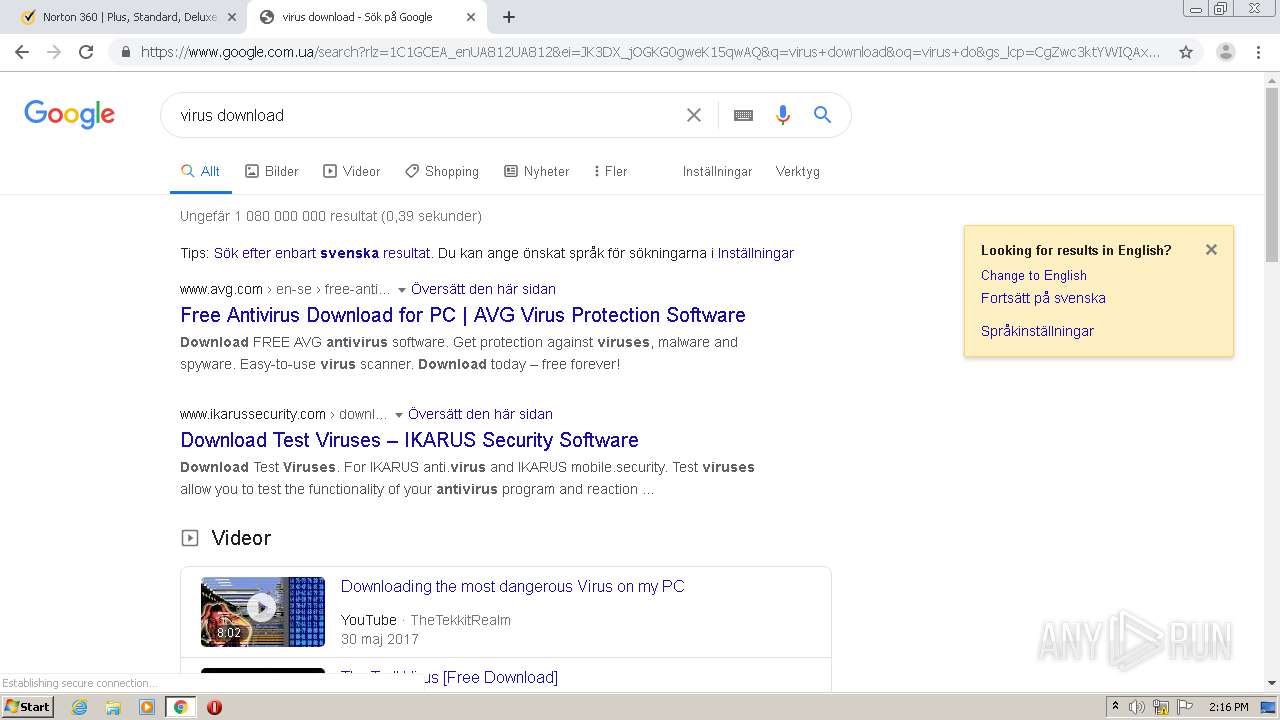
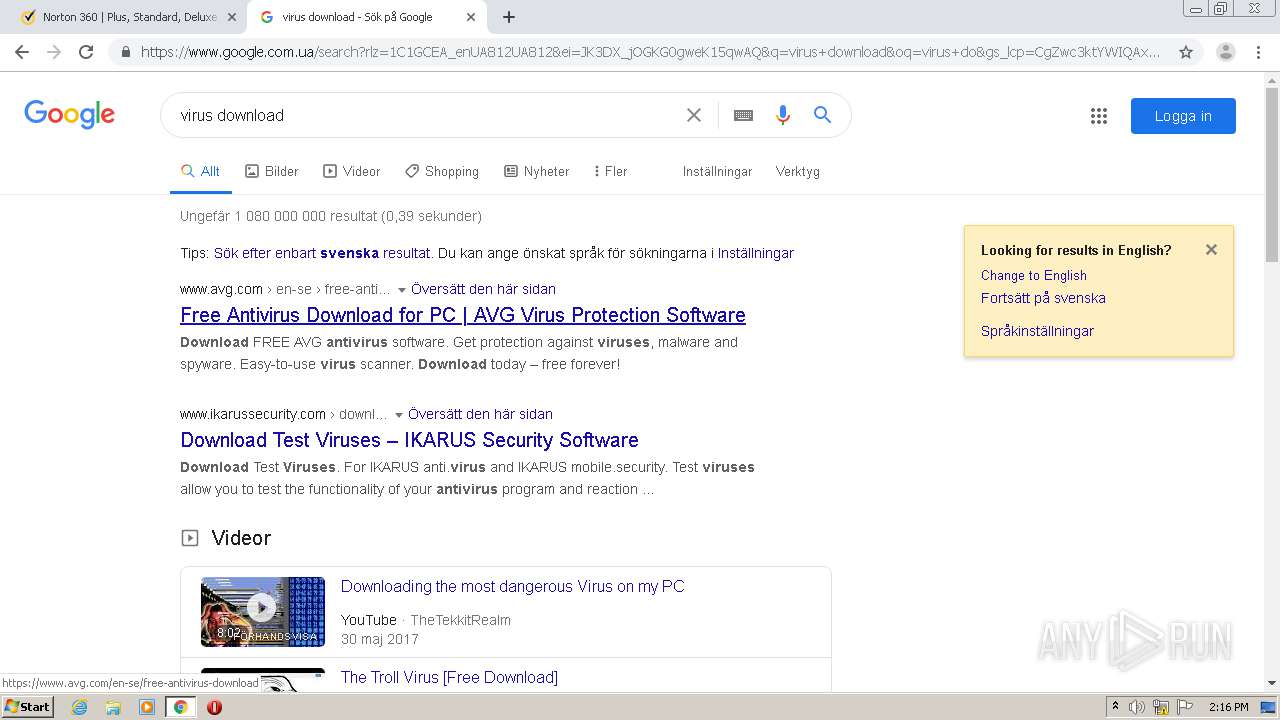
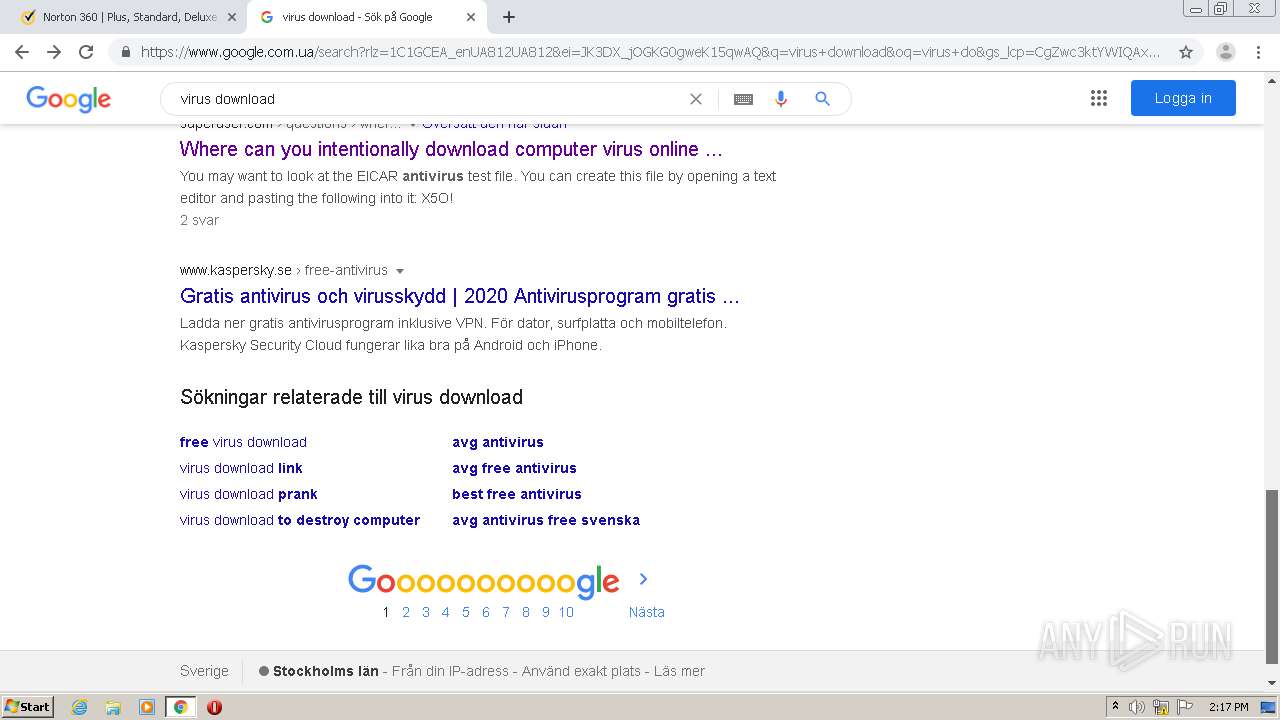
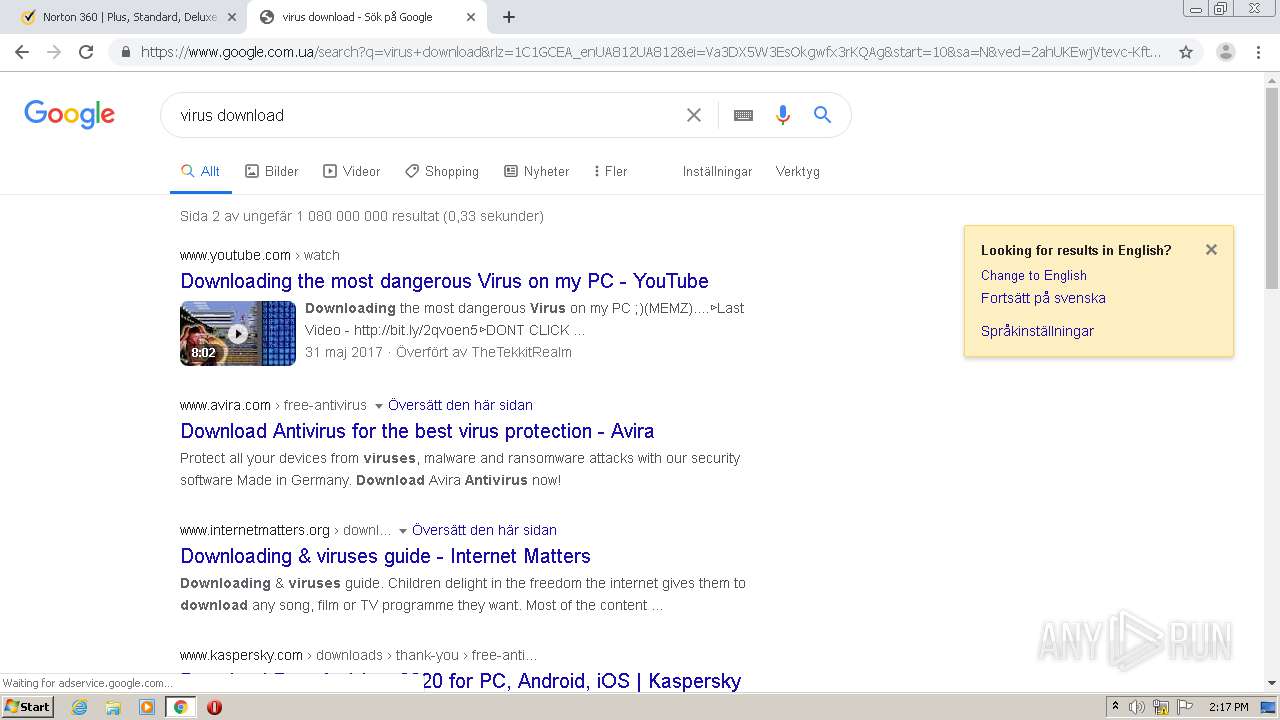
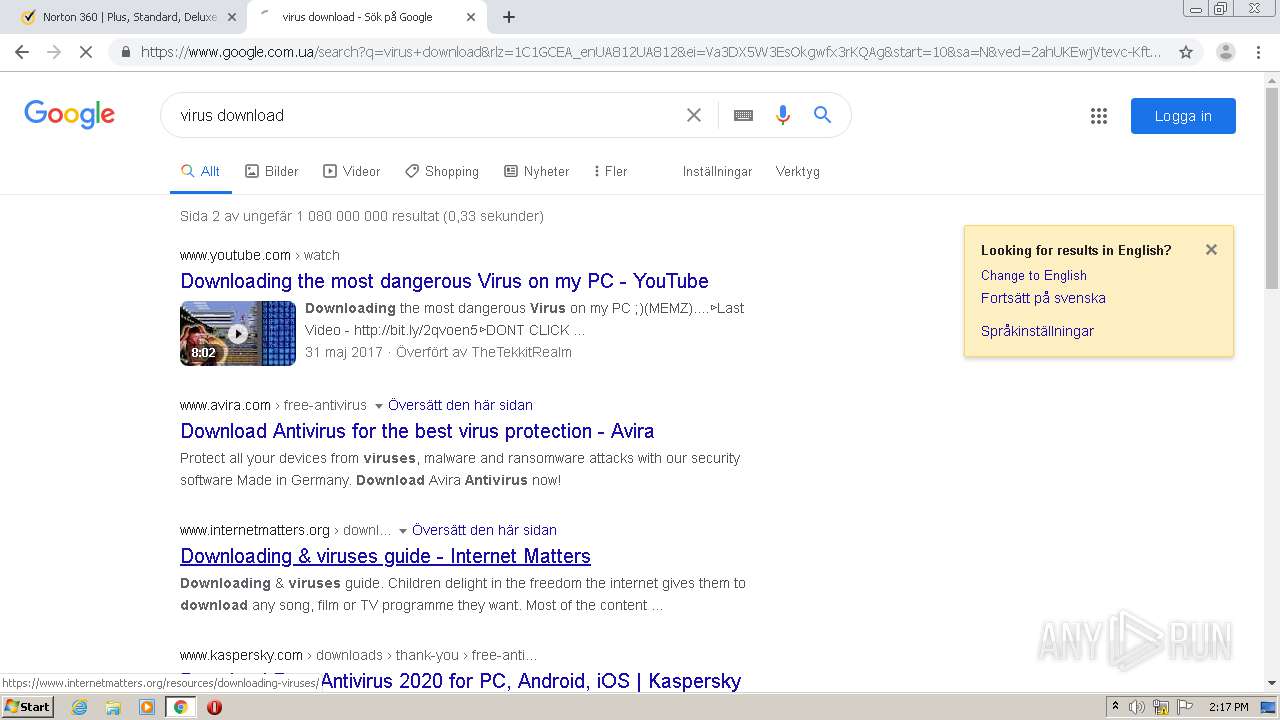
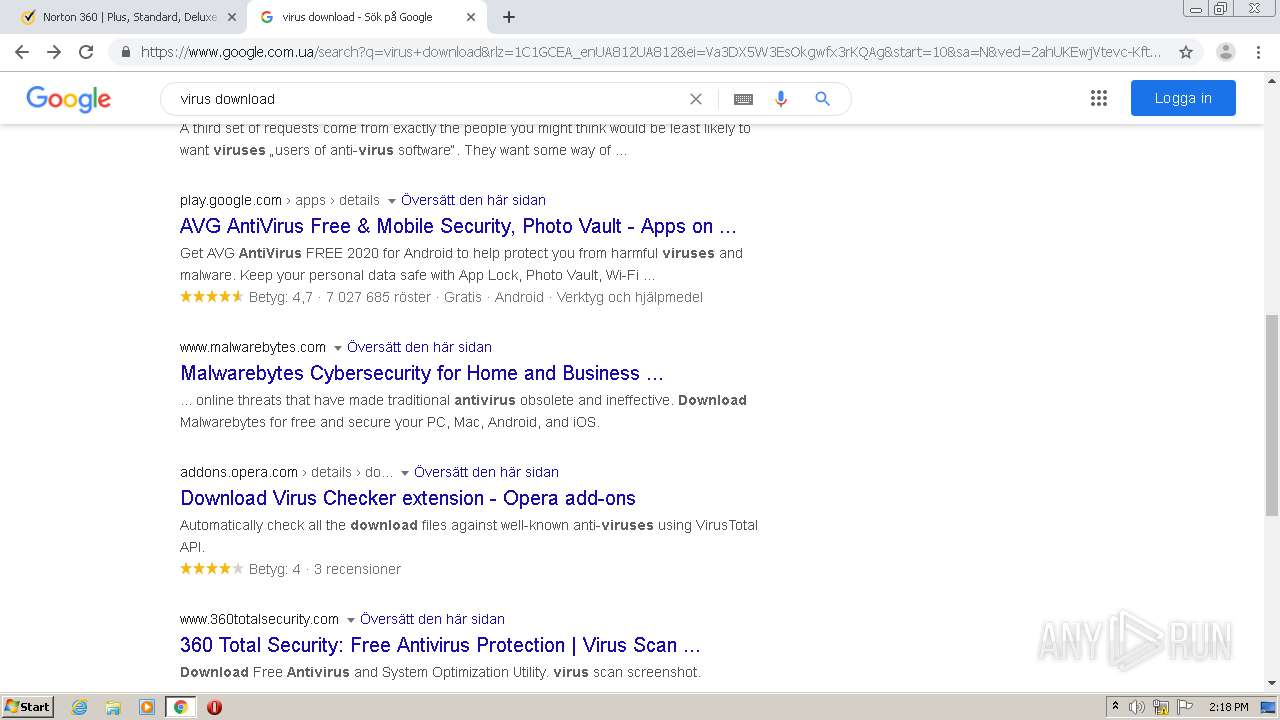
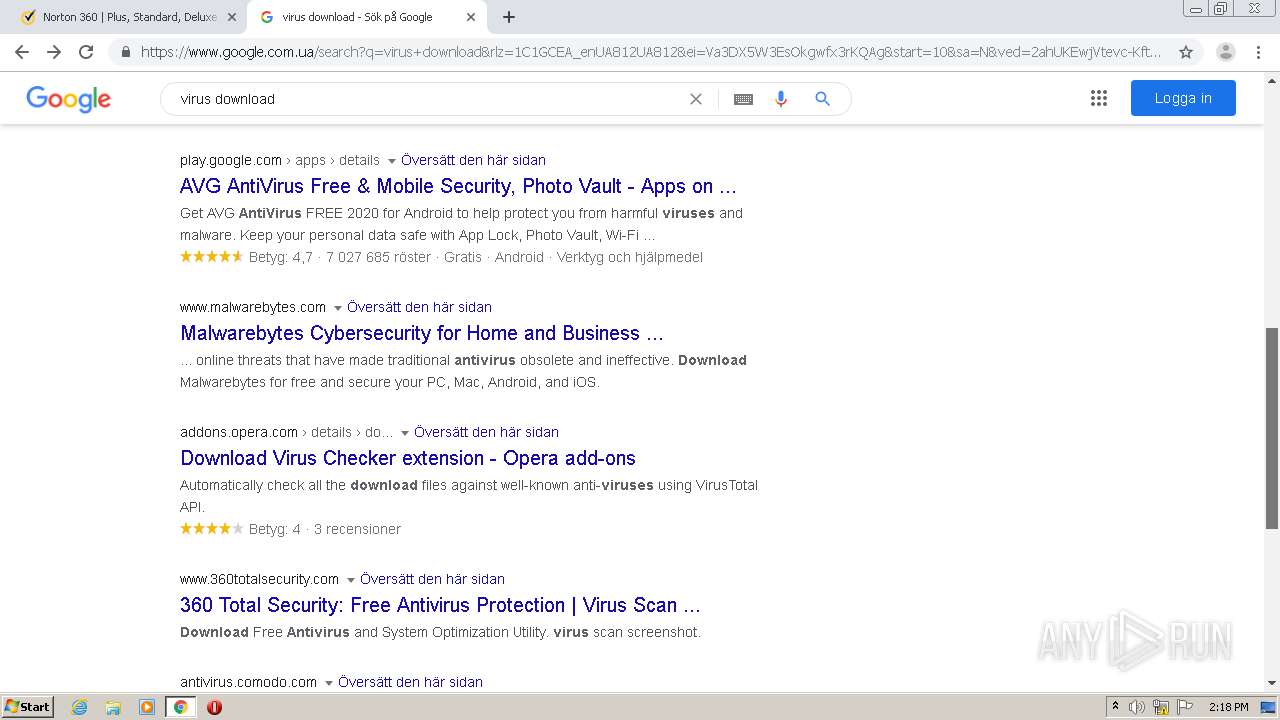
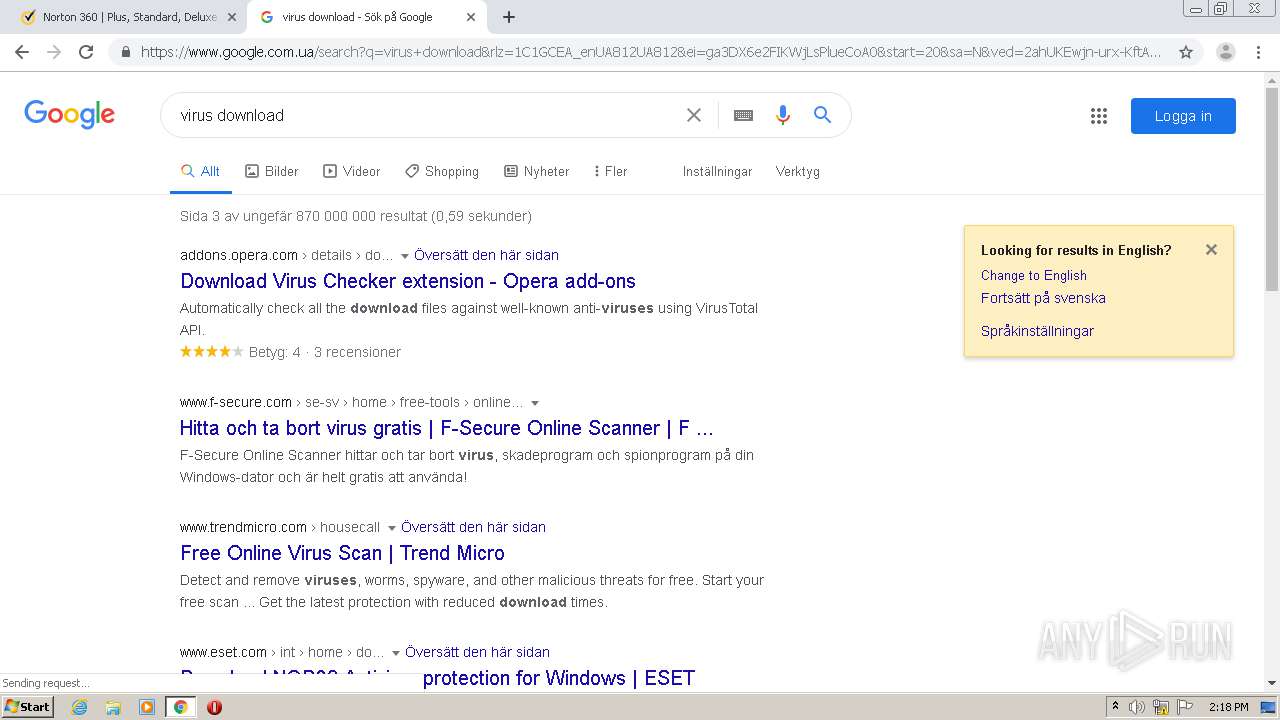
| URL: | http://yabs.yandex.ru/count/WeSejI_zO3O2xHC0T28ChUvhr3wg30K0DWCnpAp3Nm00000u109mbDoviyqVW041Y07JkfUYCv01Zi7WzowO0UAfc9yjk07OclV20i01NDW1kjAG0-01oFld2kW1_0680iolTPW2wgkY2Q02XBYM0S02cFNOrit_bEmEc0FX-oERuWRu1Bde78W5kUWSa0NtiY-W1PFK2QW5azG9i0MJr0cu1QFn3y05puWio0MpuWxvskbwmj4b1j46-MuVyiBH9GPgQP4edl4fucAm1u20c2ou1u05q0S6s0S7u0UG3V47GCSE0hnTnvc0We21n820XfW1u0Y2d4k02W6O2Z392XzGDUsGDV6g2n2qMSvnQP400DUzSeC_jGK0sGle2xde7F0B2eWCvB7UlW6f3103-4zFrCW_w0od0k0DWu20G8aETBKL-ylkw_crfzUdkFII1g0Em8Gzs0u1eG-yT9CO15RmFzaFu0y1W12vZgO4e23G4FAOhr_u4082fjSZ0GapEZ-n4WH4P0KwhU8_wH9ZfdatWjrkhWQe4-FIfuQfgVlvu1EZyG-W5AFn3wWKzx8llFwm_GNe50JG5Rp-iFq5s1N1YlRieu-y_6Fme1RG_glz1T0MvB7UlW615vWNWifzg1S9m1Sqs1V0X3sP6A0O0R0OwBUE_WNG627u6A7athZkdEEY_0606R3qkEBGlP6v890P0Q0PgWEm6RWP____0T8P4dbXOdDVSsLoTcLoBt8qE3KjCXa0fsNWYgrIz13BZnAmouPdqGTOrOap2IiFaqQ7n09UW164FohNAV288oQ0b3SczxXSvDxollwx3YBW2ZP_XW3g0RhUmEh1lO2LyHSDtkWHIoD44m00~1?from=yandex.ru%3Bsearch%26%23x2F%3B%3Bweb%3B%3B0%3B&q=%D0%BF%D1%80%D0%BE%D0%B2%D0%B5%D1%80%D0%B8%D1%82%D1%8C+%D0%BA%D0%BE%D0%BC%D0%BF%D1%8C%D1%8E%D1%82%D0%B5%D1%80+%D0%BD%D0%B0+%D0%B2%D0%B8%D1%80%D1%83%D1%81%D1%8B+%D0%BE%D0%BD%D0%BB%D0%B0%D0%B9%D0%BD+%D0%B1%D0%B5%D1%81%D0%BF%D0%BB%D0%B0%D1%82%D0%BD%D0%BE+%D0%B1%D0%B5%D0%B7+%D1%81%D0%BA%D0%B0%D1%87%D0%B8%D0%B2%D0%B0%D0%BD%D0%B8%D1%8F+%D0%B8+%D0%B2%D1%8B%D0%BB%D0%B5%D1%87%D0%B8%D1%82%D1%8C&etext=2202.YCLelgCFCbmJsP6Gh5qSk4j9SWgn72XbIqKosiH4bHZTZe7A0udlMyAEJ7ADtD7s6HSHwnGdpE59IuQUUmLpWJwf4LcXzUKwdMwxLmbzLOog3tET3N_eCEaW0aSC17Iinc-I-MukX2_zzphCPGWB72cwhJCyCBn32Xix6Z2dc1VDd1i8AeGFpk4DuRcYJ4bebGVhaHpodGJmaWFwY2Z3Zg.9372da1e10fd522e6459084c4b35a67e7a0e200d&baobab_event_id=ki37gkqjt |
| Full analysis: | https://app.any.run/tasks/67186931-d699-458b-9e34-6a0cac0aa20c |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 14:14:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 230D1ADD9E341CB62F59DA30A06654F4 |
| SHA1: | 2660F34A74C4BB874AAA21B2769EE30758381CBC |
| SHA256: | 156F29E7F2AA4B92D19E382B1D31FEC977B63068867A59F81CC05E3DA15D17A8 |
| SSDEEP: | 24:aAWAzMm+XPtn7hbUArCg1efkWvcAIxVVt15J3BKA6+/dEOVTT03bDPlYE9D1:yAQm+x1wWBefkW1IxVVH53KA11I3H15 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2800)
Executable content was dropped or overwritten
- chrome.exe (PID: 2800)
INFO
Reads the hosts file
- chrome.exe (PID: 2800)
- chrome.exe (PID: 992)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2800)
Reads settings of System Certificates
- chrome.exe (PID: 992)
Application launched itself
- chrome.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2841074949425715649 --mojo-platform-channel-handle=2764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3611764677533529022 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3898842117124179070 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4627029804513835174 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17298638912270530016 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=517606941329898858 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5469225759766094498 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12612251696380337099 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10757053131356450190 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,15907635839552640485,10760742883903349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16887784019488683172 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
936
Read events
862
Write events
71
Delete events
3
Modification events
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2800-13251132914655750 |
Value: 259 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
179
Text files
166
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3ACF3-AF0.pma | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e9ae42cc-5991-43dd-87d0-c0069ba8a80a.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF18d404.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18d3b6.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF18d443.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d5d9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
125
DNS requests
92
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
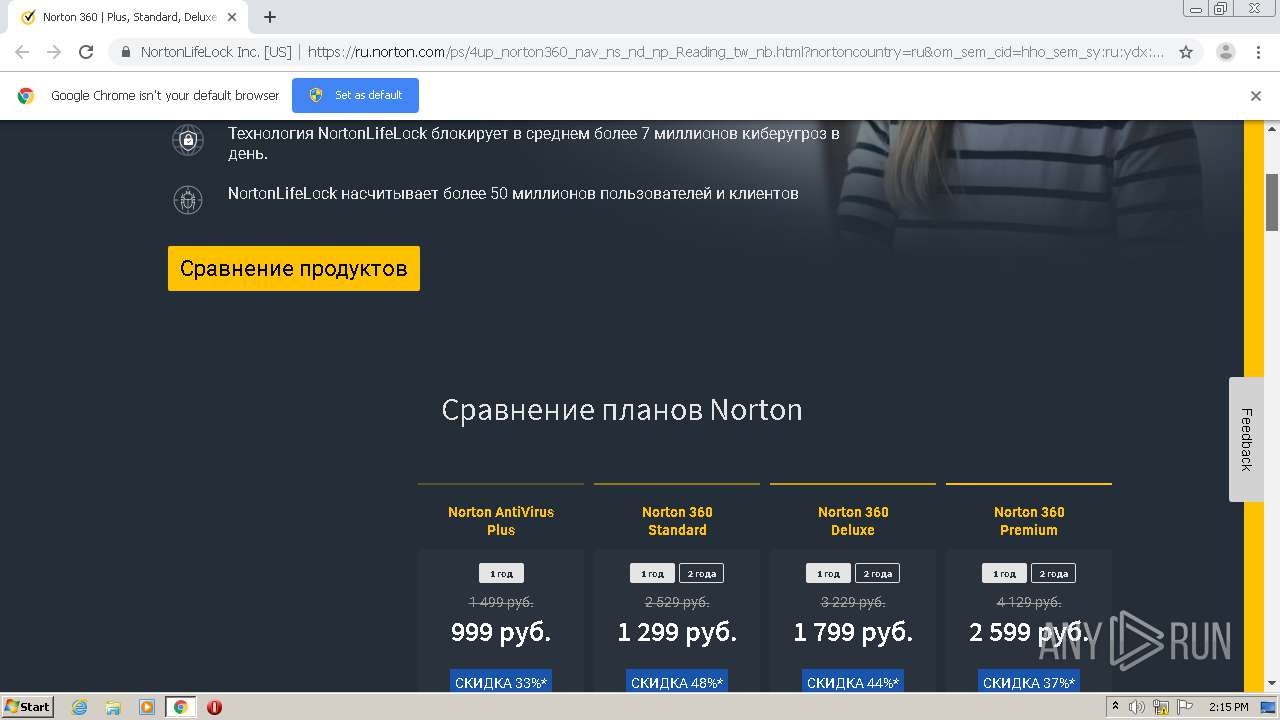
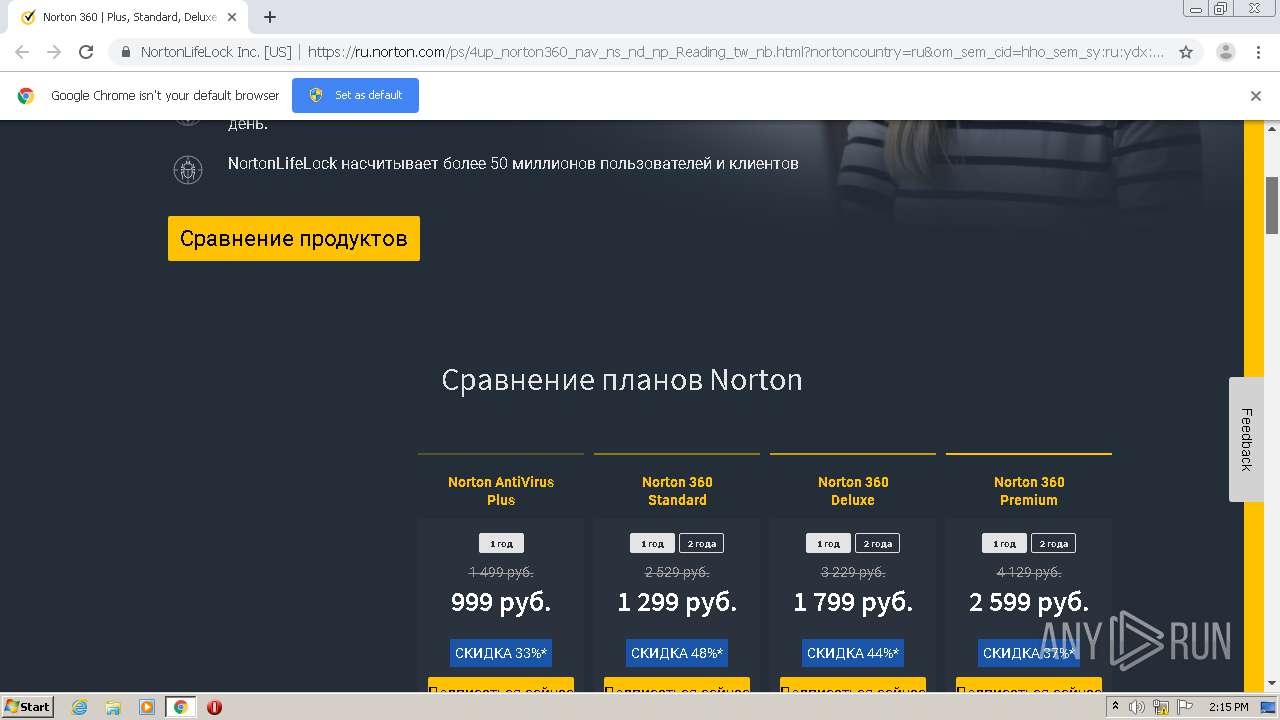
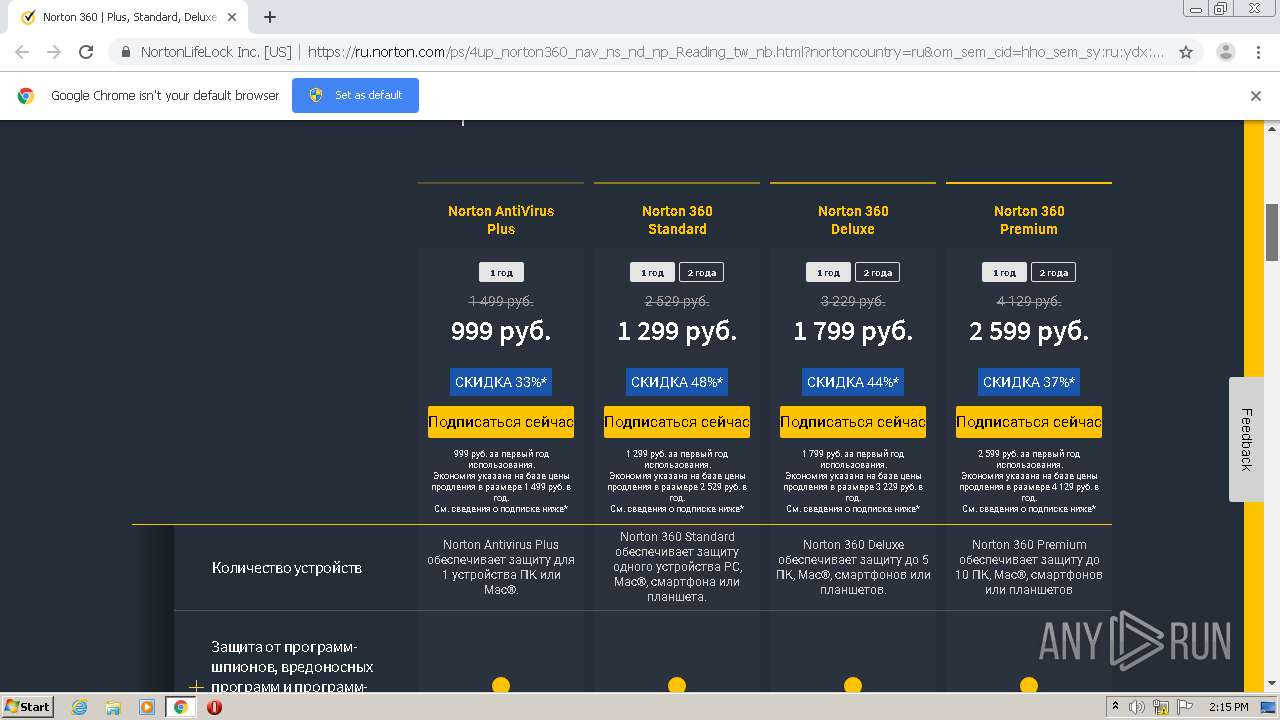
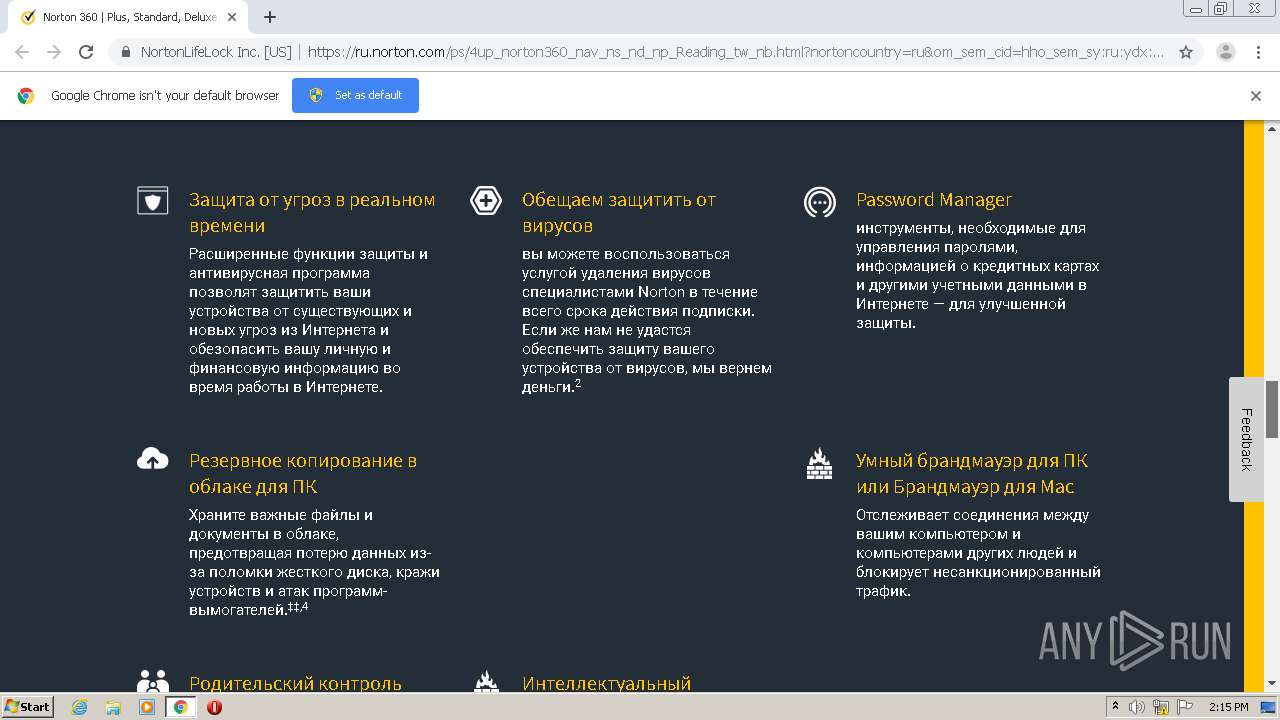
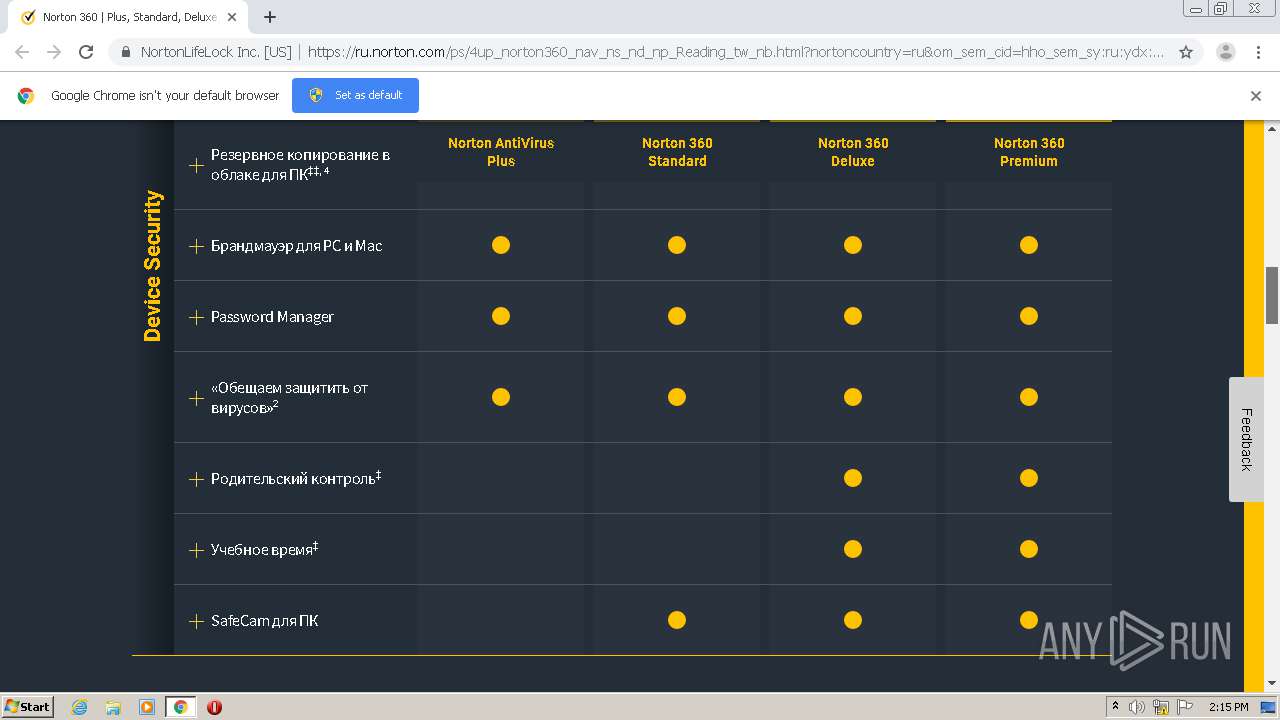
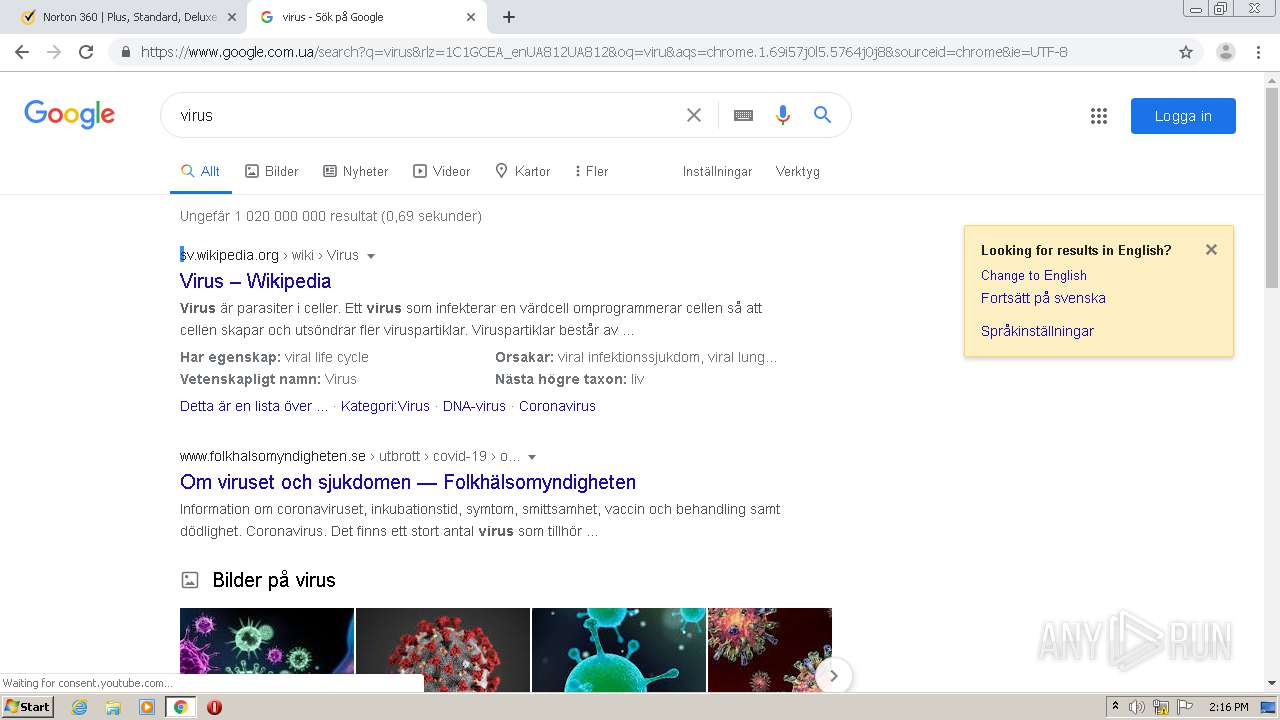
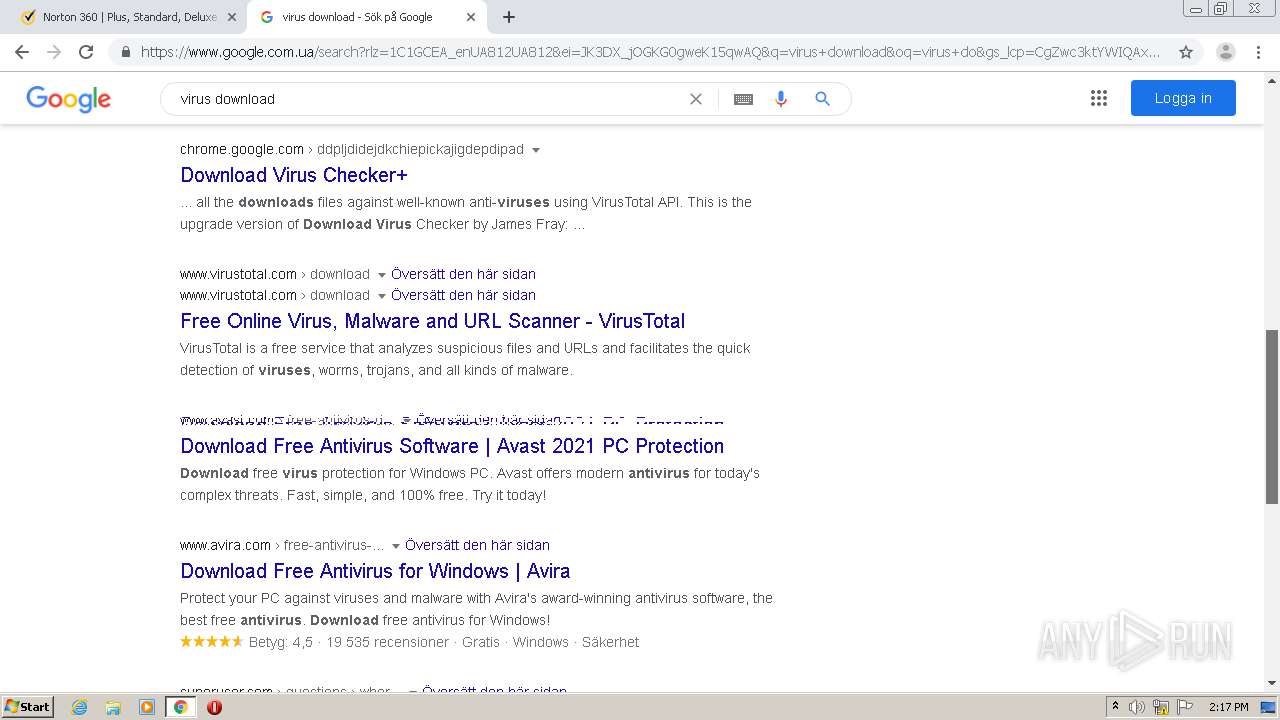
992 | chrome.exe | GET | 301 | 23.43.196.49:80 | http://ru.norton.com/ps/4up_norton360_nav_ns_nd_np_Reading_tw_nb.html?nortoncountry=ru&om_sem_cid=hho_sem_sy:ru:ydx:ru:e:nb:kw0000382213:6072502897&country=RU&yclid=7125314285640905130&gclid=CO3hkK_4p-0CFcVUGwod19MFpA&gclsrc=ds | US | — | — | unknown |
992 | chrome.exe | GET | 200 | 87.250.250.91:80 | http://yabs.yandex.ru/count/WeSejI_zO3O2xHC0T28ChUvhr3wg30K0DWCnpAp3Nm00000u109mbDoviyqVW041Y07JkfUYCv01Zi7WzowO0UAfc9yjk07OclV20i01NDW1kjAG0-01oFld2kW1_0680iolTPW2wgkY2Q02XBYM0S02cFNOrit_bEmEc0FX-oERuWRu1Bde78W5kUWSa0NtiY-W1PFK2QW5azG9i0MJr0cu1QFn3y05puWio0MpuWxvskbwmj4b1j46-MuVyiBH9GPgQP4edl4fucAm1u20c2ou1u05q0S6s0S7u0UG3V47GCSE0hnTnvc0We21n820XfW1u0Y2d4k02W6O2Z392XzGDUsGDV6g2n2qMSvnQP400DUzSeC_jGK0sGle2xde7F0B2eWCvB7UlW6f3103-4zFrCW_w0od0k0DWu20G8aETBKL-ylkw_crfzUdkFII1g0Em8Gzs0u1eG-yT9CO15RmFzaFu0y1W12vZgO4e23G4FAOhr_u4082fjSZ0GapEZ-n4WH4P0KwhU8_wH9ZfdatWjrkhWQe4-FIfuQfgVlvu1EZyG-W5AFn3wWKzx8llFwm_GNe50JG5Rp-iFq5s1N1YlRieu-y_6Fme1RG_glz1T0MvB7UlW615vWNWifzg1S9m1Sqs1V0X3sP6A0O0R0OwBUE_WNG627u6A7athZkdEEY_0606R3qkEBGlP6v890P0Q0PgWEm6RWP____0T8P4dbXOdDVSsLoTcLoBt8qE3KjCXa0fsNWYgrIz13BZnAmouPdqGTOrOap2IiFaqQ7n09UW164FohNAV288oQ0b3SczxXSvDxollwx3YBW2ZP_XW3g0RhUmEh1lO2LyHSDtkWHIoD44m00~1?from=yandex.ru%3Bsearch%26%23x2F%3B%3Bweb%3B%3B0%3B&q=%D0%BF%D1%80%D0%BE%D0%B2%D0%B5%D1%80%D0%B8%D1%82%D1%8C+%D0%BA%D0%BE%D0%BC%D0%BF%D1%8C%D1%8E%D1%82%D0%B5%D1%80+%D0%BD%D0%B0+%D0%B2%D0%B8%D1%80%D1%83%D1%81%D1%8B+%D0%BE%D0%BD%D0%BB%D0%B0%D0%B9%D0%BD+%D0%B1%D0%B5%D1%81%D0%BF%D0%BB%D0%B0%D1%82%D0%BD%D0%BE+%D0%B1%D0%B5%D0%B7+%D1%81%D0%BA%D0%B0%D1%87%D0%B8%D0%B2%D0%B0%D0%BD%D0%B8%D1%8F+%D0%B8+%D0%B2%D1%8B%D0%BB%D0%B5%D1%87%D0%B8%D1%82%D1%8C&etext=2202.YCLelgCFCbmJsP6Gh5qSk4j9SWgn72XbIqKosiH4bHZTZe7A0udlMyAEJ7ADtD7s6HSHwnGdpE59IuQUUmLpWJwf4LcXzUKwdMwxLmbzLOog3tET3N_eCEaW0aSC17Iinc-I-MukX2_zzphCPGWB72cwhJCyCBn32Xix6Z2dc1VDd1i8AeGFpk4DuRcYJ4bebGVhaHpodGJmaWFwY2Z3Zg.9372da1e10fd522e6459084c4b35a67e7a0e200d&baobab_event_id=ki37gkqjt | RU | html | 1.79 Kb | whitelisted |
992 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEA3jLpmVqI7sA8RkWHln6Ck%3D | US | der | 471 b | whitelisted |
992 | chrome.exe | GET | 200 | 23.44.192.112:80 | http://buy-static.norton.com/norton/ps/super_ant_nortoncom.html?lp=ps/4up_norton360_nav_ns_nd_np_Reading_tw_nb.html&nortoncountry=ru&om_sem_cid=hho_sem_sy:ru:ydx:ru:e:nb:kw0000382213:6072502897&country=RU&yclid=7125314285640905130&gclid=CO3hkK_4p-0CFcVUGwod19MFpA&gclsrc=ds | US | html | 415 b | whitelisted |
992 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
992 | chrome.exe | 35.181.18.61:443 | oms.norton.com | — | CA | suspicious |
992 | chrome.exe | 35.186.249.72:443 | d.impactradius-event.com | Google Inc. | US | suspicious |
992 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
992 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
992 | chrome.exe | 87.250.250.91:80 | yabs.yandex.ru | YANDEX LLC | RU | whitelisted |
992 | chrome.exe | 216.58.207.38:443 | ad.doubleclick.net | Google Inc. | US | whitelisted |
992 | chrome.exe | 23.100.48.86:443 | buy.norton.com | Microsoft Corporation | IE | whitelisted |
992 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 23.44.192.112:80 | buy-static.norton.com | Akamai Technologies, Inc. | US | unknown |
992 | chrome.exe | 23.43.196.49:80 | ru.norton.com | Akamai International B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yabs.yandex.ru |
| whitelisted |
accounts.google.com |
| shared |
ad.doubleclick.net |
| whitelisted |
buy.norton.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
buy-static.norton.com |
| whitelisted |
ru.norton.com |
| unknown |
now.symassets.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
nexus.ensighten.com |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |