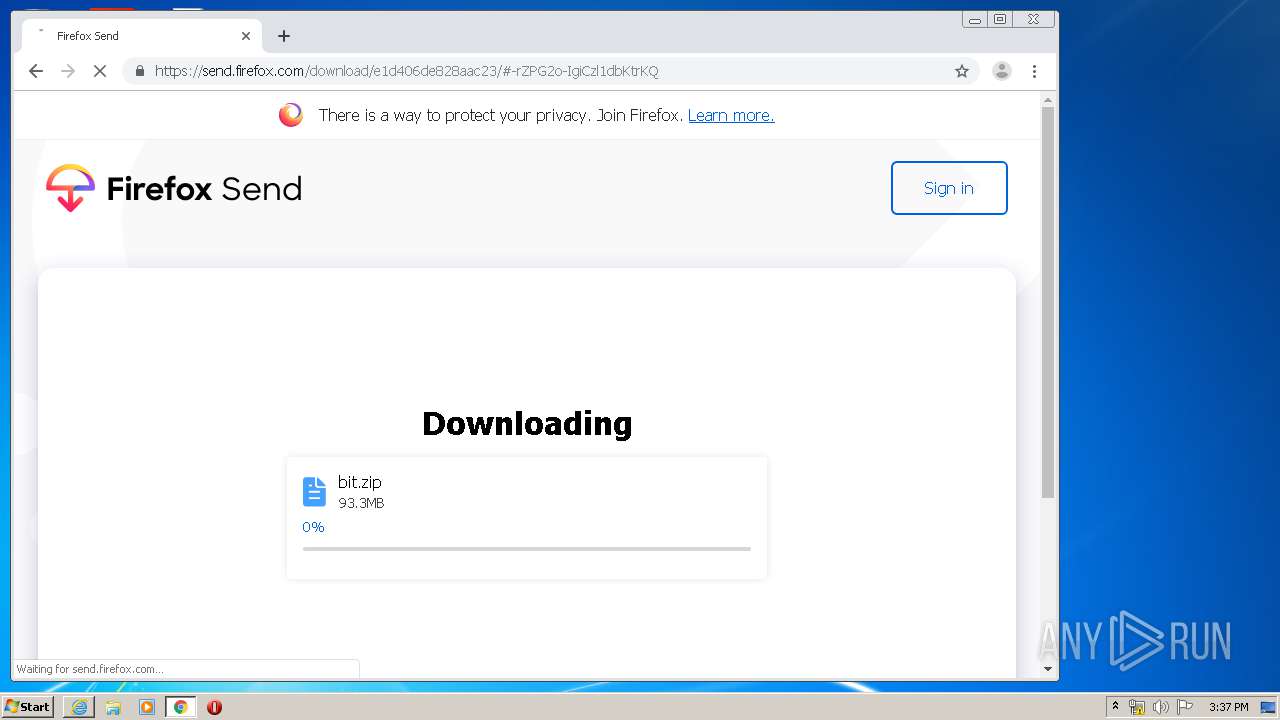
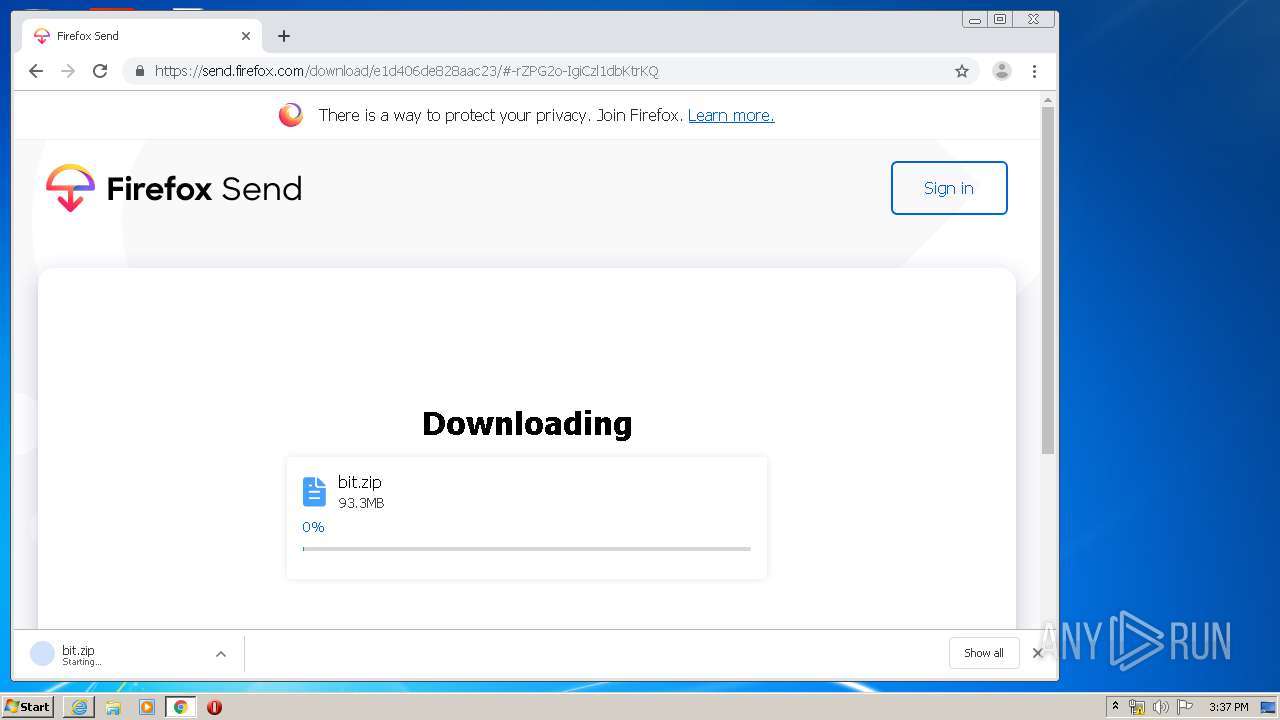
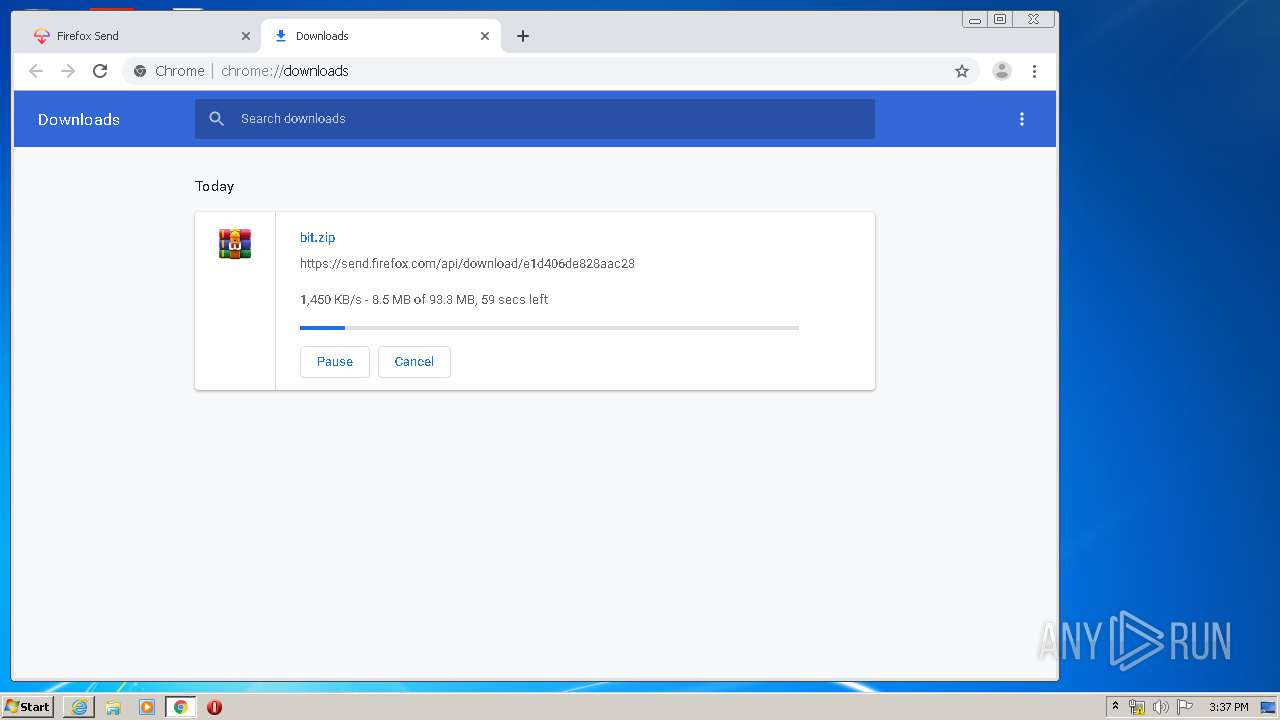
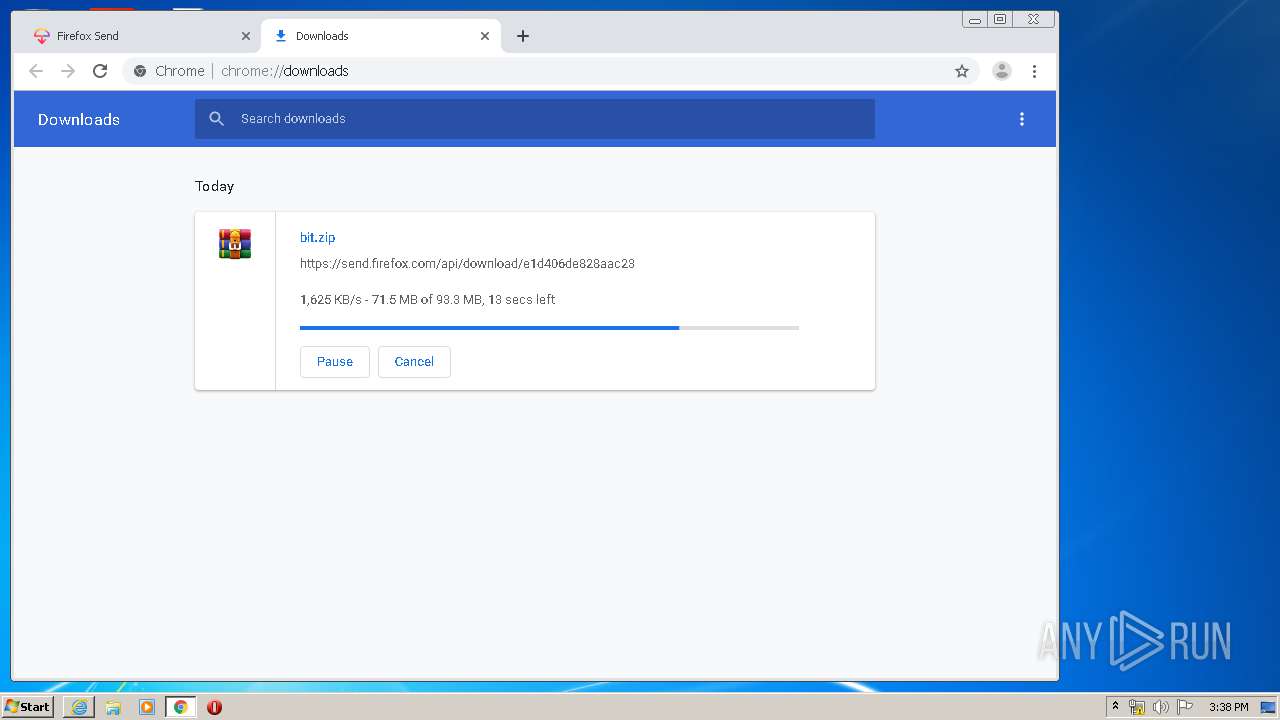
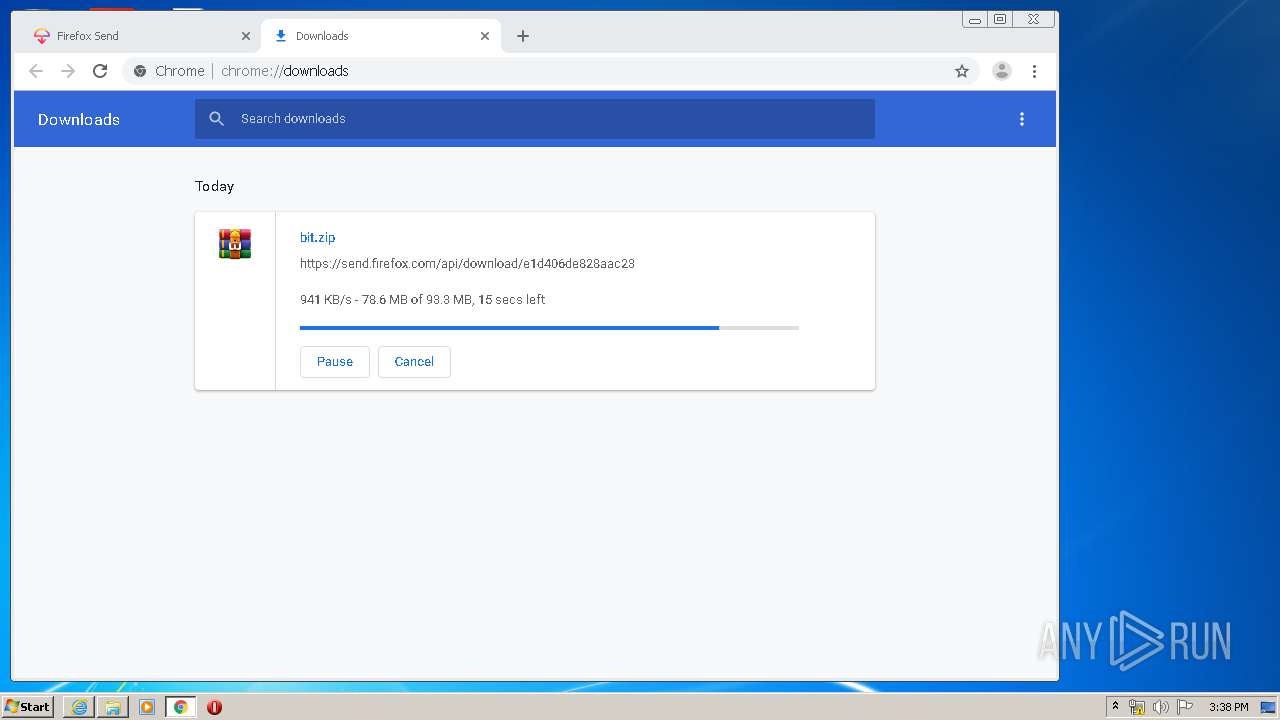
| download: | e1d406de828aac23 |
| Full analysis: | https://app.any.run/tasks/580f3502-5ed9-440b-8e7c-f47090699bef |
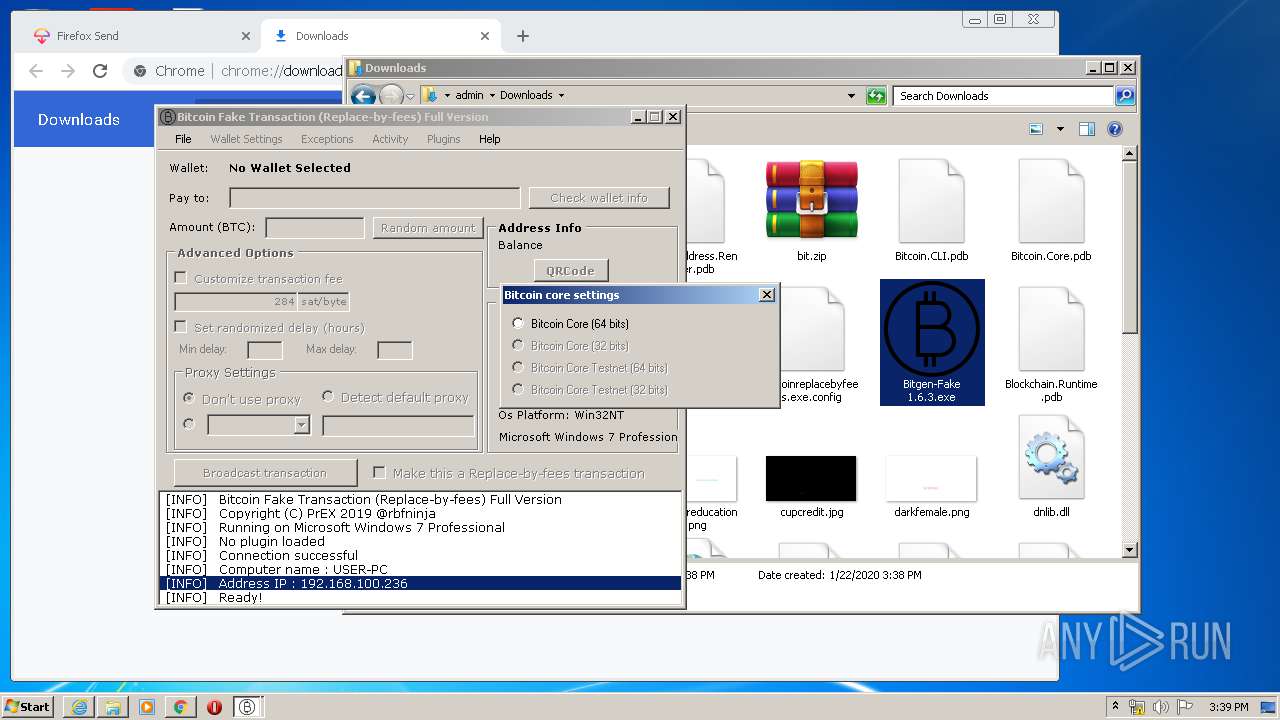
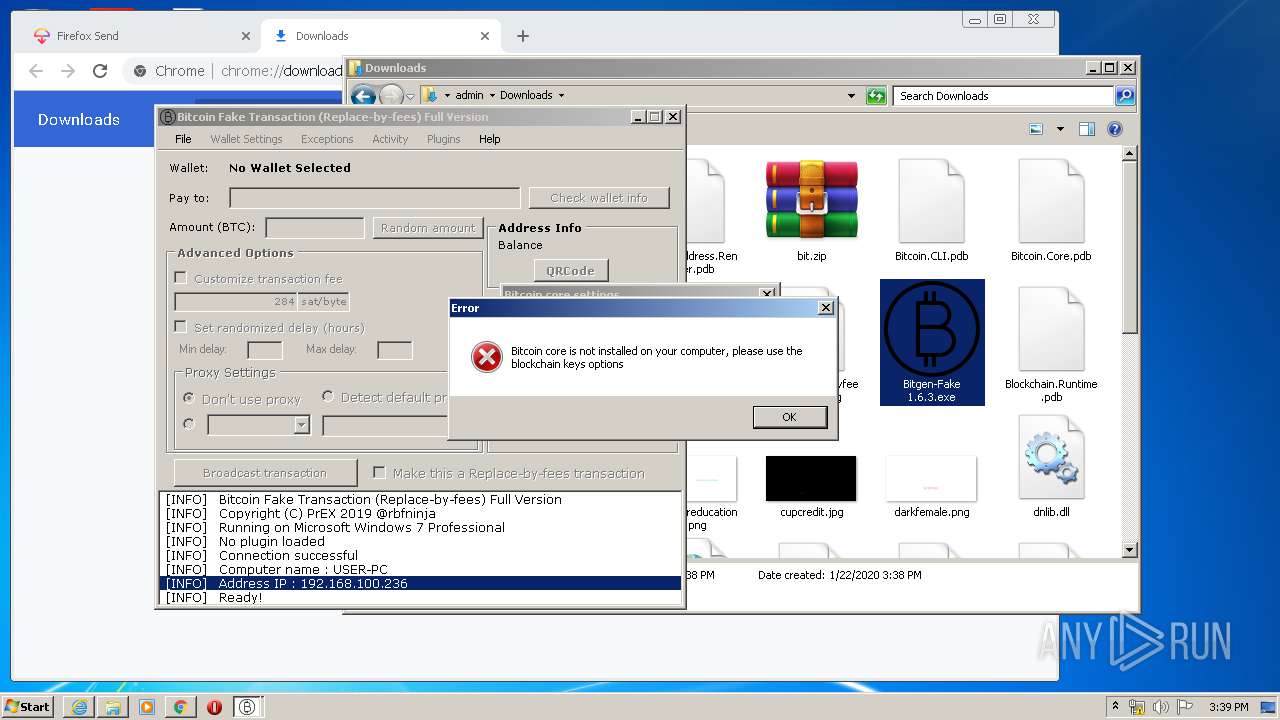
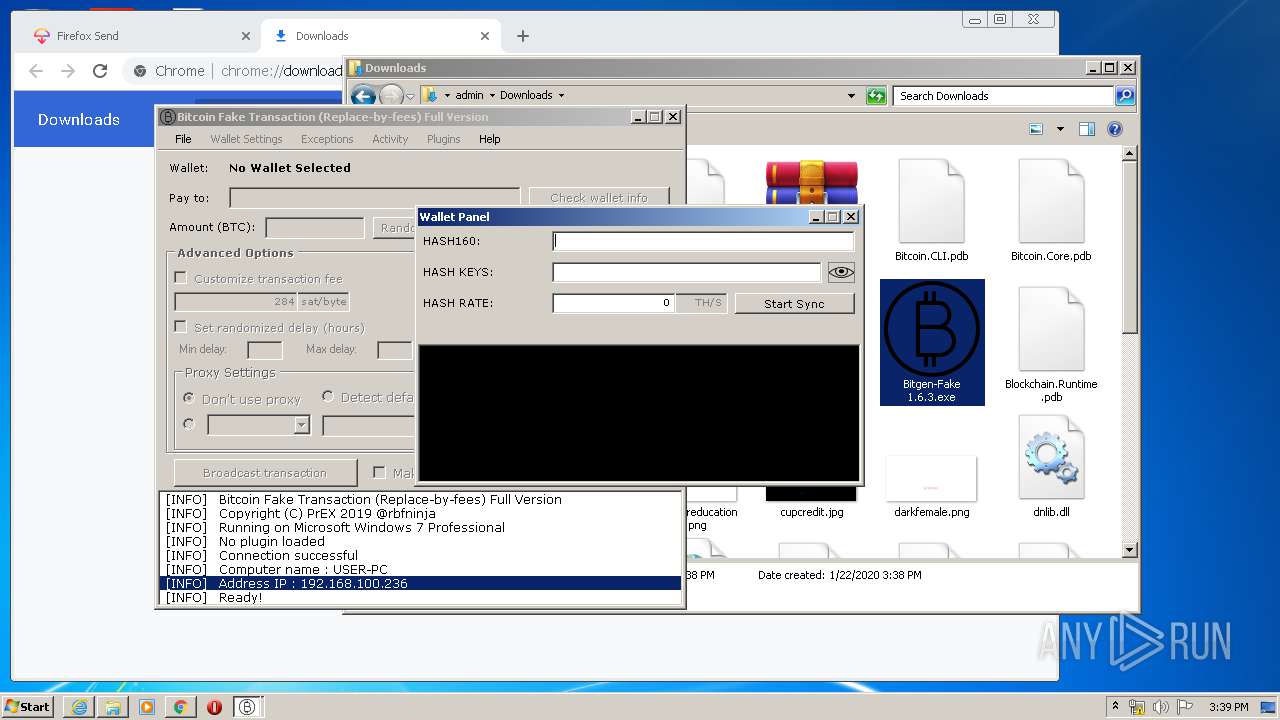
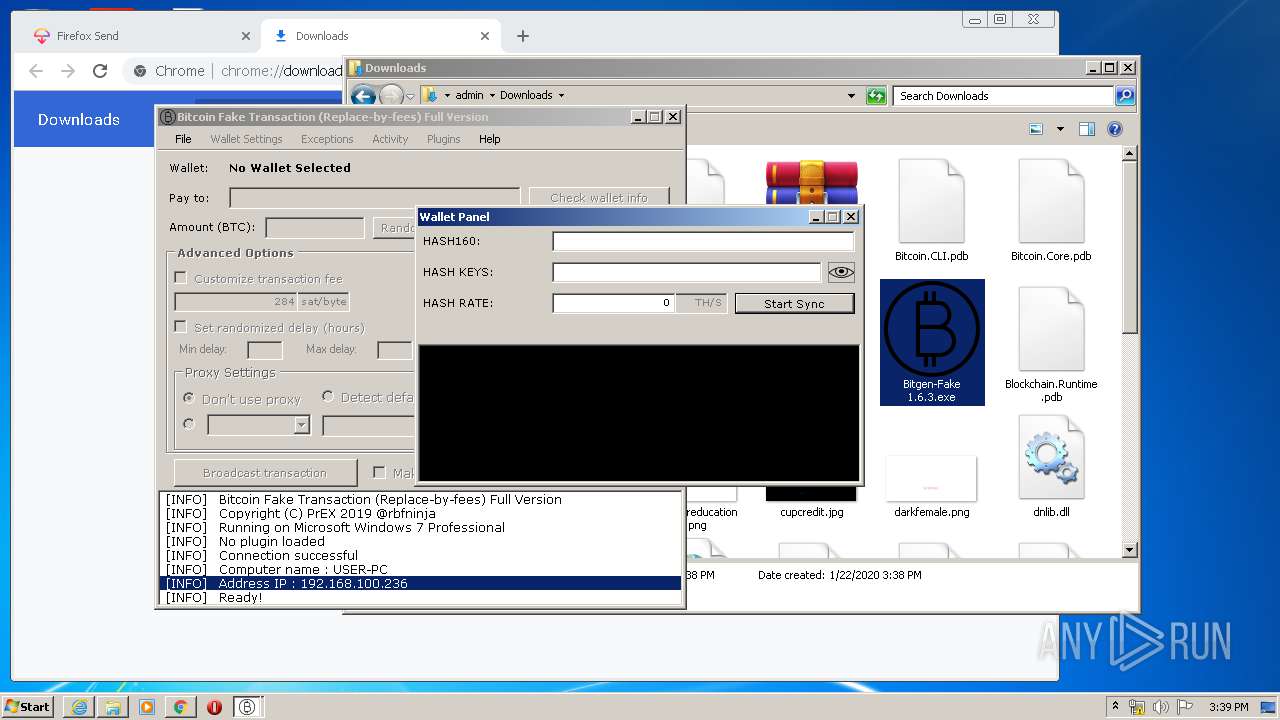
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2020, 15:36:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 4094EB44E25C93F49EB1CC60ED9A8036 |
| SHA1: | 23D4C004D2CE2CF4BEEB7E42B9F424CC4648E2E0 |
| SHA256: | 154EF45BAAF1D935CBC7F372A3DEC102AF507AA1B2733414E3A71378932AC259 |
| SSDEEP: | 96:3SnxRF+JXPv0rKkvFshi4o6Fw/6J7IhY7y8DHb4wI0SHQG:3G+v0r7vFH+fIa7bDHb4whSHQG |
MALICIOUS
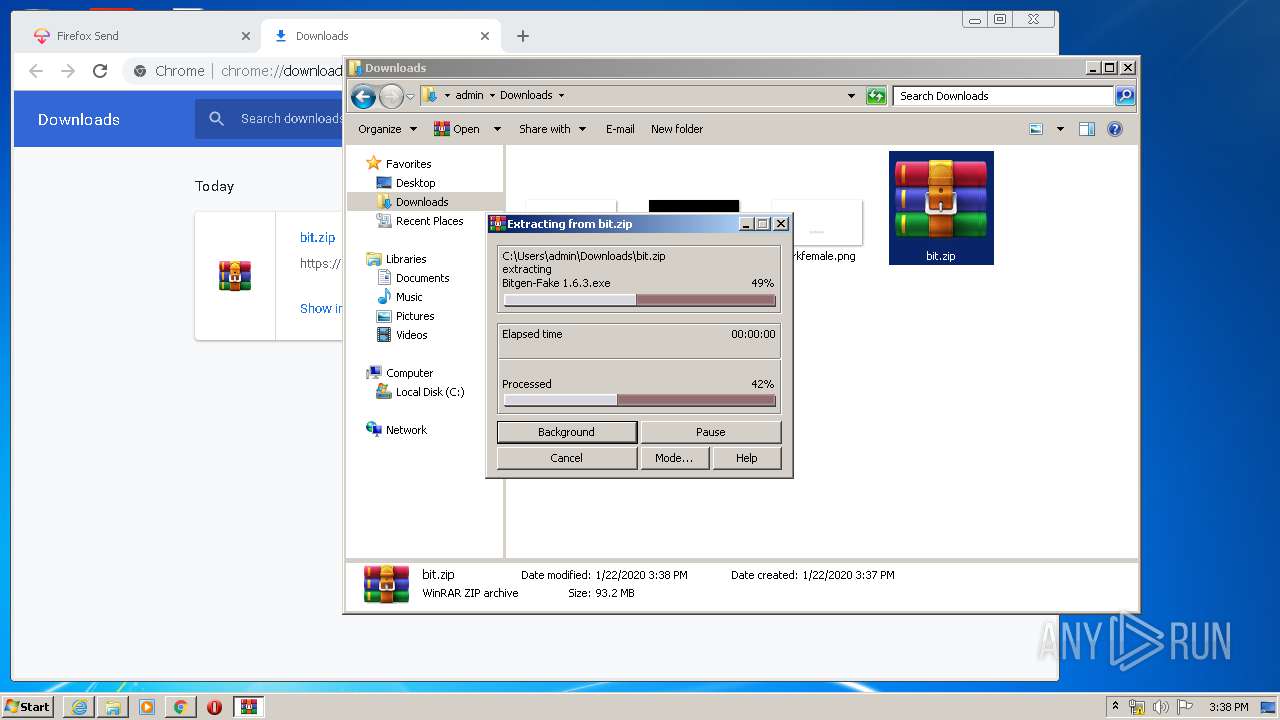
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 628)
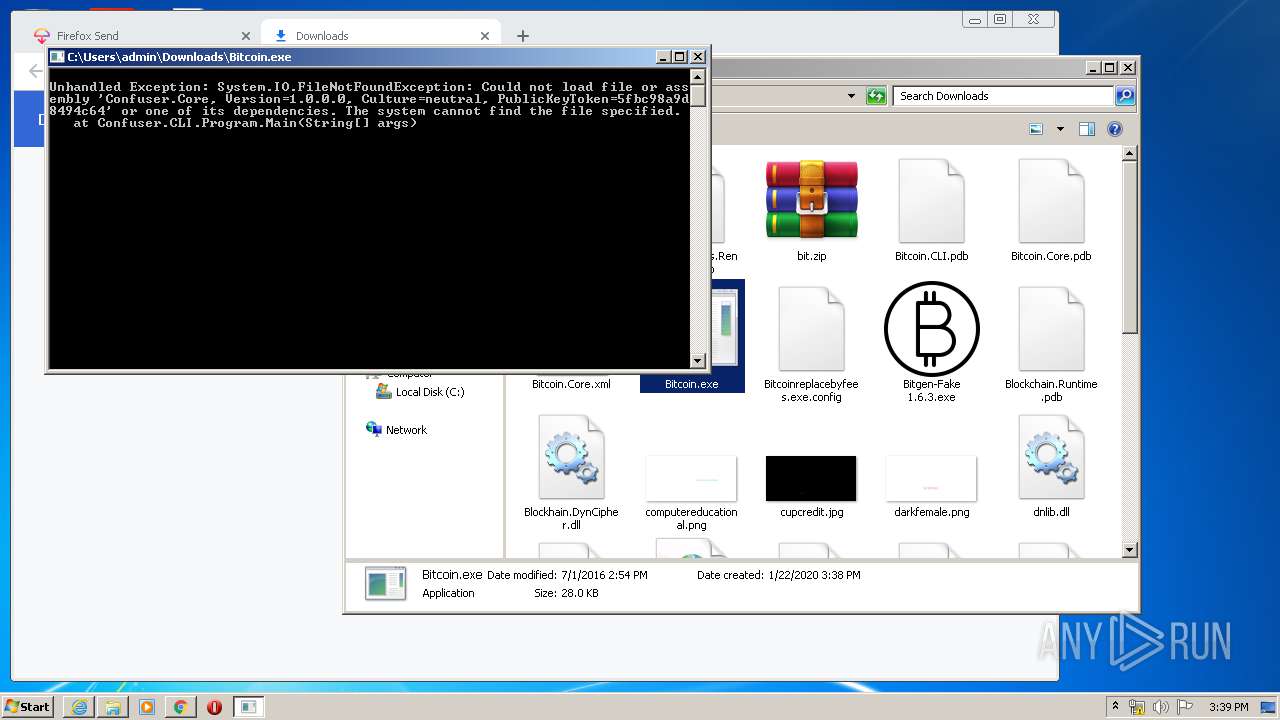
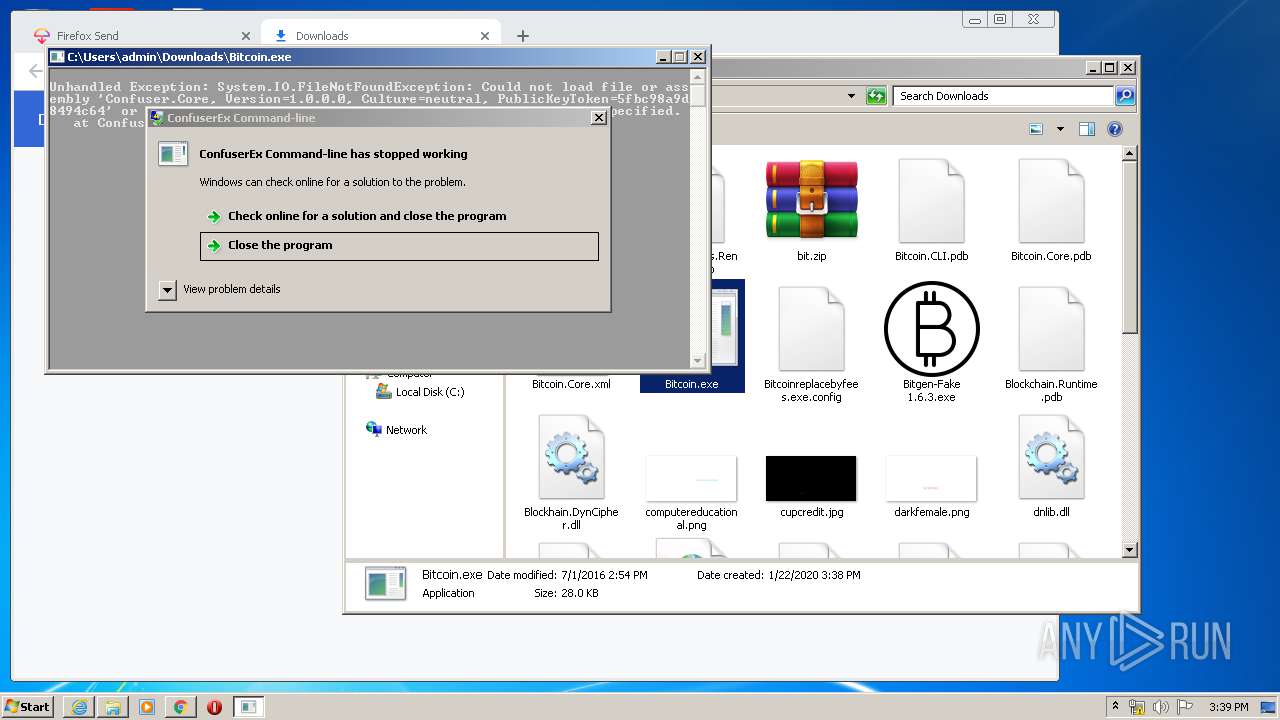
Application was dropped or rewritten from another process
- Bitcoin.exe (PID: 3940)
SUSPICIOUS
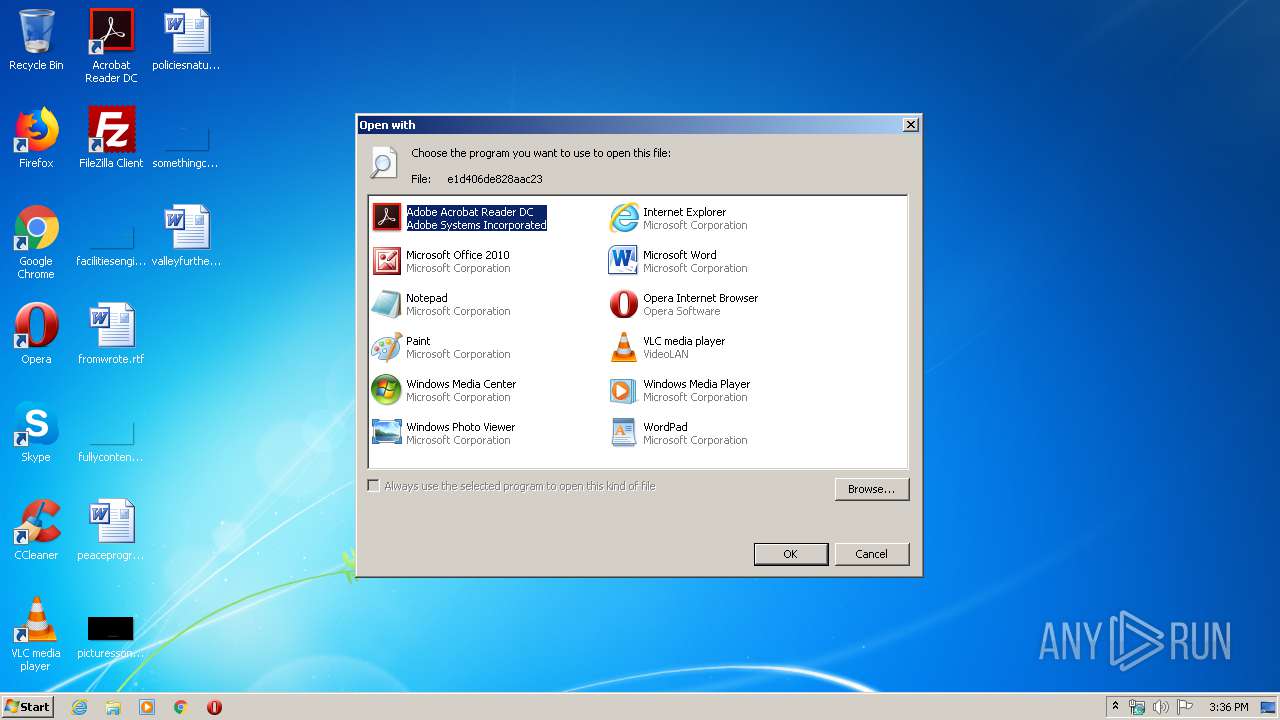
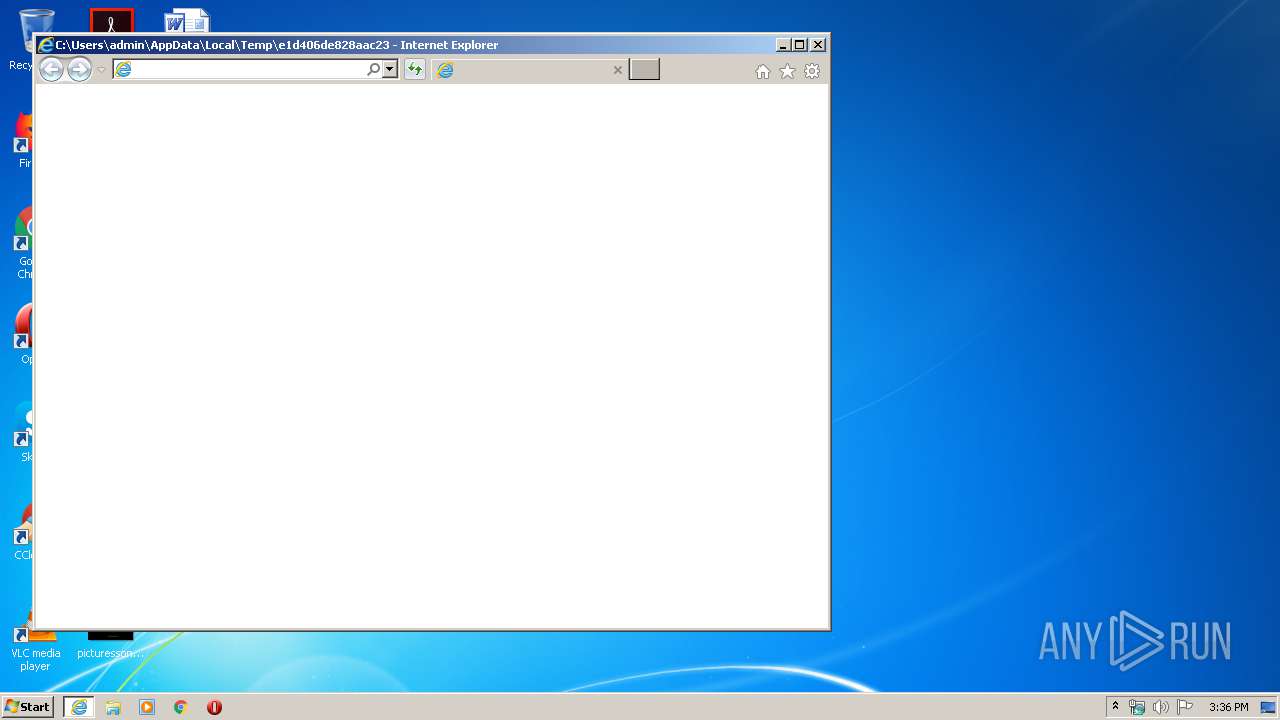
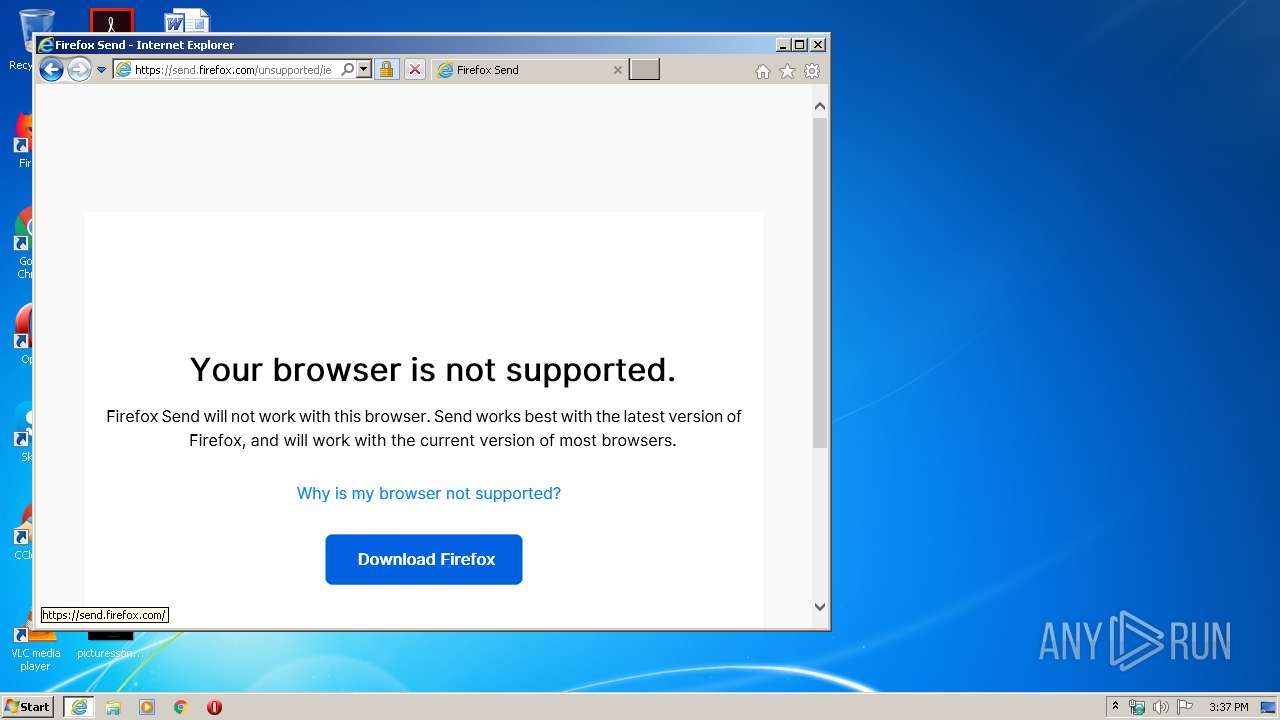
Starts Internet Explorer
- rundll32.exe (PID: 988)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2092)
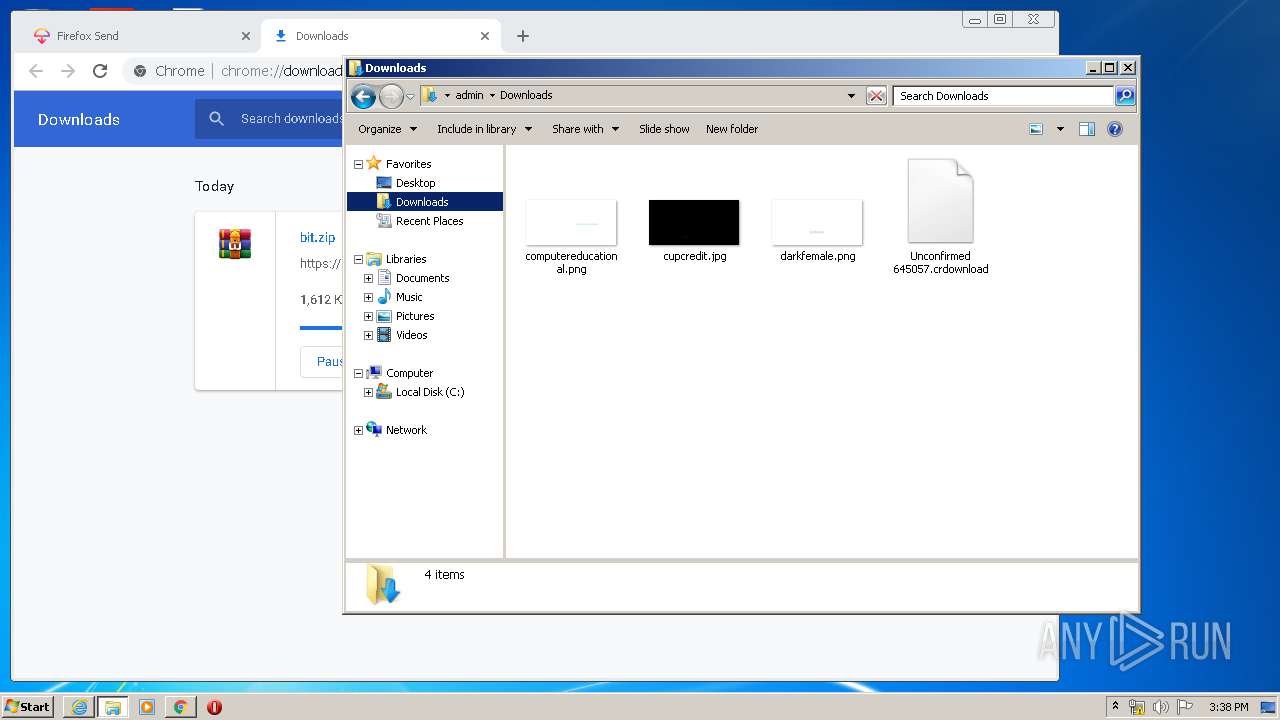
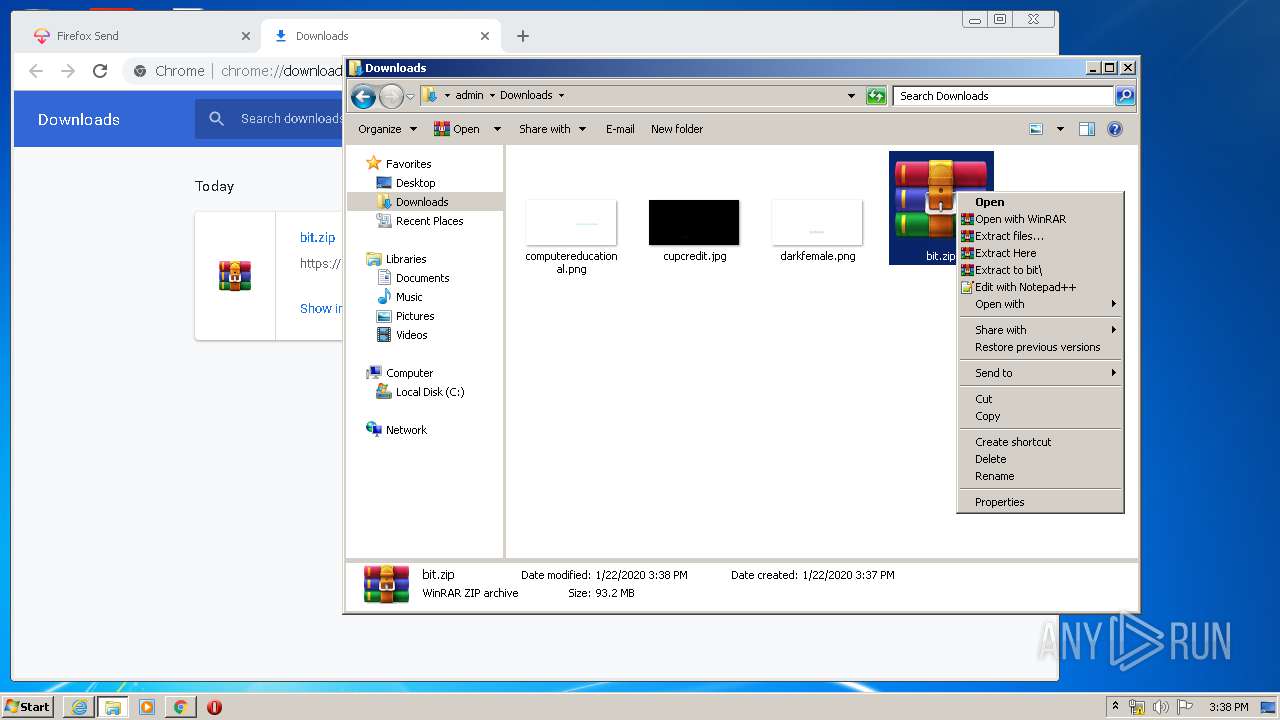
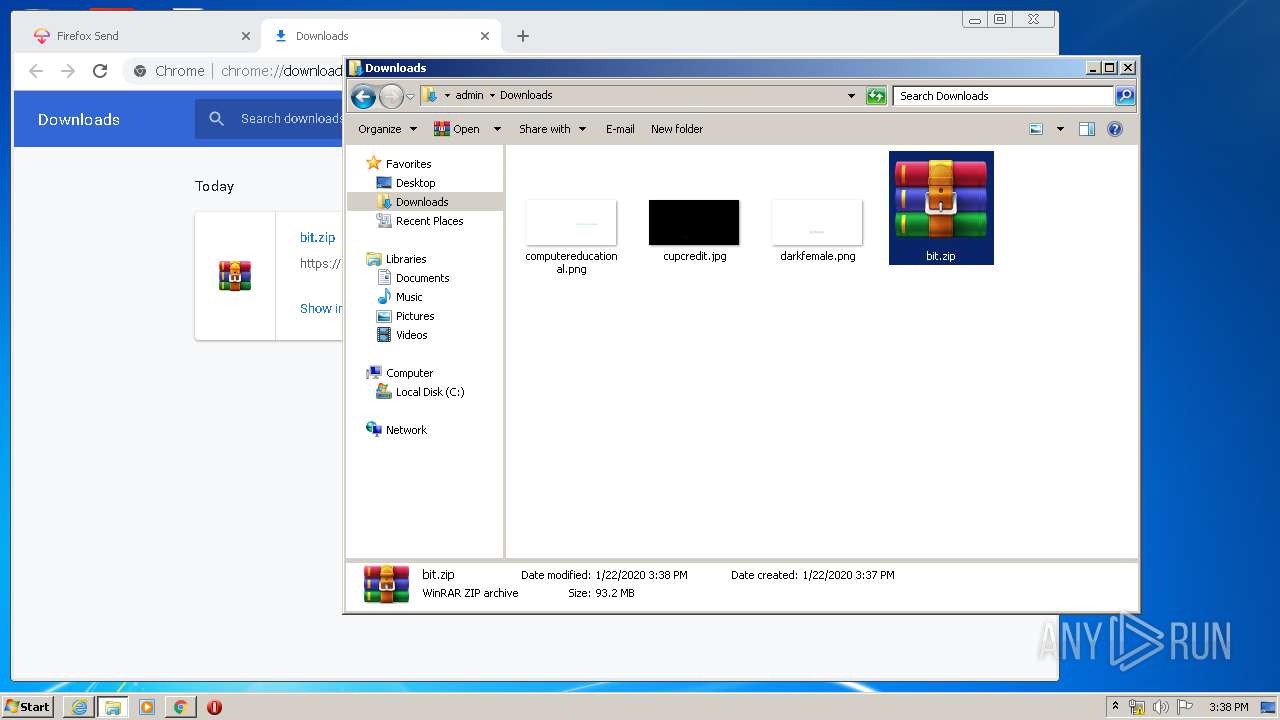
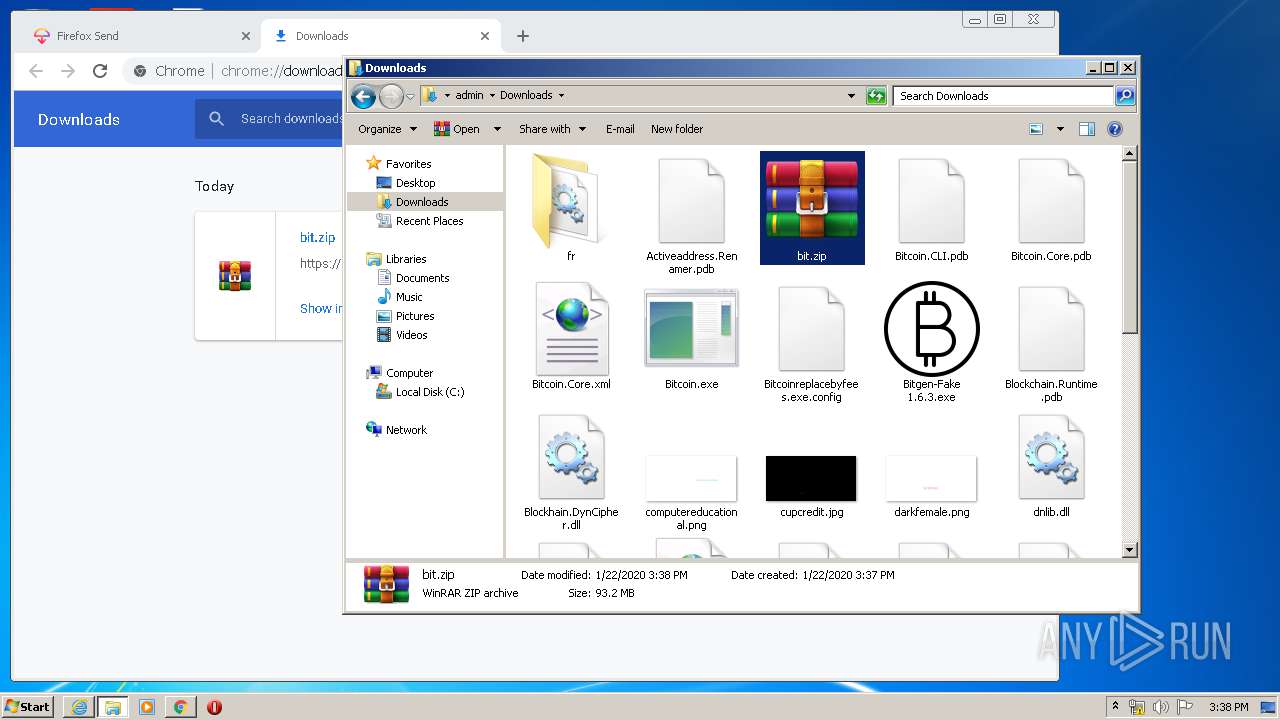
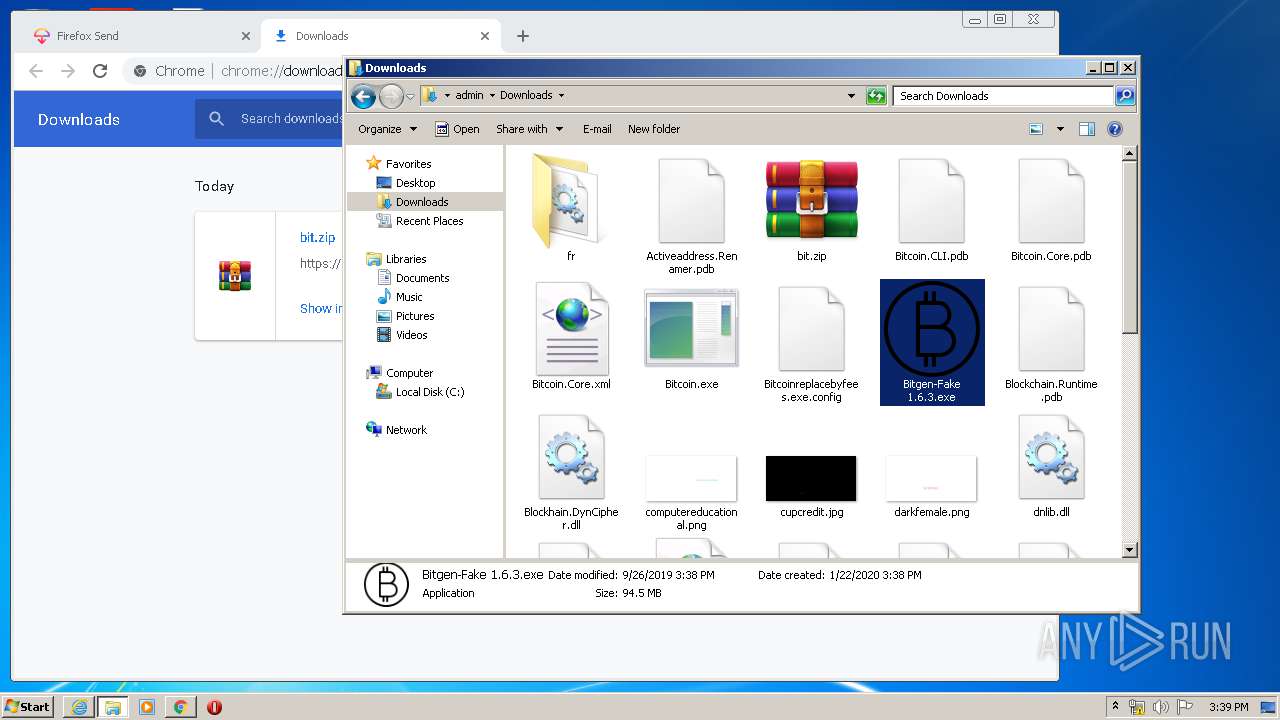
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1708)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 2076)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 3796)
Reads Internet Cache Settings
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2076)
- chrome.exe (PID: 2092)
Application launched itself
- iexplore.exe (PID: 2744)
- chrome.exe (PID: 2092)
- iexplore.exe (PID: 3796)
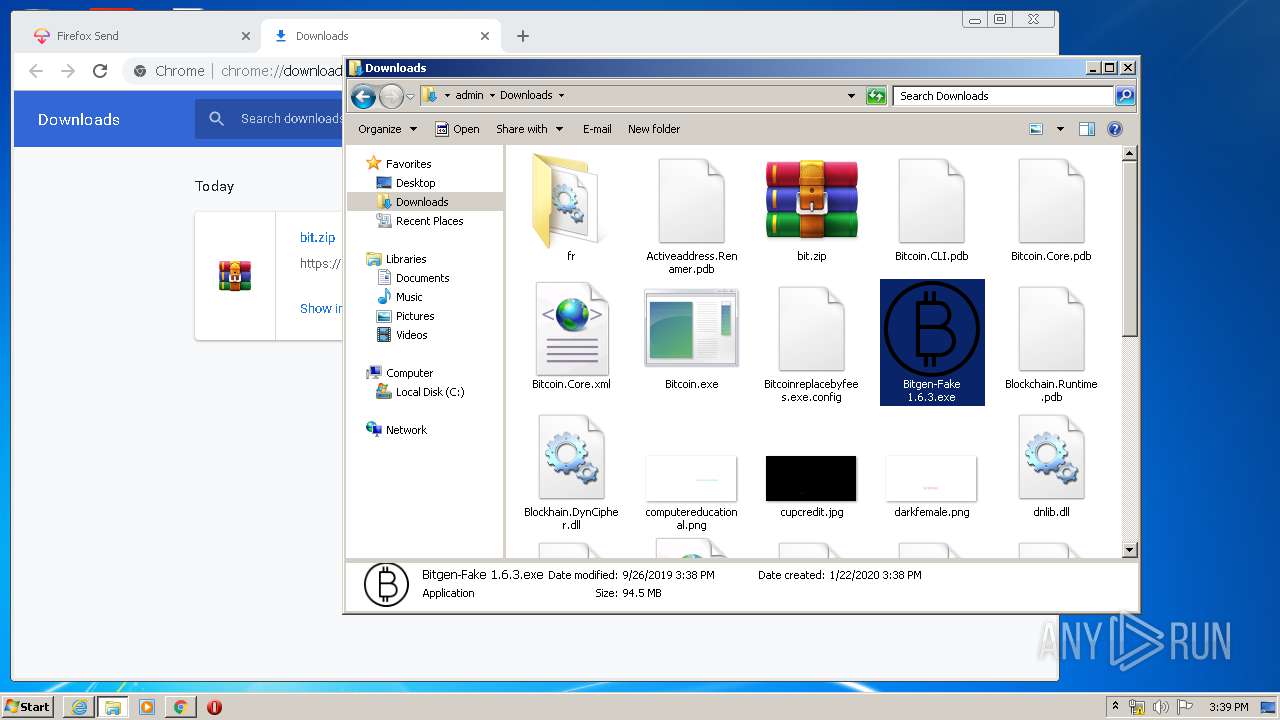
Manual execution by user
- chrome.exe (PID: 2092)
- WinRAR.exe (PID: 1708)
- Bitcoin.exe (PID: 3940)
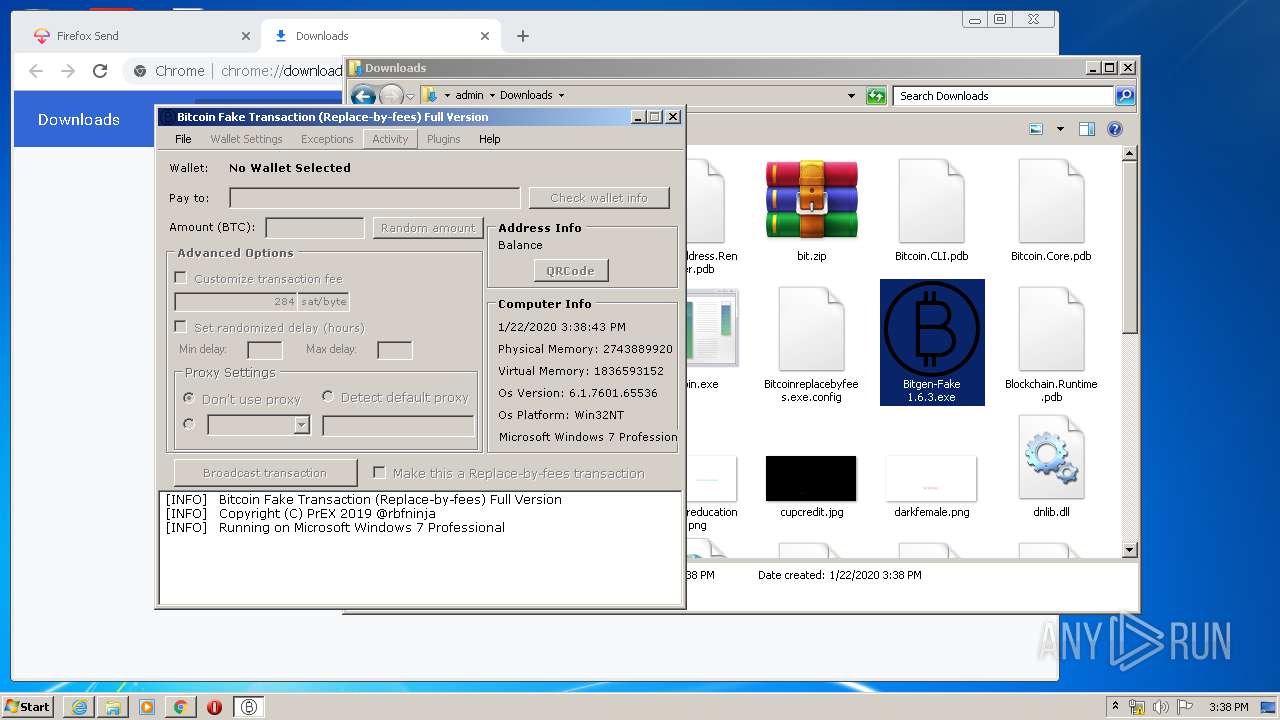
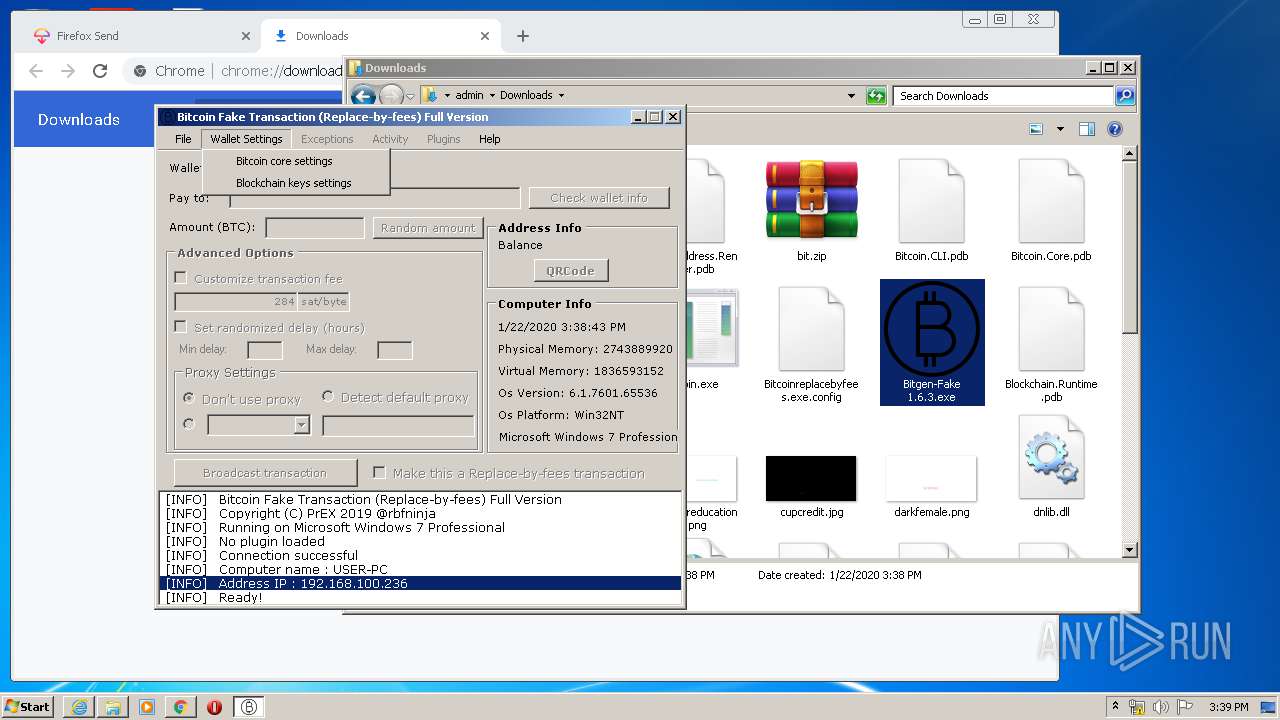
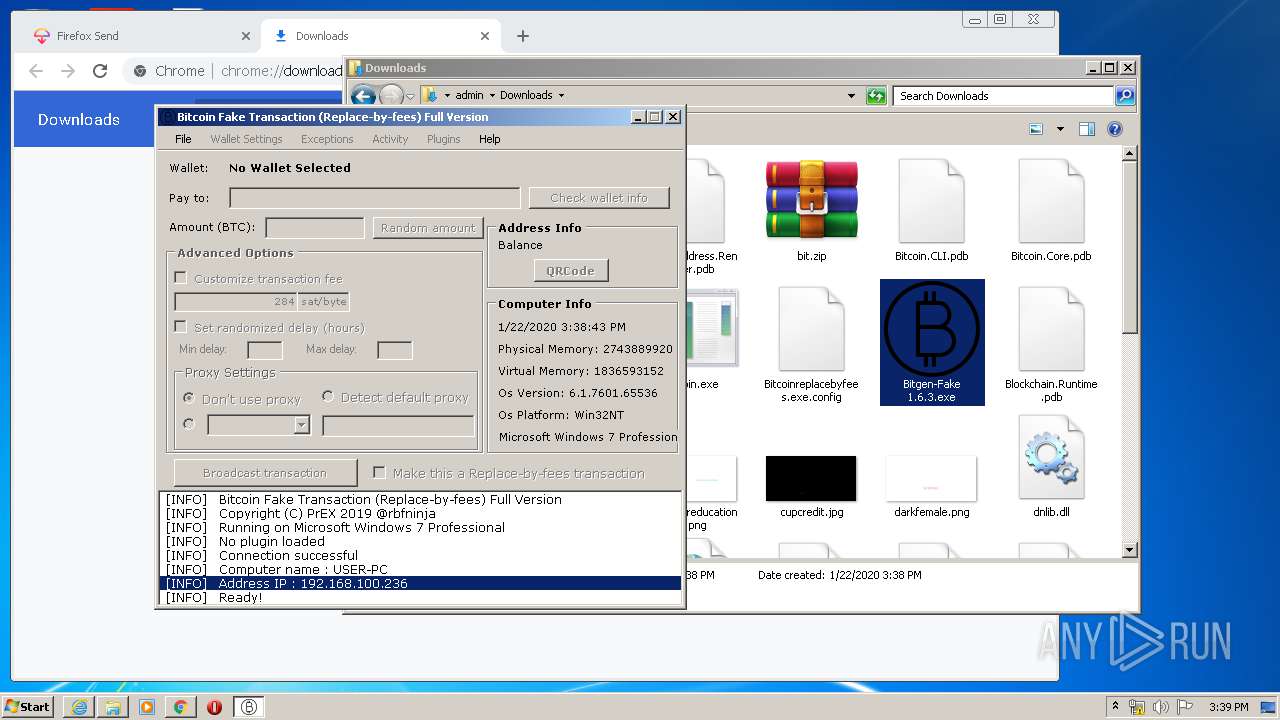
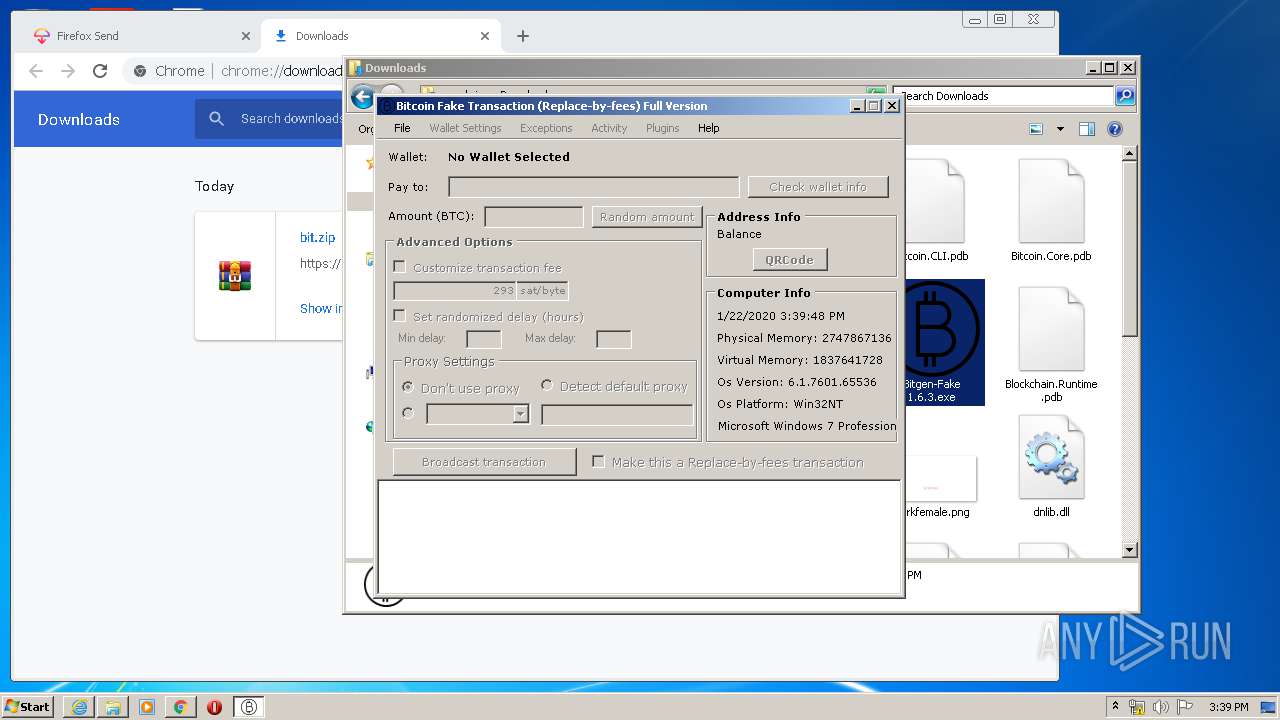
- Bitgen-Fake 1.6.3.exe (PID: 3784)
- Bitgen-Fake 1.6.3.exe (PID: 2400)
- explorer.exe (PID: 820)
Creates files in the user directory
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2744)
Reads settings of System Certificates
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 2076)
Reads the hosts file
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2904)
Changes settings of System certificates
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 2744)
Changes internet zones settings
- iexplore.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
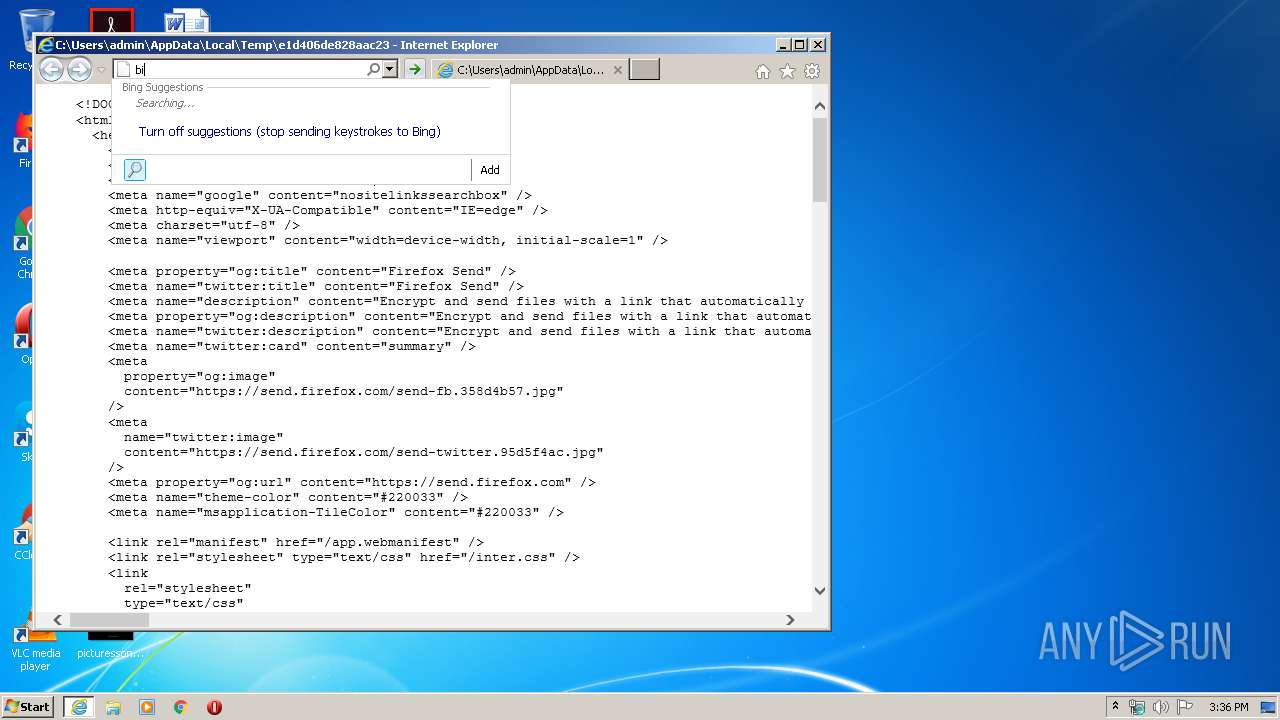
HTML
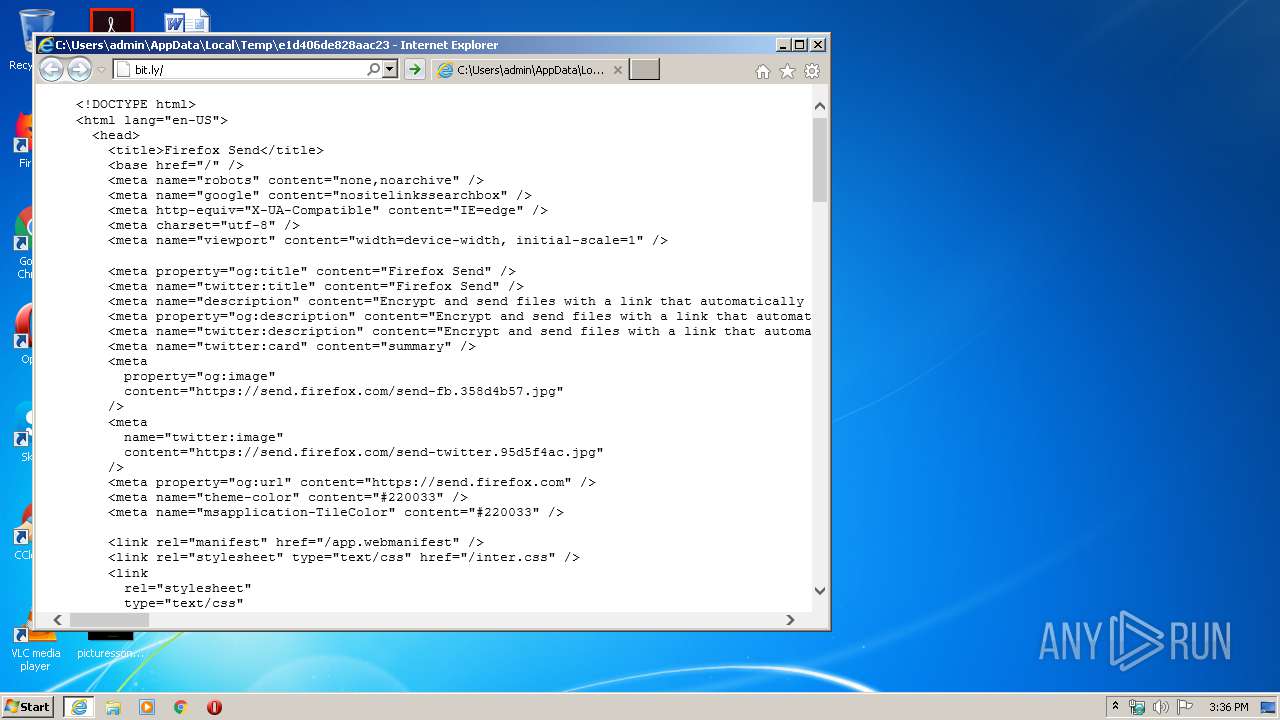
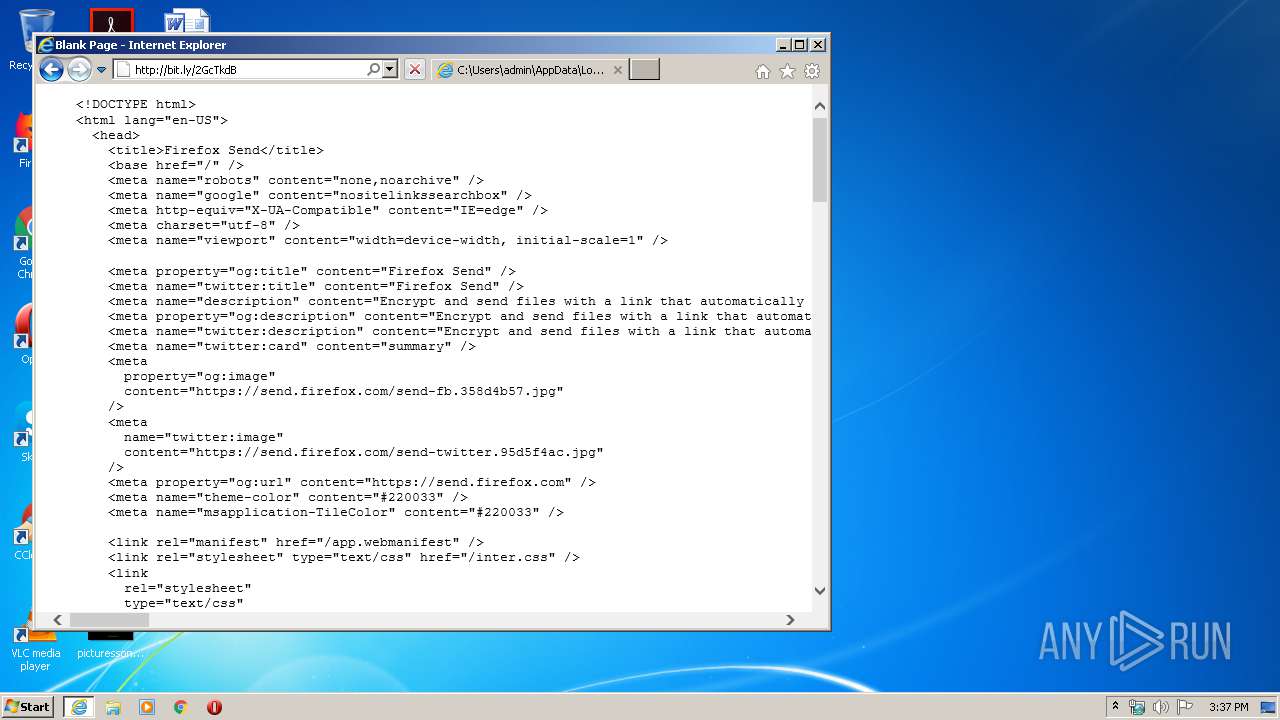
| Title: | Firefox Send |
|---|---|
| Robots: | none,noarchive |
| google: | nositelinkssearchbox |
| HTTPEquivXUACompatible: | IE=edge |
| viewport: | width=device-width, initial-scale=1 |
| twitterTitle: | Firefox Send |
| Description: | Encrypt and send files with a link that automatically expires to ensure your important documents don’t stay online forever. |
| twitterDescription: | Encrypt and send files with a link that automatically expires to ensure your important documents don’t stay online forever. |
| twitterCard: | summary |
| twitterImage: | https://send.firefox.com/send-twitter.95d5f4ac.jpg |
| themeColor: | #220033 |
| msapplicationTileColor: | #220033 |
Total processes
90
Monitored processes
45
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5295834917666951669 --mojo-platform-channel-handle=2104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12884573395053760937 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\e1d406de828aac23 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9208026941499130723 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10813746554554175847 --mojo-platform-channel-handle=3760 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1761945098807795882 --mojo-platform-channel-handle=4476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1288358778574154682 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2464690762056860202,1380349693170475209,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12203410078013748226 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 533
Read events
2 211
Write events
314
Delete events
8
Modification events
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
16
Suspicious files
99
Text files
303
Unknown types
47
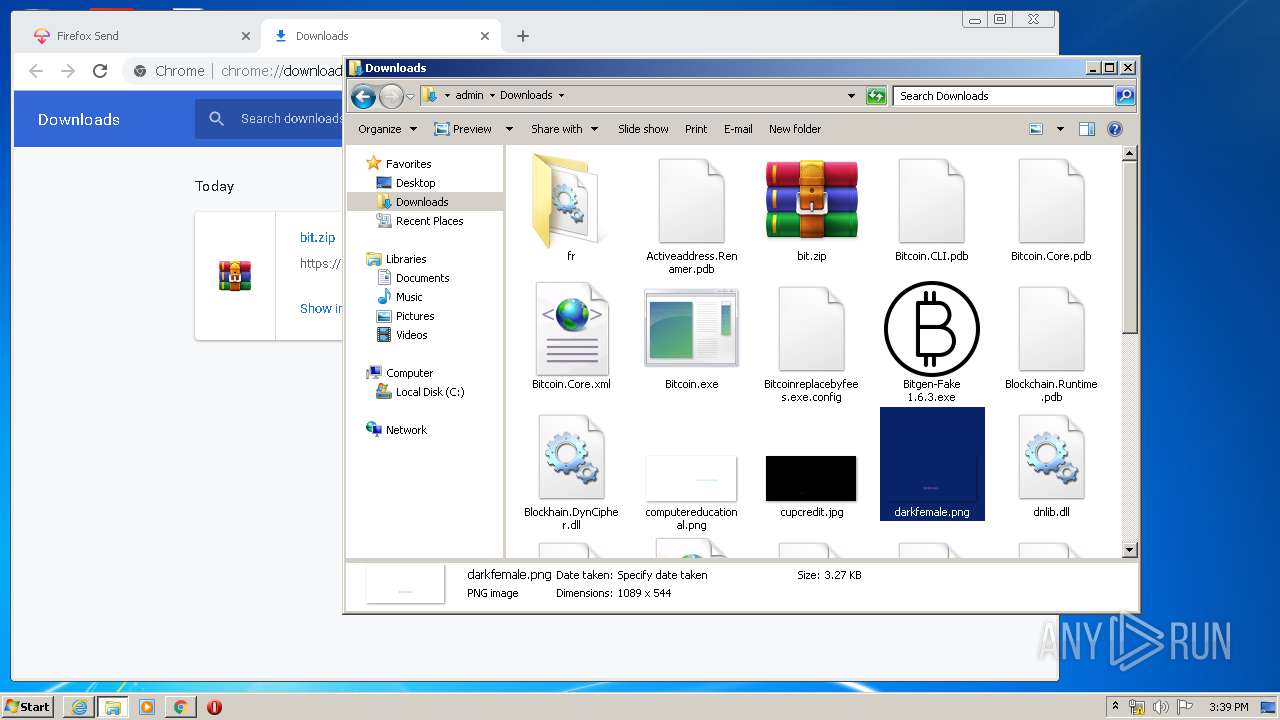
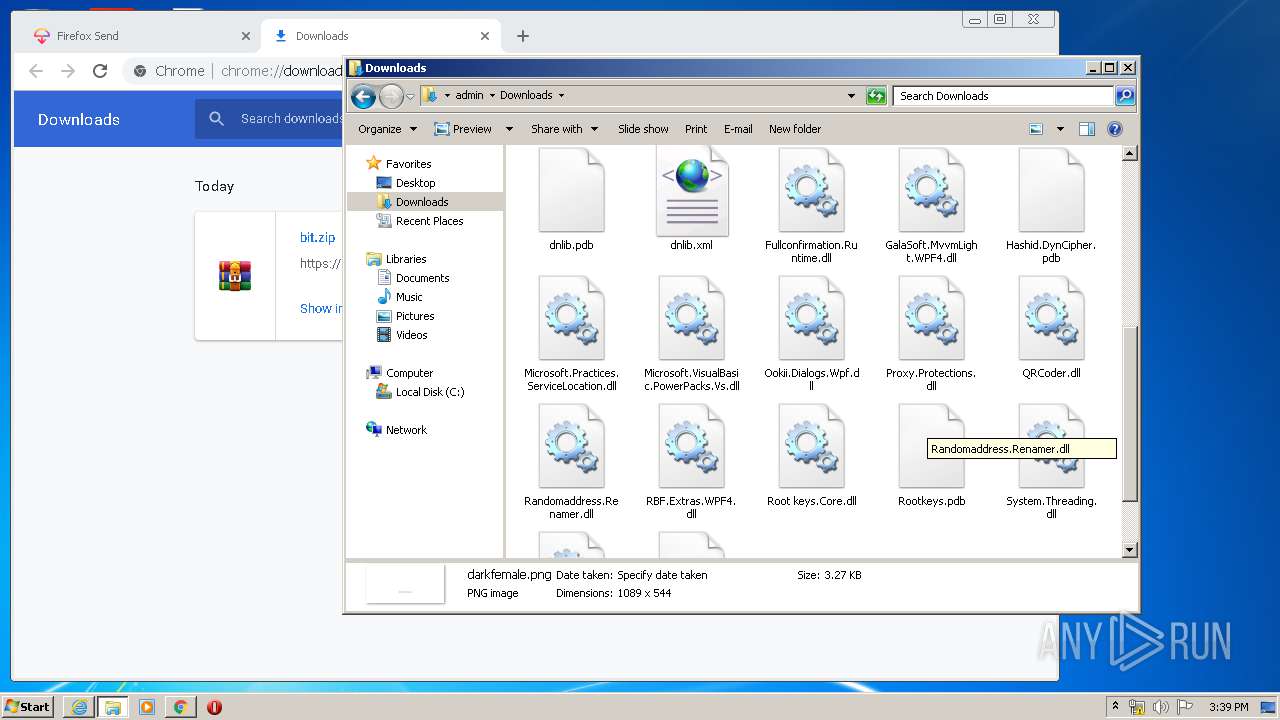
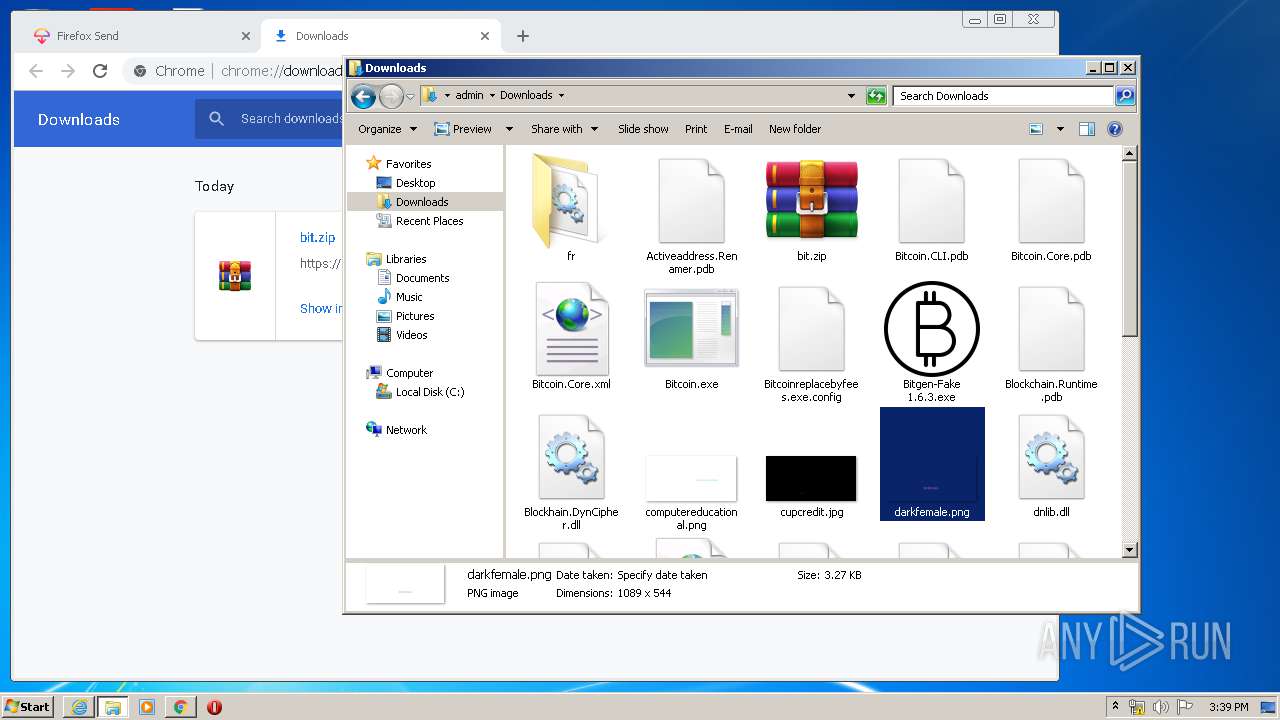
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JK8TXGVG.txt | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1ZQM7IWD.txt | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabF8D.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarF8E.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verFBE.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[6].xml | xml | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4VK5H8UM.txt | text | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsmlM24PXMMR.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
63
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
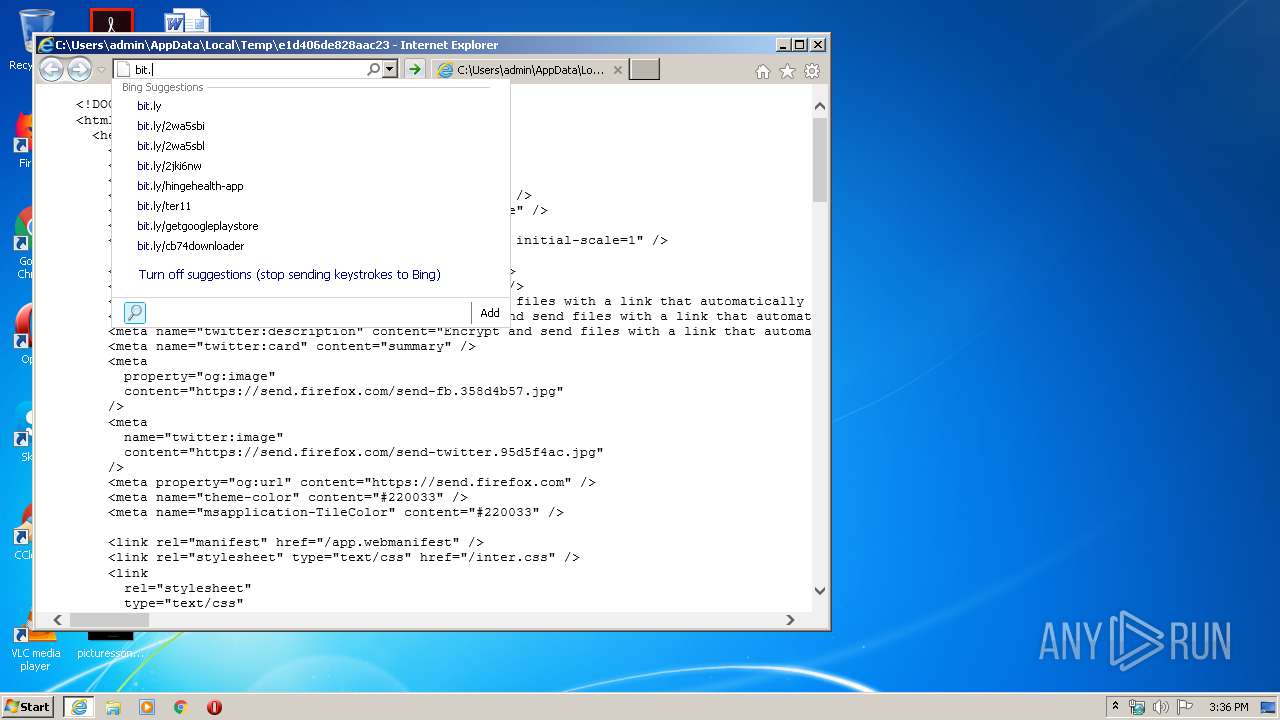
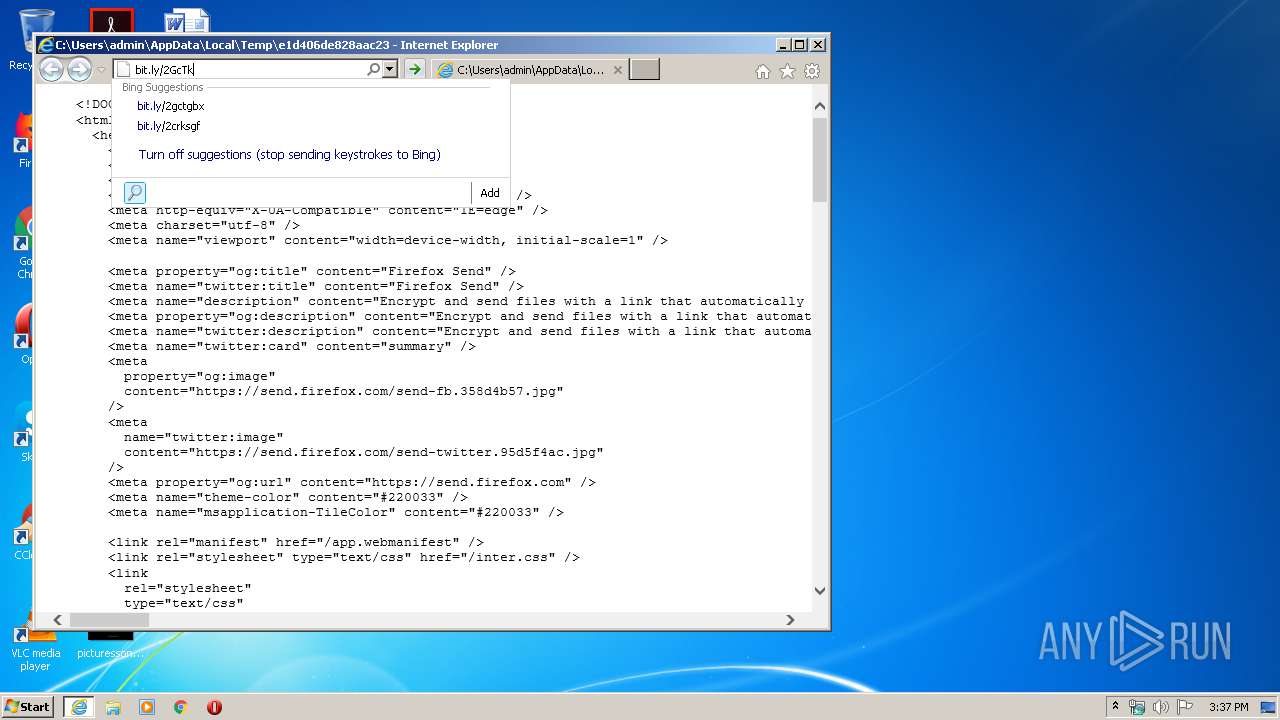
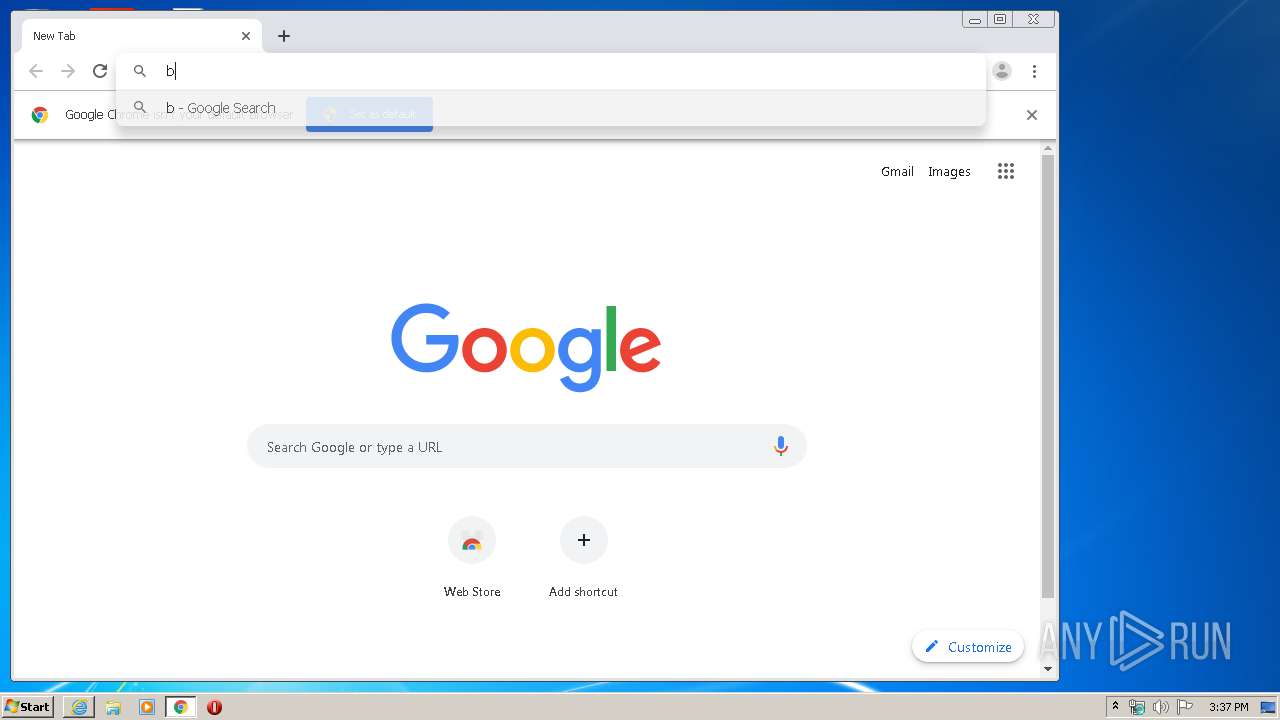
2076 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bi&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2744 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
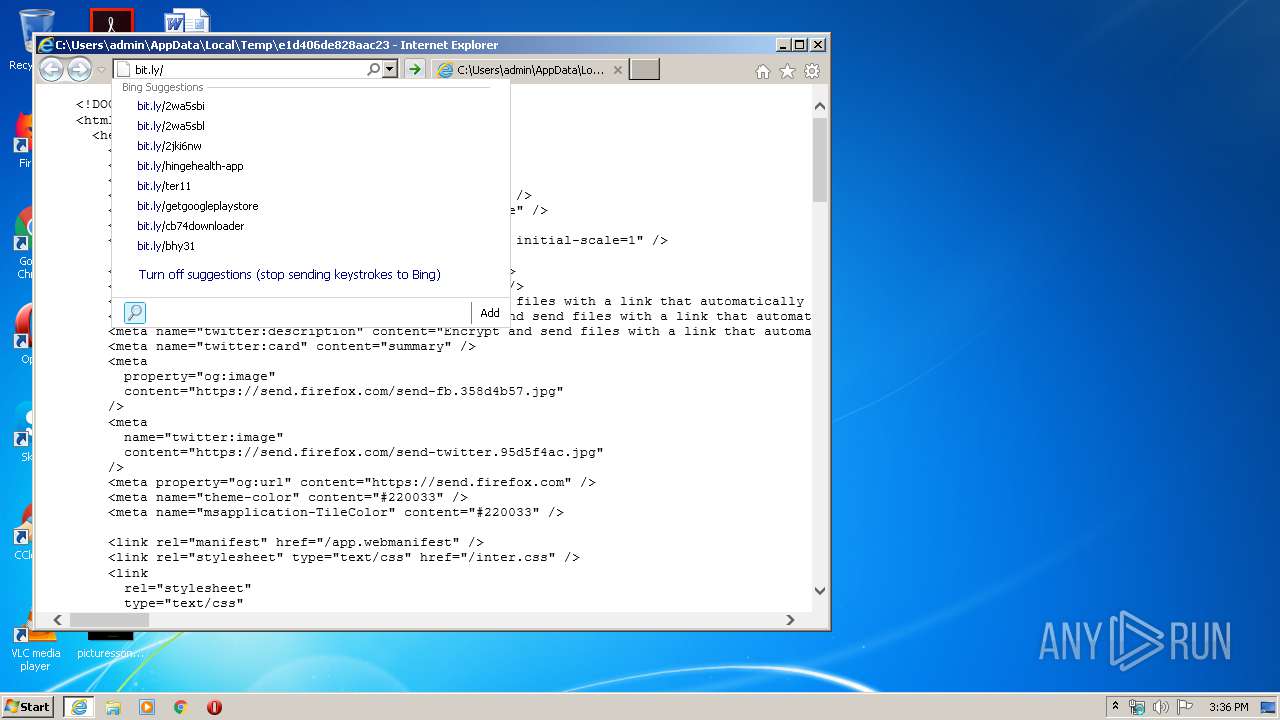
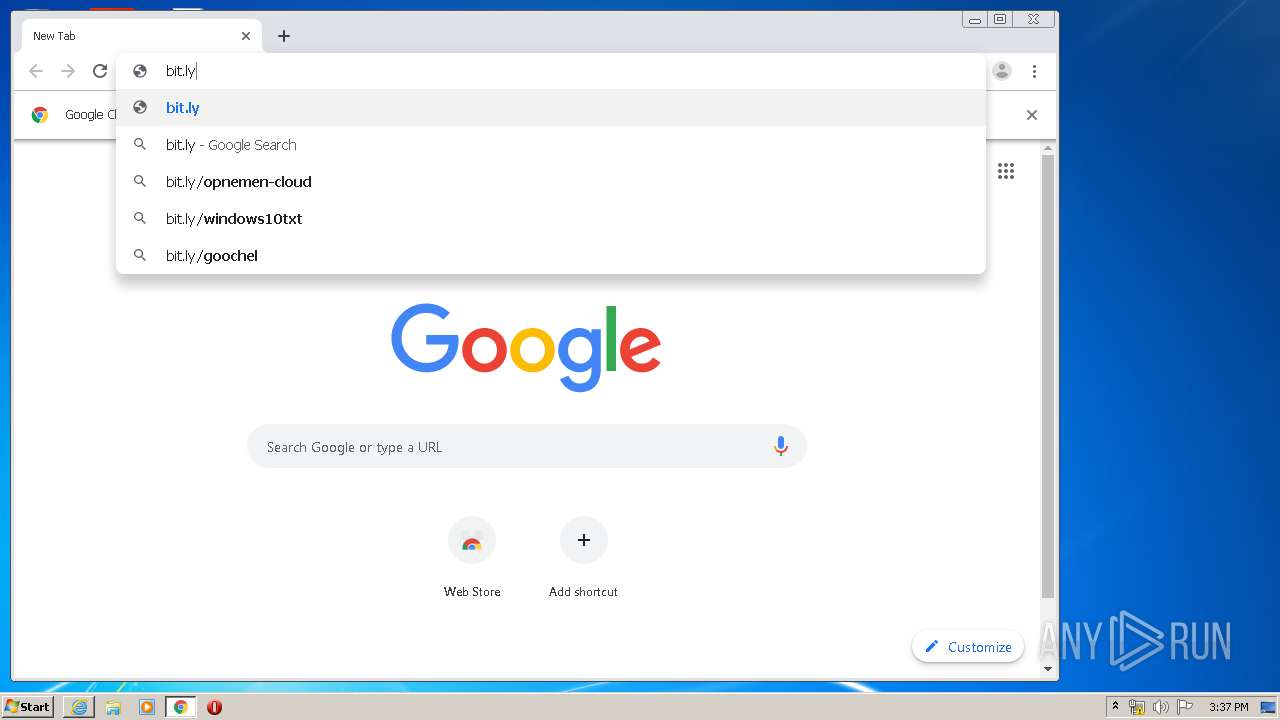
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.l&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 249 b | whitelisted |
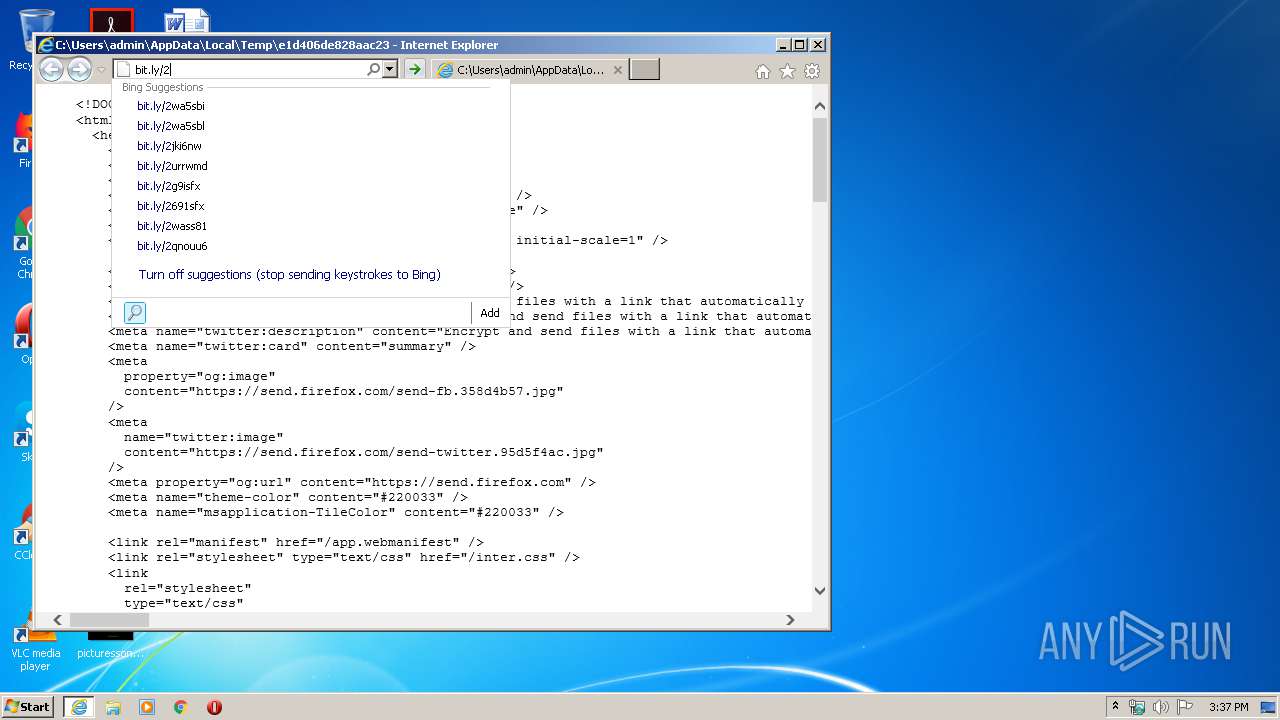
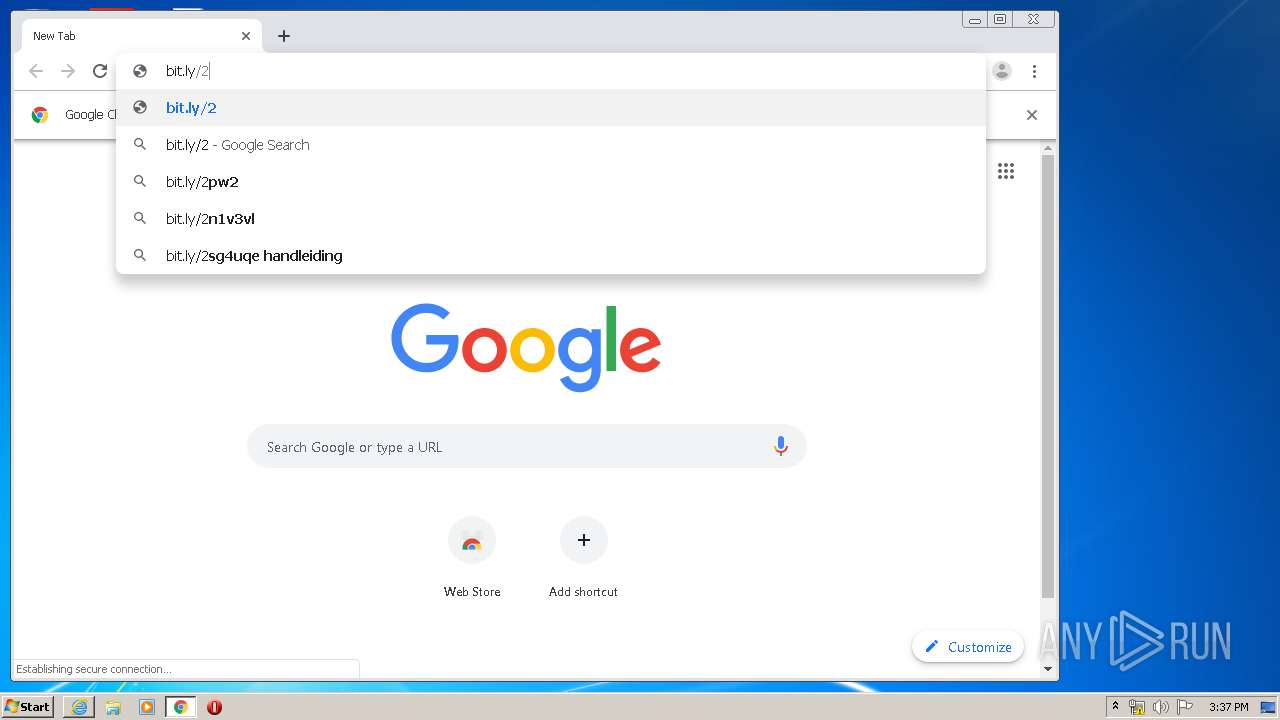
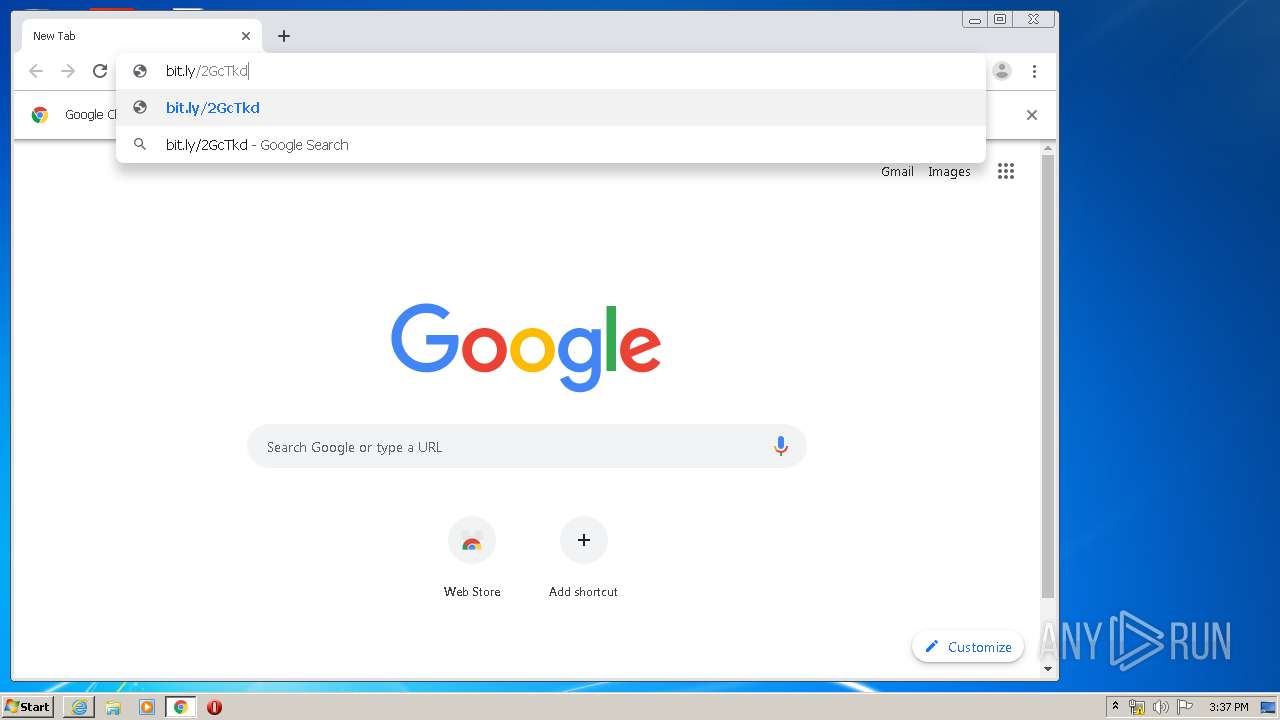
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.ly%2F2Gc&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 231 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.y&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 241 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.ly&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 248 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.ly%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 252 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.ly%2F2GcT&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 231 b | whitelisted |
2744 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=bit.&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 250 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | iexplore.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
2744 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
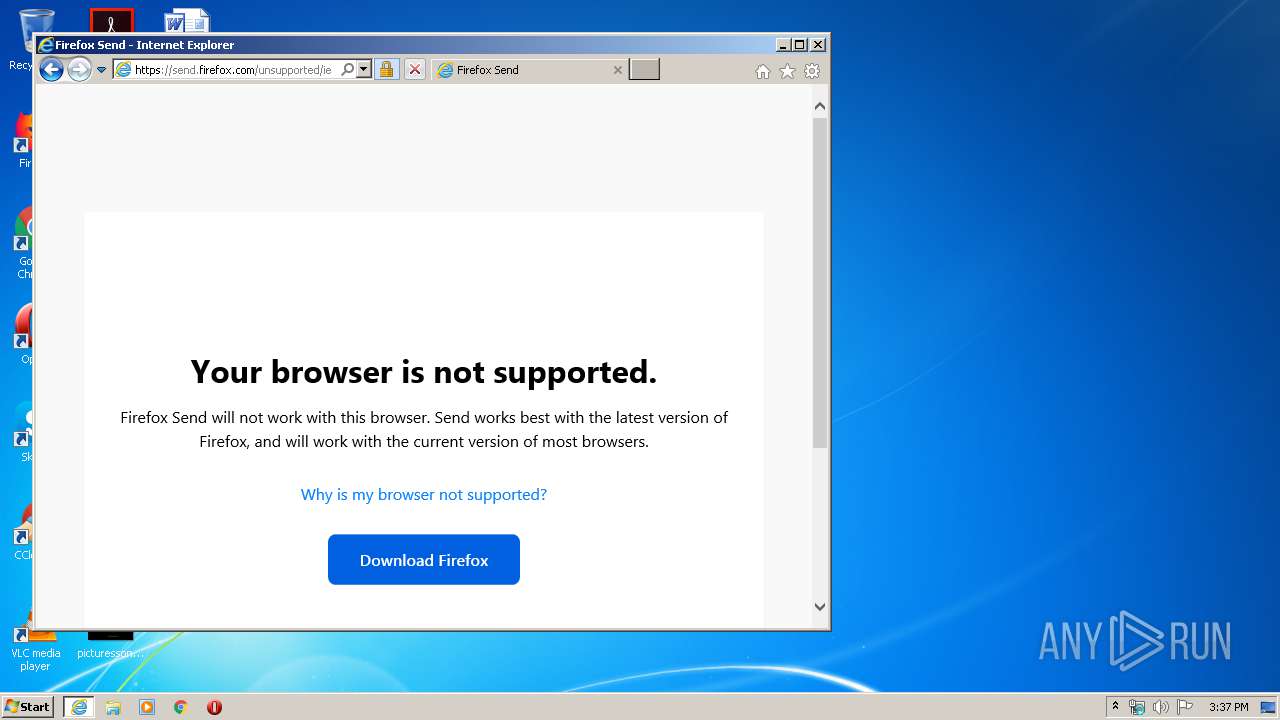
2076 | iexplore.exe | 35.186.224.242:443 | send.firefox.com | Google Inc. | US | suspicious |
2904 | chrome.exe | 172.217.16.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2076 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2744 | iexplore.exe | 35.186.224.242:443 | send.firefox.com | Google Inc. | US | suspicious |
2904 | chrome.exe | 172.217.19.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2904 | chrome.exe | 172.217.16.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 216.58.213.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
bit.ly |
| shared |
send.firefox.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |