| File name: | Webex_Meeting - Copy.js |
| Full analysis: | https://app.any.run/tasks/13d38445-5de6-482d-9fd1-4807634d19f0 |
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2021, 13:30:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/calendar |
| File info: | vCalendar calendar file |
| MD5: | 517413A48E27817BFCD6795F1146C917 |
| SHA1: | A924C64190EAA22161AE6F7F7E30E136D975D43C |
| SHA256: | 153E0EFB4D3C76D54FD57E446CCC555C23520A7BFE1B48A6C8551D9F0E2BC3AE |
| SSDEEP: | 192:PLMFYzc2nlmrjQ2QZfHE+6IDGWoWS8DnSPeo6:PGUlGBWHEMDGFbeo6 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2208)
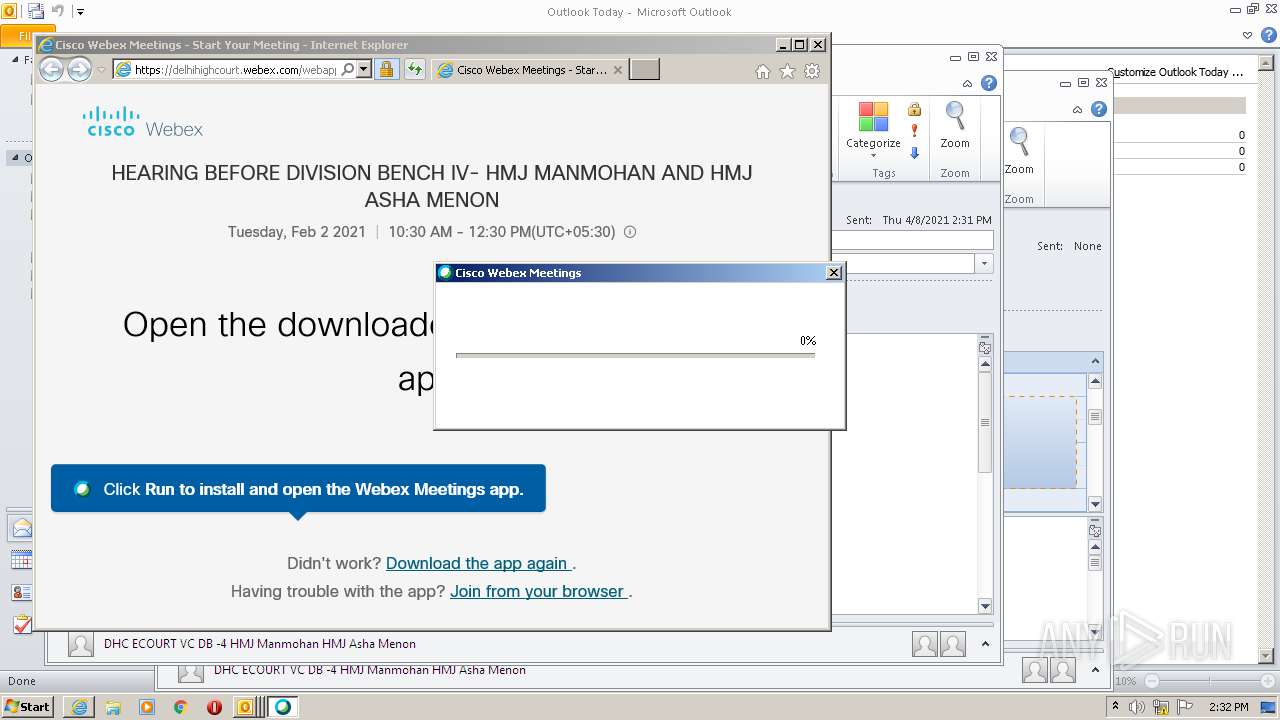
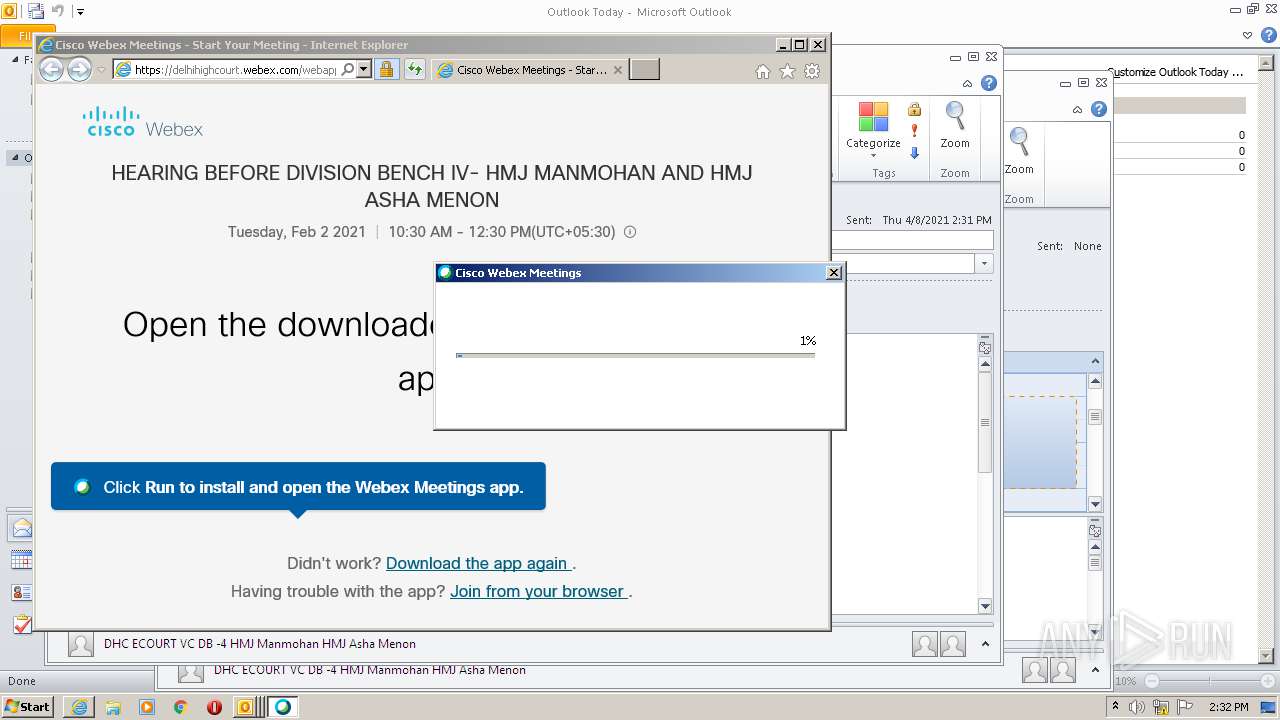
Application was dropped or rewritten from another process
- webex.exe (PID: 3036)
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
- atcliun.exe (PID: 2708)
- CiscoWebExStart.exe (PID: 3304)
- wbxreport.exe (PID: 1552)
- CiscoWebExStart.exe (PID: 3208)
- atmgr.exe (PID: 668)
- atcliun.exe (PID: 2236)
- WEBEXA~1.EXE (PID: 1744)
- CISCOW~1.EXE (PID: 1848)
- atmgr.exe (PID: 3604)
- wbxreport.exe (PID: 3468)
Loads dropped or rewritten executable
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
- CiscoWebExStart.exe (PID: 3304)
- wbxreport.exe (PID: 1552)
- CiscoWebExStart.exe (PID: 3208)
- atmgr.exe (PID: 668)
- wbxreport.exe (PID: 3468)
- atmgr.exe (PID: 3604)
Changes the autorun value in the registry
- CiscoWebExStart.exe (PID: 3304)
SUSPICIOUS
Drops a file that was compiled in debug mode
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 2520)
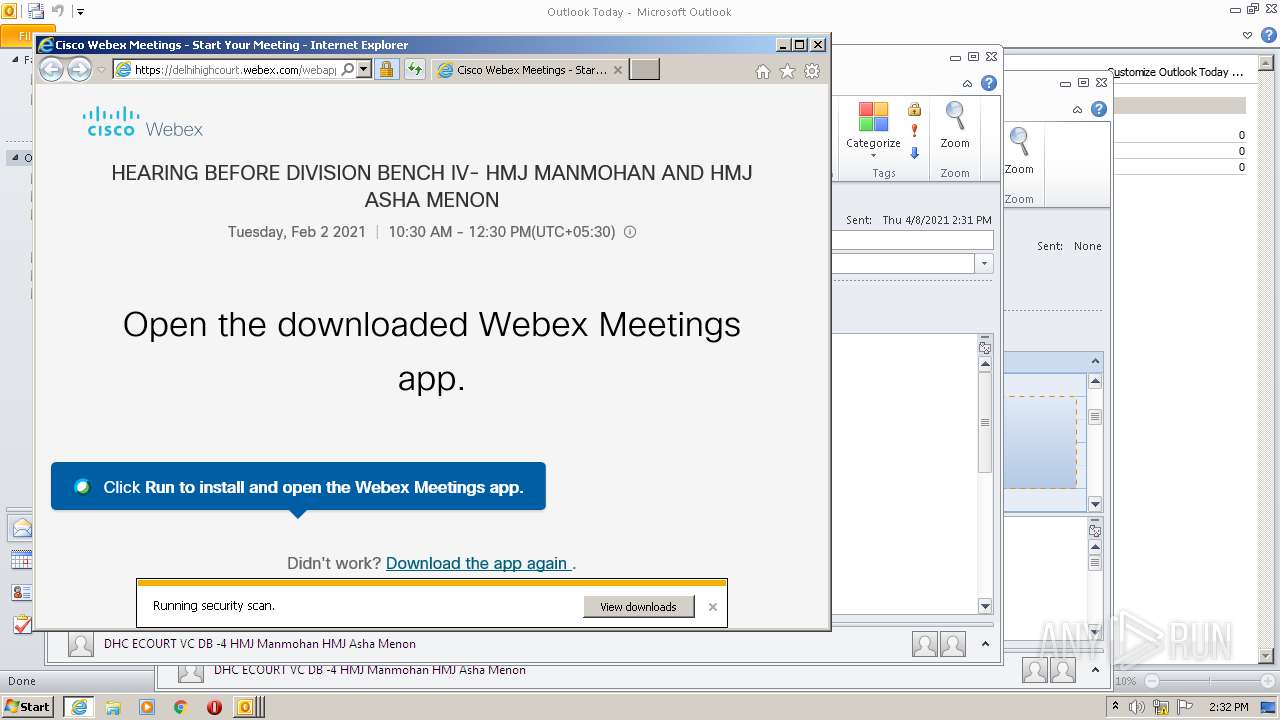
- webex.exe (PID: 3036)
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2164)
- webex.exe (PID: 3036)
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
Drops a file with a compile date too recent
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 2520)
- webex.exe (PID: 3036)
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
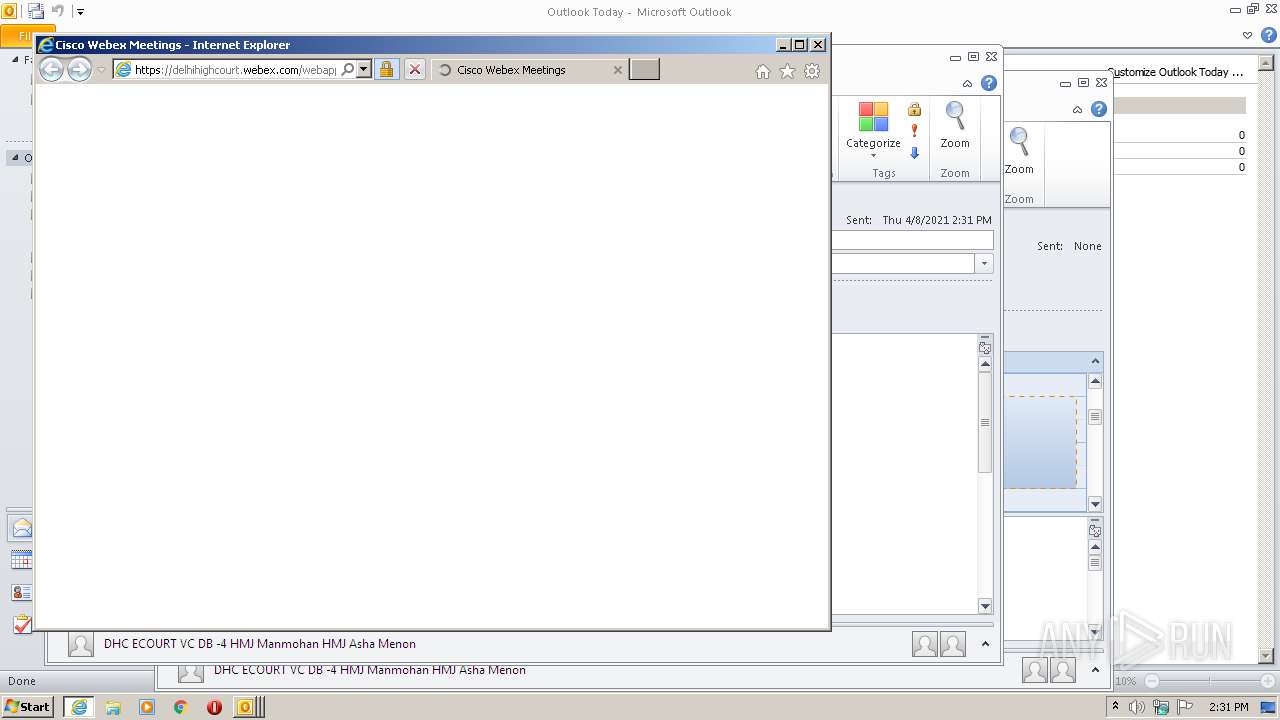
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2208)
Starts application with an unusual extension
- webex.exe (PID: 3036)
Drops a file with too old compile date
- atmgr.exe (PID: 2892)
Changes IE settings (feature browser emulation)
- atmgr.exe (PID: 2892)
- atmgr.exe (PID: 668)
- atmgr.exe (PID: 3604)
Creates a software uninstall entry
- atcliun.exe (PID: 2708)
- atcliun.exe (PID: 2236)
Application launched itself
- CiscoWebExStart.exe (PID: 3304)
Creates/Modifies COM task schedule object
- atmgr.exe (PID: 2892)
Changes default file association
- CISCOW~1.EXE (PID: 1848)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 2520)
Reads settings of System Certificates
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 2520)
- cws1.tmp (PID: 3288)
- atmgr.exe (PID: 2892)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2520)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2208)
- iexplore.exe (PID: 2164)
Changes internet zones settings
- iexplore.exe (PID: 2520)
Searches for installed software
- OUTLOOK.EXE (PID: 2208)
Application launched itself
- iexplore.exe (PID: 2520)
Changes settings of System certificates
- iexplore.exe (PID: 2520)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2208)
Dropped object may contain Bitcoin addresses
- atmgr.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ics/vcs | | | iCalendar - vCalendar (100) |
|---|
EXIF
VCard
| Classification: | PUBLIC |
|---|---|
| Priority: | 5 |
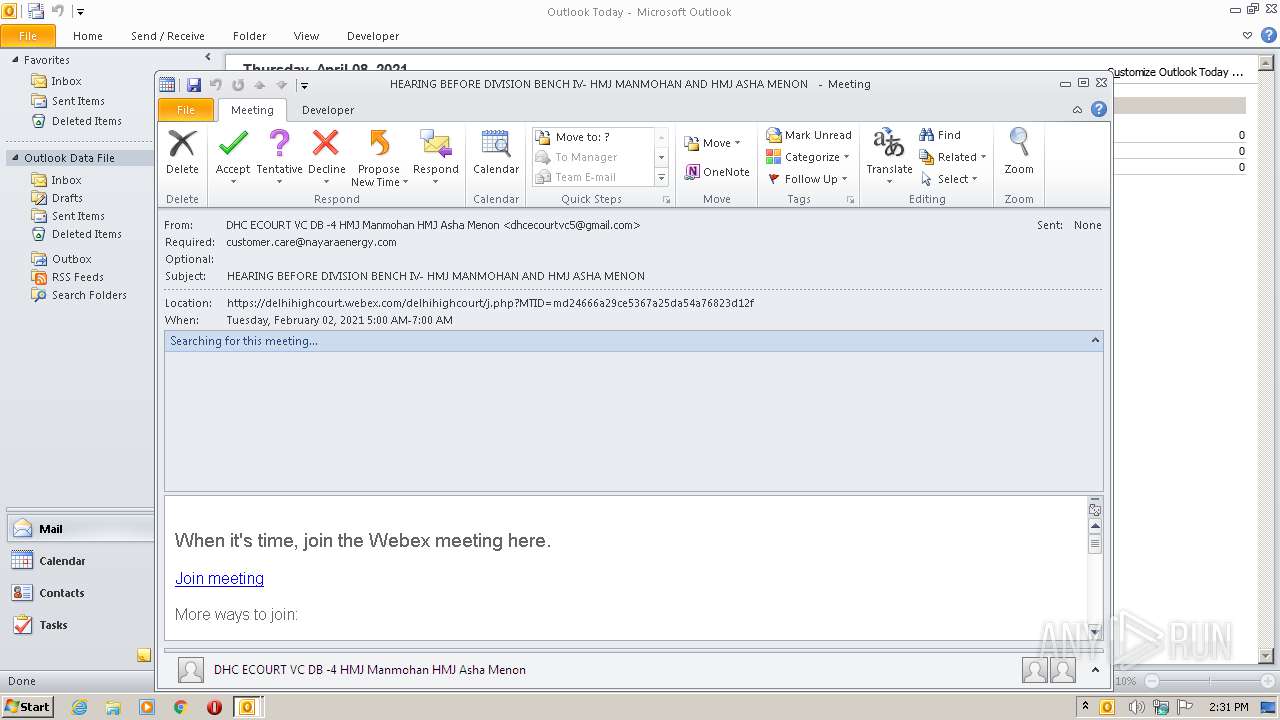
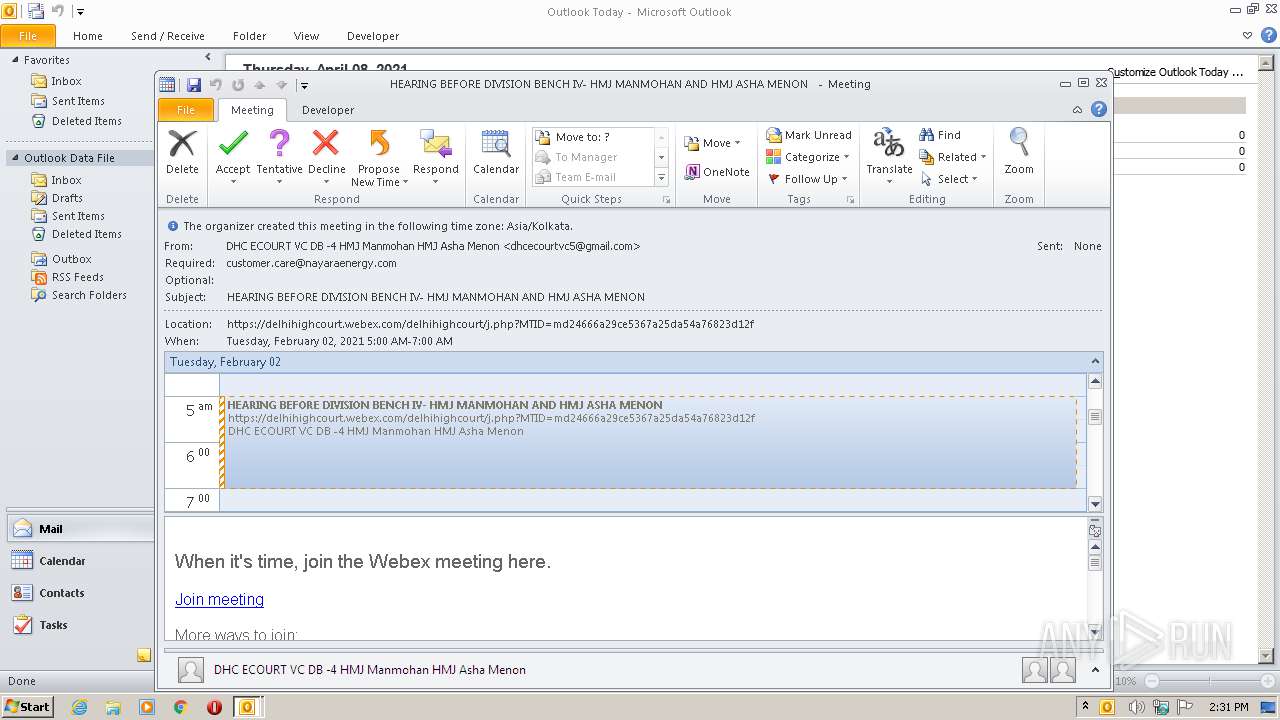
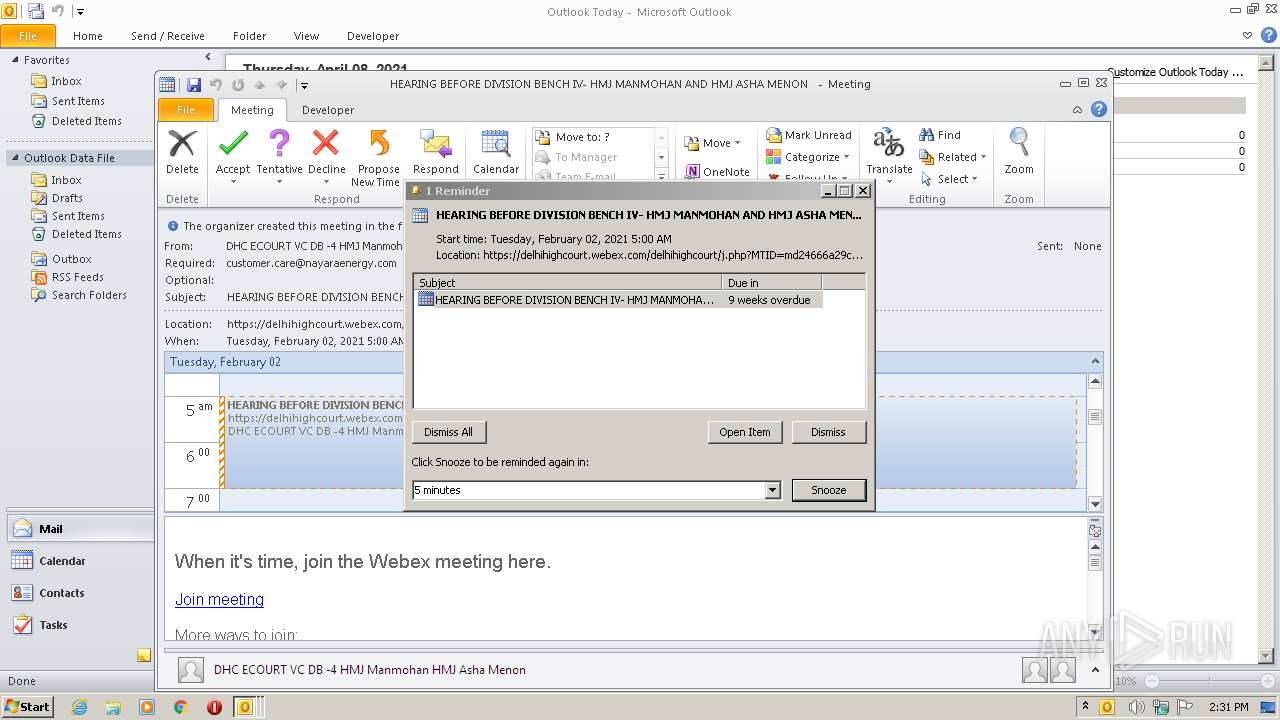
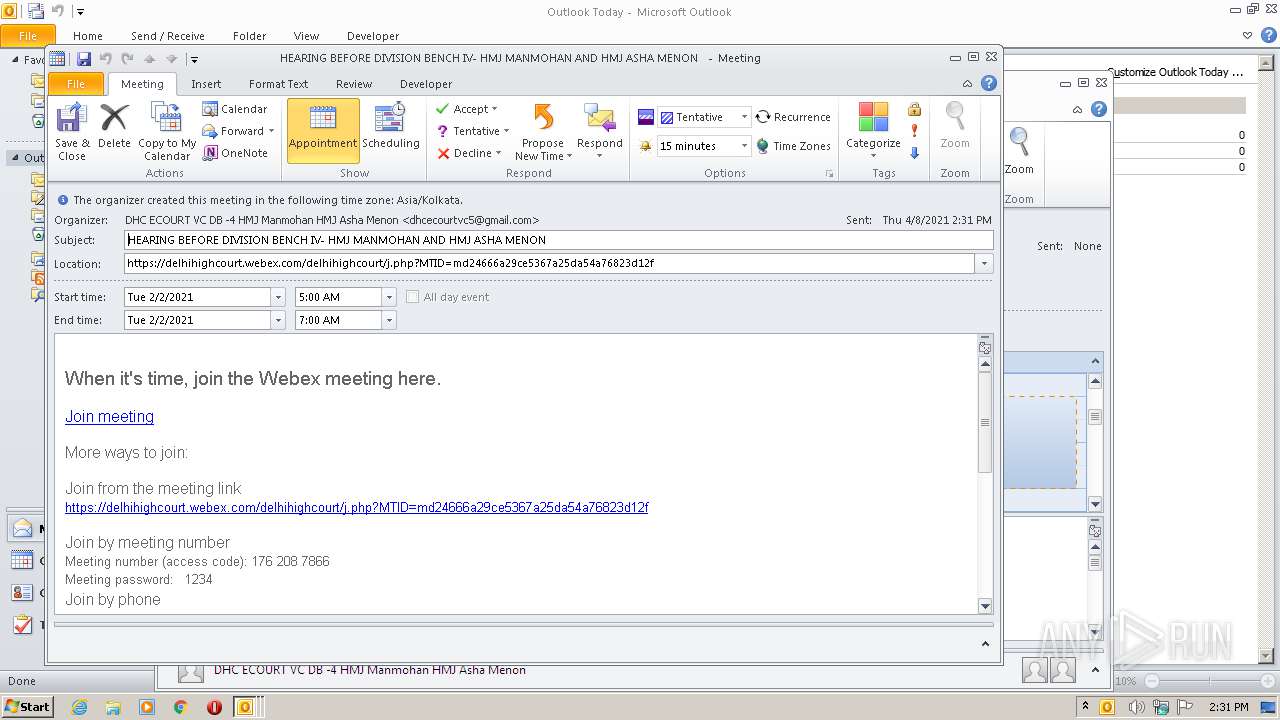
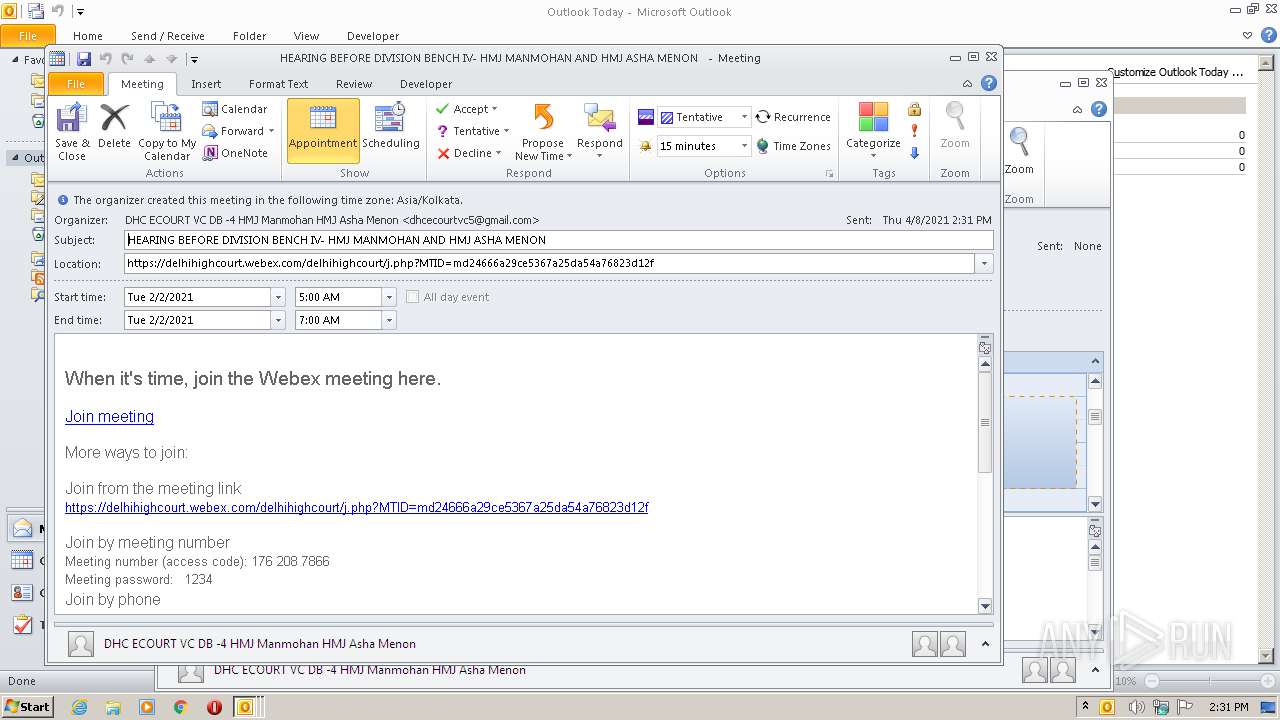
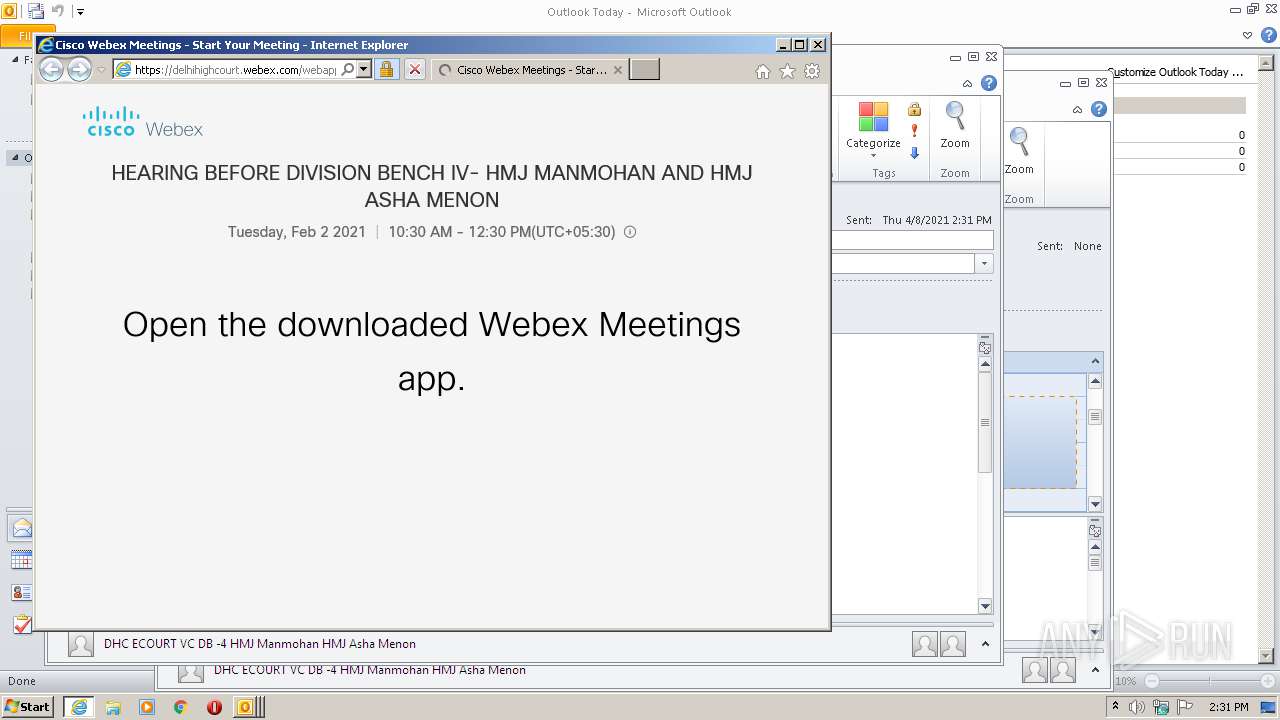
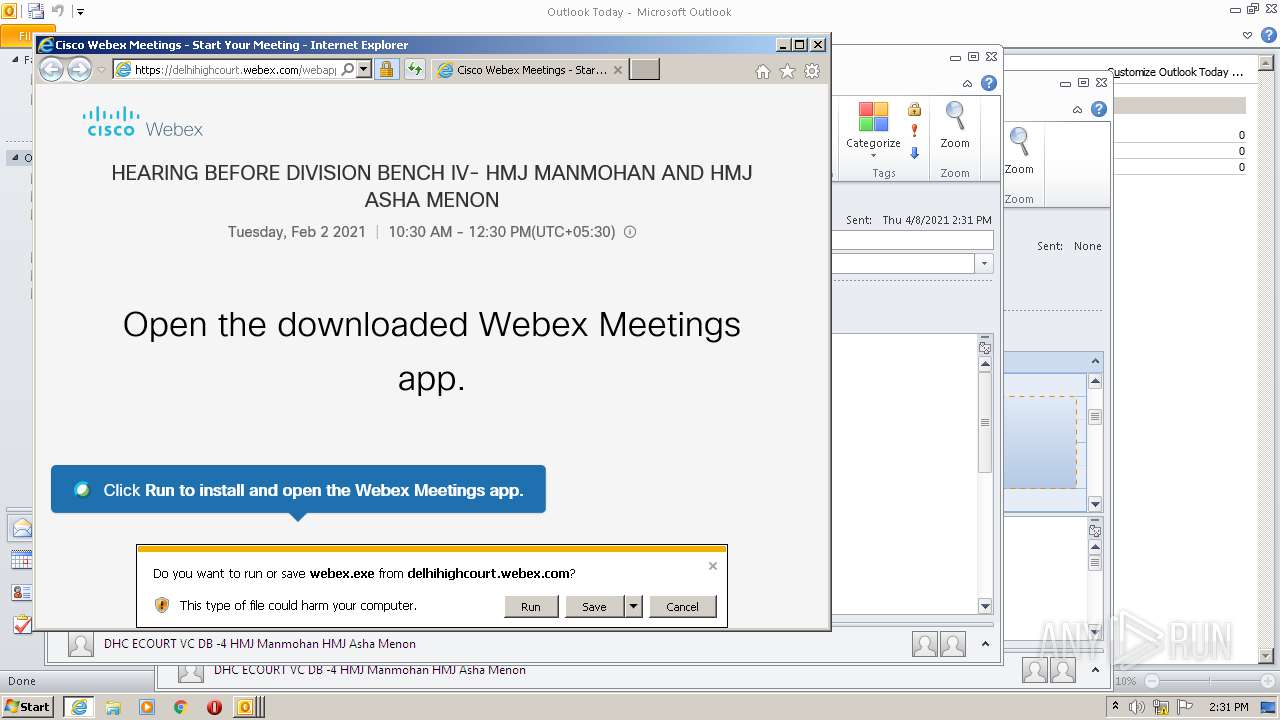
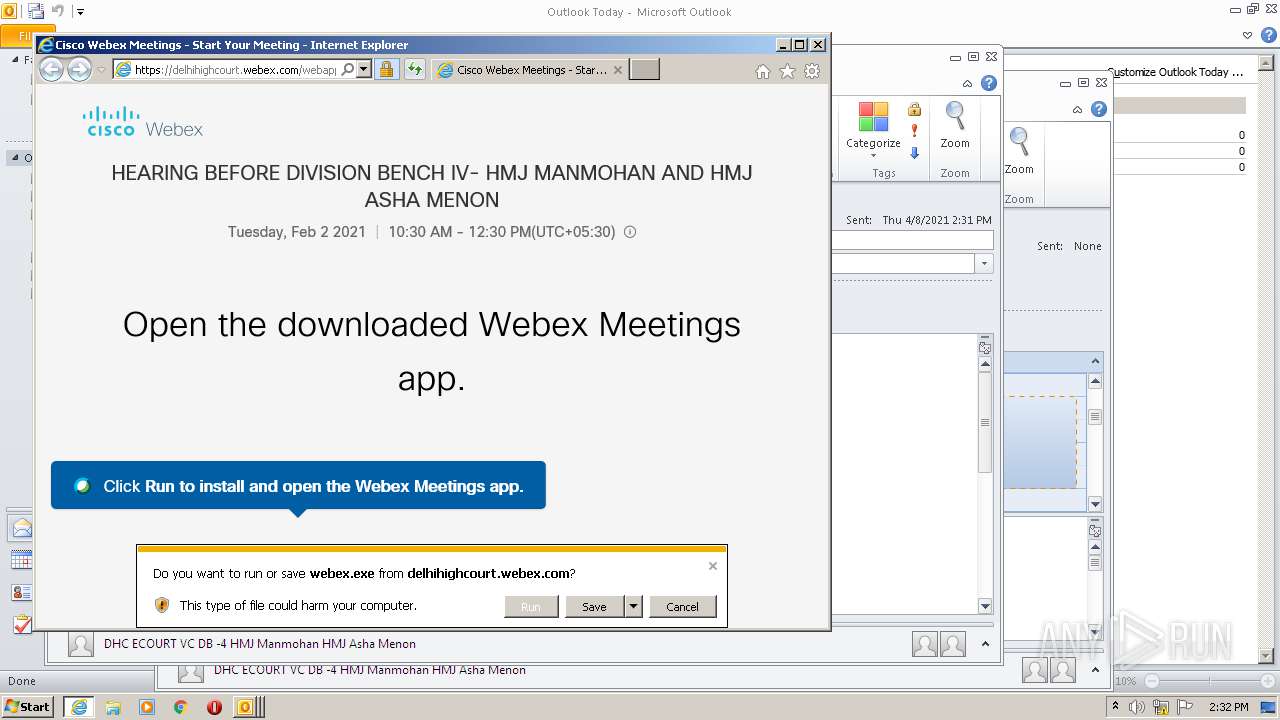
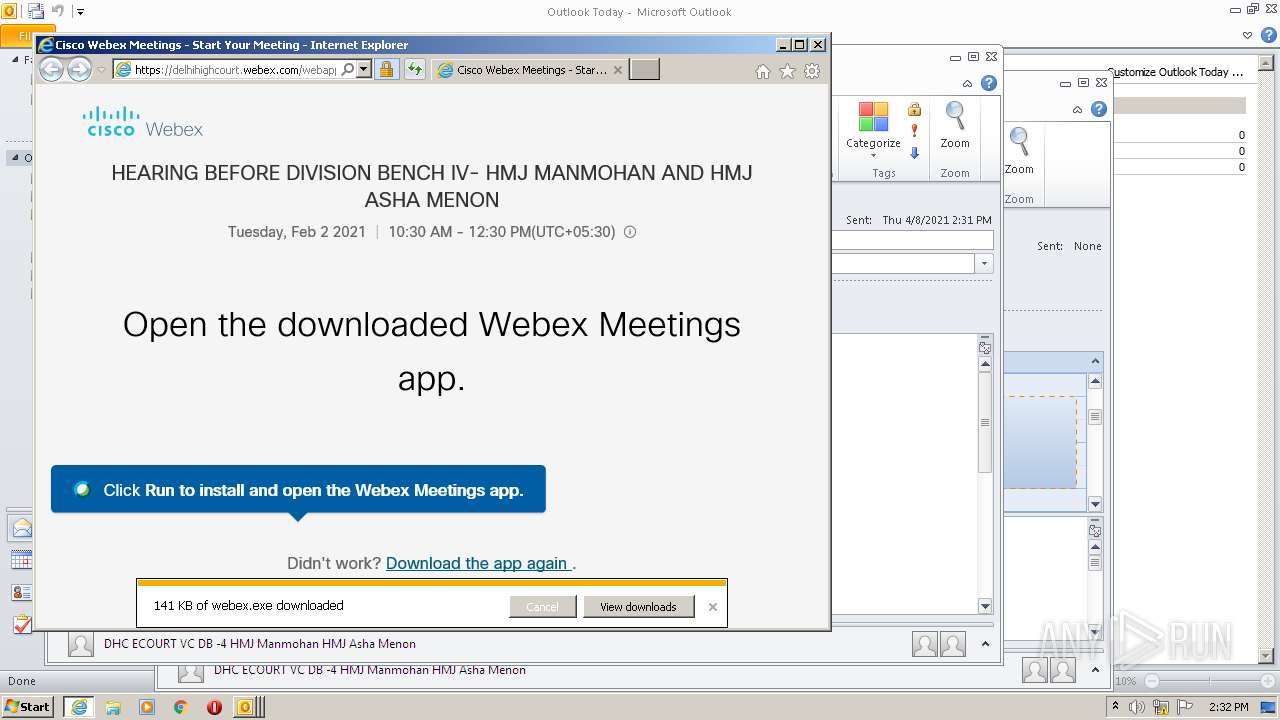
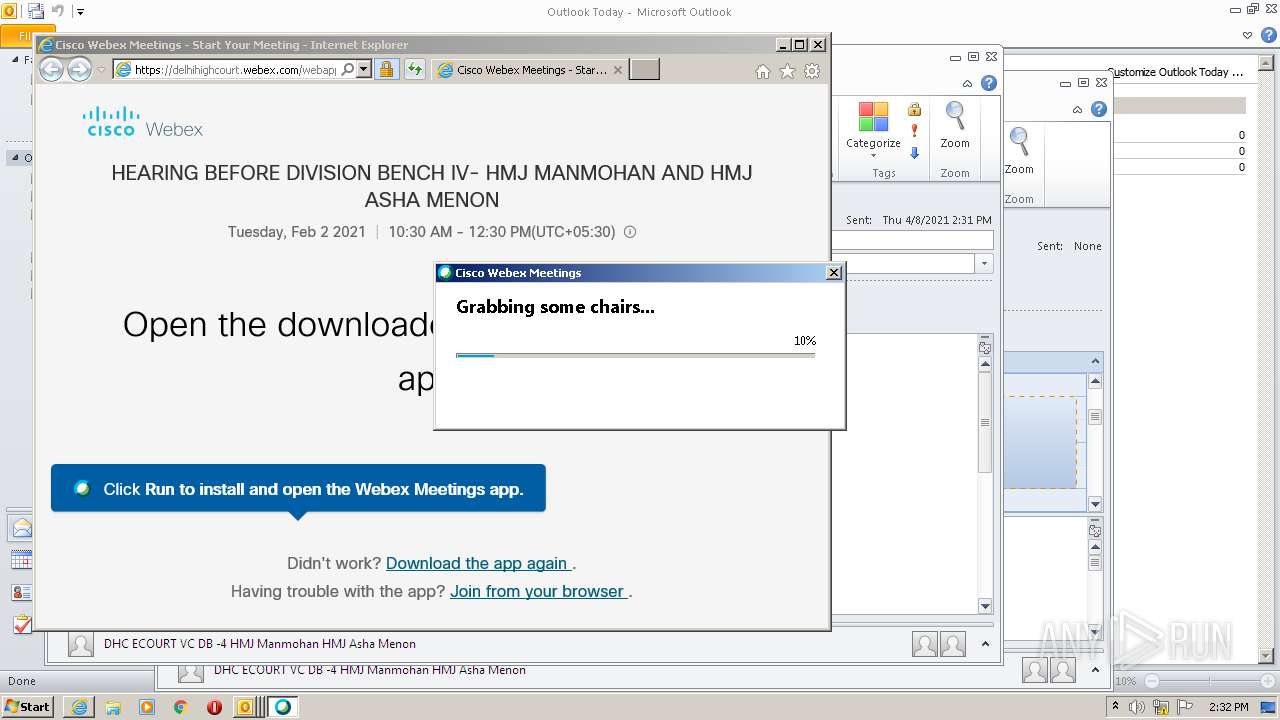
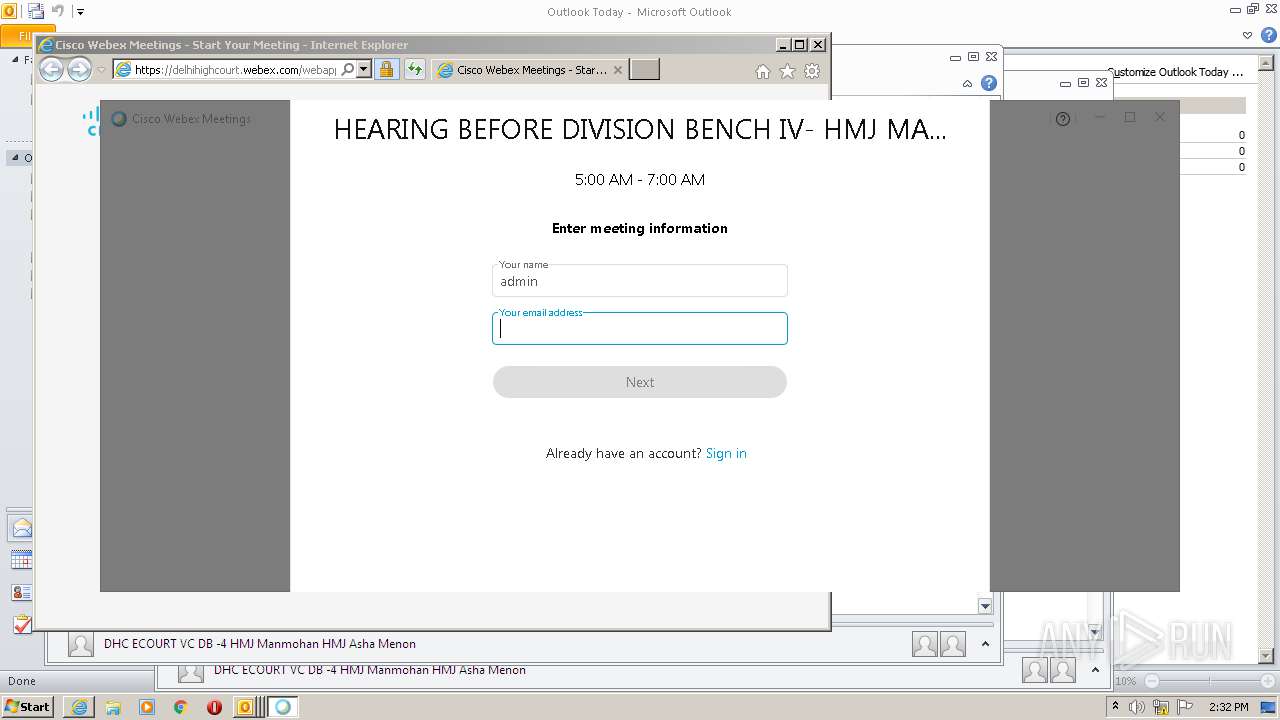
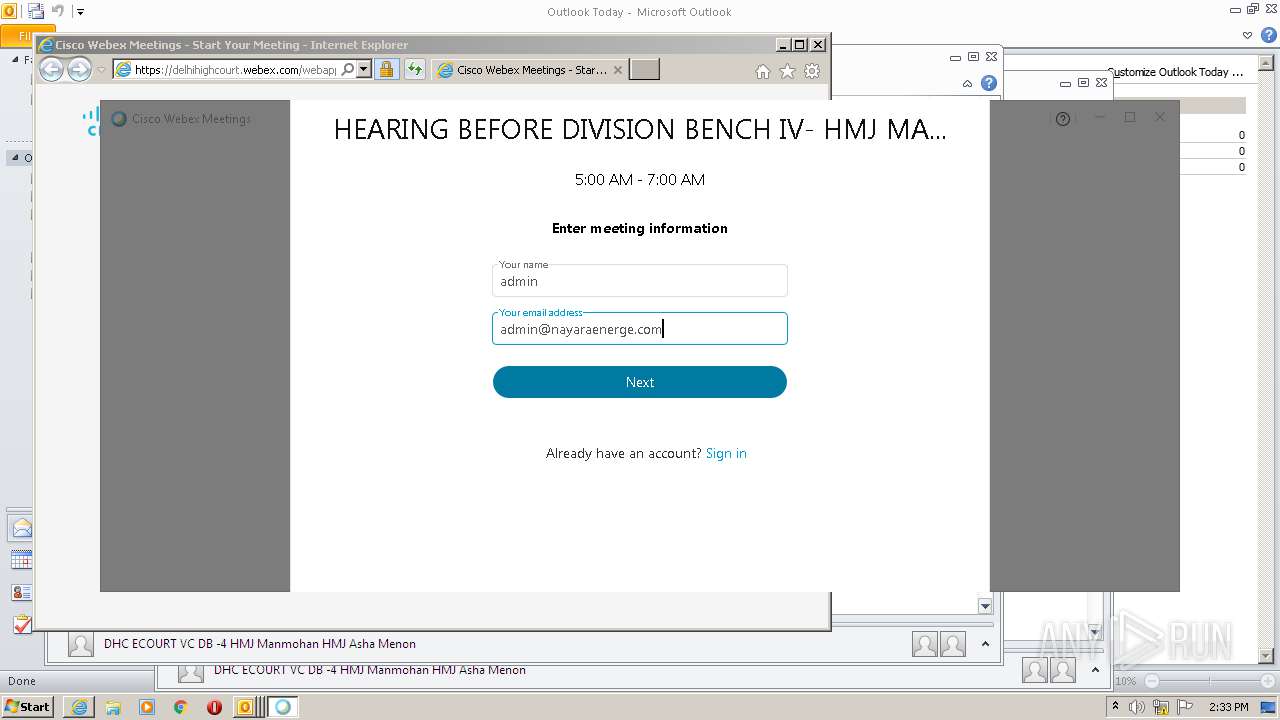
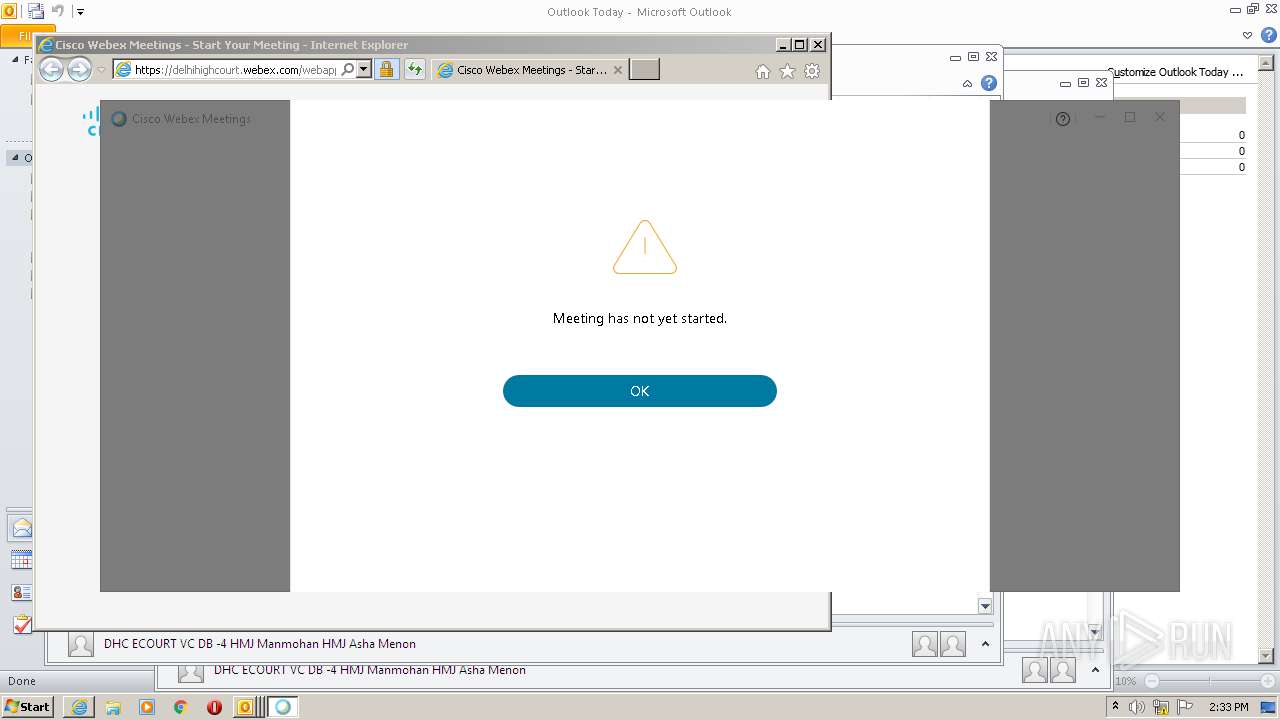
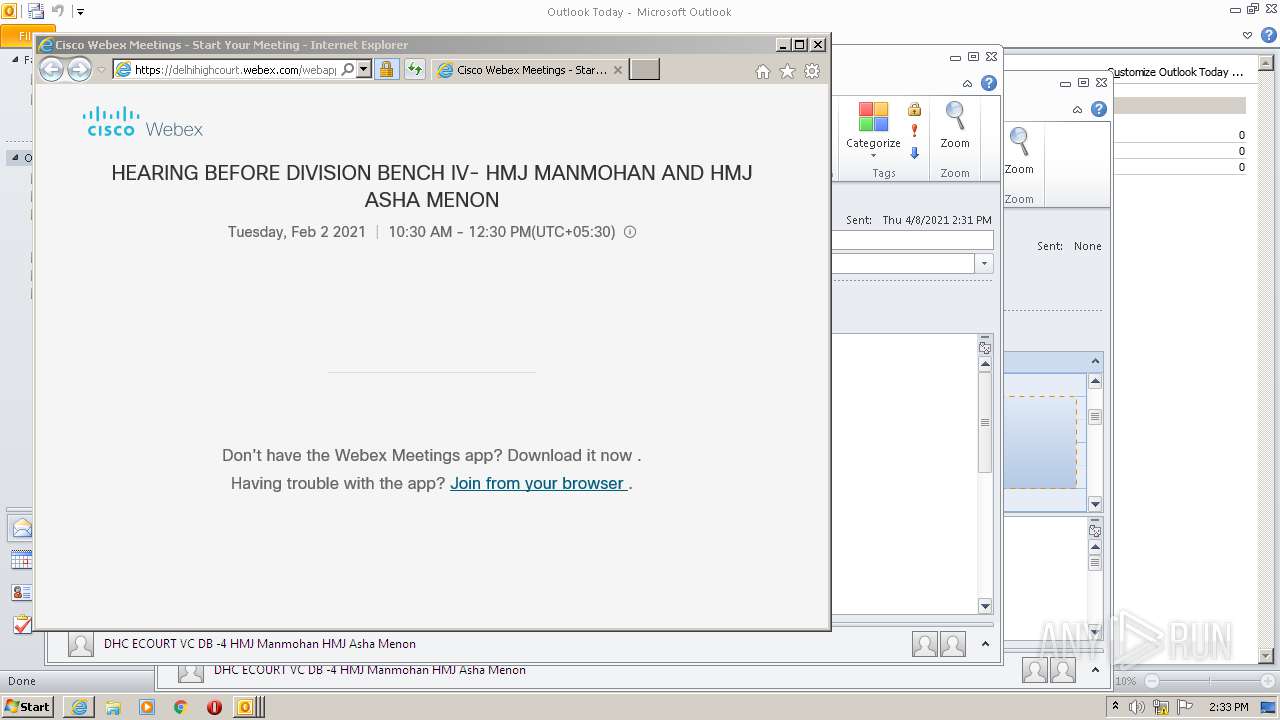
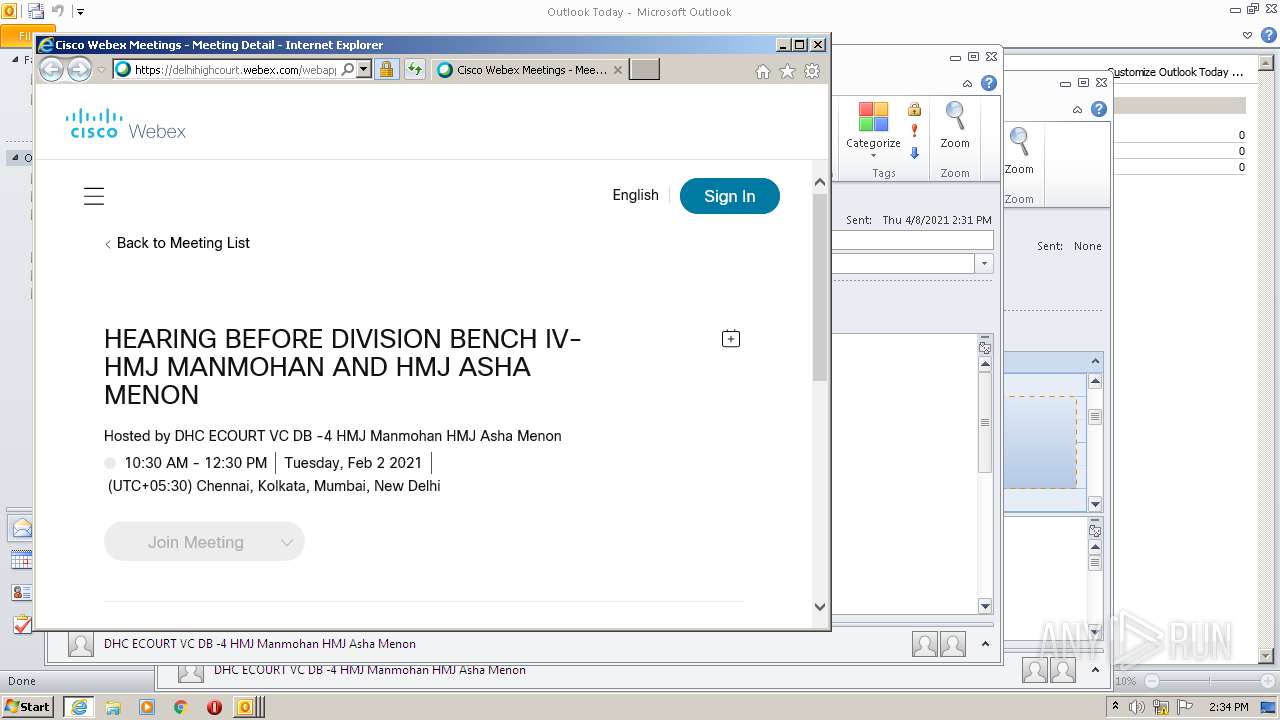
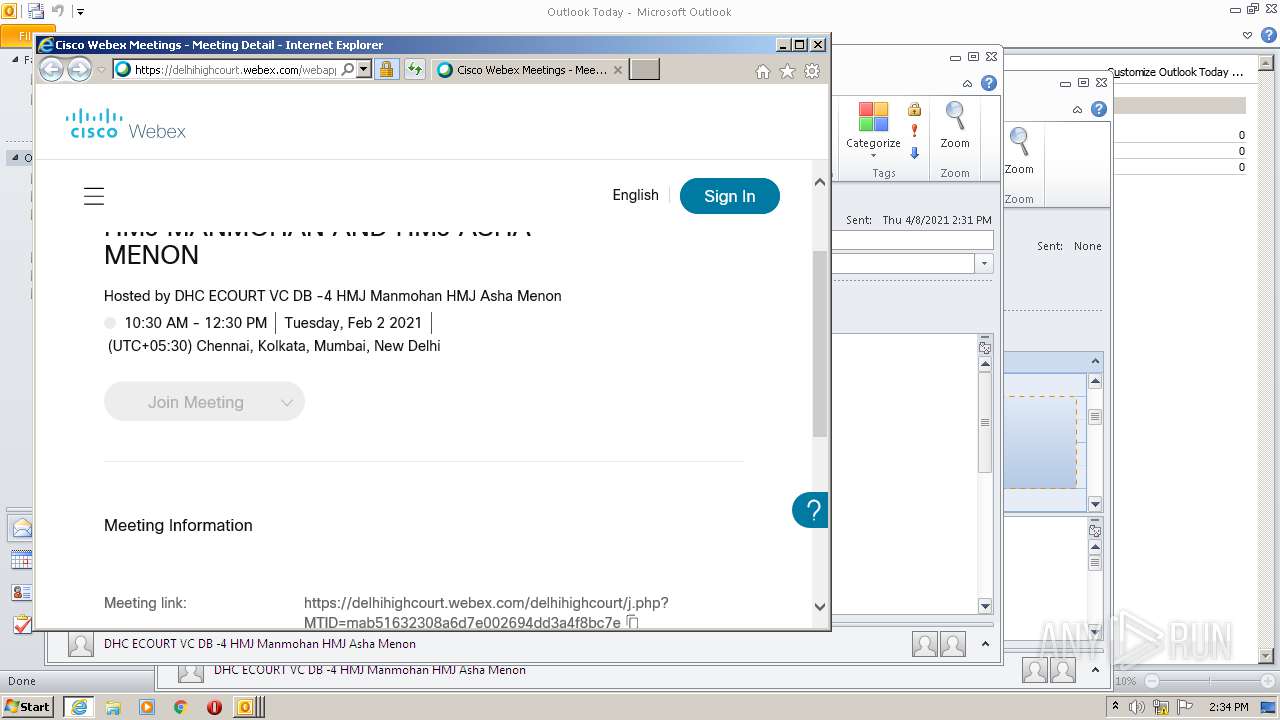
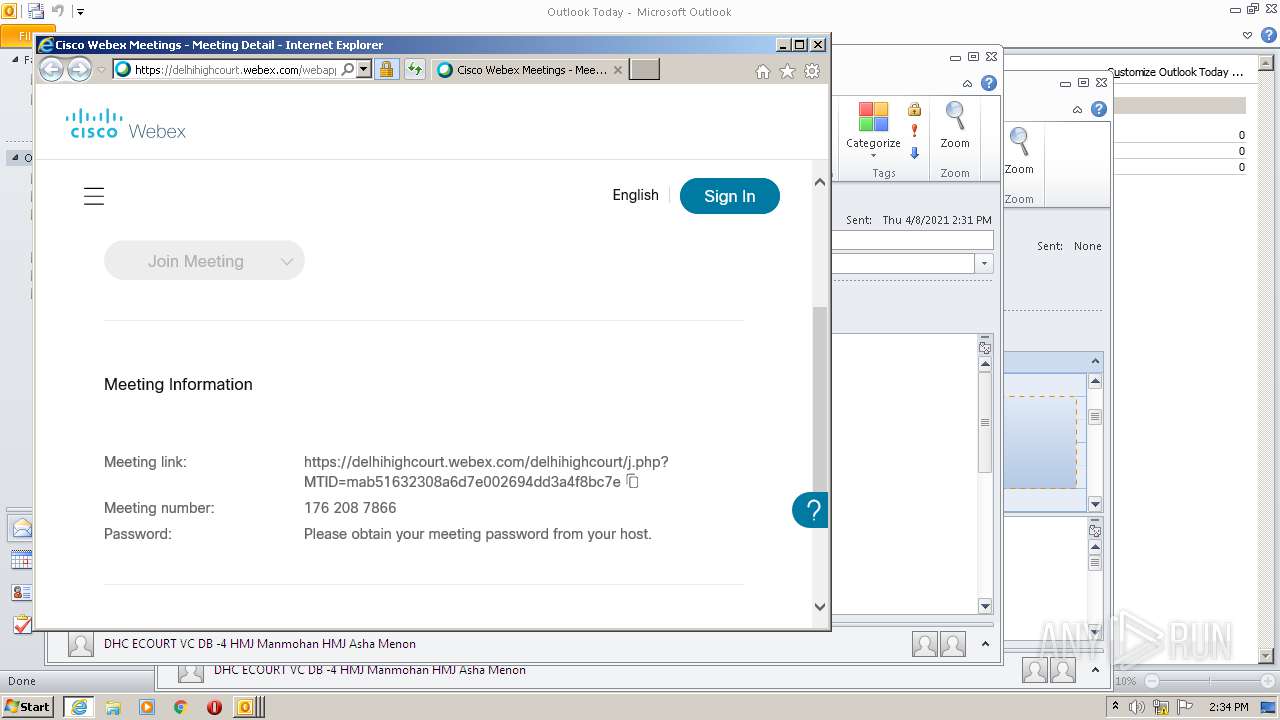
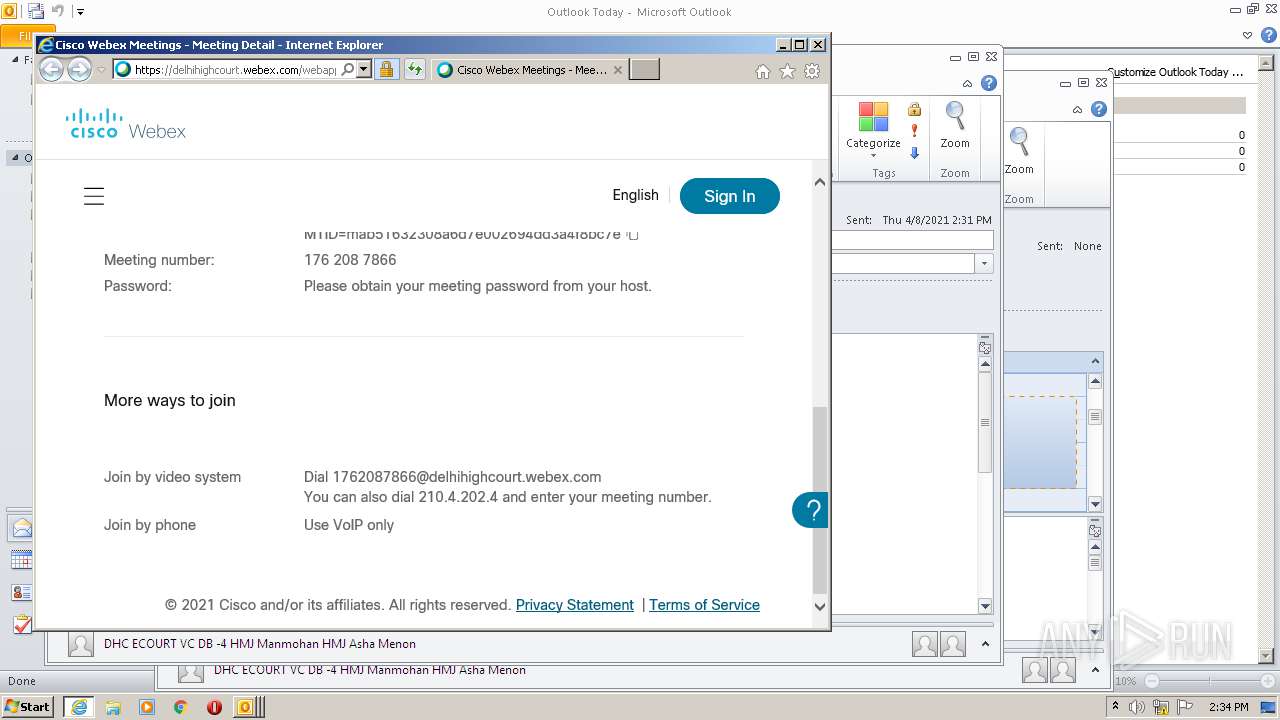
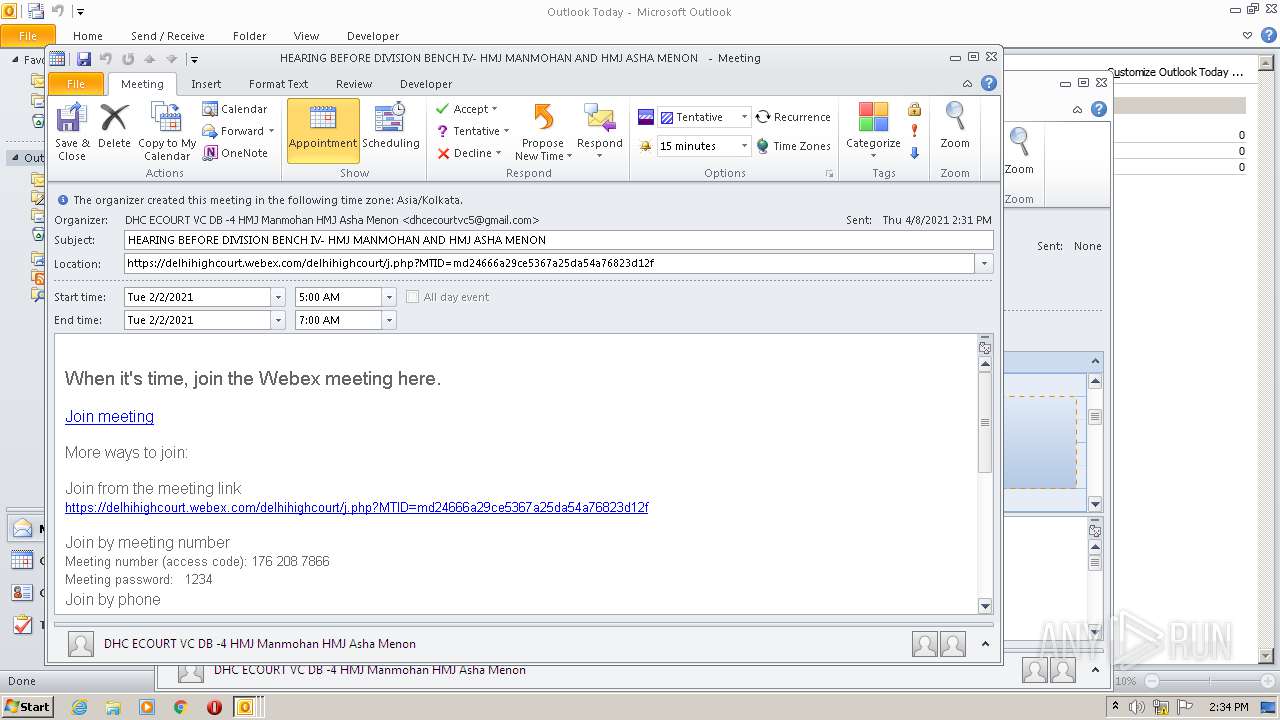
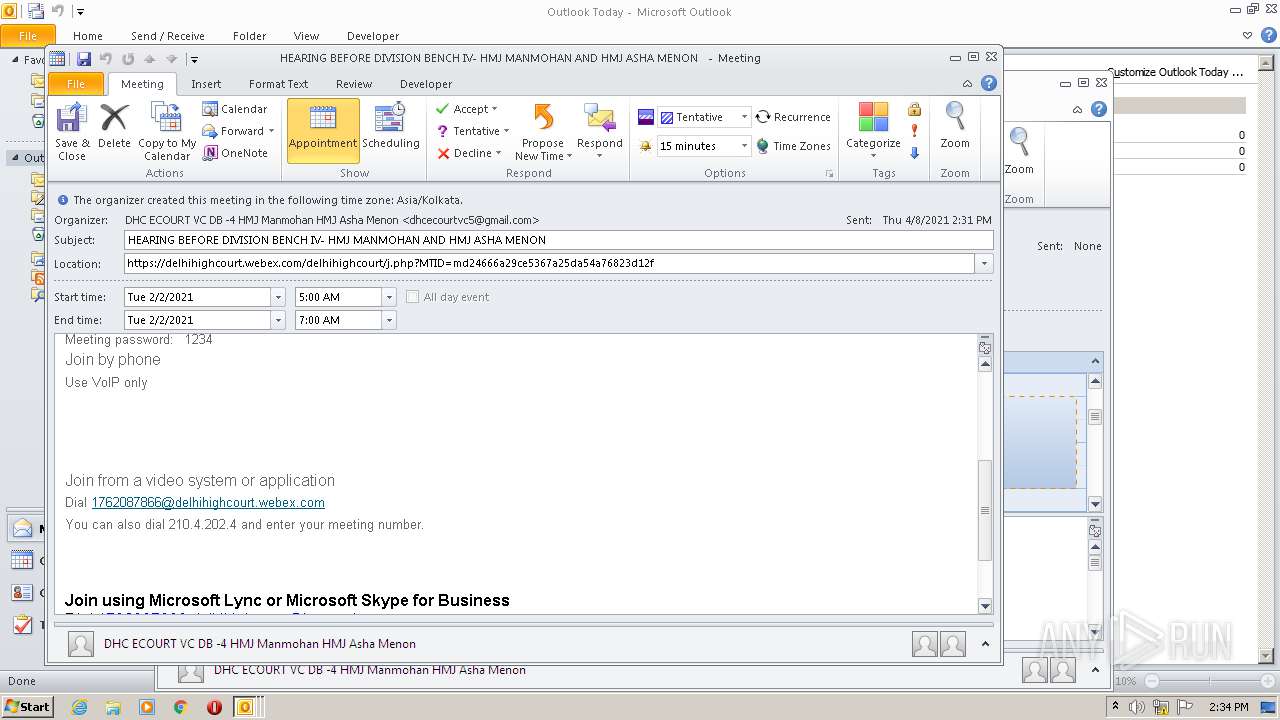
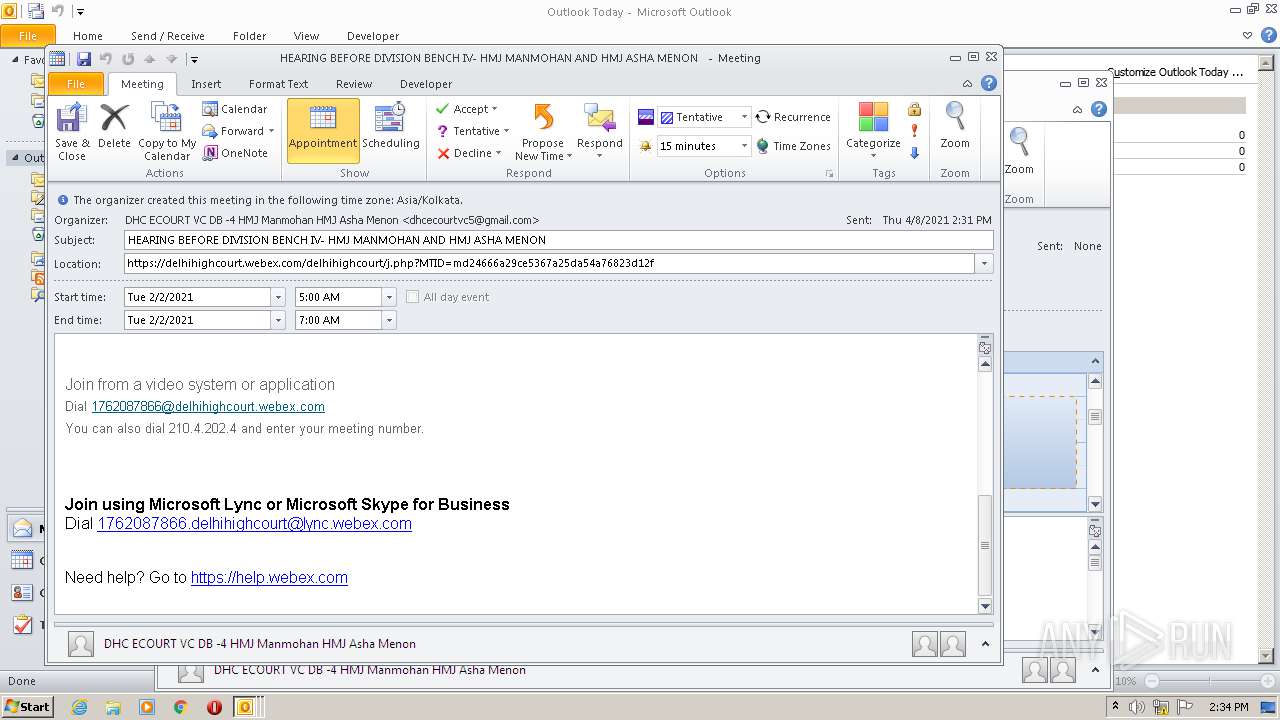
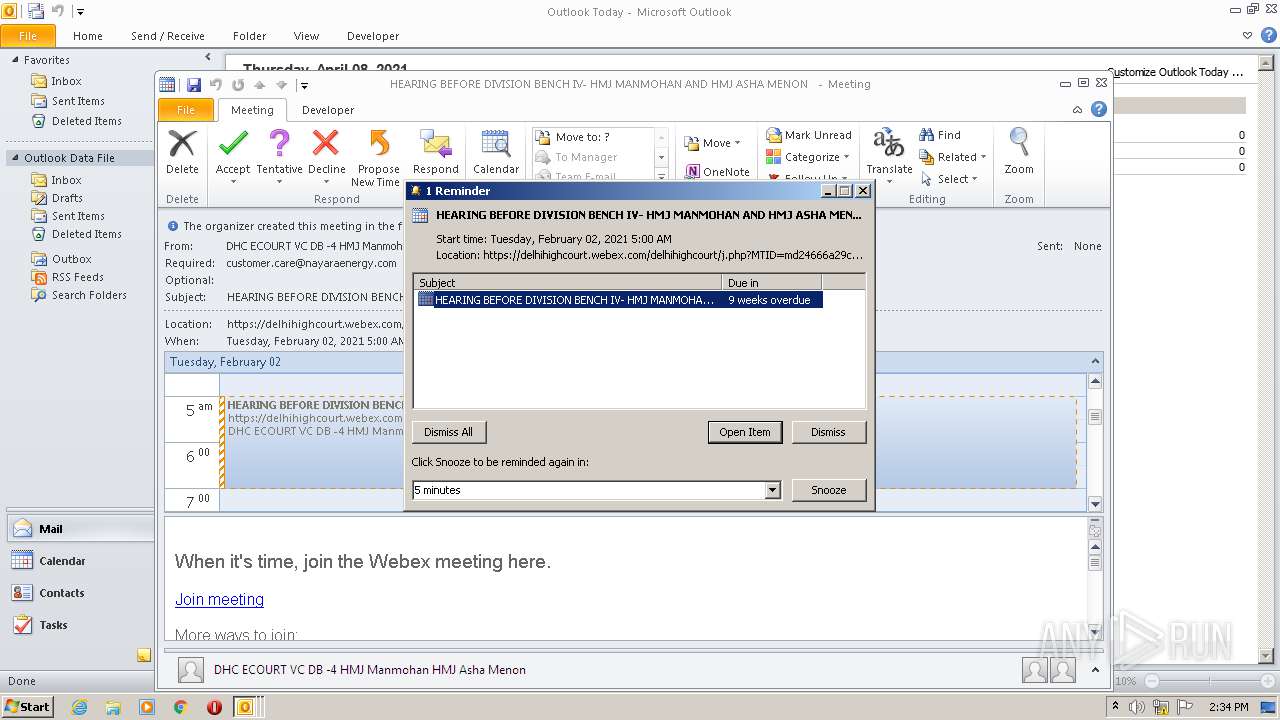
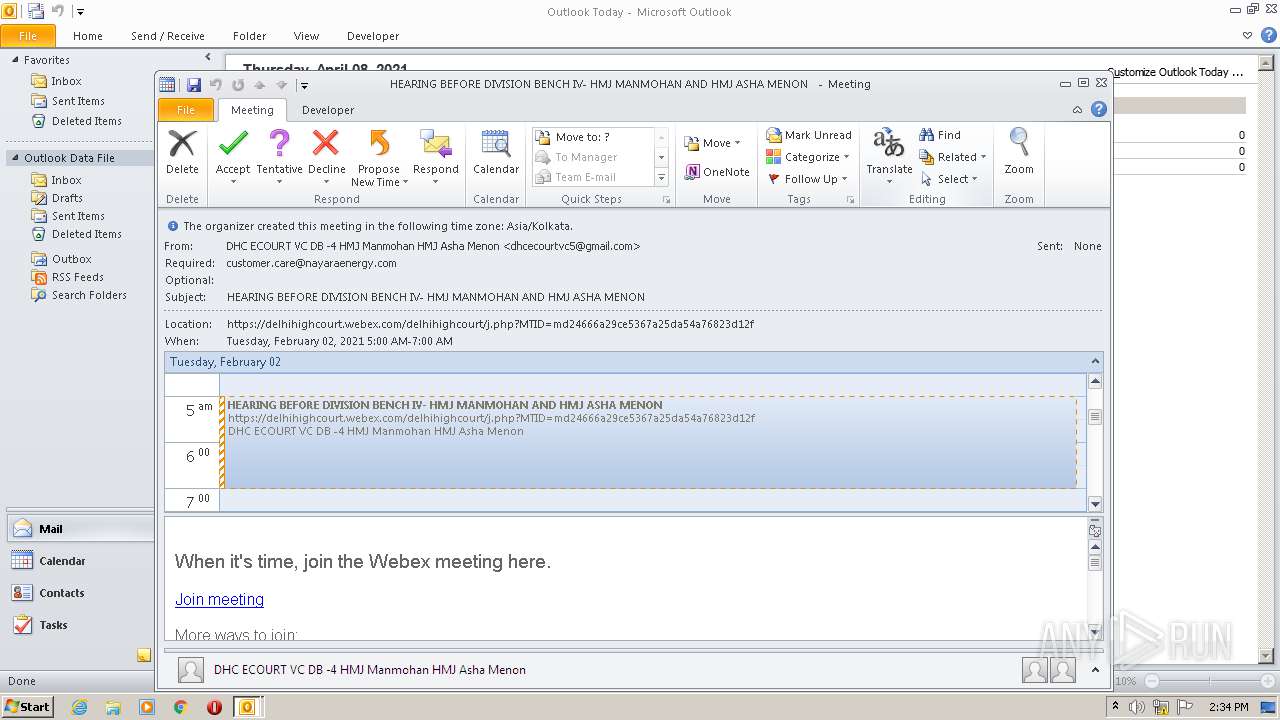
| Summary: | HEARING BEFORE DIVISION BENCH IV- HMJ MANMOHAN AND HMJ ASHA MENON |
| Alt-desc: |
|
| Description: |
|
| UID: | 353a0ed7-c1de-40a6-ad9e-d31755b41d50 |
| SequenceNumber: | 1612182153 |
| TimeTransparency: | OPAQUE |
| Location: | https://delhihighcourt.webex.com/delhihighcourt/j.php?MTID=md24666a29ce5367a25da54a76823d12f |
| DateTimeEndTimezoneID: | Asia/Kolkata |
| DateTimeEnd: | 2021:02:02 12:30:00 |
| DateTimeStartTimezoneID: | Asia/Kolkata |
| DateTimeStart: | 2021:02:02 10:30:00 |
| Organizer: | MAILTO:dhcecourtvc5@gmail.com |
| Attendee: | MAILTO:customer.care@nayaraenergy.com |
| DateTimeStamp: | 2021:02:01 12:22:33Z |
| StandardDateTimeStart: | 1970:01:01 00:00:00 |
| StandardTimezoneName: | IST |
| StandardTimezoneOffsetTo: | +0530 |
| StandardTimezoneOffsetFrom: | +0530 |
| Lic-location: | Asia/Kolkata |
| TimeZoneURL: | http://tzurl.org/zoneinfo-outlook/Asia/Kolkata |
| TimezoneID: | Asia/Kolkata |
| Method: | REQUEST |
| VCalendarVersion: | 2 |
| Software: | -//Microsoft Corporation//Outlook 10.0 MIMEDIR//EN |
Total processes
58
Monitored processes
16
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | /mcstd "C:\Users\admin\AppData\LocalLow\WebEx\preDownload_3208.ini" | c:\users\admin\appdata\local\webex\webex\meetings\atmgr.exe | CiscoWebExStart.exe | ||||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: Cisco Webex Service Exit code: 0 Version: 4104.0000.2103.1900 Modules
| |||||||||||||||
| 1552 | "C:\Users\admin\AppData\Local\WebEx\WebEx\Meetings\wbxreport.exe" C:\Users\admin\AppData\Local\Temp\wbxTraceZip.ini | C:\Users\admin\AppData\Local\WebEx\WebEx\Meetings\wbxreport.exe | — | atmgr.exe | |||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: WBXReport Module Exit code: 0 Version: 4010.0.2008.1800 Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\appdata\local\webex\WEBEXA~1.EXE" /r | C:\Users\admin\appdata\local\webex\WEBEXA~1.EXE | — | atmgr.exe | |||||||||||
User: admin Company: Cisco WebEx LLC Integrity Level: MEDIUM Description: WebEx Productivity Tools Application Exit code: 0 Version: 4104,0,2102,1900 Modules
| |||||||||||||||
| 1848 | "C:\Users\admin\appdata\local\webex\CISCOW~1.EXE" /r | C:\Users\admin\appdata\local\webex\CISCOW~1.EXE | — | atmgr.exe | |||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: Cisco Webex Meetings Exit code: 1 Version: 10051,4104,2021,0323 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2520 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /ical "C:\Users\admin\AppData\Local\Temp\Webex_Meeting - Copy.js.ics" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\WebEx\atcliun.exe" /r MC language=EN | C:\Users\admin\AppData\Local\WebEx\atcliun.exe | — | atmgr.exe | |||||||||||
User: admin Company: Cisco System Inc. Integrity Level: MEDIUM Description: Cisco Webex Uninstaller Exit code: 0 Version: 2800.4101.2011.2001 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" https://delhihighcourt.webex.com/delhihighcourt/j.php?MTID=md24666a29ce5367a25da54a76823d12f | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\WebEx\atcliun.exe" /r MC language=EN | C:\Users\admin\AppData\Local\WebEx\atcliun.exe | — | atmgr.exe | |||||||||||
User: admin Company: Cisco System Inc. Integrity Level: MEDIUM Description: Cisco Webex Uninstaller Exit code: 0 Version: 2800.4101.2011.2001 Modules
| |||||||||||||||
| 2892 | /mcstd "C:\Users\admin\AppData\LocalLow\WebEx\webex_3288.ini" | C:\Users\admin\AppData\Local\WebEx\WebEx\Meetings\atmgr.exe | cws1.tmp | ||||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: Cisco Webex Service Exit code: 0 Version: 4104.0000.2103.1900 Modules
| |||||||||||||||
Total events
4 949
Read events
3 769
Write events
1 134
Delete events
46
Modification events
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
214
Suspicious files
264
Text files
201
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF645.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\C2Q0JOAYF8YMLCYB119R.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF44B93F10B7DEDF55.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF76FAE74F94FFF881.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFEDDE9EA750CC1F51.TMP | — | |
MD5:— | SHA256:— | |||
| 2164 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA4E4.tmp | — | |
MD5:— | SHA256:— | |||
| 2164 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA4E5.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\30628a0881e64cfaa7337e5e15cf91ee[1].htm | html | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Microsoft Outlook.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
75
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2208 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2164 | iexplore.exe | GET | 200 | 35.158.10.169:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHUXFneD0EN%2BtVbDV5RuRWO469Os | DE | der | 1.78 Kb | whitelisted |
2164 | iexplore.exe | GET | 200 | 35.156.254.208:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHI7b%2BXCUnVNIYmwkVVSGjGHkW24 | DE | der | 1.78 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2164 | iexplore.exe | GET | 200 | 35.156.254.208:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHI7b%2BXCUnVNIYmwkVVSGjGHkW24 | DE | der | 1.78 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2164 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2164 | iexplore.exe | 64.68.120.41:443 | tsa.webex.com | Cisco Webex LLC | US | unknown |
2208 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2164 | iexplore.exe | 114.29.213.193:443 | delhihighcourt.webex.com | Cisco Webex LLC | SG | suspicious |
2164 | iexplore.exe | 35.158.10.169:80 | ocsp.quovadisglobal.com | Amazon.com, Inc. | DE | whitelisted |
2164 | iexplore.exe | 35.156.254.208:80 | ocsp.quovadisglobal.com | Amazon.com, Inc. | DE | unknown |
2164 | iexplore.exe | 92.122.252.10:443 | akamaicdn.webex.com | GTT Communications Inc. | — | unknown |
2520 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3036 | webex.exe | 114.29.213.193:443 | delhihighcourt.webex.com | Cisco Webex LLC | SG | suspicious |
2520 | iexplore.exe | 104.18.10.39:80 | cacerts.digicert.com | Cloudflare Inc | US | shared |
3288 | cws1.tmp | 92.122.252.10:443 | akamaicdn.webex.com | GTT Communications Inc. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
delhihighcourt.webex.com |
| suspicious |
ocsp.quovadisglobal.com |
| whitelisted |
akamaicdn.webex.com |
| whitelisted |
nebulaas.webex.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
cacerts.digicert.com |
| whitelisted |
tsa.webex.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |