIsInZlcnNpb24iOiI1NS4wIiwiZXhlTmFtZSI6ImZpcmVmb3gifSx7Im5hbWUiOiJHb29nbGUgQ2hyb21lIiwidmVyc2lvbiI6IjYxLjAiLCJleGVOYW1lIjoiY2hyb21lIn0seyJuYW1lIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiI4LjAiLCJleGVOYW1lIjoiaWV4cGxvcmUifSx7Im5hbWUiOiJPcGVyYSBJbnRlcm5ldCBCcm93c2VyIiwidmVyc2lvbiI6IjEyLjE1IiwiZXhlTmFtZSI6Im9wZXJhIn1dLCJpcCI6Ijg1LjIwNi4xNzUuMjIxIiwiY24iOiJSZXB1YmxpYyBvZiBMaXRodWFuaWEiLCJwYWNraWQiOiJsYXZhc29mdF95YWhvbyJ9 | US | text | 21 b | whitelisted |
384 | uTorrent.exe | POST | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3108 | uTorrent.exe | POST | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3108 | uTorrent.exe | POST | 200 | 174.129.255.167:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
1544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1544 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3036 | iexplore.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3036 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3036 | iexplore.exe | 172.217.22.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3036 | iexplore.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
384 | uTorrent.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
384 | uTorrent.exe | 67.215.238.66:80 | download-lb.utorrent.com | QuadraNet, Inc | US | suspicious |
3108 | uTorrent.exe | 67.215.238.66:80 | download-lb.utorrent.com | QuadraNet, Inc | US | suspicious |
3036 | iexplore.exe | 2.18.233.88:443 | f057a20f961f56a72089-b74530d2d26278124f446233f95622ef.ssl.cf1.rackcdn.com | Akamai International B.V. | — | whitelisted |
3252 | cscript.exe | 174.129.255.167:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.revouninstaller.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
f057a20f961f56a72089-b74530d2d26278124f446233f95622ef.ssl.cf1.rackcdn.com |
| unknown |
www.google-analytics.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client response_code |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client response_code |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client response_code |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
384 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client response_code |
3108 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
3108 | uTorrent.exe | Misc activity | [PT POLICY] uTorrent Hydra Client POST JSON |
Process | Message |
|---|---|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|