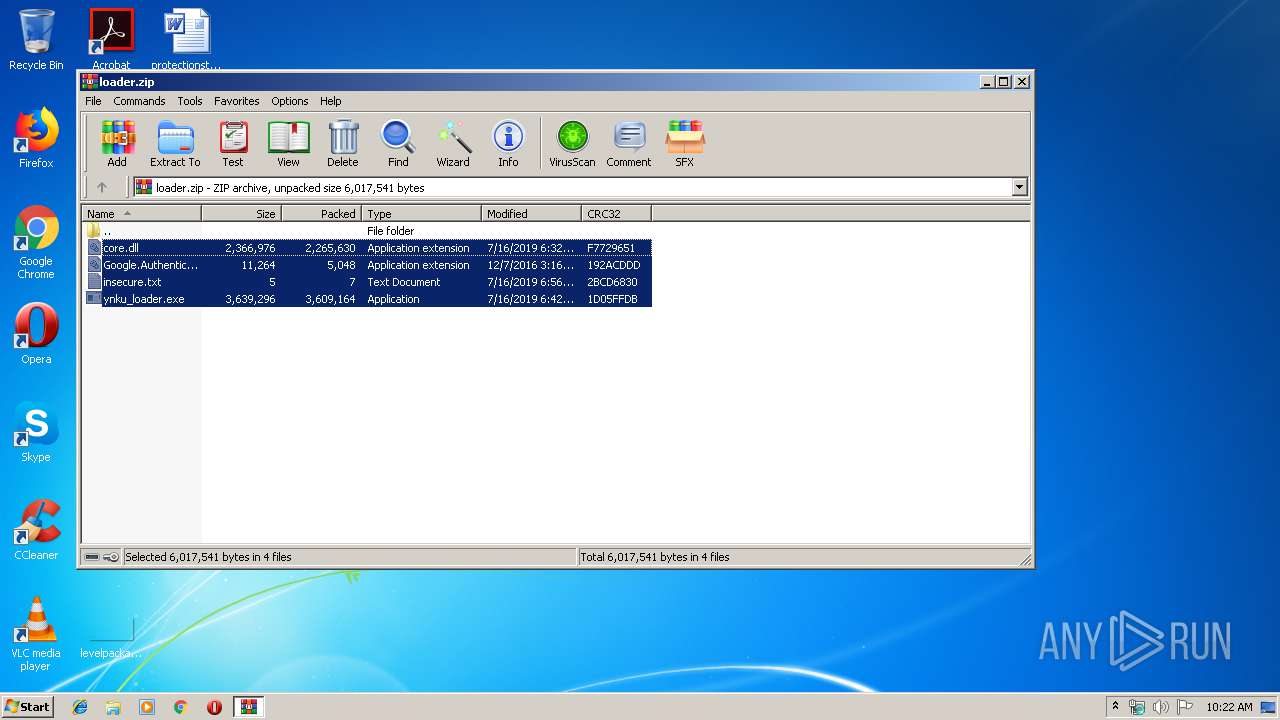
| download: | loader.zip |
| Full analysis: | https://app.any.run/tasks/88d30038-d13d-4a7f-832c-7dff7f89ac9b |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 09:21:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
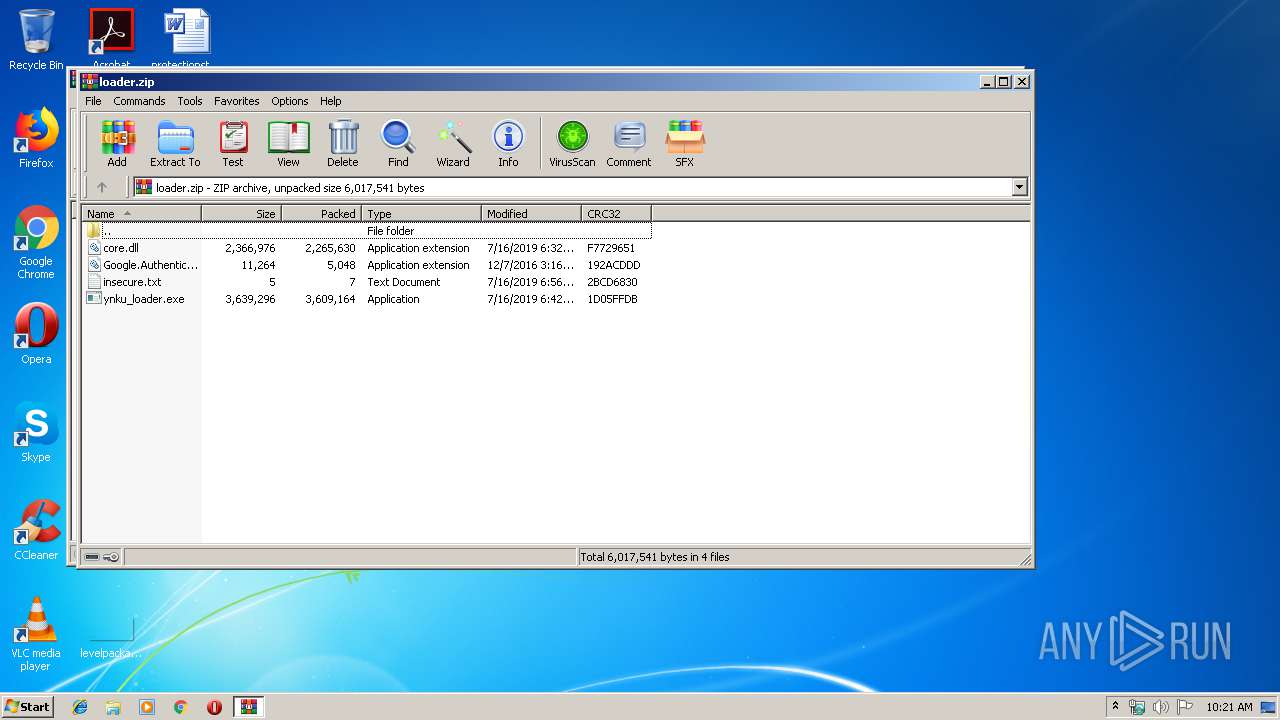
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 65CB72A3C2670D1944C84D46D5929969 |
| SHA1: | 0AF292EB3AF41EF3B5E051EF09D03185B1359224 |
| SHA256: | 154573E4BEA70F11BA39669931A413FAFC876CCB1559EF27369D4FEE68EC7264 |
| SSDEEP: | 98304:sEbxZ0TFbheOUW1NP71Xolw69n6e/5F4rDfLijJvKVY56TMudN9QDXfTC4N5jyw6:sonSeOX3P7holw6dxF4Hf8h1KBcDXfFc |
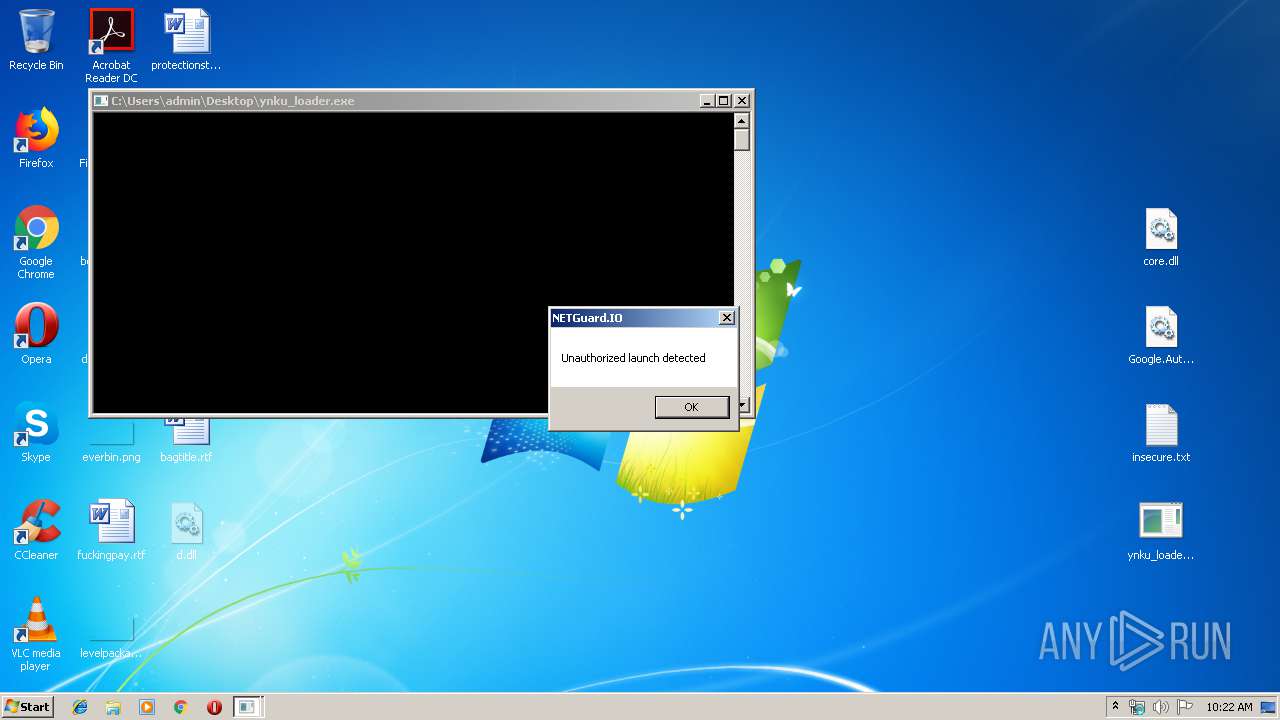
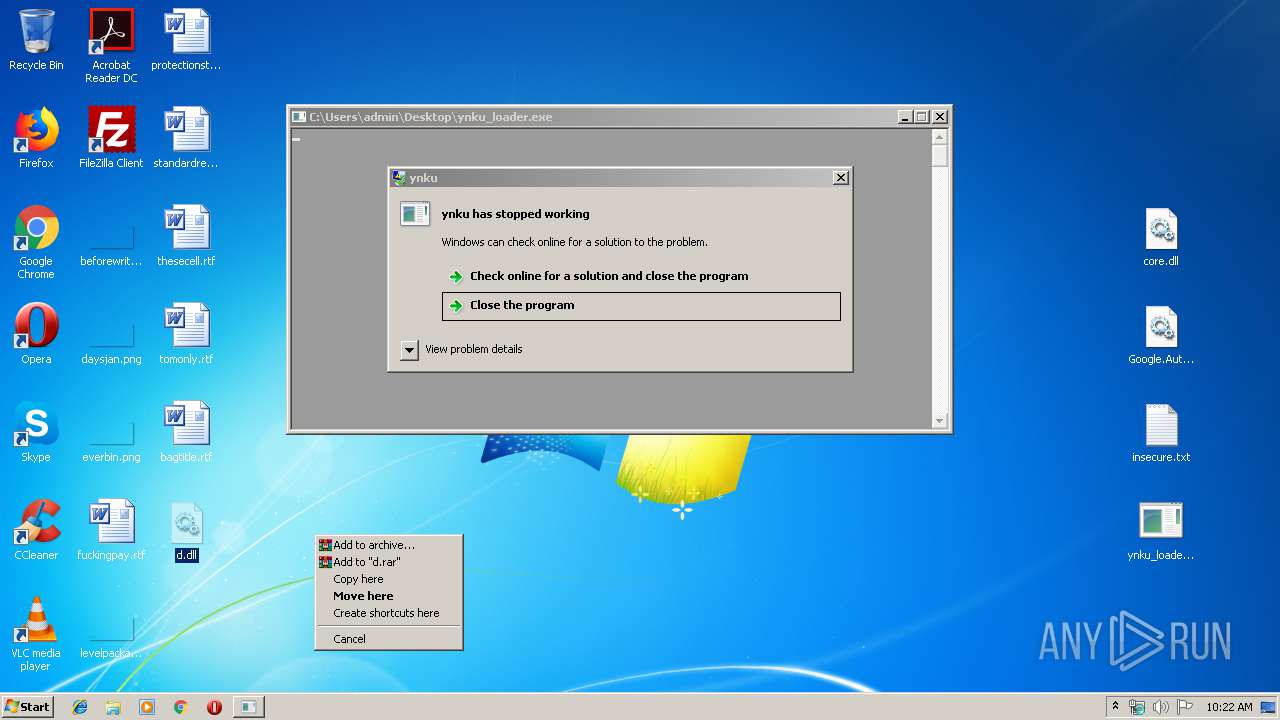
MALICIOUS
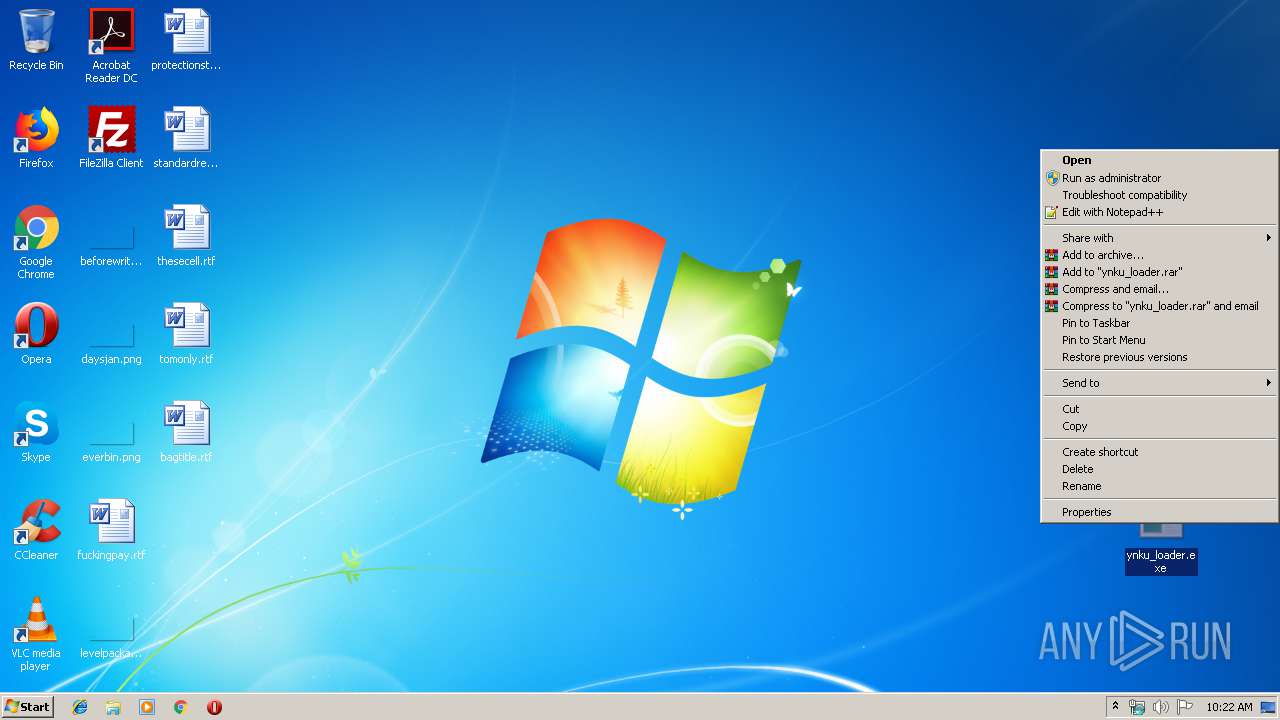
Application was dropped or rewritten from another process
- ynku_loader.exe (PID: 2224)
Loads dropped or rewritten executable
- explorer.exe (PID: 124)
- SearchProtocolHost.exe (PID: 2588)
- ynku_loader.exe (PID: 2224)
SUSPICIOUS
Executable content was dropped or overwritten
- ynku_loader.exe (PID: 2224)
- explorer.exe (PID: 124)
Creates files in the user directory
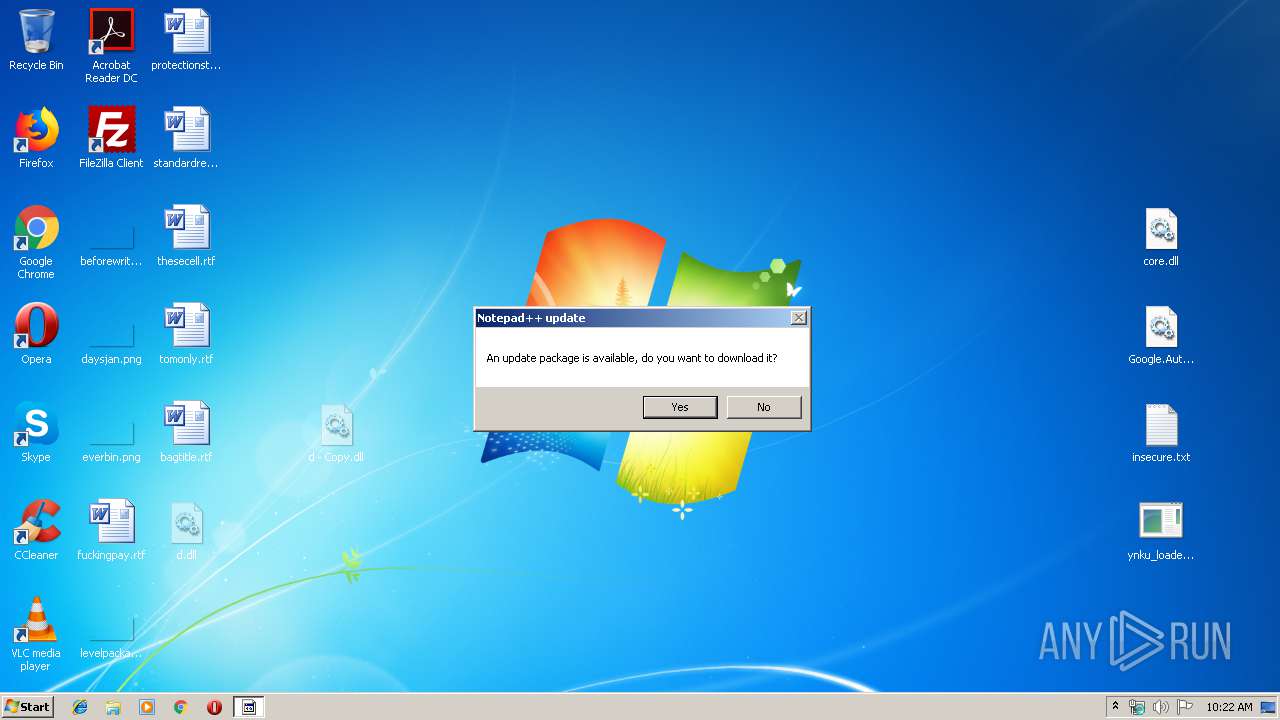
- notepad++.exe (PID: 3932)
INFO
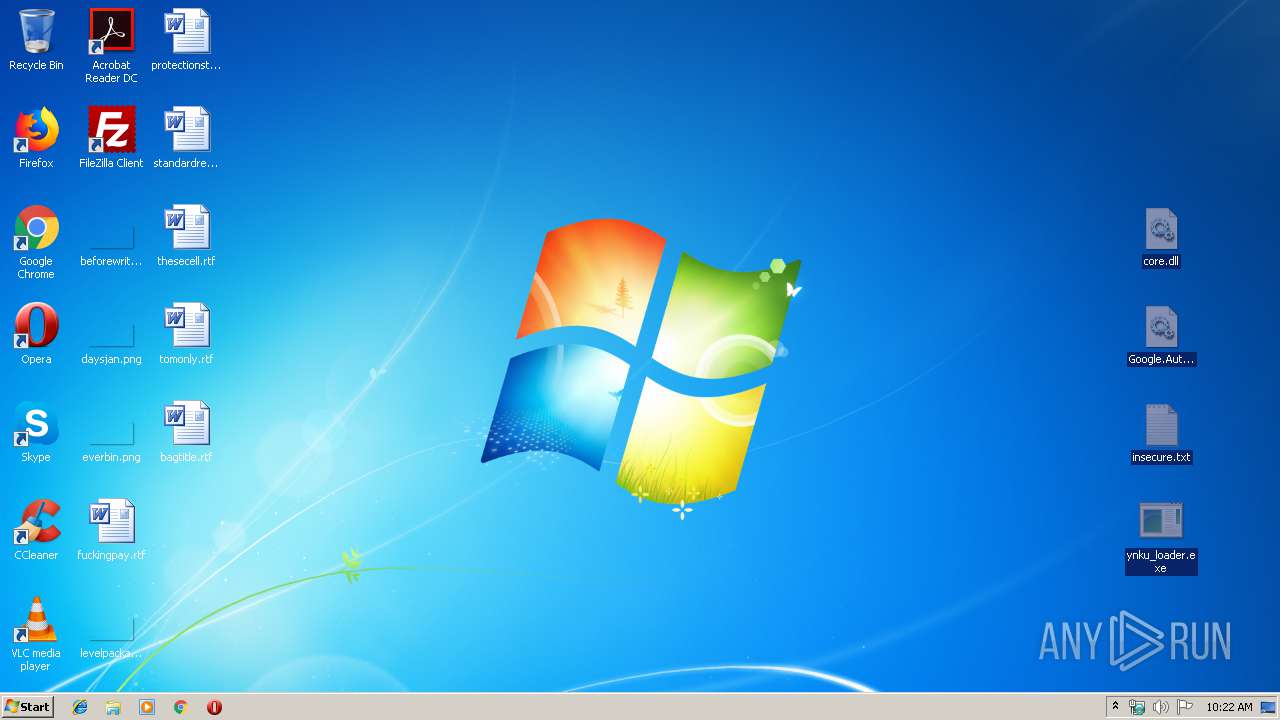
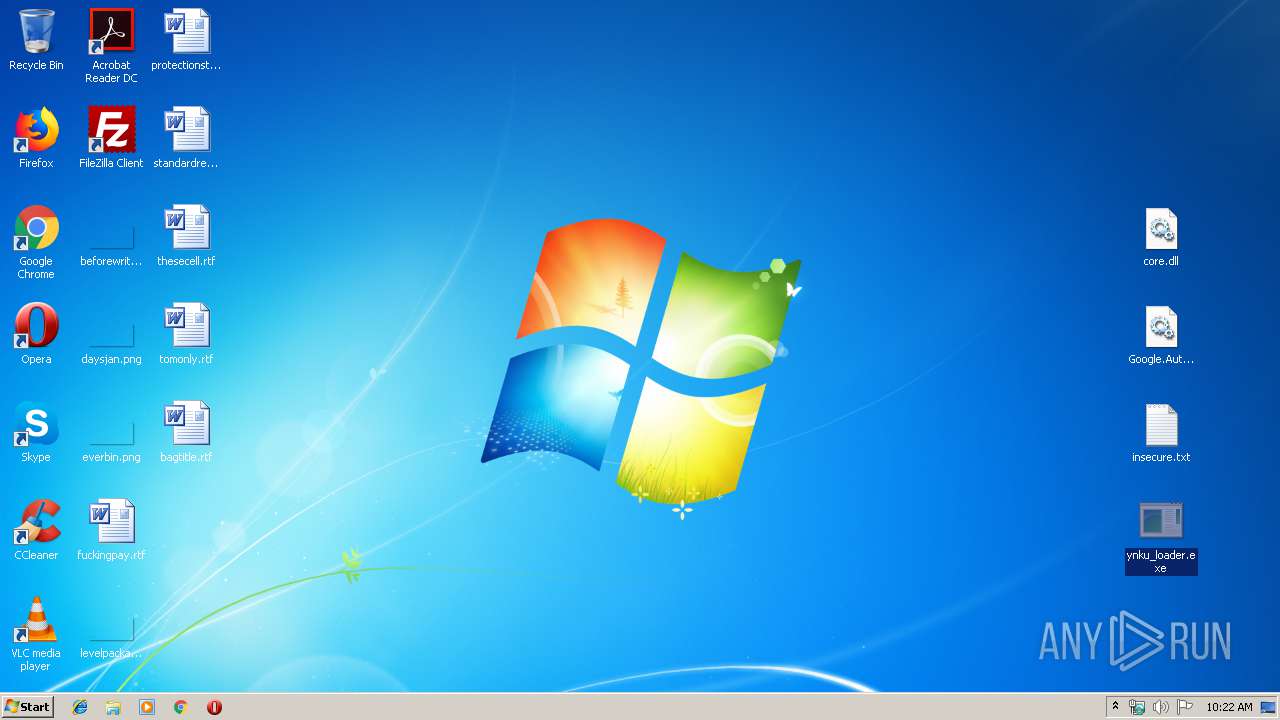
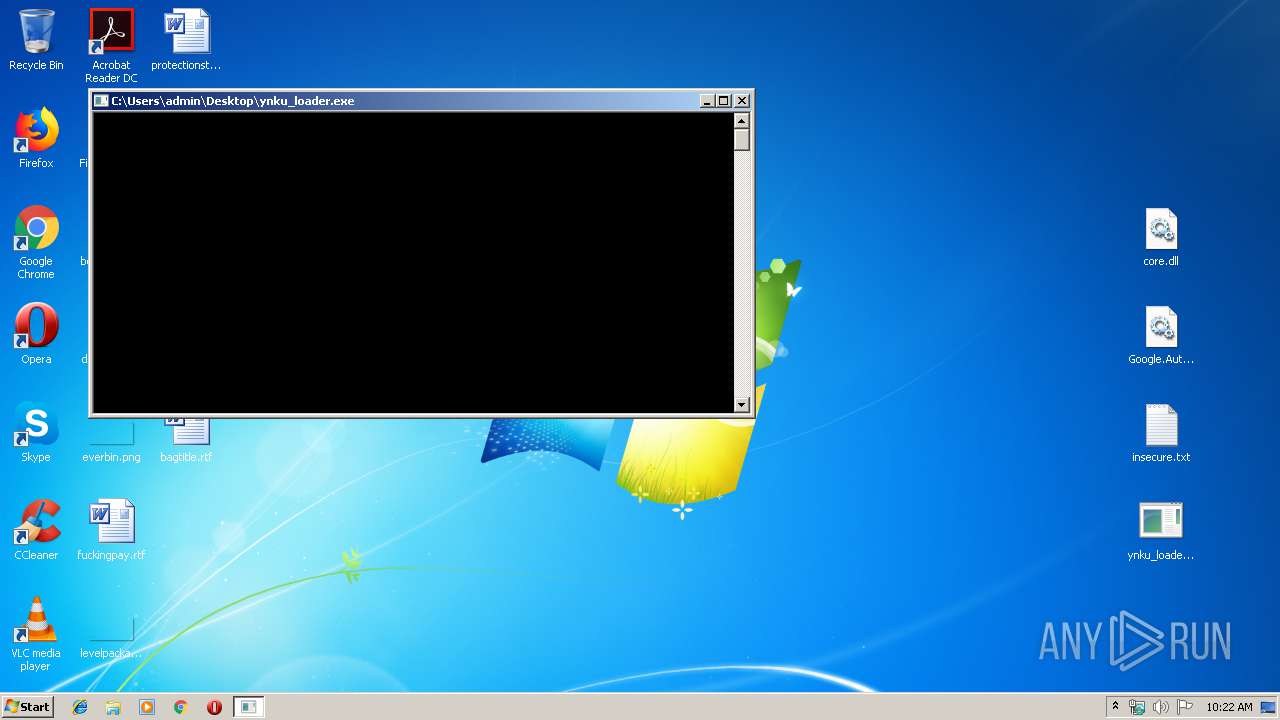
Manual execution by user
- ynku_loader.exe (PID: 2224)
Application was crashed
- ynku_loader.exe (PID: 2224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:16 19:32:21 |
| ZipCRC: | 0xf7729651 |
| ZipCompressedSize: | 2265630 |
| ZipUncompressedSize: | 2366976 |
| ZipFileName: | core.dll |
Total processes
45
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\Desktop\ynku_loader.exe" | C:\Users\admin\Desktop\ynku_loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ynku Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2588 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe8_ Global\UsGthrCtrlFltPipeMssGthrPipe8 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
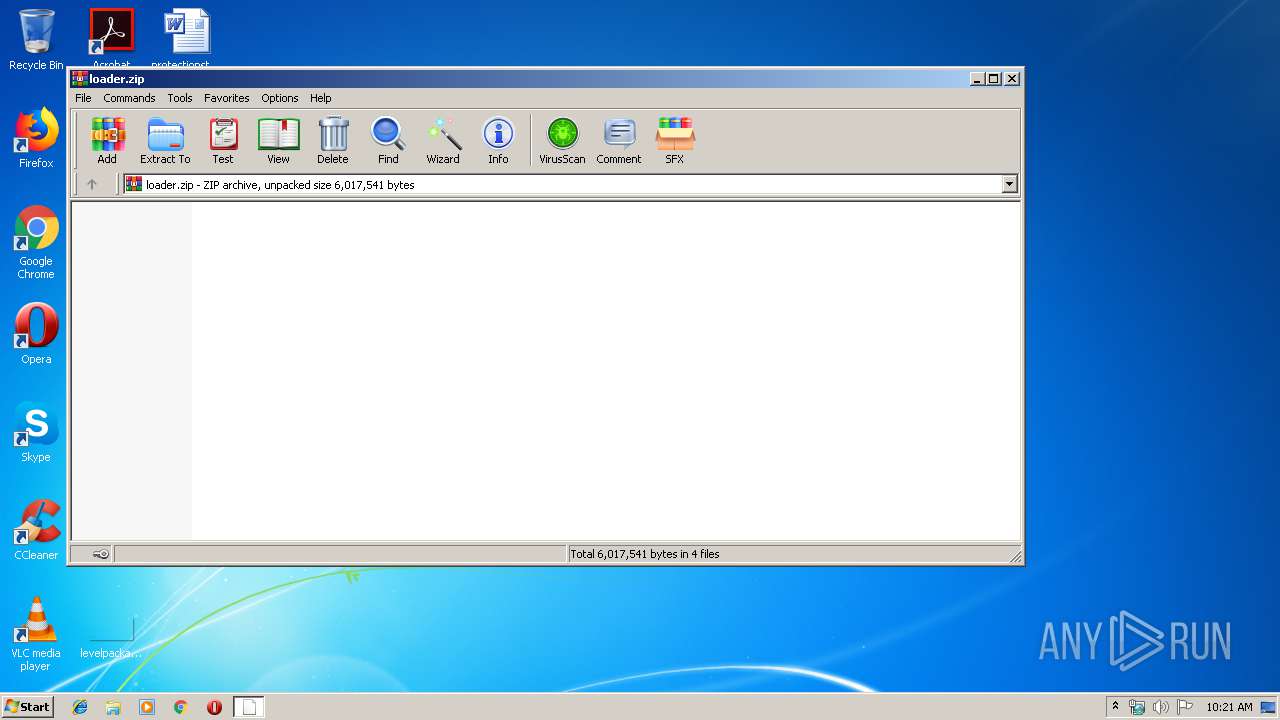
| 3552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\loader.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
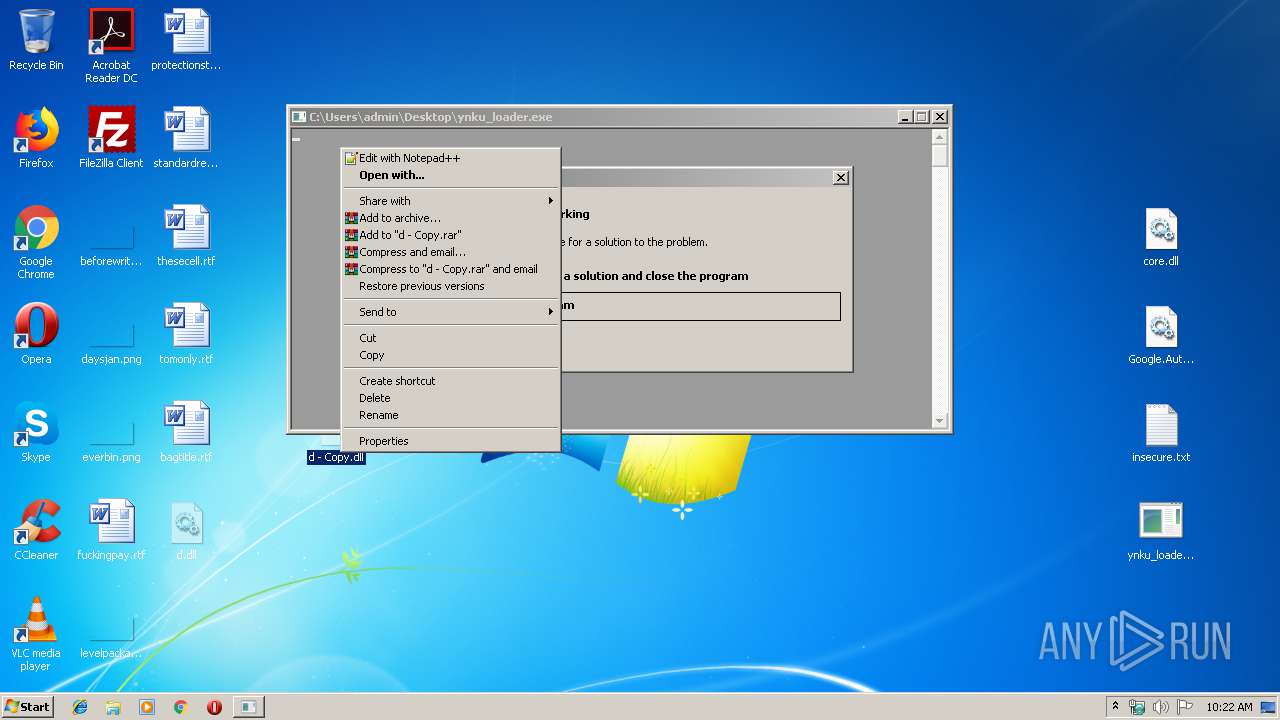
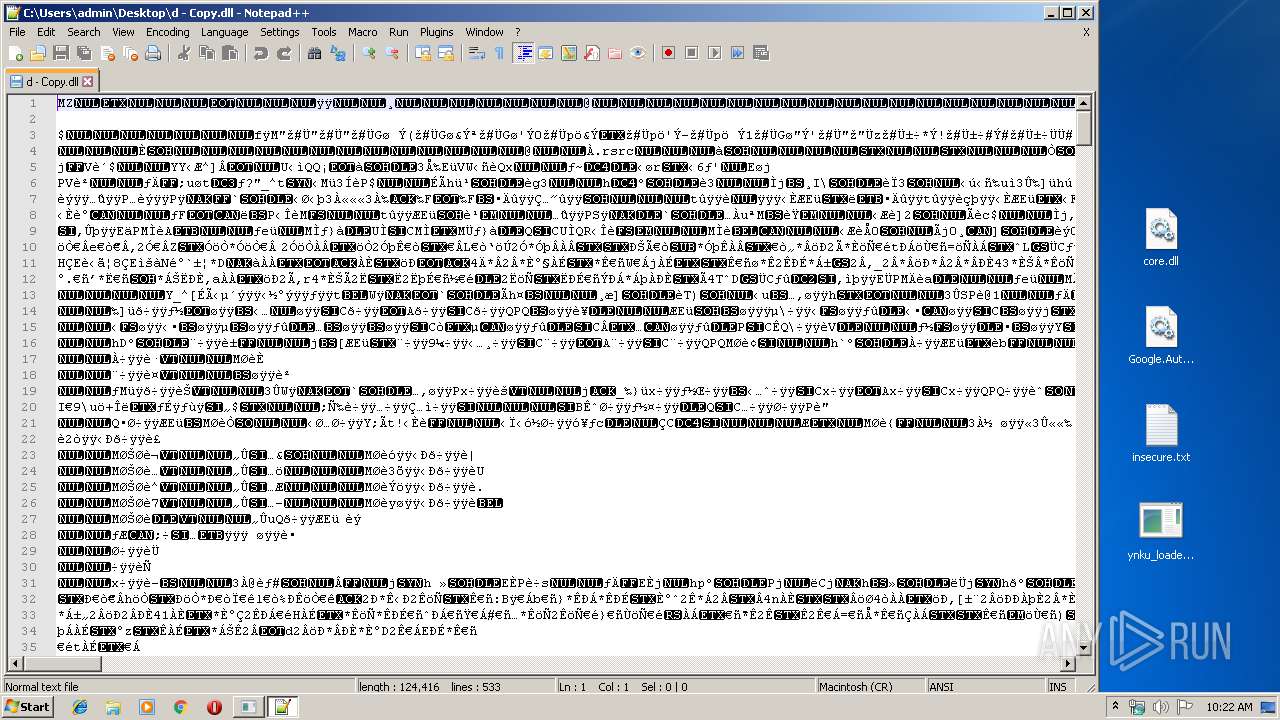
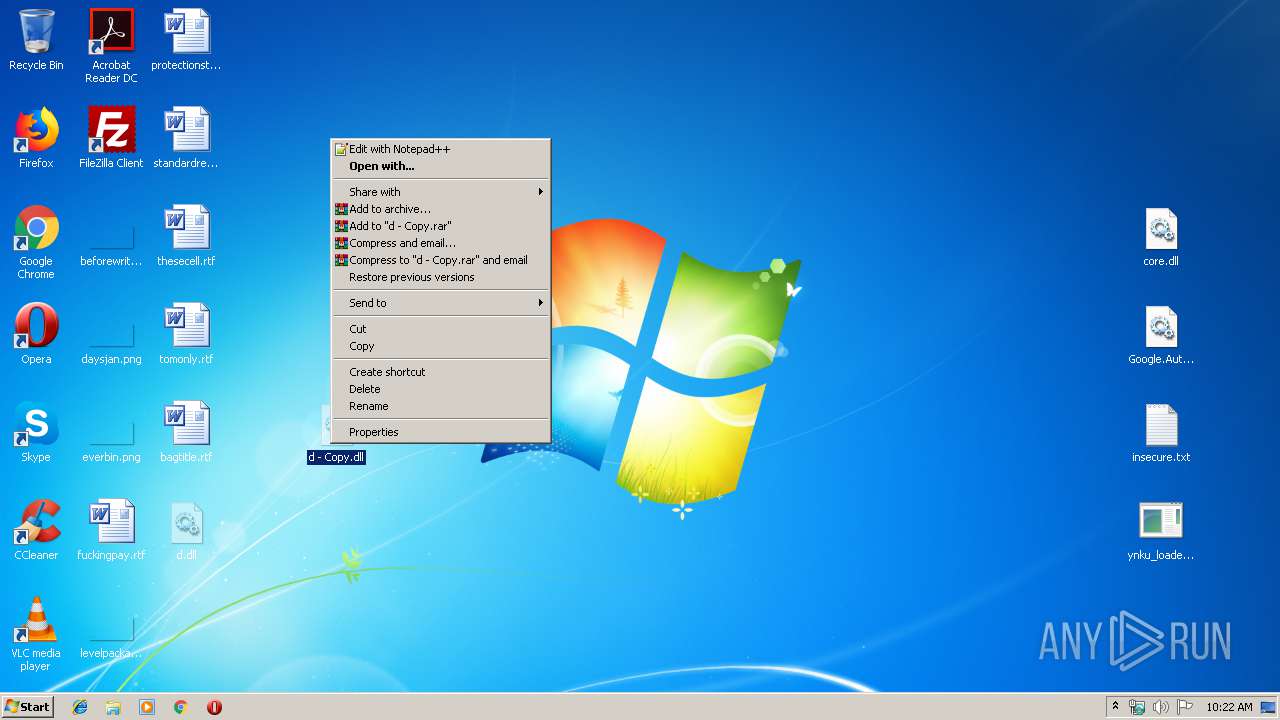
| 3932 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\d - Copy.dll" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
3 178
Read events
3 057
Write events
121
Delete events
0
Modification events
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\loader.zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
5
Suspicious files
0
Text files
7
Unknown types
0
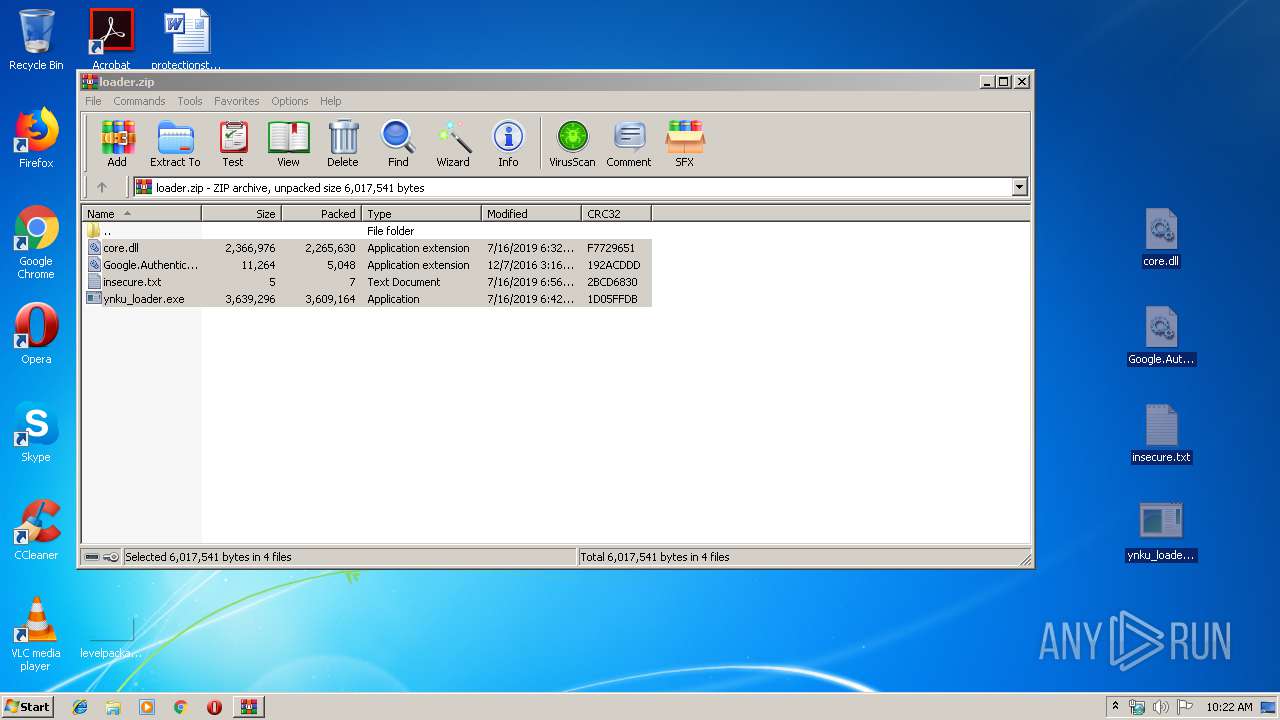
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.22635\core.dll | — | |
MD5:— | SHA256:— | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.22635\Google.Authenticator.dll | — | |
MD5:— | SHA256:— | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.22635\insecure.txt | — | |
MD5:— | SHA256:— | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.22635\ynku_loader.exe | — | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\Desktop\core.dll | executable | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\Desktop\d - Copy.dll | executable | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\Desktop\ynku_loader.exe | executable | |
MD5:— | SHA256:— | |||
| 2224 | ynku_loader.exe | C:\Users\admin\Desktop\d.dll | executable | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\Desktop\Google.Authenticator.dll | executable | |
MD5:380630DBE47BD87F57C2912BD3ACB0C3 | SHA256:80D80070C109D0465434218D5C16A824A249B8B5527D4BB66282DDA77C8B40BD | |||
| 3932 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.21.242.197:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|