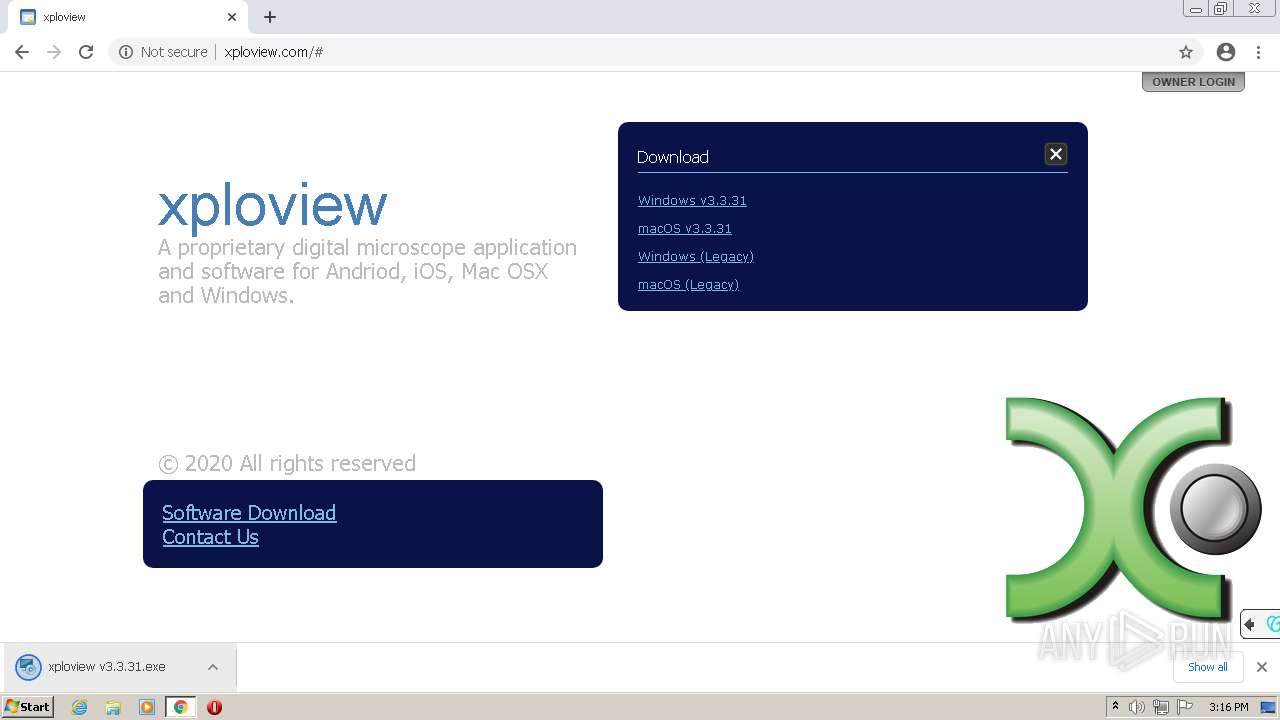
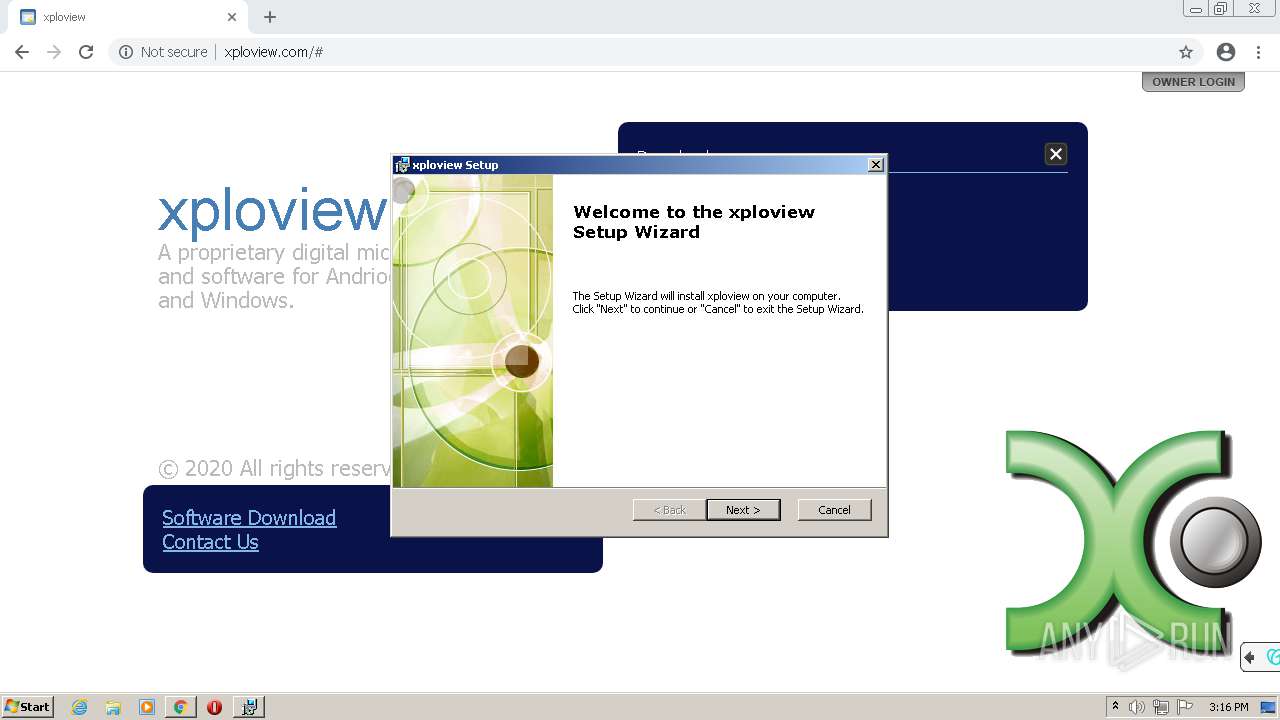
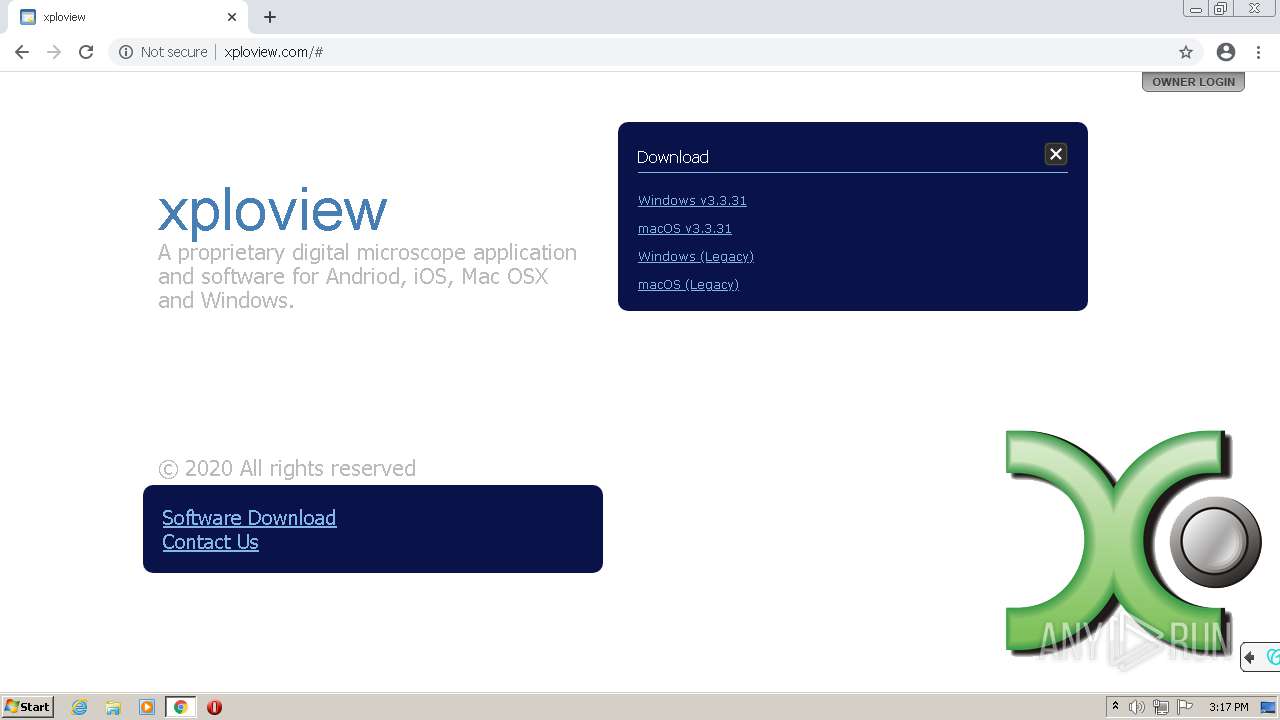
| URL: | http://www.xploview.com/ |
| Full analysis: | https://app.any.run/tasks/34806ffb-023c-48b9-8bad-513f906f7286 |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2021, 14:15:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 919879E9E0906902C6E322B82244E81D |
| SHA1: | EF2928BD33B0BE428A18D623D766EA9BD1F50CE9 |
| SHA256: | 1554FD2FC0155A0CEC63469CA29AA1A21F4657384D56040EB34E29B7E9E676CE |
| SSDEEP: | 3:N1KJS4Ld3:Cc4LR |
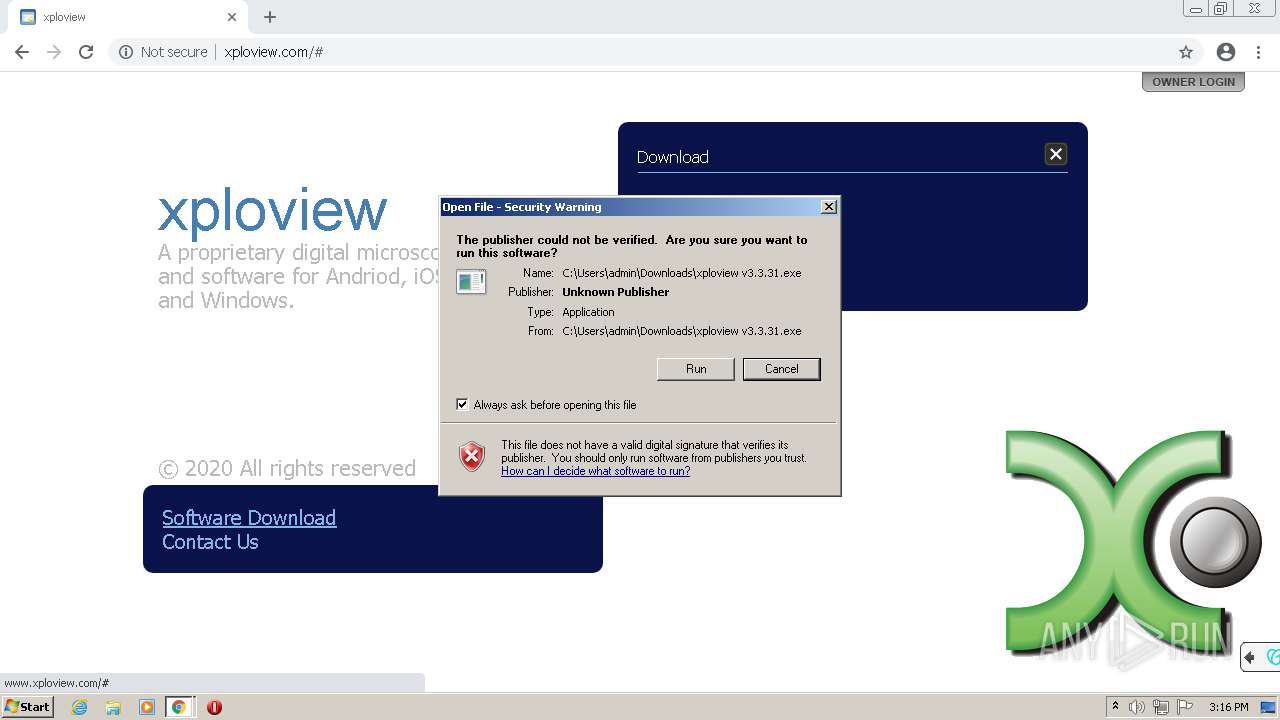
MALICIOUS
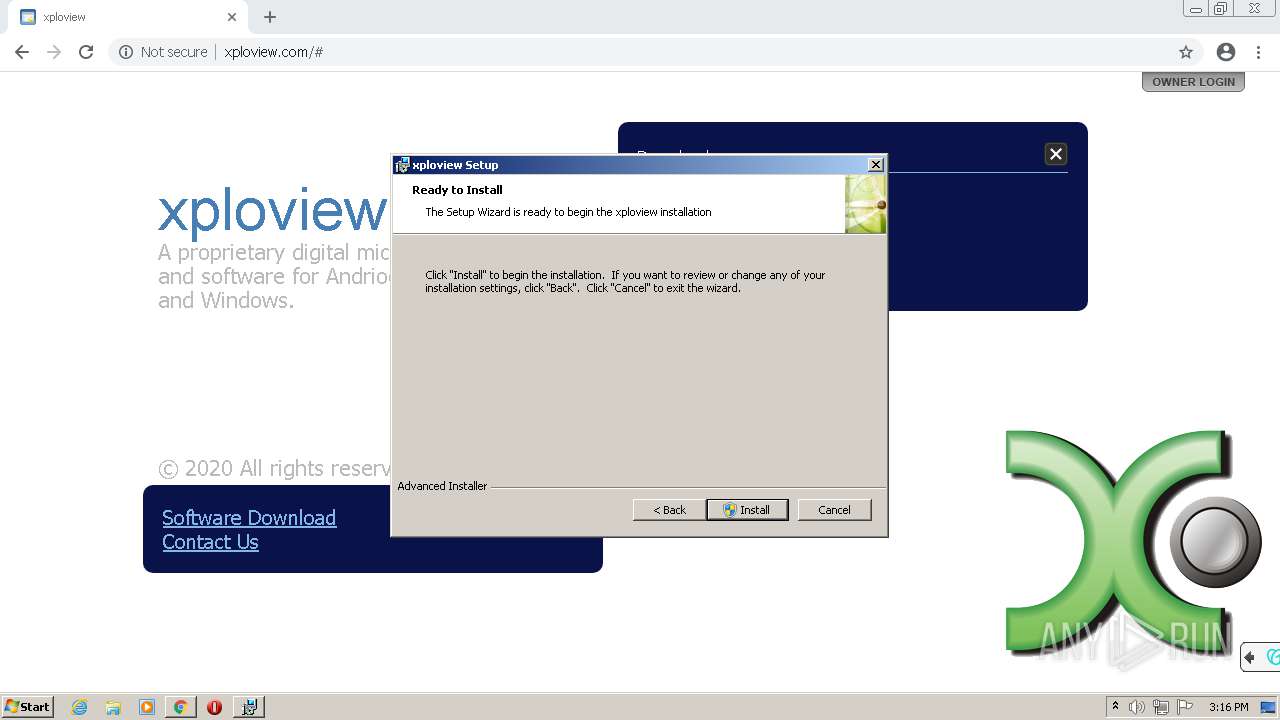
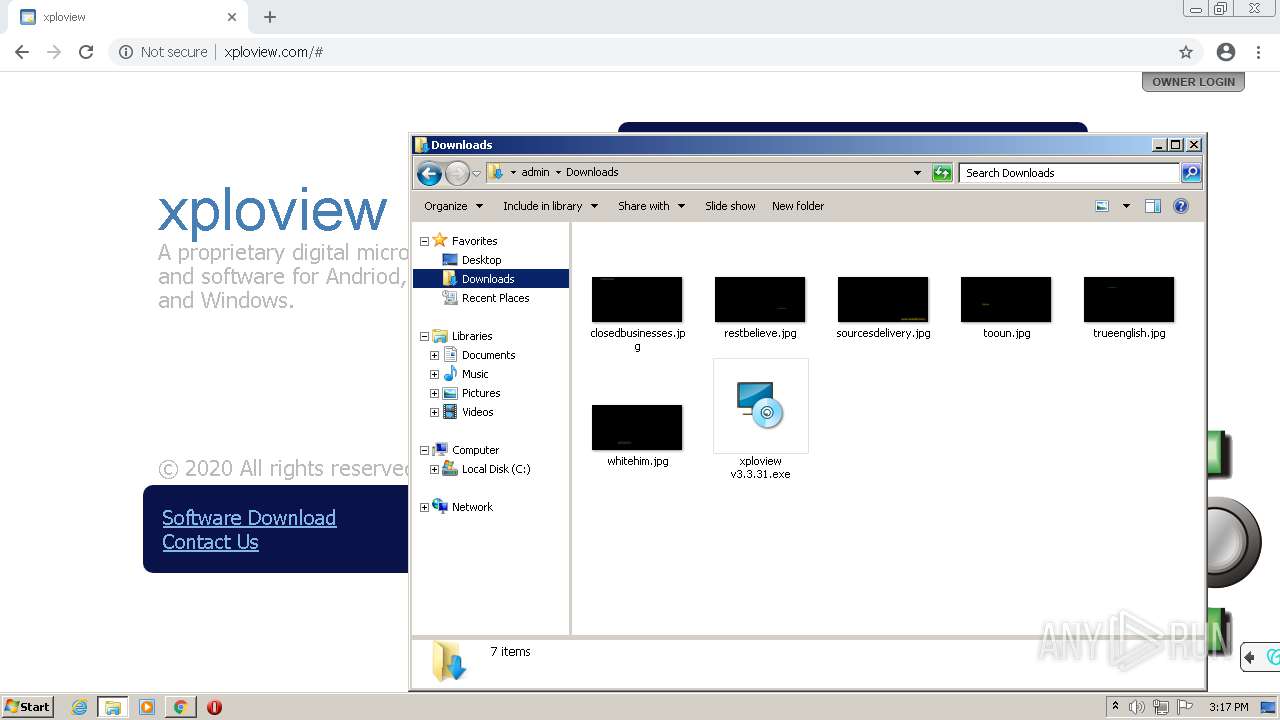
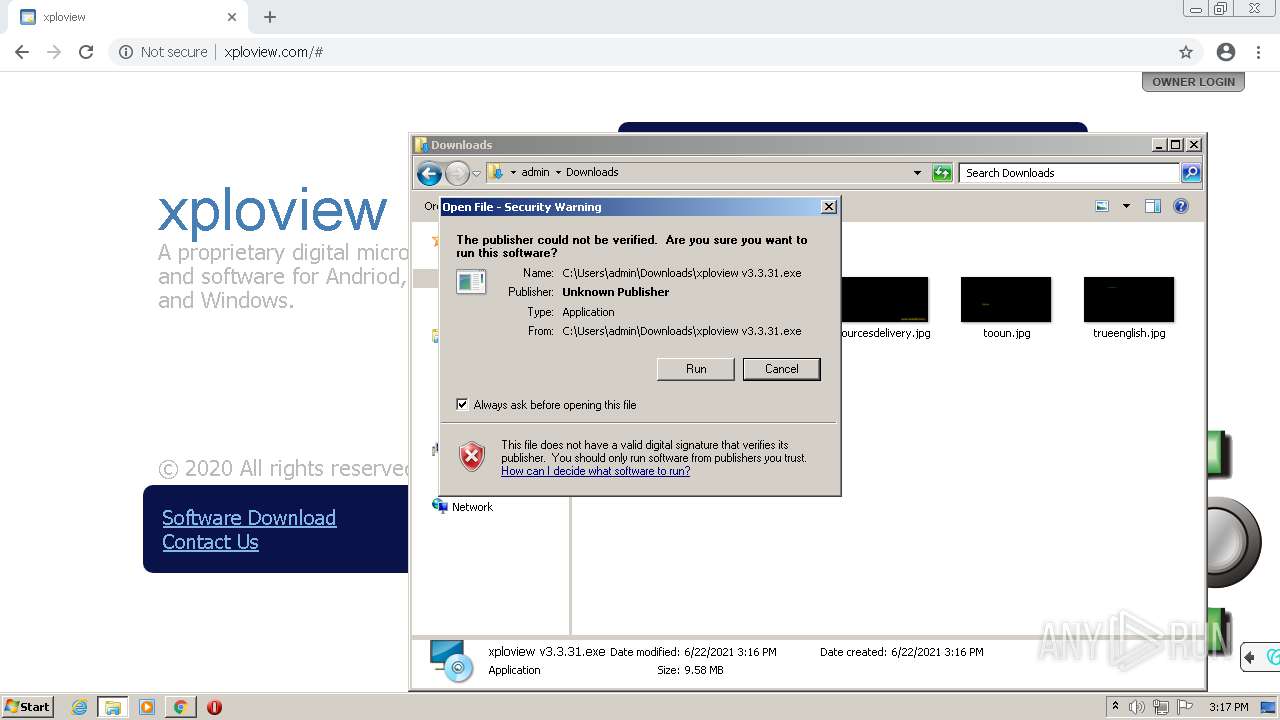
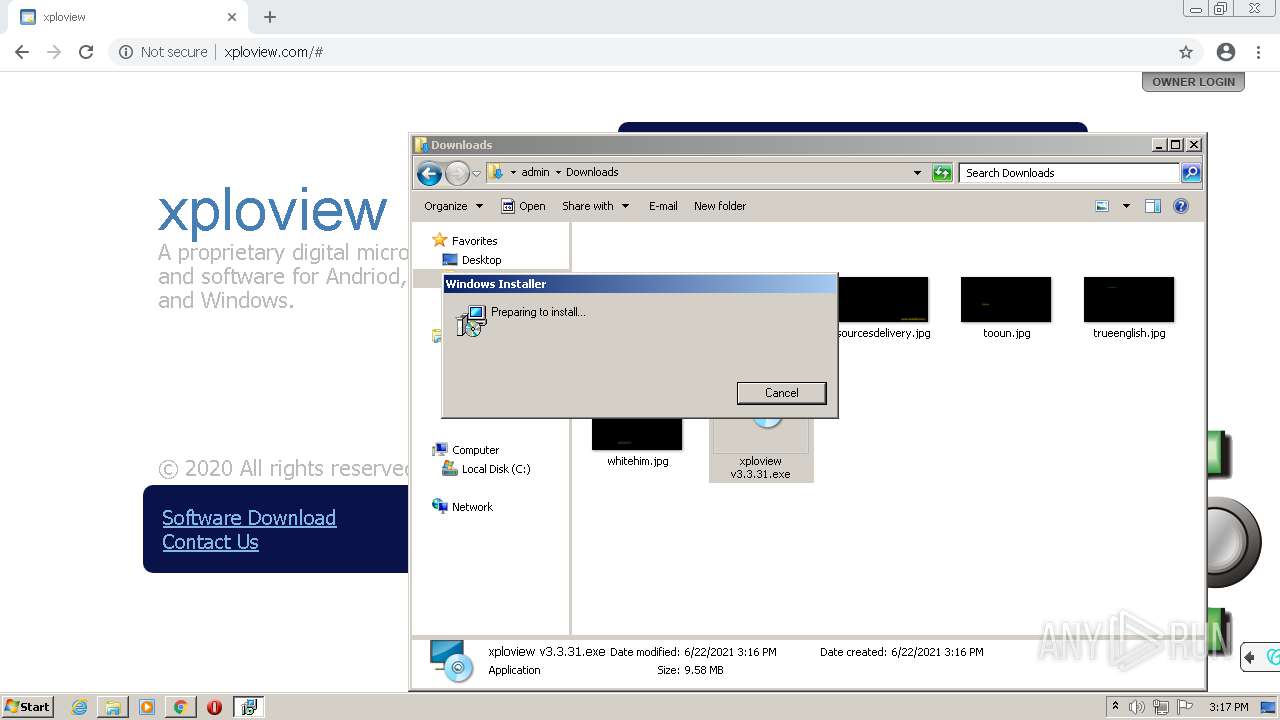
Application was dropped or rewritten from another process
- xploview v3.3.31.exe (PID: 3884)
Drops executable file immediately after starts
- msiexec.exe (PID: 2008)
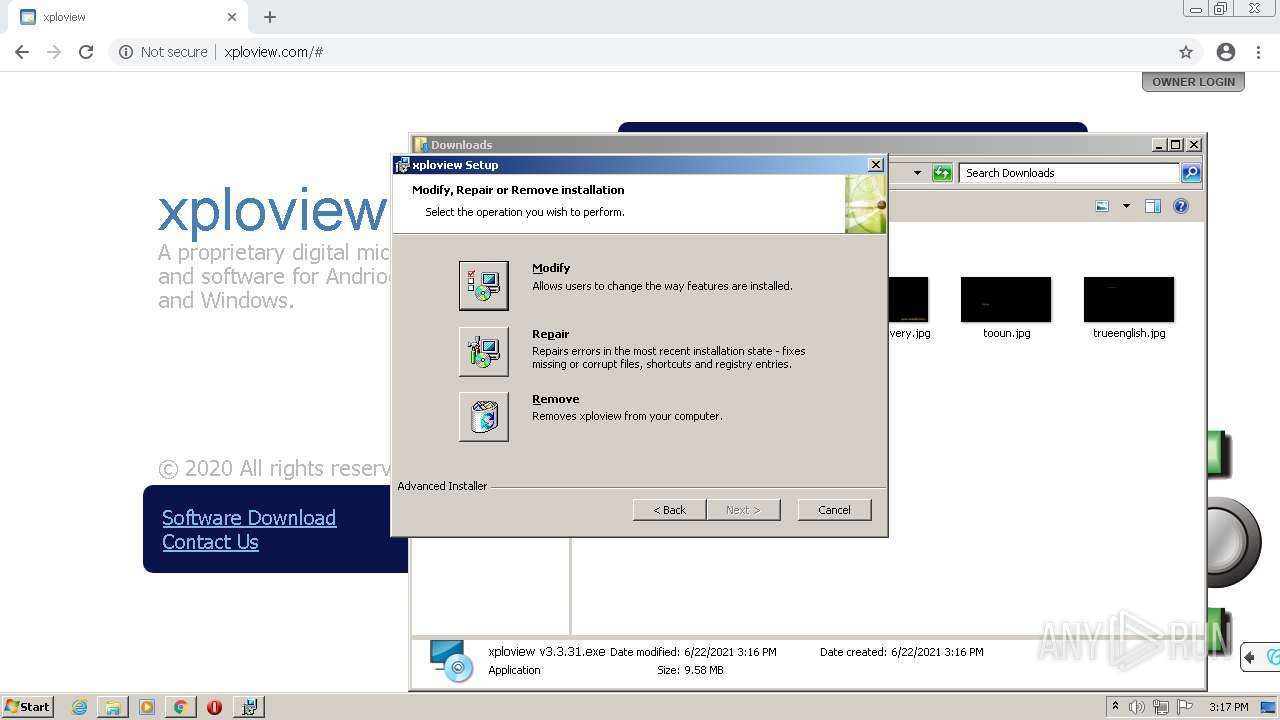
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2120)
- MsiExec.exe (PID: 2988)
Loads the Task Scheduler DLL interface
- xploview v3.3.31.exe (PID: 3884)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3776)
- xploview v3.3.31.exe (PID: 3884)
- msiexec.exe (PID: 2008)
Reads the computer name
- xploview v3.3.31.exe (PID: 3884)
Checks supported languages
- xploview v3.3.31.exe (PID: 3884)
Creates files in the user directory
- xploview v3.3.31.exe (PID: 3884)
Executed as Windows Service
- msiexec.exe (PID: 1832)
- vssvc.exe (PID: 2276)
Reads the Windows organization settings
- msiexec.exe (PID: 2008)
- msiexec.exe (PID: 1832)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2008)
- msiexec.exe (PID: 1832)
Application launched itself
- msiexec.exe (PID: 1832)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2008)
Reads Environment values
- vssvc.exe (PID: 2276)
Creates files in the Windows directory
- msiexec.exe (PID: 1832)
Creates files in the program directory
- msiexec.exe (PID: 1832)
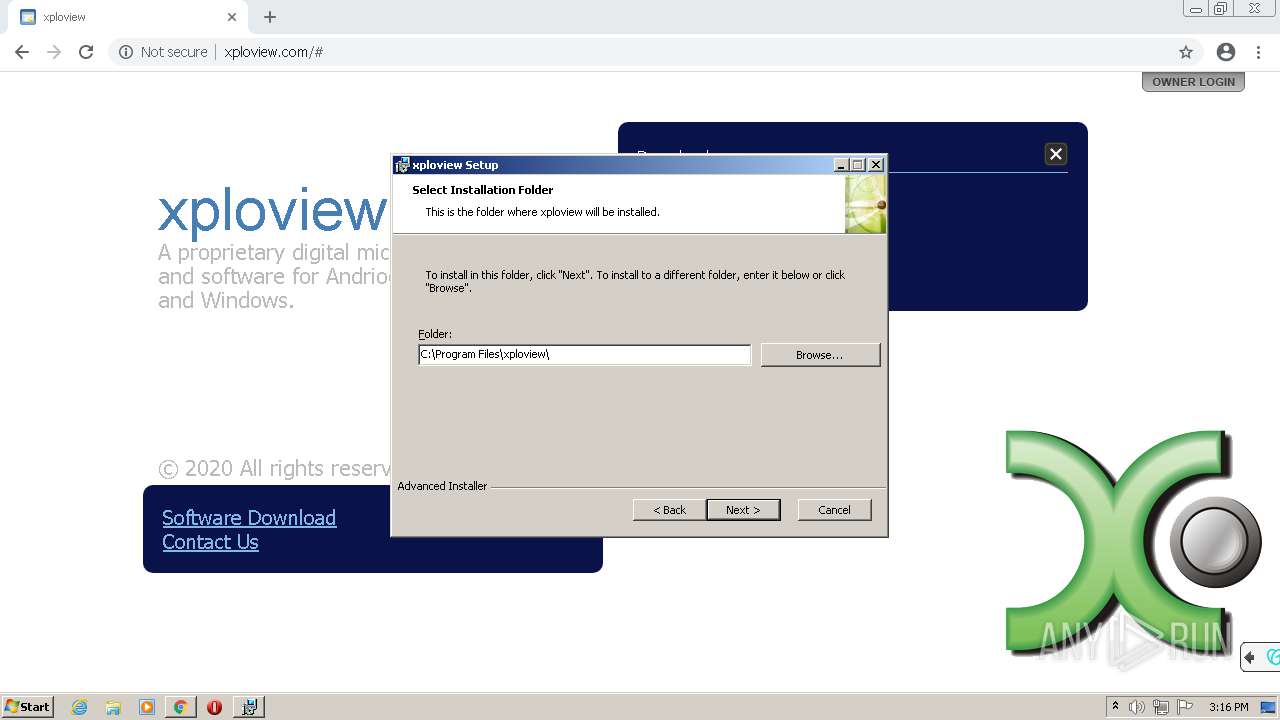
Creates a directory in Program Files
- msiexec.exe (PID: 1832)
Searches for installed software
- msiexec.exe (PID: 1832)
Creates a software uninstall entry
- msiexec.exe (PID: 1832)
INFO
Application launched itself
- chrome.exe (PID: 3776)
Checks supported languages
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 824)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3240)
- msiexec.exe (PID: 2008)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 604)
- msiexec.exe (PID: 1832)
- MsiExec.exe (PID: 2120)
- chrome.exe (PID: 3572)
- vssvc.exe (PID: 2276)
- MsiExec.exe (PID: 2988)
- chrome.exe (PID: 2000)
Reads the computer name
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 824)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2664)
- msiexec.exe (PID: 1832)
- msiexec.exe (PID: 2008)
- vssvc.exe (PID: 2276)
- MsiExec.exe (PID: 2120)
- chrome.exe (PID: 3572)
- MsiExec.exe (PID: 2988)
- chrome.exe (PID: 2000)
Reads the hosts file
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3776)
Reads settings of System Certificates
- chrome.exe (PID: 4076)
Checks Windows Trust Settings
- chrome.exe (PID: 3776)
Reads the date of Windows installation
- chrome.exe (PID: 3572)
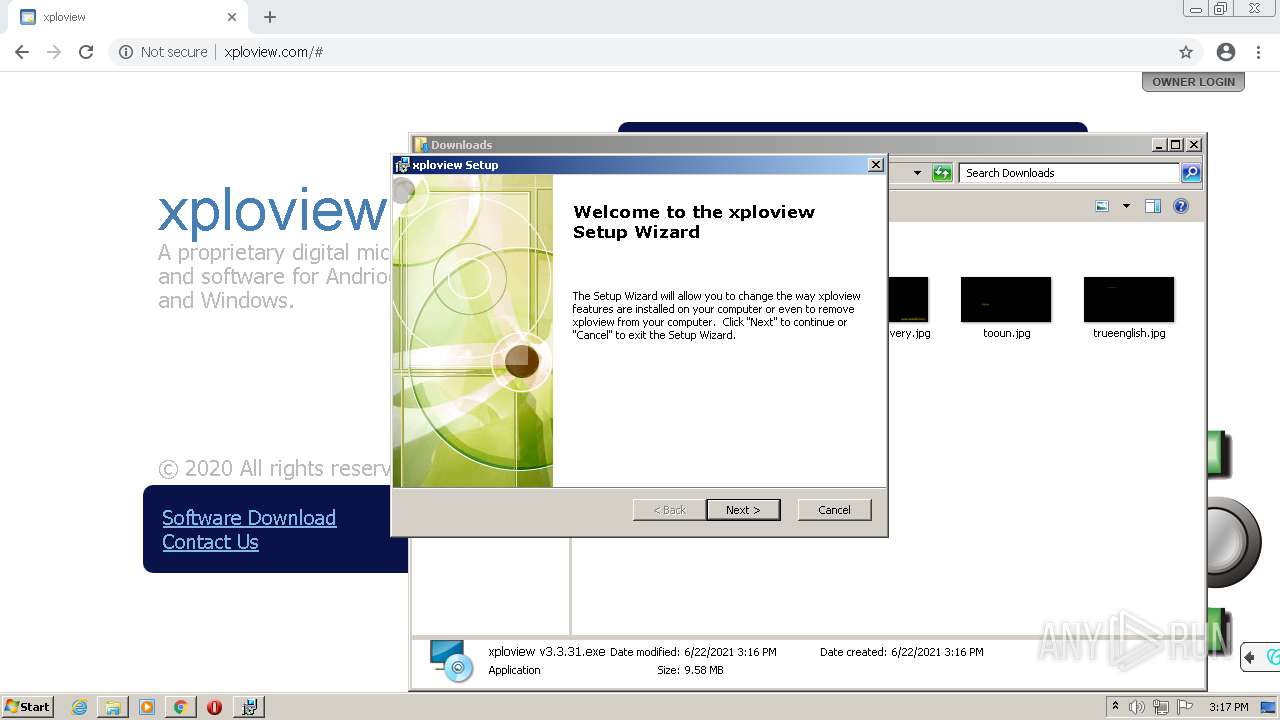
Manual execution by user
- explorer.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1052,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1052,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=1756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2672 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1052,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1652 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2008 | /i "C:\Users\admin\AppData\Roaming\xploview\xploview 3.3.31\install\xploview.msi" AI_SETUPEXEPATH="C:\Users\admin\Downloads\xploview v3.3.31.exe" SETUPEXEDIR="C:\Users\admin\Downloads\" EXE_CMD_LINE="/exenoupdates /exelang 0 /noprereqs " | C:\Windows\system32\msiexec.exe | xploview v3.3.31.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | C:\Windows\system32\MsiExec.exe -Embedding 155849DE179929D9B605F896544EA7F3 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 679
Read events
11 293
Write events
374
Delete events
12
Modification events
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
7
Suspicious files
15
Text files
65
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60D1F0A4-EC0.pma | — | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7fd068f0-6ed1-4ed2-865c-d079fd960d08.tmp | text | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF199a33.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
31
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/tcc/tcc_l.combined.1.0.5.min.js | unknown | text | 2.11 Kb | whitelisted |
4076 | chrome.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | US | der | 1.70 Kb | whitelisted |
4076 | chrome.exe | GET | 200 | 97.74.42.79:80 | http://www.xploview.com/ | US | html | 6.39 Kb | malicious |
4076 | chrome.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 1.74 Kb | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/ip/v1.2.18/scripts/ss-merged-1.0.0.0.js | unknown | html | 14.0 Kb | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/ip/v1.2.18/images/common/btn_contact_x.png | unknown | image | 606 b | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/ip/v1.2.18/style/ss-1.0.0.0.css | unknown | text | 4.90 Kb | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/ip/v1.2.18/images/common/flyout_arrow.png | unknown | image | 422 b | whitelisted |
4076 | chrome.exe | GET | 200 | 2.16.186.248:80 | http://img1.wsimg.com/ip/v1.2.18/images/common/transparent.png | unknown | image | 1.67 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4076 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
4076 | chrome.exe | 97.74.42.79:80 | www.xploview.com | GoDaddy.com, LLC | US | malicious |
4076 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
4076 | chrome.exe | 2.16.186.248:80 | img1.wsimg.com | Akamai International B.V. | — | whitelisted |
4076 | chrome.exe | 192.169.208.12:443 | widget.starfieldtech.com | GoDaddy.com, LLC | US | unknown |
4076 | chrome.exe | 2.16.186.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
4076 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4076 | chrome.exe | 192.124.249.24:80 | ocsp.starfieldtech.com | Sucuri | US | suspicious |
— | — | 104.126.36.177:443 | img4.wsimg.com | GTT Communications Inc. | US | suspicious |
4076 | chrome.exe | 104.126.36.177:443 | img4.wsimg.com | GTT Communications Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.xploview.com |
| malicious |
img1.wsimg.com |
| whitelisted |
widget.starfieldtech.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |
img4.wsimg.com |
| suspicious |
img3.wsimg.com |
| suspicious |